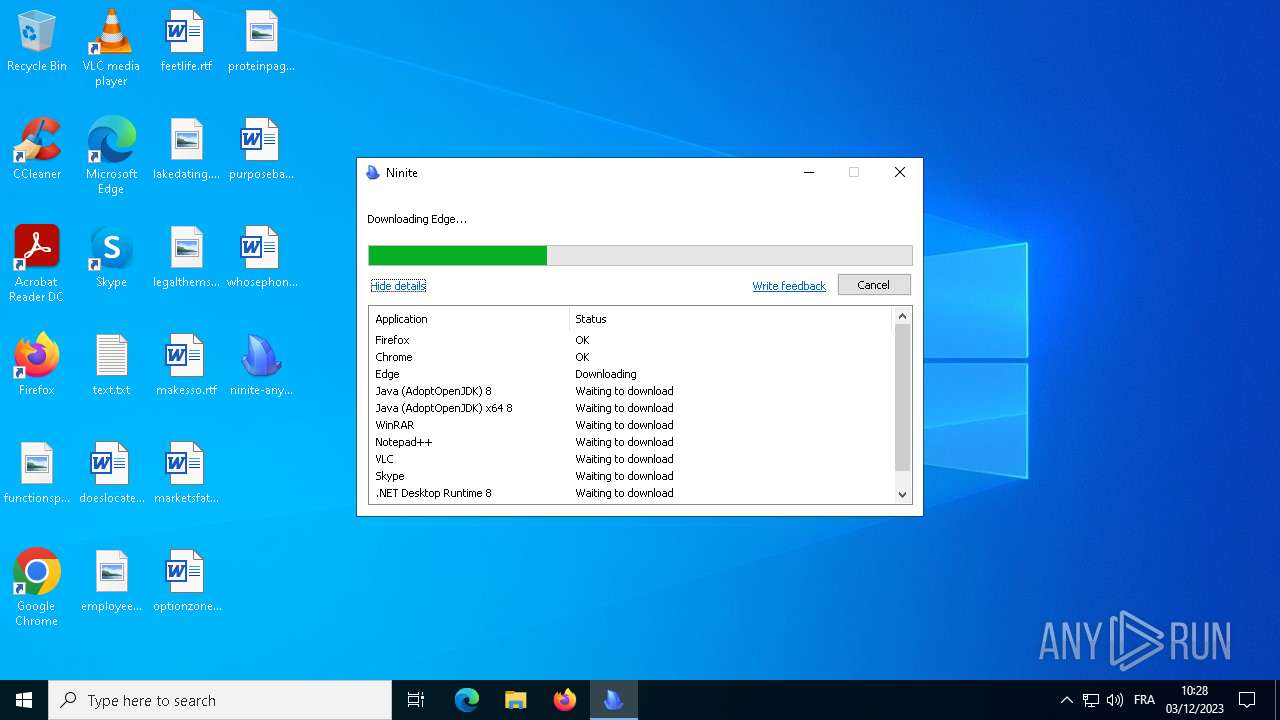
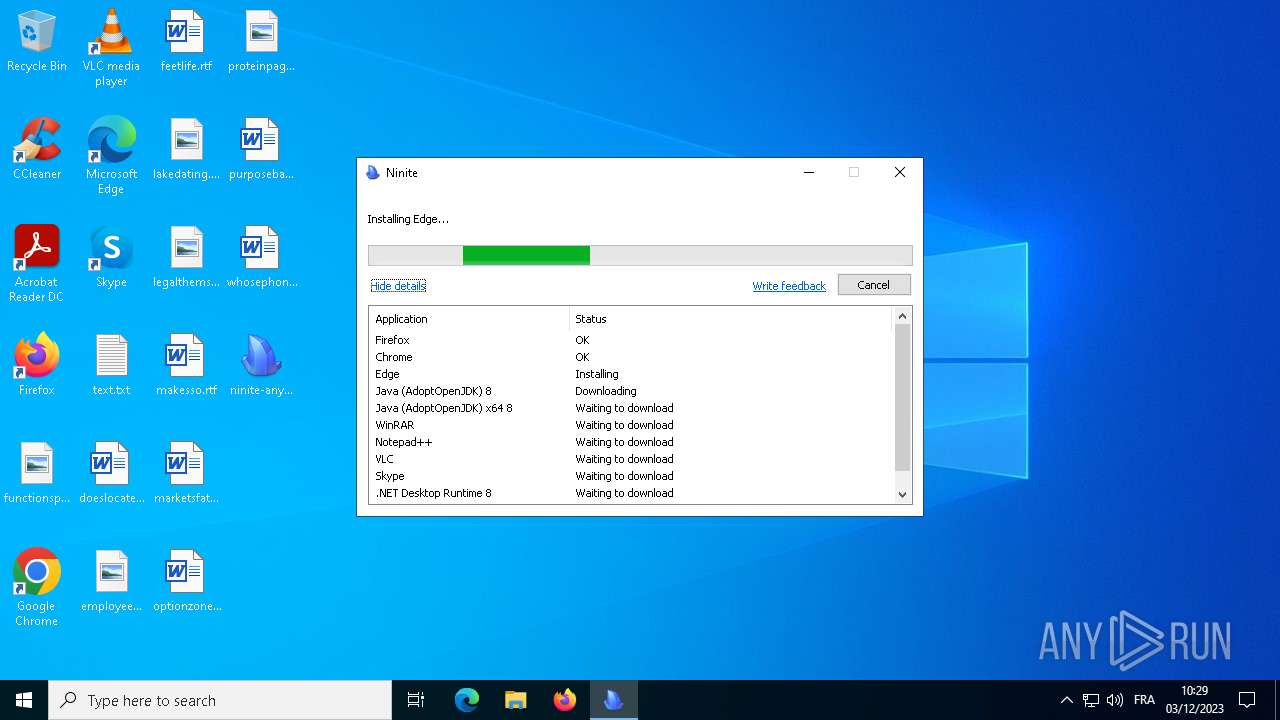
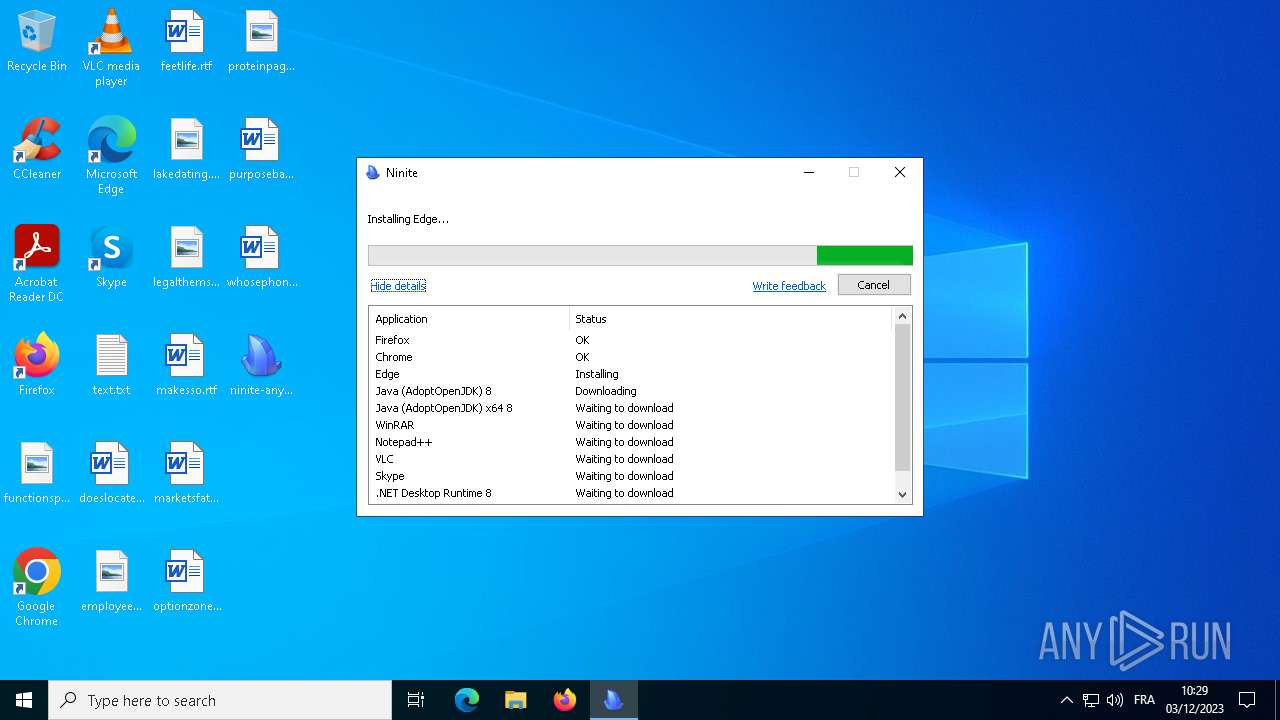
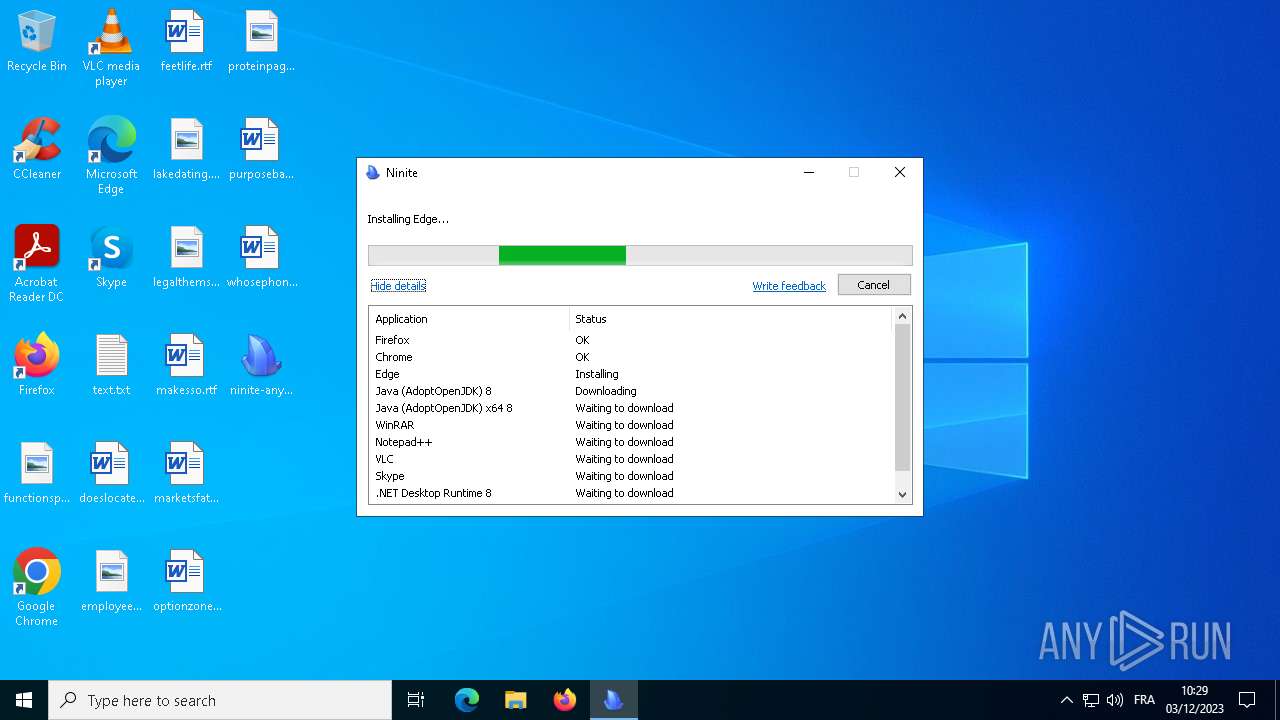
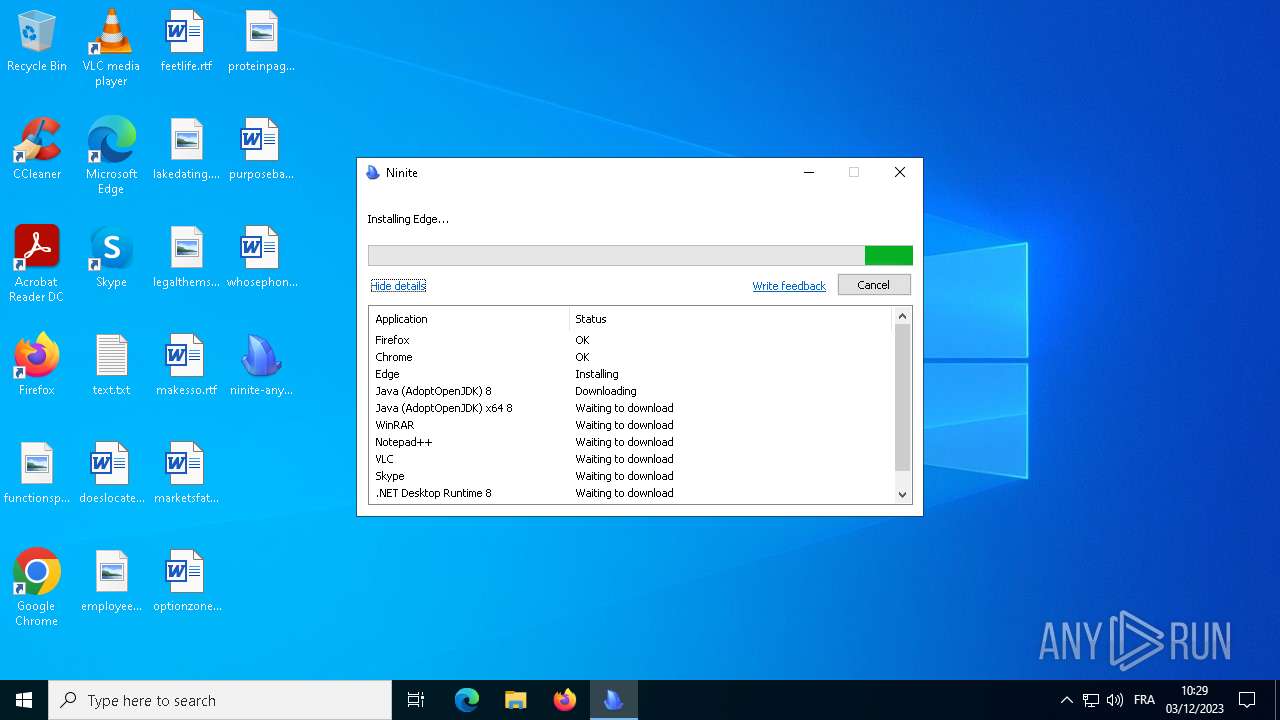
| File name: | ninite-anyrun.exe |
| Full analysis: | https://app.any.run/tasks/b23939be-57f4-46c9-9a11-1481f76c5735 |
| Verdict: | Malicious activity |
| Analysis date: | December 03, 2023, 09:25:43 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | A9F84409DC32021CACAF186E9969A5CA |
| SHA1: | C2C74EC949BD306FCE83B875A56CF6F3EF9DAC40 |
| SHA256: | B921E6E086C00D5FCA4F194C23DB49BDDC7A84DF3D11FE5E4BB3E6145B65E135 |
| SSDEEP: | 12288:MLVP603RQX2pyf+cnci2N9pKKfyeo+pW1KKRyzEw:mVP60BM2pMUN9keo+c+zEw |
MALICIOUS
Drops the executable file immediately after the start
- ninite-anyrun.exe (PID: 128)
- target.exe (PID: 6792)
- maintenanceservice_installer.exe (PID: 2060)
- setup.exe (PID: 6780)
- maintenanceservice_tmp.exe (PID: 2412)
- MSI8E23.tmp (PID: 6280)
- GoogleUpdate.exe (PID: 6728)
- chrome_installer.exe (PID: 2944)
- setup.exe (PID: 2052)
- Ninite.exe (PID: 3352)
- target.exe (PID: 2896)
- target.exe (PID: 2844)
- uninstall.exe (PID: 6812)
- target.exe (PID: 5936)
- msiexec.exe (PID: 1460)
- target.exe (PID: 5948)
- target.exe (PID: 4052)
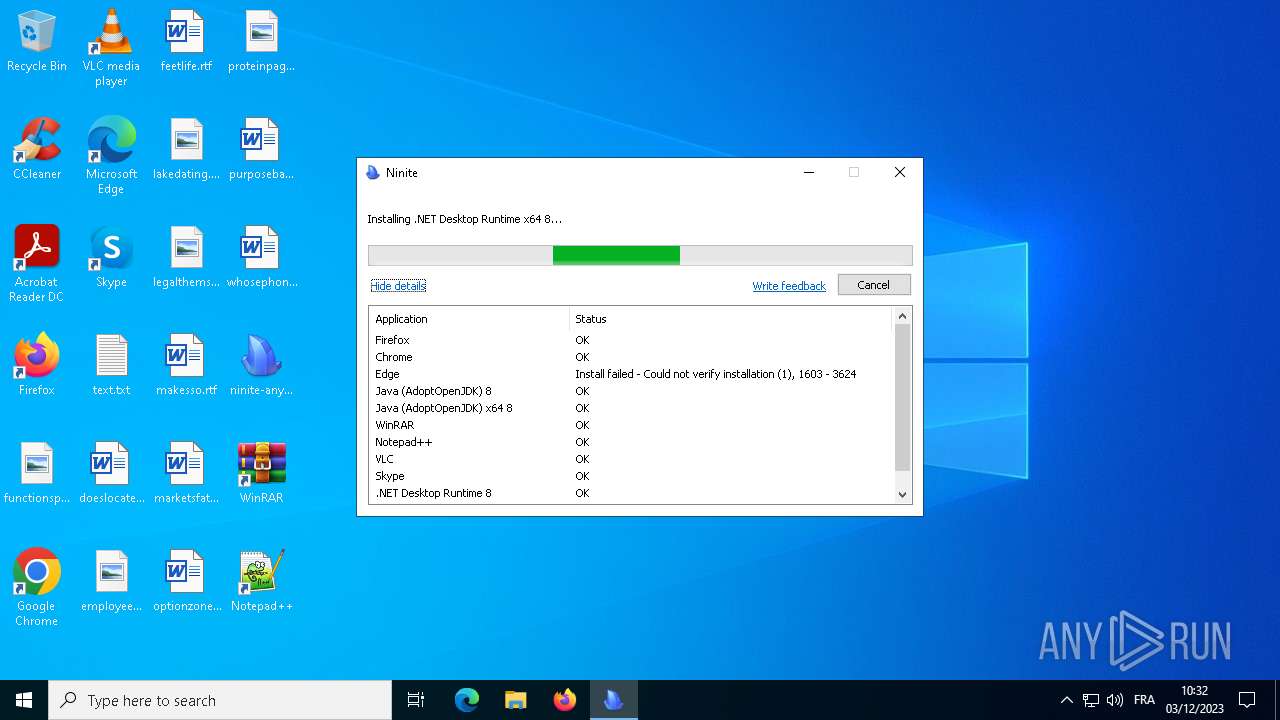
- windowsdesktop-runtime-8.0.0-win-x86.exe (PID: 6380)
- target.exe (PID: 3020)
- target.exe (PID: 2556)
- windowsdesktop-runtime-8.0.0-win-x64.exe (PID: 2652)
- MSI237D.tmp (PID: 7064)
- target.tmp (PID: 892)
- target.exe (PID: 6484)
Registers / Runs the DLL via REGSVR32.EXE
- setup.exe (PID: 6780)
- target.exe (PID: 2844)
- Un_A.exe (PID: 6600)
- target.exe (PID: 6484)
Changes the autorun value in the registry
- setup.exe (PID: 2052)
Creates a writable file in the system directory
- wermgr.exe (PID: 636)
Actions looks like stealing of personal data
- Ninite.exe (PID: 3352)
- target.tmp (PID: 892)
SUSPICIOUS
Reads security settings of Internet Explorer
- ninite-anyrun.exe (PID: 128)
- Ninite.exe (PID: 3352)
Checks Windows Trust Settings
- ninite-anyrun.exe (PID: 128)
- Ninite.exe (PID: 3352)
- msiexec.exe (PID: 1460)
Application launched itself
- Ninite.exe (PID: 2856)
- setup.exe (PID: 2052)
- setup.exe (PID: 2508)
- setup.exe (PID: 1472)
- GoogleUpdate.exe (PID: 1168)
Reads the date of Windows installation
- Ninite.exe (PID: 2856)
- GoogleUpdate.exe (PID: 6728)
- MicrosoftEdgeUpdate.exe (PID: 2936)
- target.tmp (PID: 892)
- target.exe (PID: 4052)
- target.exe (PID: 2556)
Searches for installed software
- Ninite.exe (PID: 3352)
- setup.exe (PID: 6780)
- setup.exe (PID: 1472)
- Uninstall.exe (PID: 756)
- target.exe (PID: 2844)
- target.tmp (PID: 892)
- target.exe (PID: 4052)
- windowsdesktop-runtime-8.0.0-win-x86.exe (PID: 6380)
- target.exe (PID: 2556)
- windowsdesktop-runtime-8.0.0-win-x64.exe (PID: 2652)
The process creates files with name similar to system file names
- setup.exe (PID: 6780)
- maintenanceservice_installer.exe (PID: 2060)
- target.exe (PID: 2844)
- target.exe (PID: 6484)
- msiexec.exe (PID: 1460)
Process drops legitimate windows executable
- setup.exe (PID: 6780)
- target.exe (PID: 6792)
- msiexec.exe (PID: 1460)
- MSI237D.tmp (PID: 7064)
- MicrosoftEdgeUpdate.exe (PID: 2936)
- target.tmp (PID: 892)
- target.exe (PID: 5948)
- target.exe (PID: 4052)
- windowsdesktop-runtime-8.0.0-win-x86.exe (PID: 6380)
- target.exe (PID: 3020)
- target.exe (PID: 2556)
- windowsdesktop-runtime-8.0.0-win-x64.exe (PID: 2652)
The process drops C-runtime libraries
- target.exe (PID: 6792)
- setup.exe (PID: 6780)
- msiexec.exe (PID: 1460)
- target.tmp (PID: 892)
The process drops Mozilla's DLL files
- setup.exe (PID: 6780)
- target.exe (PID: 6792)
Malware-specific behavior (creating "System.dll" in Temp)
- setup.exe (PID: 6780)
- maintenanceservice_installer.exe (PID: 2060)
- target.exe (PID: 2844)
- target.exe (PID: 6484)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 4192)
- GoogleUpdateComRegisterShell64.exe (PID: 5540)
- GoogleUpdate.exe (PID: 6928)
- GoogleUpdateComRegisterShell64.exe (PID: 1500)
- Uninstall.exe (PID: 756)
- regsvr32.exe (PID: 6856)
Loads DLL from Mozilla Firefox
- regsvr32.exe (PID: 4192)
- default-browser-agent.exe (PID: 1932)
Creates a software uninstall entry
- maintenanceservice_installer.exe (PID: 2060)
- setup.exe (PID: 1472)
- MicrosoftEdgeUpdate.exe (PID: 2936)
- Uninstall.exe (PID: 756)
- target.exe (PID: 2844)
- windowsdesktop-runtime-8.0.0-win-x86.exe (PID: 6380)
- windowsdesktop-runtime-8.0.0-win-x64.exe (PID: 2652)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 1460)
- target.tmp (PID: 892)
Disables SEHOP
- GoogleUpdate.exe (PID: 6728)
- MicrosoftEdgeUpdate.exe (PID: 2936)
Executes as Windows Service
- GoogleUpdate.exe (PID: 6500)
Starts itself from another location
- setup.exe (PID: 2052)
- uninstall.exe (PID: 6812)
- target.exe (PID: 4052)
- target.exe (PID: 2556)
Adds/modifies Windows certificates
- msiexec.exe (PID: 1460)
Checks for Java to be installed
- msiexec.exe (PID: 1460)
- Ninite.exe (PID: 3352)
Drops 7-zip archiver for unpacking
- target.exe (PID: 2896)
Process requests binary or script from the Internet
- Ninite.exe (PID: 3352)
Starts CMD.EXE for commands execution
- Ninite.exe (PID: 3352)
The process deletes folder without confirmation
- Ninite.exe (PID: 3352)
Executing commands from a ".bat" file
- Ninite.exe (PID: 3352)
Uses TASKKILL.EXE to kill process
- target.tmp (PID: 892)
The process executes via Task Scheduler
- GoogleUpdate.exe (PID: 1168)
- GoogleUpdate.exe (PID: 5168)
INFO
Checks supported languages
- ninite-anyrun.exe (PID: 128)
- Ninite.exe (PID: 2856)
- Ninite.exe (PID: 3352)
- setup.exe (PID: 6780)
- target.exe (PID: 6792)
- maintenanceservice_installer.exe (PID: 2060)
- maintenanceservice_tmp.exe (PID: 2412)
- default-browser-agent.exe (PID: 1932)
- msiexec.exe (PID: 1460)
- MSI8E23.tmp (PID: 6280)
- GoogleUpdate.exe (PID: 6728)
- msiexec.exe (PID: 5644)
- GoogleUpdate.exe (PID: 6816)
- GoogleUpdate.exe (PID: 6928)
- GoogleUpdateComRegisterShell64.exe (PID: 928)
- GoogleUpdateComRegisterShell64.exe (PID: 5540)
- GoogleUpdate.exe (PID: 6712)
- GoogleUpdateComRegisterShell64.exe (PID: 1500)
- GoogleUpdate.exe (PID: 6500)
- chrome_installer.exe (PID: 2944)
- setup.exe (PID: 2052)
- setup.exe (PID: 4944)
- setup.exe (PID: 2508)
- setup.exe (PID: 4984)
- setup.exe (PID: 1472)
- setup.exe (PID: 3332)
- msiexec.exe (PID: 4140)
- MSI237D.tmp (PID: 7064)
- MicrosoftEdgeUpdate.exe (PID: 2936)
- msiexec.exe (PID: 448)
- msiexec.exe (PID: 1712)
- msiexec.exe (PID: 6876)
- target.exe (PID: 2896)
- Uninstall.exe (PID: 756)
- target.exe (PID: 2844)
- target.exe (PID: 6484)
- uninstall.exe (PID: 6812)
- Un_A.exe (PID: 6600)
- target.tmp (PID: 892)
- target.exe (PID: 5936)
- vlc-cache-gen.exe (PID: 6480)
- target.exe (PID: 5948)
- target.exe (PID: 4052)
- windowsdesktop-runtime-8.0.0-win-x86.exe (PID: 6380)
- msiexec.exe (PID: 6880)
- msiexec.exe (PID: 5392)
- msiexec.exe (PID: 5796)
- msiexec.exe (PID: 5928)
- target.exe (PID: 3020)
- target.exe (PID: 2556)
- windowsdesktop-runtime-8.0.0-win-x64.exe (PID: 2652)
- msiexec.exe (PID: 6388)
- msiexec.exe (PID: 7120)
- msiexec.exe (PID: 1452)
- msiexec.exe (PID: 6712)
- GoogleUpdate.exe (PID: 5168)
- GoogleUpdate.exe (PID: 1168)
- GoogleCrashHandler.exe (PID: 2944)
- GoogleUpdate.exe (PID: 6724)
- GoogleCrashHandler64.exe (PID: 6788)
- GoogleUpdate.exe (PID: 7056)
Checks proxy server information
- ninite-anyrun.exe (PID: 128)
- Ninite.exe (PID: 3352)
- setup.exe (PID: 6780)
Reads the machine GUID from the registry
- ninite-anyrun.exe (PID: 128)
- Ninite.exe (PID: 3352)
- setup.exe (PID: 6780)
- msiexec.exe (PID: 1460)
- vlc-cache-gen.exe (PID: 6480)
- windowsdesktop-runtime-8.0.0-win-x86.exe (PID: 6380)
- windowsdesktop-runtime-8.0.0-win-x64.exe (PID: 2652)
Create files in a temporary directory
- ninite-anyrun.exe (PID: 128)
- setup.exe (PID: 6780)
- Ninite.exe (PID: 3352)
- target.exe (PID: 6792)
- maintenanceservice_installer.exe (PID: 2060)
- msiexec.exe (PID: 3924)
- msiexec.exe (PID: 6892)
- target.exe (PID: 2844)
- uninstall.exe (PID: 6812)
- Un_A.exe (PID: 6600)
- target.exe (PID: 6484)
- target.exe (PID: 5936)
- target.tmp (PID: 892)
- target.exe (PID: 4052)
- windowsdesktop-runtime-8.0.0-win-x86.exe (PID: 6380)
- target.exe (PID: 2556)
- windowsdesktop-runtime-8.0.0-win-x64.exe (PID: 2652)
Creates files or folders in the user directory
- ninite-anyrun.exe (PID: 128)
- Ninite.exe (PID: 3352)
- msiexec.exe (PID: 1460)
- Uninstall.exe (PID: 756)
- target.exe (PID: 2844)
- GoogleUpdate.exe (PID: 6724)
Reads the software policy settings
- ninite-anyrun.exe (PID: 128)
- Ninite.exe (PID: 3352)
- msiexec.exe (PID: 1460)
- wermgr.exe (PID: 636)
- GoogleUpdate.exe (PID: 5168)
- GoogleUpdate.exe (PID: 6724)
- MicrosoftEdgeUpdate.exe (PID: 2936)
Reads the computer name
- Ninite.exe (PID: 2856)
- ninite-anyrun.exe (PID: 128)
- Ninite.exe (PID: 3352)
- setup.exe (PID: 6780)
- maintenanceservice_installer.exe (PID: 2060)
- maintenanceservice_tmp.exe (PID: 2412)
- msiexec.exe (PID: 1460)
- msiexec.exe (PID: 5644)
- GoogleUpdate.exe (PID: 6728)
- GoogleUpdate.exe (PID: 6816)
- GoogleUpdate.exe (PID: 6928)
- GoogleUpdateComRegisterShell64.exe (PID: 5540)
- GoogleUpdateComRegisterShell64.exe (PID: 928)
- GoogleUpdateComRegisterShell64.exe (PID: 1500)
- GoogleUpdate.exe (PID: 6712)
- GoogleUpdate.exe (PID: 6500)
- chrome_installer.exe (PID: 2944)
- setup.exe (PID: 2052)
- setup.exe (PID: 2508)
- setup.exe (PID: 1472)
- msiexec.exe (PID: 4140)
- MicrosoftEdgeUpdate.exe (PID: 2936)
- msiexec.exe (PID: 448)
- msiexec.exe (PID: 1712)
- msiexec.exe (PID: 6876)
- target.exe (PID: 2896)
- Uninstall.exe (PID: 756)
- target.exe (PID: 2844)
- target.exe (PID: 6484)
- target.tmp (PID: 892)
- target.exe (PID: 4052)
- windowsdesktop-runtime-8.0.0-win-x86.exe (PID: 6380)
- msiexec.exe (PID: 6880)
- msiexec.exe (PID: 5392)
- msiexec.exe (PID: 5796)
- msiexec.exe (PID: 5928)
- target.exe (PID: 2556)
- windowsdesktop-runtime-8.0.0-win-x64.exe (PID: 2652)
- msiexec.exe (PID: 6388)
- msiexec.exe (PID: 7120)
- msiexec.exe (PID: 1452)
- msiexec.exe (PID: 6712)
- GoogleUpdate.exe (PID: 5168)
- GoogleUpdate.exe (PID: 1168)
- GoogleUpdate.exe (PID: 6724)
- GoogleCrashHandler.exe (PID: 2944)
- GoogleCrashHandler64.exe (PID: 6788)
- GoogleUpdate.exe (PID: 7056)
Creates files in the program directory
- setup.exe (PID: 6780)
- maintenanceservice_installer.exe (PID: 2060)
- MSI8E23.tmp (PID: 6280)
- GoogleUpdate.exe (PID: 6728)
- GoogleUpdate.exe (PID: 6816)
- GoogleUpdate.exe (PID: 6928)
- GoogleUpdate.exe (PID: 6712)
- GoogleUpdate.exe (PID: 6500)
- chrome_installer.exe (PID: 2944)
- setup.exe (PID: 2052)
- setup.exe (PID: 4944)
- setup.exe (PID: 2508)
- setup.exe (PID: 1472)
- MSI237D.tmp (PID: 7064)
- target.exe (PID: 2896)
- Uninstall.exe (PID: 756)
- target.exe (PID: 2844)
- vlc-cache-gen.exe (PID: 6480)
- target.exe (PID: 6484)
- windowsdesktop-runtime-8.0.0-win-x86.exe (PID: 6380)
- windowsdesktop-runtime-8.0.0-win-x64.exe (PID: 2652)
- GoogleUpdate.exe (PID: 5168)
- GoogleUpdate.exe (PID: 1168)
- GoogleUpdate.exe (PID: 6724)
- GoogleCrashHandler.exe (PID: 2944)
- GoogleCrashHandler64.exe (PID: 6788)
- GoogleUpdate.exe (PID: 7056)
- target.tmp (PID: 892)
Application launched itself
- firefox.exe (PID: 6832)
- firefox.exe (PID: 1696)
Starts application with an unusual extension
- msiexec.exe (PID: 1460)
Reads Environment values
- msiexec.exe (PID: 1460)
- MicrosoftEdgeUpdate.exe (PID: 2936)
- target.exe (PID: 2844)
Process checks computer location settings
- MicrosoftEdgeUpdate.exe (PID: 2936)
- target.exe (PID: 2896)
- target.exe (PID: 4052)
- target.exe (PID: 2556)
- target.tmp (PID: 892)
Dropped object may contain TOR URL's
- target.exe (PID: 2844)
The executable file from the user directory is run by the CMD process
- target.exe (PID: 5936)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:04:12 02:19:47+02:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 233472 |
| InitializedDataSize: | 182272 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1a53a |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.1.1.1183 |
| ProductVersionNumber: | 0.1.1.1183 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Secure By Design Inc. |
| FileDescription: | Ninite |
| FileVersion: | 0,1,1,1183 |
| InternalName: | Ninite |
| LegalCopyright: | Copyright (C) 2009 Secure By Design Inc |
| OriginalFileName: | - |
| ProductName: | Ninite |
| ProductVersion: | 0,1,1,1183 |
Total processes
210
Monitored processes
85
Malicious processes
24
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\Users\admin\Desktop\ninite-anyrun.exe" | C:\Users\admin\Desktop\ninite-anyrun.exe | explorer.exe | ||||||||||||
User: admin Company: Secure By Design Inc. Integrity Level: MEDIUM Description: Ninite Exit code: 0 Version: 0,1,1,1183 Modules
| |||||||||||||||
| 364 | msiexec.exe /i "C:\Users\admin\AppData\Local\Temp\750892~1\target.msi" /qn /norestart REBOOT=ReallySuppress ALLUSERS=1 INSTALLLEVEL=3 | C:\Windows\SysWOW64\msiexec.exe | — | Ninite.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 448 | C:\Windows\syswow64\MsiExec.exe -Embedding F4E79354299AF76AB94B007197C80FA9 E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 636 | "C:\WINDOWS\system32\wermgr.exe" "-outproc" "0" "2936" "1928" "1608" "1932" "0" "0" "0" "0" "0" "0" "0" "0" | C:\Windows\SysWOW64\wermgr.exe | MicrosoftEdgeUpdate.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1081 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 756 | "C:\Program Files\WinRAR\uninstall.exe" /setup | C:\Program Files\WinRAR\Uninstall.exe | — | target.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: HIGH Description: Uninstall WinRAR Exit code: 0 Version: 6.24.0 Modules
| |||||||||||||||
| 892 | "C:\Users\admin\AppData\Local\Temp\is-I5JP9.tmp\target.tmp" /SL5="$E01E4,88308993,404480,C:\Users\admin\AppData\Local\Temp\9FE92B~1\target.exe" /VerySilent /NoRestart | C:\Users\admin\AppData\Local\Temp\is-I5JP9.tmp\target.tmp | target.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 928 | "C:\Program Files (x86)\Google\Update\1.3.36.311\GoogleUpdateComRegisterShell64.exe" | C:\Program Files (x86)\Google\Update\1.3.36.311\GoogleUpdateComRegisterShell64.exe | — | GoogleUpdate.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 1168 | "C:\Program Files (x86)\Google\Update\GoogleUpdate.exe" /c | C:\Program Files (x86)\Google\Update\GoogleUpdate.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Installer Exit code: 0 Version: 1.3.36.51 Modules
| |||||||||||||||
| 1324 | /s "C:\Program Files\VideoLAN\VLC\axvlc.dll" | C:\Windows\System32\regsvr32.exe | — | regsvr32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1452 | C:\Windows\syswow64\MsiExec.exe -Embedding 8F68DEA290B46422D2365C4795E7EE65 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
68 221
Read events
65 624
Write events
775
Delete events
1 822
Modification events
| (PID) Process: | (128) ninite-anyrun.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (128) ninite-anyrun.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (128) ninite-anyrun.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (128) ninite-anyrun.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2856) Ninite.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2856) Ninite.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2856) Ninite.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2856) Ninite.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3352) Ninite.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3352) Ninite.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
2 147
Suspicious files
627
Text files
562
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3352 | Ninite.exe | C:\Users\admin\AppData\Local\Temp\fe21cfd0-91bd-11ee-b4d2-18f7786f96ee\target.exe_fe21cfd2-91bd-11ee-b4d2-18f7786f96ee | — | |
MD5:— | SHA256:— | |||
| 3352 | Ninite.exe | C:\Users\admin\AppData\Local\Temp\fe21cfd0-91bd-11ee-b4d2-18f7786f96ee\target.exe | — | |
MD5:— | SHA256:— | |||
| 128 | ninite-anyrun.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\75CA58072B9926F763A91F0CC2798706_645BC4A49DCDC40FE5917FA45C6D4517 | binary | |
MD5:388DF9D0EA05A46CC6515A59C6FB62AD | SHA256:D2897ECB3304927C2E52CE2D2428537814C40253D8CF7FF323F534D1225000D3 | |||
| 3352 | Ninite.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\F2DDCD2B5F37625B82E81F4976CEE400_8FF5BE4204C5F704E3914BEF4952C317 | binary | |
MD5:03356FB1D4796FD1E42ABE75E8DB617C | SHA256:A39E5B8DE3E0B71BDFD8D1AC36D119E659C20D346914AE5E41166BE451566686 | |||
| 3352 | Ninite.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:51029E171FE3A2C47D36B4E6E1107B46 | SHA256:5FCF047D5230D6FC2121CC22C4617997137E7815DA0C609ABDF3253913FCD245 | |||
| 128 | ninite-anyrun.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\A1D627669EFC8CD4F21BCF387D97F9B5_BCCFCBC66B448214318C9391CA0E275F | binary | |
MD5:D031D103ABD147AFAEA5BD4D5058F46B | SHA256:435B091F292D57F6422EC56DE9FC3A8C42F0ACADEE6EF8126593ECFA118DA05D | |||
| 128 | ninite-anyrun.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\A1D627669EFC8CD4F21BCF387D97F9B5_BCCFCBC66B448214318C9391CA0E275F | binary | |
MD5:6B99BDA9F593FA9108E8B0505827F877 | SHA256:A8A12283A50003C87C49A0D7FC1C359C729B844FC8988B81F76427AF903E6FF7 | |||
| 3352 | Ninite.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\46601BB2A7864E9EC2BBA825A8FC06E1 | binary | |
MD5:5EBCE1CA3889FD5D126C1922D9C2D779 | SHA256:24F0E332A783D73EF1586C78BCCCC96DC7B86C3C99BED74214D07B84DDE0B4B3 | |||
| 6792 | target.exe | C:\Users\admin\AppData\Local\Temp\7zS88AEF2E4\core\application.ini | text | |
MD5:CE3F63440B7D6F2434E6D0ED3DA63349 | SHA256:5903DC1D6DD35554D99CA71F19757B75D957527D7719CBEF301ACCBAC26AC289 | |||
| 3352 | Ninite.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\46601BB2A7864E9EC2BBA825A8FC06E1 | binary | |
MD5:78FB998C794C5D837415DC308CFEE215 | SHA256:C5B304531F08B03C44D96C24FA6E6F5D6F689B8C4C3DA067120417BEC8EB665B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
38
TCP/UDP connections
69
DNS requests
31
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
128 | ninite-anyrun.exe | GET | 200 | 18.66.190.71:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwdzEkzUBtJnwJkc3SmanzgxeYU%3D | unknown | binary | 1.39 Kb | unknown |
4868 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | unknown | binary | 471 b | unknown |
128 | ninite-anyrun.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/rootr3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEHgDGEJFcIpBz28BuO60qVQ%3D | unknown | binary | 1.40 Kb | unknown |
128 | ninite-anyrun.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/codesigningrootr45/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQVFZP5vqhCrtRN5SWf40Rn6NM1IAQUHwC%2FRoAK%2FHg5t6W0Q9lWULvOljsCEHe9DgOhtwj4VKsGchDZBEc%3D | unknown | binary | 1.67 Kb | unknown |
128 | ninite-anyrun.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/gsgccr45codesignca2020/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBTLuA3ygnKW%2F7xuSx%2F09F%2BhHVuEUQQU2rONwCSQo2t30wygWd0hZ2R2C3gCDGPUxoqhhiZifL455A%3D%3D | unknown | binary | 1.64 Kb | unknown |
3352 | Ninite.exe | GET | 200 | 184.24.77.54:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgSwUTPS41fHcx80eIwxy6iZxw%3D%3D | unknown | binary | 503 b | unknown |
5056 | SIHClient.exe | GET | 200 | 23.218.209.163:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | binary | 418 b | unknown |
5056 | SIHClient.exe | GET | 200 | 23.218.209.163:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | binary | 409 b | unknown |
2152 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | binary | 471 b | unknown |
3352 | Ninite.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | binary | 1.41 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
128 | ninite-anyrun.exe | 108.138.36.69:443 | ninite.com | AMAZON-02 | US | unknown |
128 | ninite-anyrun.exe | 18.66.190.71:80 | ocsp.rootca1.amazontrust.com | AMAZON-02 | US | unknown |
4868 | backgroundTaskHost.exe | 20.223.35.26:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4868 | backgroundTaskHost.exe | 192.229.221.95:80 | — | EDGECAST | US | whitelisted |
128 | ninite-anyrun.exe | 104.18.20.226:80 | ocsp.globalsign.com | CLOUDFLARENET | — | shared |
3352 | Ninite.exe | 108.138.36.69:443 | ninite.com | AMAZON-02 | US | unknown |
3352 | Ninite.exe | 34.117.35.28:443 | download-installer.cdn.mozilla.net | GOOGLE-CLOUD-PLATFORM | US | unknown |
3352 | Ninite.exe | 184.24.77.54:80 | r3.o.lencr.org | Akamai International B.V. | DE | unknown |
2224 | svchost.exe | 20.190.159.68:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ninite.com |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| shared |
arc.msn.com |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
download-installer.cdn.mozilla.net |
| whitelisted |
r3.o.lencr.org |
| shared |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
dl.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3352 | Ninite.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3352 | Ninite.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
Process | Message |
|---|---|
vlc-cache-gen.exe | main libvlc debug: Copyright © 1996-2023 the VideoLAN team
|
vlc-cache-gen.exe | main libvlc debug: revision 3.0.20-0-g6f0d0ab126
|
vlc-cache-gen.exe | main libvlc debug: VLC media player - 3.0.20 Vetinari
|
vlc-cache-gen.exe | main libvlc debug: using multimedia timers as clock source
|
vlc-cache-gen.exe | main libvlc debug: min period: 1 ms, max period: 1000000 ms
|
vlc-cache-gen.exe | main libvlc debug: configured with /builds/videolan/vlc/extras/package/win32/../../../configure '--enable-update-check' '--enable-lua' '--enable-faad' '--enable-flac' '--enable-theora' '--enable-avcodec' '--enable-merge-ffmpeg' '--enable-dca' '--enable-mpc' '--enable-libass' '--enable-schroedinger' '--enable-realrtsp' '--enable-live555' '--enable-shout' '--enable-goom' '--enable-sse' '--enable-mmx' '--enable-libcddb' '--enable-zvbi' '--disable-telx' '--enable-nls' '--host=x86_64-w64-mingw32' '--with-contrib=../contrib/x86_64-w64-mingw32' '--with-breakpad=https://win.crashes.videolan.org' '--enable-qt' '--enable-skins2' '--enable-dvdread' '--enable-caca' 'host_alias=x86_64-w64-mingw32' 'CFLAGS= -D_WIN32_WINNT=0x0502 -DWINVER=0x502 -D__MSVCRT_VERSION__=0x700 ' 'CXXFLAGS= -D_WIN32_WINNT=0x0502 -DWINVER=0x502 -D__MSVCRT_VERSION__=0x700 ' 'PKG_CONFIG=pkg-config' 'PKG_CONFIG_LIBDIR=/usr/x86_64-w64-mingw32/lib/pkgconfig:/usr/lib/x86_64-w64-mingw32/pkgconfig'
|
vlc-cache-gen.exe | main libvlc debug: ignoring plugins cache file
|
vlc-cache-gen.exe | main libvlc debug: recursively browsing `C:\Program Files\VideoLAN\VLC\plugins'
|
vlc-cache-gen.exe | main libvlc debug: searching plug-in modules
|
vlc-cache-gen.exe | main libvlc debug: saving plugins cache C:\Program Files\VideoLAN\VLC\plugins\plugins.dat
|