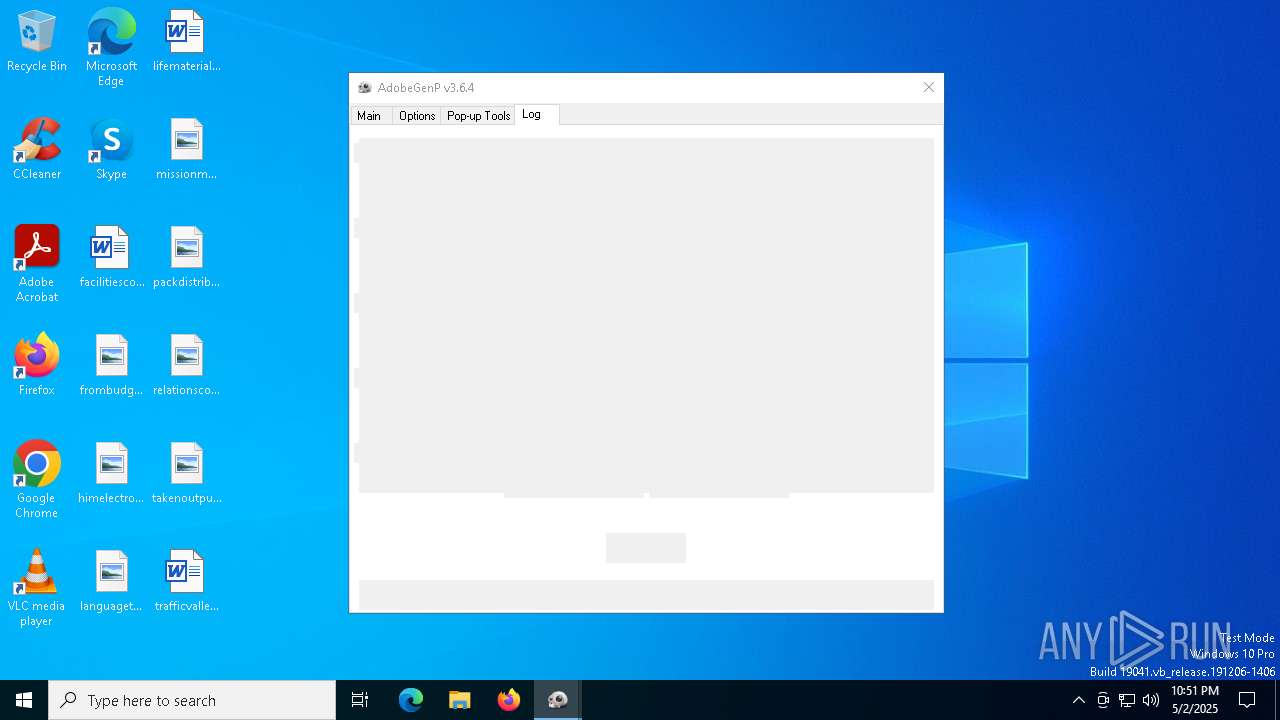
| File name: | GenP 3.6.4.exe |
| Full analysis: | https://app.any.run/tasks/8bbfc492-4200-48fc-a1df-71ad583495f3 |
| Verdict: | Malicious activity |
| Analysis date: | May 02, 2025, 22:50:44 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 6 sections |
| MD5: | 859E24EAF9E2B231CF7FADF25D8DB232 |
| SHA1: | EE1782596BC1574459B69B1DE675FFF66931E25B |
| SHA256: | B92860632A6DDAE2532206833CC0C4A18548D469136271ACDBD760E4986E260B |
| SSDEEP: | 98304:a9rem5Oid1RME3XUVZ6z2Mn85M7LRKUDmkSQXkkzvuPVca+fl3VgvtfvXW9AALqE:cZul |
MALICIOUS
GENERIC has been found (auto)
- GenP 3.6.4.exe (PID: 4944)
SUSPICIOUS
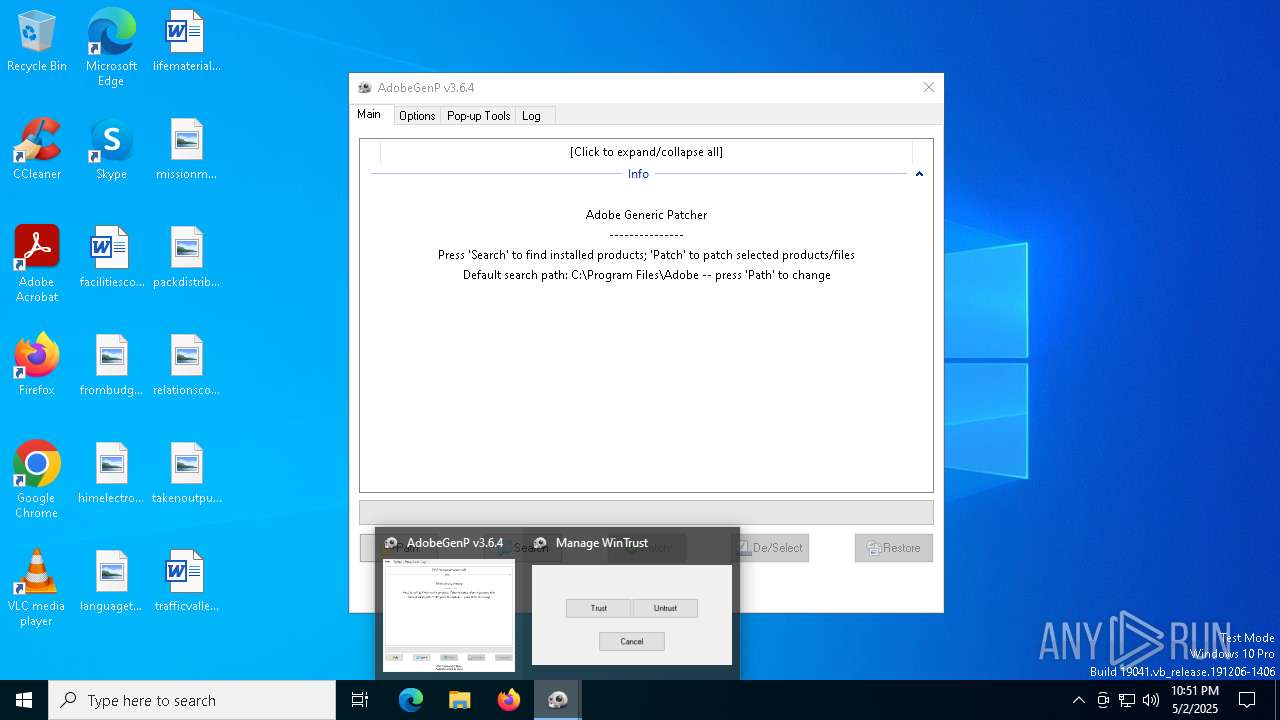
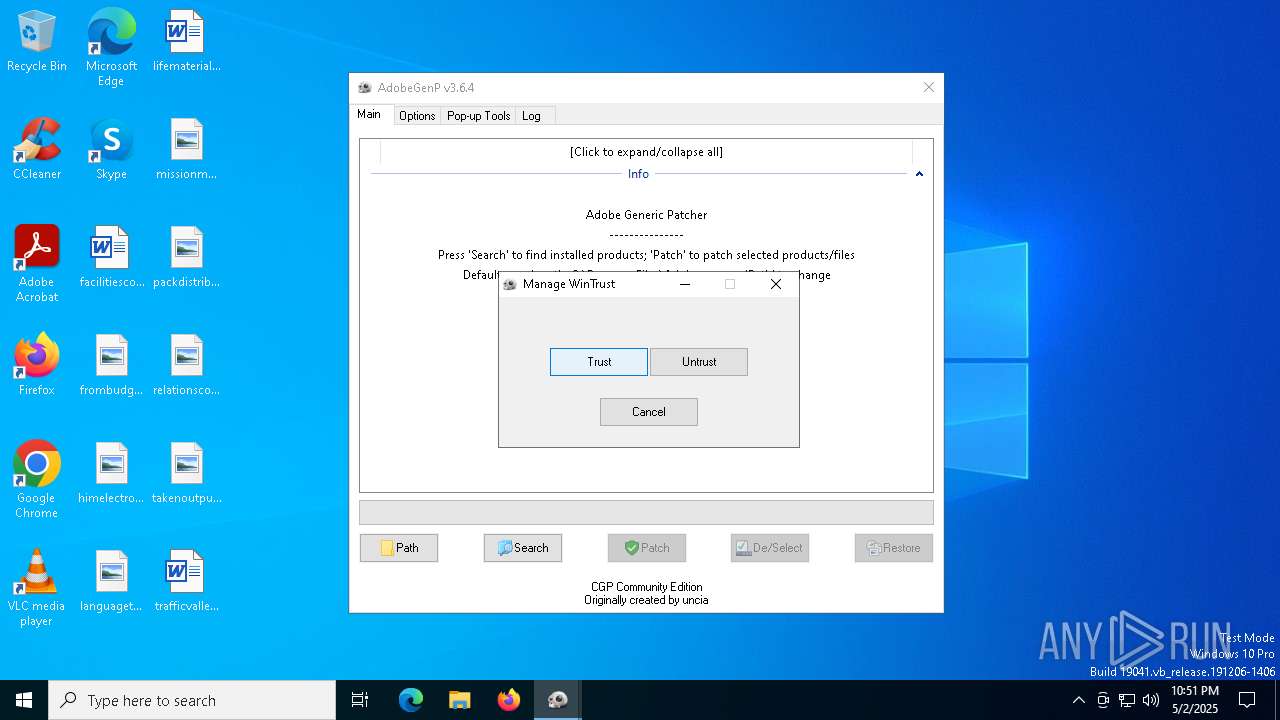
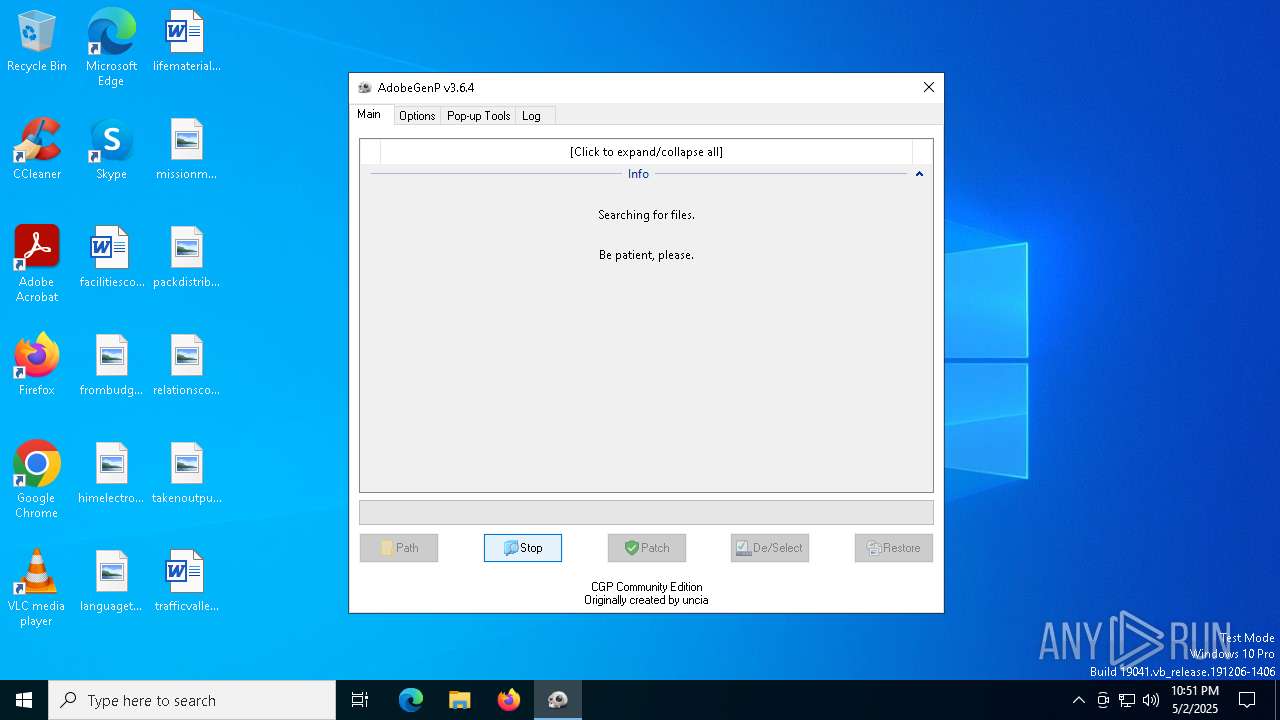
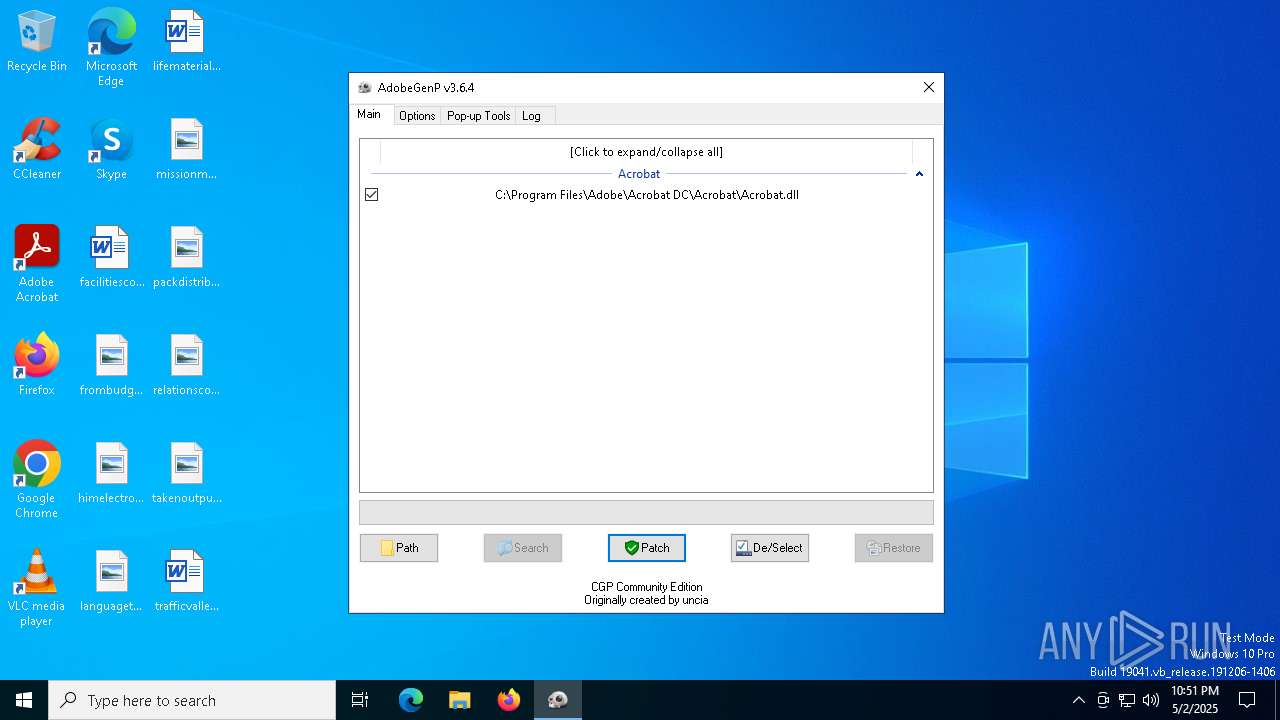
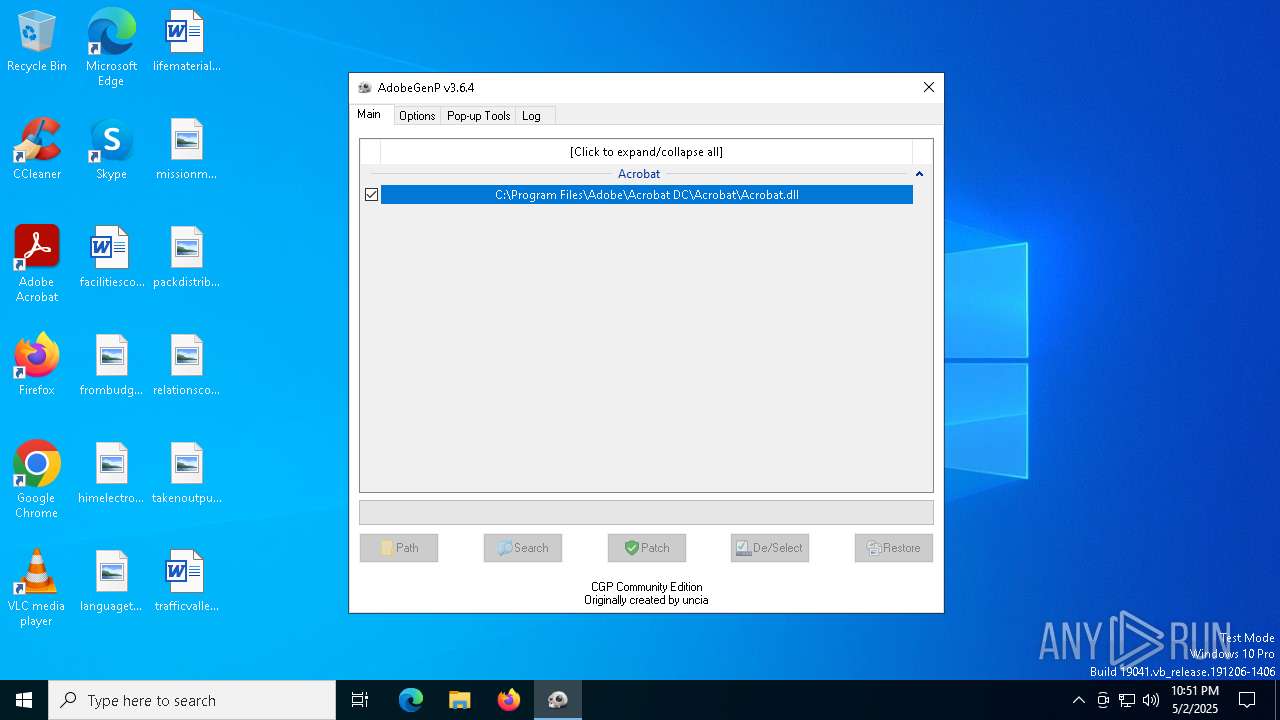
ADOBEGENP mutex has been found
- GenP 3.6.4.exe (PID: 4944)
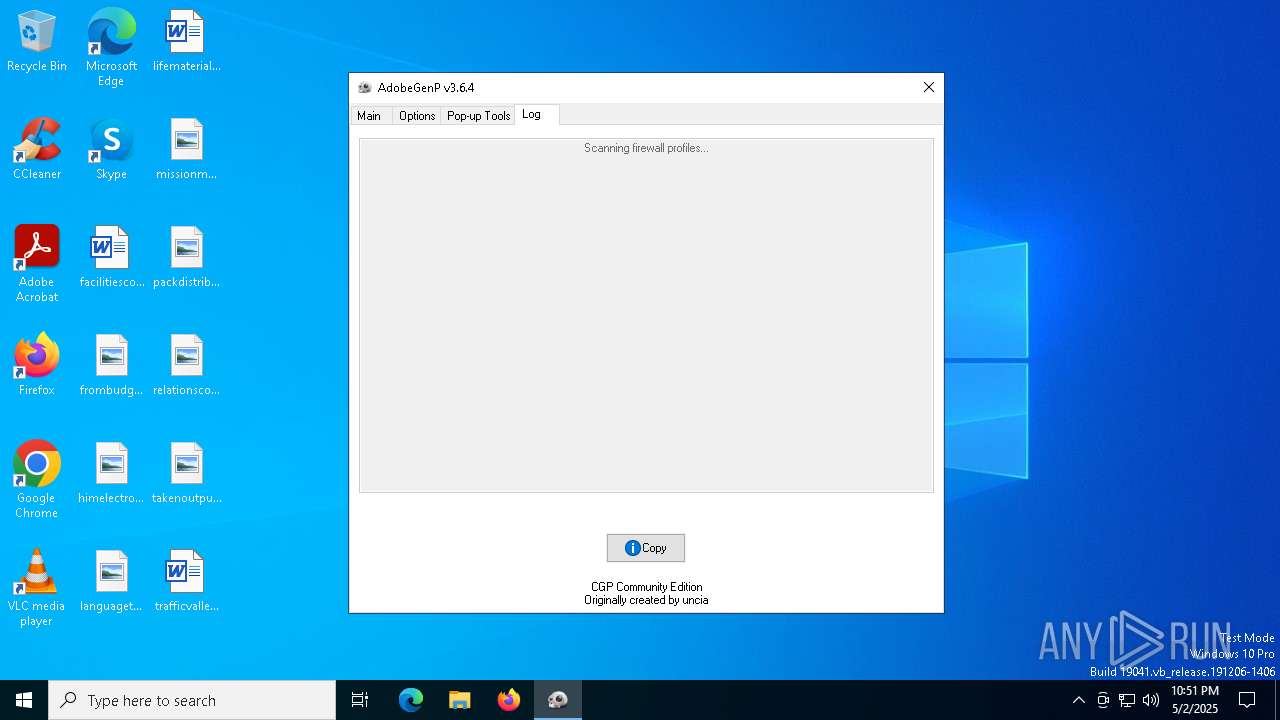
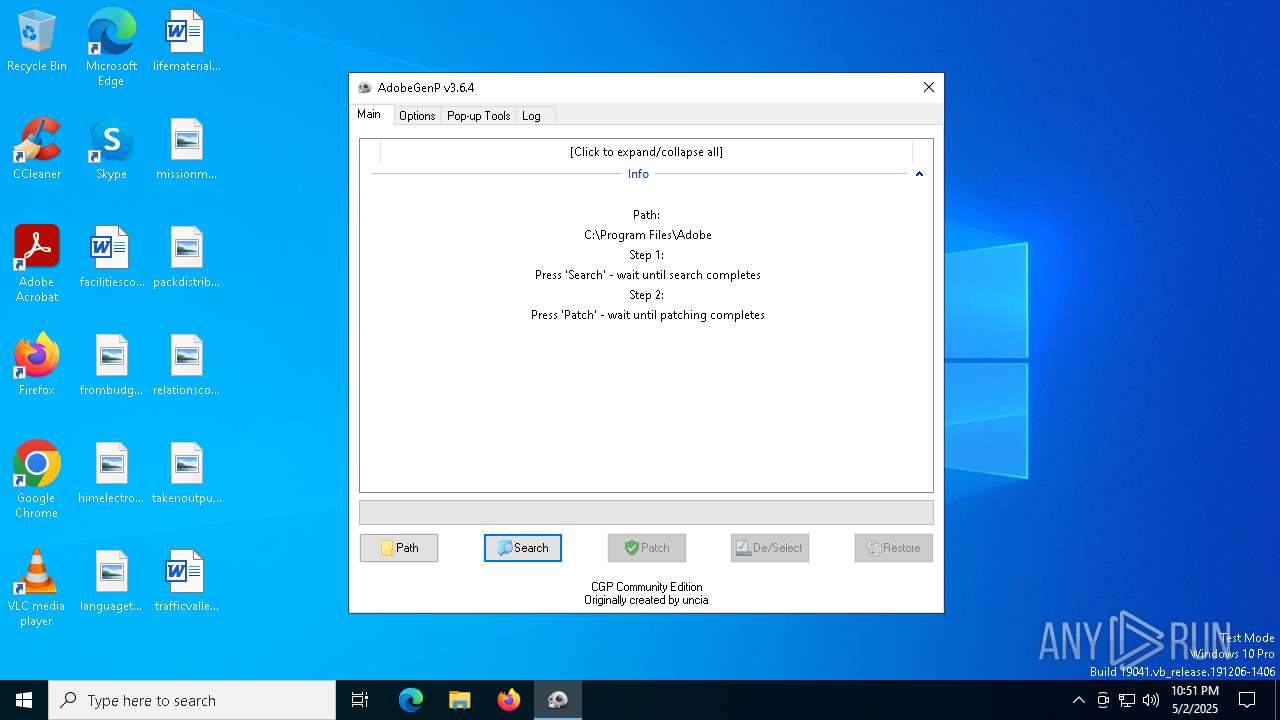
Starts CMD.EXE for commands execution
- GenP 3.6.4.exe (PID: 4944)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 5176)
- cmd.exe (PID: 2600)
- cmd.exe (PID: 1324)
- cmd.exe (PID: 1184)
- cmd.exe (PID: 4892)
- cmd.exe (PID: 5392)
- GenP 3.6.4.exe (PID: 4944)
There is functionality for taking screenshot (YARA)
- GenP 3.6.4.exe (PID: 4944)
INFO
Reads mouse settings
- GenP 3.6.4.exe (PID: 4944)
Create files in a temporary directory
- GenP 3.6.4.exe (PID: 4944)
Reads the computer name
- GenP 3.6.4.exe (PID: 4944)
The sample compiled with english language support
- GenP 3.6.4.exe (PID: 4944)
The process uses AutoIt
- GenP 3.6.4.exe (PID: 4944)
Checks supported languages
- GenP 3.6.4.exe (PID: 4944)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 1512)
- powershell.exe (PID: 6652)
- powershell.exe (PID: 2984)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6652)
- powershell.exe (PID: 5776)
- powershell.exe (PID: 1512)
- powershell.exe (PID: 2984)
- powershell.exe (PID: 5136)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:04:23 18:29:11+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.16 |
| CodeSize: | 734208 |
| InitializedDataSize: | 2232320 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2549c |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.6.4.0 |
| ProductVersionNumber: | 3.6.4.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
| FileVersion: | 3.6.4.0 |
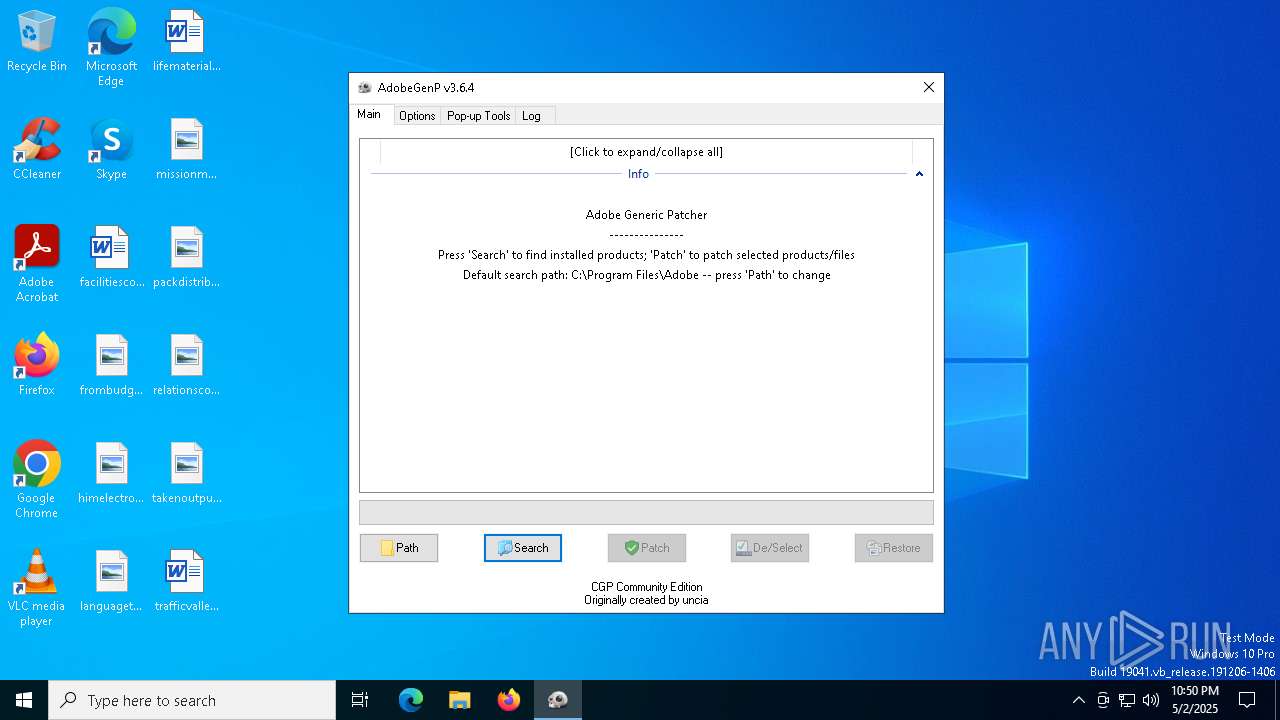
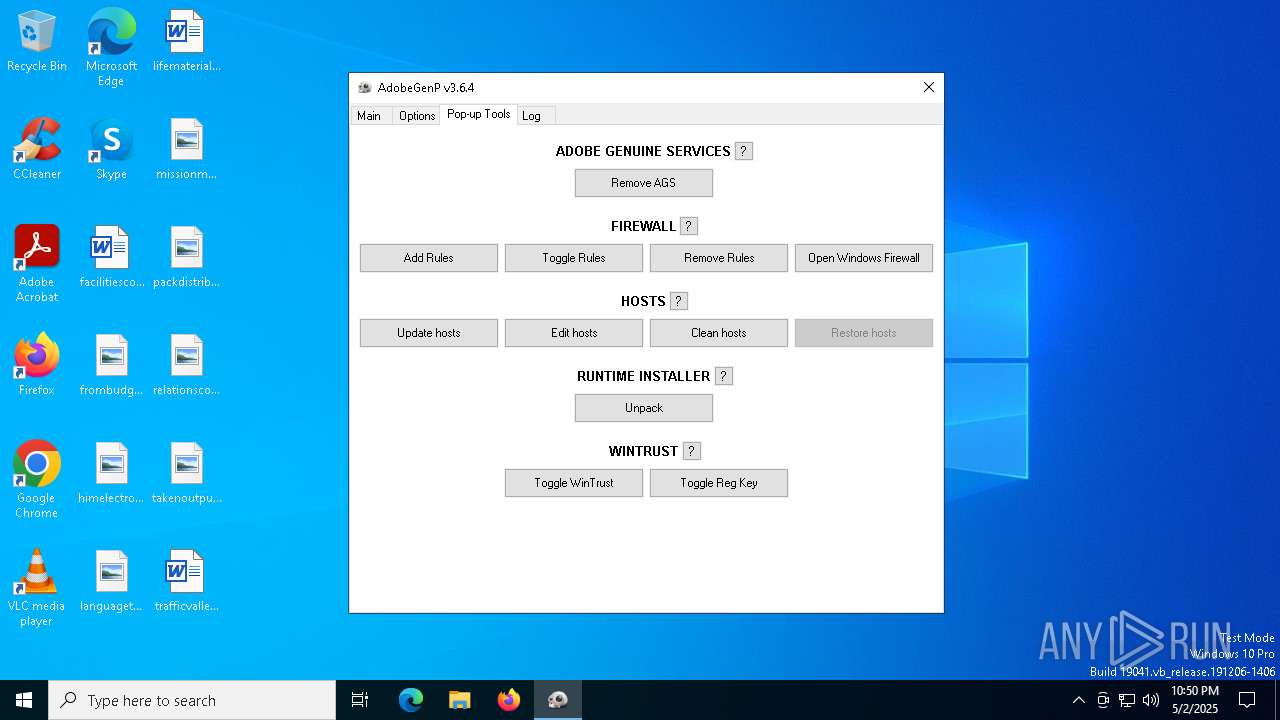
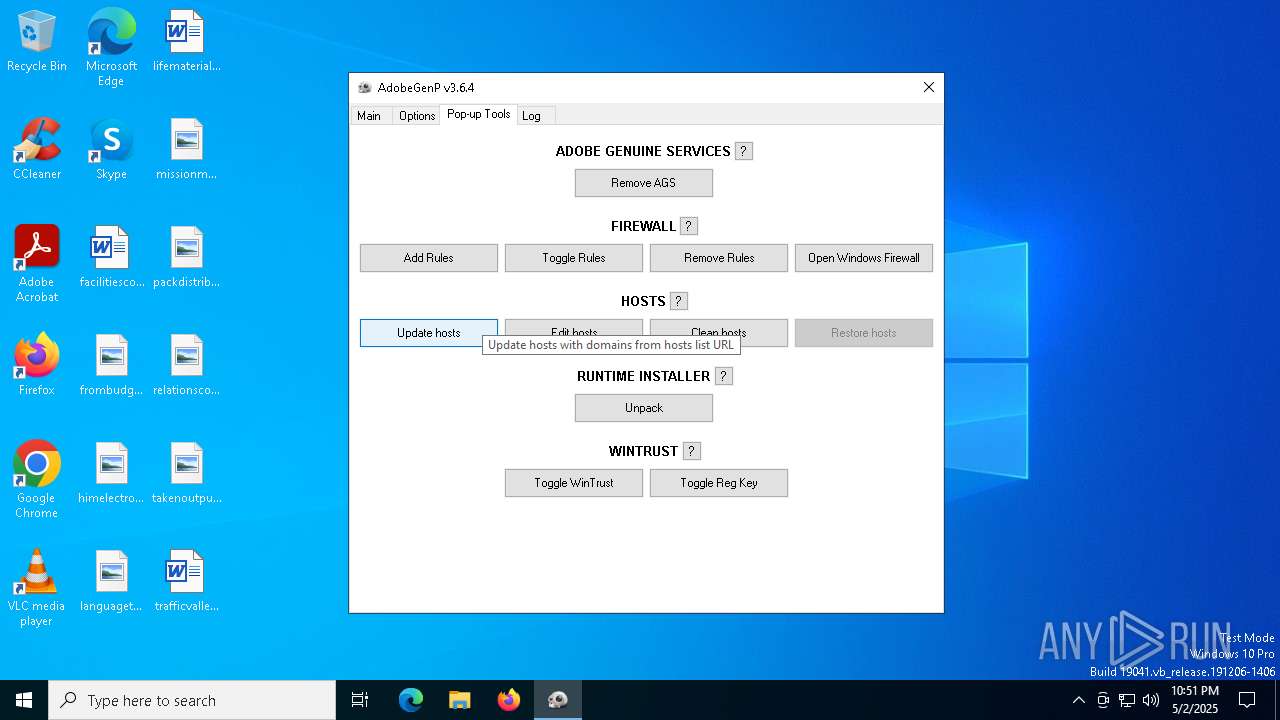
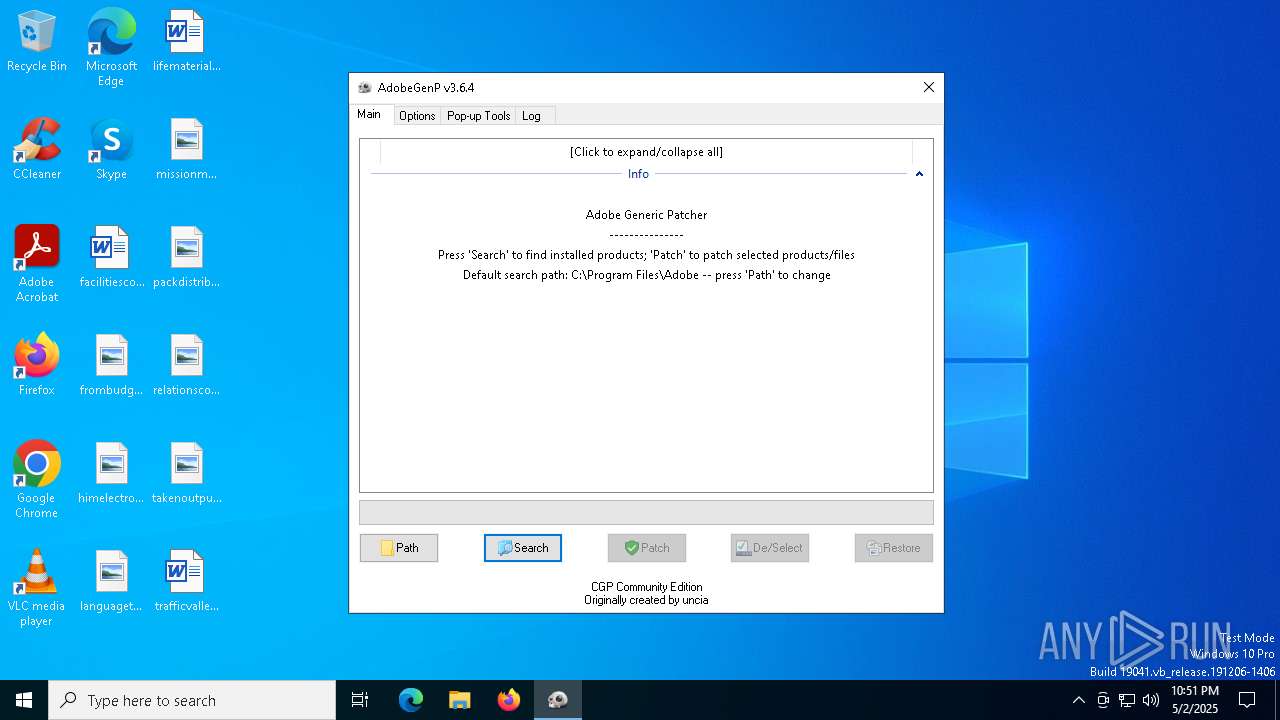
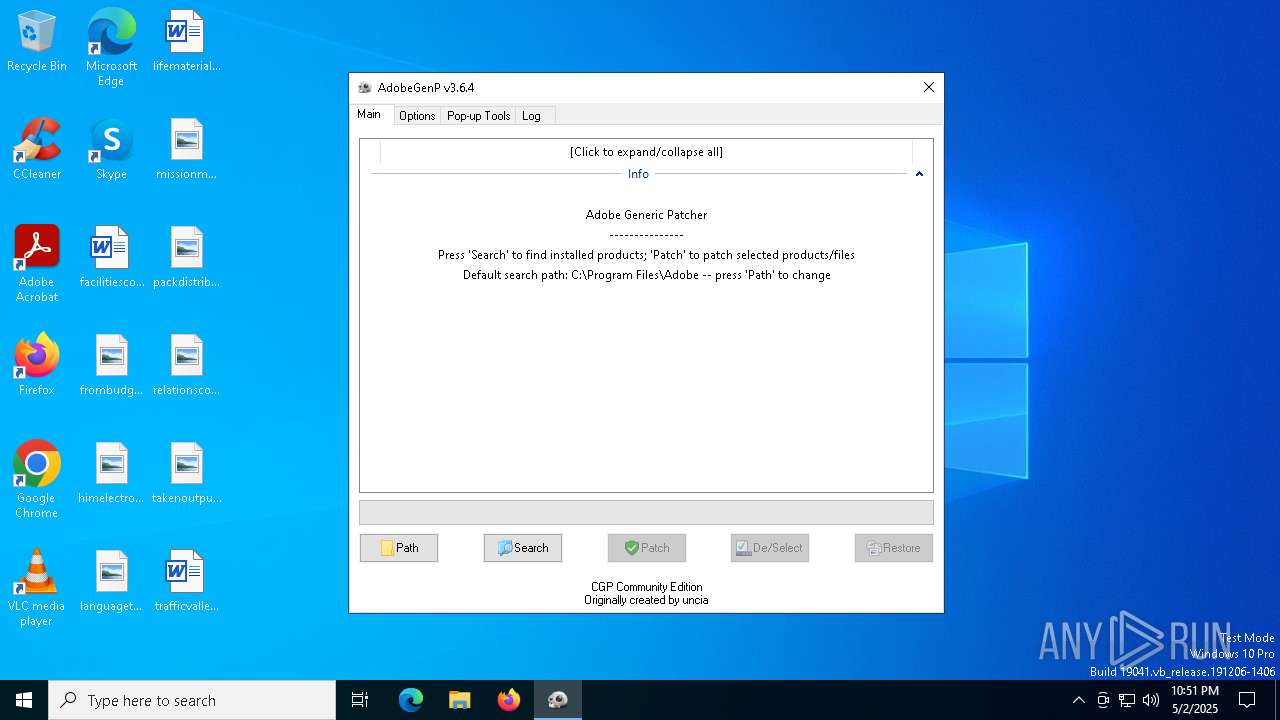
| Comments: | AdobeGenP |
| FileDescription: | Adobe Generic Patcher |
| ProductName: | AdobeGenP |
| ProductVersion: | 3.6.4 |
| CompanyName: | AdobeGenp |
| LegalCopyright: | AdobeGenP 2025 |
| LegalTradeMarks: | AdobeGenP 2025 |
Total processes
152
Monitored processes
24
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 780 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1052 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
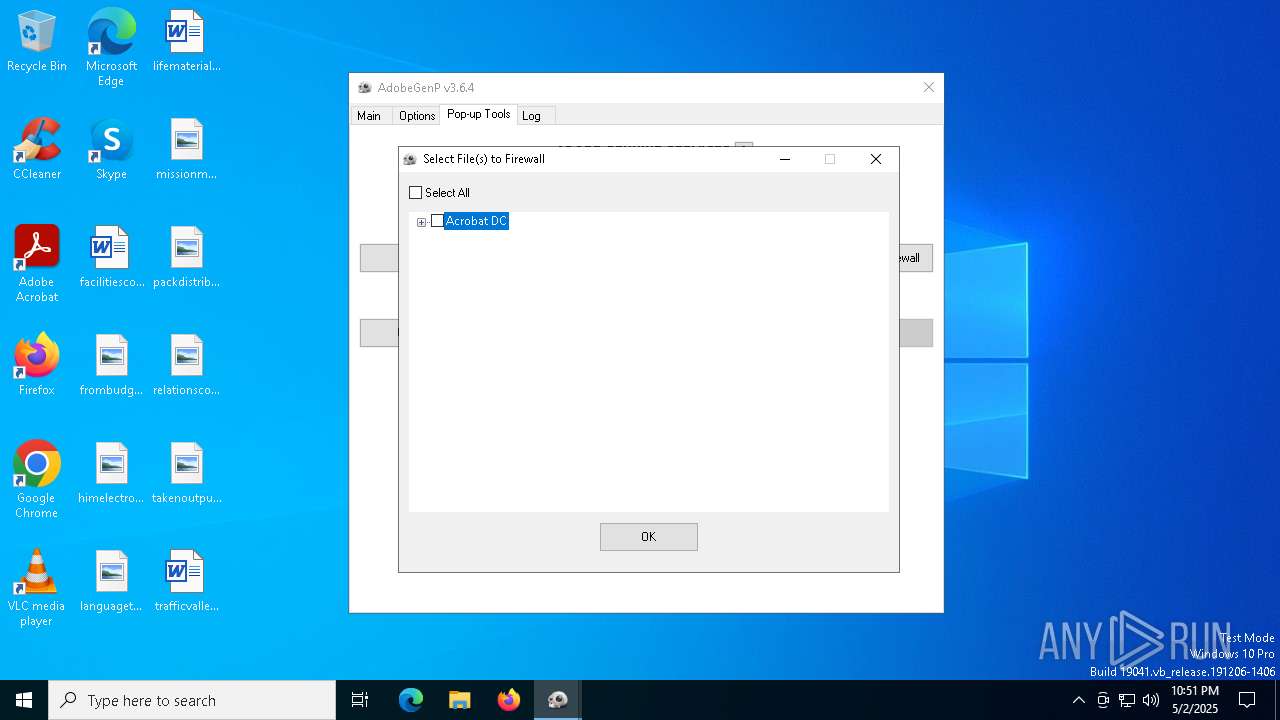
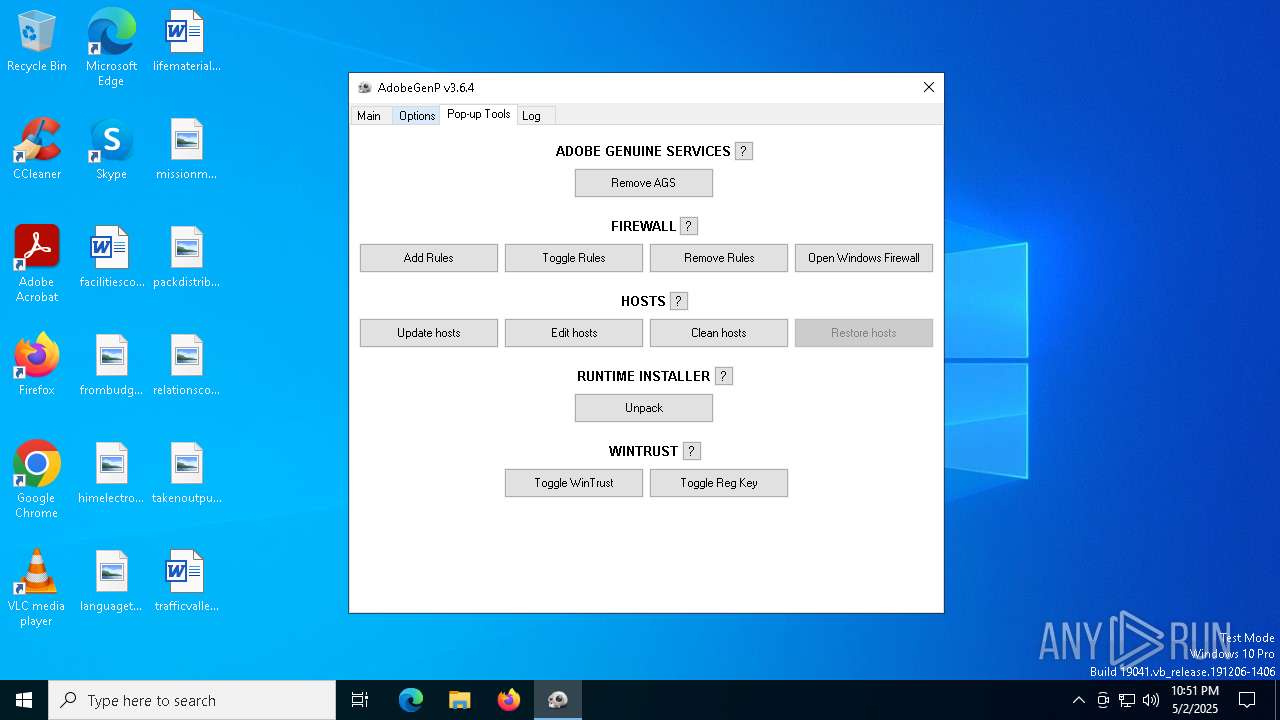
| 1184 | C:\WINDOWS\system32\cmd.exe /c powershell.exe -Command "Get-NetFirewallRule -DisplayName 'Adobe-Block - C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.exe' | Measure-Object | Select-Object -ExpandProperty Count" | C:\Windows\System32\cmd.exe | — | GenP 3.6.4.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1324 | C:\WINDOWS\system32\cmd.exe /c powershell.exe -Command "Get-Service MpsSvc | Select-Object -Property Status,DisplayName | Format-List" | C:\Windows\System32\cmd.exe | — | GenP 3.6.4.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1328 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1512 | powershell.exe -Command "Get-NetFirewallRule -DisplayName 'Adobe-Block - C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.exe' | Measure-Object | Select-Object -ExpandProperty Count" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2600 | C:\WINDOWS\system32\cmd.exe /c powershell.exe -Command "Get-NetFirewallProfile | Select-Object -Property Name,Enabled | Format-Table -HideTableHeaders" | C:\Windows\System32\cmd.exe | — | GenP 3.6.4.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2852 | "C:\Users\admin\AppData\Local\Temp\GenP 3.6.4.exe" | C:\Users\admin\AppData\Local\Temp\GenP 3.6.4.exe | — | explorer.exe | |||||||||||
User: admin Company: AdobeGenp Integrity Level: MEDIUM Description: Adobe Generic Patcher Exit code: 3221226540 Version: 3.6.4.0 Modules
| |||||||||||||||
| 2984 | powershell.exe -Command "Get-Service MpsSvc | Select-Object -Property Status,DisplayName | Format-List" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2984 | powershell.exe -Command "Get-NetFirewallRule -DisplayName 'Adobe-Block - C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe' | Measure-Object | Select-Object -ExpandProperty Count" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
42 139
Read events
42 101
Write events
36
Delete events
2
Modification events
| (PID) Process: | (4944) GenP 3.6.4.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (4944) GenP 3.6.4.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 04000000030000000E00000000000000100000000F0000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
| (PID) Process: | (4944) GenP 3.6.4.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\4\0\5 |
| Operation: | write | Name: | 6 |
Value: 50003100000000004658D068100041646F6265003C0009000400EFBE4658D068A25A62B62E000000E46100000000200000000000000000000000000000004AE5D900410064006F0062006500000014000000 | |||
| (PID) Process: | (4944) GenP 3.6.4.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\4\0\5\6 |
| Operation: | delete value | Name: | MRUList |
Value: | |||
| (PID) Process: | (4944) GenP 3.6.4.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\4\0\5 |
| Operation: | write | Name: | MRUListEx |
Value: 06000000040000000500000003000000010000000200000000000000FFFFFFFF | |||
| (PID) Process: | (4944) GenP 3.6.4.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (4944) GenP 3.6.4.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\4\0\5\6 |
| Operation: | write | Name: | NodeSlot |
Value: 254 | |||
| (PID) Process: | (4944) GenP 3.6.4.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\4\0\5\6 |
| Operation: | write | Name: | MRUListEx |
Value: FFFFFFFF | |||
| (PID) Process: | (4944) GenP 3.6.4.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\254\Shell |
| Operation: | write | Name: | SniffedFolderType |
Value: Generic | |||
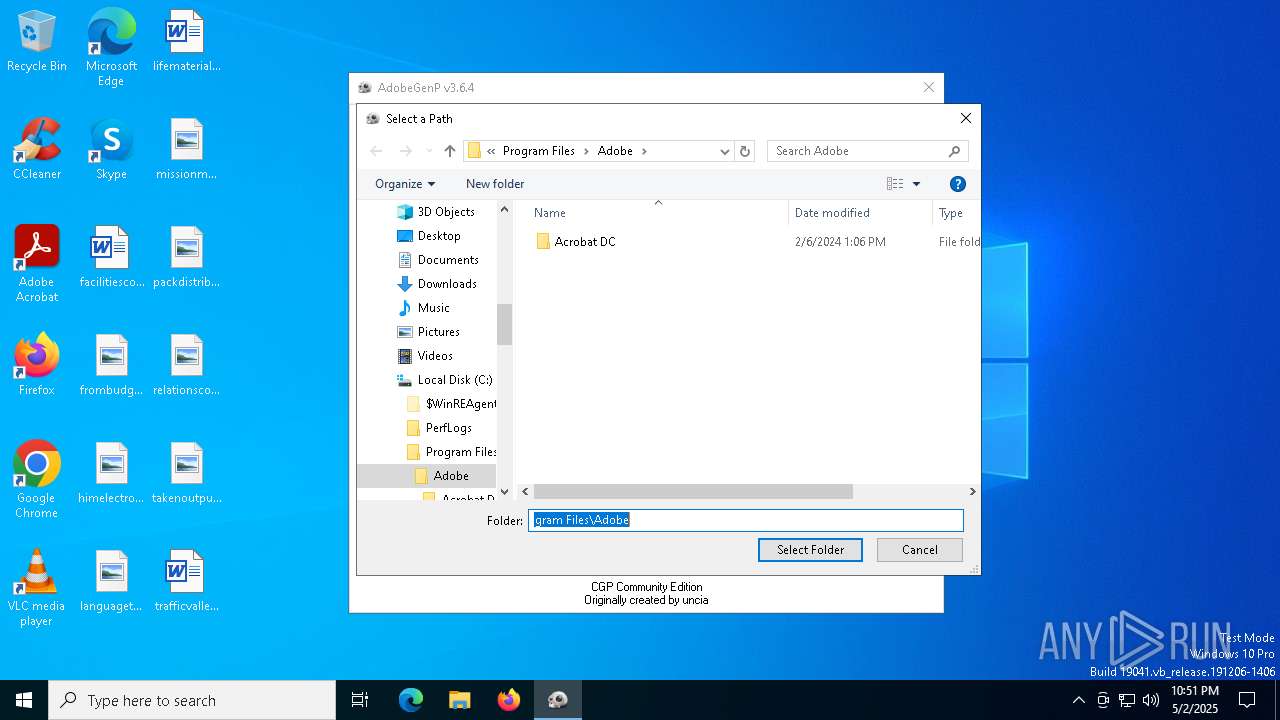
| (PID) Process: | (4944) GenP 3.6.4.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\OpenSavePidlMRU\* |
| Operation: | write | Name: | 8 |
Value: 14001F50E04FD020EA3A6910A2D808002B30309D19002F433A5C000000000000000000000000000000000000008C003100000000004658AC76110050524F4752417E310000740009000400EFBE874FDB49A25A58B62E000000A5A400000000050000000000000000004A000000000077310C01500072006F006700720061006D002000460069006C0065007300000040007300680065006C006C00330032002E0064006C006C002C002D00320031003700380031000000180050003100000000004658D068100041646F6265003C0009000400EFBE4658D068A25A62B62E000000E46100000000200000000000000000000000000000004AE5D900410064006F0062006500000014000000 | |||
Executable files
1
Suspicious files
2
Text files
14
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5892 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ipmgg5ea.4cx.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4944 | GenP 3.6.4.exe | C:\Users\admin\AppData\Local\Temp\autB5F4.tmp | binary | |
MD5:FC28D09F35A6D32EAE8D4CAF9BFF09D1 | SHA256:5B3003EE371F41596FBB89A40B0126BA3980E8D8FAF1DBE4B7388E462BF44442 | |||
| 2984 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_gy24k4wi.g15.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6652 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_lqx4b0pv.vvg.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1512 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_t5ujgwim.d5l.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2984 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_tltiqgpe.og0.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1512 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_3rce2mpx.hqk.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6652 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_4zdogf4m.2vn.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5136 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_o1gysw0l.hvy.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4944 | GenP 3.6.4.exe | C:\Users\admin\AppData\Local\Temp\config.ini | text | |
MD5:FABC1F7F0E77C6882B9A16851E7D7E77 | SHA256:5E9A06AB44D12EC8AAAF3918859E8ED807E76CC58B7FEEB9B25741DE8AC4C56D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
19
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.162:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6272 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6272 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.162:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |