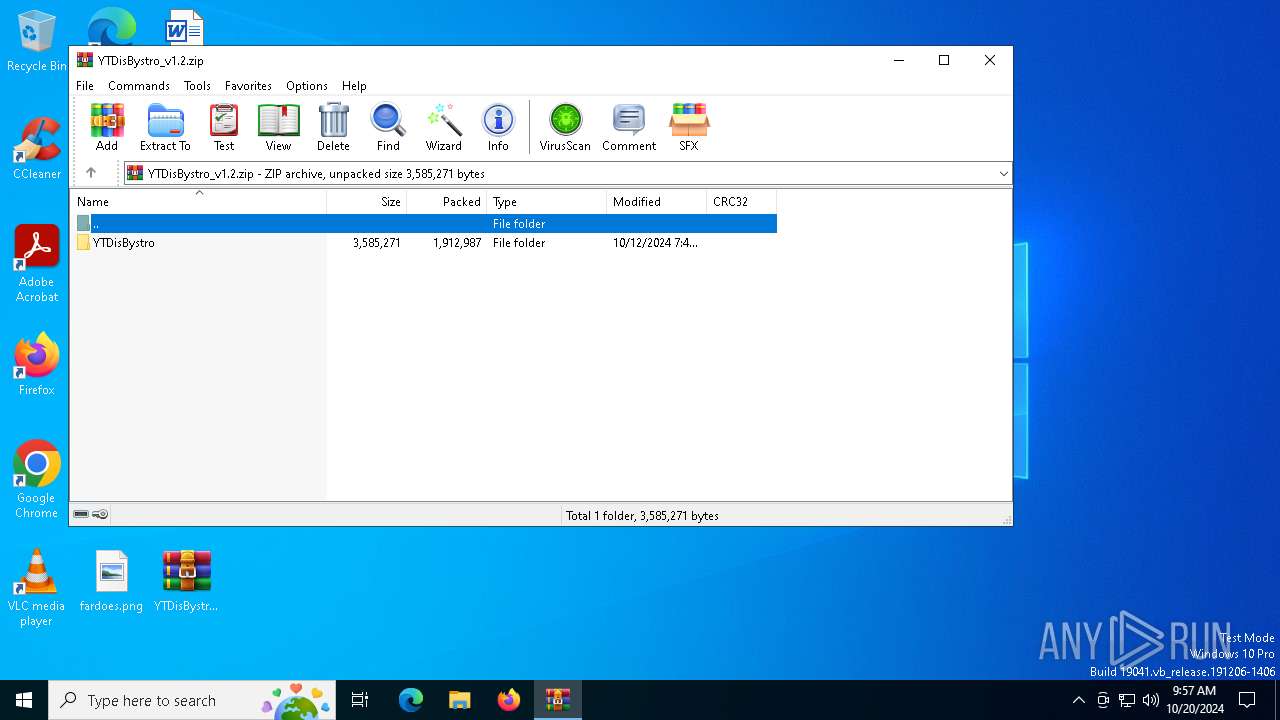
| File name: | YTDisBystro_v1.2.zip |
| Full analysis: | https://app.any.run/tasks/01eacaac-87b8-4509-9238-1e477edc2c0f |
| Verdict: | Malicious activity |
| Analysis date: | October 20, 2024, 09:57:13 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | AF812DC3B3741DDBB55E412EB99A818C |
| SHA1: | 607CA3C896477FA05A0EB23A1D2E96A1FB7183D9 |
| SHA256: | B93A22CB2AB73E6727DE825E1EA0C36182F2B2D8679BAB5D281855E4F44E44B1 |
| SSDEEP: | 98304:ALr7W8jxWdsXYq5CvRR0owqvpAGv+iK3bLyuul5HjZ4Q50OrIby0YdvGgm5QEKjA:A3 |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 4408)
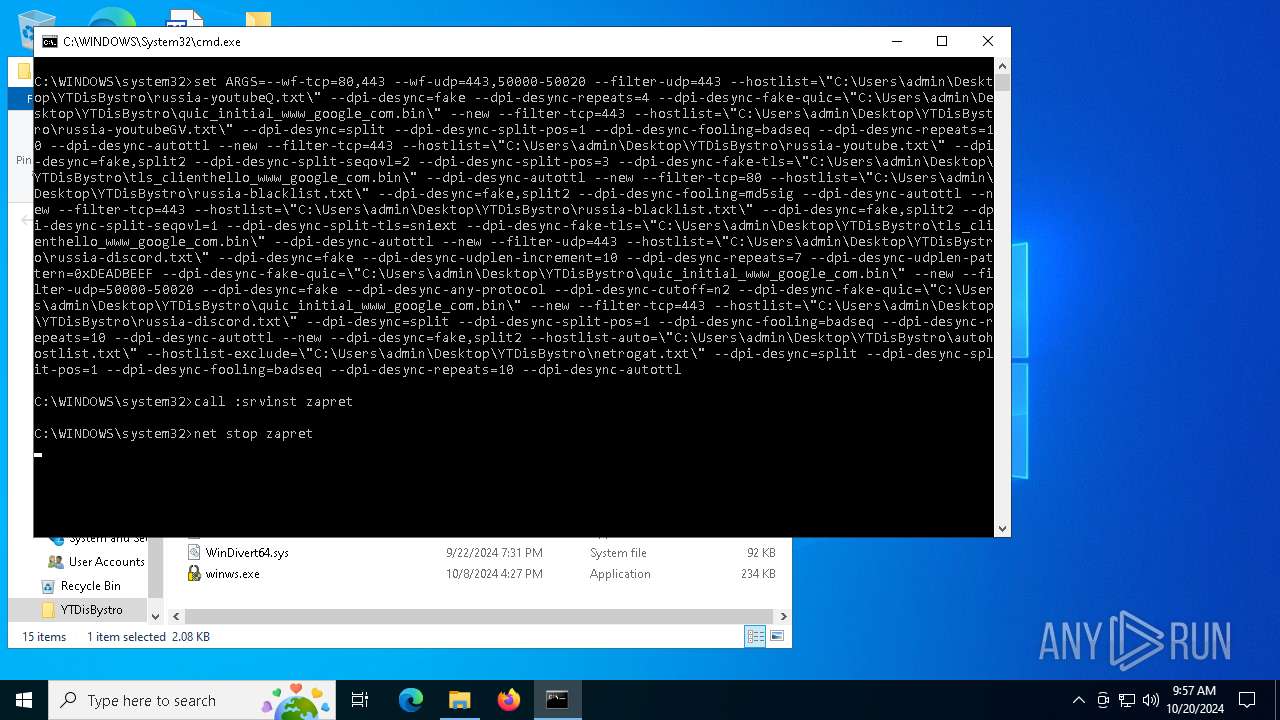
Starts NET.EXE for service management
- cmd.exe (PID: 5792)
- net.exe (PID: 5068)
Detects Cygwin installation
- WinRAR.exe (PID: 5220)
SUSPICIOUS
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 5220)
Starts SC.EXE for service management
- cmd.exe (PID: 5792)
Executes as Windows Service
- winws.exe (PID: 7116)
INFO
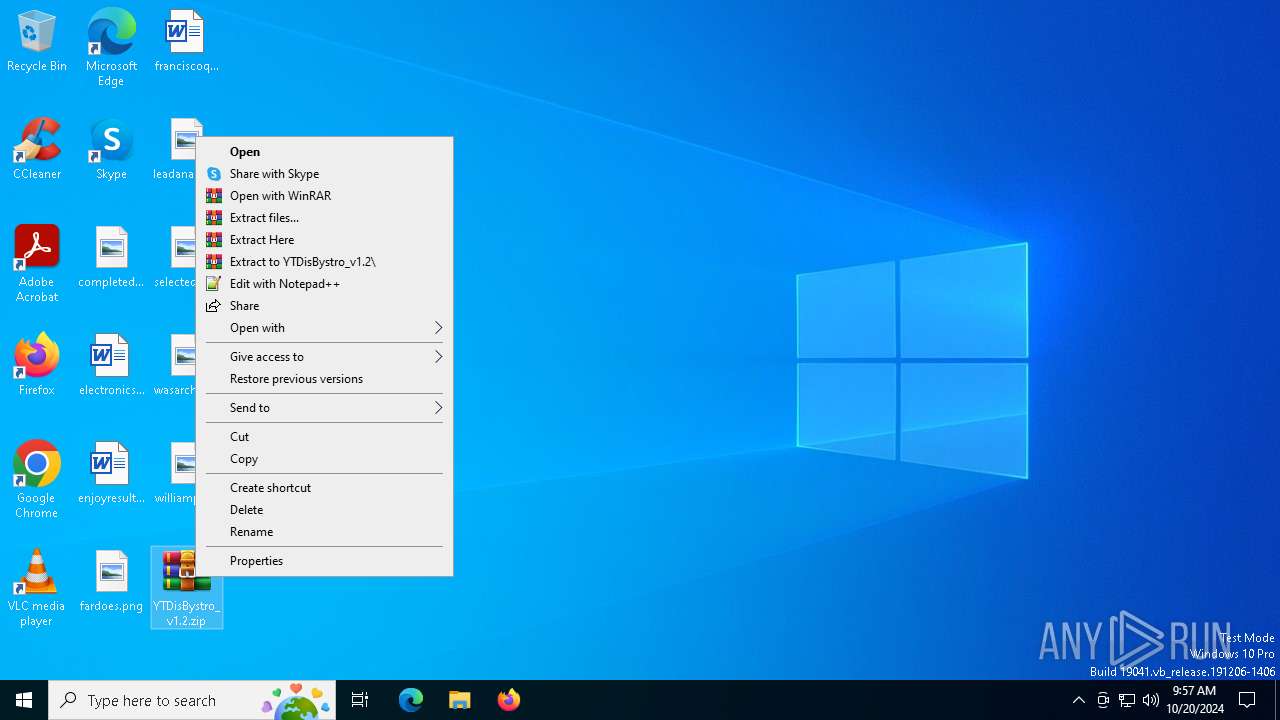
Manual execution by a user
- WinRAR.exe (PID: 5220)
- cmd.exe (PID: 5792)
The process uses the downloaded file
- WinRAR.exe (PID: 5220)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5220)
UPX packer has been detected
- winws.exe (PID: 7116)
Reads the computer name
- winws.exe (PID: 7116)
Checks supported languages
- winws.exe (PID: 7116)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xpi | | | Mozilla Firefox browser extension (66.6) |
|---|---|---|
| .zip | | | ZIP compressed archive (33.3) |
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:10:12 22:41:52 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | YTDisBystro/ |
Total processes
140
Monitored processes
12
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 204 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 696 | sc delete zapret | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 860 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3028 | C:\WINDOWS\system32\net1 stop zapret | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3836 | sc description zapret "Zapret DPI bypass software" | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4408 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\YTDisBystro_v1.2.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 4464 | sc start zapret | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5068 | net stop zapret | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
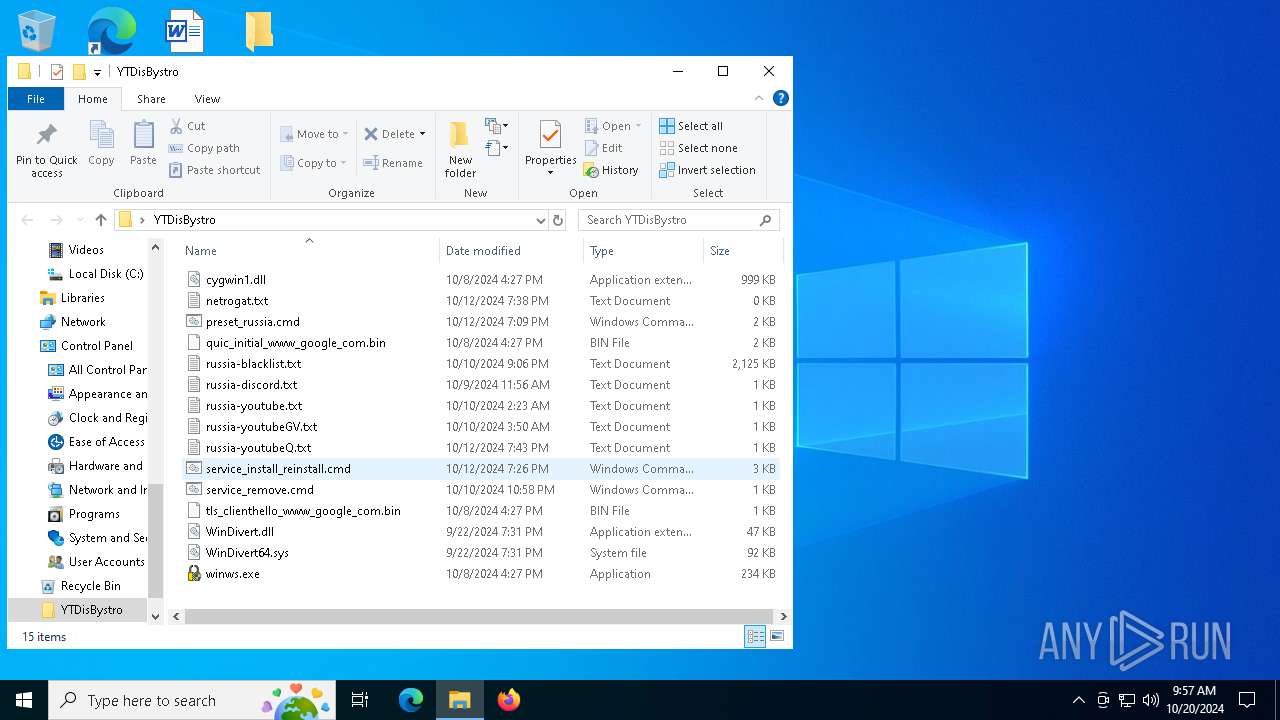
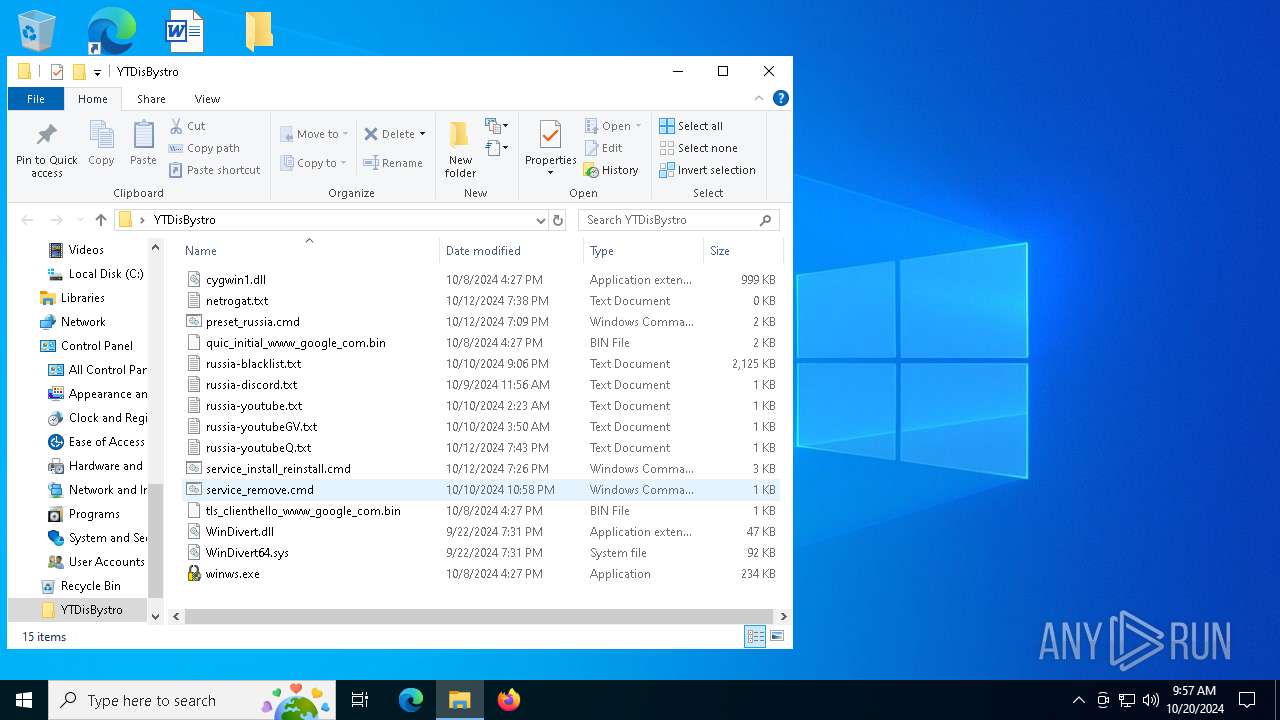
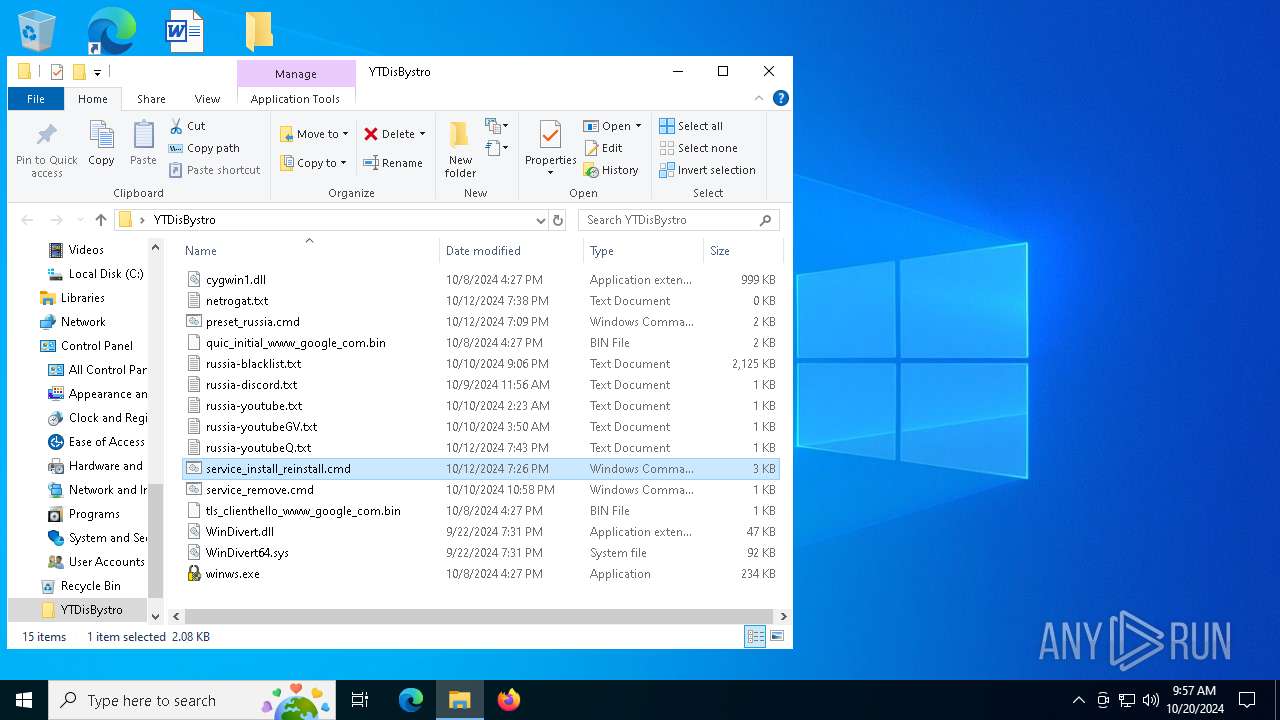
| 5220 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\YTDisBystro_v1.2.zip" C:\Users\admin\Desktop\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
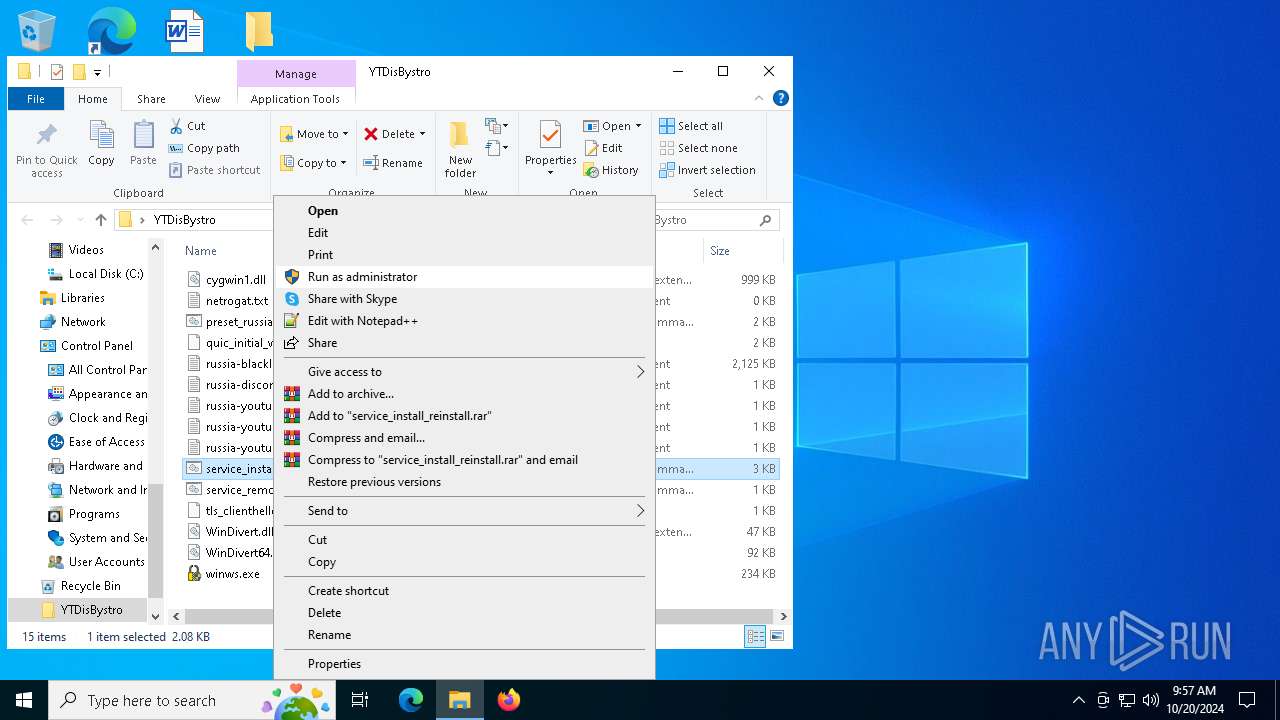
| 5792 | "C:\WINDOWS\System32\cmd.exe" /C "C:\Users\admin\Desktop\YTDisBystro\service_install_reinstall.cmd" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 542
Read events
1 519
Write events
23
Delete events
0
Modification events
| (PID) Process: | (4408) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (4408) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\YTDisBystro_v1.2.zip | |||
| (PID) Process: | (4408) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4408) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4408) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4408) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4408) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (4408) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
| (PID) Process: | (4408) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4408) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | psize |
Value: 80 | |||
Executable files
4
Suspicious files
2
Text files
8
Unknown types
0
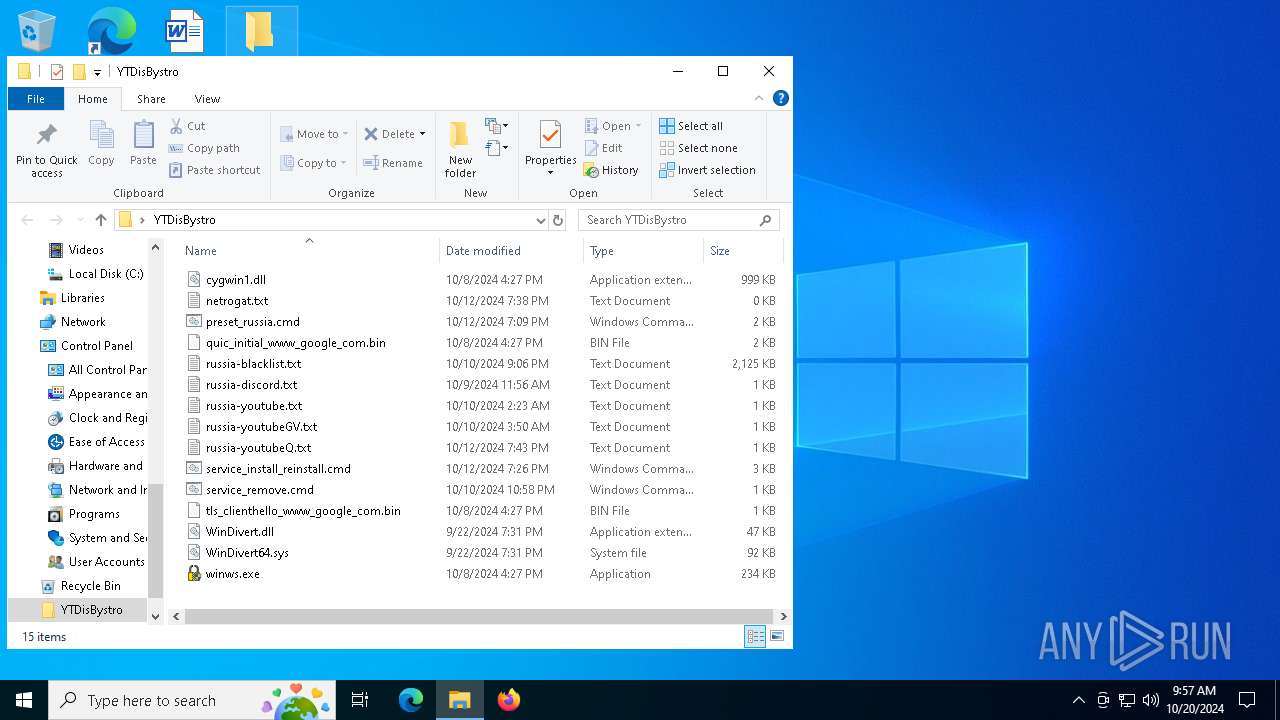
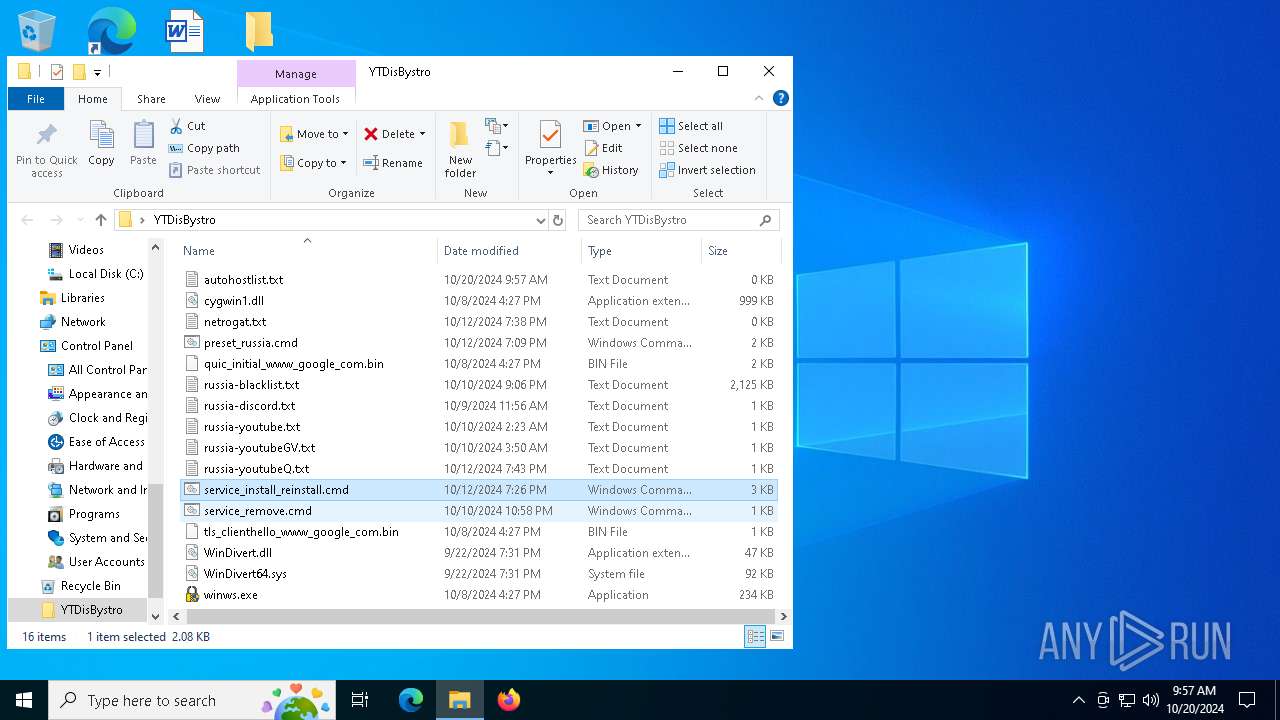
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
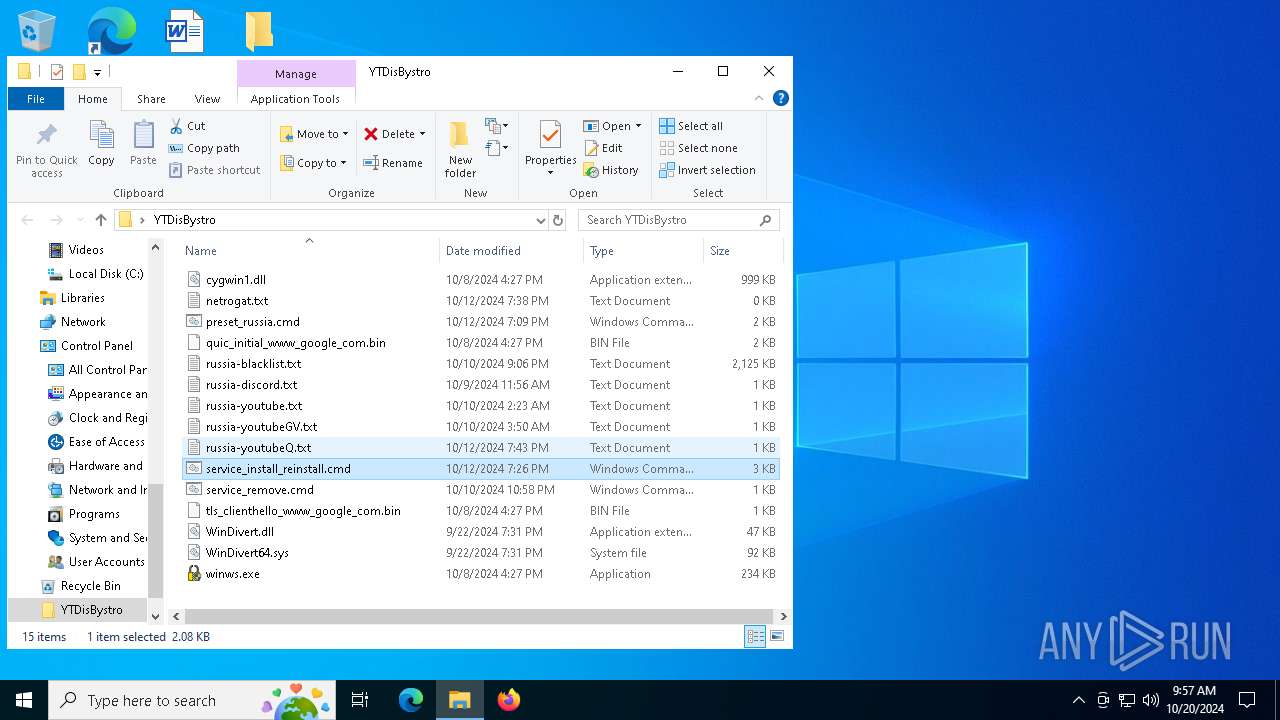
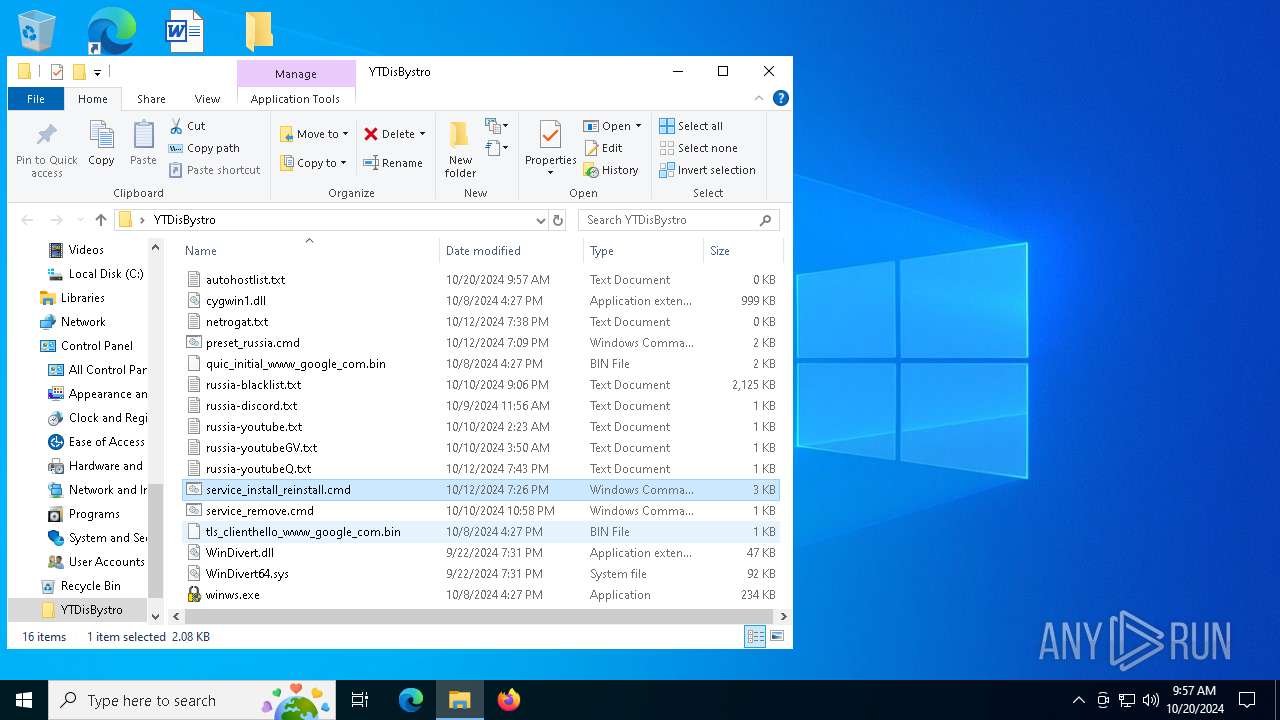
| 5220 | WinRAR.exe | C:\Users\admin\Desktop\YTDisBystro\preset_russia.cmd | text | |
MD5:007085CC6256E662E350D133465AE62C | SHA256:B5C17D2C48CCD0E8E4B88358529BE7BBE86C3DC1BAC329A30761AAB72A3FEA18 | |||
| 5220 | WinRAR.exe | C:\Users\admin\Desktop\YTDisBystro\russia-youtubeGV.txt | text | |
MD5:26AE3D472B7EA155B5ED2A283C6F272A | SHA256:B273DA098B1819FE0CD9EEF6C8AA67D649D1DCE0376687B87B1358460A9D6D0E | |||
| 5220 | WinRAR.exe | C:\Users\admin\Desktop\YTDisBystro\WinDivert.dll | executable | |
MD5:B2014D33EE645112D5DC16FE9D9FCBFF | SHA256:C1E060EE19444A259B2162F8AF0F3FE8C4428A1C6F694DCE20DE194AC8D7D9A2 | |||
| 5220 | WinRAR.exe | C:\Users\admin\Desktop\YTDisBystro\tls_clienthello_www_google_com.bin | binary | |
MD5:7AB7AD857C5B8794FBDF1091B494DC94 | SHA256:E5938780152169F720383F80EABB309E9477369B83B5EC40CC137C397F862CDE | |||
| 5220 | WinRAR.exe | C:\Users\admin\Desktop\YTDisBystro\quic_initial_www_google_com.bin | binary | |
MD5:312526D39958D89B1F8AB67789AB985F | SHA256:F4589C57749F956BB30538197A521D7005F8B0A8723B4707E72405E51DDAC50A | |||
| 5220 | WinRAR.exe | C:\Users\admin\Desktop\YTDisBystro\winws.exe | executable | |
MD5:8C624E64742BC19447D52F61EDEC52DB | SHA256:13FD7A9C6F7C98239A61A212F69211A0F19159B2E8CDAE8B1EFC57D35CDCD5AD | |||
| 5220 | WinRAR.exe | C:\Users\admin\Desktop\YTDisBystro\WinDivert64.sys | executable | |
MD5:89ED5BE7EA83C01D0DE33D3519944AA5 | SHA256:8DA085332782708D8767BCACE5327A6EC7283C17CFB85E40B03CD2323A90DDC2 | |||
| 5220 | WinRAR.exe | C:\Users\admin\Desktop\YTDisBystro\russia-blacklist.txt | text | |
MD5:AAA4A3FA782DF525B220AC750B6D8535 | SHA256:37D88B634CEC8BCE81A41F365A620159D221B7187E73E3EEB9FC749E827F1ED7 | |||
| 5220 | WinRAR.exe | C:\Users\admin\Desktop\YTDisBystro\cygwin1.dll | executable | |
MD5:C50B50303FAE4AFE7248307339A00D13 | SHA256:712C39A069541AFA69CFCBE01B422BD67B4201EEE7E94CC1327D4ED8B4FA2167 | |||
| 5220 | WinRAR.exe | C:\Users\admin\Desktop\YTDisBystro\russia-discord.txt | text | |
MD5:09F90DED3F579338996DFCB119A58408 | SHA256:F32AEE579D9499A9F5ACEA2F635F5024175FD19699BC6A9F5DAF5BF8D0650321 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report