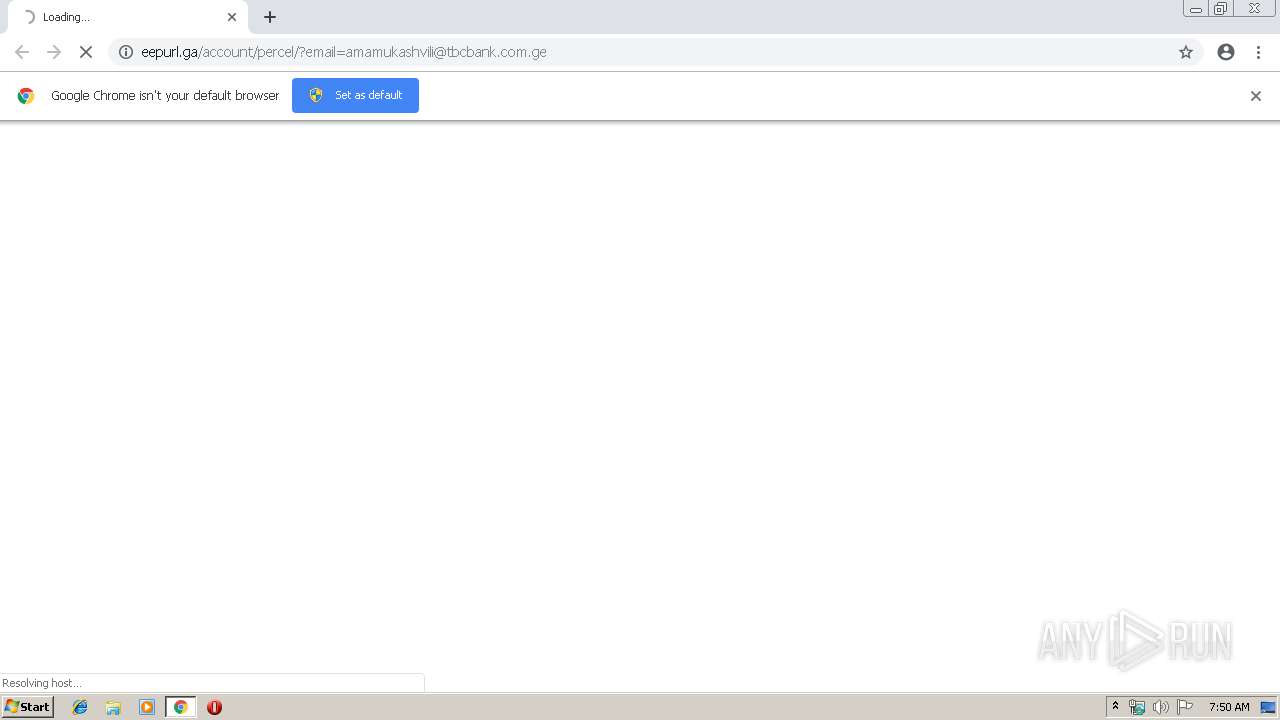
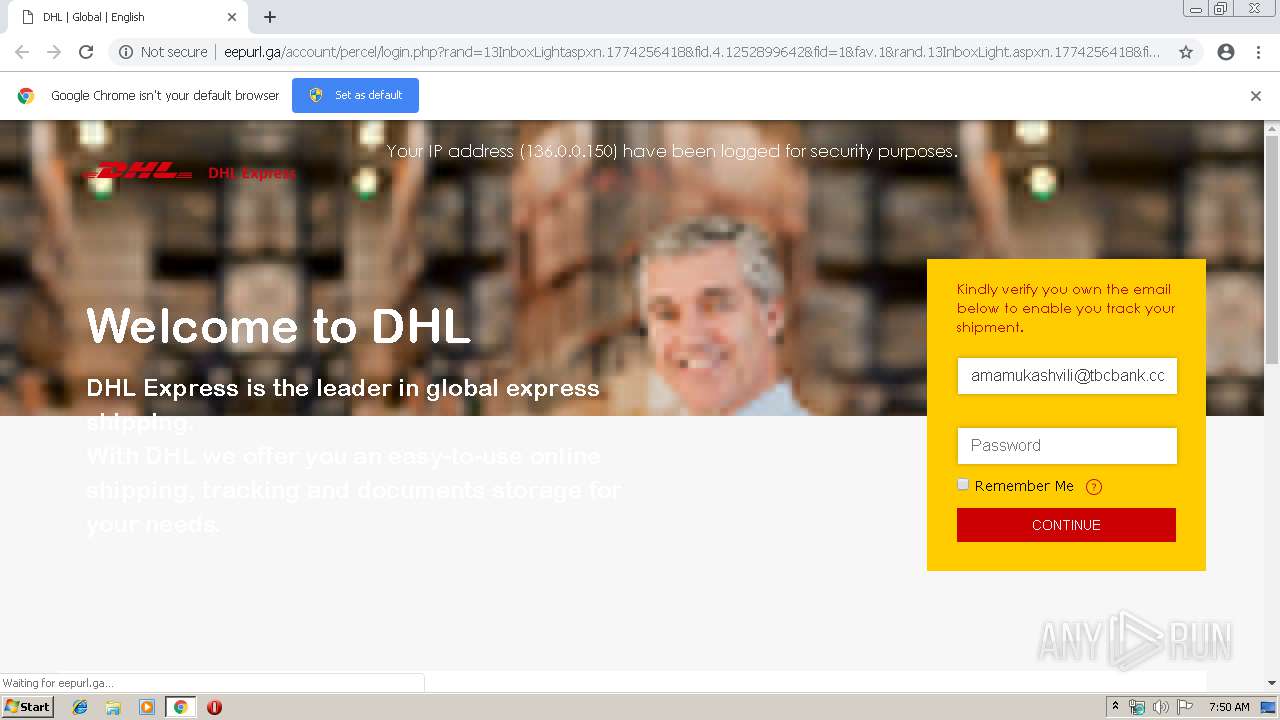
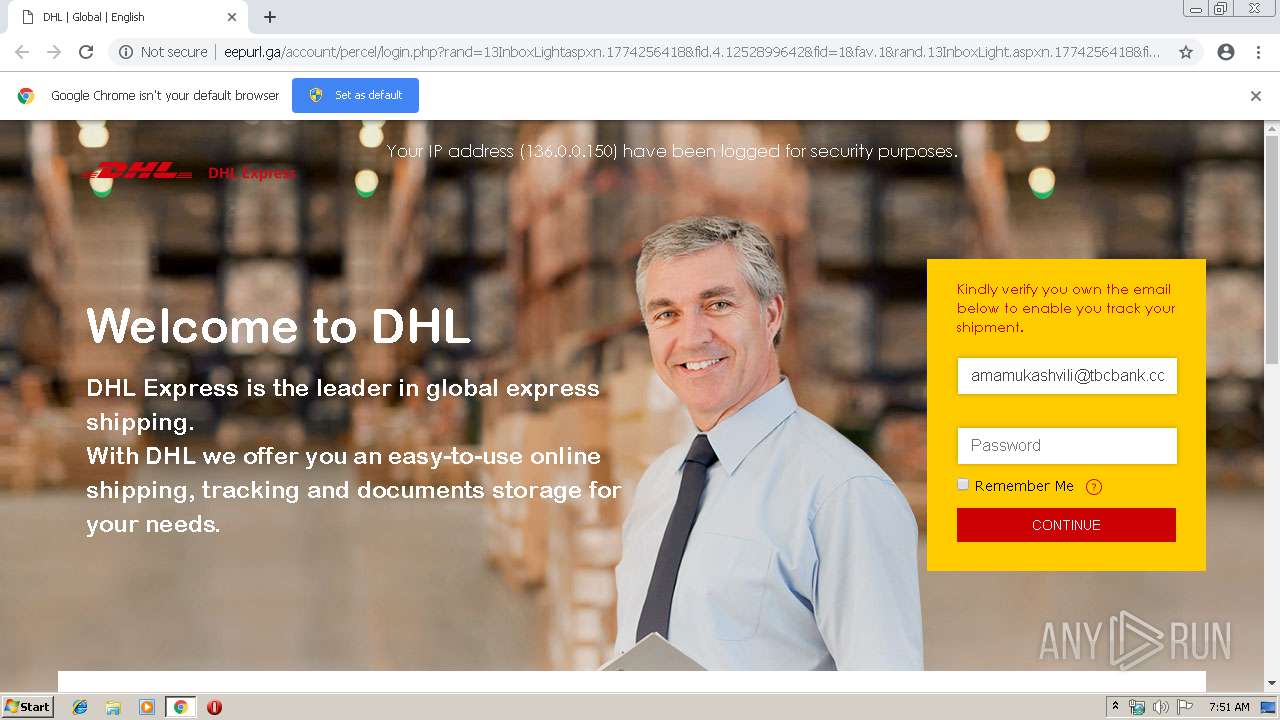
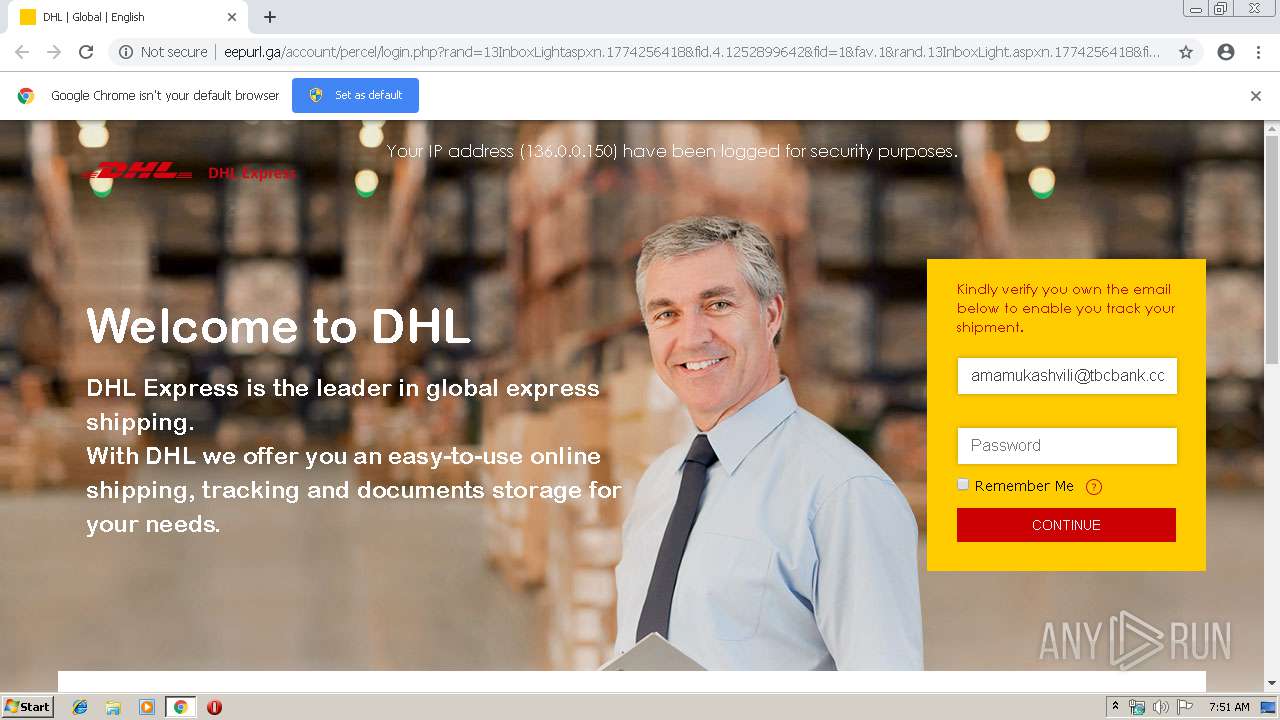
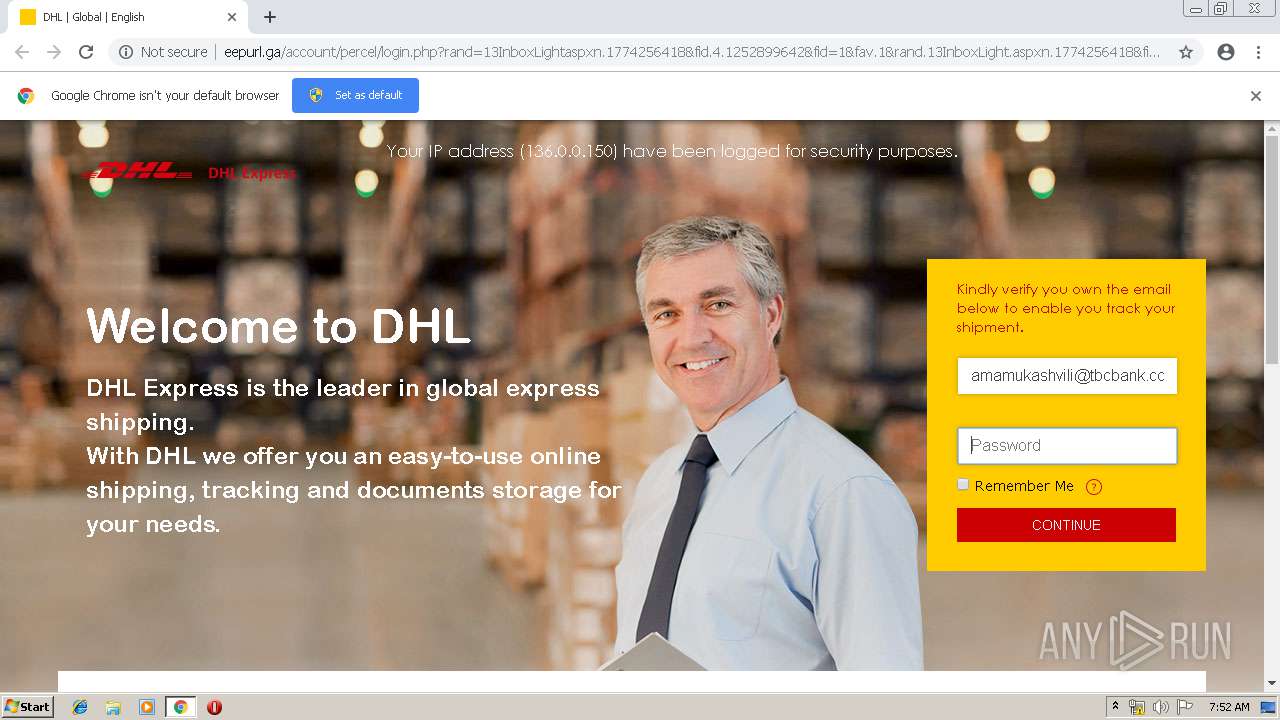
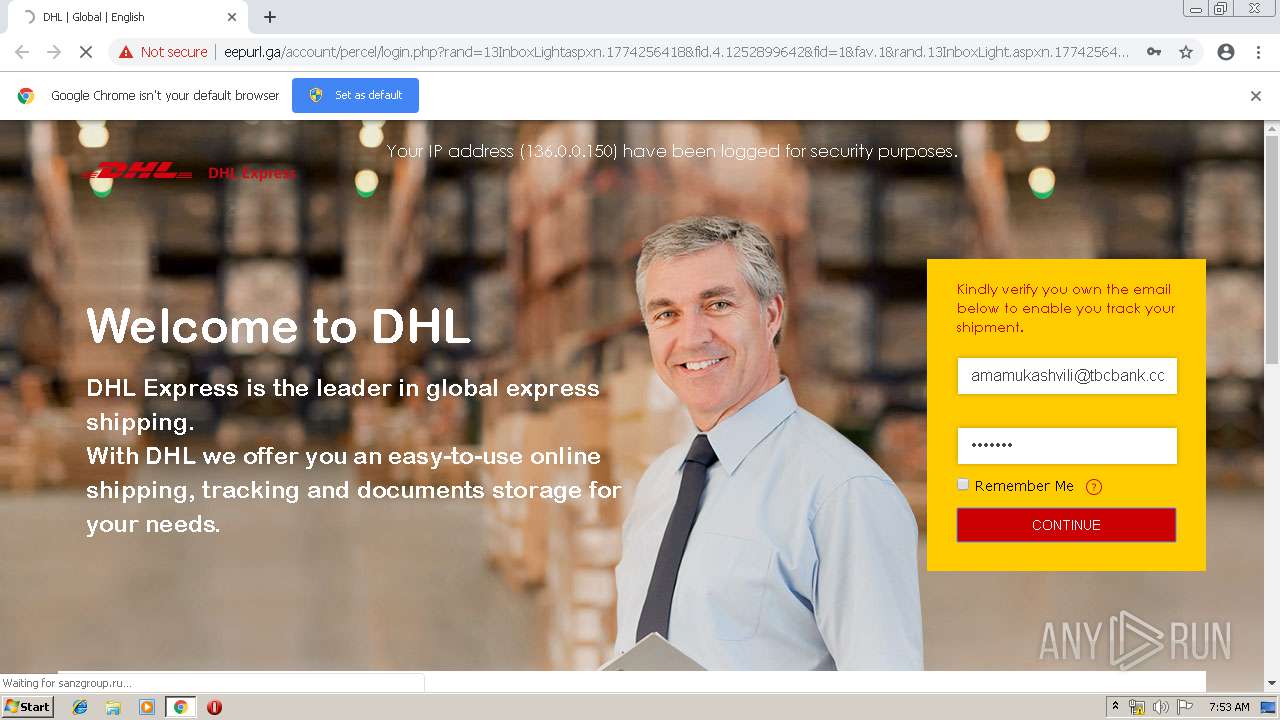
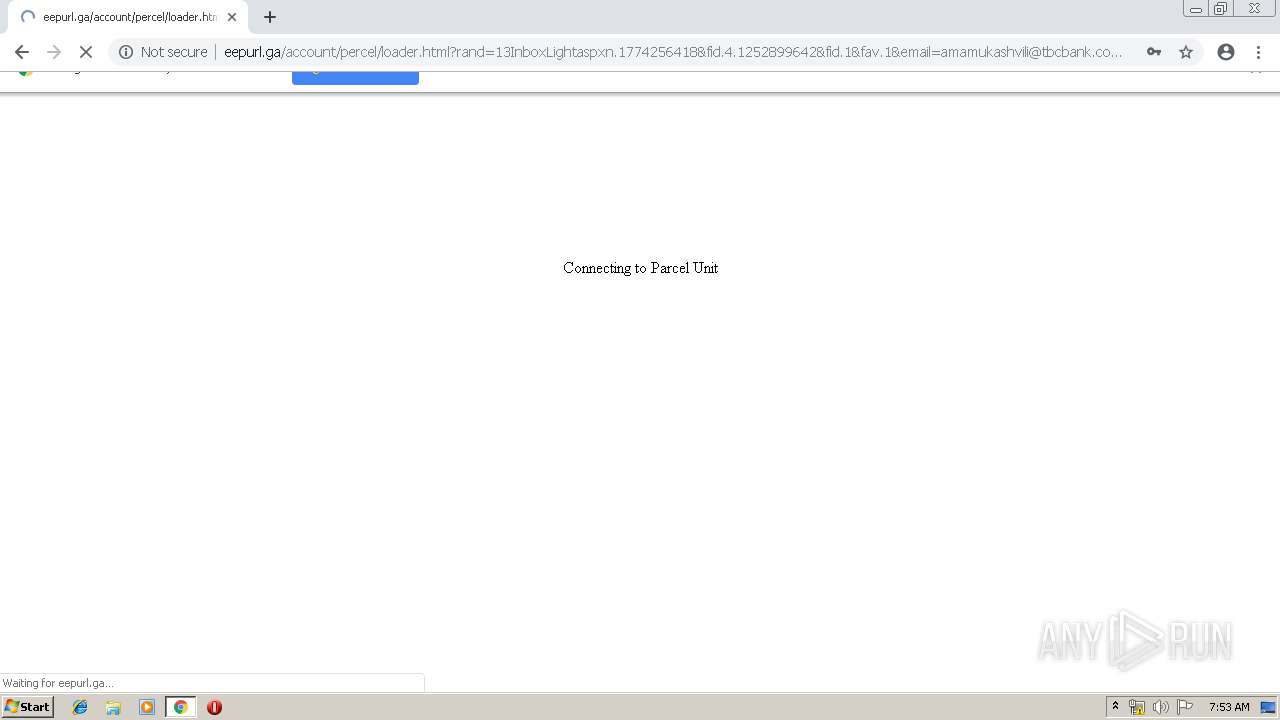
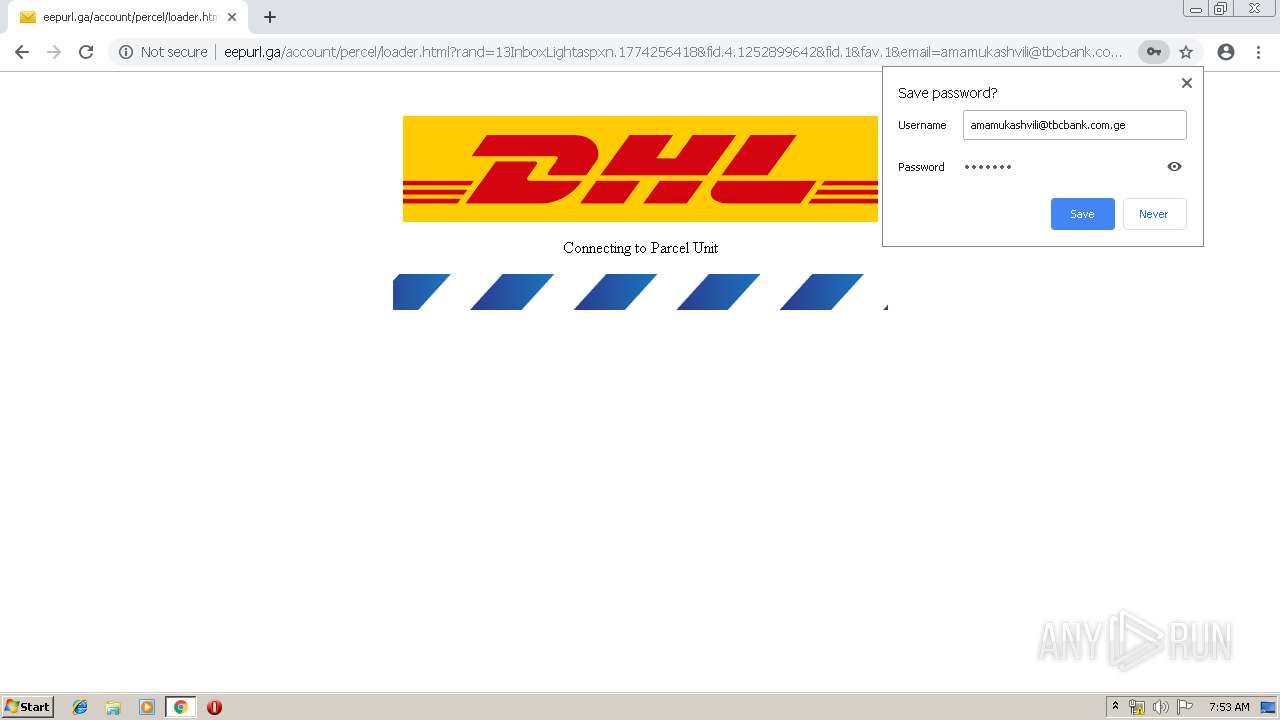
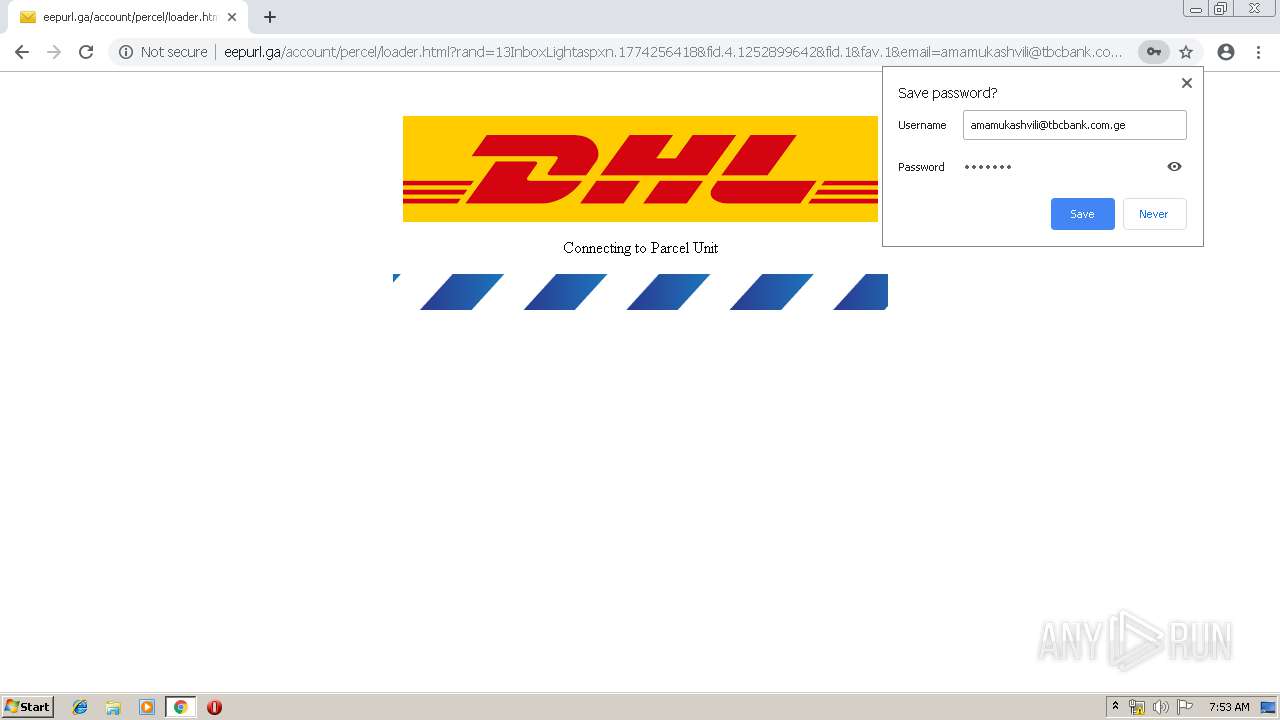
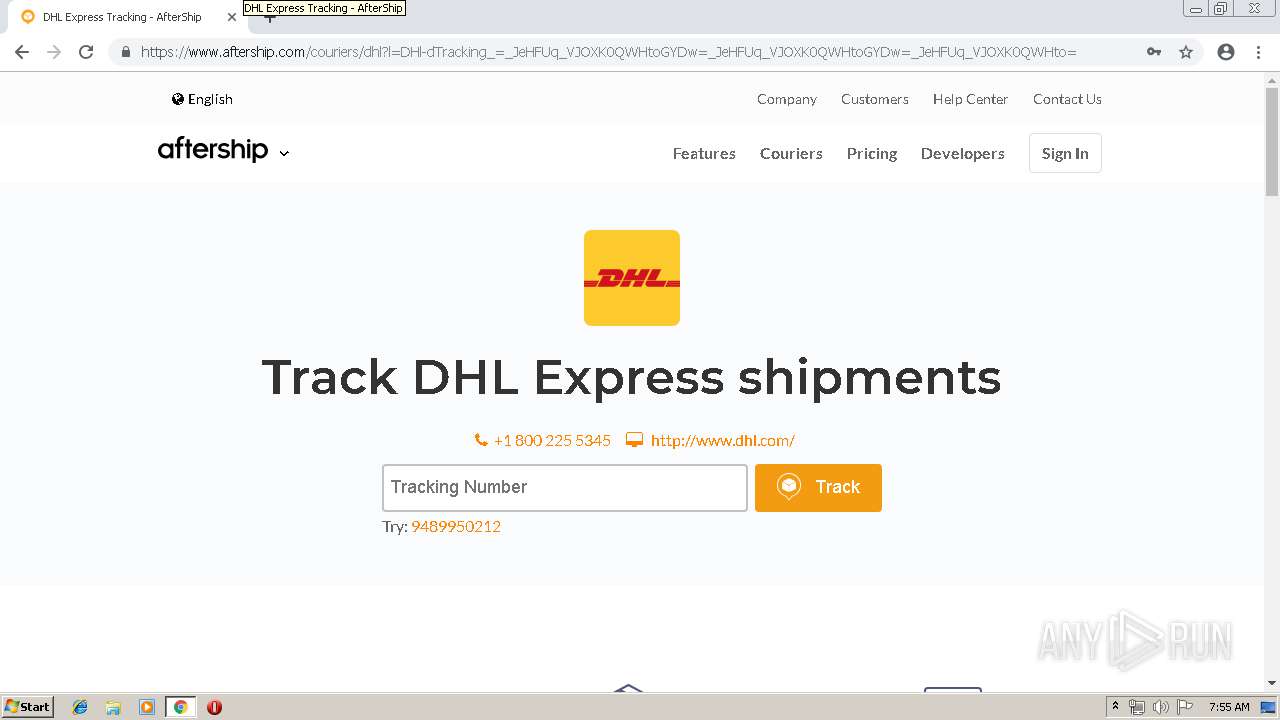
| URL: | http://eepurl.ga/account/percel/?email=amamukashvili@tbcbank.com.ge |
| Full analysis: | https://app.any.run/tasks/7a04e4a7-b6c1-4f30-9978-980475d7dac1 |
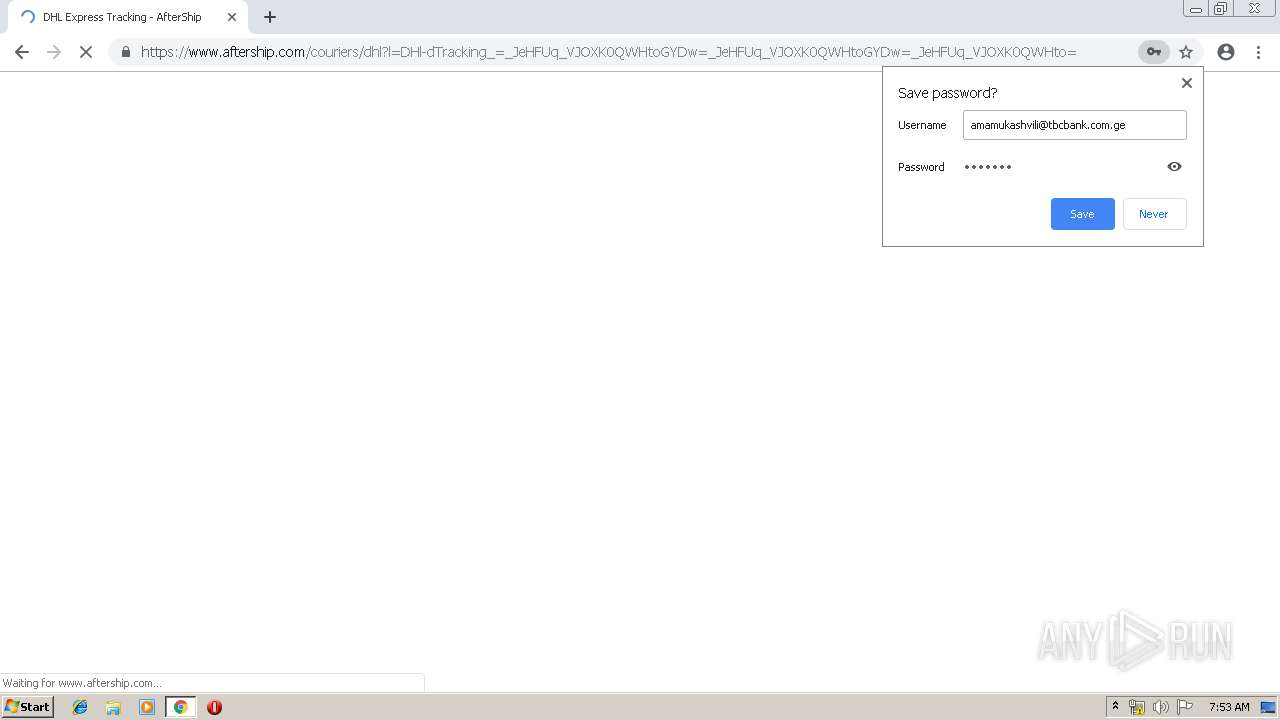
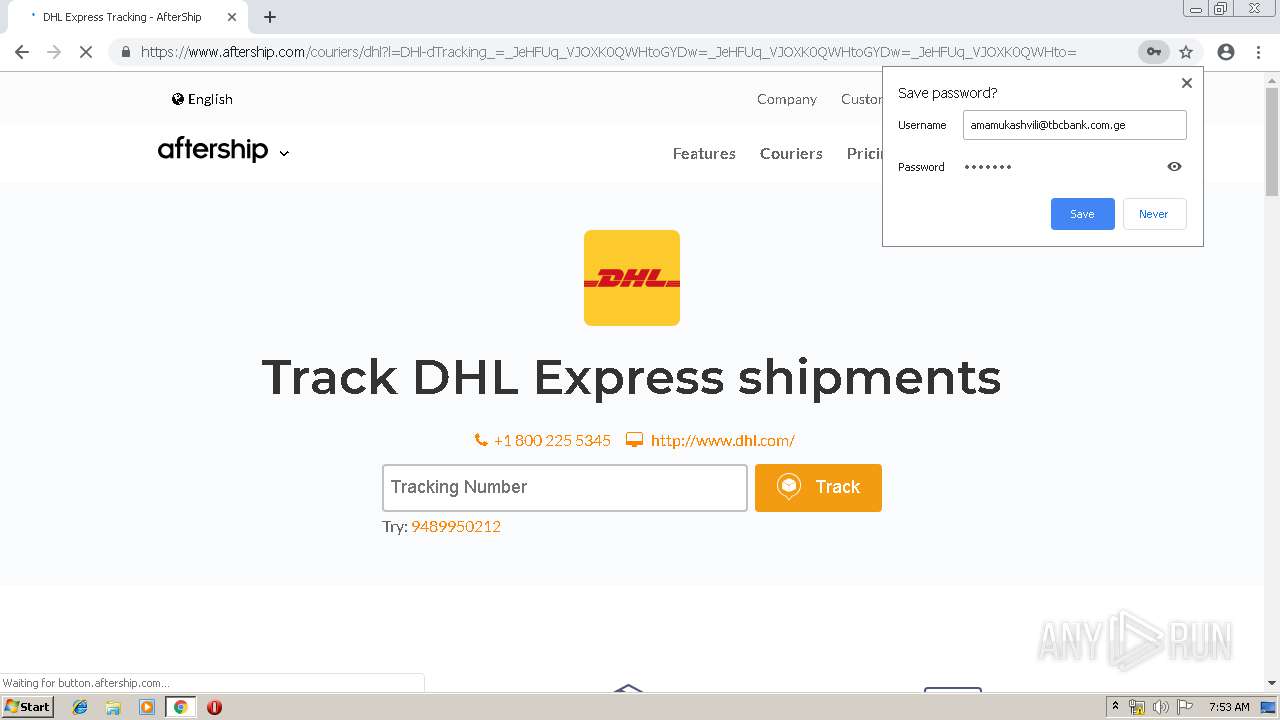
| Verdict: | Malicious activity |
| Analysis date: | March 21, 2019, 07:50:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 94DF671999D83D40E36C45B1E24B1A66 |
| SHA1: | 35E722F99C4BF3F92D3372BFAE6D3FF7B8C2C980 |
| SHA256: | B9427E01AEB44F6BB775AA1437D0B7035DE0C365A9558710D9F3434FBE7AFA33 |
| SSDEEP: | 3:N1KbajEx39JpXCBIYwEgQCA:Ce4VrcgQD |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2384)
INFO
Application launched itself
- chrome.exe (PID: 2384)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2384)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
48
Monitored processes
19
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 560 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,6907526002362335447,9360612466800495537,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2833037803134775076 --mojo-platform-channel-handle=3160 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,6907526002362335447,9360612466800495537,131072 --enable-features=PasswordImport --service-pipe-token=11869023512236525713 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11869023512236525713 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2028 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,6907526002362335447,9360612466800495537,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=10050271949424713765 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10050271949424713765 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1888 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2388 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,6907526002362335447,9360612466800495537,131072 --enable-features=PasswordImport --service-pipe-token=7192034131873126549 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7192034131873126549 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2020 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2100 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,6907526002362335447,9360612466800495537,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2015744647669879216 --mojo-platform-channel-handle=3152 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2176 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,6907526002362335447,9360612466800495537,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9231970388999678073 --mojo-platform-channel-handle=3284 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2384 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://eepurl.ga/account/percel/?email=amamukashvili@tbcbank.com.ge | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,6907526002362335447,9360612466800495537,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=3838438260037387969 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3838438260037387969 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2240 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,6907526002362335447,9360612466800495537,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15316604874316880429 --mojo-platform-channel-handle=3456 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
576
Read events
474
Write events
97
Delete events
5
Modification events
| (PID) Process: | (2384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1940) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2384-13197628253475375 |
Value: 259 | |||
| (PID) Process: | (2384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2384) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
103
Text files
158
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\67e578f2-2e6c-43fe-b065-4b304aa34f8a.tmp | — | |
MD5:— | SHA256:— | |||
| 2384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
71
DNS requests
36
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3308 | chrome.exe | GET | — | 185.144.30.215:80 | http://eepurl.ga/account/percel/Files/buttons.js | RU | — | — | malicious |
3308 | chrome.exe | GET | 302 | 185.144.30.215:80 | http://eepurl.ga/account/percel/?email=amamukashvili@tbcbank.com.ge | RU | — | — | malicious |
3308 | chrome.exe | GET | — | 185.144.30.215:80 | http://eepurl.ga/account/percel/Files/ga.js | RU | — | — | malicious |
3308 | chrome.exe | GET | — | 185.144.30.215:80 | http://eepurl.ga/account/percel/Files/jquery.js | RU | — | — | malicious |
3308 | chrome.exe | GET | 200 | 68.232.35.182:80 | http://fast.fonts.net/t/1.css?apiType=css&projectid=a3f6fe50-744f-4123-952d-600048fa8a7c | US | — | — | whitelisted |
3308 | chrome.exe | GET | — | 185.144.30.215:80 | http://eepurl.ga/account/percel/images/icon-arrow-close.png | RU | — | — | malicious |
3308 | chrome.exe | GET | — | 185.144.30.215:80 | http://eepurl.ga/account/percel/images/bg-header.png | RU | — | — | malicious |
3308 | chrome.exe | GET | — | 185.144.30.215:80 | http://eepurl.ga/account/percel/Files/jquery.js | RU | — | — | malicious |
3308 | chrome.exe | GET | 200 | 185.144.30.215:80 | http://eepurl.ga/account/percel/Files/mydhl_benefit_1.png | RU | image | 5.13 Kb | malicious |
3308 | chrome.exe | GET | 200 | 185.144.30.215:80 | http://eepurl.ga/account/percel/Files/mydhl_benefit_3.png | RU | image | 6.36 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3308 | chrome.exe | 172.217.18.109:443 | accounts.google.com | Google Inc. | US | suspicious |
3308 | chrome.exe | 68.232.35.182:80 | fast.fonts.net | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3308 | chrome.exe | 23.5.106.24:443 | www.mydhl.dhl.com | Akamai Technologies, Inc. | NL | whitelisted |
3308 | chrome.exe | 172.217.22.46:443 | clients1.google.com | Google Inc. | US | whitelisted |
3308 | chrome.exe | 185.144.30.215:80 | eepurl.ga | Chelyabinsk-Signal LLC | RU | suspicious |
3308 | chrome.exe | 216.58.208.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3308 | chrome.exe | 156.137.1.33:443 | sso.dhl-usa.com | DHL Information Services (Europe) s.r.o | US | unknown |
3308 | chrome.exe | 216.58.210.14:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3308 | chrome.exe | 172.217.23.142:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
3308 | chrome.exe | 216.58.207.67:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
eepurl.ga |
| malicious |
accounts.google.com |
| shared |
fast.fonts.net |
| whitelisted |
www.mydhl.dhl.com |
| unknown |
www.google-analytics.com |
| whitelisted |
agricultureinkenya.com |
| suspicious |
clients1.google.com |
| whitelisted |
sso.dhl-usa.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1072 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .ga Domain |
3308 | chrome.exe | A Network Trojan was detected | MALWARE [PTsecurity] Adobe PDF Phishing Landing |
3308 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
3308 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
2 ETPRO signatures available at the full report