| File name: | WinSSHDownloadInstaller_2_12_0.exe |
| Full analysis: | https://app.any.run/tasks/4f880083-77d0-49a4-9628-9ba74e7f615e |
| Verdict: | Malicious activity |
| Analysis date: | October 17, 2023, 21:40:10 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 6A44E0118363F0A6CAD8D80DA8A34010 |
| SHA1: | F86C767984F3B07D76A36B0EFF17EC75BD980BAC |
| SHA256: | B92C94B0FD1DED58932DC3A424CCF6B13B453E364C25AD23FF8CA65321D40314 |
| SSDEEP: | 393216:AzVM8+ih5ELOyBuu57tIOFT+NtlXm10pvi/HhOD0suCVZL:ABJh0jpUPU5Wdb |
MALICIOUS
Drops the executable file immediately after the start
- WinSSHDownloadInstaller_2_12_0.exe (PID: 1596)
- WinSshBootstrapper.exe (PID: 3292)
- WinSSHDownloadInstaller.exe (PID: 3804)
- SSHDownloadInstaller.exe (PID: 6788)
- SSHDownloadInstaller.exe (PID: 3864)
- vc_redist.x86.exe (PID: 2472)
- vcredist_x86.exe (PID: 6372)
- vcredist_x86.exe (PID: 1728)
- msiexec.exe (PID: 1040)
Application was dropped or rewritten from another process
- OrganizerReg.exe (PID: 3140)
- ISBEW64.exe (PID: 1152)
- ISBEW64.exe (PID: 4052)
- ISBEW64.exe (PID: 5236)
- ISBEW64.exe (PID: 5288)
- ISBEW64.exe (PID: 1732)
- ISBEW64.exe (PID: 3536)
- ISBEW64.exe (PID: 4056)
- ISBEW64.exe (PID: 4528)
- ISBEW64.exe (PID: 4752)
- ISBEW64.exe (PID: 1516)
- SSHDownloadInstaller.exe (PID: 3864)
- ISBEW64.exe (PID: 6044)
- ISBEW64.exe (PID: 5820)
- GetAppdata.exe (PID: 7128)
- SSHDownloadInstaller.exe (PID: 6788)
- vcredist_x86.exe (PID: 6372)
- vcredist_x86.exe (PID: 1728)
- vc_redist.x86.exe (PID: 6980)
- vc_redist.x86.exe (PID: 2472)
Loads dropped or rewritten executable
- SSHDownloadInstaller.exe (PID: 3864)
- WinSshBootstrapper.exe (PID: 3292)
- SSHDownloadInstaller.exe (PID: 6788)
- vcredist_x86.exe (PID: 6372)
- vc_redist.x86.exe (PID: 2472)
Creates a writable file the system directory
- msiexec.exe (PID: 1040)
SUSPICIOUS
Reads the Windows owner or organization settings
- WinSshBootstrapper.exe (PID: 3292)
- SSHDownloadInstaller.exe (PID: 3864)
- msiexec.exe (PID: 1040)
Reads the date of Windows installation
- WinSshBootstrapper.exe (PID: 3292)
Executes as Windows Service
- VSSVC.exe (PID: 1868)
Searches for installed software
- dllhost.exe (PID: 2756)
- vc_redist.x86.exe (PID: 2472)
- vcredist_x86.exe (PID: 1728)
- vcredist_x86.exe (PID: 6372)
Process drops legitimate windows executable
- SSHDownloadInstaller.exe (PID: 3864)
- vc_redist.x86.exe (PID: 2472)
- vcredist_x86.exe (PID: 1728)
- vcredist_x86.exe (PID: 6372)
- msiexec.exe (PID: 1040)
Checks Windows Trust Settings
- SSHDownloadInstaller.exe (PID: 6788)
- msiexec.exe (PID: 1040)
- vcredist_x86.exe (PID: 1728)
Starts CMD.EXE for commands execution
- SSHDownloadInstaller.exe (PID: 6788)
Application launched itself
- vc_redist.x86.exe (PID: 6980)
- vcredist_x86.exe (PID: 1728)
Reads security settings of Internet Explorer
- SSHDownloadInstaller.exe (PID: 6788)
- vcredist_x86.exe (PID: 1728)
Creates a software uninstall entry
- vcredist_x86.exe (PID: 1728)
INFO
Reads the computer name
- WinSSHDownloadInstaller_2_12_0.exe (PID: 1596)
- ISBEW64.exe (PID: 1732)
- WinSshBootstrapper.exe (PID: 3292)
- ISBEW64.exe (PID: 5288)
- OrganizerReg.exe (PID: 3140)
- WinSSHDownloadInstaller.exe (PID: 3804)
- SSHDownloadInstaller.exe (PID: 3864)
- ISBEW64.exe (PID: 4056)
- ISBEW64.exe (PID: 4528)
- ISBEW64.exe (PID: 4752)
- ISBEW64.exe (PID: 6044)
- ISBEW64.exe (PID: 1516)
- ISBEW64.exe (PID: 5820)
- SSHDownloadInstaller.exe (PID: 6788)
- ISBEW64.exe (PID: 4052)
- ISBEW64.exe (PID: 3536)
- ISBEW64.exe (PID: 5236)
- ISBEW64.exe (PID: 1152)
- vc_redist.x86.exe (PID: 6980)
- vc_redist.x86.exe (PID: 2472)
- vcredist_x86.exe (PID: 1728)
- vcredist_x86.exe (PID: 6372)
- msiexec.exe (PID: 1040)
- ShellExperienceHost.exe (PID: 3352)
Checks supported languages
- ISBEW64.exe (PID: 1152)
- ISBEW64.exe (PID: 1732)
- WinSSHDownloadInstaller_2_12_0.exe (PID: 1596)
- WinSshBootstrapper.exe (PID: 3292)
- ISBEW64.exe (PID: 4052)
- ISBEW64.exe (PID: 5288)
- OrganizerReg.exe (PID: 3140)
- WinSSHDownloadInstaller.exe (PID: 3804)
- SSHDownloadInstaller.exe (PID: 3864)
- ISBEW64.exe (PID: 4752)
- ISBEW64.exe (PID: 4056)
- ISBEW64.exe (PID: 4528)
- ISBEW64.exe (PID: 1516)
- ISBEW64.exe (PID: 5820)
- ISBEW64.exe (PID: 6044)
- SSHDownloadInstaller.exe (PID: 6788)
- GetAppdata.exe (PID: 7128)
- vc_redist.x86.exe (PID: 6980)
- vc_redist.x86.exe (PID: 2472)
- ISBEW64.exe (PID: 3536)
- ISBEW64.exe (PID: 5236)
- vcredist_x86.exe (PID: 6372)
- vcredist_x86.exe (PID: 1728)
- msiexec.exe (PID: 1040)
- ShellExperienceHost.exe (PID: 3352)
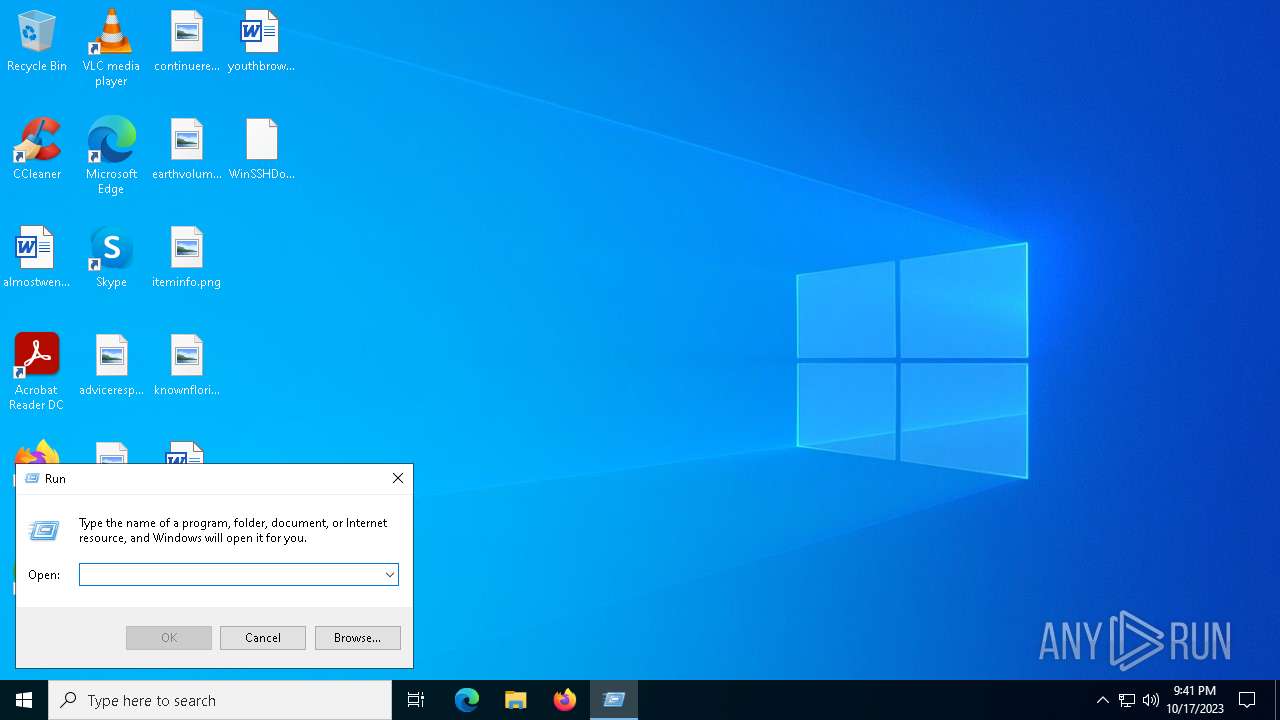
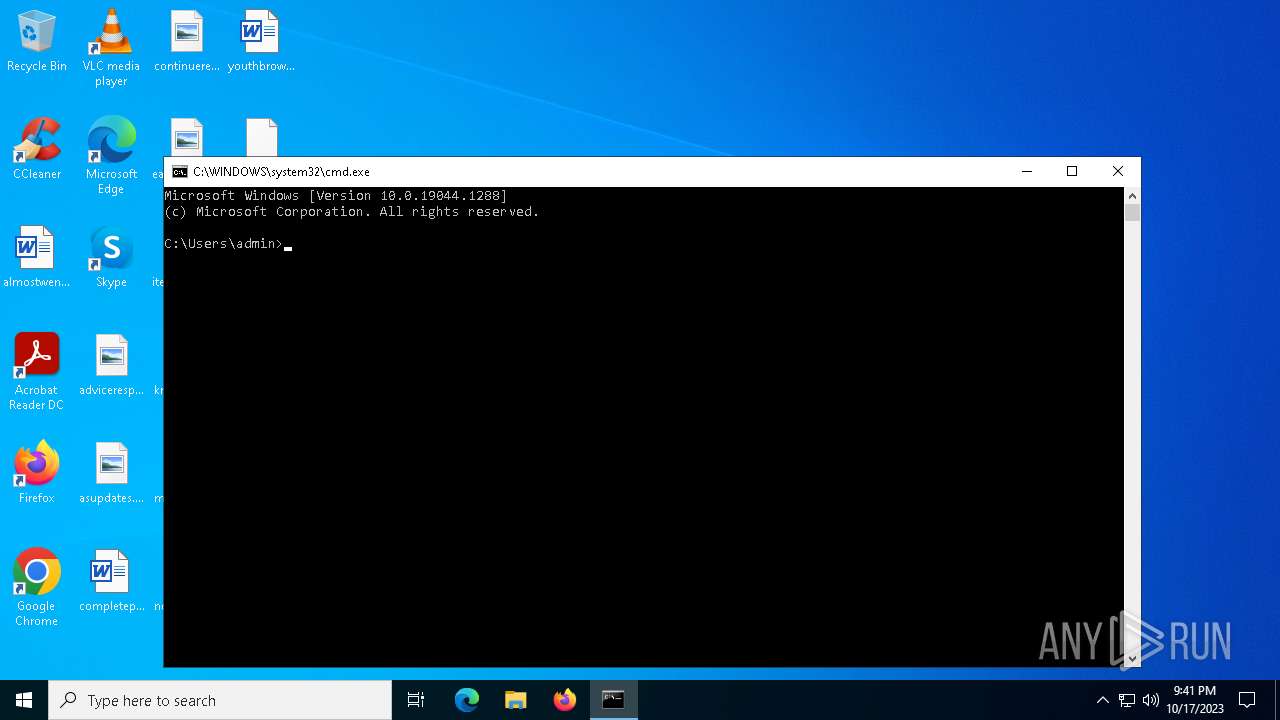
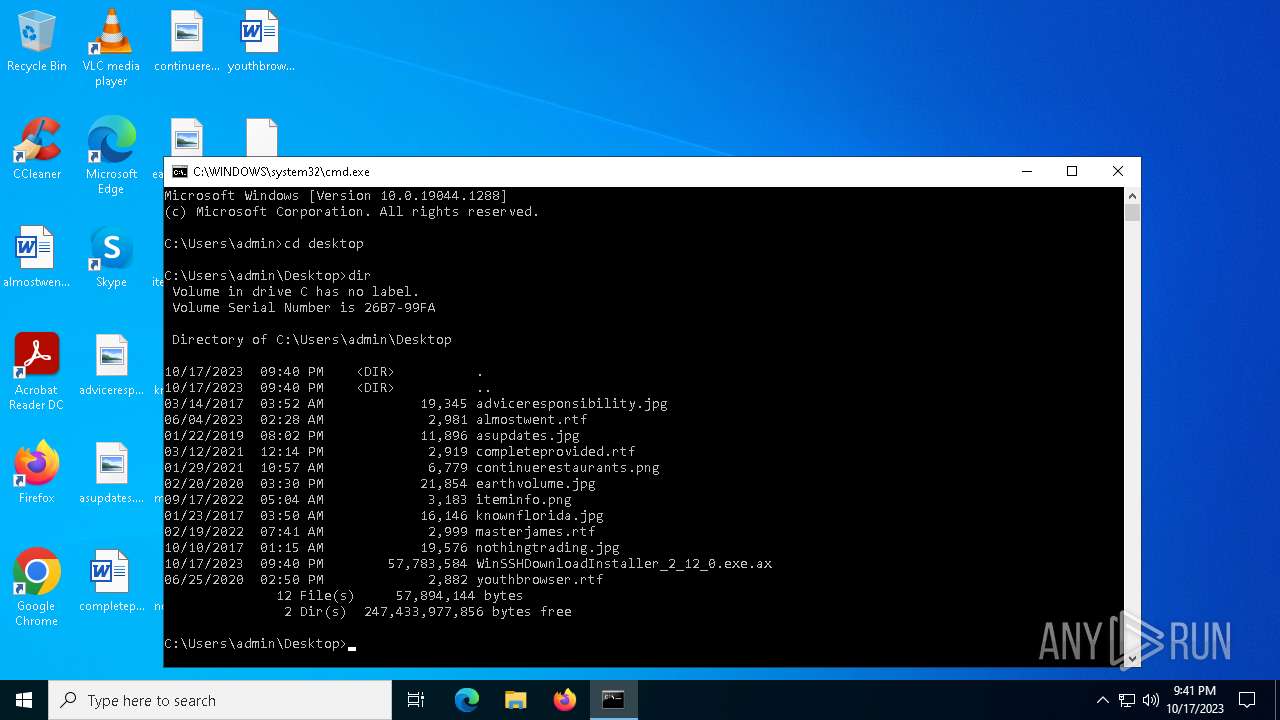
Manual execution by a user
- WinSSHDownloadInstaller_2_12_0.exe (PID: 1596)
- cmd.exe (PID: 1240)
Create files in a temporary directory
- WinSSHDownloadInstaller_2_12_0.exe (PID: 1596)
- WinSshBootstrapper.exe (PID: 3292)
- WinSSHDownloadInstaller.exe (PID: 3804)
- SSHDownloadInstaller.exe (PID: 3864)
- SSHDownloadInstaller.exe (PID: 6788)
- vc_redist.x86.exe (PID: 2472)
- vcredist_x86.exe (PID: 6372)
- vcredist_x86.exe (PID: 1728)
Creates files or folders in the user directory
- WinSshBootstrapper.exe (PID: 3292)
- OrganizerReg.exe (PID: 3140)
- SSHDownloadInstaller.exe (PID: 6788)
- vcredist_x86.exe (PID: 1728)
Process checks computer location settings
- WinSshBootstrapper.exe (PID: 3292)
- SSHDownloadInstaller.exe (PID: 6788)
Creates files in the program directory
- WinSshBootstrapper.exe (PID: 3292)
- SSHDownloadInstaller.exe (PID: 3864)
- SSHDownloadInstaller.exe (PID: 6788)
- GetAppdata.exe (PID: 7128)
- vcredist_x86.exe (PID: 1728)
Checks proxy server information
- SSHDownloadInstaller.exe (PID: 6788)
- vcredist_x86.exe (PID: 1728)
The executable file from the user directory is run by the CMD process
- vc_redist.x86.exe (PID: 6980)
- vcredist_x86.exe (PID: 1728)
Reads the machine GUID from the registry
- SSHDownloadInstaller.exe (PID: 6788)
- vcredist_x86.exe (PID: 1728)
- msiexec.exe (PID: 1040)
Reads the software policy settings
- SSHDownloadInstaller.exe (PID: 6788)
- msiexec.exe (PID: 1040)
- vcredist_x86.exe (PID: 1728)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .ax | | | DirectShow filter (56.9) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (7.7) |
| .exe | | | Win32 Executable (generic) (1.2) |
| .exe | | | Generic Win/DOS Executable (0.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:05:14 20:51:32+02:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 430592 |
| InitializedDataSize: | 510464 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x41c07 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.12.0.1 |
| ProductVersionNumber: | 2.12.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | PFU |
| FileDescription: | InstallScript Setup Launcher Unicode |
| FileVersion: | 2.12.0.1 |
| InternalName: | Setup |
| LegalCopyright: | Copyright (c) 2018 Flexera. All Rights Reserved. |
| OriginalFileName: | InstallShield Setup.exe |
| ProductName: | WinSshBootstrapper |
| ProductVersion: | 2.12.0.1 |
| InternalBuildNumber: | 182945 |
| ISInternalVersion: | 24.0.464 |
| ISInternalDescription: | InstallScript Setup Launcher Unicode |
Total processes
170
Monitored processes
39
Malicious processes
23
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 856 | "C:\WINDOWS\System32\OpenWith.exe" "C:\Users\admin\Desktop\WinSSHDownloadInstaller_2_12_0.exe.ax" | C:\Windows\System32\OpenWith.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 2147943623 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1040 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1152 | C:\Users\admin\AppData\Local\Temp\{A021FABC-FF8A-4432-8347-B55570948B3A}\ISBEW64.exe {EFB7539B-24F3-46B6-AF6E-3B021B51EFEF}:{87F3FDD7-1B71-490B-83CC-C1F7D6342E0D} | C:\Users\admin\AppData\Local\Temp\{A021FABC-FF8A-4432-8347-B55570948B3A}\ISBEW64.exe | — | WinSshBootstrapper.exe | |||||||||||
User: admin Company: Flexera Integrity Level: MEDIUM Description: InstallShield (R) 64-bit Setup Engine Exit code: 0 Version: 24.0.464 Modules
| |||||||||||||||
| 1240 | "C:\WINDOWS\system32\cmd.exe" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1516 | C:\Users\admin\AppData\Local\Temp\{414BD4CE-04EF-46BF-8124-F4942154C998}\ISBEW64.exe {EFB7539B-24F3-46B6-AF6E-3B021B51EFEF}:{D6F50EB9-F3C7-4CB0-A848-33EBF6605C8B} | C:\Users\admin\AppData\Local\Temp\{414BD4CE-04EF-46BF-8124-F4942154C998}\ISBEW64.exe | — | SSHDownloadInstaller.exe | |||||||||||
User: admin Company: Flexera Integrity Level: HIGH Description: InstallShield (R) 64-bit Setup Engine Exit code: 0 Version: 24.0.464 Modules
| |||||||||||||||
| 1596 | "C:\Users\admin\Desktop\WinSSHDownloadInstaller_2_12_0.exe" | C:\Users\admin\Desktop\WinSSHDownloadInstaller_2_12_0.exe | — | explorer.exe | |||||||||||
User: admin Company: PFU Integrity Level: MEDIUM Description: InstallScript Setup Launcher Unicode Exit code: 0 Version: 2.12.0.1 Modules
| |||||||||||||||
| 1728 | "C:\Users\admin\AppData\Local\Temp\SSHomeDownloadInstaller\Prerequisite\ms_vcredist_x86_2013\vcredist_x86.exe" /passive /quiet /norestart | C:\Users\admin\AppData\Local\Temp\SSHomeDownloadInstaller\Prerequisite\ms_vcredist_x86_2013\vcredist_x86.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2013 Redistributable (x86) - 12.0.30501 Exit code: 0 Version: 12.0.30501.0 Modules
| |||||||||||||||
| 1732 | C:\Users\admin\AppData\Local\Temp\{A021FABC-FF8A-4432-8347-B55570948B3A}\ISBEW64.exe {EFB7539B-24F3-46B6-AF6E-3B021B51EFEF}:{5F4B969F-B3CD-4704-AF4F-61488CF47BF4} | C:\Users\admin\AppData\Local\Temp\{A021FABC-FF8A-4432-8347-B55570948B3A}\ISBEW64.exe | — | WinSshBootstrapper.exe | |||||||||||
User: admin Company: Flexera Integrity Level: MEDIUM Description: InstallShield (R) 64-bit Setup Engine Exit code: 0 Version: 24.0.464 Modules
| |||||||||||||||
| 1868 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2472 | "C:\Users\admin\AppData\Local\Temp\SSHomeDownloadInstaller\Prerequisite\ms_vcredist_x86_2017\vc_redist.x86.exe" /passive /quiet /norestart -burn.unelevated BurnPipe.{0F9BD7EE-BAEA-418A-AC8D-793148A8395E} {E592140E-8CD1-4BDA-95EB-263B853D295B} 6980 | C:\Users\admin\AppData\Local\Temp\SSHomeDownloadInstaller\Prerequisite\ms_vcredist_x86_2017\vc_redist.x86.exe | — | vc_redist.x86.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2017 Redistributable (x86) - 14.10.25008 Exit code: 1638 Version: 14.10.25008.0 Modules
| |||||||||||||||
Total events
13 094
Read events
12 975
Write events
83
Delete events
36
Modification events
| (PID) Process: | (3292) WinSshBootstrapper.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{FAEF32A4-2231-48DC-8084-B1FB69A8D185} |
| Operation: | delete value | Name: | DisplayName |
Value: WinSshBootstrapper | |||
| (PID) Process: | (3292) WinSshBootstrapper.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3292) WinSshBootstrapper.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3292) WinSshBootstrapper.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3292) WinSshBootstrapper.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3864) SSHDownloadInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000B794B581A43CD9010C0A0000180C0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2756) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000B794B581A43CD9010C0A0000180C0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2756) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 48000000000000003607CB81A43CD9010C0A0000180C0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2756) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 48000000000000004369CD81A43CD9010C0A0000180C0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2756) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 48000000000000004369CD81A43CD9010C0A0000180C0000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
118
Suspicious files
97
Text files
201
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1240 | cmd.exe | C:\Users\admin\Desktop\WinSSHDownloadInstaller_2_12_0.exe | — | |
MD5:— | SHA256:— | |||
| 1596 | WinSSHDownloadInstaller_2_12_0.exe | C:\Users\admin\AppData\Local\Temp\{68F817FB-5D98-4CFC-A1F6-22E19B2B22B1}\Disk1\0x0407.ini | text | |
MD5:AC20509373836978506DE9562F946FC1 | SHA256:E12AB3866C7DAB7482E1D571D611549D4485A5D7DD808590D7717B028B9DB38B | |||
| 1596 | WinSSHDownloadInstaller_2_12_0.exe | C:\Users\admin\AppData\Local\Temp\{68F817FB-5D98-4CFC-A1F6-22E19B2B22B1}\Disk1\0x0404.ini | text | |
MD5:4676329DFC858D9857E6D491E95CAF31 | SHA256:68DAA2DA6131AE26FF0D35C3C6E4F76C54B51A8CBDB0E2776703482EFA765356 | |||
| 1596 | WinSSHDownloadInstaller_2_12_0.exe | C:\Users\admin\AppData\Local\Temp\{68F817FB-5D98-4CFC-A1F6-22E19B2B22B1}\Disk1\0x0413.ini | text | |
MD5:0163281185163396867F4E337FDFBC52 | SHA256:D4A9124D10CF042616EBA4B8DC4722C97CB6F6156E3AFD2A37AD18A0003B90F8 | |||
| 1596 | WinSSHDownloadInstaller_2_12_0.exe | C:\Users\admin\AppData\Local\Temp\{68F817FB-5D98-4CFC-A1F6-22E19B2B22B1}\Disk1\layout.bin | binary | |
MD5:2158BE9E4377EFA42835B5A045C78BEB | SHA256:C3A149FCAF5200D40296104458BE7840A2F39310EAC48687E56909243346448C | |||
| 1596 | WinSSHDownloadInstaller_2_12_0.exe | C:\Users\admin\AppData\Local\Temp\{68F817FB-5D98-4CFC-A1F6-22E19B2B22B1}\Disk1\0x0416.ini | text | |
MD5:C405C76CB3B7A2E0C838A44EA550FBAC | SHA256:A6828EB5EF5B5151109E9282EB4BCD533977A24B774EC6E906E639E2C639E762 | |||
| 1596 | WinSSHDownloadInstaller_2_12_0.exe | C:\Users\admin\AppData\Local\Temp\{68F817FB-5D98-4CFC-A1F6-22E19B2B22B1}\Disk1\0x0419.ini | text | |
MD5:21132D49C8C7AB8A96BE2FC33410366D | SHA256:45AC44420E048EE23E513FD0D3ECB83DD20A94CDA9A394A00BA6CAFF474ECEF4 | |||
| 1596 | WinSSHDownloadInstaller_2_12_0.exe | C:\Users\admin\AppData\Local\Temp\{68F817FB-5D98-4CFC-A1F6-22E19B2B22B1}\Disk1\setup.ini | text | |
MD5:9C7112F50FF2BD092474188542E3DC30 | SHA256:E178A0EA5600344963FE86768C0F87C72DCE03C1B9E357EF499452E14874F5B5 | |||
| 1596 | WinSSHDownloadInstaller_2_12_0.exe | C:\Users\admin\AppData\Local\Temp\{68F817FB-5D98-4CFC-A1F6-22E19B2B22B1}\Disk1\0x0804.ini | text | |
MD5:ED3CF5EF1C0337B41ADD0A375E51A1F1 | SHA256:B70BDB0D16766A3272574C74BA1485D1AFBAF2C7EFD93574C09DF759C578FB37 | |||
| 1596 | WinSSHDownloadInstaller_2_12_0.exe | C:\Users\admin\AppData\Local\Temp\{68F817FB-5D98-4CFC-A1F6-22E19B2B22B1}\Disk1\data1.cab | compressed | |
MD5:47C23EC8A7B6F1C455F50CC5F04B68D5 | SHA256:1A8AACEA72E3B438626B93E95DD6F2C2E41D29F6C1F54FC3441A286F09FD5C58 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
28
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5960 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | unknown |
2820 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | binary | 1.47 Kb | unknown |
6788 | SSHDownloadInstaller.exe | GET | 200 | 104.18.20.226:80 | http://ocsp2.globalsign.com/rootr3/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCDQHuXyId%2FGI71DM6hVc%3D | unknown | binary | 1.40 Kb | unknown |
5012 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | US | binary | 471 b | unknown |
6788 | SSHDownloadInstaller.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/gsrsaovsslca2018/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBRrcGT%2BanRD3C1tW3nsrKeuXC7DPwQU%2BO9%2F8s14Z6jeb48kjYjxhwMCs%2BsCDHeW%2FuykxI8Oj4hqTw%3D%3D | unknown | binary | 1.40 Kb | unknown |
1728 | vcredist_x86.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicrosoftTimeStampPCA.crl | DE | binary | 519 b | unknown |
2984 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | US | binary | 471 b | unknown |
1728 | vcredist_x86.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicCodSigPCA_08-31-2010.crl | DE | binary | 564 b | unknown |
1728 | vcredist_x86.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | DE | binary | 767 b | unknown |
2980 | svchost.exe | GET | 200 | 23.206.95.234:80 | http://x1.c.lencr.org/ | NL | binary | 717 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2620 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3792 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
5960 | svchost.exe | 40.126.31.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5960 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2820 | backgroundTaskHost.exe | 104.126.37.186:443 | — | Akamai International B.V. | DE | unknown |
2820 | backgroundTaskHost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
5012 | backgroundTaskHost.exe | 20.74.47.205:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | unknown |
5012 | backgroundTaskHost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
origin.pfultd.com |
| whitelisted |
ocsp2.globalsign.com |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |