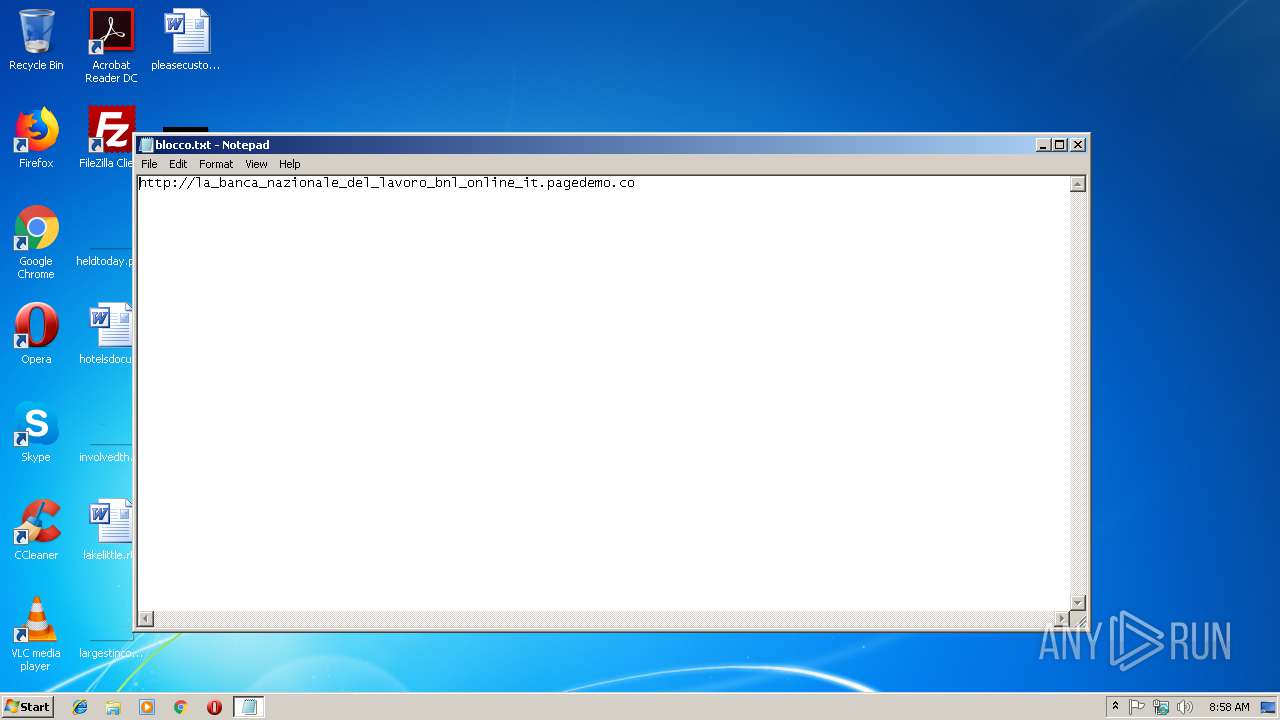
| File name: | blocco.txt |
| Full analysis: | https://app.any.run/tasks/c127e1e1-b4d2-4264-9b4a-5efd90e7d415 |
| Verdict: | Malicious activity |
| Analysis date: | December 14, 2018, 08:57:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with no line terminators |
| MD5: | 853000385EF6B0482D2F90E5A70F3CE9 |
| SHA1: | 30CC66C7FA38544F00052CFD20CD5890240C3436 |
| SHA256: | B94D6885BB09A4E3A0E70371D3DB594E5F3B37FBFC45EFED731E2AC083F1C2D3 |
| SSDEEP: | 3:N1KSE6CTaHrYMRLjZ:CST9YQLjZ |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 4080)
Reads settings of System Certificates
- chrome.exe (PID: 4080)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
41
Monitored processes
12
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=4084 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2204 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,2711759363646038479,13200592699440873029,131072 --enable-features=PasswordImport --service-pipe-token=E4A745658BBD781D30A94E673EA59142 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=E4A745658BBD781D30A94E673EA59142 --renderer-client-id=5 --mojo-platform-channel-handle=1900 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2420 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,2711759363646038479,13200592699440873029,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=A8CB62F72E6A1AA0747F02334C16E5EF --mojo-platform-channel-handle=4228 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2724 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,2711759363646038479,13200592699440873029,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=60226A4512C08296AE42C2577917B138 --mojo-platform-channel-handle=2460 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6f3b00b0,0x6f3b00c0,0x6f3b00cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2944 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\blocco.txt | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2972 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,2711759363646038479,13200592699440873029,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=E9AD147314892FA1F131C9123C7B8182 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=E9AD147314892FA1F131C9123C7B8182 --renderer-client-id=6 --mojo-platform-channel-handle=3632 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3052 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=984,2711759363646038479,13200592699440873029,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=E128D2D43D109D445D4E70277ECFBC8E --mojo-platform-channel-handle=4408 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,2711759363646038479,13200592699440873029,131072 --enable-features=PasswordImport --service-pipe-token=B02BBD33E8BD4F1F756A245C658F00DC --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=B02BBD33E8BD4F1F756A245C658F00DC --renderer-client-id=3 --mojo-platform-channel-handle=2076 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=984,2711759363646038479,13200592699440873029,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=8D20C2F4628B2E9CA5558AC1EF2EE3D2 --mojo-platform-channel-handle=944 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
528
Read events
479
Write events
46
Delete events
3
Modification events
| (PID) Process: | (4080) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4080) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2132) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 4080-13189251497941625 |
Value: 259 | |||
| (PID) Process: | (4080) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4080) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (4080) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (4080) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (4080) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (4080) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 4080-13189251497941625 |
Value: 259 | |||
| (PID) Process: | (4080) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
0
Suspicious files
62
Text files
68
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4080 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\8efaae2b-2473-45c3-9106-3078fab0d1c8.tmp | — | |
MD5:— | SHA256:— | |||
| 4080 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 4080 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 4080 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\51ff961b-335c-45c9-88dd-9075d03491d2.tmp | — | |
MD5:— | SHA256:— | |||
| 4080 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 4080 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 4080 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\CacheStorage\e6622492fa163609ddd4212f54512baa07929ed3\caecb3bd-7969-4305-84d6-3a376453ec73\index-dir\temp-index | — | |
MD5:— | SHA256:— | |||
| 4080 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Thumbnails\LOG.old~RF2496a3.TMP | text | |
MD5:— | SHA256:— | |||
| 4080 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF248359.TMP | text | |
MD5:— | SHA256:— | |||
| 4080 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Translate Ranker Model~RF249887.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
129
TCP/UDP connections
63
DNS requests
41
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
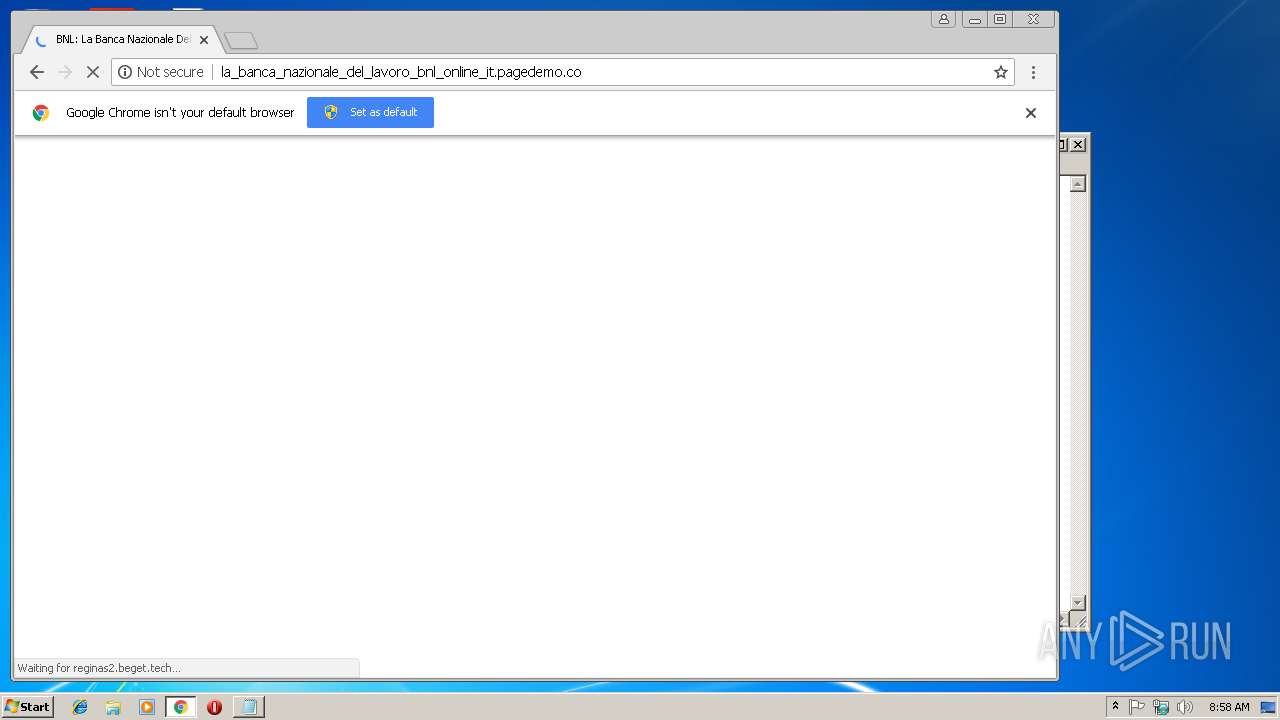
4080 | chrome.exe | GET | 302 | 5.101.152.4:80 | http://reginas2.beget.tech/ | RU | — | — | malicious |
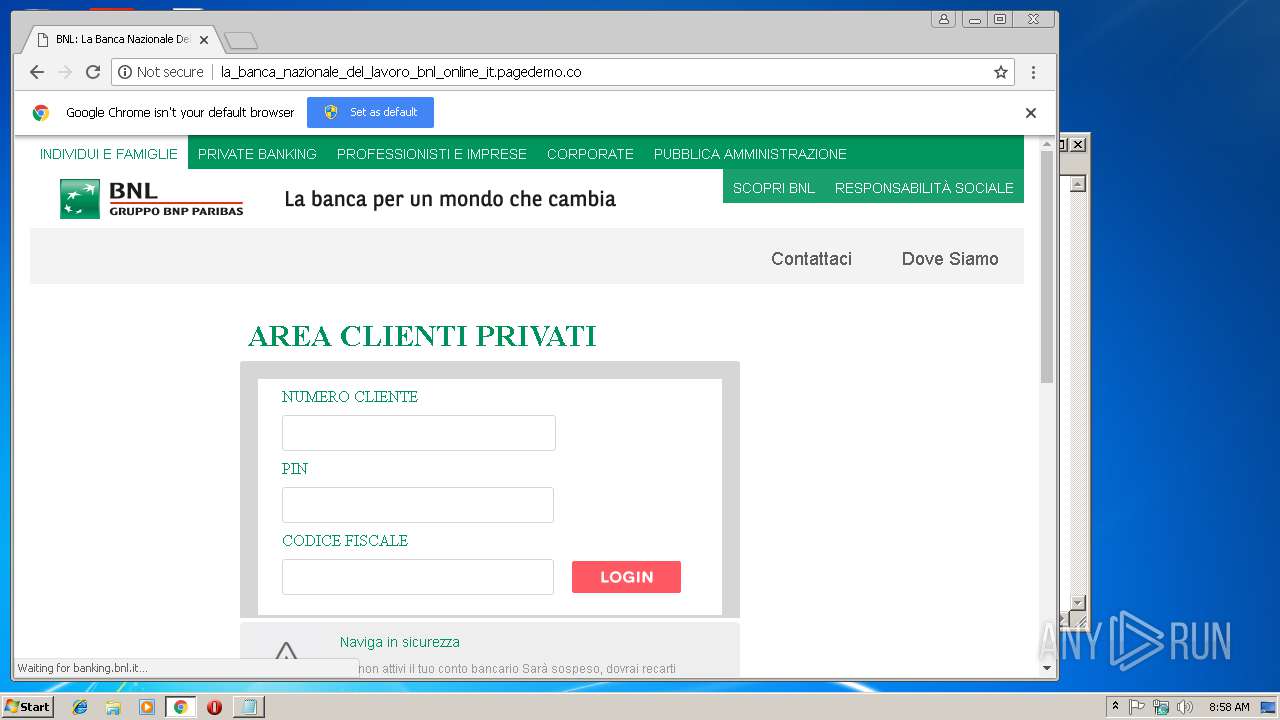
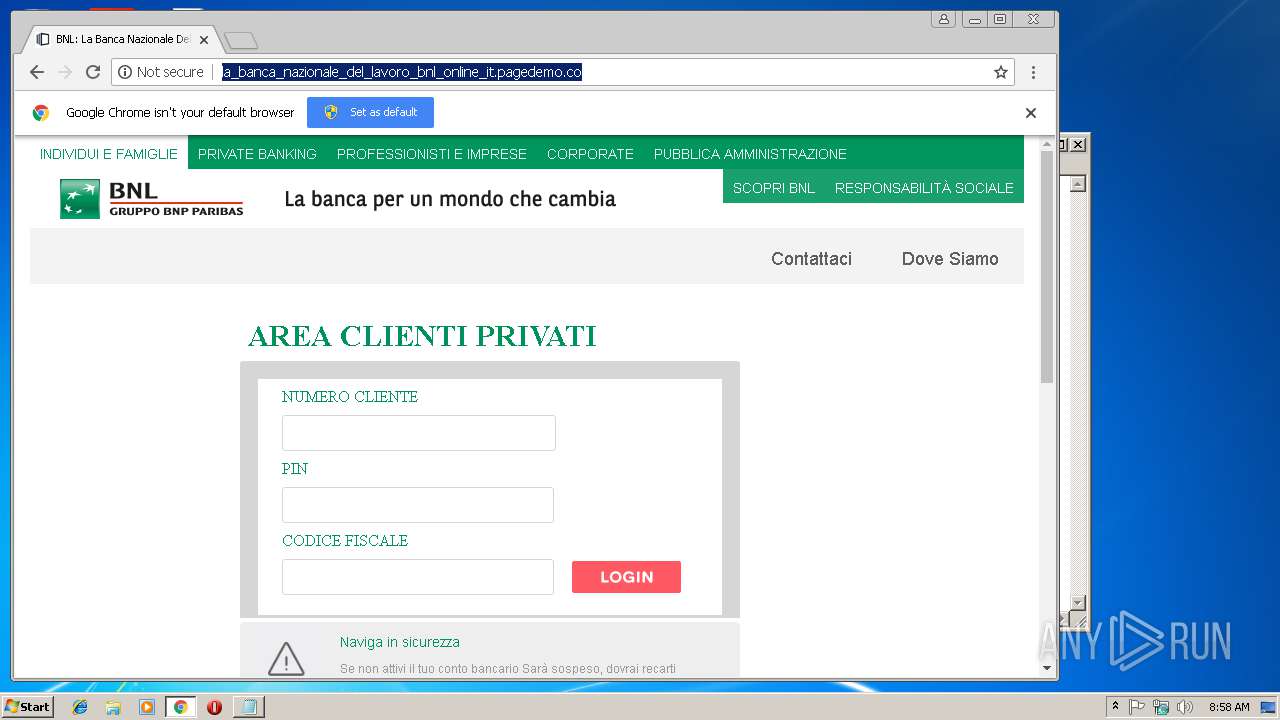
4080 | chrome.exe | GET | 200 | 52.8.28.190:80 | http://la_banca_nazionale_del_lavoro_bnl_online_it.pagedemo.co/ | US | html | 2.34 Kb | suspicious |
4080 | chrome.exe | GET | 200 | 147.75.83.19:80 | http://static.hotjar.com/c/hotjar-730294.js?sv=5 | US | text | 1.01 Kb | whitelisted |
4080 | chrome.exe | GET | 200 | 52.85.182.205:80 | http://dnn506yrbagrg.cloudfront.net/pages/scripts/0022/9093.js?428879 | US | text | 25.9 Kb | whitelisted |
4080 | chrome.exe | GET | 200 | 5.101.152.4:80 | http://reginas2.beget.tech/0d7ed3f773d12a0c4605bc9d6846f211/login_files/style.css | RU | text | 4.38 Kb | malicious |
4080 | chrome.exe | GET | 200 | 23.201.183.73:80 | http://tags.bkrtx.com/js/bk-coretag.js | NL | text | 10.1 Kb | whitelisted |
4080 | chrome.exe | GET | 200 | 172.217.22.80:80 | http://storage.googleapis.com/page-generator/js/utils.beb530071620efacb519.js | US | text | 10.3 Kb | whitelisted |
4080 | chrome.exe | GET | 404 | 5.101.152.4:80 | http://reginas2.beget.tech/0d7ed3f773d12a0c4605bc9d6846f211/login_files/jquery.mCustomScrollbar.min.css | RU | html | 357 b | malicious |
4080 | chrome.exe | GET | 200 | 52.85.182.205:80 | http://dnn506yrbagrg.cloudfront.net/pages/scripts/0022/9093.js?428795 | US | text | 25.9 Kb | whitelisted |
4080 | chrome.exe | GET | 200 | 5.101.152.4:80 | http://reginas2.beget.tech/0d7ed3f773d12a0c4605bc9d6846f211/login_files/fonts.css | RU | text | 1.13 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4080 | chrome.exe | 172.217.16.131:443 | www.gstatic.com | Google Inc. | US | whitelisted |
4080 | chrome.exe | 172.217.23.170:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
4080 | chrome.exe | 172.217.16.196:443 | www.google.com | Google Inc. | US | whitelisted |
4080 | chrome.exe | 52.8.28.190:80 | la_banca_nazionale_del_lavoro_bnl_online_it.pagedemo.co | Amazon.com, Inc. | US | unknown |
4080 | chrome.exe | 5.101.152.4:80 | reginas2.beget.tech | Beget Ltd | RU | malicious |
4080 | chrome.exe | 216.58.207.67:443 | www.google.de | Google Inc. | US | whitelisted |
4080 | chrome.exe | 147.75.83.19:80 | static.hotjar.com | Packet Host, Inc. | US | unknown |
4080 | chrome.exe | 23.201.183.73:80 | tags.bkrtx.com | Akamai Technologies, Inc. | NL | whitelisted |
4080 | chrome.exe | 172.217.18.174:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
4080 | chrome.exe | 172.217.21.195:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.google.de |
| whitelisted |
www.gstatic.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
la_banca_nazionale_del_lavoro_bnl_online_it.pagedemo.co |
| suspicious |
fonts.gstatic.com |
| whitelisted |
storage.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4080 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP Host header invalid |
4080 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS Possible Phishing Redirect Feb 09 2016 |
4080 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP Host header invalid |
1 ETPRO signatures available at the full report