| File name: | GUP.exe |
| Full analysis: | https://app.any.run/tasks/4f590715-3baf-4673-9d57-f9ddfb5a5c2a |
| Verdict: | Malicious activity |
| Analysis date: | July 29, 2024, 04:38:39 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows |
| MD5: | 67BAA5943AC95009ACC6D9EC46875462 |
| SHA1: | 678855F7001BBE90651063FBDC6C3113AFB8A33E |
| SHA256: | B94A58C21019D2CE2D1AB6C5A4D6229A88DD71C486C31F94C6C566E792DF7378 |
| SSDEEP: | 12288:ApUwT/hb4TFQrdIvkgXcu/75DoRh9RdVeEFSTqC4T5UNwuuuuuuuYVfOJwtSwuuh:Apr9b4TMdIcg1whOJwtFxB1 |
MALICIOUS
Drops the executable file immediately after the start
- rundll32.exe (PID: 1292)
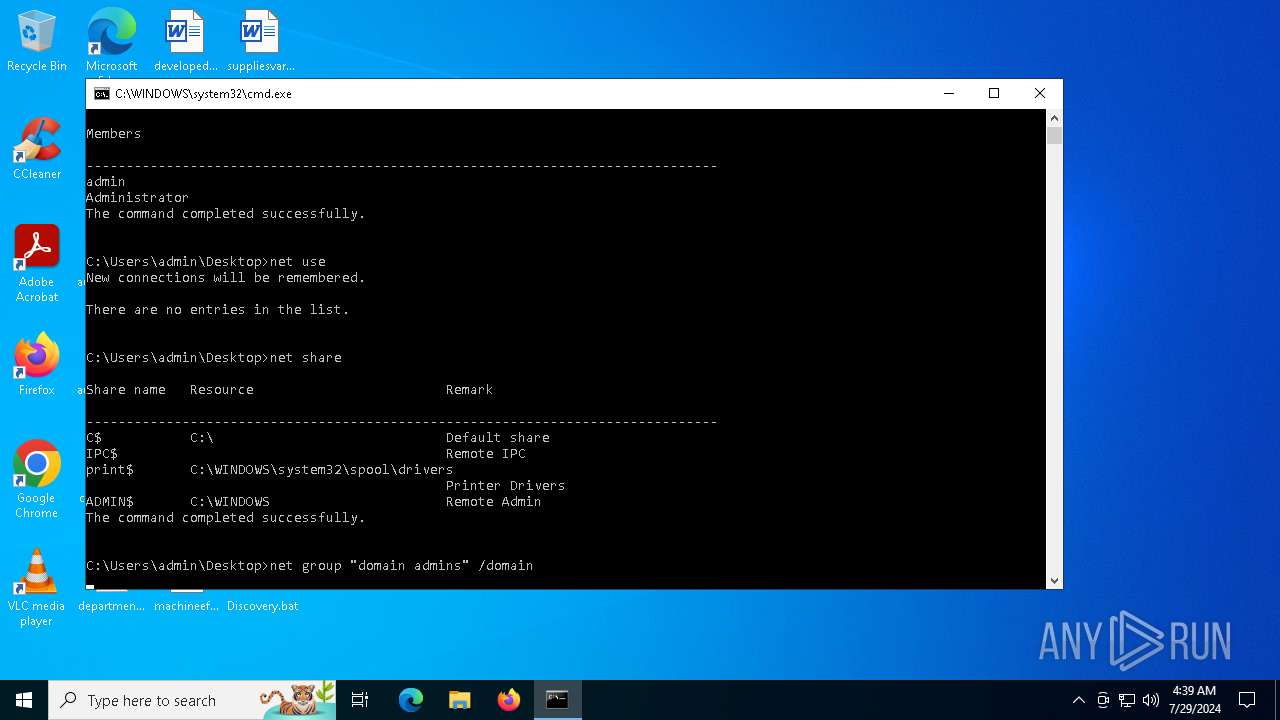
Starts NET.EXE to view/add/change user profiles
- net.exe (PID: 1428)
- cmd.exe (PID: 4580)
Starts NET.EXE to view/change users localgroup
- net.exe (PID: 4436)
- cmd.exe (PID: 4580)
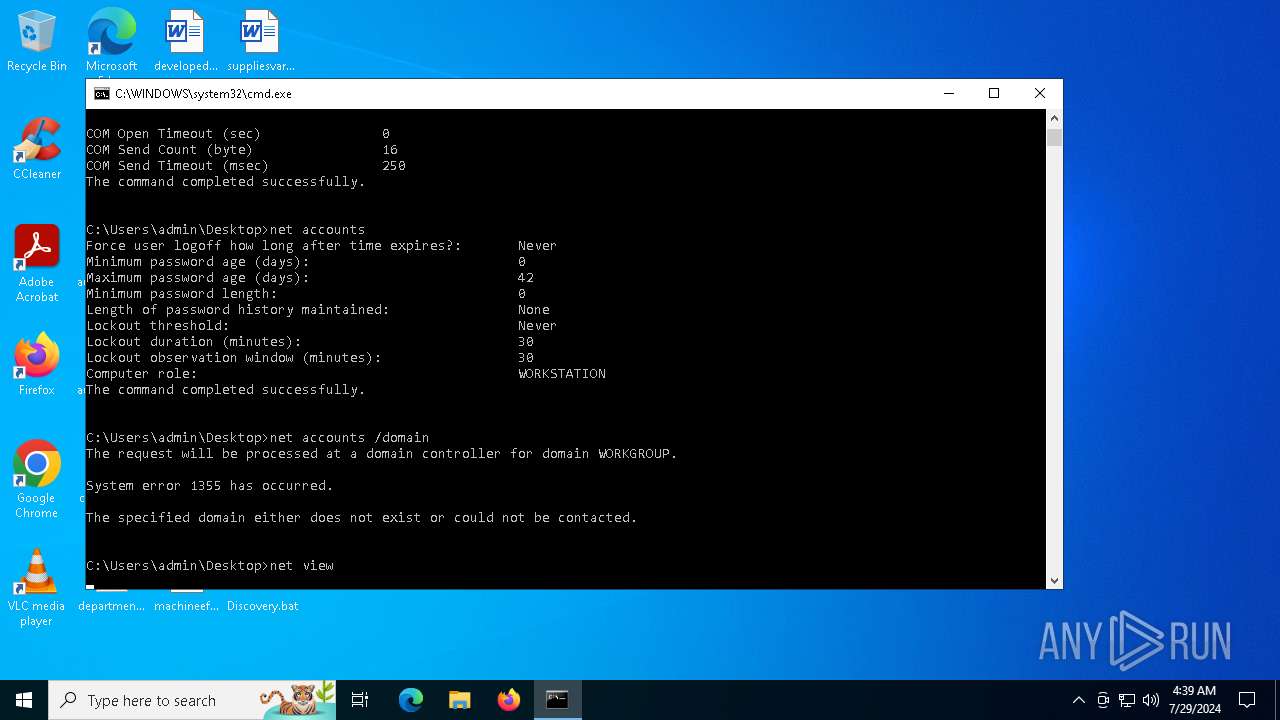
Starts NET.EXE to view/change login properties
- net.exe (PID: 7028)
- cmd.exe (PID: 4580)
- net.exe (PID: 2088)
- net.exe (PID: 7072)
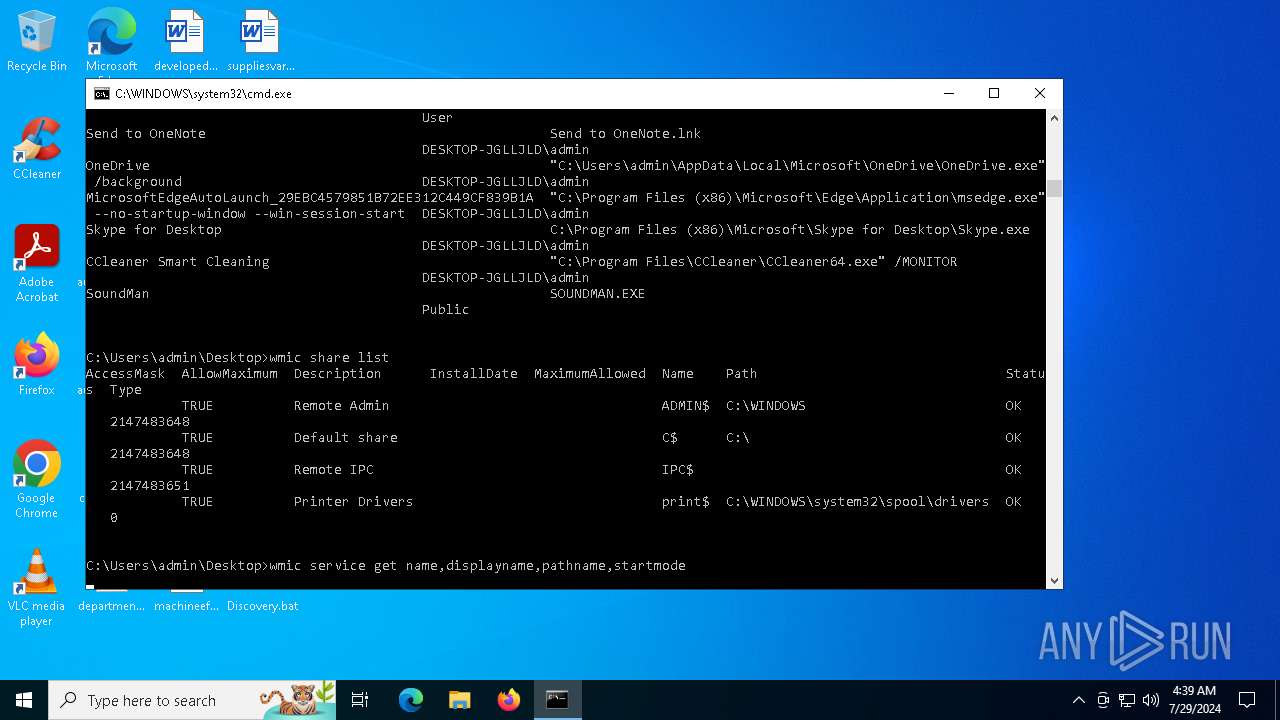
Starts NET.EXE to view/change shared resources
- cmd.exe (PID: 4580)
- net.exe (PID: 3188)
Starts NET.EXE to view/change users group
- cmd.exe (PID: 4580)
- net.exe (PID: 5392)
SUSPICIOUS
Starts NET.EXE to map network drives
- cmd.exe (PID: 4580)
Starts NET.EXE to manage network resources
- cmd.exe (PID: 4580)
- net.exe (PID: 5728)
Starts NET.EXE for network exploration
- cmd.exe (PID: 4580)
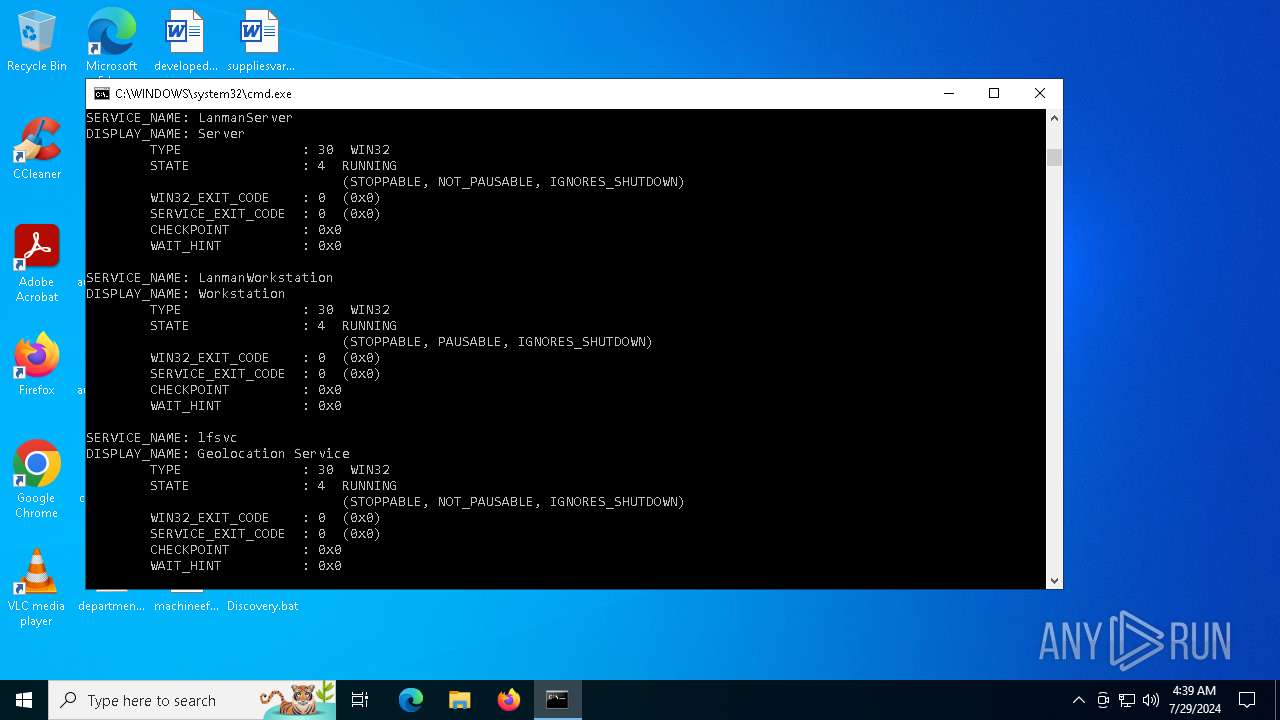
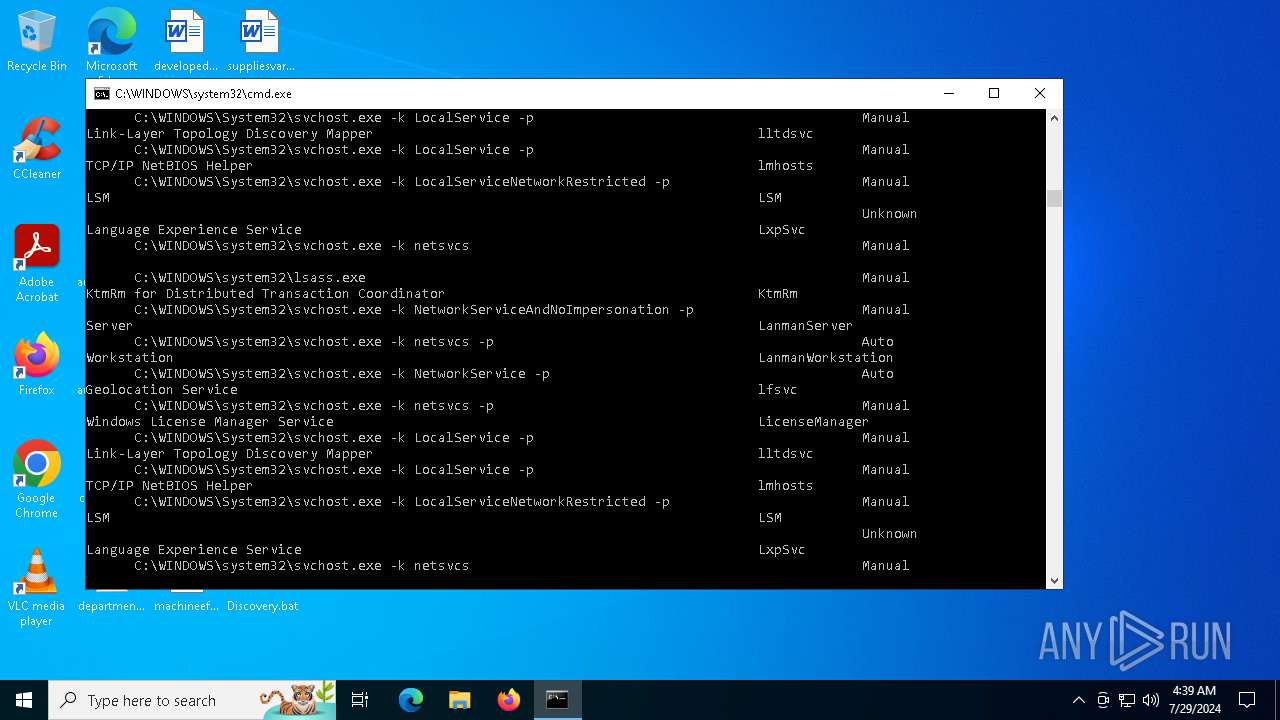
Starts SC.EXE for service management
- cmd.exe (PID: 4580)
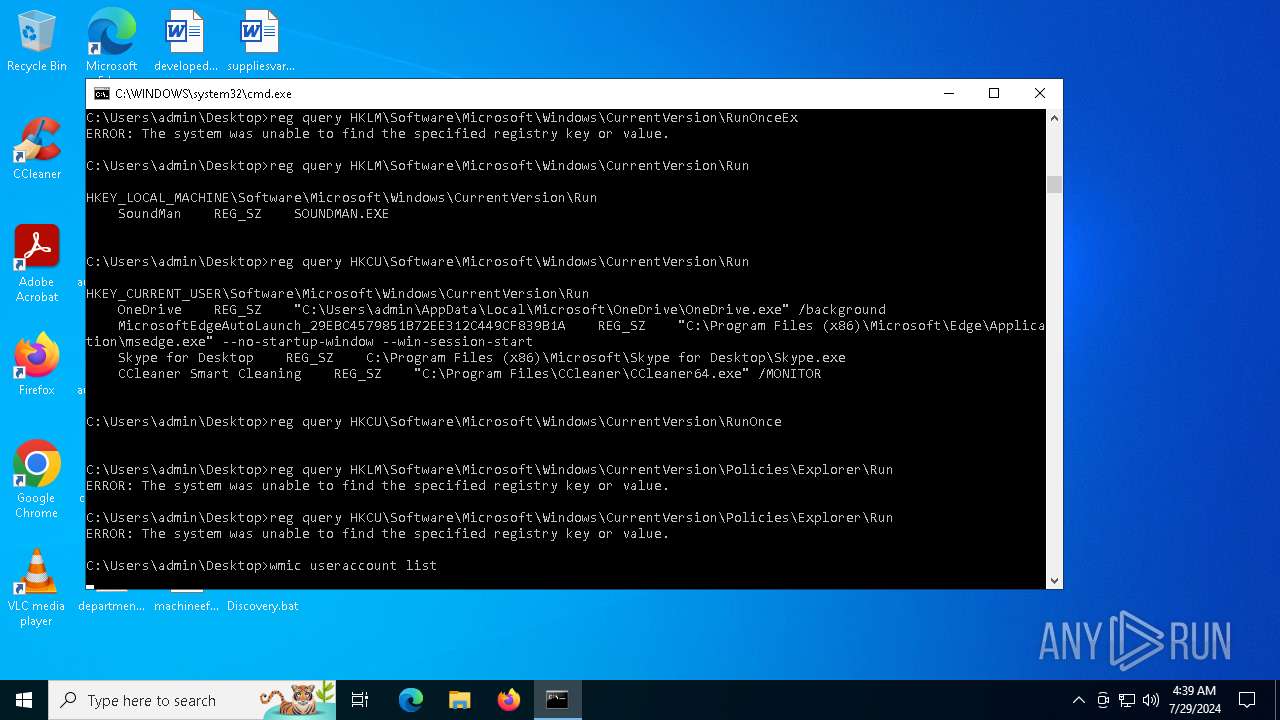
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 4580)
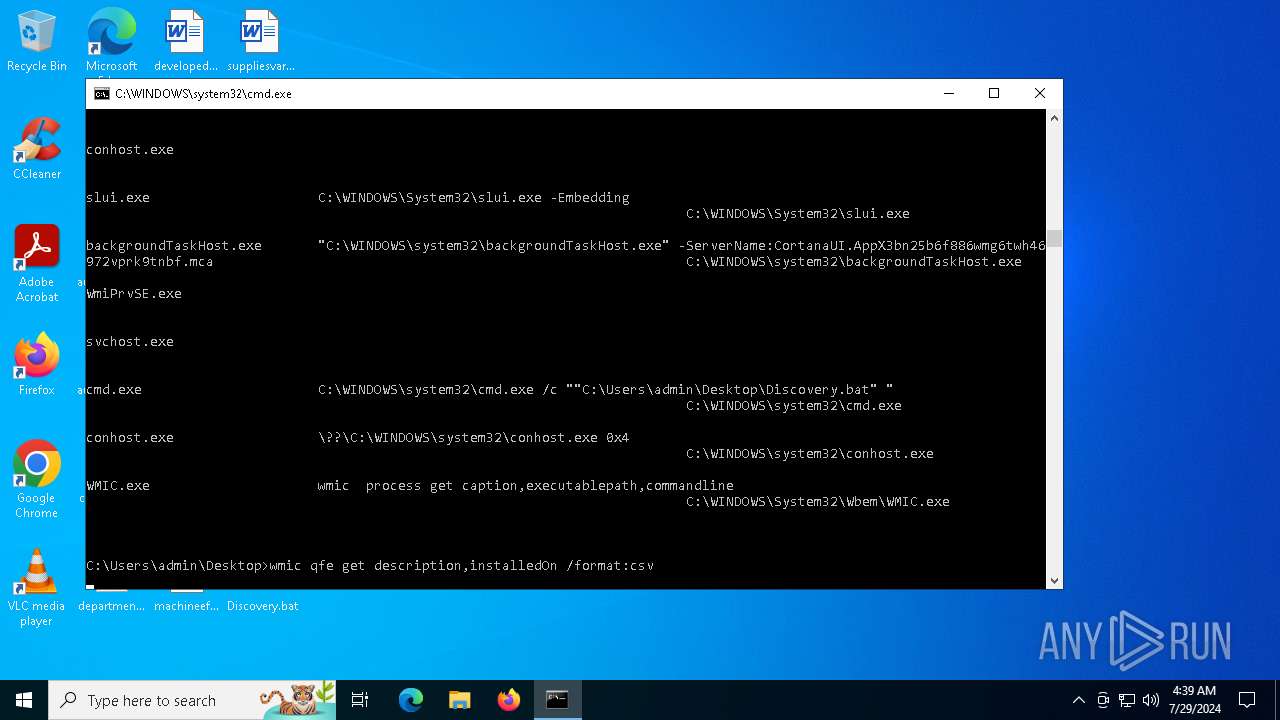
Uses WMIC.EXE to obtain user accounts information
- cmd.exe (PID: 4580)
Accesses computer name via WMI (SCRIPT)
- WMIC.exe (PID: 6876)
- WMIC.exe (PID: 5152)
- WMIC.exe (PID: 4040)
Accesses current user name via WMI (SCRIPT)
- WMIC.exe (PID: 6876)
- WMIC.exe (PID: 5152)
- WMIC.exe (PID: 2368)
- WMIC.exe (PID: 5040)
Uses WMIC.EXE to obtain commands that are run when users log in
- cmd.exe (PID: 4580)
Uses WMIC.EXE to obtain shared resources information
- cmd.exe (PID: 4580)
Uses WMIC.EXE to obtain service application data
- cmd.exe (PID: 4580)
Identifying current user with WHOAMI command
- cmd.exe (PID: 4580)
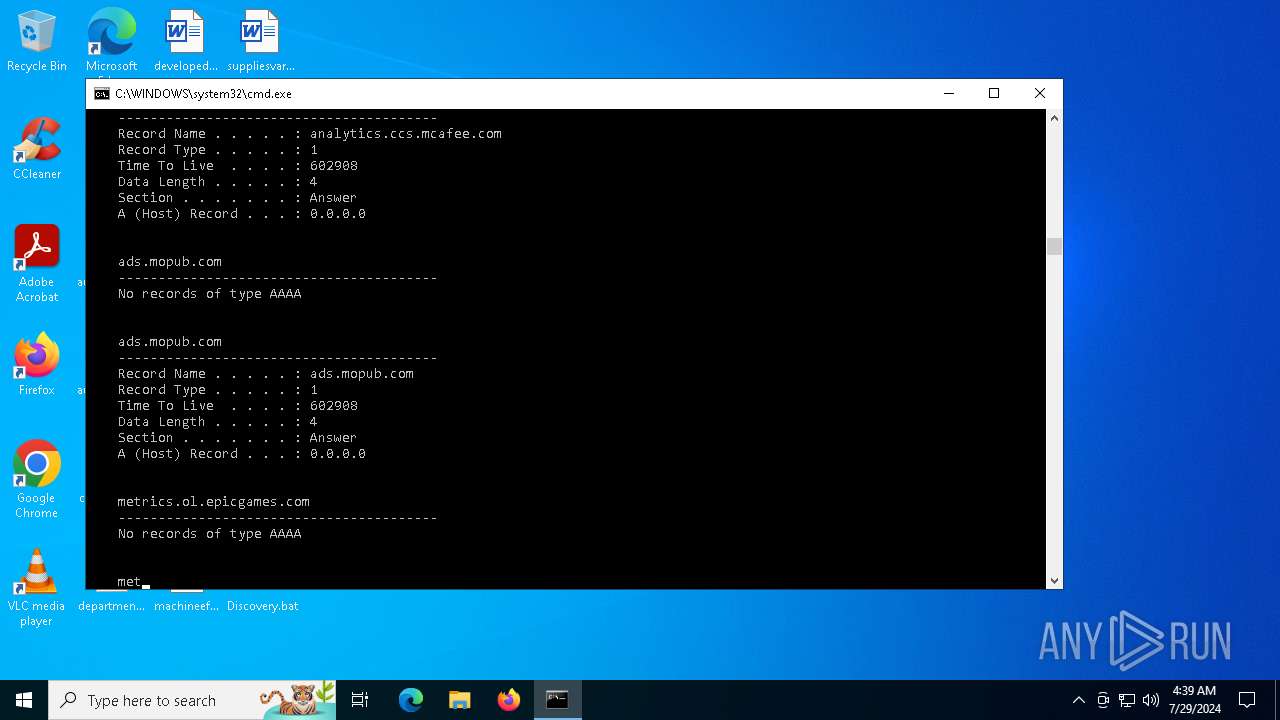
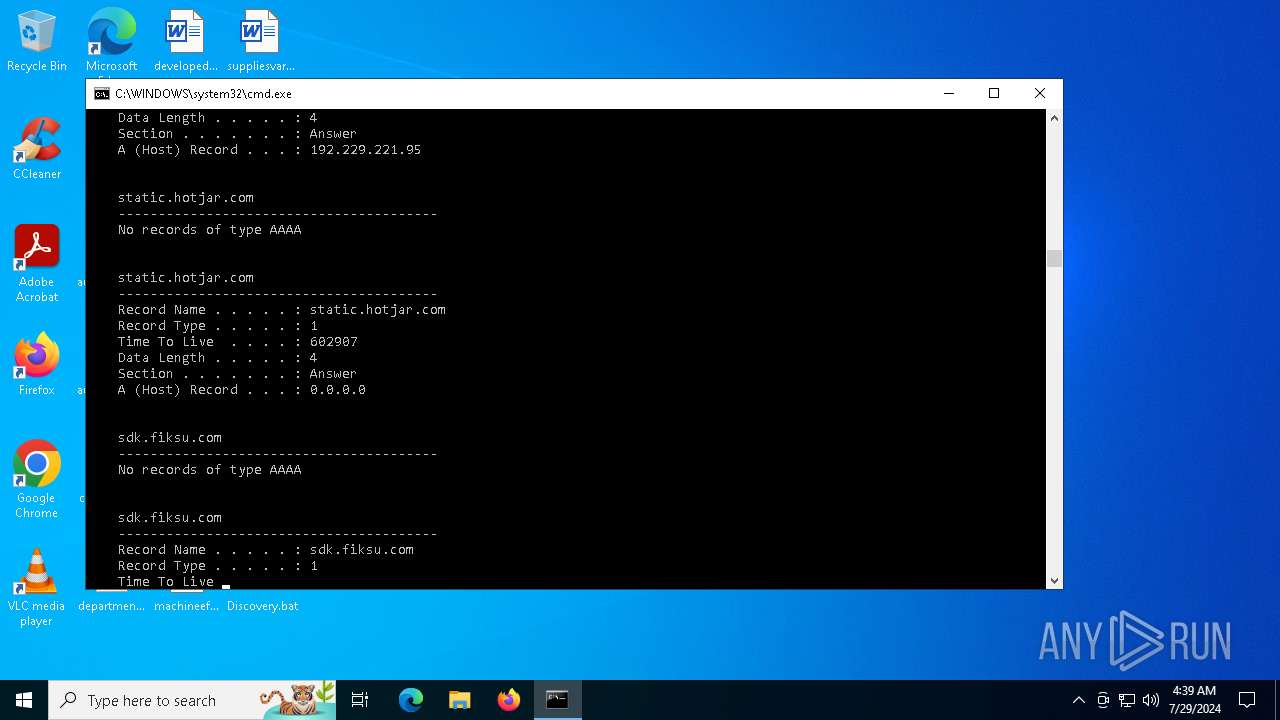
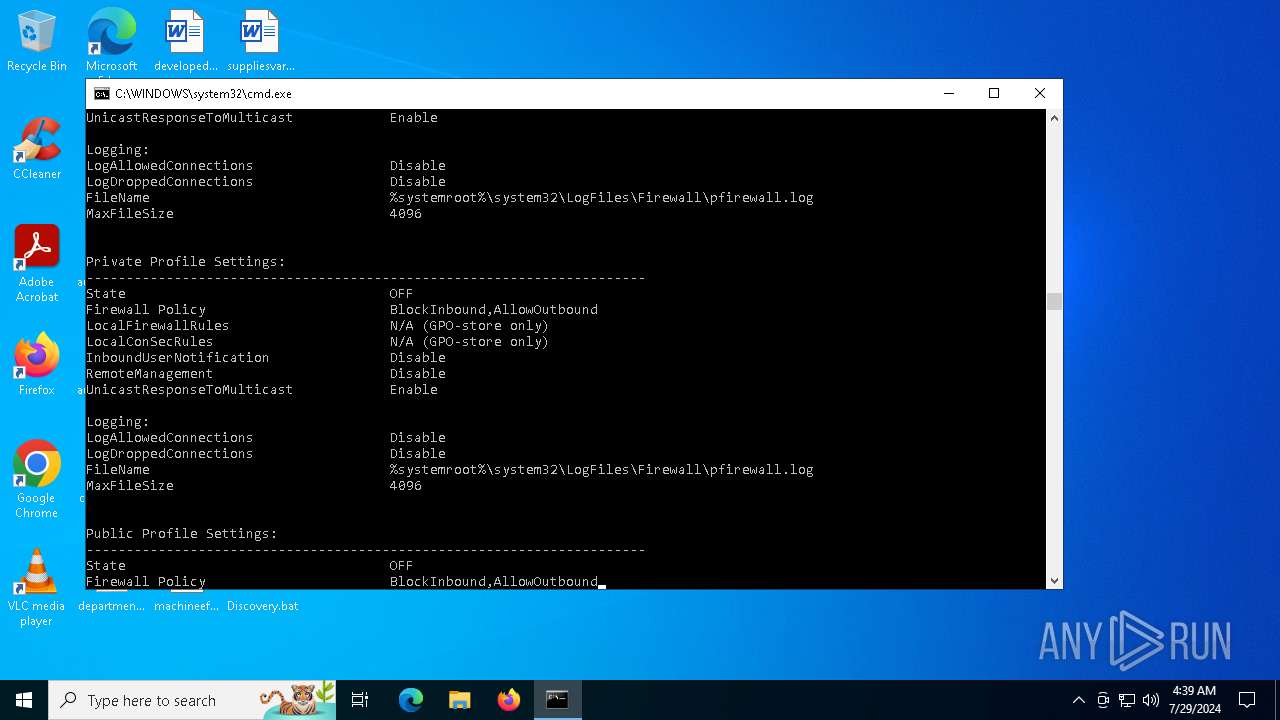
Process uses IPCONFIG to discover network configuration
- cmd.exe (PID: 4580)
Suspicious use of NETSH.EXE
- cmd.exe (PID: 4580)
Starts CMD.EXE for commands execution
- rundll32.exe (PID: 4840)
Uses WMIC.EXE to obtain data on processes
- cmd.exe (PID: 4580)
Uses WMIC.EXE to obtain quick Fix Engineering (patches) data
- cmd.exe (PID: 4580)
Process uses ARP to discover network configuration
- cmd.exe (PID: 4580)
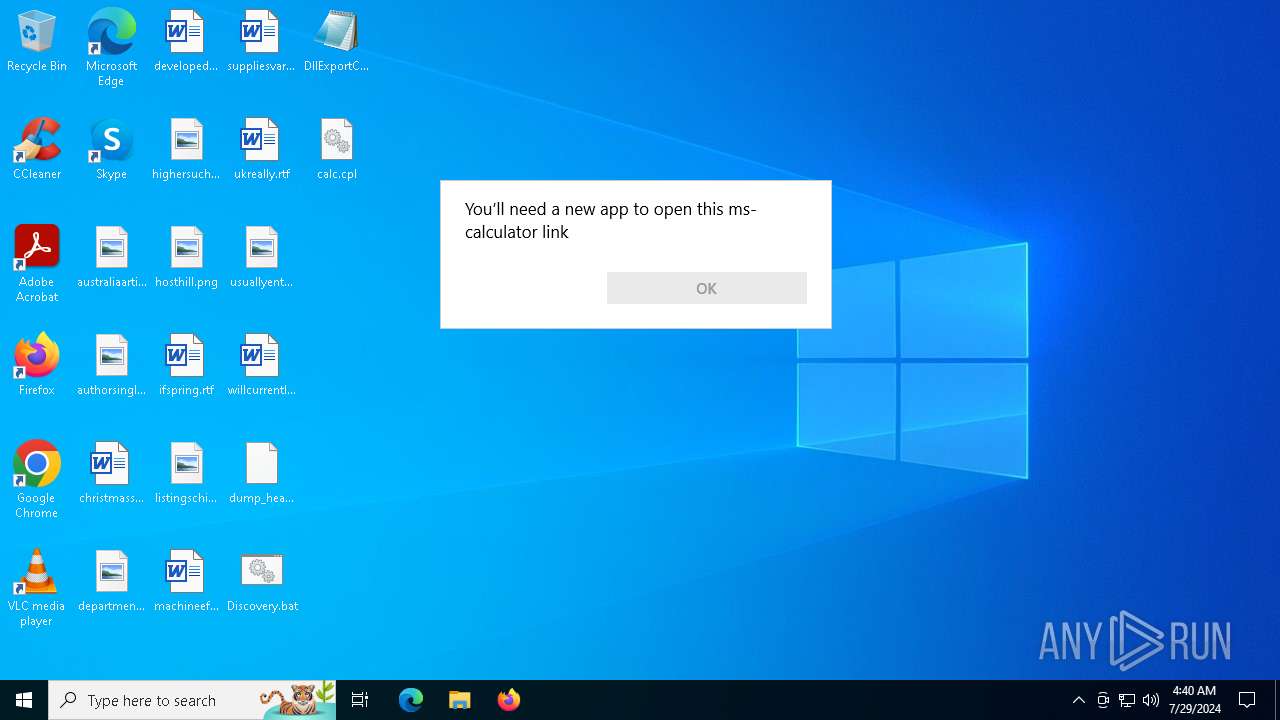
Uses RUNDLL32.EXE to load library
- control.exe (PID: 6524)
Uses ROUTE.EXE to obtain the routing table information
- cmd.exe (PID: 4580)
INFO
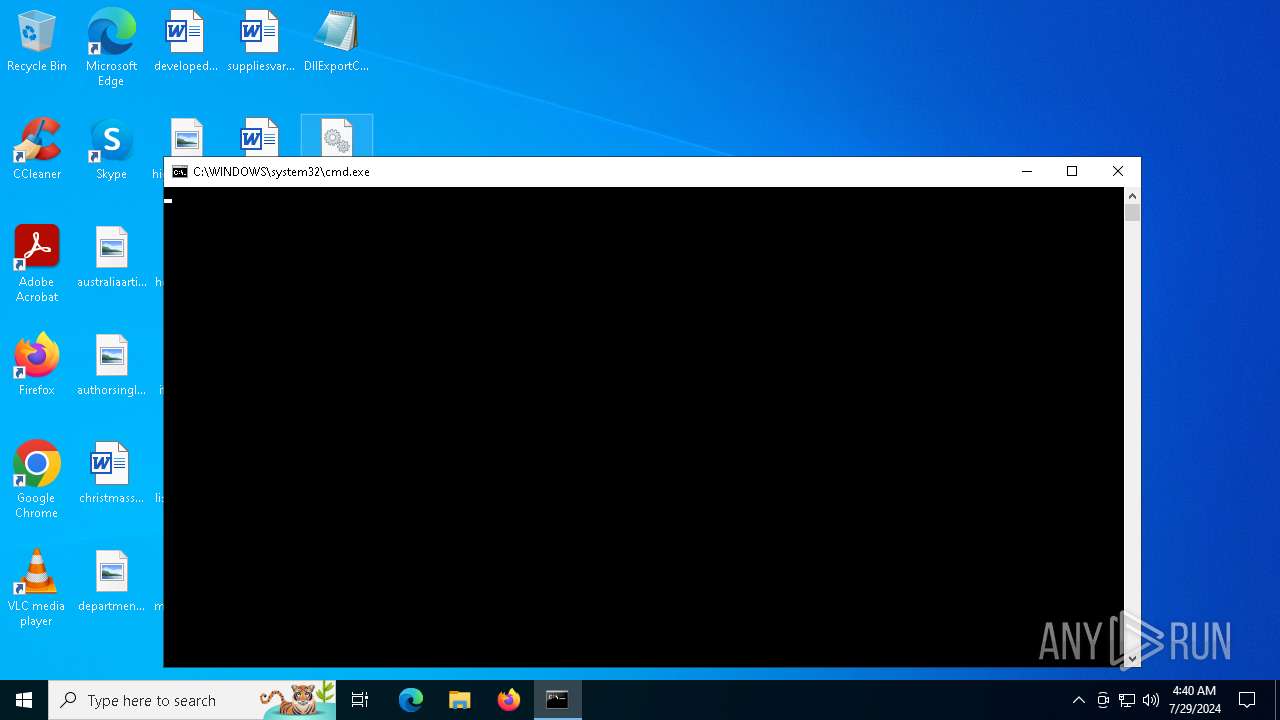
Manual execution by a user
- cmd.exe (PID: 4580)
- control.exe (PID: 6524)
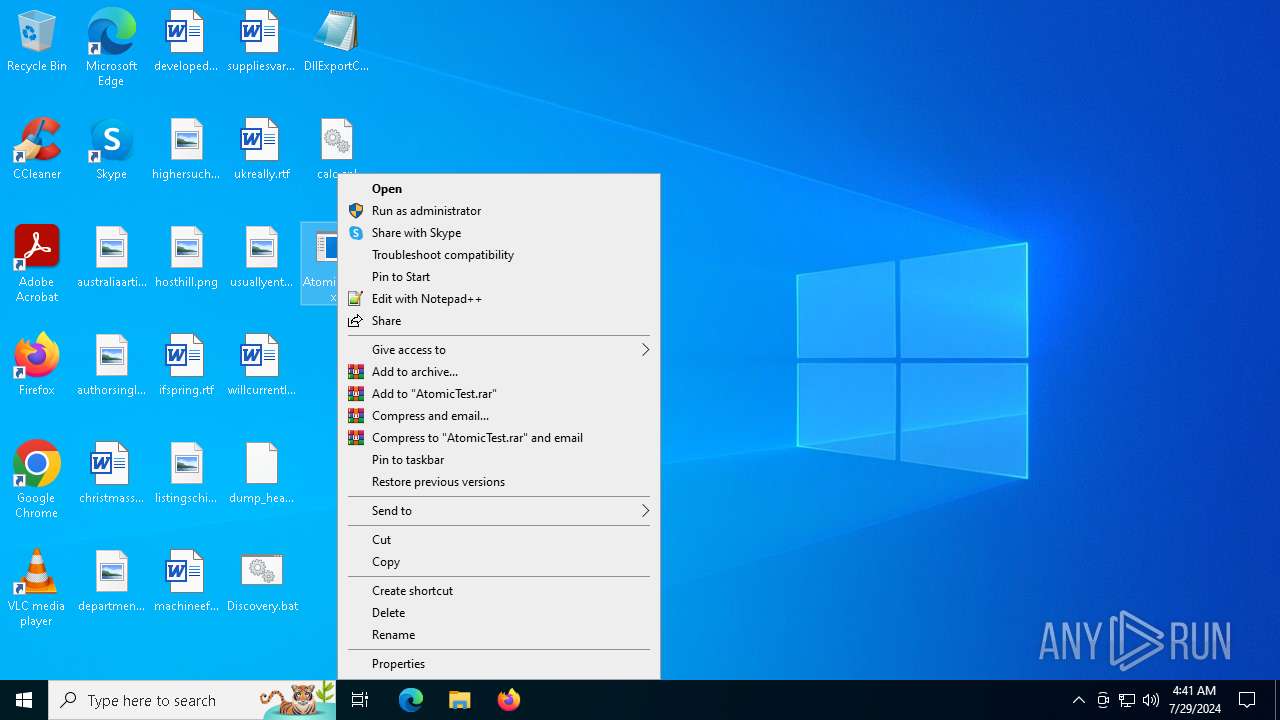
- AtomicTest.exe (PID: 2672)
- AtomicTest.exe (PID: 3360)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 6876)
- WMIC.exe (PID: 5152)
- WMIC.exe (PID: 5040)
- WMIC.exe (PID: 2368)
- WMIC.exe (PID: 4040)
- WMIC.exe (PID: 1736)
- control.exe (PID: 6524)
- calc.exe (PID: 3788)
- WMIC.exe (PID: 6164)
- WMIC.exe (PID: 5284)
- OpenWith.exe (PID: 6584)
Reads the software policy settings
- slui.exe (PID: 6084)
Checks proxy server information
- slui.exe (PID: 6084)
Checks supported languages
- AtomicTest.exe (PID: 3360)
- AtomicTest.exe (PID: 2672)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2019:10:15 20:52:53+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14 |
| CodeSize: | 483328 |
| InitializedDataSize: | 242688 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x33ff0 |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.1.1.0 |
| ProductVersionNumber: | 5.1.1.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Don HO don.h@free.fr |
| FileDescription: | WinGup for Notepad++ |
| FileVersion: | 5.11 |
| InternalName: | gup.exe |
| LegalCopyright: | Copyright 2018 by Don HO |
| OriginalFileName: | gup.exe |
| ProductName: | WinGup for Notepad++ |
| ProductVersion: | 5.11 |
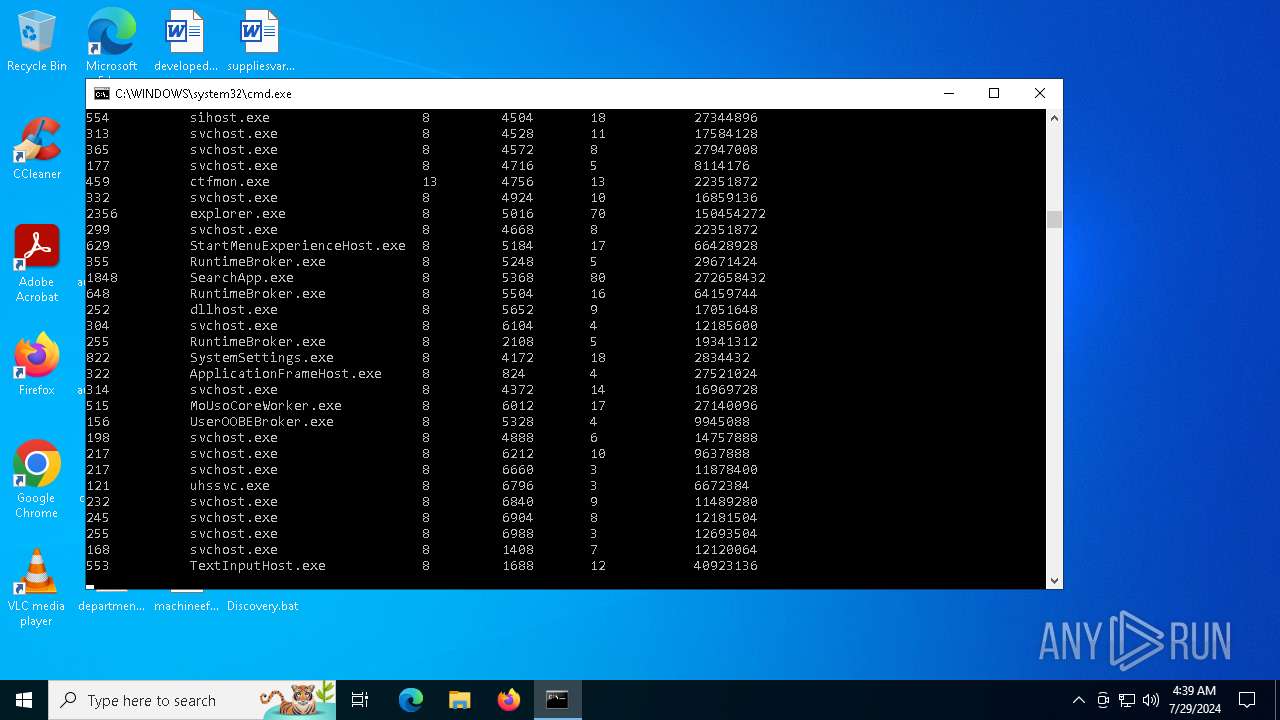
Total processes
215
Monitored processes
68
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | reg query HKCU\Software\Microsoft\Windows\CurrentVersion\RunOnce | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 236 | reg query HKLM\Software\Microsoft\Windows\CurrentVersion\RunServicesOnce | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 488 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1140 | whoami | C:\Windows\System32\whoami.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: whoami - displays logged on user information Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1292 | "C:\Windows\System32\rundll32.exe" C:\Users\admin\Downloads\GUP.exe, #1 | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1428 | net user Administrator /domain | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1544 | quser | C:\Windows\System32\quser.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Query User Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1736 | wmic process list brief | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1772 | systeminfo | C:\Windows\System32\systeminfo.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Displays system information Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1912 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
16 848
Read events
16 827
Write events
21
Delete events
0
Modification events
| (PID) Process: | (5124) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SideBySide |
| Operation: | write | Name: | LastScavengingStarvationReport |
Value: C959BF5271E1DA01 | |||
| (PID) Process: | (5124) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Component Based Servicing |
| Operation: | write | Name: | SessionIdHigh |
Value: 31121777 | |||
| (PID) Process: | (5124) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Component Based Servicing |
| Operation: | write | Name: | SessionIdLow |
Value: | |||
| (PID) Process: | (1772) systeminfo.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3c\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\mlang.dll,-4386 |
Value: English (United States) | |||
| (PID) Process: | (6524) control.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6524) control.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6524) control.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6524) control.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3788) calc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (3788) calc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5124 | TiWorker.exe | C:\Windows\Logs\CBS\CBS.log | text | |
MD5:745EF410B230FEC285E887994987693C | SHA256:6D933265A774BE46D6794BDCA29E847F1D5E53EB7720195D9593BCAA94181701 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
54
DNS requests
27
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4424 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5368 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
3840 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5368 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
4132 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
3676 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5368 | SearchApp.exe | 131.253.33.254:443 | a-ring-fallback.msedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
3952 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6064 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5368 | SearchApp.exe | 104.126.37.160:443 | www.bing.com | Akamai International B.V. | DE | unknown |
— | — | 40.91.76.224:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6716 | slui.exe | 40.91.76.224:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6012 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4032 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
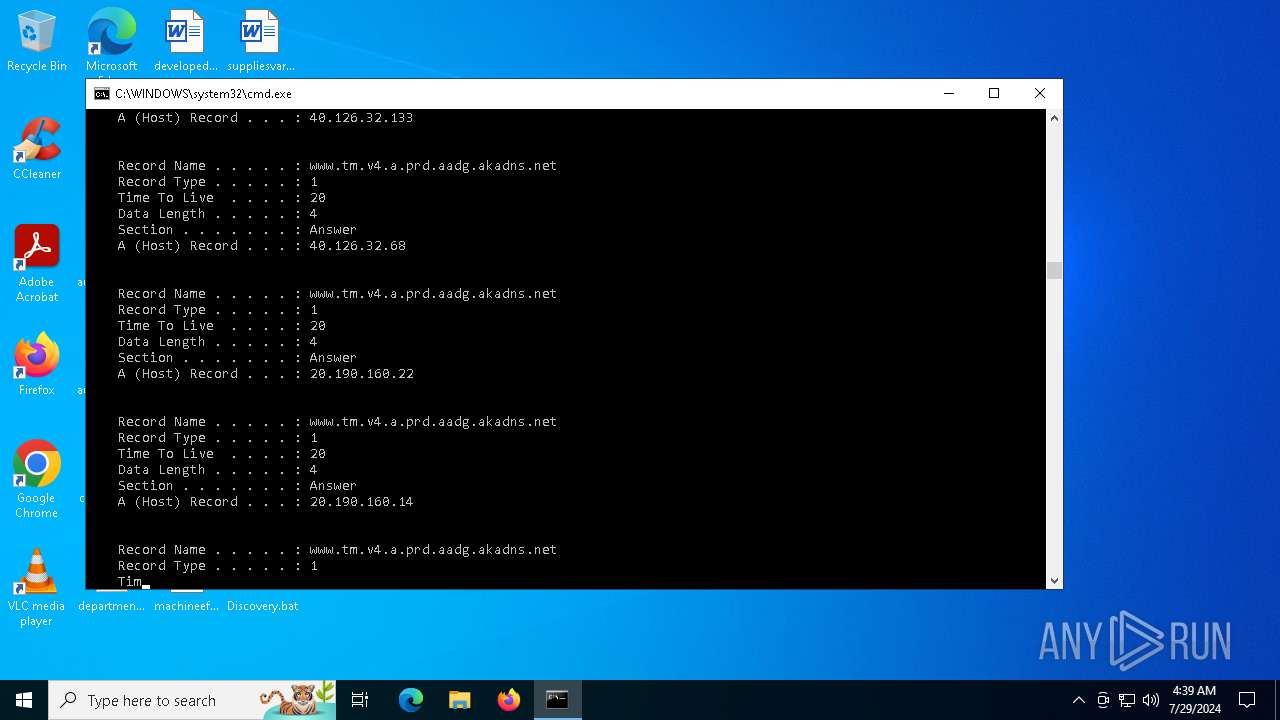
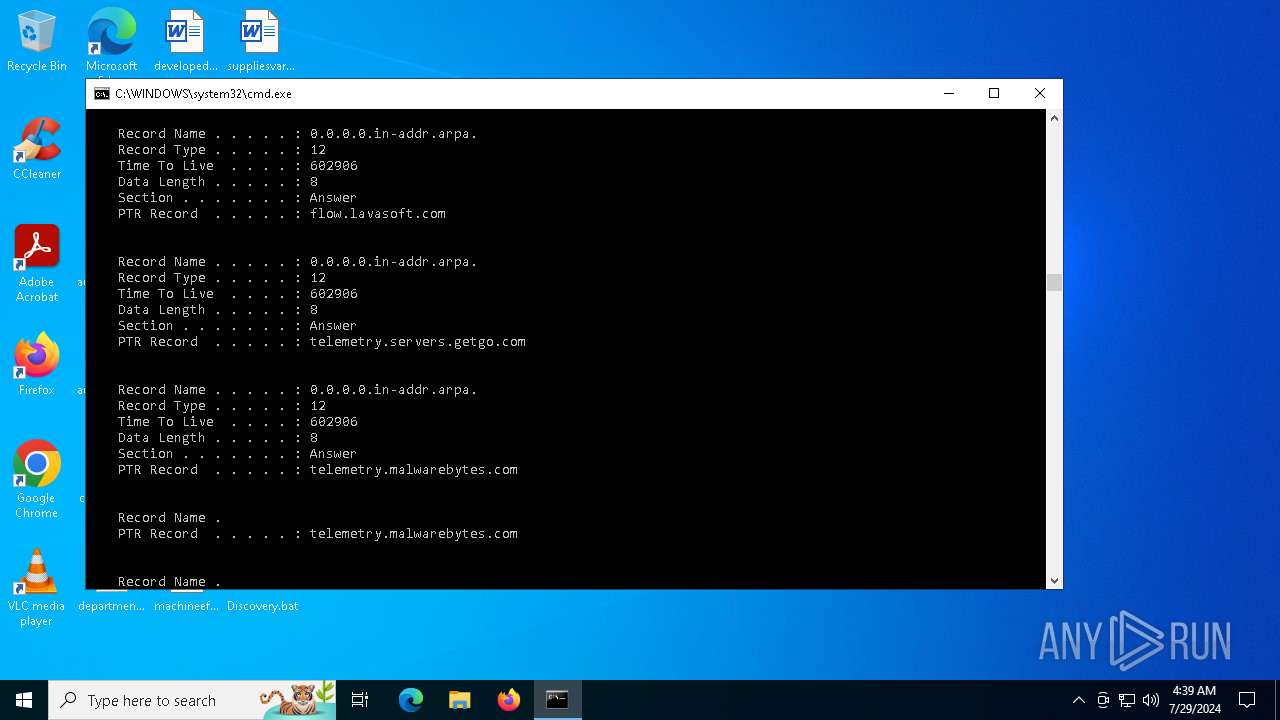
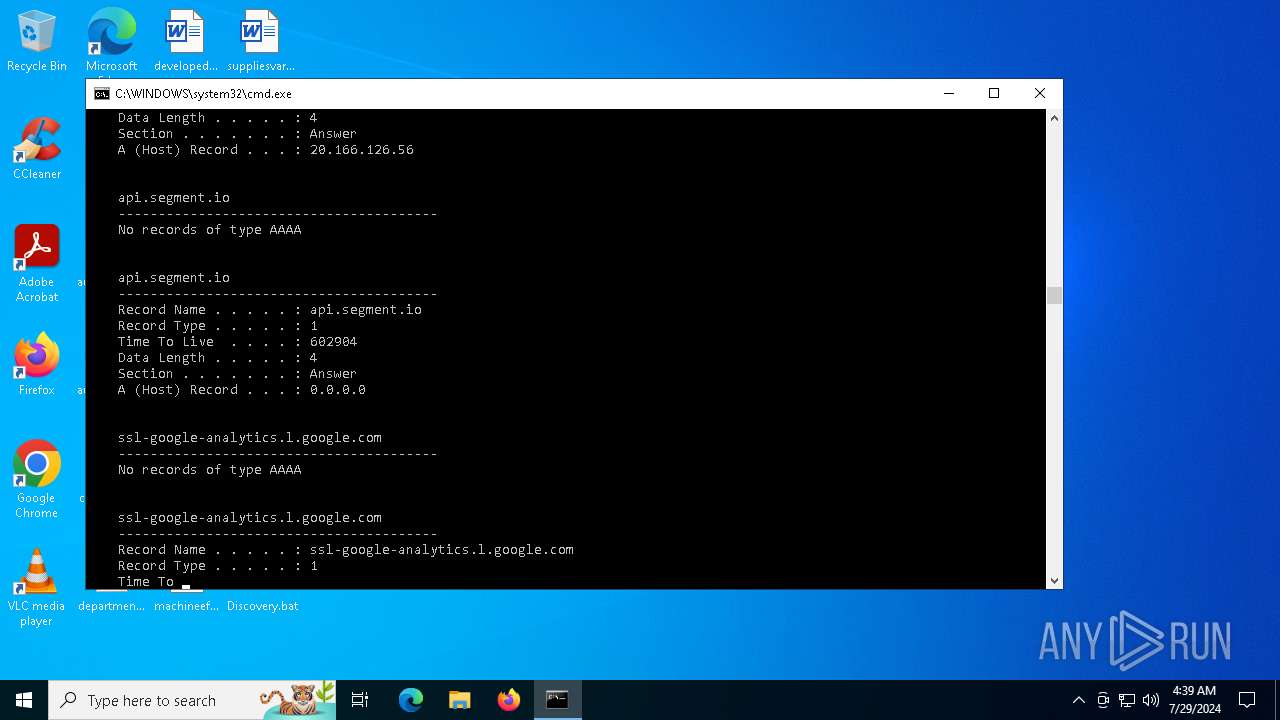
DNS requests
Domain | IP | Reputation |
|---|---|---|
t-ring-fdv2.msedge.net |
| unknown |
a-ring-fallback.msedge.net |
| unknown |
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
fp-afd-nocache-ccp.azureedge.net |
| whitelisted |
client.wns.windows.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |