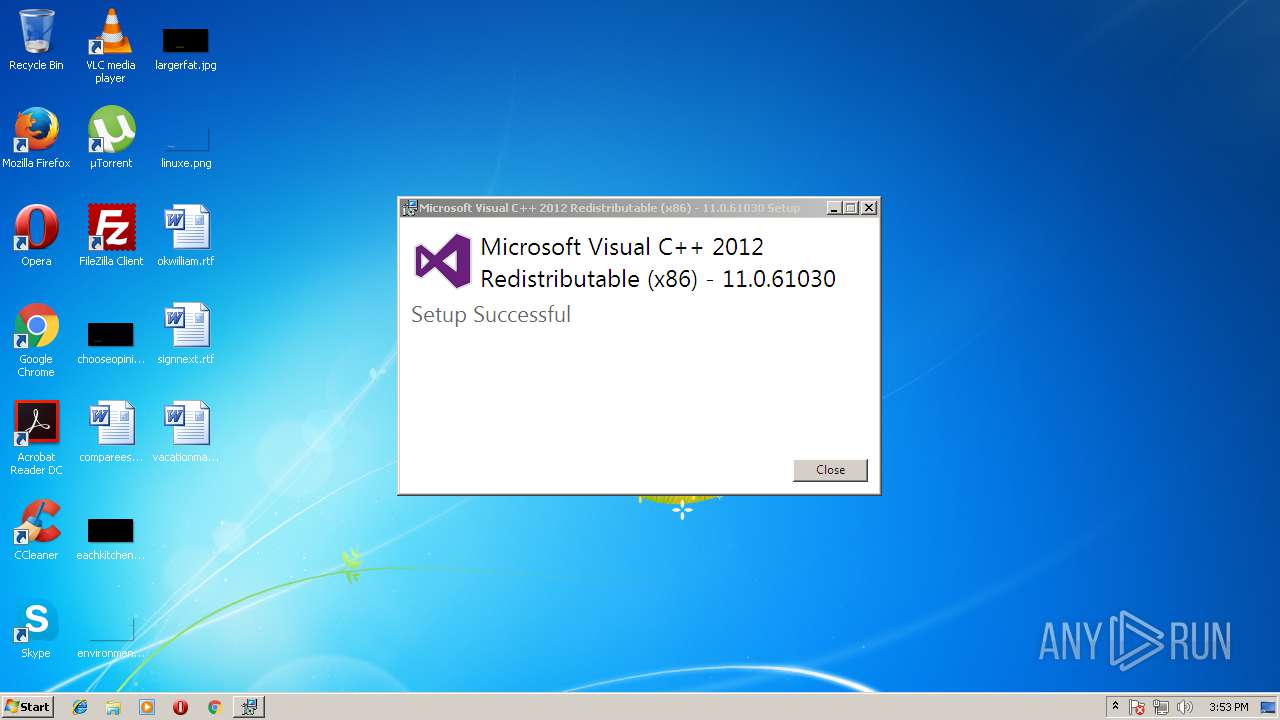
| File name: | vcredist_x86.exe |
| Full analysis: | https://app.any.run/tasks/5c25381c-cc87-4441-a388-de11fa3f9fd3 |
| Verdict: | Malicious activity |
| Analysis date: | May 07, 2018, 14:51:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 7F52A19ECAF7DB3C163DD164BE3E592E |
| SHA1: | 96B377A27AC5445328CBAAE210FC4F0AAA750D3F |
| SHA256: | B924AD8062EAF4E70437C8BE50FA612162795FF0839479546CE907FFA8D6E386 |
| SSDEEP: | 196608:OwKjLs+UIkzHlAv4X6zQRgiwHLD2LQIX/:9KjaxFFP1iLD2LnP |
MALICIOUS
Application loaded dropped or rewritten executable
- vcredist_x86.exe (PID: 3076)
Application was dropped or rewritten from another process
- vcredist_x86.exe (PID: 3840)
Changes the autorun value in the registry
- vcredist_x86.exe (PID: 3840)
SUSPICIOUS
Creates files in the Windows directory
- vcredist_x86.exe (PID: 3840)
- msiexec.exe (PID: 2968)
Creates or modifies windows services
- vcredist_x86.exe (PID: 3840)
Searches for installed software
- vcredist_x86.exe (PID: 3076)
- vcredist_x86.exe (PID: 3840)
Creates a software uninstall entry
- vcredist_x86.exe (PID: 3840)
INFO
Loads rich edit control libraries
- vcredist_x86.exe (PID: 3076)
Dropped object may contain URL's
- vcredist_x86.exe (PID: 3076)
- vcredist_x86.exe (PID: 3840)
- msiexec.exe (PID: 2968)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3460)
Creates a software uninstall entry
- msiexec.exe (PID: 2968)
Reads settings of System Certificates
- DrvInst.exe (PID: 3660)
Application loaded dropped or rewritten executable
- msiexec.exe (PID: 2968)
Creates or modifies windows services
- vssvc.exe (PID: 3460)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:08:21 01:25:02+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 320000 |
| InitializedDataSize: | 34816 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x474b |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 11.0.61030.0 |
| ProductVersionNumber: | 11.0.61030.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Microsoft Corporation |
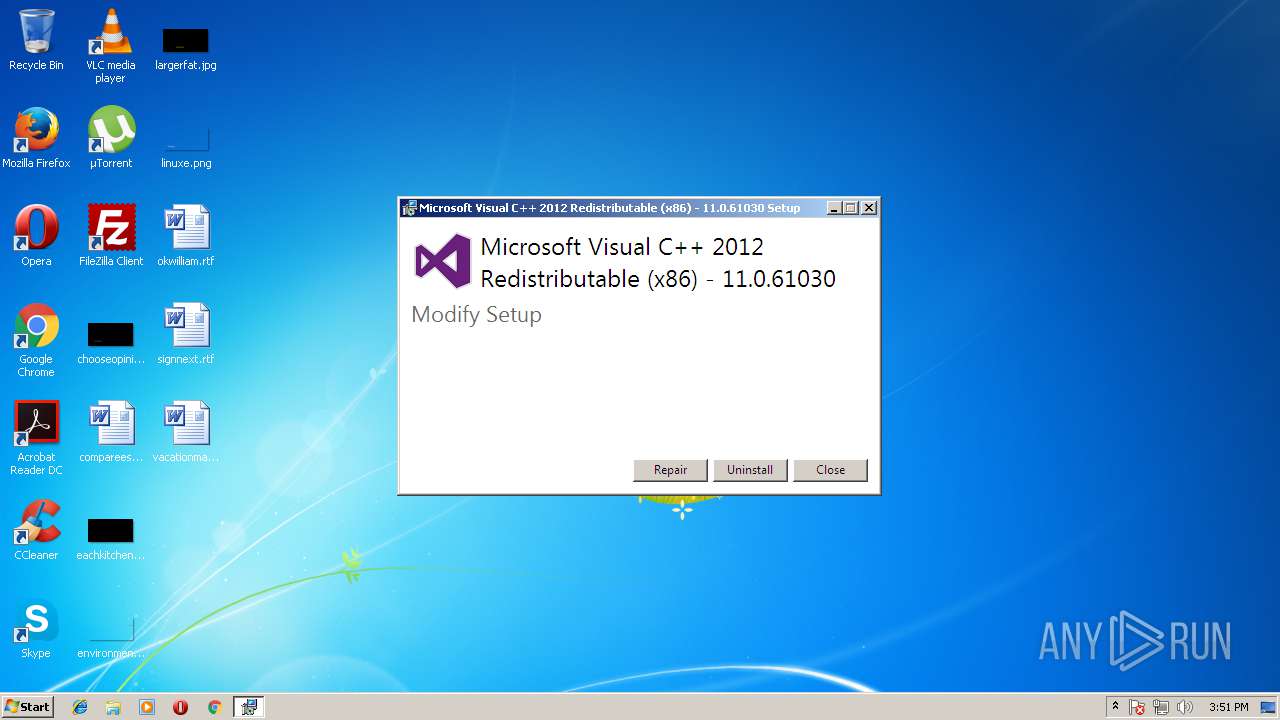
| FileDescription: | Microsoft Visual C++ 2012 Redistributable (x86) - 11.0.61030 |
| FileVersion: | 11.0.61030.0 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) Microsoft Corporation. All rights reserved. |
| OriginalFileName: | vcredist_x86.exe |
| ProductName: | Microsoft Visual C++ 2012 Redistributable (x86) - 11.0.61030 |
| ProductVersion: | 11.0.61030.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 20-Aug-2013 23:25:02 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | Microsoft Visual C++ 2012 Redistributable (x86) - 11.0.61030 |
| FileVersion: | 11.0.61030.0 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) Microsoft Corporation. All rights reserved. |
| OriginalFilename: | vcredist_x86.exe |
| ProductName: | Microsoft Visual C++ 2012 Redistributable (x86) - 11.0.61030 |
| ProductVersion: | 11.0.61030.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 20-Aug-2013 23:25:02 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0004E19A | 0x0004E200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.6013 |
.data | 0x00050000 | 0x00002E7C | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.43181 |
.wixburn8 | 0x00053000 | 0x00000038 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.739068 |
.tls | 0x00054000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00055000 | 0x00003184 | 0x00003200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.49682 |
.reloc | 0x00059000 | 0x0000415E | 0x00004200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.57742 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.3189 | 1174 | Latin 1 / Western European | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
CRYPT32.dll |
Cabinet.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
RPCRT4.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
Total processes
40
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2968 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3076 | "C:\Users\admin\AppData\Local\Temp\vcredist_x86.exe" | C:\Users\admin\AppData\Local\Temp\vcredist_x86.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Visual C++ 2012 Redistributable (x86) - 11.0.61030 Exit code: 0 Version: 11.0.61030.0 Modules
| |||||||||||||||
| 3460 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3660 | DrvInst.exe "1" "200" "STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot43" "" "" "6bb2f14fb" "00000000" "000005DC" "000003D4" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3840 | "C:\Users\admin\AppData\Local\Temp\{33d1fd90-4274-48a1-9bc1-97e33d9c2d6f}\.be\vcredist_x86.exe" -q -burn.elevated BurnPipe.{FA465D0A-565F-48A0-A761-8E615F54716C} {60A9A977-E287-4EF1-8D59-F9D0BD29EB95} 3076 | C:\Users\admin\AppData\Local\Temp\{33d1fd90-4274-48a1-9bc1-97e33d9c2d6f}\.be\vcredist_x86.exe | vcredist_x86.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2012 Redistributable (x86) - 11.0.61030 Exit code: 0 Version: 11.0.61030.0 Modules
| |||||||||||||||
Total events
1 236
Read events
687
Write events
504
Delete events
45
Modification events
| (PID) Process: | (3076) vcredist_x86.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3076) vcredist_x86.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3840) vcredist_x86.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 40000000000000006F489DFE12E6D301000F0000040F0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3840) vcredist_x86.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 40000000000000006F489DFE12E6D301000F0000040F0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3840) vcredist_x86.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 48 | |||
| (PID) Process: | (3840) vcredist_x86.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 40000000000000008DCD03FF12E6D301000F0000040F0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3840) vcredist_x86.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000E72F06FF12E6D301000F0000480B0000E803000001000000000000000000000099A93D66D25BBA40B59A83B5B8AA31A40000000000000000 | |||
| (PID) Process: | (3460) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000037E14FF12E6D301840D0000FC0F0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3460) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000037E14FF12E6D301840D0000F80F0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3460) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000037E14FF12E6D301840D0000000C0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
43
Suspicious files
14
Text files
74
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3840 | vcredist_x86.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 3460 | vssvc.exe | C: | — | |
MD5:— | SHA256:— | |||
| 3840 | vcredist_x86.exe | C:\Users\admin\AppData\Local\Temp\Cab67C4.tmp | — | |
MD5:— | SHA256:— | |||
| 3840 | vcredist_x86.exe | C:\Users\admin\AppData\Local\Temp\Tar67C5.tmp | — | |
MD5:— | SHA256:— | |||
| 2968 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF2968753DB3D06487.TMP | — | |
MD5:— | SHA256:— | |||
| 3840 | vcredist_x86.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:— | SHA256:— | |||
| 3660 | DrvInst.exe | C:\Windows\INF\setupapi.ev3 | binary | |
MD5:— | SHA256:— | |||
| 3840 | vcredist_x86.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{663da999-5bd2-40ba-b59a-83b5b8aa31a4}_OnDiskSnapshotProp | binary | |
MD5:— | SHA256:— | |||
| 3660 | DrvInst.exe | C:\Windows\INF\setupapi.dev.log | ini | |
MD5:— | SHA256:— | |||
| 3840 | vcredist_x86.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\696F3DE637E6DE85B458996D49D759AD | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.186.120:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | der | 781 b | whitelisted |
— | — | GET | 200 | 2.16.186.120:80 | http://crl.microsoft.com/pki/crl/products/MicCodSigPCA_08-31-2010.crl | unknown | der | 609 b | whitelisted |
— | — | GET | 200 | 2.16.186.120:80 | http://crl.microsoft.com/pki/crl/products/MicrosoftTimeStampPCA.crl | unknown | der | 550 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 2.16.186.120:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |