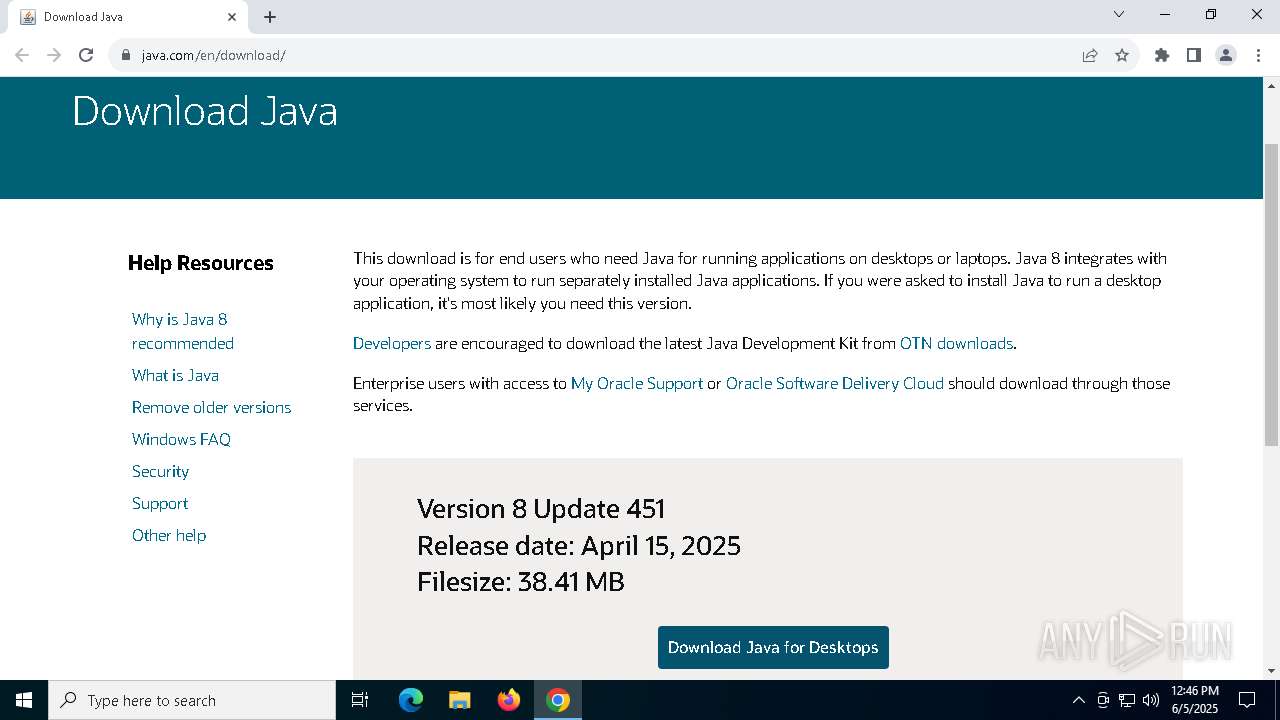
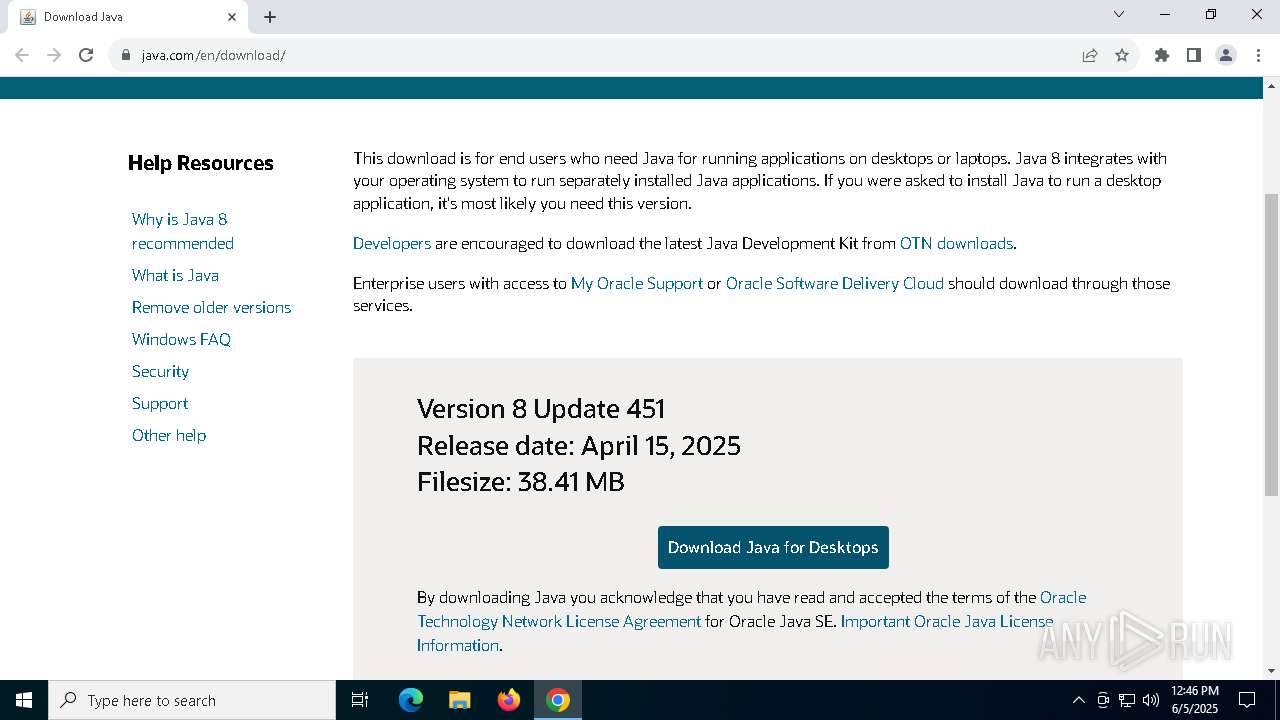
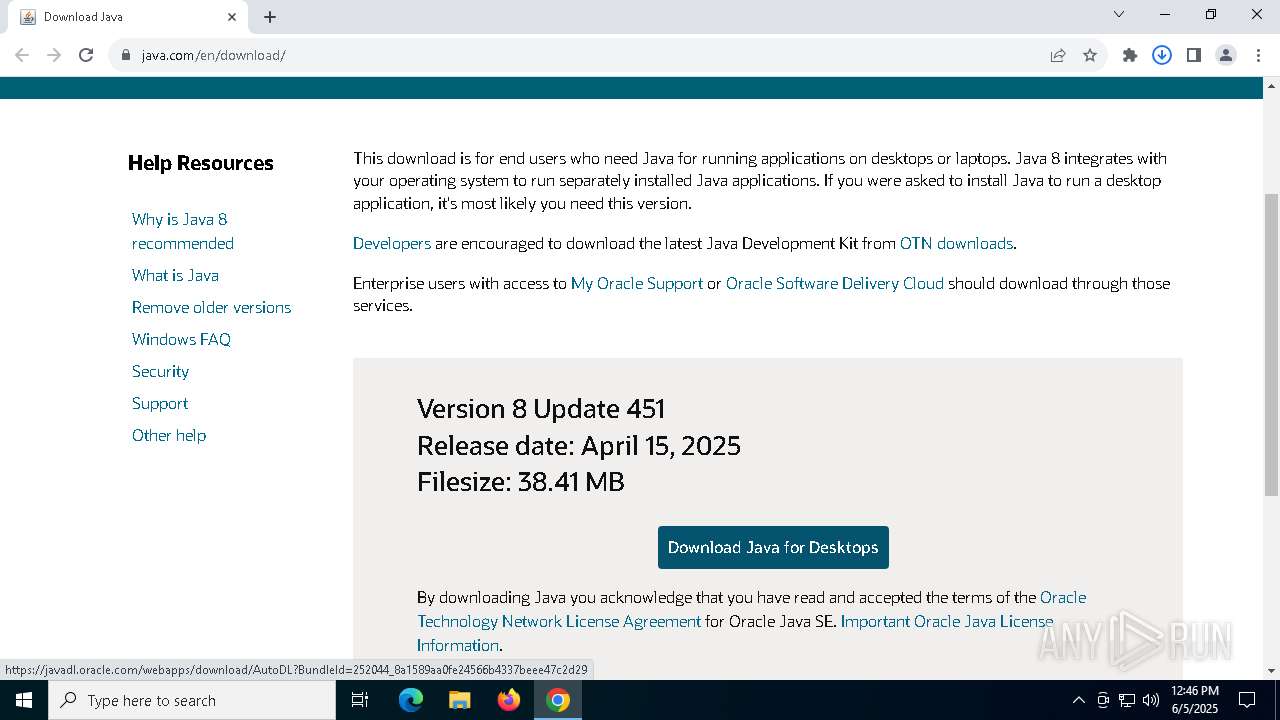
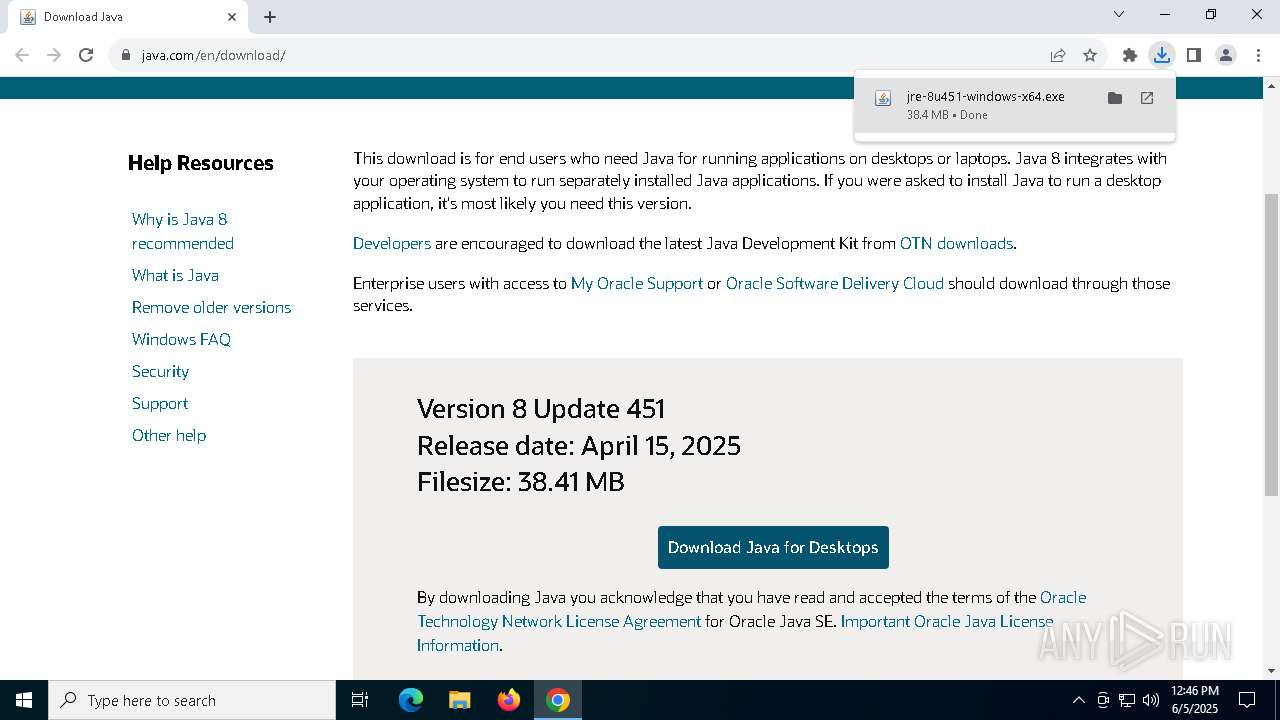
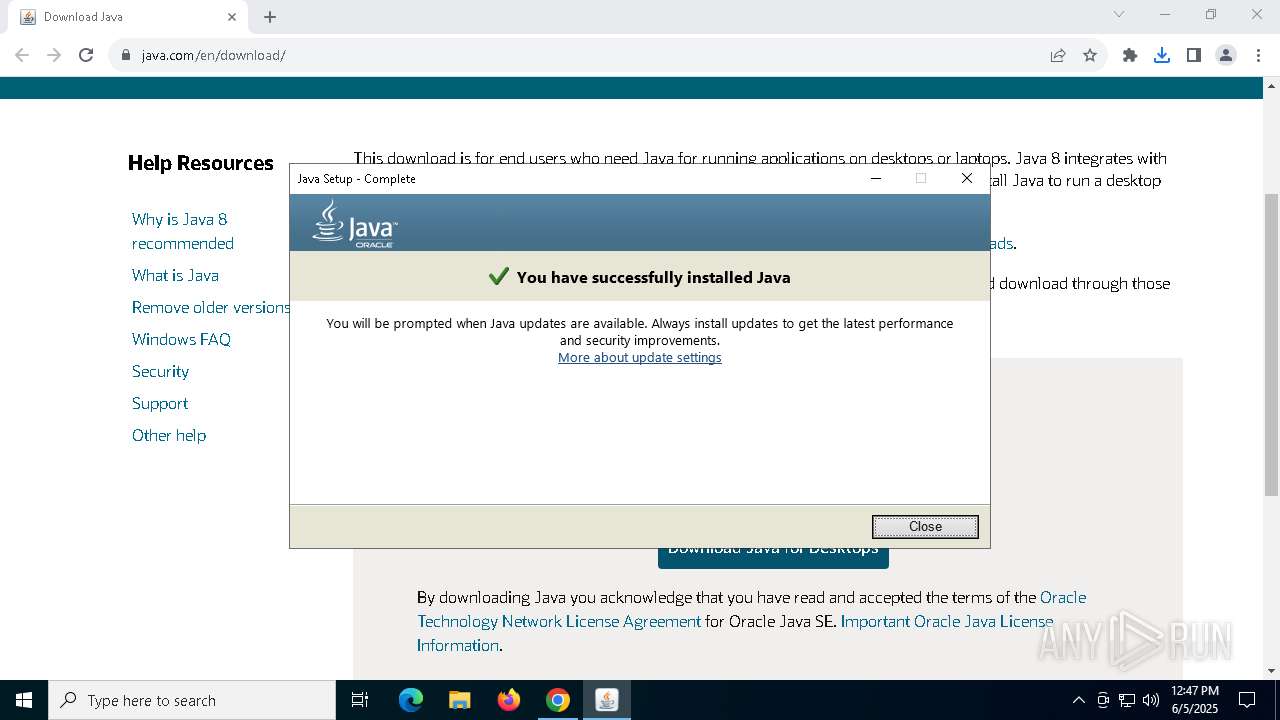
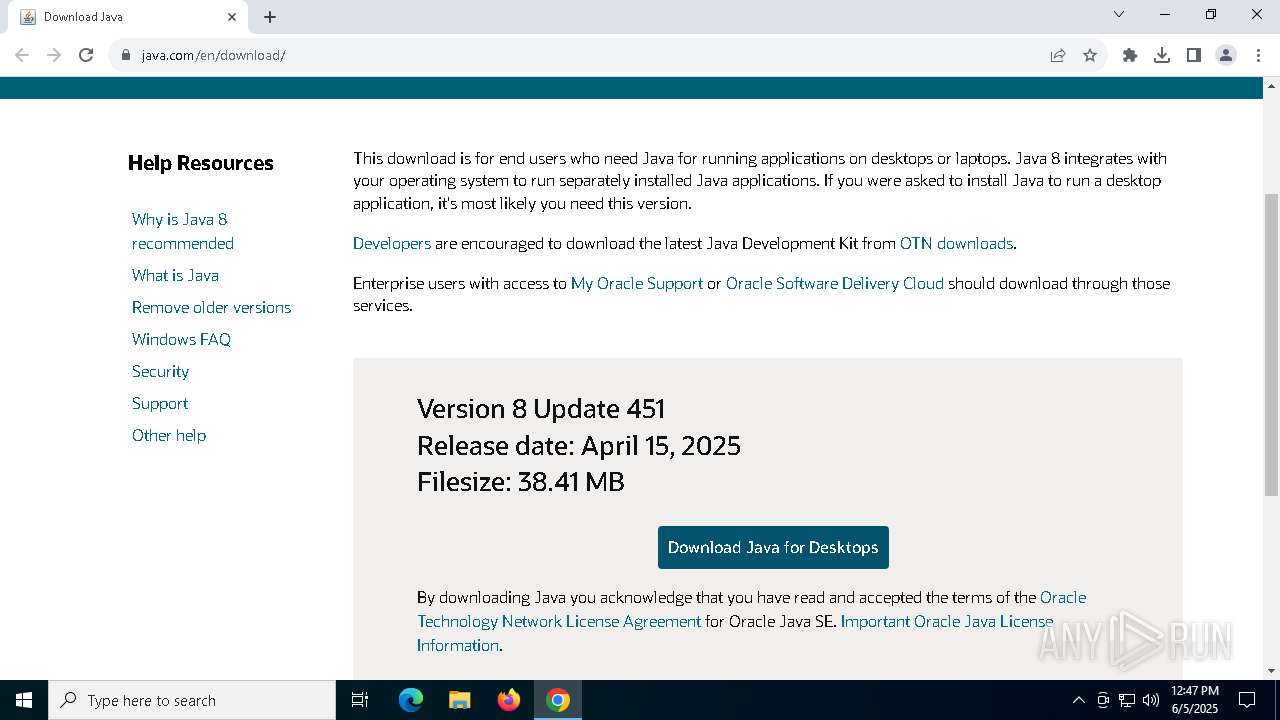
| URL: | https://www.java.com/en/download/ |
| Full analysis: | https://app.any.run/tasks/97cb9e16-2663-4c31-b3b6-e809e995d888 |
| Verdict: | Malicious activity |
| Analysis date: | June 05, 2025, 12:45:56 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 84607FB83B5206C656EDBCB6BB307062 |
| SHA1: | CDA2463B0319486995625E3D6D673B16DC76792E |
| SHA256: | B909AA08DF51B2D4DA578EF72009B4D6FC9F6B013F7A9D7A66D73767ECEABFA4 |
| SSDEEP: | 3:N8DSL8TiGK1BKSCn:2OL8huB4 |
MALICIOUS
No malicious indicators.SUSPICIOUS
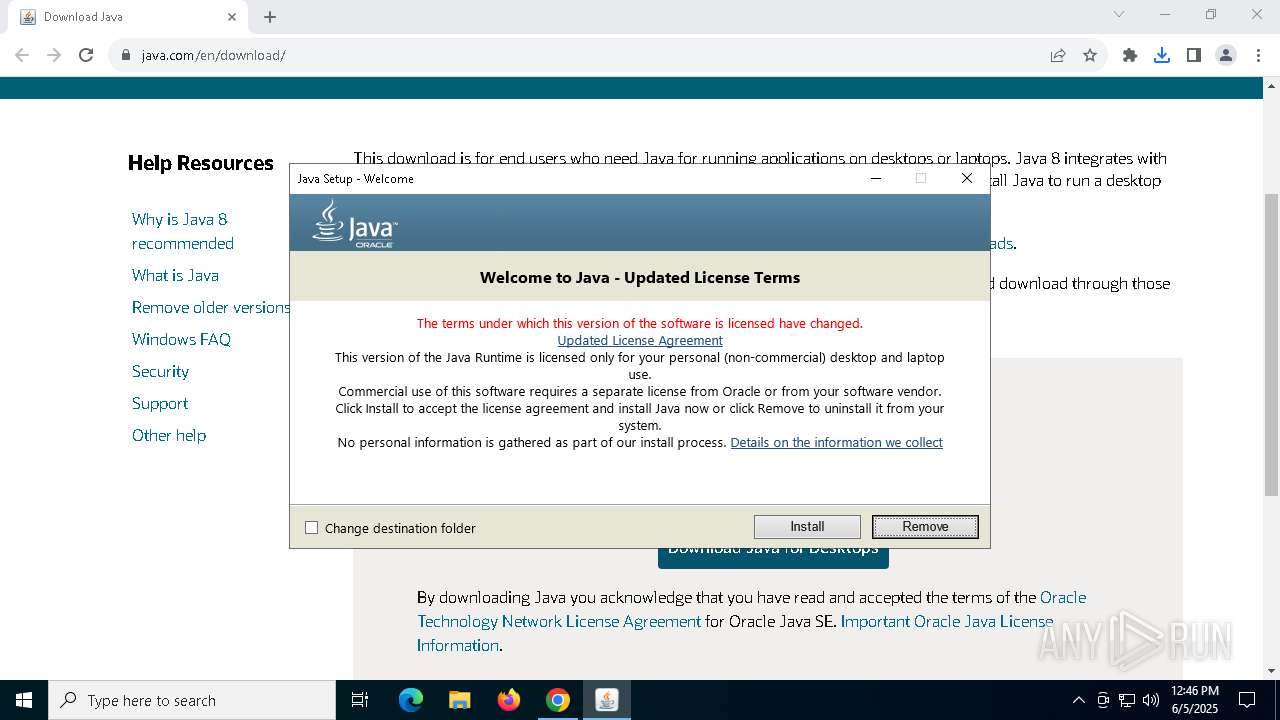
Checks for Java to be installed
- jre-8u451-windows-x64.exe (PID: 5776)
- msiexec.exe (PID: 6800)
- msiexec.exe (PID: 3032)
- installer.exe (PID: 2504)
Application launched itself
- msiexec.exe (PID: 3032)
Reads security settings of Internet Explorer
- jre-8u451-windows-x64.exe (PID: 5776)
- installer.exe (PID: 2504)
Reads Microsoft Outlook installation path
- jre-8u451-windows-x64.exe (PID: 5776)
Reads Internet Explorer settings
- jre-8u451-windows-x64.exe (PID: 5776)
The process drops C-runtime libraries
- msiexec.exe (PID: 3032)
Reads Mozilla Firefox installation path
- MSI9E68.tmp (PID: 5056)
Process drops legitimate windows executable
- msiexec.exe (PID: 3032)
There is functionality for taking screenshot (YARA)
- jre-8u451-windows-x64.exe (PID: 5776)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 3032)
Executable content was dropped or overwritten
- installer.exe (PID: 2504)
- jre-8u451-windows-x64.exe (PID: 5776)
Creates/Modifies COM task schedule object
- installer.exe (PID: 2504)
INFO
Application launched itself
- chrome.exe (PID: 7360)
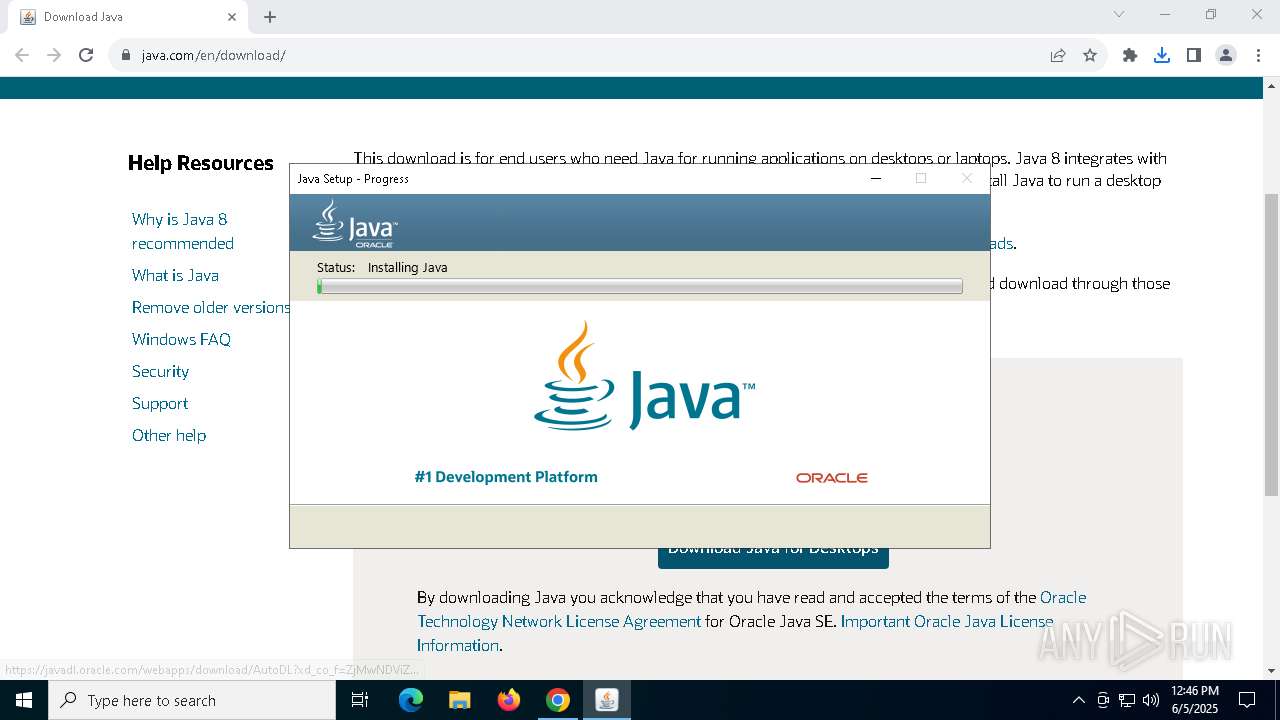
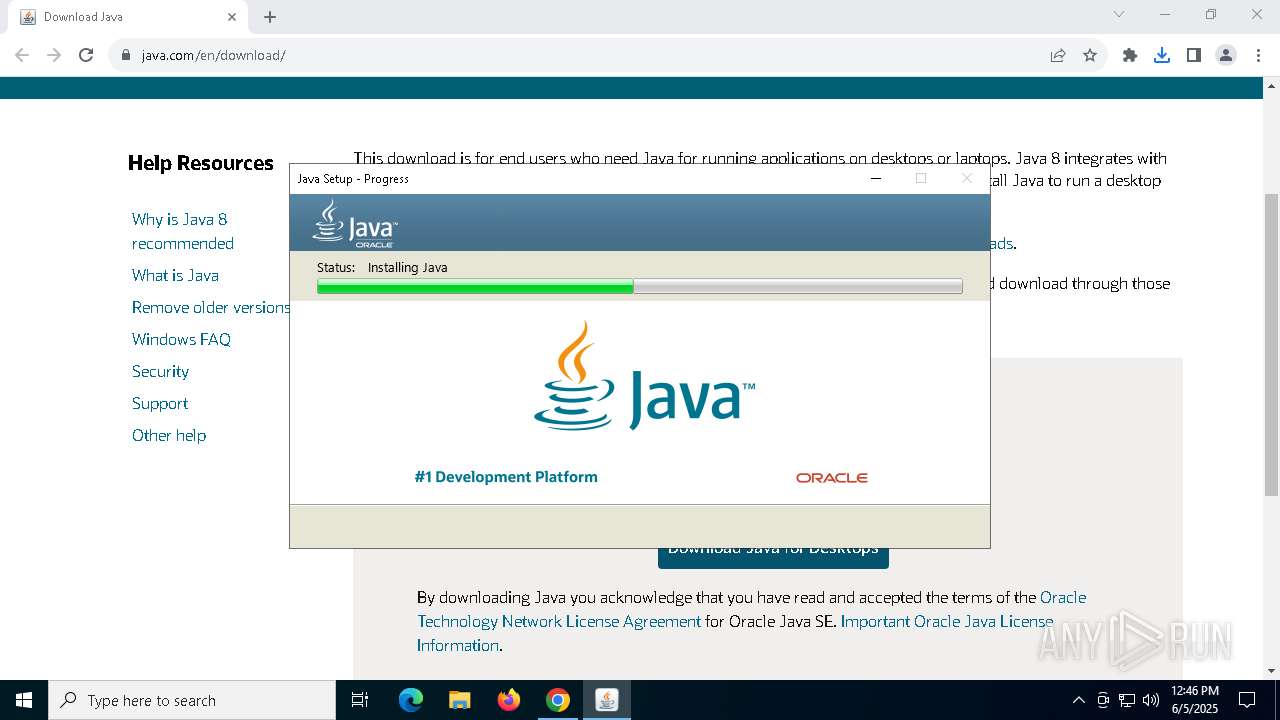
Java executable
- jre-8u451-windows-x64.exe (PID: 7896)
- jre-8u451-windows-x64.exe (PID: 5776)
- jre-8u451-windows-x64.exe (PID: 5332)
- installer.exe (PID: 2504)
- MSI9E68.tmp (PID: 5056)
Create files in a temporary directory
- jre-8u451-windows-x64.exe (PID: 5332)
- MSI9E68.tmp (PID: 5056)
- javaw.exe (PID: 1128)
Checks supported languages
- jre-8u451-windows-x64.exe (PID: 5332)
- jre-8u451-windows-x64.exe (PID: 5776)
- msiexec.exe (PID: 3032)
- MSI9E68.tmp (PID: 5056)
- jaureg.exe (PID: 7544)
- msiexec.exe (PID: 6800)
- javaw.exe (PID: 1128)
- installer.exe (PID: 2504)
Executable content was dropped or overwritten
- chrome.exe (PID: 7360)
- msiexec.exe (PID: 3032)
Reads Environment values
- jre-8u451-windows-x64.exe (PID: 5776)
Reads the machine GUID from the registry
- jre-8u451-windows-x64.exe (PID: 5776)
- msiexec.exe (PID: 3032)
Reads the computer name
- jre-8u451-windows-x64.exe (PID: 5332)
- msiexec.exe (PID: 3032)
- msiexec.exe (PID: 6800)
- jre-8u451-windows-x64.exe (PID: 5776)
- MSI9E68.tmp (PID: 5056)
- installer.exe (PID: 2504)
Creates files or folders in the user directory
- msiexec.exe (PID: 3032)
- jre-8u451-windows-x64.exe (PID: 5776)
Reads the software policy settings
- msiexec.exe (PID: 3032)
- jre-8u451-windows-x64.exe (PID: 5776)
Checks proxy server information
- jre-8u451-windows-x64.exe (PID: 5776)
Starts application with an unusual extension
- msiexec.exe (PID: 3032)
Creates a software uninstall entry
- msiexec.exe (PID: 3032)
Creates files in the program directory
- installer.exe (PID: 2504)
- javaw.exe (PID: 1128)
The sample compiled with english language support
- msiexec.exe (PID: 3032)
- installer.exe (PID: 2504)
- jre-8u451-windows-x64.exe (PID: 5776)
Reads CPU info
- msiexec.exe (PID: 3032)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
169
Monitored processes
41
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --mojo-platform-channel-handle=4420 --field-trial-handle=1904,i,1891960078101228836,8047301611681236047,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 540 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 644 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 864 | -Djdk.disableLastUsageTracking -cp "C:\Program Files\Java\jre1.8.0_451\bin\..\lib\deploy.jar" com.sun.deploy.panel.ControlPanel -systemConfig deployment.expiration.check.enabled false | C:\Program Files\Java\jre1.8.0_451\bin\javaw.exe | — | jre-8u451-windows-x64.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.4510.10 Modules
| |||||||||||||||
| 1128 | "C:\Program Files\Java\jre1.8.0_451\bin\javaw.exe" -Xshare:dump -Djdk.disableLastUsageTracking | C:\Program Files\Java\jre1.8.0_451\bin\javaw.exe | installer.exe | ||||||||||||
User: SYSTEM Company: Oracle Corporation Integrity Level: SYSTEM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.4510.10 Modules
| |||||||||||||||
| 1284 | "C:\Program Files\Java\jre1.8.0_451\bin\javaws.exe" -wait -fix -shortcut -silent | C:\Program Files\Java\jre1.8.0_451\bin\javaws.exe | installer.exe | ||||||||||||
User: SYSTEM Company: Oracle Corporation Integrity Level: SYSTEM Description: Java(TM) Web Start Launcher Exit code: 0 Version: 11.451.0.10 Modules
| |||||||||||||||
| 2504 | "C:\Program Files\Java\jre1.8.0_451\installer.exe" /s INSTALLDIR="C:\Program Files\Java\jre1.8.0_451\\" INSTALL_SILENT=1 AUTO_UPDATE=0 SPONSORS=0 REPAIRMODE=0 ProductCode={71024AE4-039E-4CA4-87B4-2F64180451F0} | C:\Program Files\Java\jre1.8.0_451\installer.exe | msiexec.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java Platform SE binary Exit code: 0 Version: 8.0.4510.10 Modules
| |||||||||||||||
| 2772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3044 --field-trial-handle=1904,i,1891960078101228836,8047301611681236047,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgABAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=1900 --field-trial-handle=1904,i,1891960078101228836,8047301611681236047,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 3032 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
48 030
Read events
20 159
Write events
13 030
Delete events
14 841
Modification events
| (PID) Process: | (7360) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7360) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7360) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7360) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7360) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6436) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000466944DB17D6DB01 | |||
| (PID) Process: | (5776) jre-8u451-windows-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\JavaSoft |
| Operation: | delete value | Name: | InstallStatus |
Value: | |||
| (PID) Process: | (5776) jre-8u451-windows-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5776) jre-8u451-windows-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5776) jre-8u451-windows-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
346
Suspicious files
98
Text files
204
Unknown types
65
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7360 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF120325.TMP | — | |
MD5:— | SHA256:— | |||
| 7360 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7360 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF120334.TMP | — | |
MD5:— | SHA256:— | |||
| 7360 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7360 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF120325.TMP | — | |
MD5:— | SHA256:— | |||
| 7360 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7360 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF120344.TMP | — | |
MD5:— | SHA256:— | |||
| 7360 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7360 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF120344.TMP | — | |
MD5:— | SHA256:— | |||
| 7360 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF120363.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
78
DNS requests
86
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1088 | svchost.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7512 | SIHClient.exe | GET | 200 | 23.209.214.100:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7512 | SIHClient.exe | GET | 200 | 23.209.214.100:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5776 | jre-8u451-windows-x64.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | unknown | — | — | whitelisted |
3032 | msiexec.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAqhj2P5bxF3HLsLQ%2BTWkLg%3D | unknown | — | — | whitelisted |
3032 | msiexec.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
3032 | msiexec.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1088 | svchost.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
7768 | RUXIMICS.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6048 | chrome.exe | 64.233.166.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
7360 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6048 | chrome.exe | 2.19.122.21:443 | www.java.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.java.com |
| whitelisted |
accounts.google.com |
| whitelisted |
consent.trustarc.com |
| whitelisted |
www.oracle.com |
| whitelisted |
s.go-mpulse.net |
| whitelisted |
c.oracleinfinity.io |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |