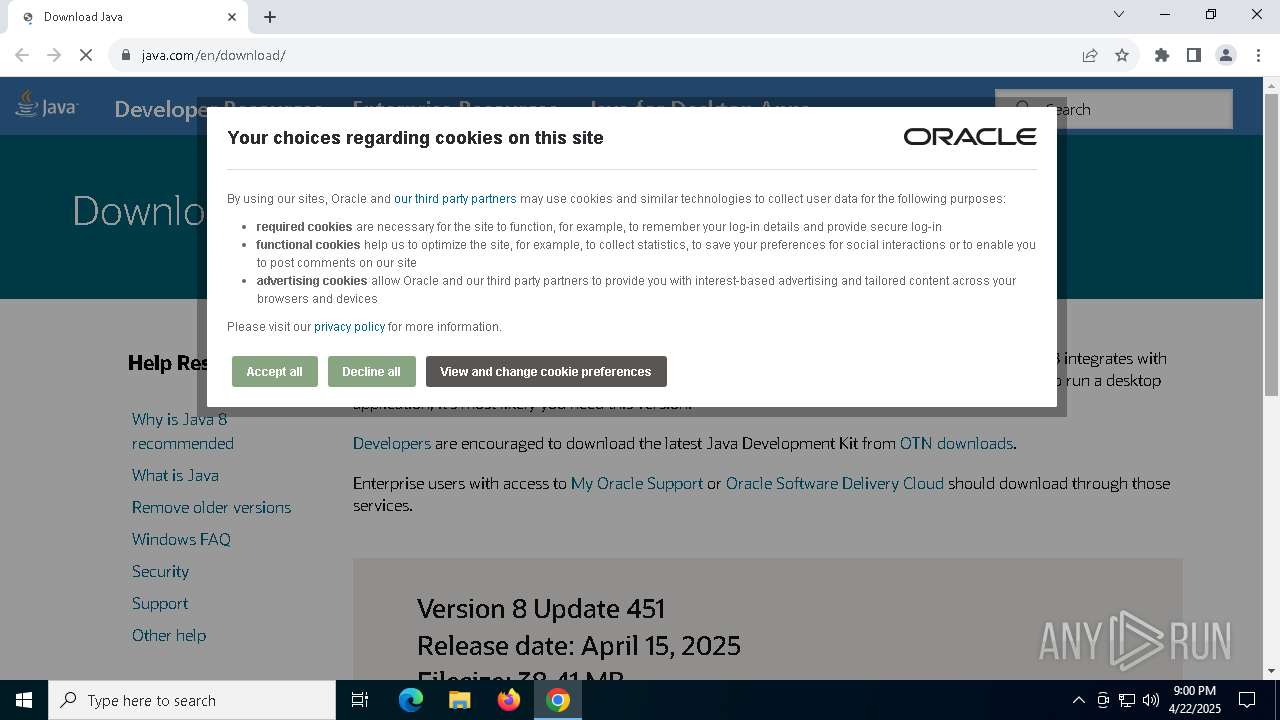
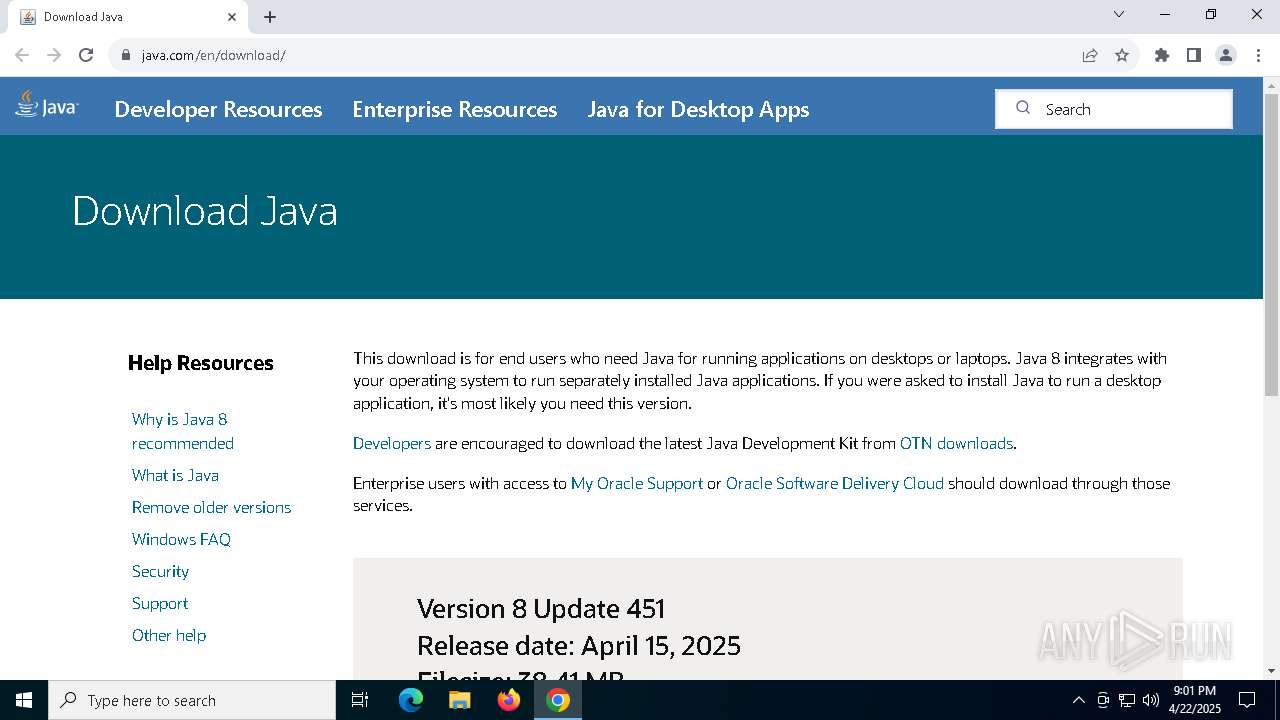
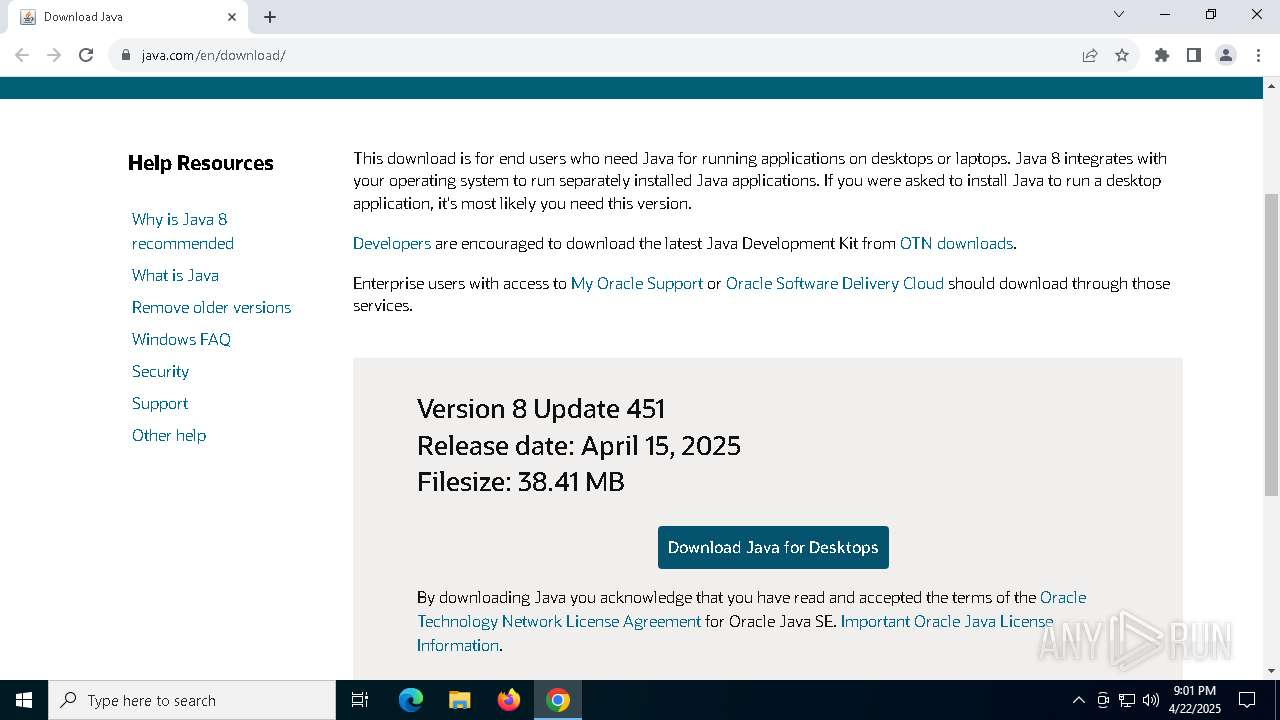
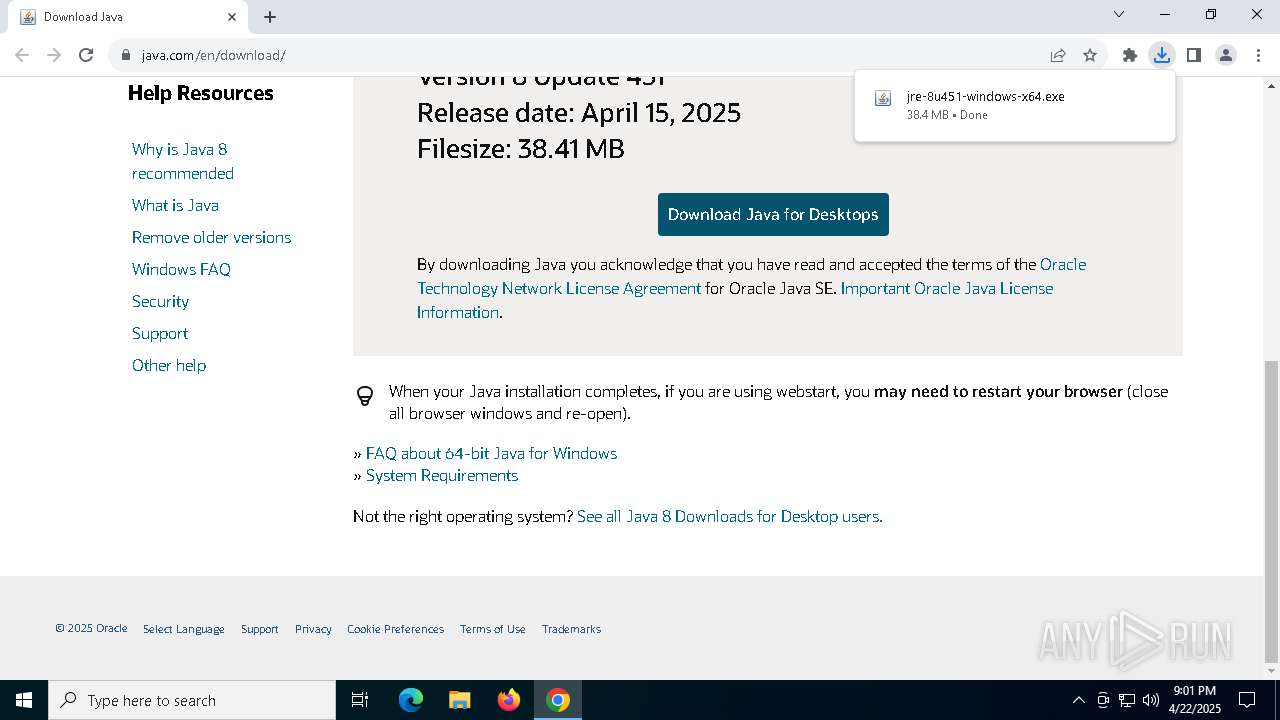
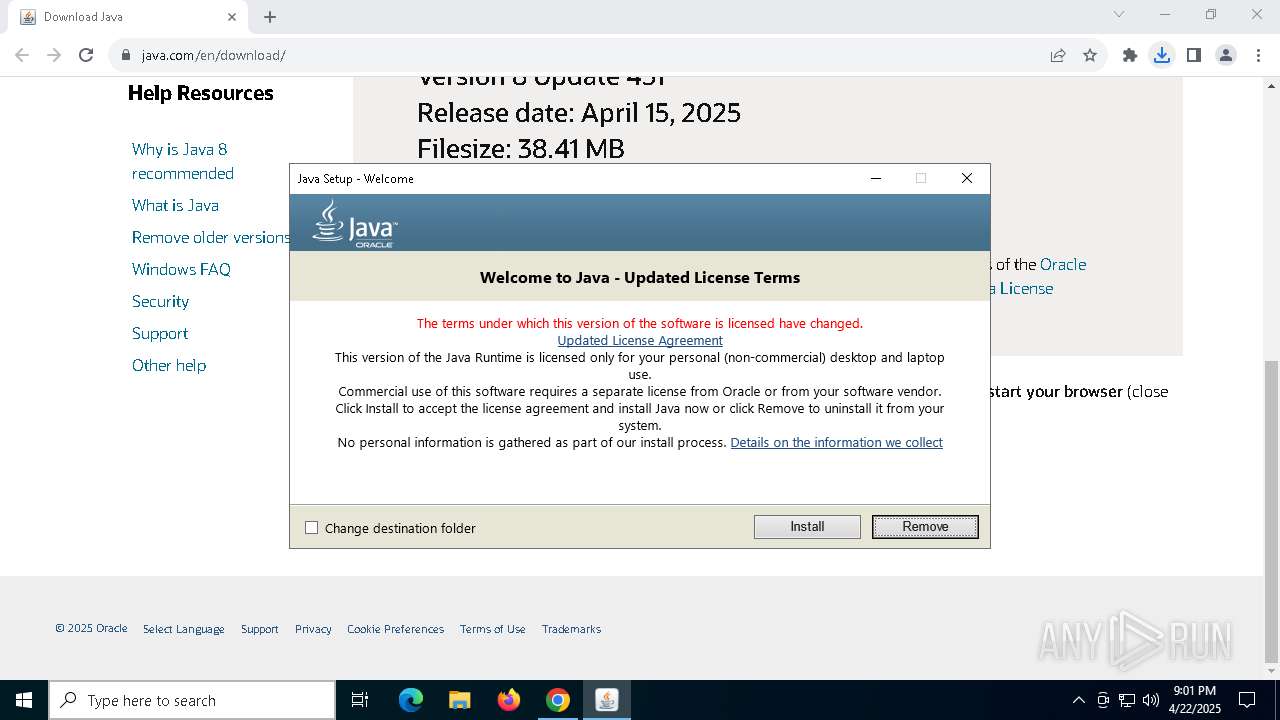
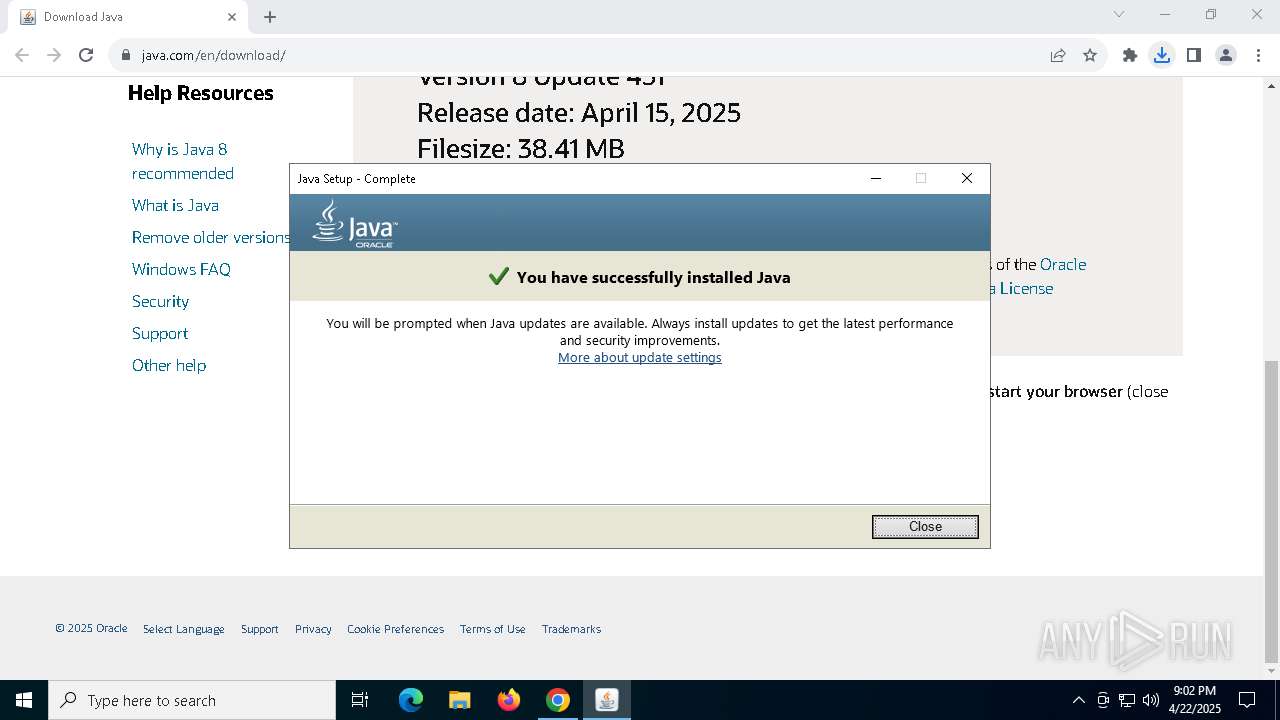
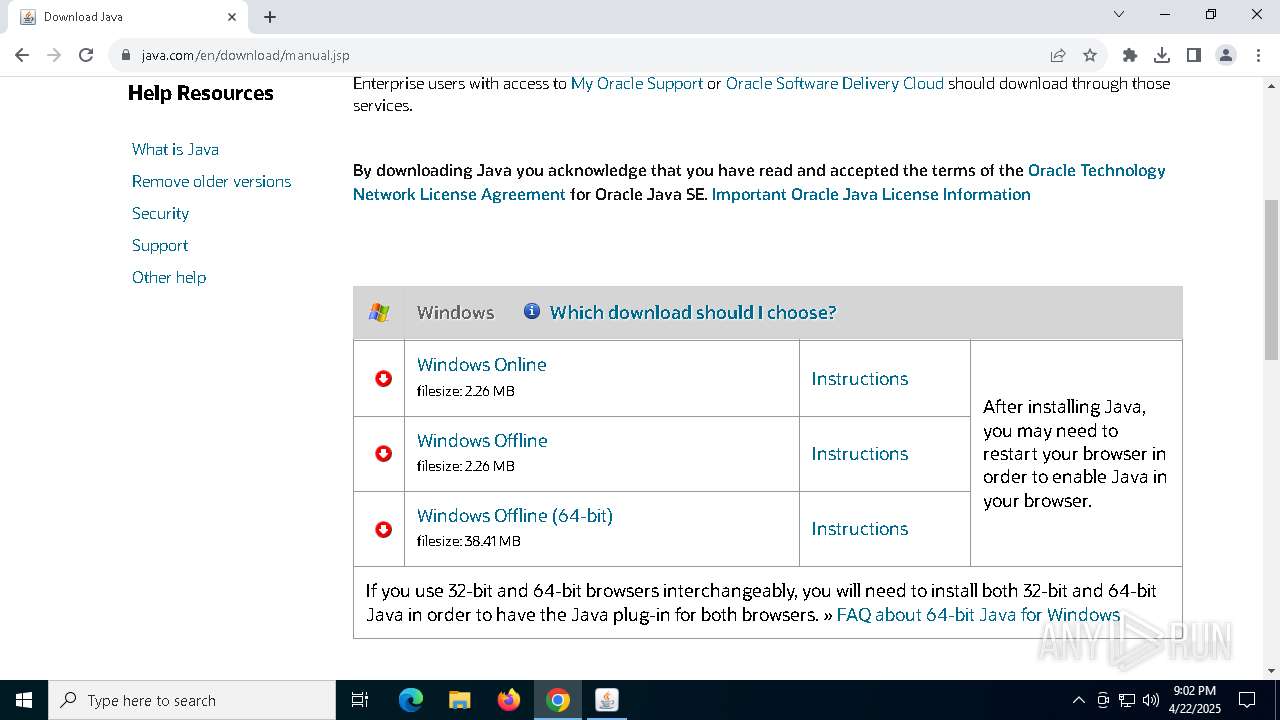
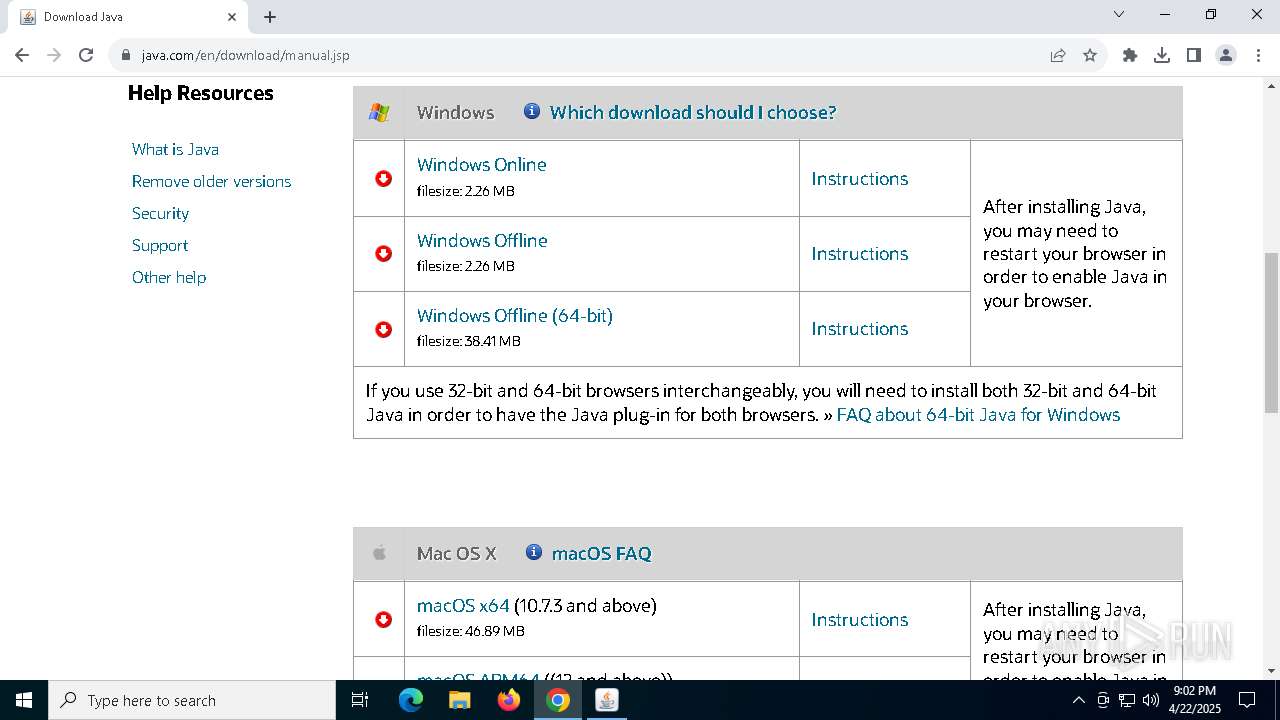
| URL: | https://www.java.com/en/download/ |
| Full analysis: | https://app.any.run/tasks/e1593c33-bdef-48a9-8af7-20ff7a472df8 |
| Verdict: | Malicious activity |
| Analysis date: | April 22, 2025, 21:00:45 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 84607FB83B5206C656EDBCB6BB307062 |
| SHA1: | CDA2463B0319486995625E3D6D673B16DC76792E |
| SHA256: | B909AA08DF51B2D4DA578EF72009B4D6FC9F6B013F7A9D7A66D73767ECEABFA4 |
| SSDEEP: | 3:N8DSL8TiGK1BKSCn:2OL8huB4 |
MALICIOUS
No malicious indicators.SUSPICIOUS
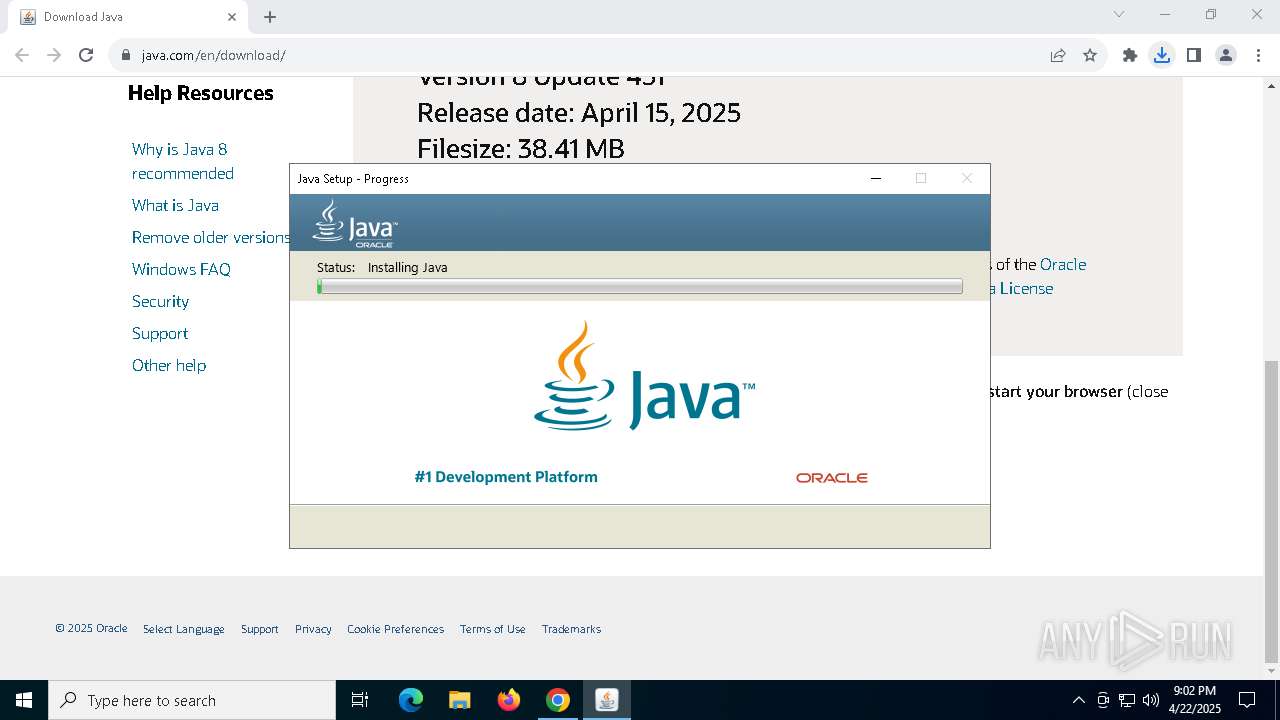
Checks for Java to be installed
- jre-8u451-windows-x64.exe (PID: 5384)
- msiexec.exe (PID: 6660)
- msiexec.exe (PID: 6392)
- installer.exe (PID: 7664)
- jp2launcher.exe (PID: 7944)
- jp2launcher.exe (PID: 2596)
- ssvagent.exe (PID: 4688)
- msiexec.exe (PID: 6572)
- javaw.exe (PID: 5136)
Reads security settings of Internet Explorer
- jre-8u451-windows-x64.exe (PID: 5384)
- installer.exe (PID: 7664)
- jp2launcher.exe (PID: 7944)
- jp2launcher.exe (PID: 2596)
Reads Microsoft Outlook installation path
- jre-8u451-windows-x64.exe (PID: 5384)
Application launched itself
- msiexec.exe (PID: 6392)
Reads Internet Explorer settings
- jre-8u451-windows-x64.exe (PID: 5384)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 6392)
Reads Mozilla Firefox installation path
- MSIF5E3.tmp (PID: 680)
- installer.exe (PID: 7664)
Executable content was dropped or overwritten
- installer.exe (PID: 7664)
Process drops legitimate windows executable
- msiexec.exe (PID: 6392)
The process drops C-runtime libraries
- msiexec.exe (PID: 6392)
Creates/Modifies COM task schedule object
- installer.exe (PID: 7664)
- ssvagent.exe (PID: 4688)
INFO
Create files in a temporary directory
- jre-8u451-windows-x64.exe (PID: 8008)
- MSIF5E3.tmp (PID: 680)
- javaw.exe (PID: 3968)
- jp2launcher.exe (PID: 7944)
- jp2launcher.exe (PID: 2596)
Executable content was dropped or overwritten
- chrome.exe (PID: 2148)
- msiexec.exe (PID: 6392)
Java executable
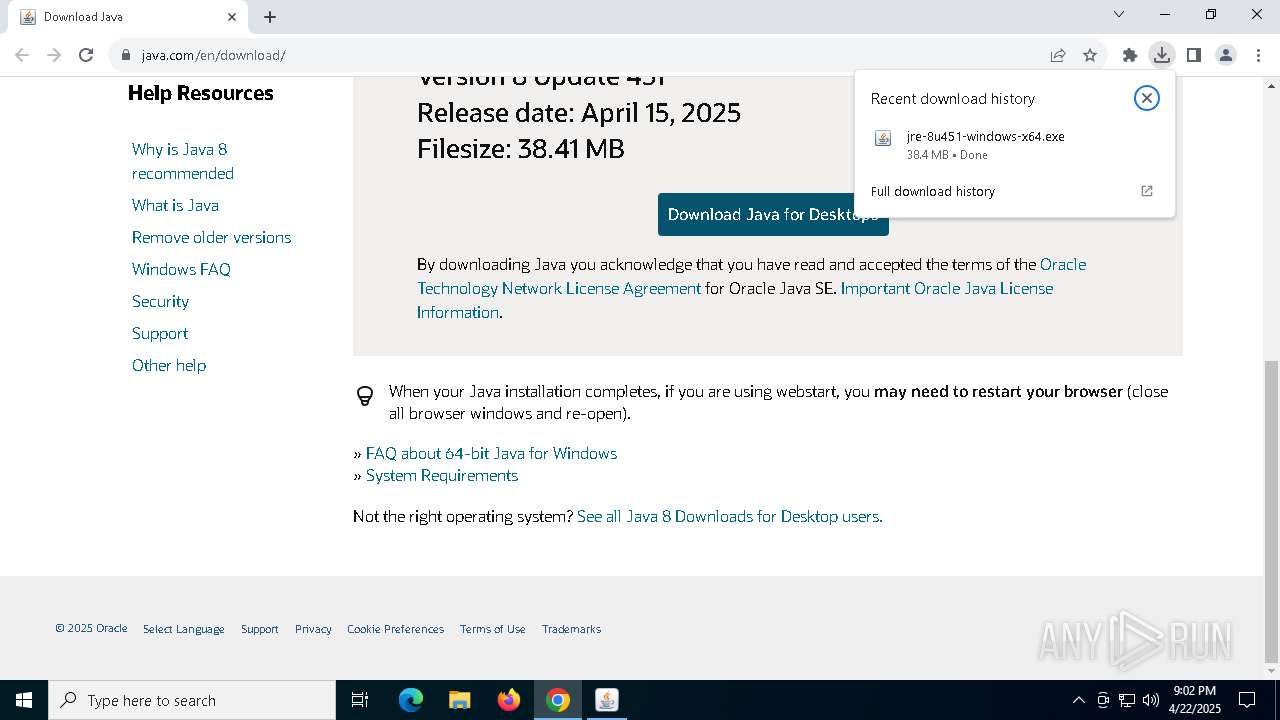
- jre-8u451-windows-x64.exe (PID: 8008)
- jre-8u451-windows-x64.exe (PID: 7968)
- jre-8u451-windows-x64.exe (PID: 5384)
- MSIF5E3.tmp (PID: 680)
- installer.exe (PID: 7664)
Reads the computer name
- jre-8u451-windows-x64.exe (PID: 8008)
- jre-8u451-windows-x64.exe (PID: 5384)
- msiexec.exe (PID: 6660)
- msiexec.exe (PID: 6392)
- MSIF5E3.tmp (PID: 680)
- installer.exe (PID: 7664)
- javaws.exe (PID: 7852)
- jp2launcher.exe (PID: 7944)
- jp2launcher.exe (PID: 2596)
- javaws.exe (PID: 8164)
- msiexec.exe (PID: 6572)
- msiexec.exe (PID: 644)
- javaw.exe (PID: 5136)
- javaw.exe (PID: 6872)
Checks supported languages
- jre-8u451-windows-x64.exe (PID: 8008)
- jre-8u451-windows-x64.exe (PID: 5384)
- msiexec.exe (PID: 6660)
- msiexec.exe (PID: 6392)
- MSIF5E3.tmp (PID: 680)
- jaureg.exe (PID: 7600)
- installer.exe (PID: 7664)
- javaw.exe (PID: 3968)
- ssvagent.exe (PID: 4688)
- javaws.exe (PID: 7852)
- javaws.exe (PID: 8164)
- jp2launcher.exe (PID: 2596)
- msiexec.exe (PID: 6572)
- jp2launcher.exe (PID: 7944)
- javaw.exe (PID: 5136)
- javaw.exe (PID: 6872)
- msiexec.exe (PID: 644)
Application launched itself
- chrome.exe (PID: 2148)
Reads Environment values
- jre-8u451-windows-x64.exe (PID: 5384)
Reads the machine GUID from the registry
- jre-8u451-windows-x64.exe (PID: 5384)
- msiexec.exe (PID: 6392)
Checks proxy server information
- jre-8u451-windows-x64.exe (PID: 5384)
- jp2launcher.exe (PID: 7944)
- slui.exe (PID: 516)
- jp2launcher.exe (PID: 2596)
Reads the software policy settings
- jre-8u451-windows-x64.exe (PID: 5384)
- slui.exe (PID: 7740)
- msiexec.exe (PID: 6392)
- slui.exe (PID: 516)
Creates files or folders in the user directory
- jre-8u451-windows-x64.exe (PID: 5384)
- msiexec.exe (PID: 6392)
The sample compiled with english language support
- msiexec.exe (PID: 6392)
- installer.exe (PID: 7664)
Reads CPU info
- msiexec.exe (PID: 6392)
Starts application with an unusual extension
- msiexec.exe (PID: 6392)
Creates a software uninstall entry
- msiexec.exe (PID: 6392)
Creates files in the program directory
- javaw.exe (PID: 3968)
- installer.exe (PID: 7664)
Local mutex for internet shortcut management
- installer.exe (PID: 7664)
JAVA mutex has been found
- jp2launcher.exe (PID: 7944)
- jp2launcher.exe (PID: 2596)
- msiexec.exe (PID: 644)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
182
Monitored processes
45
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 516 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 644 | C:\Windows\syswow64\MsiExec.exe -Embedding 315C03A26D5B72F8E36FACB30DBFC49A E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 680 | "C:\WINDOWS\Installer\MSIF5E3.tmp" INSTALLDIR="C:\Program Files\Java\jre1.8.0_271\\" ProductCode={26A24AE4-039D-4CA4-87B4-2F64180271F0} /s BASEIMAGECHECKSUMSHA256= | C:\Windows\Installer\MSIF5E3.tmp | — | msiexec.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 1348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=2080 --field-trial-handle=1908,i,3774153436295833503,12100124424764935068,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1452 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | jaureg.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "https://www.java.com/en/download/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2596 | "C:\Program Files\Java\jre1.8.0_451\bin\jp2launcher.exe" -secure -javaws -jre "C:\Program Files\Java\jre1.8.0_451" -vma LWNsYXNzcGF0aABDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfNDUxXGxpYlxkZXBsb3kuamFyAC1EamF2YS5zZWN1cml0eS5wb2xpY3k9ZmlsZTpDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfNDUxXGxpYlxzZWN1cml0eVxqYXZhd3MucG9saWN5AC1EdHJ1c3RQcm94eT10cnVlAC1YdmVyaWZ5OnJlbW90ZQAtRGpubHB4LmhvbWU9QzpcUHJvZ3JhbSBGaWxlc1xKYXZhXGpyZTEuOC4wXzQ1MVxiaW4ALURqYXZhLnNlY3VyaXR5Lm1hbmFnZXIALURzdW4uYXd0Lndhcm11cD10cnVlAC1YYm9vdGNsYXNzcGF0aC9hOkM6XFByb2dyYW0gRmlsZXNcSmF2YVxqcmUxLjguMF80NTFcbGliXGphdmF3cy5qYXI7QzpcUHJvZ3JhbSBGaWxlc1xKYXZhXGpyZTEuOC4wXzQ1MVxsaWJcZGVwbG95LmphcjtDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfNDUxXGxpYlxwbHVnaW4uamFyAC1EamF2YS5hd3QuaGVhZGxlc3M9dHJ1ZQAtRGpubHB4Lmp2bT1DOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfNDUxXGJpblxqYXZhdy5leGU= -ma LXdhaXQALWZpeAAtc2hvcnRjdXQALXNpbGVudAAtbm90V2ViSmF2YQ== | C:\Program Files\Java\jre1.8.0_451\bin\jp2launcher.exe | — | javaws.exe | |||||||||||
User: SYSTEM Company: Oracle Corporation Integrity Level: SYSTEM Description: Java(TM) Web Launcher Exit code: 0 Version: 11.451.0.10 Modules
| |||||||||||||||
| 3768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --extension-process --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=17 --mojo-platform-channel-handle=4692 --field-trial-handle=1908,i,3774153436295833503,12100124424764935068,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 3968 | "C:\Program Files\Java\jre1.8.0_451\bin\javaw.exe" -Xshare:dump -Djdk.disableLastUsageTracking | C:\Program Files\Java\jre1.8.0_451\bin\javaw.exe | installer.exe | ||||||||||||
User: SYSTEM Company: Oracle Corporation Integrity Level: SYSTEM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.4510.10 Modules
| |||||||||||||||
| 4056 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoABAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=1128 --field-trial-handle=1908,i,3774153436295833503,12100124424764935068,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
50 631
Read events
22 830
Write events
12 975
Delete events
14 826
Modification events
| (PID) Process: | (2148) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2148) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2148) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2148) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2148) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (7940) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000A5DCCAC1C9B3DB01 | |||
| (PID) Process: | (5384) jre-8u451-windows-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\JavaSoft |
| Operation: | delete value | Name: | InstallStatus |
Value: | |||
| (PID) Process: | (5384) jre-8u451-windows-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5384) jre-8u451-windows-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5384) jre-8u451-windows-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
342
Suspicious files
518
Text files
225
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10c3af.TMP | — | |
MD5:— | SHA256:— | |||
| 2148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF10c3af.TMP | — | |
MD5:— | SHA256:— | |||
| 2148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10c3af.TMP | — | |
MD5:— | SHA256:— | |||
| 2148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10c3bf.TMP | — | |
MD5:— | SHA256:— | |||
| 2148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10c3bf.TMP | — | |
MD5:— | SHA256:— | |||
| 2148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
72
DNS requests
75
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.147:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
8168 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5e4lkmgfcesq6avv3awfgt73ia_20250408.743742949.14/obedbbhbpmojnkanicioggnmelmoomoc_20250408.743742949.14_all_ENUS500000_adtc2ilipjdpfvjnsxcksxzvyiya.crx3 | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1020 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1020 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5384 | jre-8u451-windows-x64.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | unknown | — | — | whitelisted |
8168 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5e4lkmgfcesq6avv3awfgt73ia_20250408.743742949.14/obedbbhbpmojnkanicioggnmelmoomoc_20250408.743742949.14_all_ENUS500000_adtc2ilipjdpfvjnsxcksxzvyiya.crx3 | unknown | — | — | whitelisted |
8168 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5e4lkmgfcesq6avv3awfgt73ia_20250408.743742949.14/obedbbhbpmojnkanicioggnmelmoomoc_20250408.743742949.14_all_ENUS500000_adtc2ilipjdpfvjnsxcksxzvyiya.crx3 | unknown | — | — | whitelisted |
8168 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5e4lkmgfcesq6avv3awfgt73ia_20250408.743742949.14/obedbbhbpmojnkanicioggnmelmoomoc_20250408.743742949.14_all_ENUS500000_adtc2ilipjdpfvjnsxcksxzvyiya.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.147:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1348 | chrome.exe | 104.126.37.145:443 | www.java.com | Akamai International B.V. | DE | whitelisted |
2148 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1348 | chrome.exe | 74.125.71.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
1348 | chrome.exe | 69.192.161.97:443 | www.oracle.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.java.com |
| whitelisted |
accounts.google.com |
| whitelisted |
consent.trustarc.com |
| whitelisted |
www.oracle.com |
| whitelisted |
login.live.com |
| whitelisted |
s.go-mpulse.net |
| whitelisted |