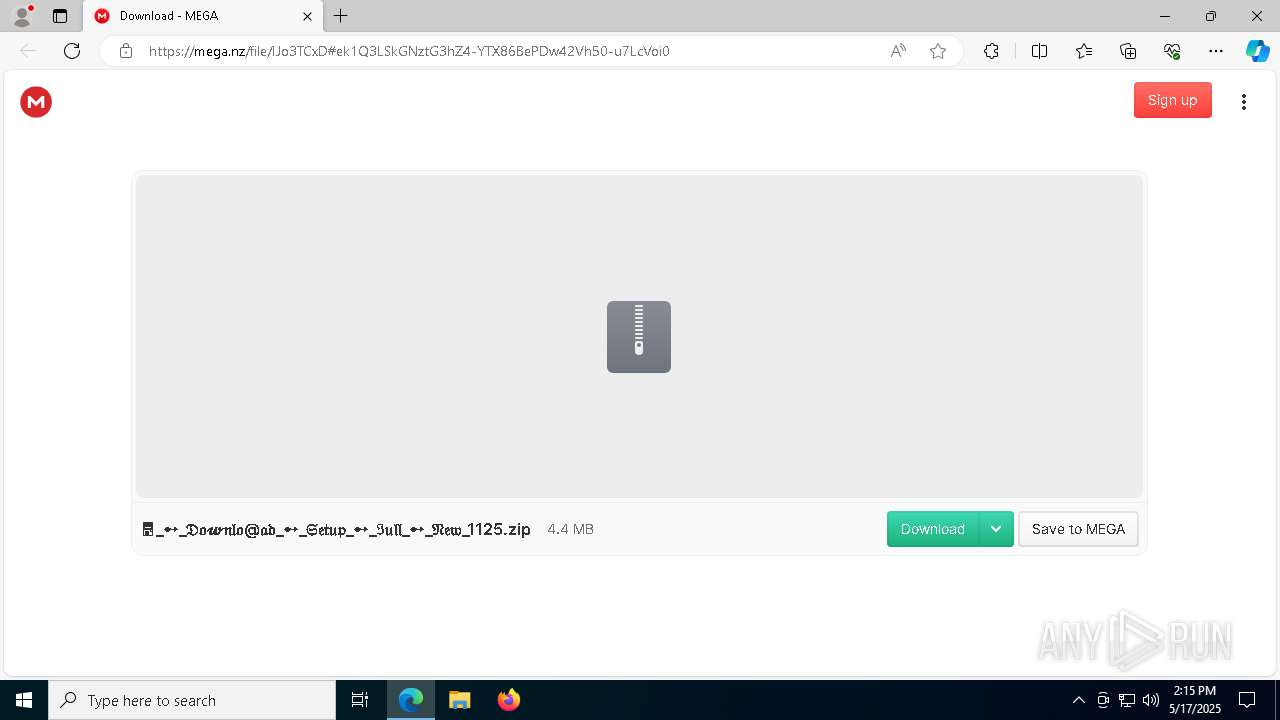
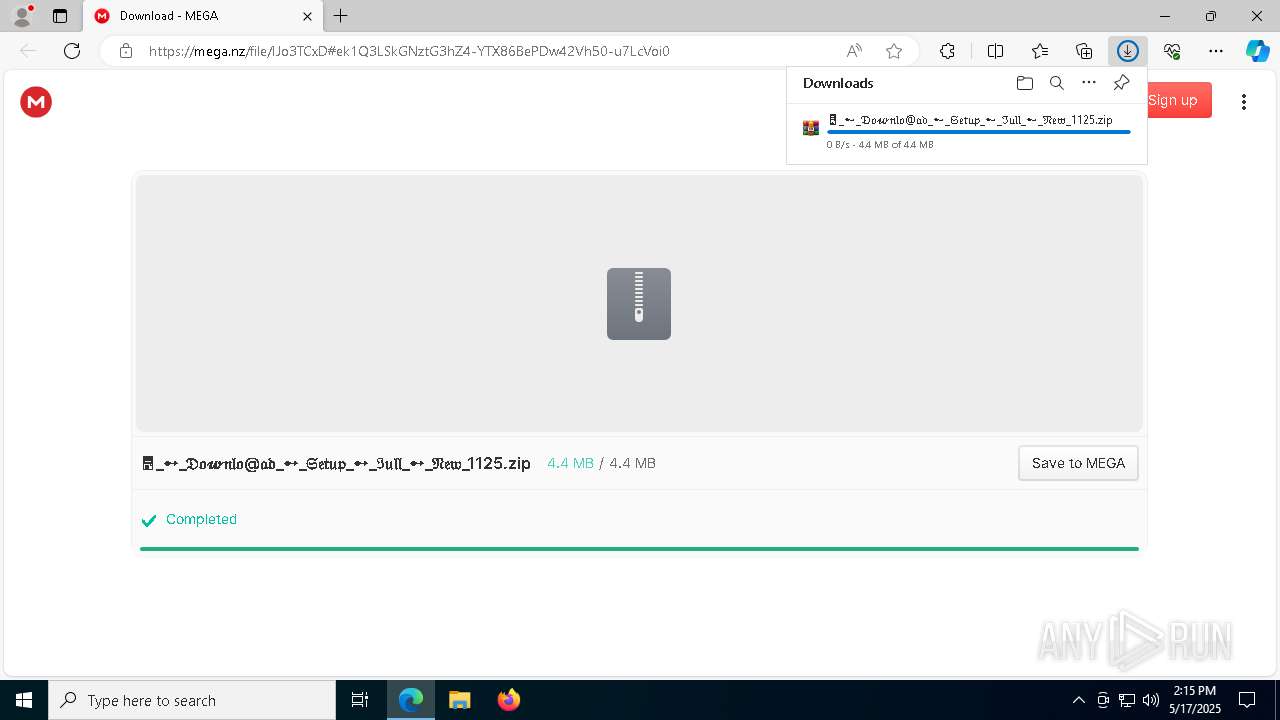
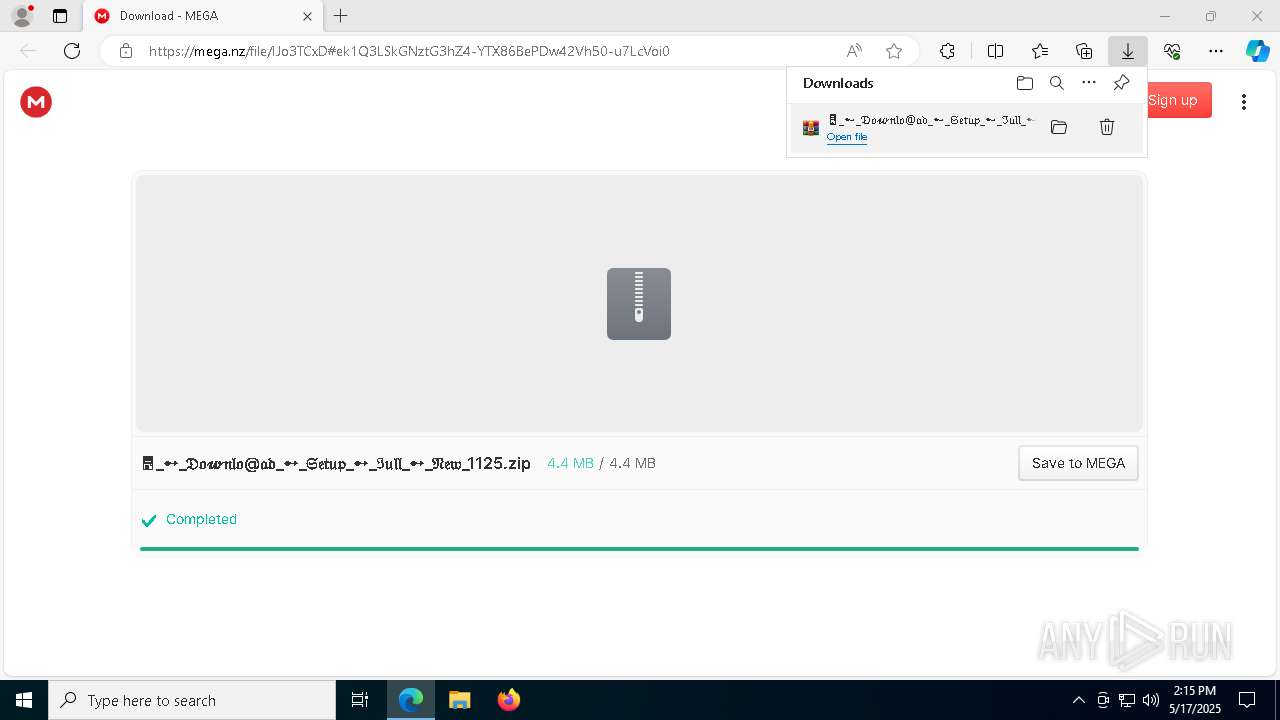
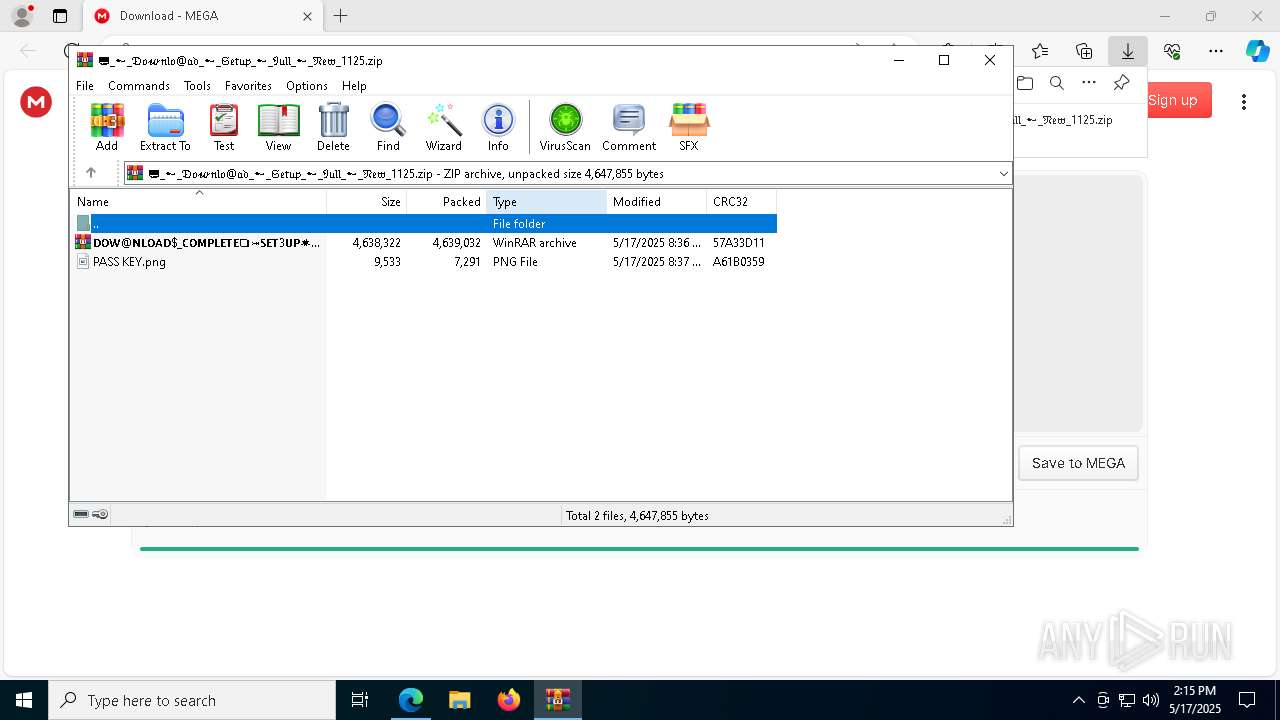
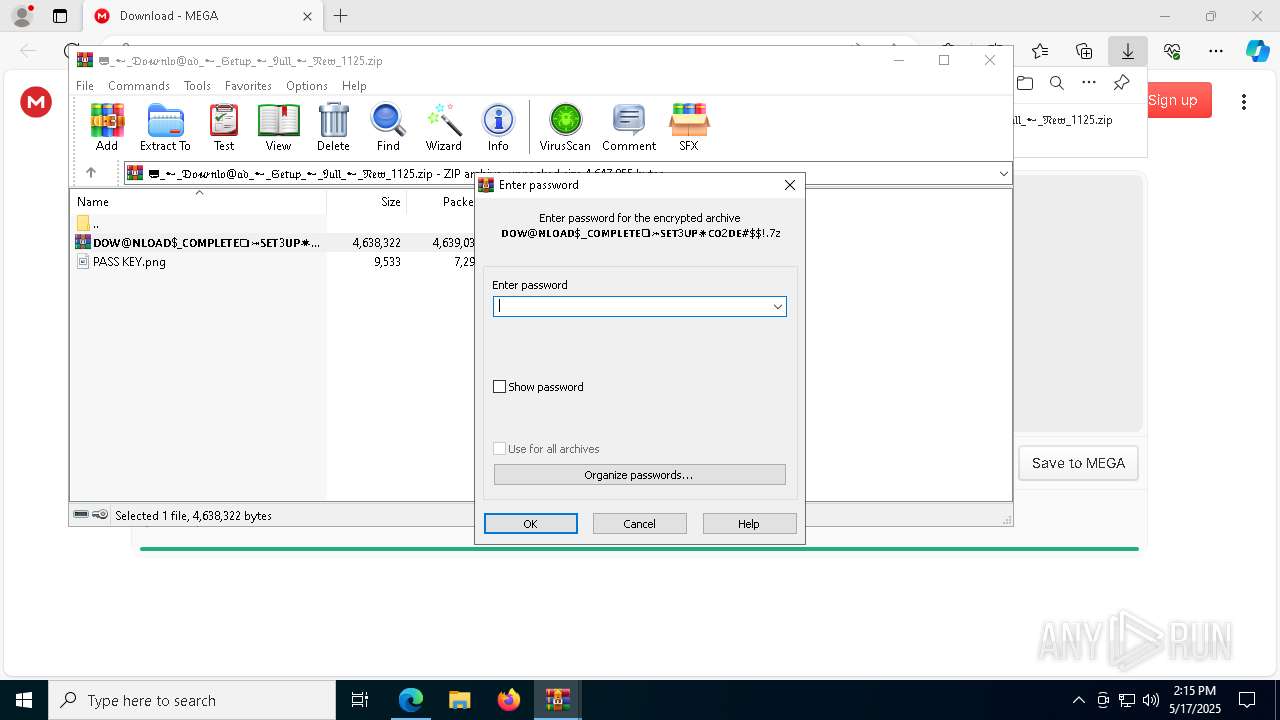
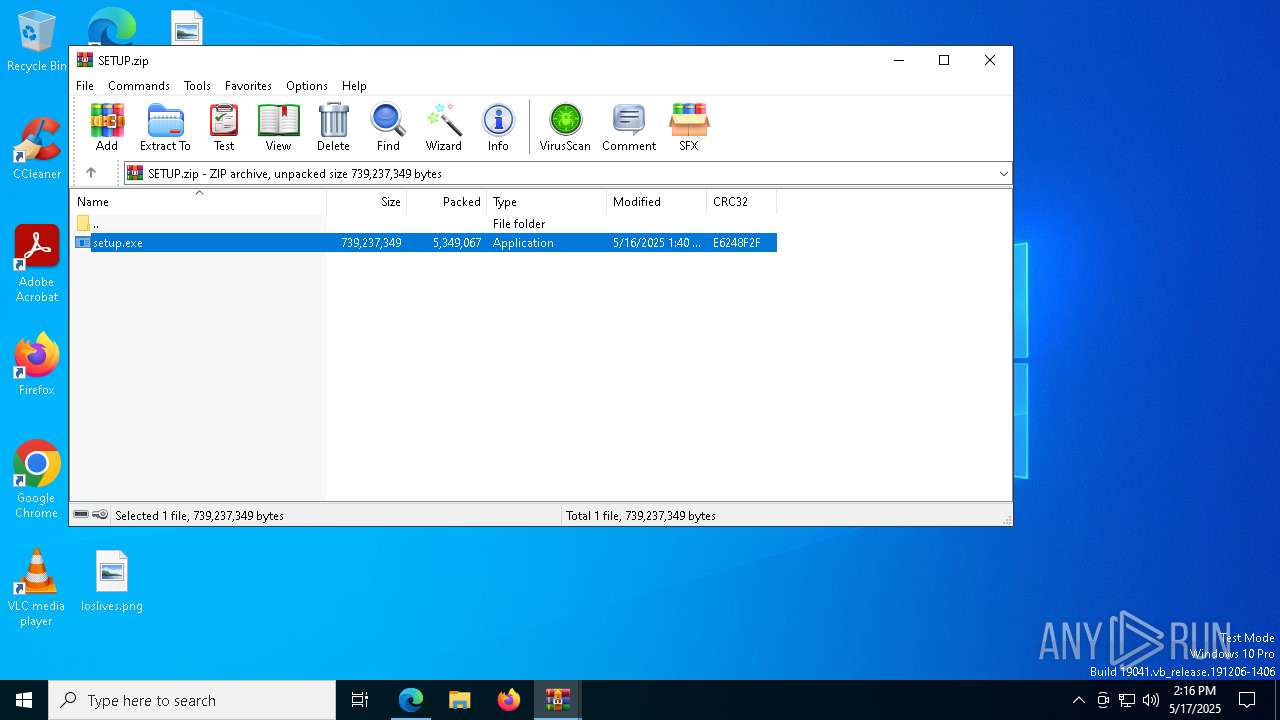
| URL: | https://mega.nz/file/IJo3TCxD#ek1Q3LSkGNztG3hZ4-YTX86BePDw42Vh50-u7LcVoi0 |
| Full analysis: | https://app.any.run/tasks/675041d5-407b-4d86-9f0f-387bb3d8d5a5 |
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | May 17, 2025, 14:15:29 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | F964FF85C0A7043DCDBF332D5FFA9FF3 |
| SHA1: | A056D0F372EFBA4643FC29EA5AE48F91D2FE6F48 |
| SHA256: | B962218C2EEE22145085DE66E7DA61BDEB26399B7B18CEBC74284D0BC2725836 |
| SSDEEP: | 3:N8X/idZke4Wtd9SSxCtSpA:2eZBbtd93CtaA |
MALICIOUS
Executing a file with an untrusted certificate
- setup.exe (PID: 1168)
- hjksfmp.exe (PID: 4756)
- DistriCompiler89.exe (PID: 6620)
- DistriCompiler89.exe (PID: 6252)
- DistriCompiler89.exe (PID: 7760)
- VirtuServer128.exe (PID: 7952)
- setup.exe (PID: 7428)
- hjksfwn.exe (PID: 7612)
- DistriCompiler89.exe (PID: 5528)
- DistriCompiler89.exe (PID: 6244)
- VirtuServer128.exe (PID: 7588)
- DistriCompiler89.exe (PID: 2268)
- setup.exe (PID: 8060)
Actions looks like stealing of personal data
- setup.exe (PID: 1168)
Steals credentials from Web Browsers
- setup.exe (PID: 1168)
Known privilege escalation attack
- dllhost.exe (PID: 4112)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 516)
- WinRAR.exe (PID: 7916)
- WinRAR.exe (PID: 8124)
- hjksfmp.exe (PID: 4756)
- VirtuServer128.exe (PID: 7952)
- MicrosoftEdgeUpdate.exe (PID: 1240)
Application launched itself
- WinRAR.exe (PID: 8124)
- WinRAR.exe (PID: 516)
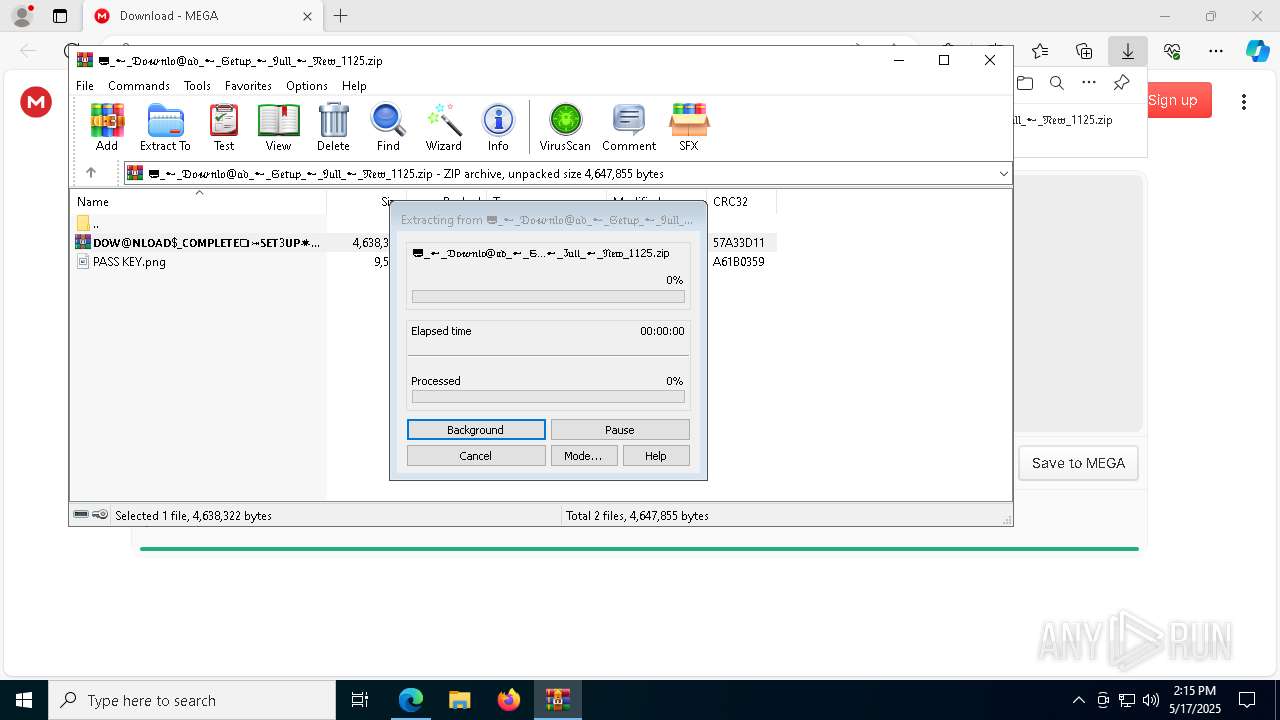
Executable content was dropped or overwritten
- setup.exe (PID: 1168)
- hjksfmp.exe (PID: 4756)
- DistriCompiler89.exe (PID: 7760)
- DistriCompiler89.exe (PID: 6620)
- DistriCompiler89.exe (PID: 6252)
- VirtuServer128.exe (PID: 7952)
- MicrosoftEdgeWebview2Setup.exe (PID: 5036)
- hjksfwn.exe (PID: 7612)
- MicrosoftEdgeWebview2Setup.exe (PID: 7992)
- setup.exe (PID: 7428)
Process drops legitimate windows executable
- setup.exe (PID: 1168)
- VirtuServer128.exe (PID: 7952)
- MicrosoftEdgeWebview2Setup.exe (PID: 5036)
- MicrosoftEdgeUpdate.exe (PID: 1240)
- MicrosoftEdgeWebview2Setup.exe (PID: 7992)
- MicrosoftEdgeUpdate.exe (PID: 7832)
- setup.exe (PID: 7428)
The process drops C-runtime libraries
- setup.exe (PID: 1168)
- setup.exe (PID: 7428)
Potential Corporate Privacy Violation
- setup.exe (PID: 1168)
- setup.exe (PID: 7428)
Drops 7-zip archiver for unpacking
- DistriCompiler89.exe (PID: 6620)
Starts itself from another location
- DistriCompiler89.exe (PID: 7760)
- DistriCompiler89.exe (PID: 6244)
There is functionality for taking screenshot (YARA)
- DistriCompiler89.exe (PID: 6620)
- DistriCompiler89.exe (PID: 6252)
- DistriCompiler89.exe (PID: 2268)
Starts process via Powershell
- powershell.exe (PID: 4776)
- powershell.exe (PID: 7816)
Connects to unusual port
- VirtuServer128.exe (PID: 7952)
- VirtuServer128.exe (PID: 7588)
Starts POWERSHELL.EXE for commands execution
- VirtuServer128.exe (PID: 7952)
- VirtuServer128.exe (PID: 7588)
Starts a Microsoft application from unusual location
- MicrosoftEdgeUpdate.exe (PID: 1240)
- MicrosoftEdgeUpdate.exe (PID: 7832)
Disables SEHOP
- MicrosoftEdgeUpdate.exe (PID: 1240)
INFO
Checks supported languages
- identity_helper.exe (PID: 728)
- setup.exe (PID: 1168)
- elevation_service.exe (PID: 2108)
- hjksfmp.exe (PID: 4756)
- DistriCompiler89.exe (PID: 6620)
- 7za.exe (PID: 5744)
- DistriCompiler89.exe (PID: 6252)
- DistriCompiler89.exe (PID: 7760)
- 7za.exe (PID: 7976)
- VirtuServer128.exe (PID: 7952)
- MicrosoftEdgeWebview2Setup.exe (PID: 5036)
- MicrosoftEdgeUpdate.exe (PID: 1240)
Reads the computer name
- identity_helper.exe (PID: 728)
- elevation_service.exe (PID: 2108)
- setup.exe (PID: 1168)
- hjksfmp.exe (PID: 4756)
- DistriCompiler89.exe (PID: 7760)
- DistriCompiler89.exe (PID: 6620)
- 7za.exe (PID: 5744)
- DistriCompiler89.exe (PID: 6252)
- VirtuServer128.exe (PID: 7952)
- MicrosoftEdgeUpdate.exe (PID: 1240)
- 7za.exe (PID: 7976)
Executes as Windows Service
- elevation_service.exe (PID: 2108)
- elevation_service.exe (PID: 7296)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6564)
Reads Environment values
- identity_helper.exe (PID: 728)
- MicrosoftEdgeUpdate.exe (PID: 1240)
Reads the machine GUID from the registry
- setup.exe (PID: 1168)
- 7za.exe (PID: 5744)
- VirtuServer128.exe (PID: 7952)
Creates files in the program directory
- DistriCompiler89.exe (PID: 6620)
- DistriCompiler89.exe (PID: 6252)
- VirtuServer128.exe (PID: 7952)
- DistriCompiler89.exe (PID: 7760)
- MicrosoftEdgeWebview2Setup.exe (PID: 5036)
Create files in a temporary directory
- DistriCompiler89.exe (PID: 6620)
- DistriCompiler89.exe (PID: 6252)
Reads the software policy settings
- slui.exe (PID: 6404)
- VirtuServer128.exe (PID: 7952)
- MicrosoftEdgeUpdate.exe (PID: 1240)
- slui.exe (PID: 7704)
- wermgr.exe (PID: 7552)
Application launched itself
- msedge.exe (PID: 6564)
The sample compiled with english language support
- DistriCompiler89.exe (PID: 6620)
- setup.exe (PID: 1168)
- DistriCompiler89.exe (PID: 6252)
- VirtuServer128.exe (PID: 7952)
- MicrosoftEdgeWebview2Setup.exe (PID: 5036)
- MicrosoftEdgeUpdate.exe (PID: 1240)
- MicrosoftEdgeWebview2Setup.exe (PID: 7992)
- MicrosoftEdgeUpdate.exe (PID: 7832)
- setup.exe (PID: 7428)
Checks transactions between databases Windows and Oracle
- 7za.exe (PID: 5744)
Reads security settings of Internet Explorer
- dllhost.exe (PID: 4112)
Process checks computer location settings
- hjksfmp.exe (PID: 4756)
- MicrosoftEdgeUpdate.exe (PID: 1240)
Checks proxy server information
- VirtuServer128.exe (PID: 7952)
- MicrosoftEdgeUpdate.exe (PID: 1240)
- slui.exe (PID: 7704)
- wermgr.exe (PID: 7552)
Creates files or folders in the user directory
- VirtuServer128.exe (PID: 7952)
- wermgr.exe (PID: 7552)
Manual execution by a user
- setup.exe (PID: 7428)
- setup.exe (PID: 8060)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
227
Monitored processes
92
Malicious processes
16
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
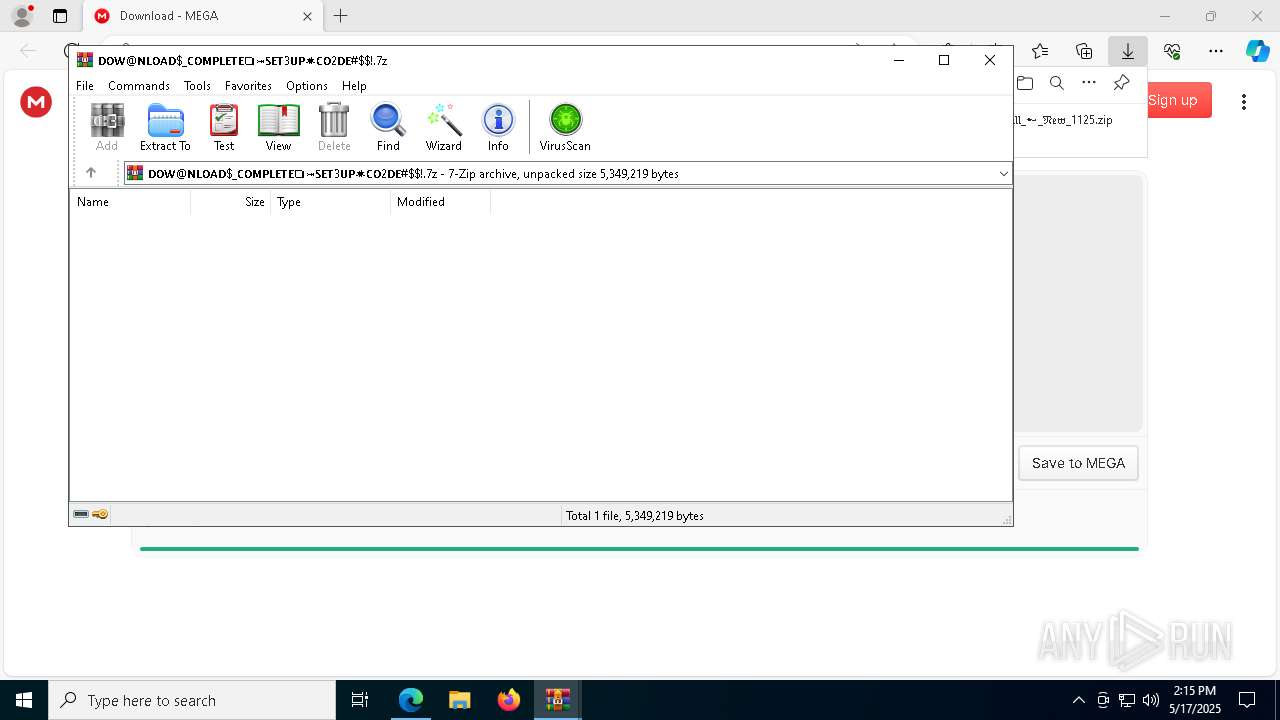
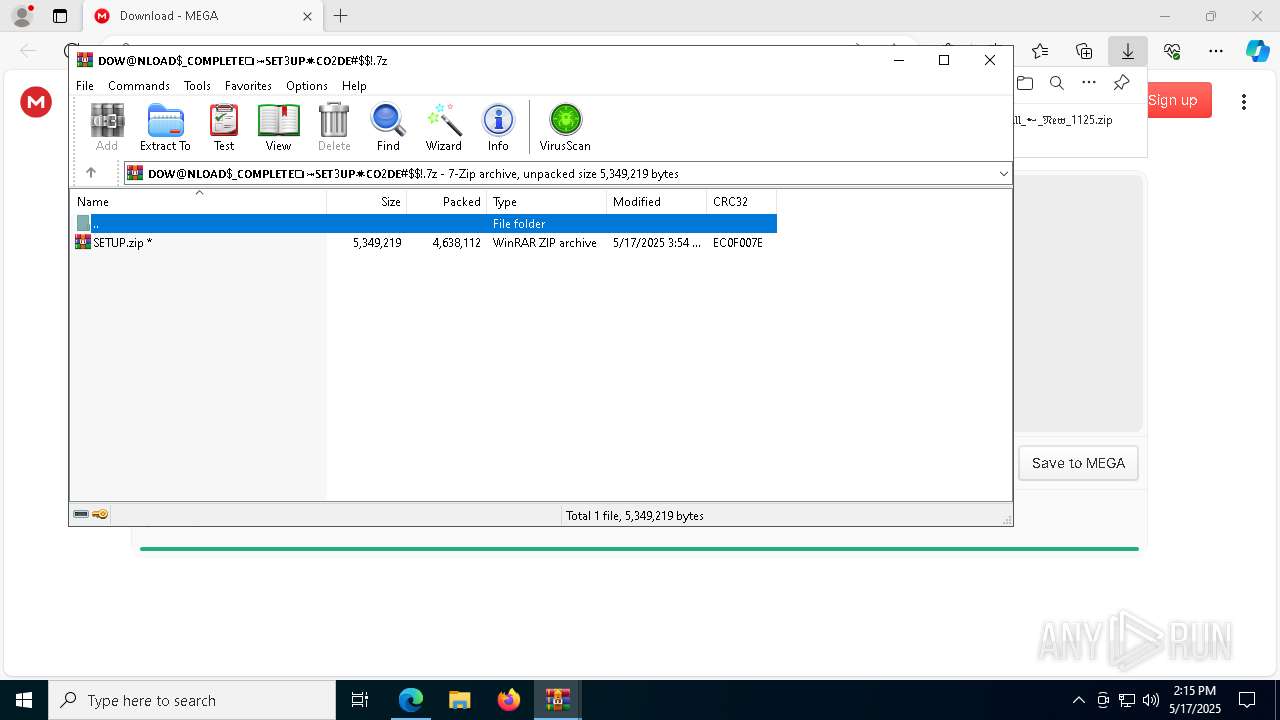
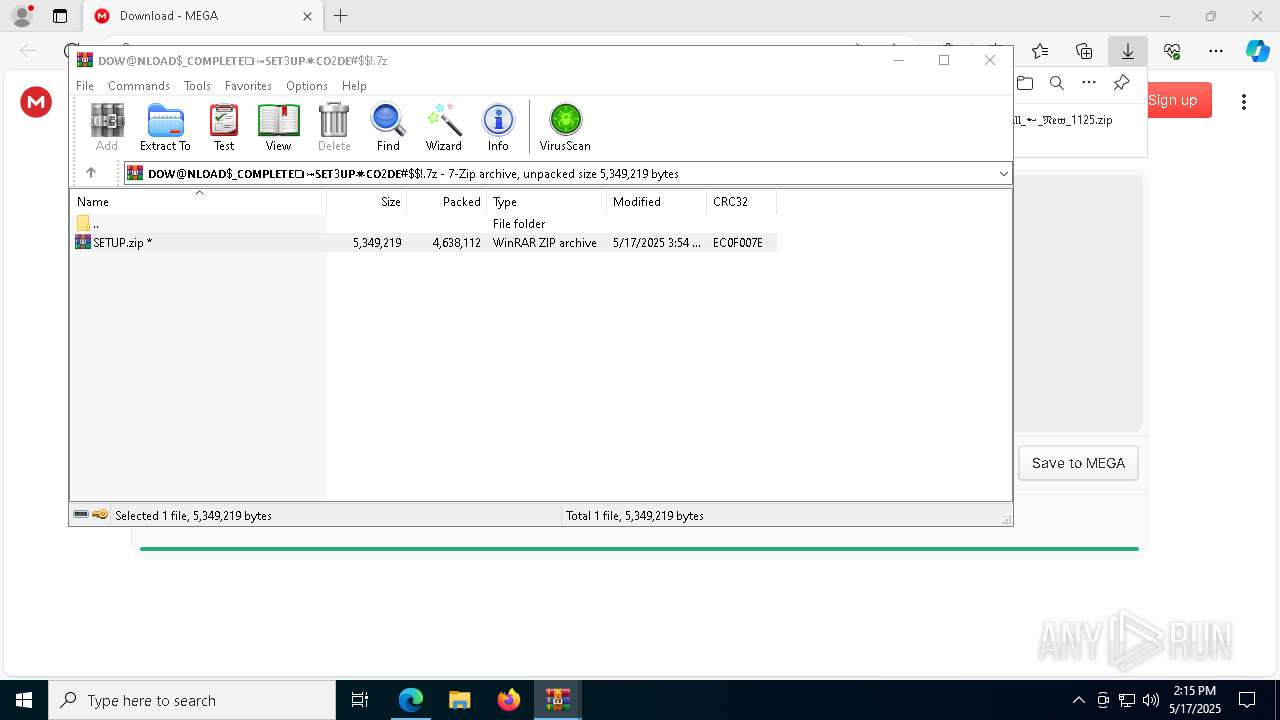
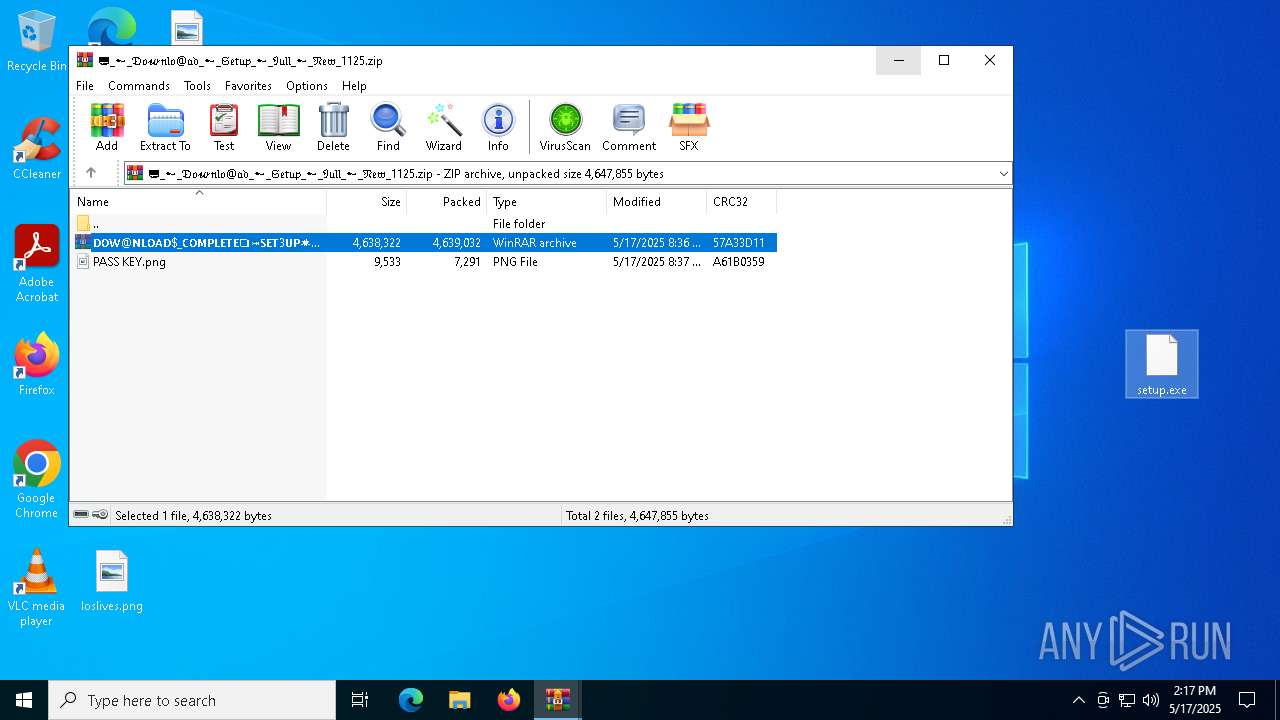
| 516 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIa8124.15967\𝗗𝗢𝗪@𝗡𝗟𝗢𝗔𝗗$_𝗖𝗢𝗠𝗣𝗟𝗘𝗧𝗘❏⤖𝗦𝗘𝗧3𝗨𝗣✷𝗖𝗢2𝗗𝗘#$!.7z | C:\Program Files\WinRAR\WinRAR.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 728 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6396 --field-trial-handle=2488,i,12197761361330860526,11493196911251114728,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 780 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x294,0x298,0x29c,0x290,0x2a4,0x7ffc881e5fd8,0x7ffc881e5fe4,0x7ffc881e5ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | — | setup.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 1 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1128 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --no-appcompat-clear --mojo-platform-channel-handle=5760 --field-trial-handle=2488,i,12197761361330860526,11493196911251114728,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
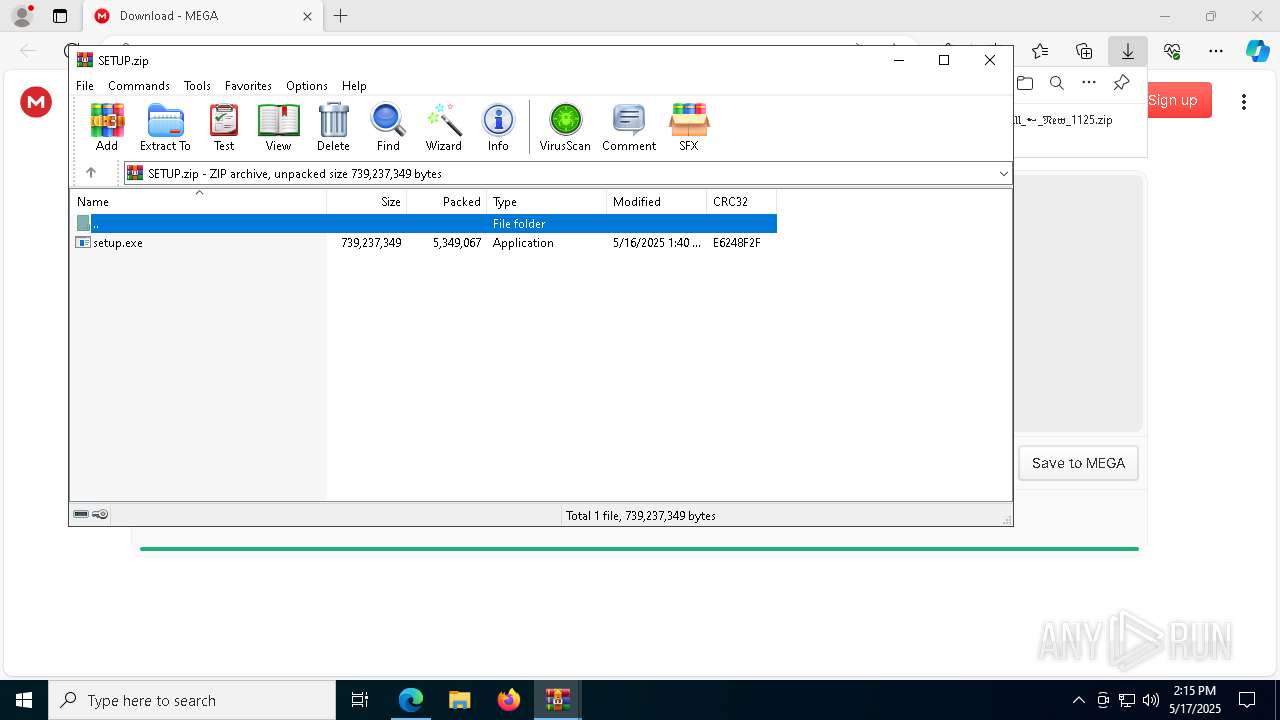
| 1168 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa7916.16822\setup.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa7916.16822\setup.exe | WinRAR.exe | ||||||||||||
User: admin Company: XnView, http://www.xnview.com Integrity Level: MEDIUM Description: XnView Classic for Windows Exit code: 0 Version: 2.52.0 Modules
| |||||||||||||||
| 1240 | "C:\Program Files (x86)\Microsoft\Temp\EU8DC1.tmp\MicrosoftEdgeUpdate.exe" /silent /install "appguid={F3017226-FE2A-4295-8BDF-00C3A9A7E4C5}&appname=Microsoft%20Edge%20Webview2%20Runtime&needsadmin=prefers" | C:\Program Files (x86)\Microsoft\Temp\EU8DC1.tmp\MicrosoftEdgeUpdate.exe | MicrosoftEdgeWebview2Setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Update Exit code: 2147747592 Version: 1.3.195.25 Modules
| |||||||||||||||
| 2108 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\elevation_service.exe" | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\elevation_service.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2236 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 1 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2268 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=29 --mojo-platform-channel-handle=6892 --field-trial-handle=2488,i,12197761361330860526,11493196911251114728,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
30 809
Read events
30 633
Write events
171
Delete events
5
Modification events
| (PID) Process: | (2616) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2616) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2616) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2616) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2616) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2616) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (6564) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6564) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6564) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6564) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
326
Suspicious files
166
Text files
65
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6564 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10c3fe.TMP | — | |
MD5:— | SHA256:— | |||
| 6564 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6564 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10c3ee.TMP | — | |
MD5:— | SHA256:— | |||
| 6564 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10c40d.TMP | — | |
MD5:— | SHA256:— | |||
| 6564 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6564 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6564 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10c40d.TMP | — | |
MD5:— | SHA256:— | |||
| 6564 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10c41d.TMP | — | |
MD5:— | SHA256:— | |||
| 6564 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6564 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
113
DNS requests
69
Threats
26
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.29:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.29:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6148 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1168 | setup.exe | GET | 200 | 172.67.221.174:80 | http://h4.tattlererun.life/sh.ext.bin | unknown | — | — | unknown |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6148 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1168 | setup.exe | GET | 200 | 172.67.221.174:80 | http://h4.tattlererun.life/shark.bin | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.29:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.216.77.29:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
2104 | svchost.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
7324 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7324 | msedge.exe | 31.216.144.5:443 | mega.nz | Datacenter Luxembourg S.A. | LU | whitelisted |
7324 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
mega.nz |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
7324 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
7324 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
7324 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
7324 | msedge.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
7324 | msedge.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
7324 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
7324 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
7324 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
7324 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |