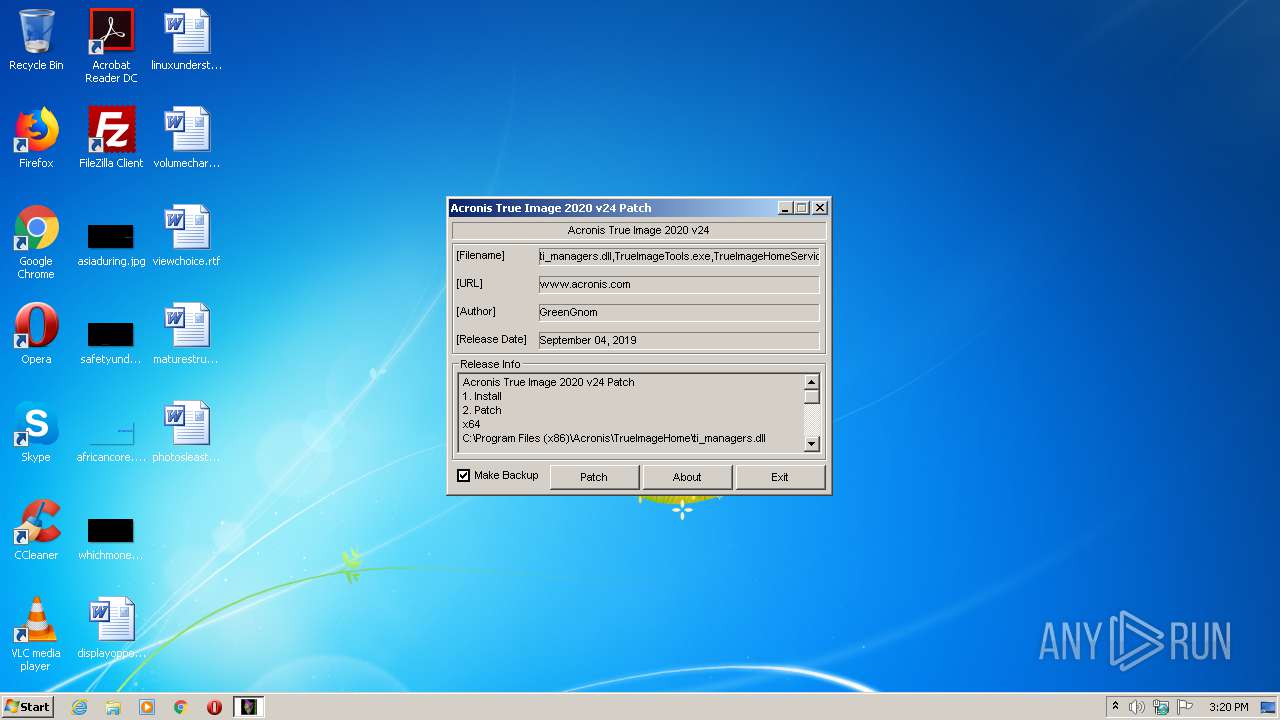
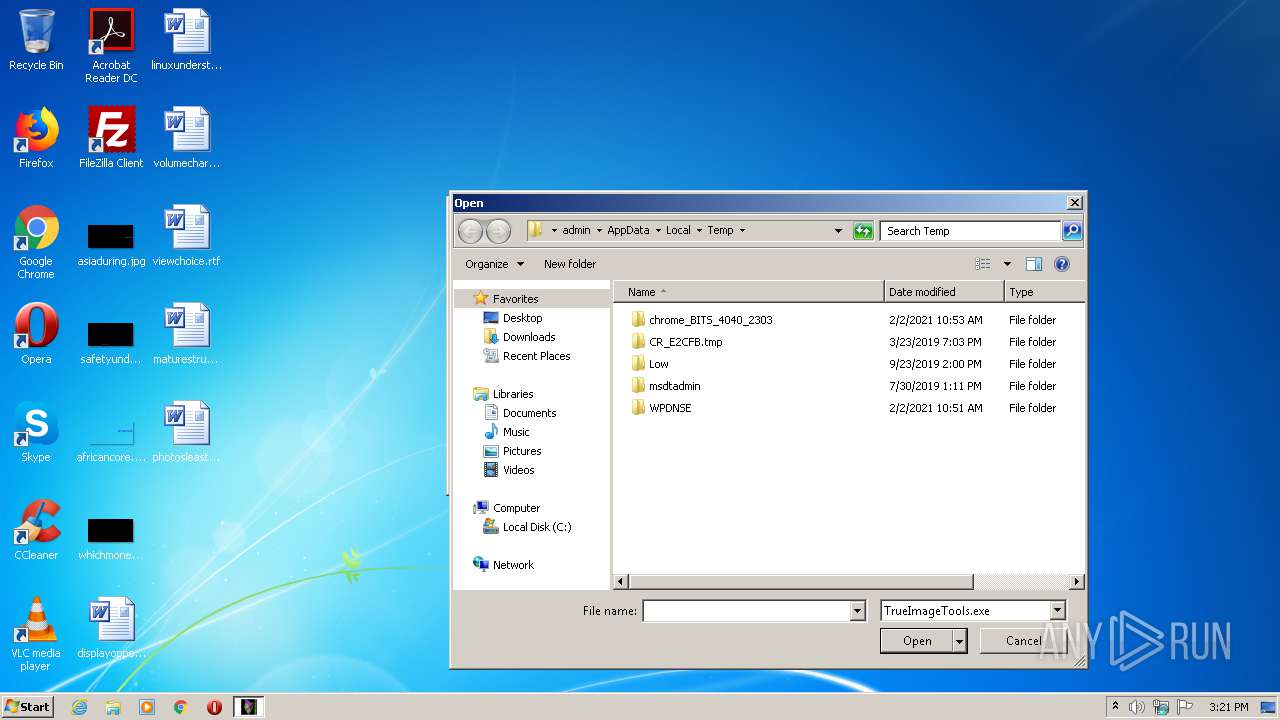
| File name: | Acronis True Image 2020 v24 Patch.exe |
| Full analysis: | https://app.any.run/tasks/eb70e7cc-3b28-43a4-ac27-2d221ee8daf9 |
| Verdict: | Malicious activity |
| Analysis date: | June 28, 2021, 14:20:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 04A995DE3FA34A02F4C67B8BA9948D57 |
| SHA1: | 4516107E8F2FB76E8953F50408D4974EB07CA509 |
| SHA256: | B9612E5428D48C7A523059D60C982087D258A1B21077474C0DBF6F1EBEE91397 |
| SSDEEP: | 6144:e3YKqFJF2DxwWoPPHy5LbPM7eIEPbQbs/DobI:efqPWwWgy+Icbyos |
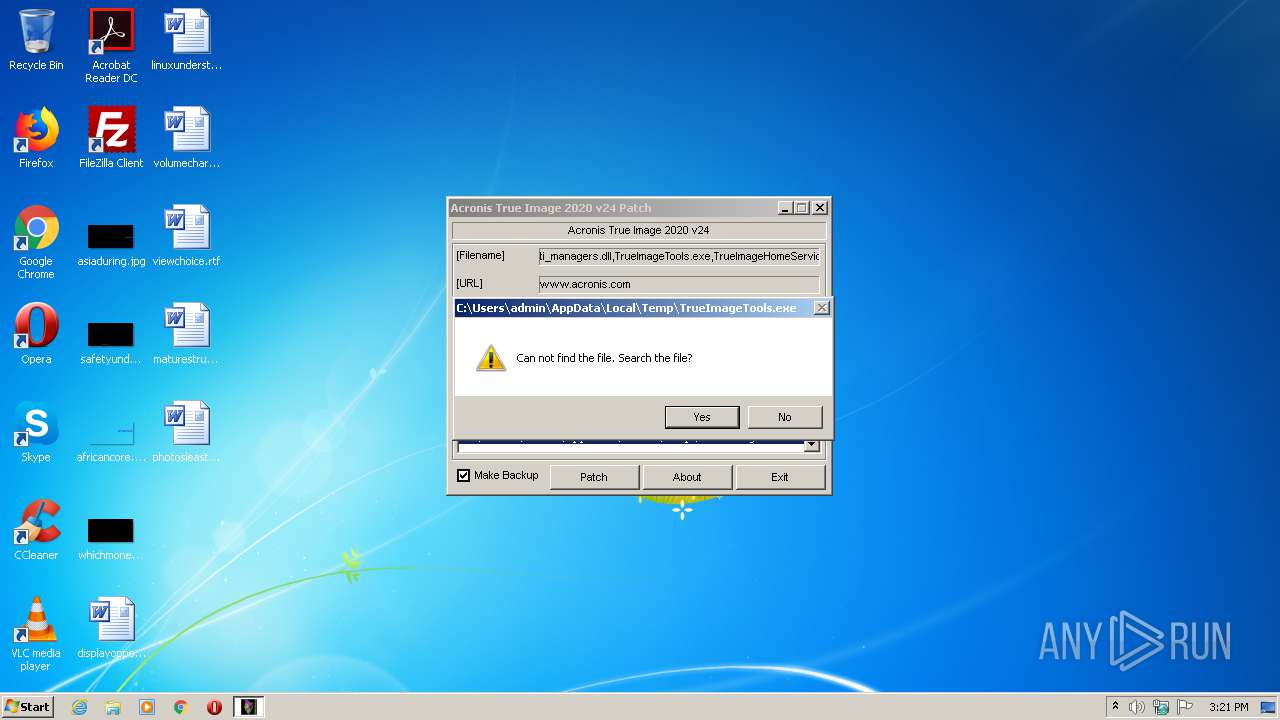
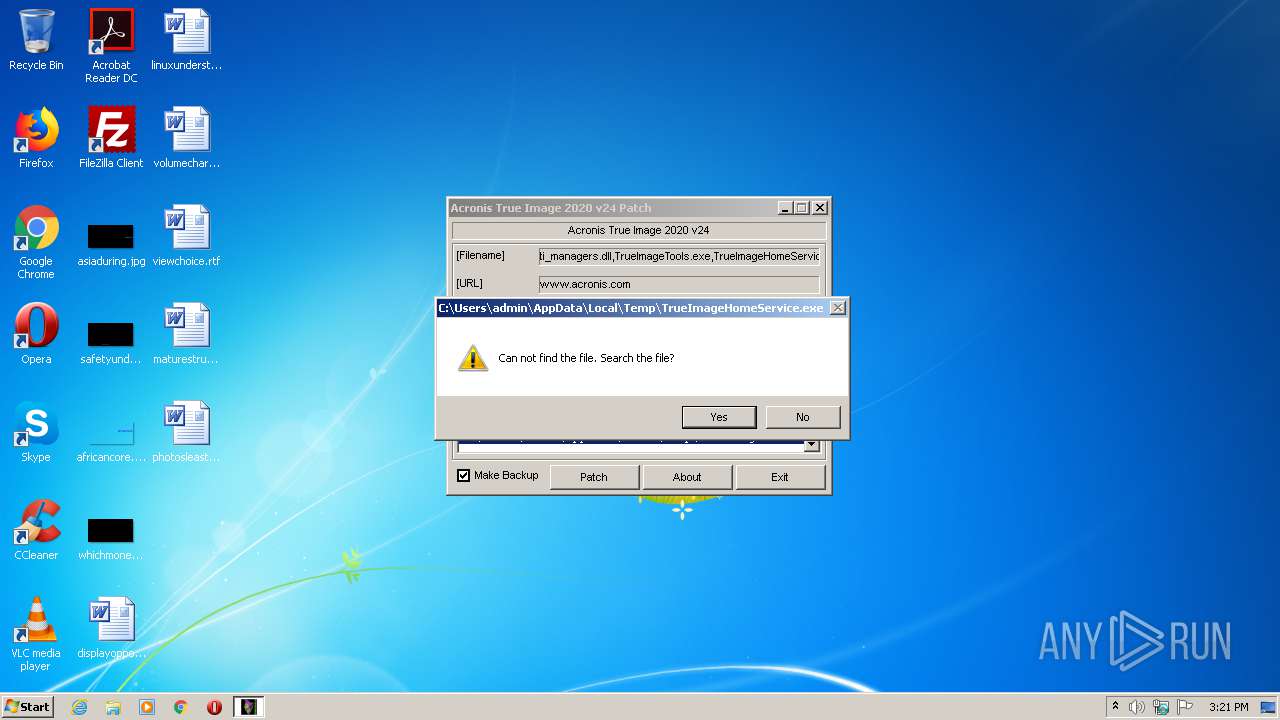
MALICIOUS
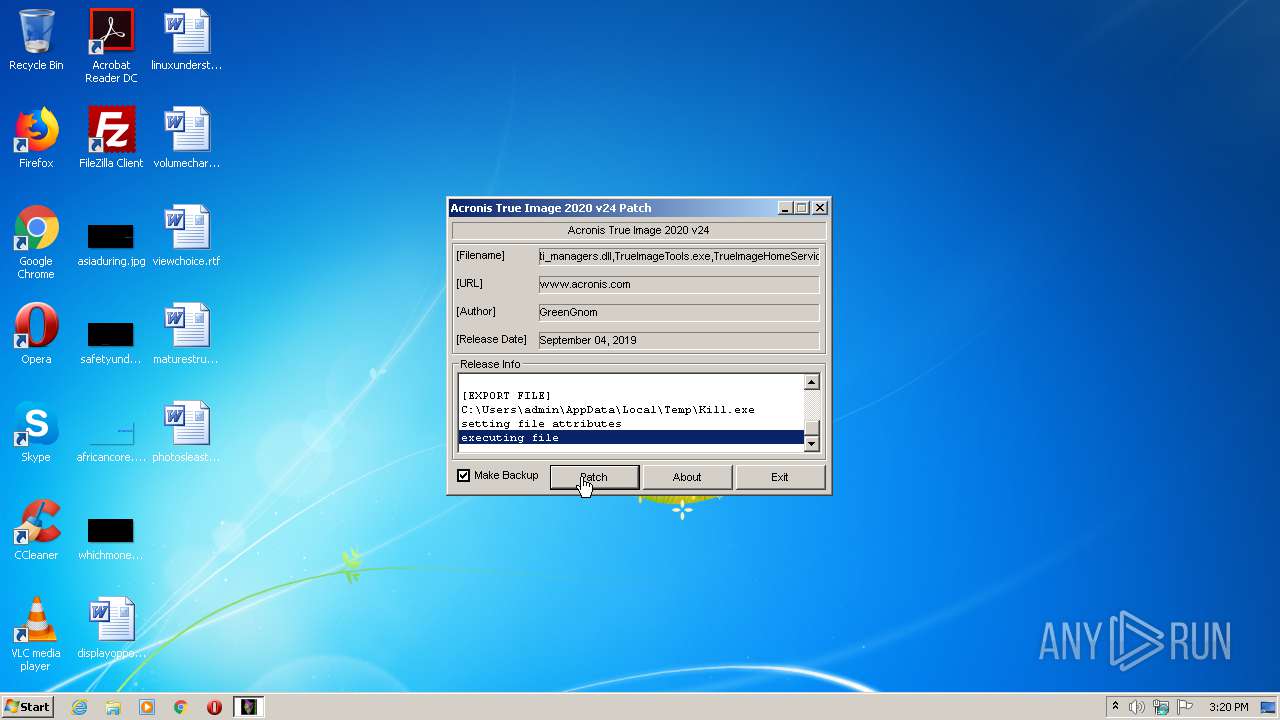
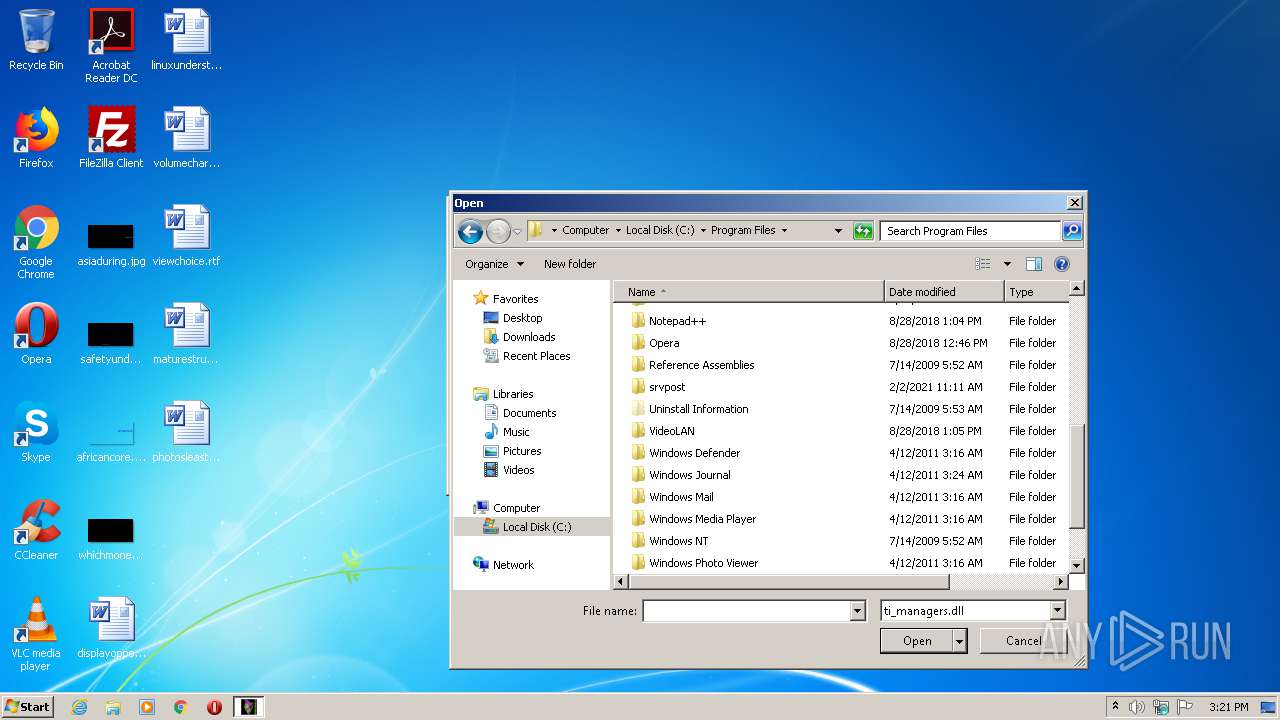
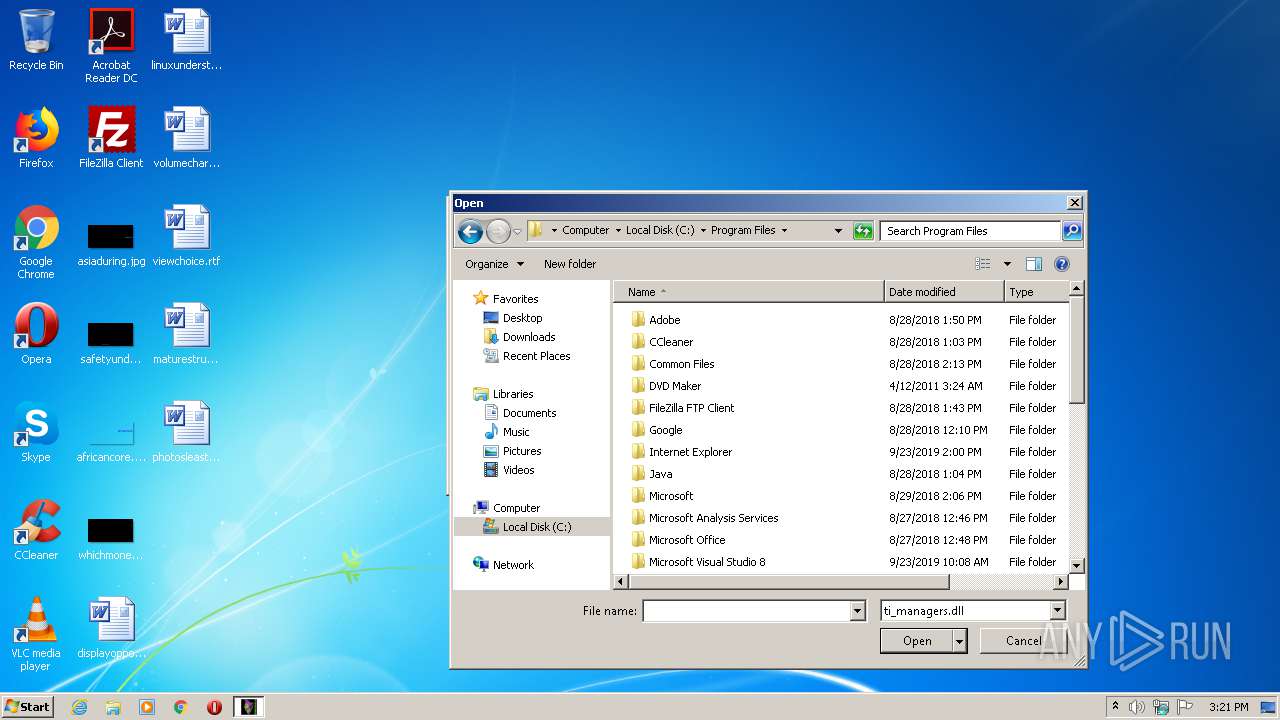
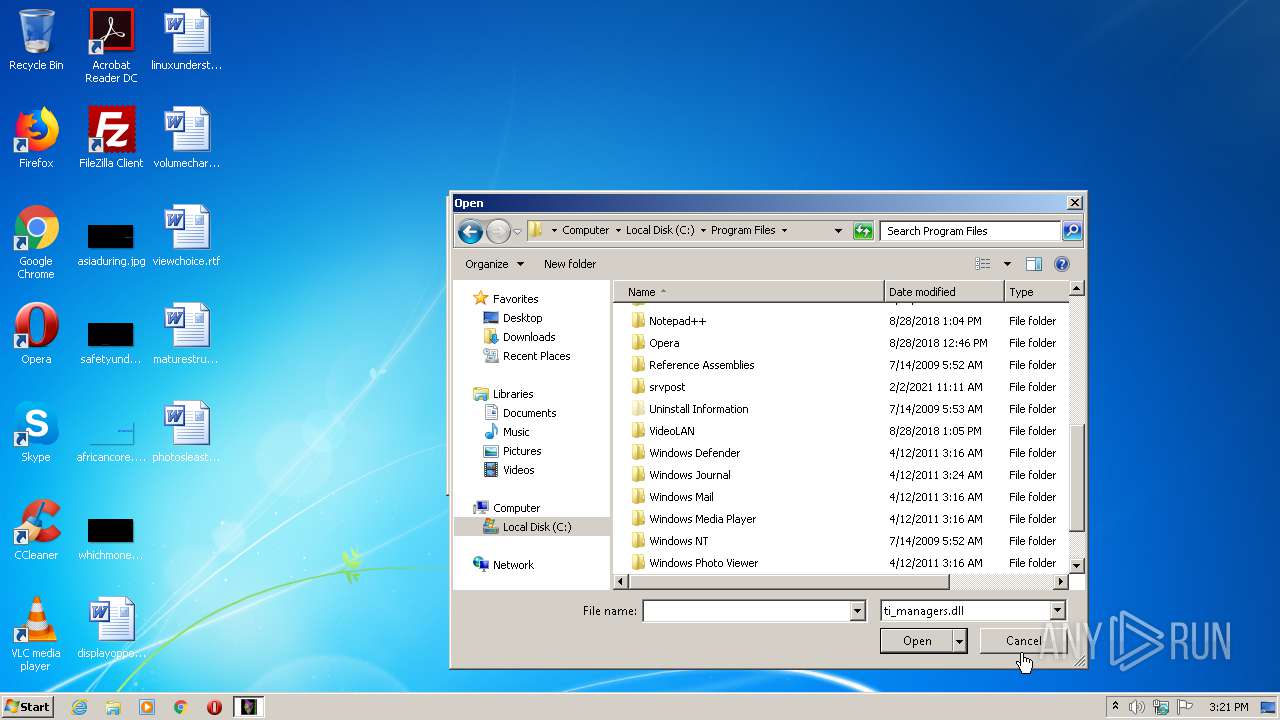
Loads dropped or rewritten executable
- Acronis True Image 2020 v24 Patch.exe (PID: 3660)
Drops executable file immediately after starts
- Acronis True Image 2020 v24 Patch.exe (PID: 3660)
Starts NET.EXE for service management
- cmd.exe (PID: 3596)
Application was dropped or rewritten from another process
- Kill.exe (PID: 1976)
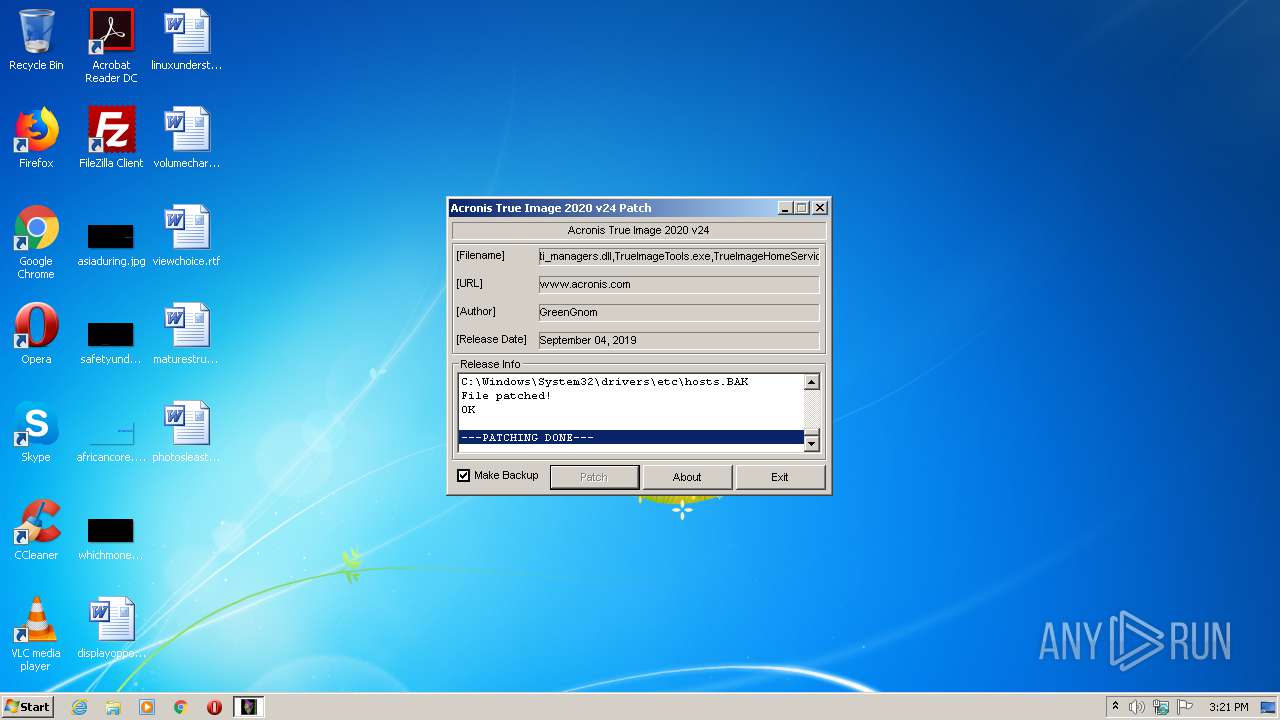
Writes to the hosts file
- Acronis True Image 2020 v24 Patch.exe (PID: 3660)
SUSPICIOUS
Executable content was dropped or overwritten
- Acronis True Image 2020 v24 Patch.exe (PID: 3660)
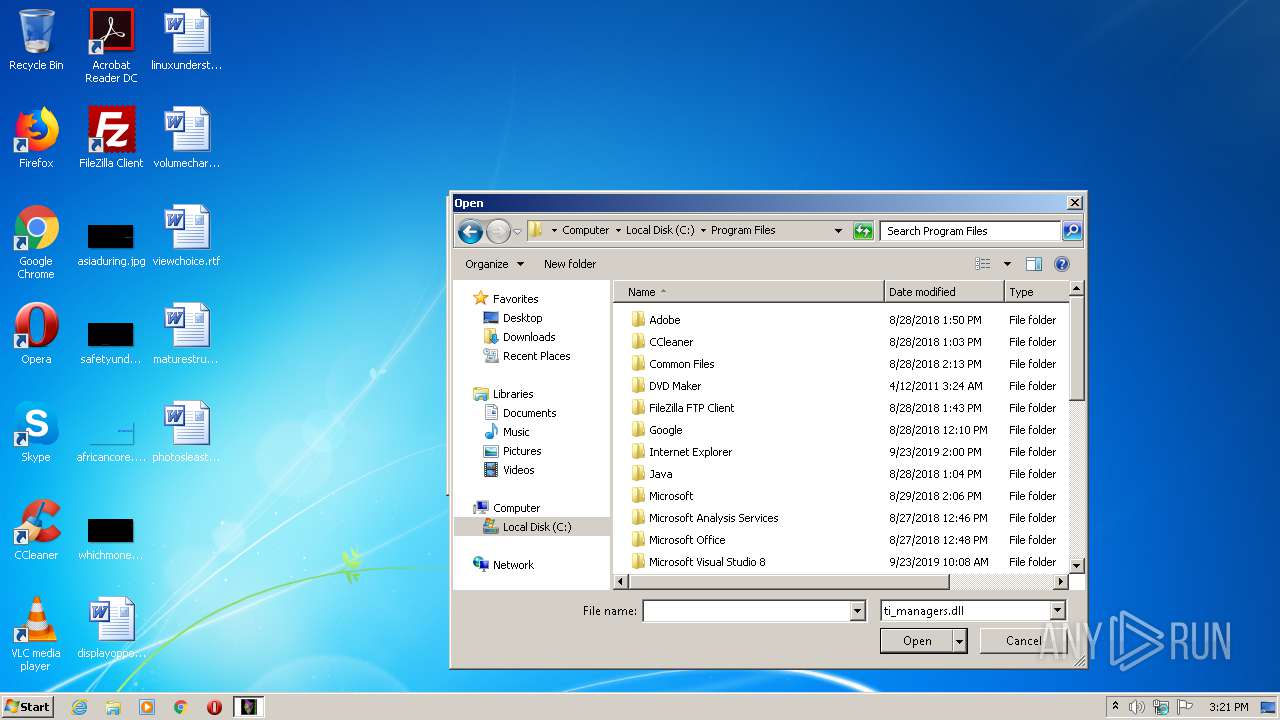
Creates files in the Windows directory
- Acronis True Image 2020 v24 Patch.exe (PID: 3660)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 3596)
Starts CMD.EXE for commands execution
- Kill.exe (PID: 1976)
Creates files in the driver directory
- Acronis True Image 2020 v24 Patch.exe (PID: 3660)
INFO
Reads the hosts file
- Acronis True Image 2020 v24 Patch.exe (PID: 3660)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5 |
| ImageVersion: | - |
| OSVersion: | 5 |
| EntryPoint: | 0x102b |
| UninitializedDataSize: | - |
| InitializedDataSize: | 221696 |
| CodeSize: | 512 |
| LinkerVersion: | 10 |
| PEType: | PE32 |
| TimeStamp: | 2012:12:21 21:59:46+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 21-Dec-2012 20:59:46 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 21-Dec-2012 20:59:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000001F6 | 0x00000200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.06408 |
.rdata | 0x00002000 | 0x000001D8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.27064 |
.data | 0x00003000 | 0x00000034 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.568988 |
.rsrc | 0x00004000 | 0x00035A18 | 0x00035C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.88135 |
.reloc | 0x0003A000 | 0x00000052 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.736046 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.85663 | 898 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 3.43672 | 744 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 5.61072 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 5.83052 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 5.53294 | 3752 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 5.44357 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 5.21743 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 5.00142 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
9 | 7.96694 | 60888 | Latin 1 / Western European | UNKNOWN | RT_ICON |
500 | 2.84132 | 132 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
Imports
kernel32.dll |
Total processes
63
Monitored processes
23
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 864 | net stop afcdpsrv | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1340 | net stop mobile_backup_server | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1704 | net stop syncagentsrv | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1824 | taskkill /F /IM syncagentsrv.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1844 | taskkill /F /IM TrueImageMonitor.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1900 | net stop AcronisActiveProtectionService | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1976 | "C:\Users\admin\AppData\Local\Temp\Kill.exe" start "" "C:\Users\admin\AppData\Local\Temp\Kill.exe" | C:\Users\admin\AppData\Local\Temp\Kill.exe | — | Acronis True Image 2020 v24 Patch.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 128 Modules
| |||||||||||||||
| 2496 | taskkill /F /IM TibMounterMonitor.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2500 | C:\Windows\system32\net1 stop syncagentsrv | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2512 | C:\Windows\system32\net1 stop AcronisActiveProtectionService | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
891
Read events
730
Write events
158
Delete events
3
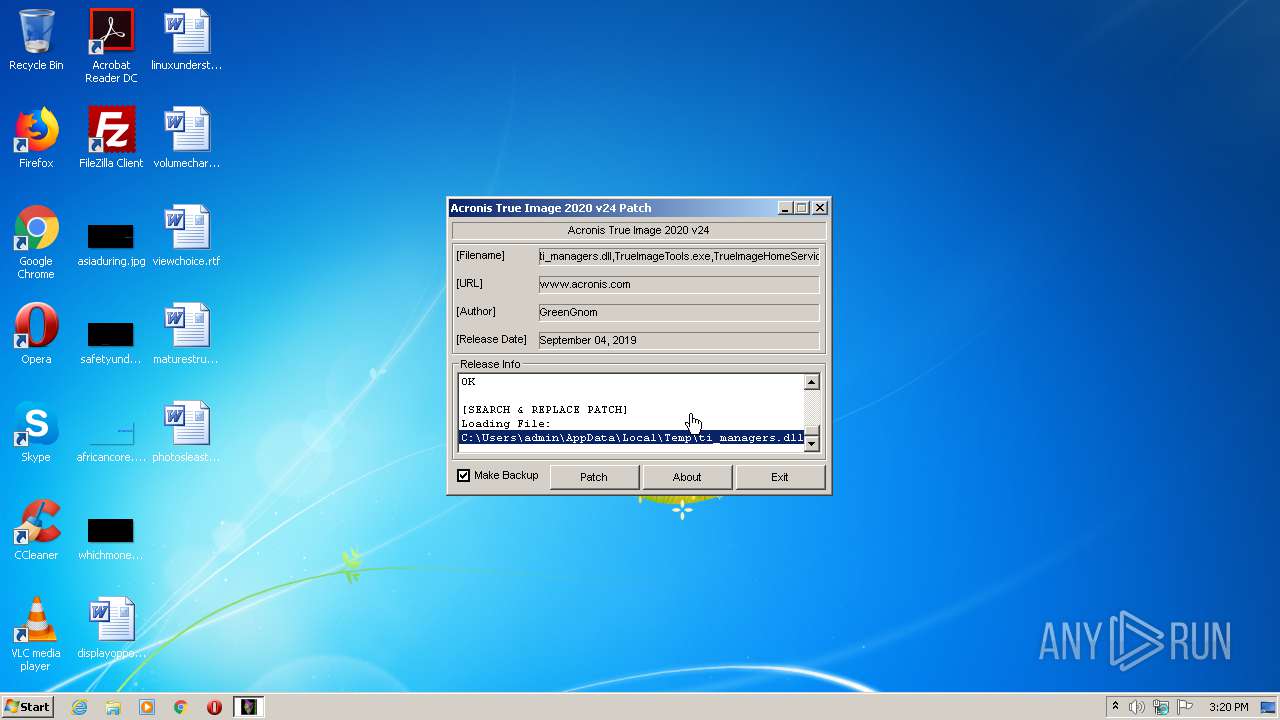
Modification events
| (PID) Process: | (2712) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Acronis\TrueImage |
| Operation: | write | Name: | standard |
Value: 19 98 19 25 99 98108 1120102 19 6 23 18 6 98 22120 19 25 1 30 30 27 30 23120 20 22 6 30 25 99 19 19120 13 0 30 18 16 20 23 4120 30 97 4 22 15 4 2 18120 31 0 19 3 27 2 5 2120 1 7 6109108102 0109 | |||
| (PID) Process: | (2712) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Acronis\TrueImageHome\Settings |
| Operation: | write | Name: | ActivatoionBlob |
Value: { "Error" : 0, "Status" : "", "Value" : "1234", "Version" : 1} | |||
| (PID) Process: | (2712) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Acronis\TrueImageHome\Settings |
| Operation: | write | Name: | AutocheckUpdates |
Value: 0 | |||
| (PID) Process: | (2712) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Acronis\TrueImageHome\Settings |
| Operation: | write | Name: | CEP |
Value: 0 | |||
| (PID) Process: | (3660) Acronis True Image 2020 v24 Patch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3660) Acronis True Image 2020 v24 Patch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3932) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Acronis\TrueImage |
| Operation: | write | Name: | standard |
Value: 19 98 19 25 99 98108 1120102 19 6 23 18 6 98 22120 19 25 1 30 30 27 30 23120 20 22 6 30 25 99 19 19120 13 0 30 18 16 20 23 4120 30 97 4 22 15 4 2 18120 31 0 19 3 27 2 5 2120 1 7 6109108102 0109 | |||
| (PID) Process: | (3932) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Acronis\TrueImageHome\Settings |
| Operation: | write | Name: | ActivatoionBlob |
Value: { "Error" : 0, "Status" : "", "Value" : "1234", "Version" : 1} | |||
| (PID) Process: | (3932) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Acronis\TrueImageHome\Settings |
| Operation: | write | Name: | AutocheckUpdates |
Value: 0 | |||
| (PID) Process: | (3932) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Acronis\TrueImageHome\Settings |
| Operation: | write | Name: | CEP |
Value: 0 | |||
Executable files
2
Suspicious files
0
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
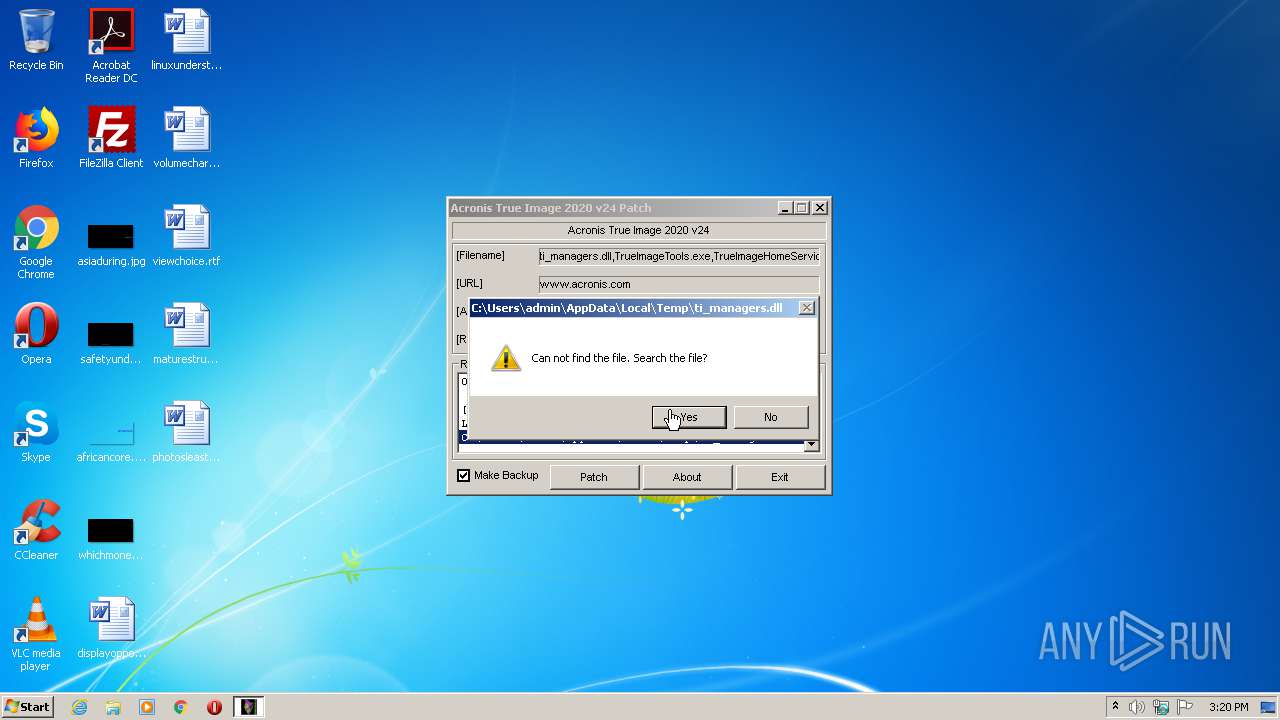
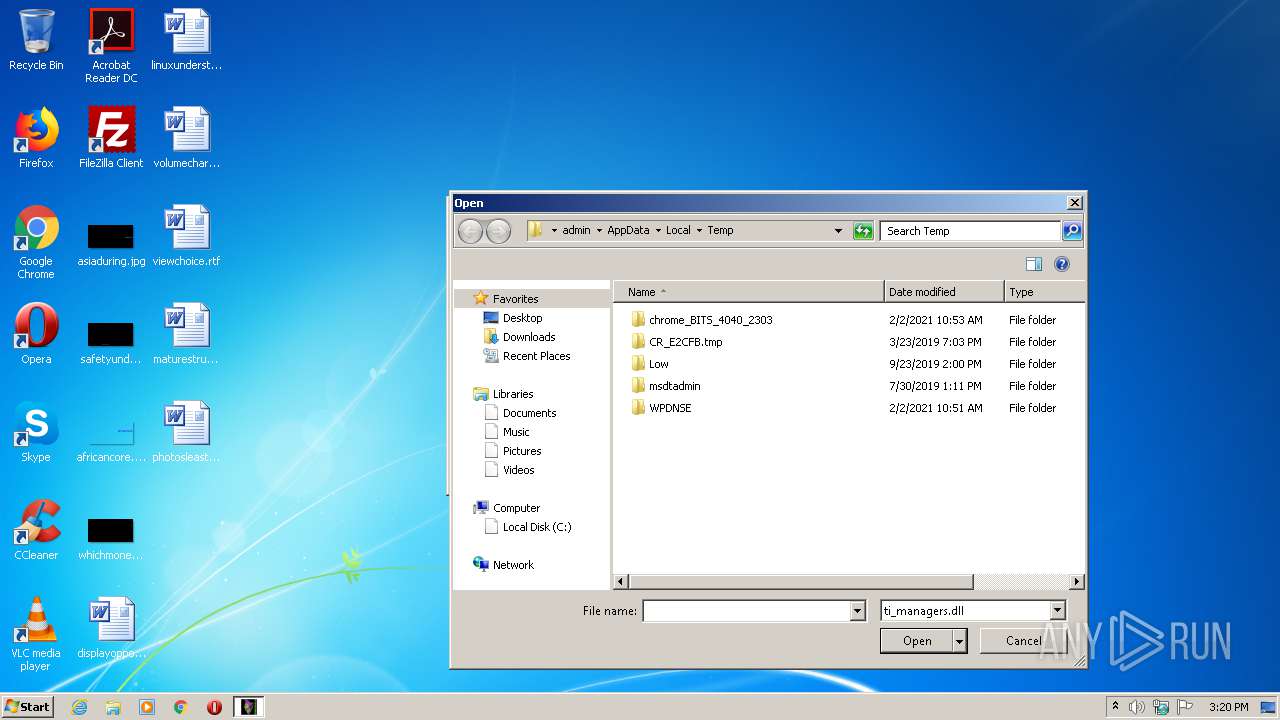
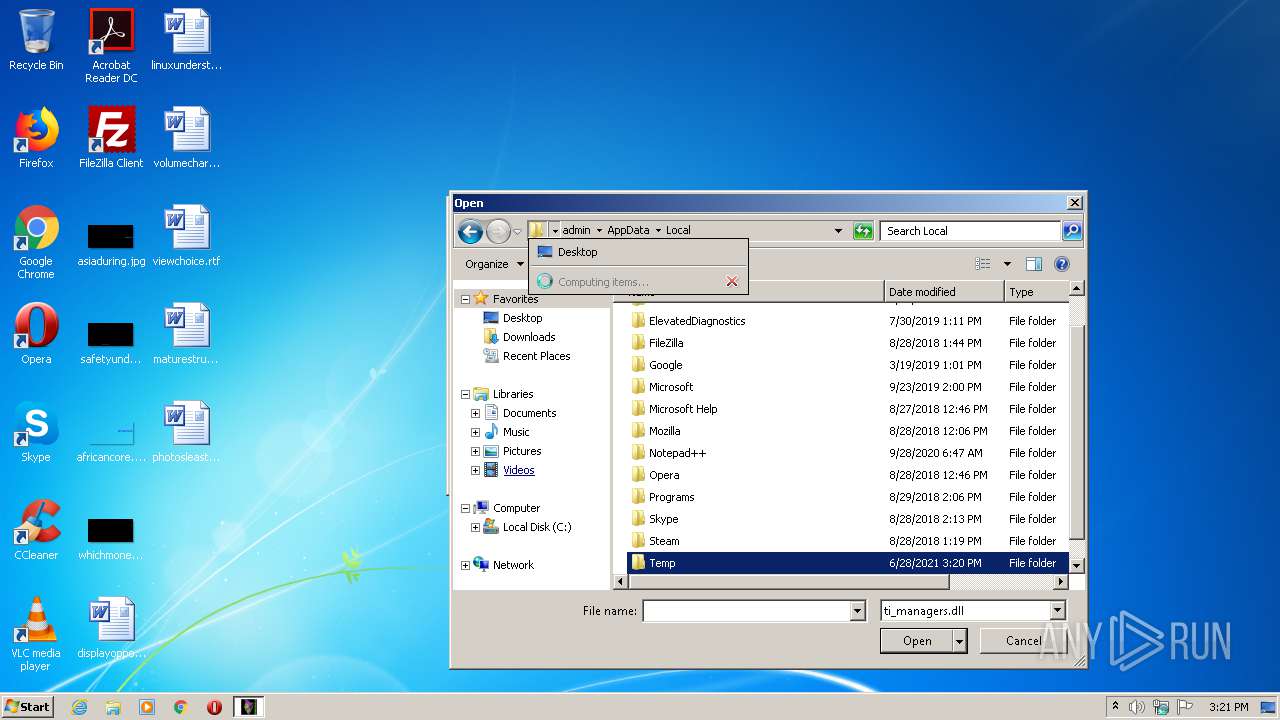
| 3660 | Acronis True Image 2020 v24 Patch.exe | C:\Users\admin\AppData\Local\Temp\regpatch.reg | text | |
MD5:4F4A808FCC40A756A65D0B774641C7CA | SHA256:1670E7E11EF0AC4313ADE7F0BB615C3AE77CDF5D409C5D82FB0B28877EBC0396 | |||
| 3660 | Acronis True Image 2020 v24 Patch.exe | C:\Users\admin\AppData\Local\Temp\dup2patcher.dll | executable | |
MD5:F36216E6044E18EC3ACE3C620DEF0976 | SHA256:3B8934957E3298CCE03EDB5E0CBE6226BBBAE7649F4F4B79691D15B29385C3BC | |||
| 1976 | Kill.exe | C:\Users\admin\AppData\Local\Temp\1F7D.tmp\1F7E.bat | text | |
MD5:3F69D98253DD6D0074AC243758A3B669 | SHA256:09E9BFF474ECDDB663E6FE33A75BC2151220AA1DCA2A9D5E814C982B57BCF9F6 | |||
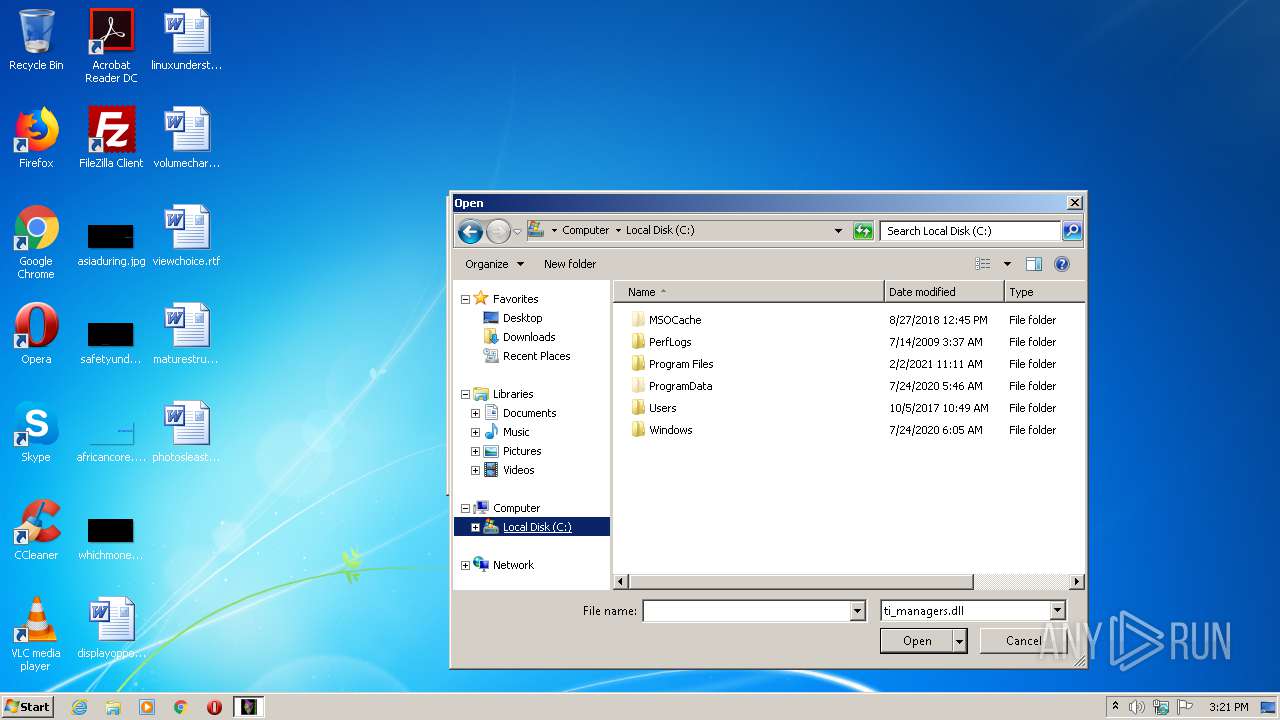
| 3660 | Acronis True Image 2020 v24 Patch.exe | C:\Windows\System32\drivers\etc\hosts | text | |
MD5:DCC1DC6988D277EA5ECA8D7333527A15 | SHA256:351BE0FD2DC49A81B98467763A62BFE6D17A916DDC1ECB7415344250380164BB | |||
| 3660 | Acronis True Image 2020 v24 Patch.exe | C:\Windows\System32\drivers\etc\hosts.BAK | text | |
MD5:3688374325B992DEF12793500307566D | SHA256:2D6BDFB341BE3A6234B24742377F93AA7C7CFB0D9FD64EFA9282C87852E57085 | |||
| 3660 | Acronis True Image 2020 v24 Patch.exe | C:\Users\admin\AppData\Local\Temp\Kill.exe | executable | |
MD5:52E8AD00B03376A80DA0A08BD557700A | SHA256:7DA674AF781BA684ADB85B413DE6F1AE9EFBE1FE6FDB0C4EE0DC6539036D31D9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report