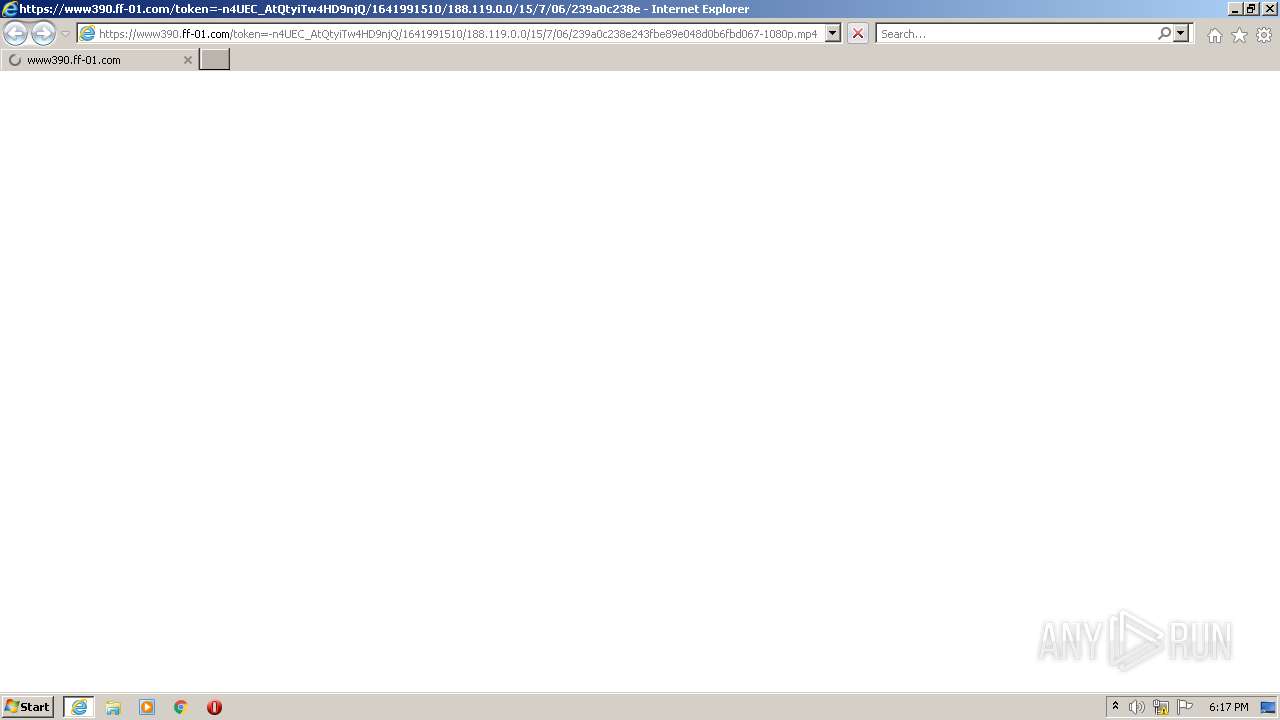
| URL: | https://www390.ff-01.com/token=-n4UEC_AtQtyiTw4HD9njQ/1641991510/188.119.0.0/15/7/06/239a0c238e243fbe89e048d0b6fbd067-1080p.mp4 |
| Full analysis: | https://app.any.run/tasks/dc30812b-f106-4988-8834-5f6c1fa48864 |
| Verdict: | Malicious activity |
| Analysis date: | January 15, 2022, 18:17:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C2C76E2CC98F26F7E215E7308336D655 |
| SHA1: | CF5E9D1F0ED59A6566D5FEB279CEAF8B45693735 |
| SHA256: | B9640FFBC394CCF47D13ABF2F4C6A08F0D785B49FB77E27022DC3233C832B0A9 |
| SSDEEP: | 3:N8DSWcVhGdMg2/Rta4bc0OLh2JsGXLBrJHPHjEVxM:2O2dh2TXbc0BsALL2M |
MALICIOUS
Loads the Task Scheduler COM API
- CCleaner.exe (PID: 3572)
- CCleaner.exe (PID: 3684)
Drops executable file immediately after starts
- CCleaner.exe (PID: 3684)
Changes settings of System certificates
- CCleaner.exe (PID: 3684)
Loads dropped or rewritten executable
- CCleaner.exe (PID: 3684)
SUSPICIOUS
Executed via COM
- DllHost.exe (PID: 2120)
Reads Environment values
- CCleaner.exe (PID: 3572)
- CCleaner.exe (PID: 3684)
Checks supported languages
- CCleaner.exe (PID: 3572)
- CCleaner.exe (PID: 3684)
Reads the computer name
- CCleaner.exe (PID: 3572)
- CCleaner.exe (PID: 3684)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3764)
Creates files in the program directory
- CCleaner.exe (PID: 3684)
Executable content was dropped or overwritten
- CCleaner.exe (PID: 3684)
Reads the date of Windows installation
- CCleaner.exe (PID: 3684)
Reads CPU info
- CCleaner.exe (PID: 3684)
Reads internet explorer settings
- CCleaner.exe (PID: 3684)
Creates files in the user directory
- CCleaner.exe (PID: 3684)
Executed via Task Scheduler
- CCleaner.exe (PID: 3684)
Drops a file that was compiled in debug mode
- CCleaner.exe (PID: 3684)
Searches for installed software
- CCleaner.exe (PID: 3684)
Adds / modifies Windows certificates
- CCleaner.exe (PID: 3684)
INFO
Reads the computer name
- iexplore.exe (PID: 2752)
- iexplore.exe (PID: 3764)
- DllHost.exe (PID: 2120)
Checks Windows Trust Settings
- iexplore.exe (PID: 2752)
- iexplore.exe (PID: 3764)
- CCleaner.exe (PID: 3684)
Reads the date of Windows installation
- iexplore.exe (PID: 2752)
Reads settings of System Certificates
- iexplore.exe (PID: 3764)
- iexplore.exe (PID: 2752)
- CCleaner.exe (PID: 3684)
Reads internet explorer settings
- iexplore.exe (PID: 3764)
Checks supported languages
- DllHost.exe (PID: 2120)
- iexplore.exe (PID: 3764)
- iexplore.exe (PID: 2752)
Manual execution by user
- CCleaner.exe (PID: 3572)
Changes internet zones settings
- iexplore.exe (PID: 2752)
Application launched itself
- iexplore.exe (PID: 2752)
Reads the hosts file
- CCleaner.exe (PID: 3684)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
45
Monitored processes
5
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2120 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
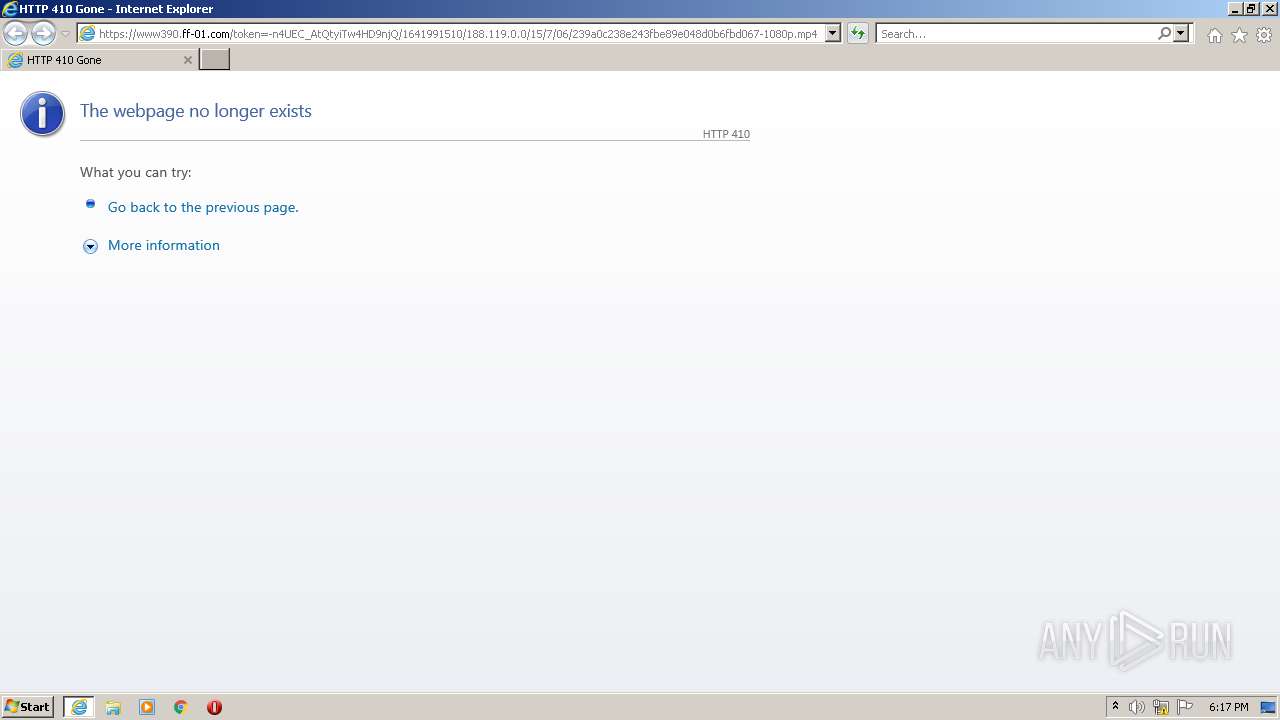
| 2752 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www390.ff-01.com/token=-n4UEC_AtQtyiTw4HD9njQ/1641991510/188.119.0.0/15/7/06/239a0c238e243fbe89e048d0b6fbd067-1080p.mp4" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
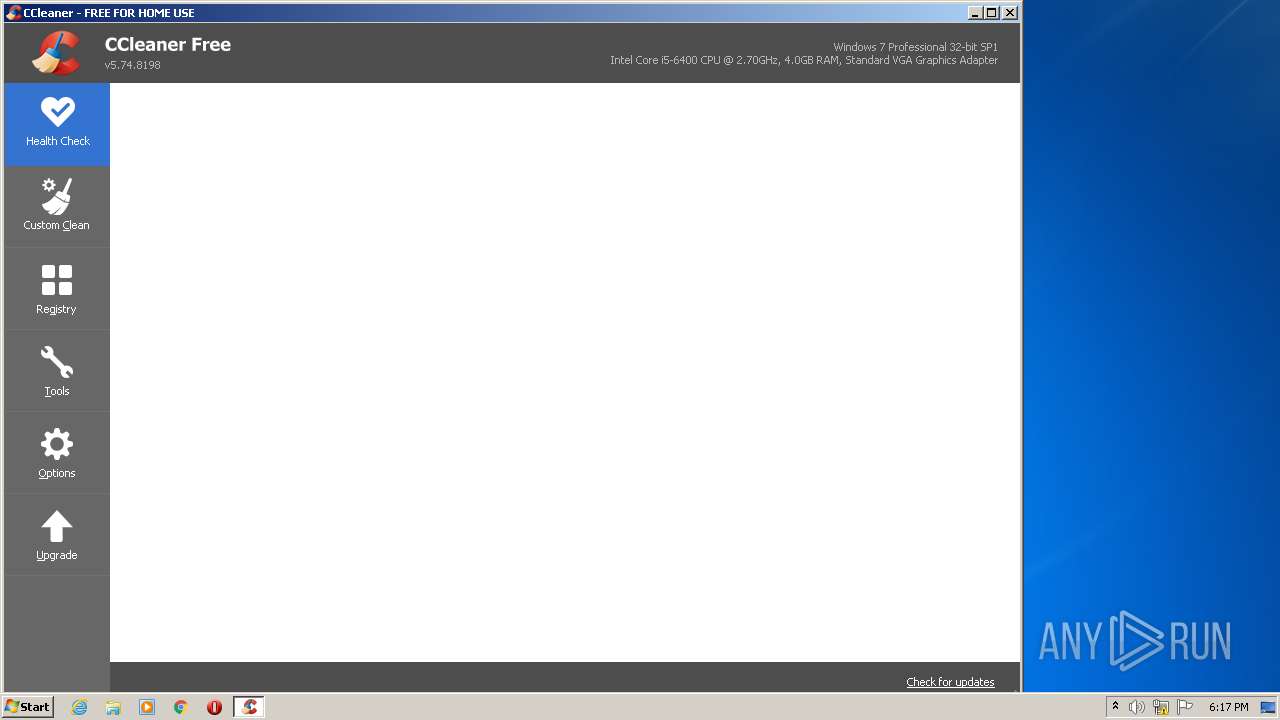
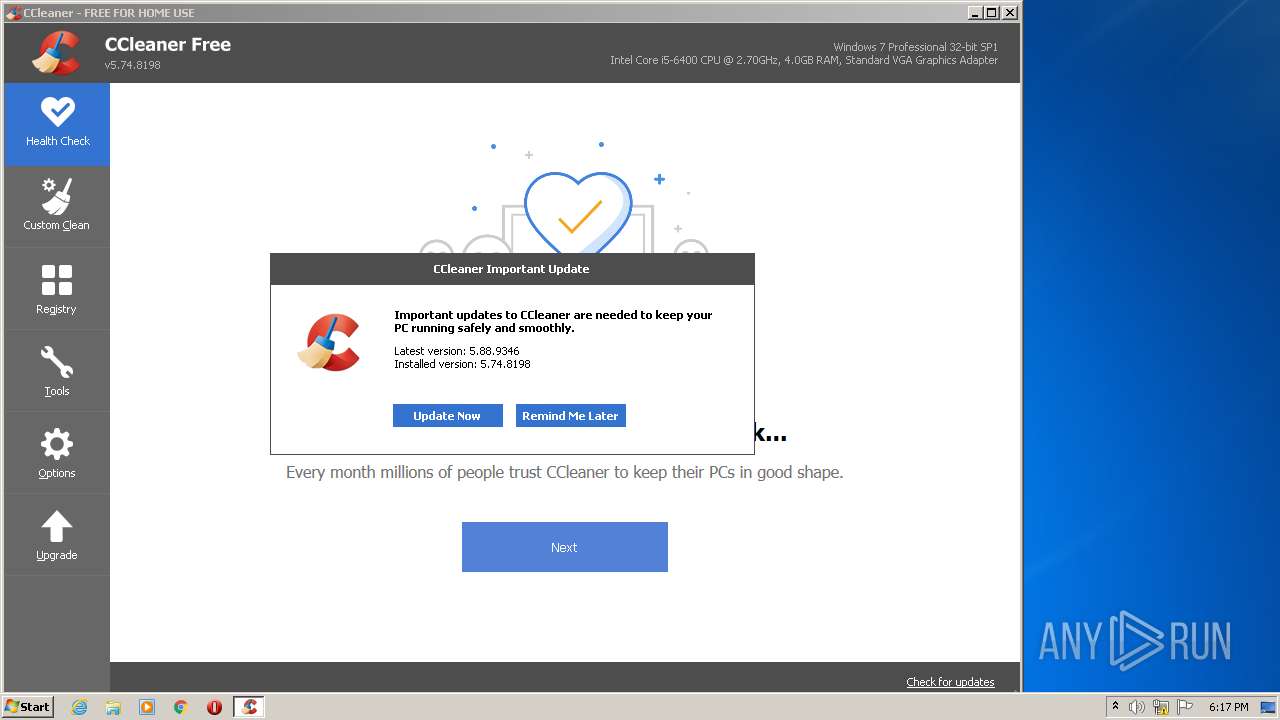
| 3572 | "C:\Program Files\CCleaner\CCleaner.exe" | C:\Program Files\CCleaner\CCleaner.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Piriform Software Ltd Integrity Level: MEDIUM Description: CCleaner Exit code: 0 Version: 5.74.0.8198 Modules
| |||||||||||||||
| 3684 | "C:\Program Files\CCleaner\CCleaner.exe" /uac | C:\Program Files\CCleaner\CCleaner.exe | taskeng.exe | ||||||||||||
User: admin Company: Piriform Software Ltd Integrity Level: HIGH Description: CCleaner Exit code: 0 Version: 5.74.0.8198 Modules
| |||||||||||||||
| 3764 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2752 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
20 747
Read events
20 455
Write events
261
Delete events
31
Modification events
| (PID) Process: | (2752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 446574848 | |||
| (PID) Process: | (2752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30935612 | |||
| (PID) Process: | (2752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 746739301 | |||
| (PID) Process: | (2752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30935612 | |||
| (PID) Process: | (2752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
2
Suspicious files
19
Text files
11
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3764 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2752 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 2752 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 3764 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\3538626A1FCCCA43C7E18F220BDD9B02 | der | |
MD5:— | SHA256:— | |||
| 3764 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | binary | |
MD5:— | SHA256:— | |||
| 3764 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | der | |
MD5:— | SHA256:— | |||
| 3764 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\FED433BE71543CCB62C77C994DCBBB03 | der | |
MD5:— | SHA256:— | |||
| 3764 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\FED433BE71543CCB62C77C994DCBBB03 | binary | |
MD5:— | SHA256:— | |||
| 3764 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\3538626A1FCCCA43C7E18F220BDD9B02 | binary | |
MD5:— | SHA256:— | |||
| 2752 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\RecoveryStore.{42C873D0-1D90-11EB-BA2C-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
31
DNS requests
23
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2752 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3764 | iexplore.exe | GET | 200 | 104.18.31.182:80 | http://crl.usertrust.com/USERTrustRSACertificationAuthority.crl | US | der | 978 b | whitelisted |
3684 | CCleaner.exe | GET | 200 | 151.101.2.202:80 | http://www.ccleaner.com/auto?a=0&p=cc&v=5.74.8198&l=1033&lk=&mk=IJR6-W5SV-5KYR-QBZD-6BY4-RN5Z-WAV9-RVK2-HZ8S&o=6.1W3&au=0&mx=97B7721C4994E2556FF6A439510F665DB45337A341A47E15F4997584423BF714&gd=19ce970b-f6c0-4a09-bae4-274b971730e0 | US | text | 61 b | whitelisted |
3764 | iexplore.exe | GET | 200 | 104.18.31.182:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEA%2FiBetP1QN%2FMJbWitZZqNo%3D | US | der | 471 b | whitelisted |
3684 | CCleaner.exe | GET | 200 | 104.18.20.226:80 | http://ocsp2.globalsign.com/rootr3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEHophRq39F1meVBmQbb%2F1x0%3D | US | der | 1.40 Kb | whitelisted |
3764 | iexplore.exe | GET | 200 | 104.18.30.182:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
3684 | CCleaner.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
3684 | CCleaner.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAonX%2BcE1u7LI9XNW0saTgQ%3D | US | der | 471 b | whitelisted |
3684 | CCleaner.exe | GET | 200 | 104.18.20.226:80 | http://ocsp2.globalsign.com/rootr3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEHgDGCDPAjbzpoUYuu%2B39wE%3D | US | der | 1.40 Kb | whitelisted |
3684 | CCleaner.exe | GET | 200 | 151.101.2.109:80 | http://license.piriform.com/verify/?p=ccpro&c=cc&cv=5.74.8198&l=1033&lk=CJ9T-J7CU-SPNV-GWMB-WBEC&mk=IJR6-W5SV-5KYR-QBZD-6BY4-RN5Z-WAV9-RVK2-HZ8S&mx=97B7721C4994E2556FF6A439510F665DB45337A341A47E15F4997584423BF714&gd=19ce970b-f6c0-4a09-bae4-274b971730e0 | US | text | 14 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3764 | iexplore.exe | 95.211.249.168:443 | www390.ff-01.com | LeaseWeb Netherlands B.V. | NL | unknown |
3764 | iexplore.exe | 8.253.204.249:80 | ctldl.windowsupdate.com | Global Crossing | US | suspicious |
3764 | iexplore.exe | 104.18.31.182:80 | ocsp.comodoca.com | Cloudflare Inc | US | unknown |
2752 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2752 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3764 | iexplore.exe | 104.18.30.182:80 | ocsp.comodoca.com | Cloudflare Inc | US | suspicious |
3764 | iexplore.exe | 67.27.233.126:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
2752 | iexplore.exe | 152.199.19.161:443 | r20swj13mr.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3684 | CCleaner.exe | 5.62.40.214:443 | analytics.ff.avast.com | AVAST Software s.r.o. | DE | unknown |
3684 | CCleaner.exe | 151.101.2.202:80 | www.ccleaner.com | Fastly | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www390.ff-01.com |
| unknown |
www.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
crl.usertrust.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3684 | CCleaner.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
Process | Message |
|---|---|
CCleaner.exe | Failed to open log file 'C:\Program Files\CCleaner' |
CCleaner.exe | startCheckingLicense()
|
CCleaner.exe | Using Sciter version 4.4.4.4-r8057
|
CCleaner.exe | OnLanguage - en
|
CCleaner.exe | OnLanguage - en
|
CCleaner.exe | observing CurrentIndex changed - 0
|
CCleaner.exe | observing CurrentIndex changed - Context.FirstTime=true CurrentIndex=0 LastIndex=4
|
CCleaner.exe | observing currentResultDetails changed - None
|
CCleaner.exe | SetStrings - Live Region updated: ,
|
CCleaner.exe | observing currentModeType changed - Preview
|