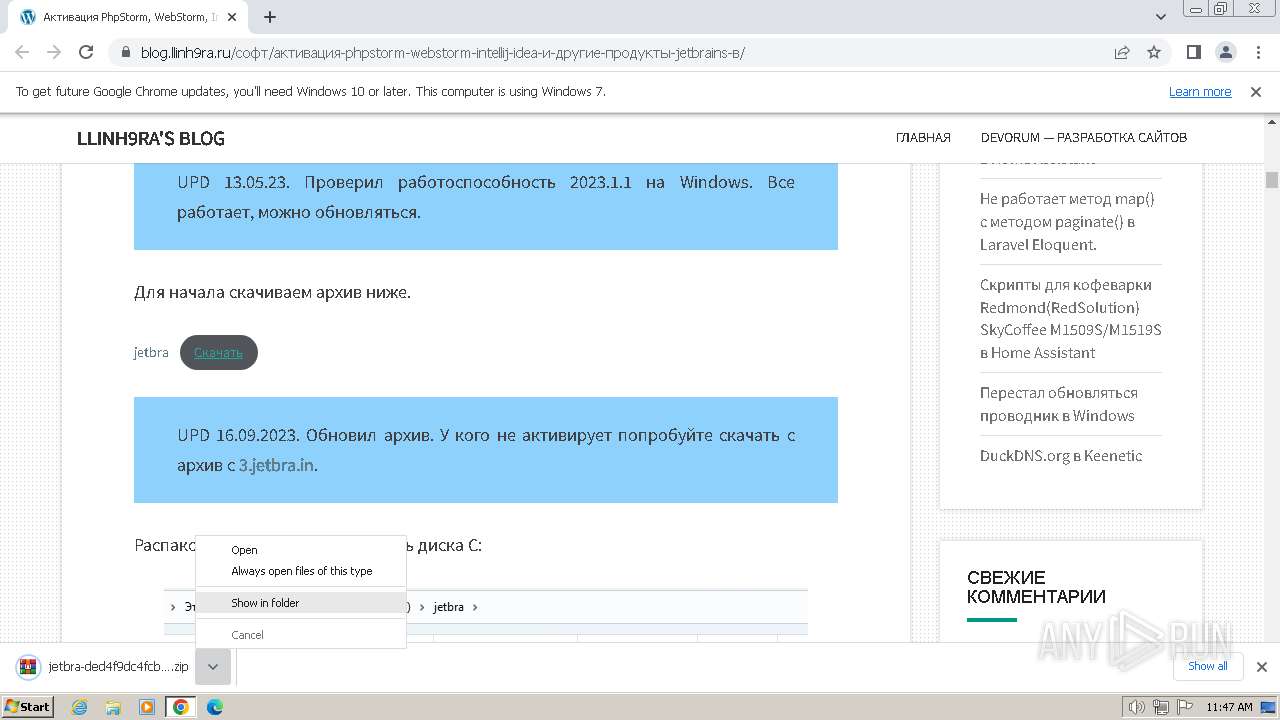
| URL: | https://blog.llinh9ra.ru/%D1%81%D0%BE%D1%84%D1%82/%D0%B0%D0%BA%D1%82%D0%B8%D0%B2%D0%B0%D1%86%D0%B8%D1%8F-phpstorm-webstorm-intellij-idea-%D0%B8-%D0%B4%D1%80%D1%83%D0%B3%D0%B8%D0%B5-%D0%BF%D1%80%D0%BE%D0%B4%D1%83%D0%BA%D1%82%D1%8B-jetbrains-%D0%B2/ |
| Full analysis: | https://app.any.run/tasks/a685c443-8c0b-4f74-9d42-8d4bd317f344 |
| Verdict: | Malicious activity |
| Analysis date: | April 03, 2024, 10:47:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 8351C05E13C038A9C343E49838657C64 |
| SHA1: | 7A33E03AB667814FFCD4492ED349DD0E78B56A1A |
| SHA256: | B8FD658F8E6A51816EA02A3175E66CC86E95093BAF25FBF43C5C316055D8DBDD |
| SSDEEP: | 6:2ZrzlEYLD2qVUEVjLijswV7BkBApEVtbZdPbXWoEMrc:2ZrzlEij/GBkRXTJE7 |
MALICIOUS
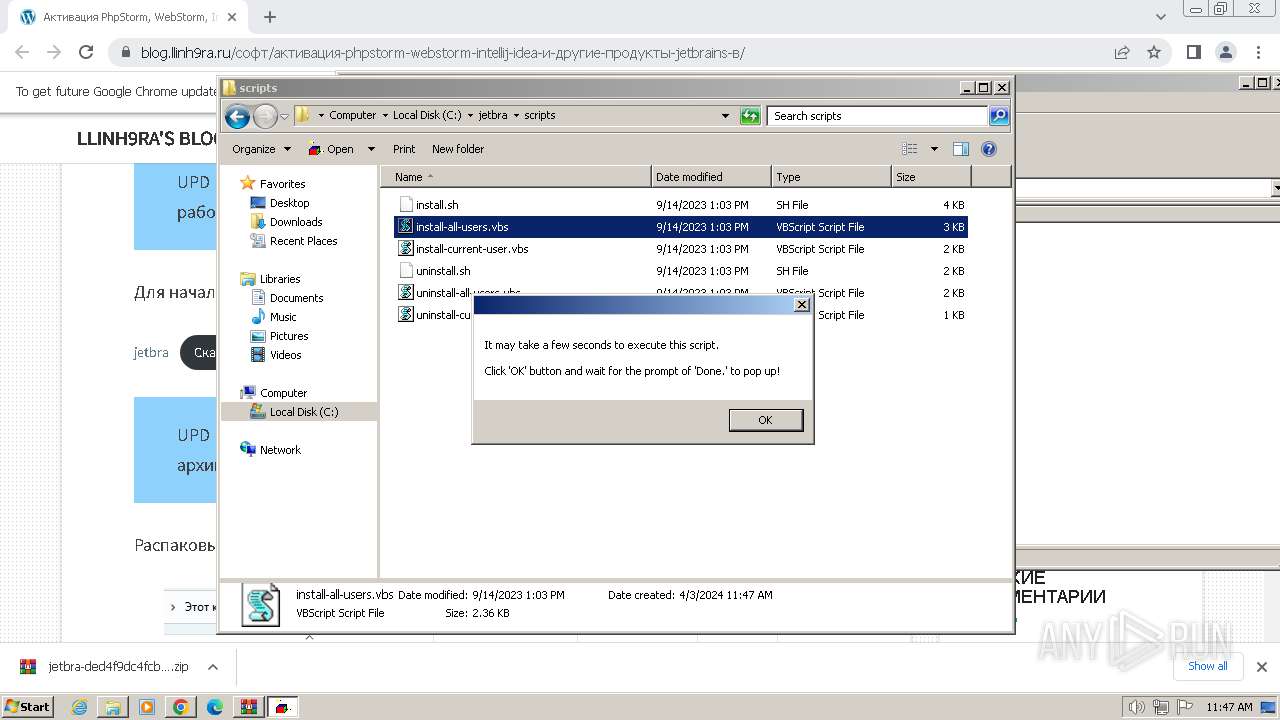
Opens a text file (SCRIPT)
- wscript.exe (PID: 2612)
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 2612)
SUSPICIOUS
Reads the Internet Settings
- wscript.exe (PID: 3136)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 3136)
- wscript.exe (PID: 2612)
Application launched itself
- wscript.exe (PID: 3136)
The process executes VB scripts
- wscript.exe (PID: 3136)
Runs shell command (SCRIPT)
- wscript.exe (PID: 3136)
Checks whether a specific file exists (SCRIPT)
- wscript.exe (PID: 2612)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 2612)
Reads data from a binary Stream object (SCRIPT)
- wscript.exe (PID: 2612)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 2612)
INFO
Application launched itself
- chrome.exe (PID: 2580)
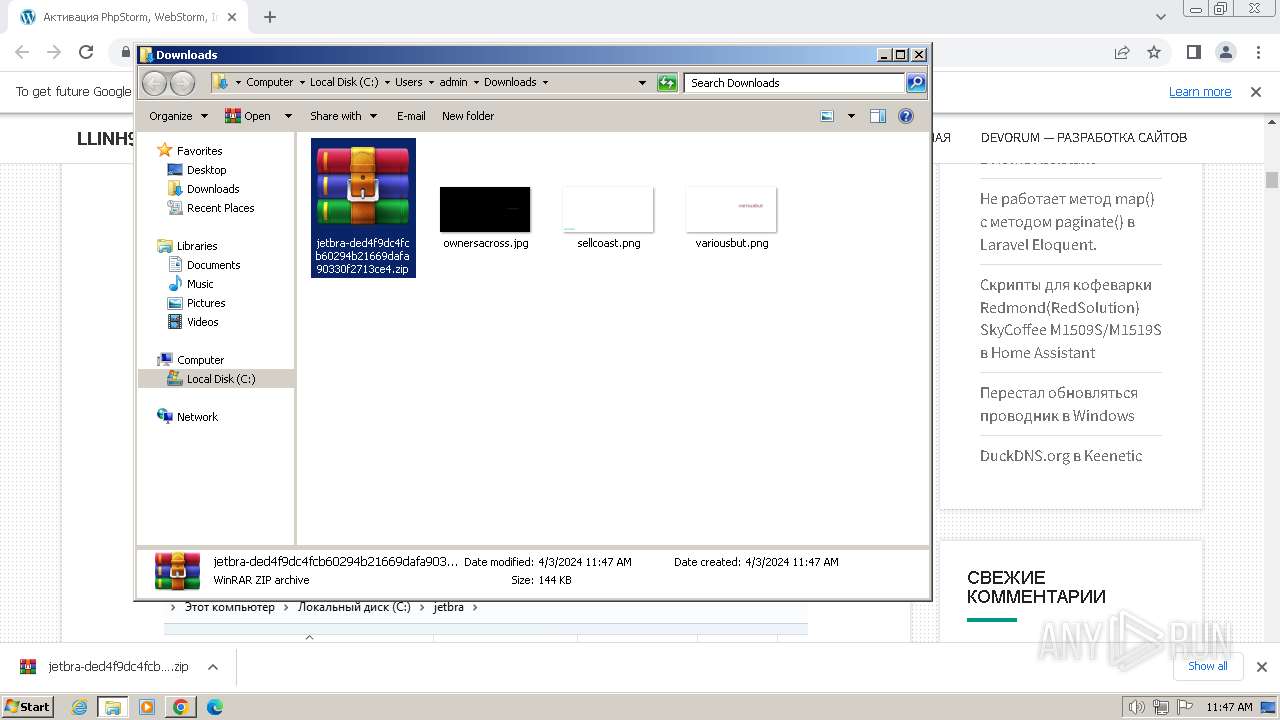
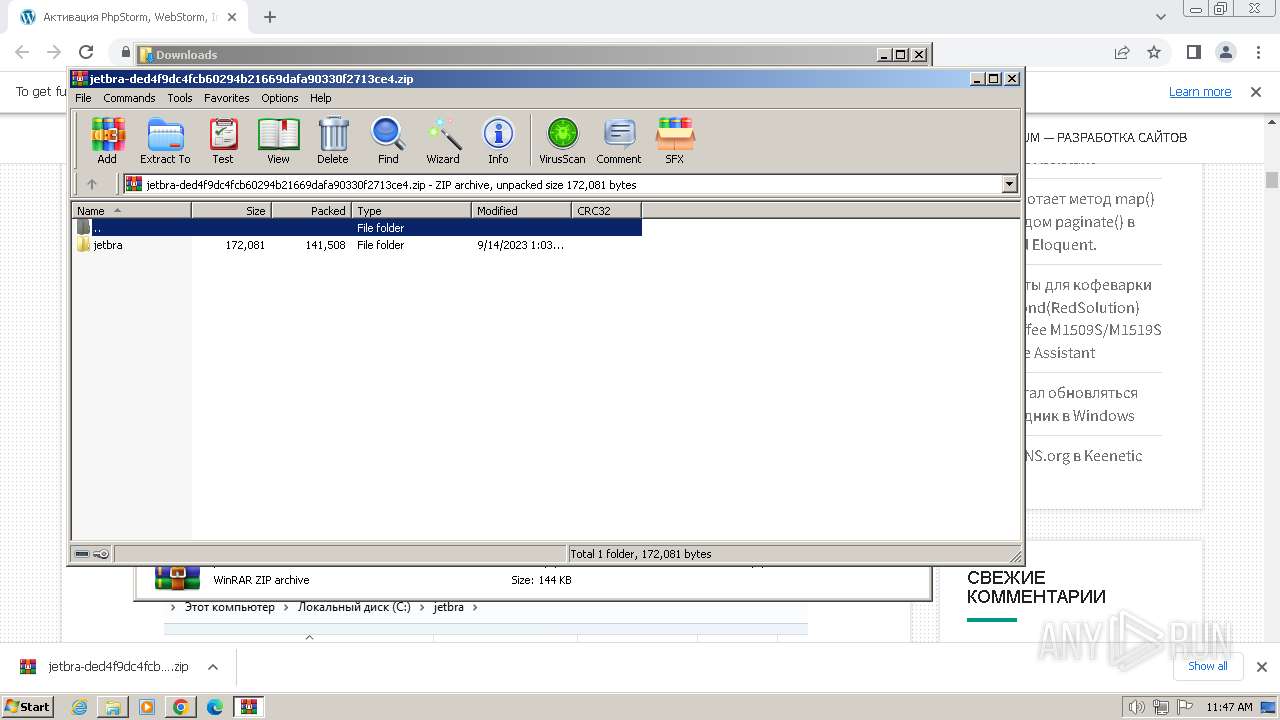
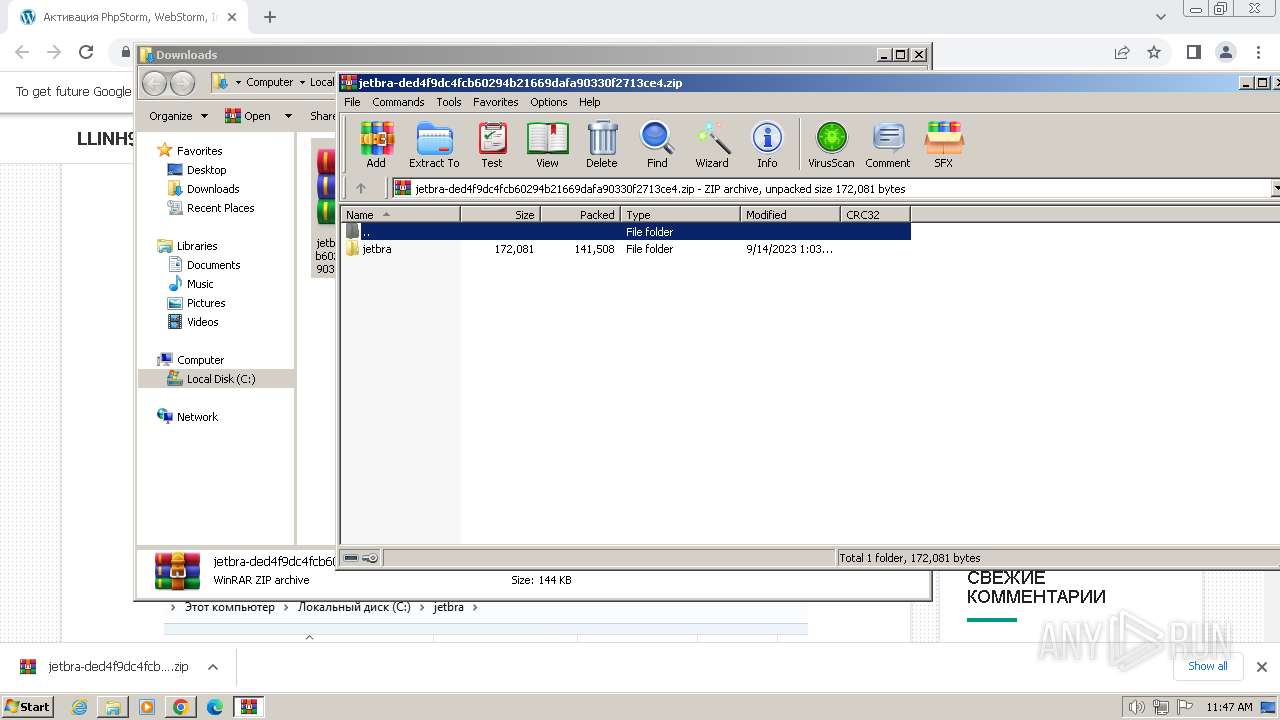
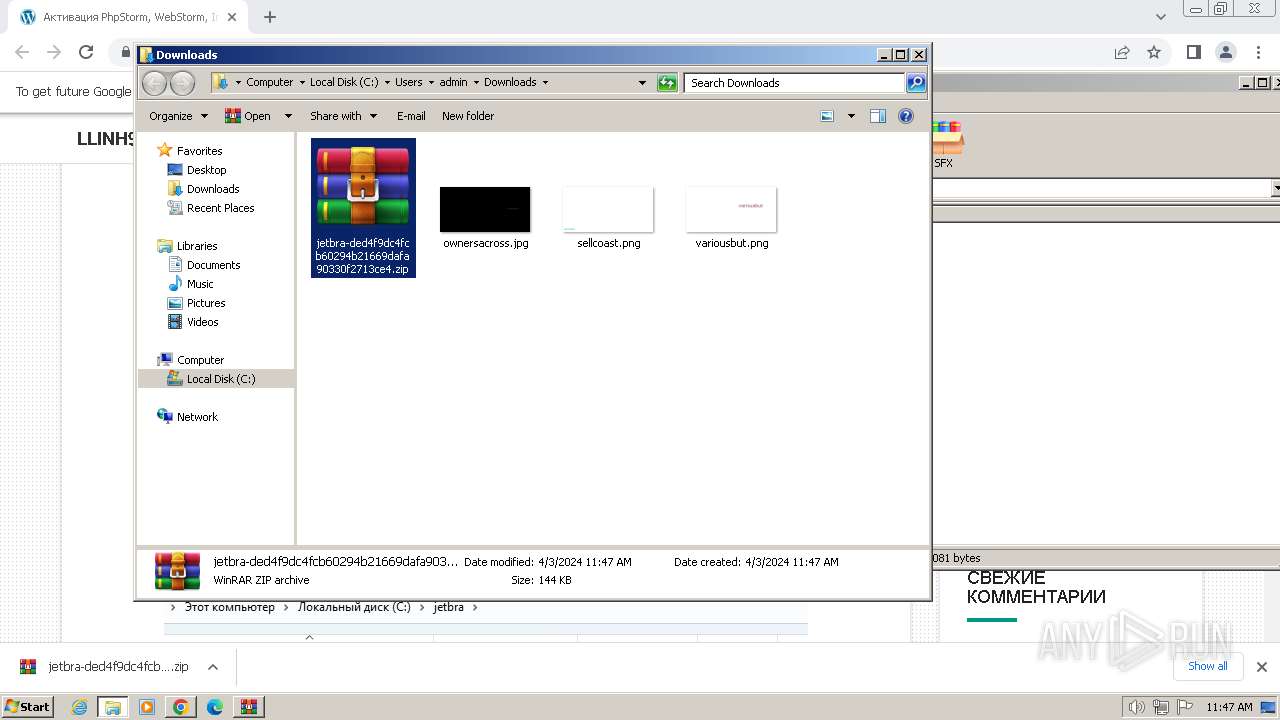
The process uses the downloaded file
- chrome.exe (PID: 992)
- WinRAR.exe (PID: 3172)
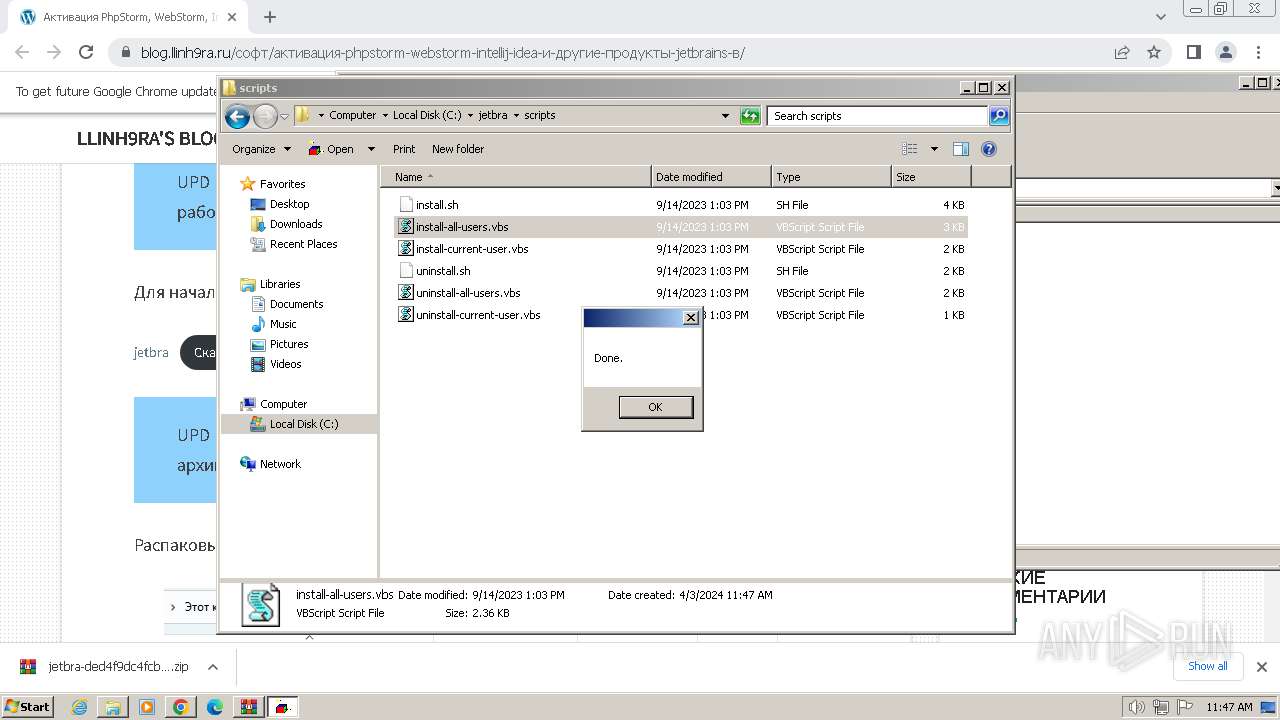
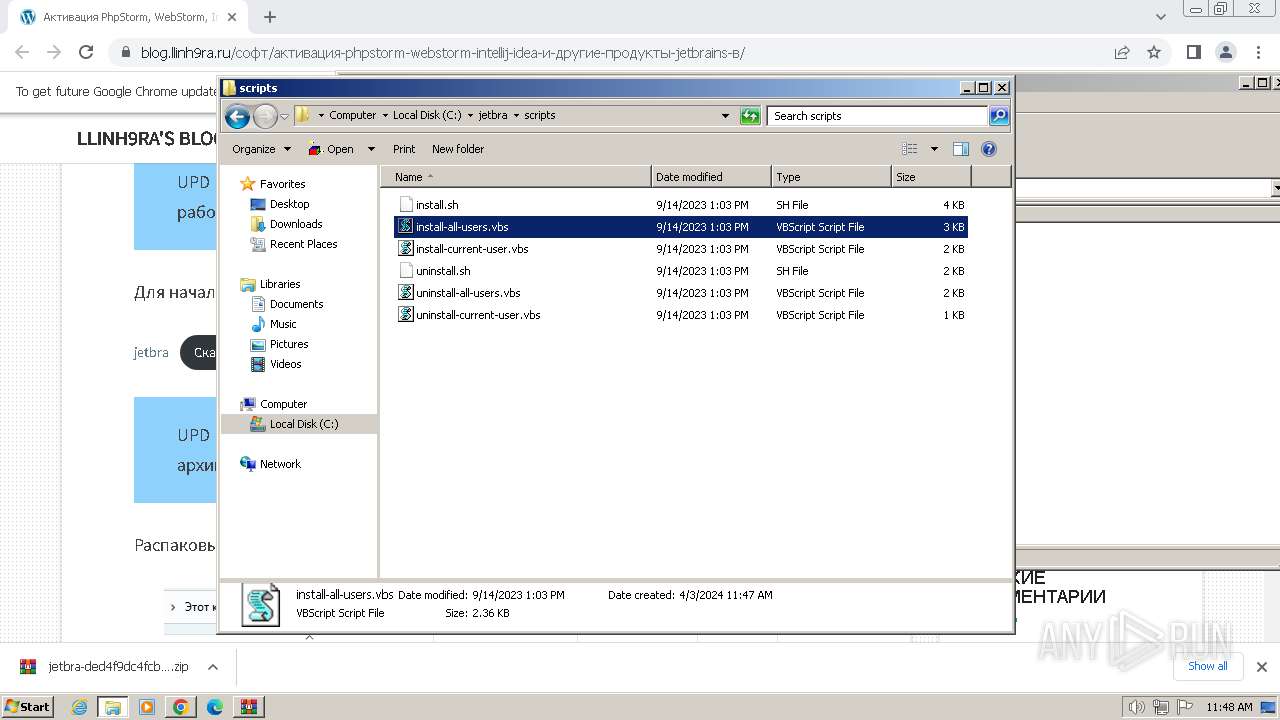
Manual execution by a user
- WinRAR.exe (PID: 3172)
- wscript.exe (PID: 3136)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
65
Monitored processes
22
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 696 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1340 --field-trial-handle=1144,i,5059450349654238844,5145550341043328008,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3864 --field-trial-handle=1144,i,5059450349654238844,5145550341043328008,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1652 --field-trial-handle=1144,i,5059450349654238844,5145550341043328008,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.FileUtilService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3104 --field-trial-handle=1144,i,5059450349654238844,5145550341043328008,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --first-renderer-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2024 --field-trial-handle=1144,i,5059450349654238844,5145550341043328008,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1120 --field-trial-handle=1144,i,5059450349654238844,5145550341043328008,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=4044 --field-trial-handle=1144,i,5059450349654238844,5145550341043328008,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2232 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6bcd8b38,0x6bcd8b48,0x6bcd8b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=14 --mojo-platform-channel-handle=3780 --field-trial-handle=1144,i,5059450349654238844,5145550341043328008,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3756 --field-trial-handle=1144,i,5059450349654238844,5145550341043328008,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
12 789
Read events
12 675
Write events
107
Delete events
7
Modification events
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
4
Suspicious files
13
Text files
68
Unknown types
69
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF182277.TMP | — | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF182287.TMP | text | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF182296.TMP | text | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ae0ff66d-6f14-4325-9d9f-47f8ec042d69.tmp | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
552
DNS requests
599
Threats
99
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acezyjyt2fp2x53dhyqbvt3gxdlq_63/khaoiebndkojlmppeemjhbpbandiljpe_63_win_pz5ggrx6ddtwepg55hf2663jnu.crx3 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | unknown | — | — | unknown |
696 | chrome.exe | GET | 200 | 69.192.161.44:80 | http://r3.i.lencr.org/ | unknown | — | — | unknown |
696 | chrome.exe | GET | 200 | 69.192.161.44:80 | http://x1.i.lencr.org/ | unknown | — | — | unknown |
696 | chrome.exe | GET | 200 | 184.24.77.47:80 | http://apps.identrust.com/roots/dstrootcax3.p7c | unknown | — | — | unknown |
696 | chrome.exe | GET | 200 | 192.229.221.95:80 | http://cacerts.digicert.com/EncryptionEverywhereDVTLSCA-G1.crt | unknown | — | — | unknown |
696 | chrome.exe | GET | 200 | 104.18.38.233:80 | http://zerossl.crt.sectigo.com/ZeroSSLECCDomainSecureSiteCA.crt | unknown | — | — | unknown |
696 | chrome.exe | GET | 200 | 184.24.77.47:80 | http://apps.identrust.com/roots/dstrootcax3.p7c | unknown | — | — | unknown |
696 | chrome.exe | GET | 200 | 69.192.161.44:80 | http://x1.i.lencr.org/ | unknown | — | — | unknown |
856 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acezyjyt2fp2x53dhyqbvt3gxdlq_63/khaoiebndkojlmppeemjhbpbandiljpe_63_win_pz5ggrx6ddtwepg55hf2663jnu.crx3 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
696 | chrome.exe | 142.250.110.84:443 | accounts.google.com | GOOGLE | US | unknown |
2580 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
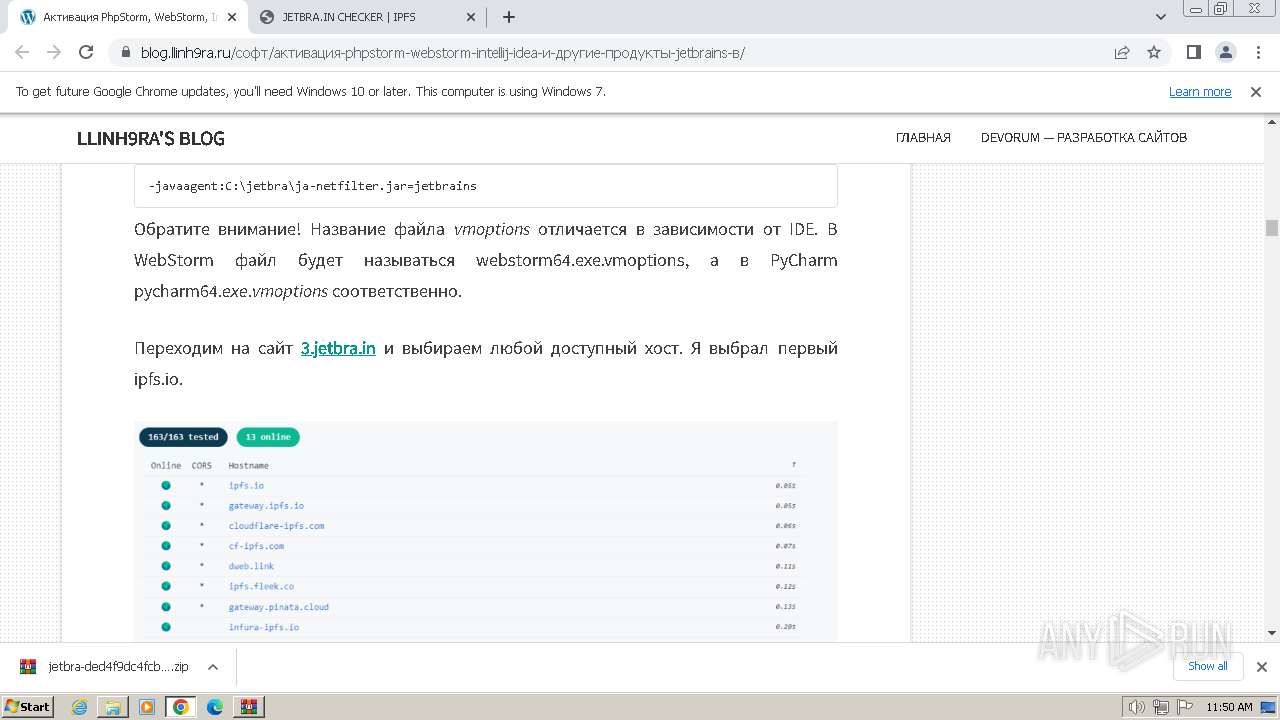
696 | chrome.exe | 91.201.42.20:443 | blog.llinh9ra.ru | EuroByte LLC | RU | unknown |
696 | chrome.exe | 142.250.186.106:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
696 | chrome.exe | 142.250.184.227:443 | fonts.gstatic.com | GOOGLE | US | whitelisted |
696 | chrome.exe | 5.255.255.77:443 | yandex.ru | YANDEX LLC | RU | whitelisted |
696 | chrome.exe | 142.250.186.168:443 | www.googletagmanager.com | GOOGLE | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
blog.llinh9ra.ru |
| unknown |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
yandex.ru |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
mc.yandex.ru |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
yastatic.net |
| whitelisted |
avatars.mds.yandex.net |
| whitelisted |
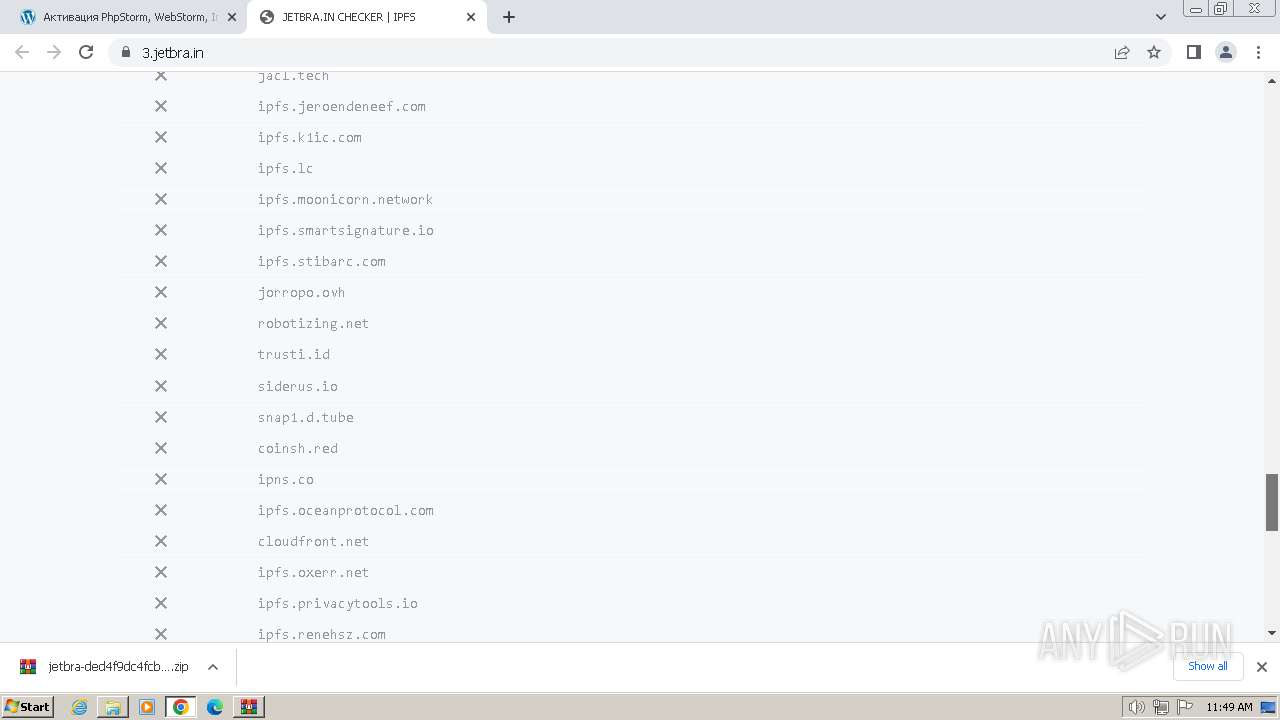
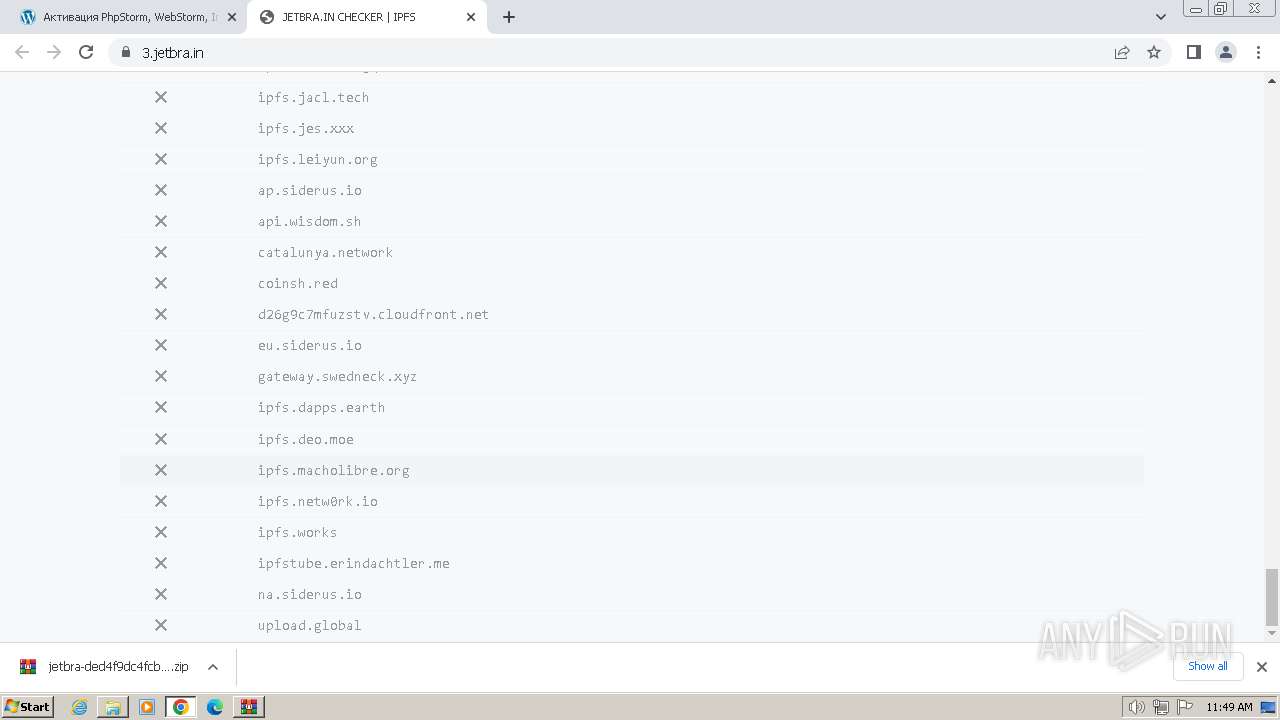
Threats
PID | Process | Class | Message |
|---|---|---|---|
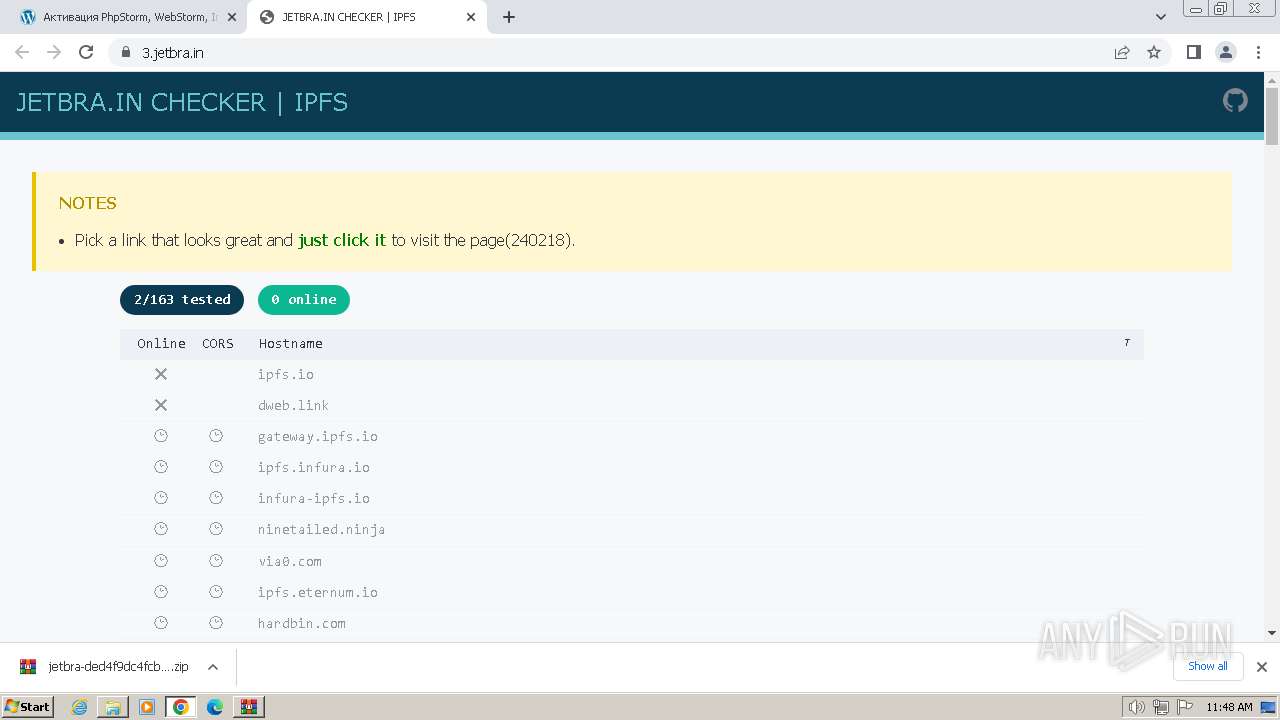
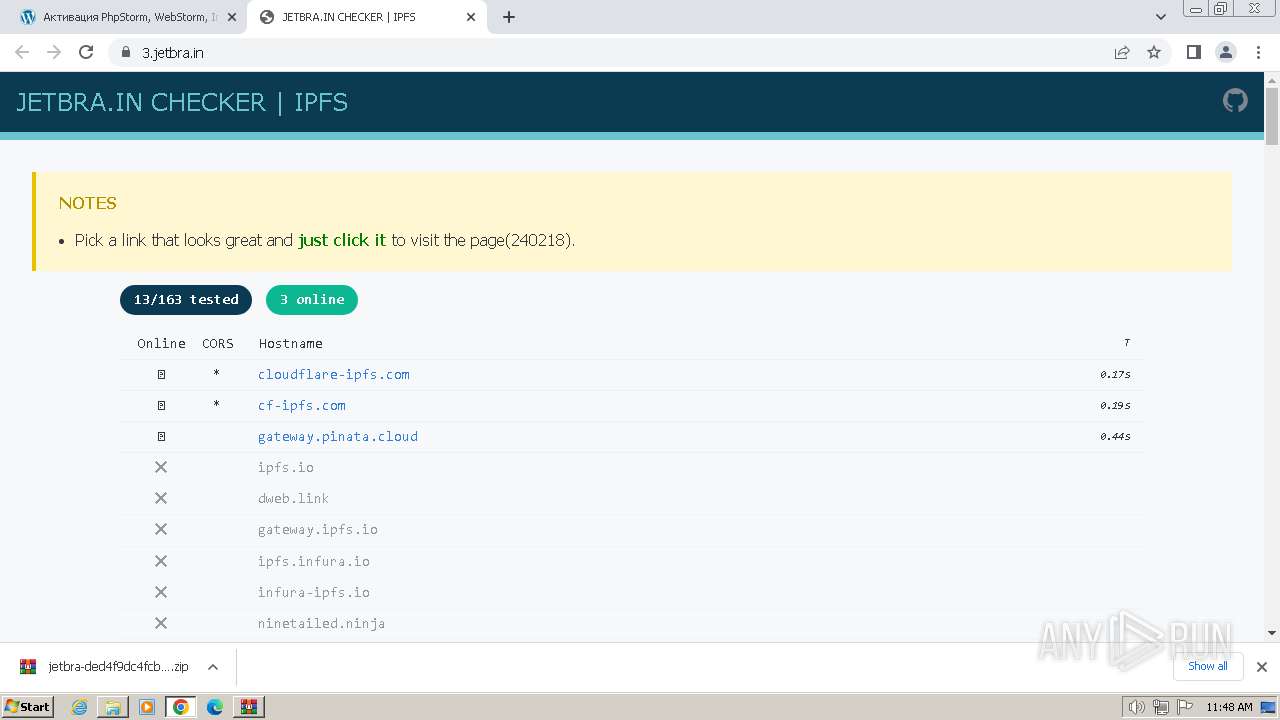
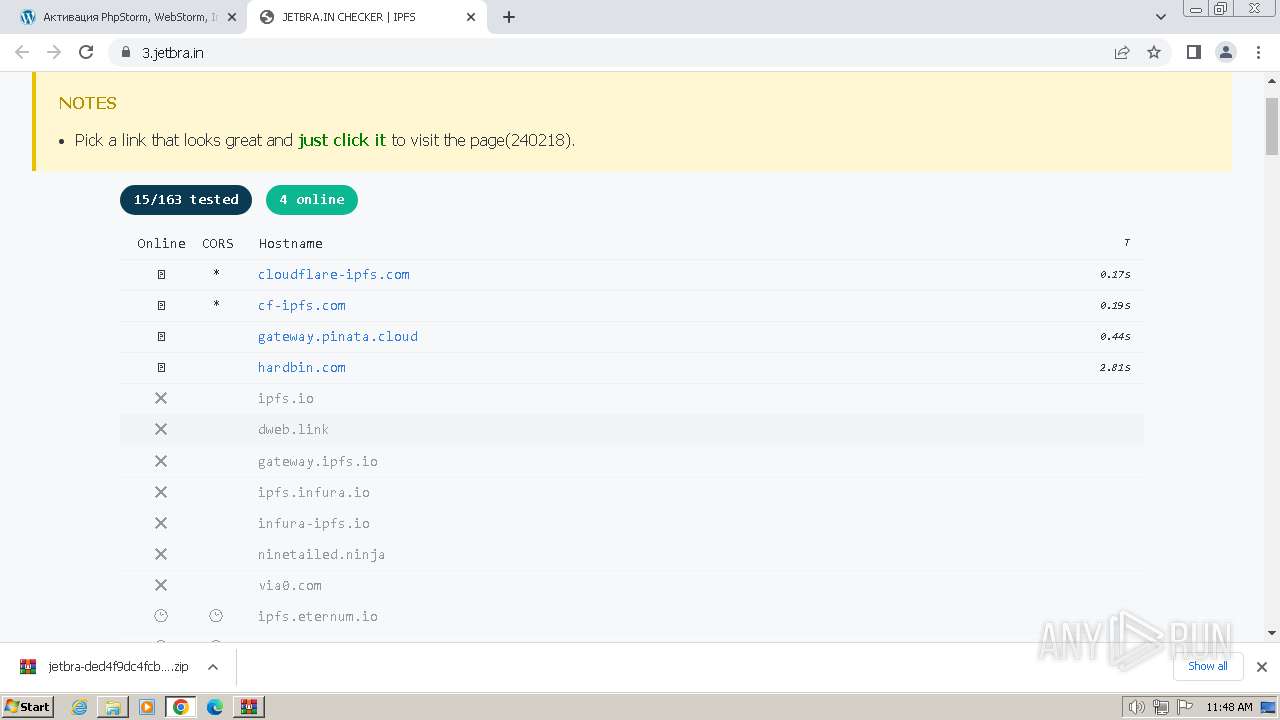
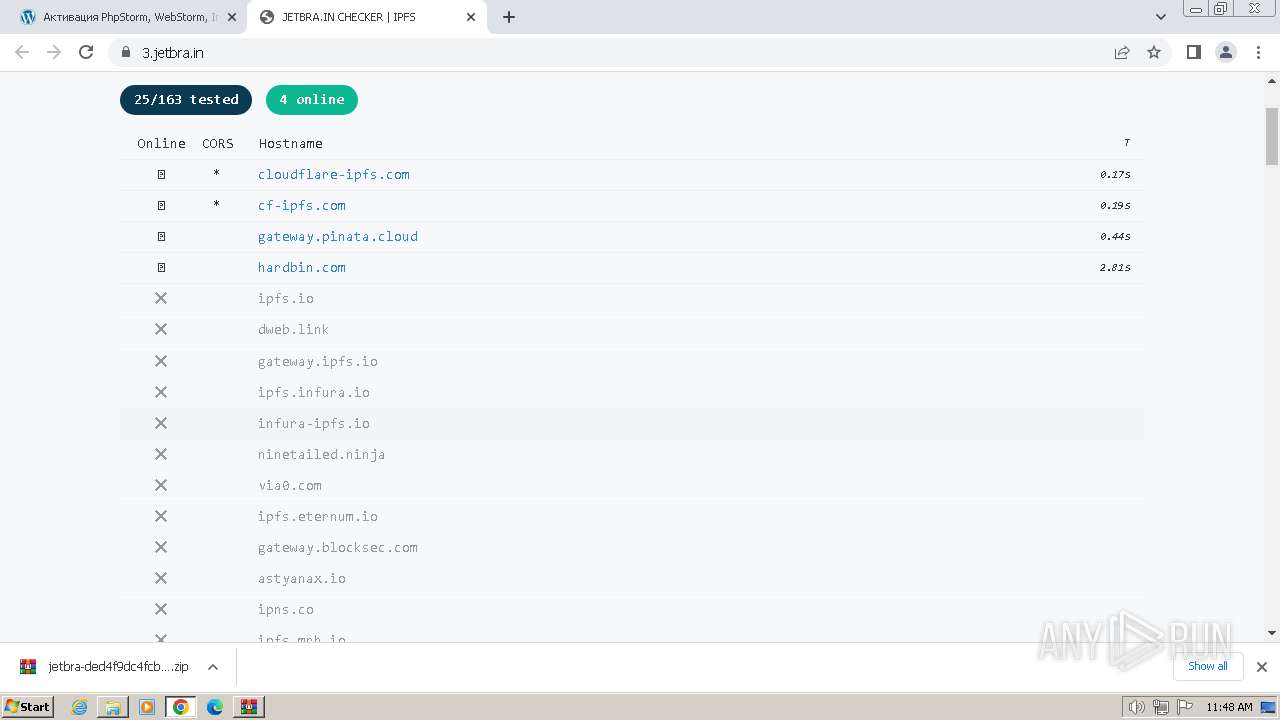
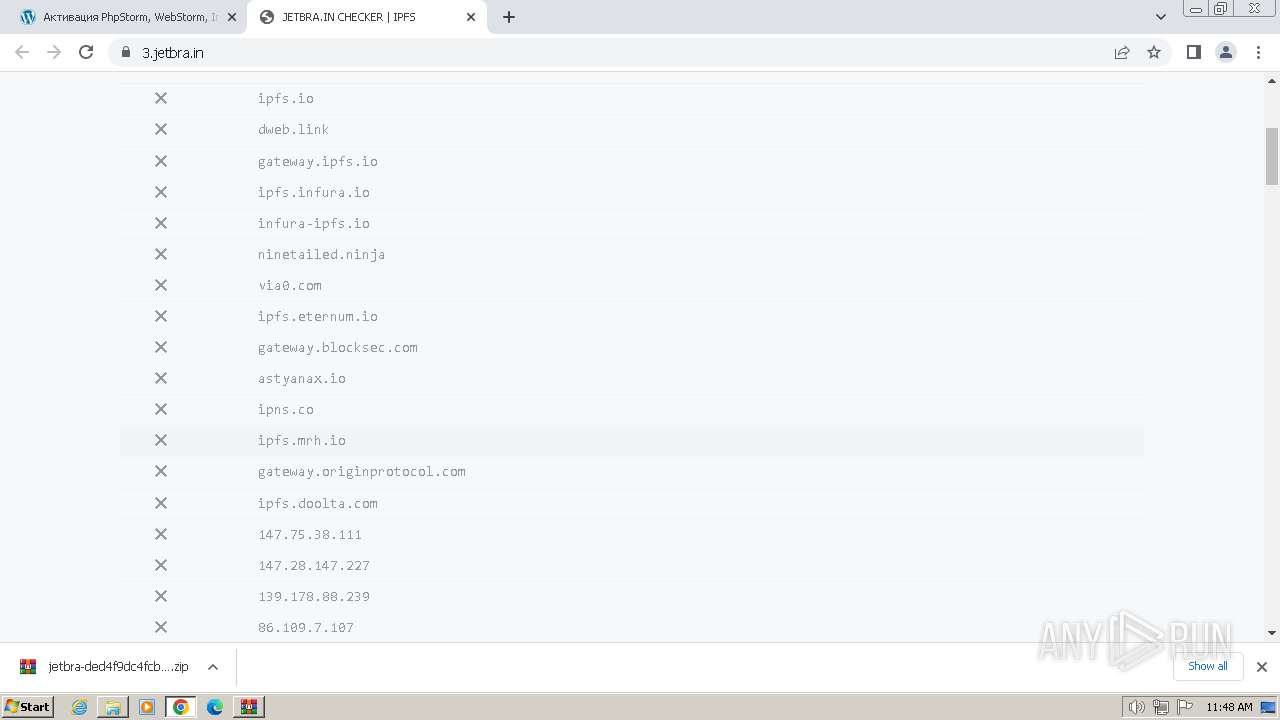
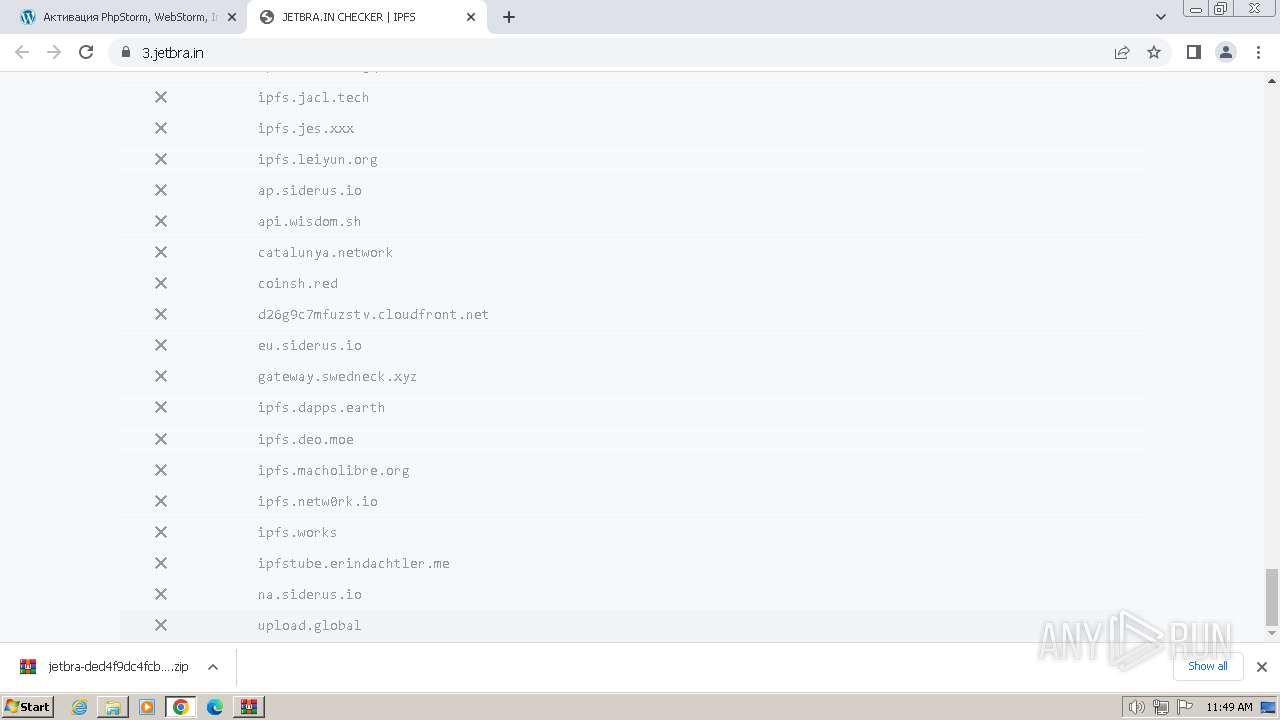
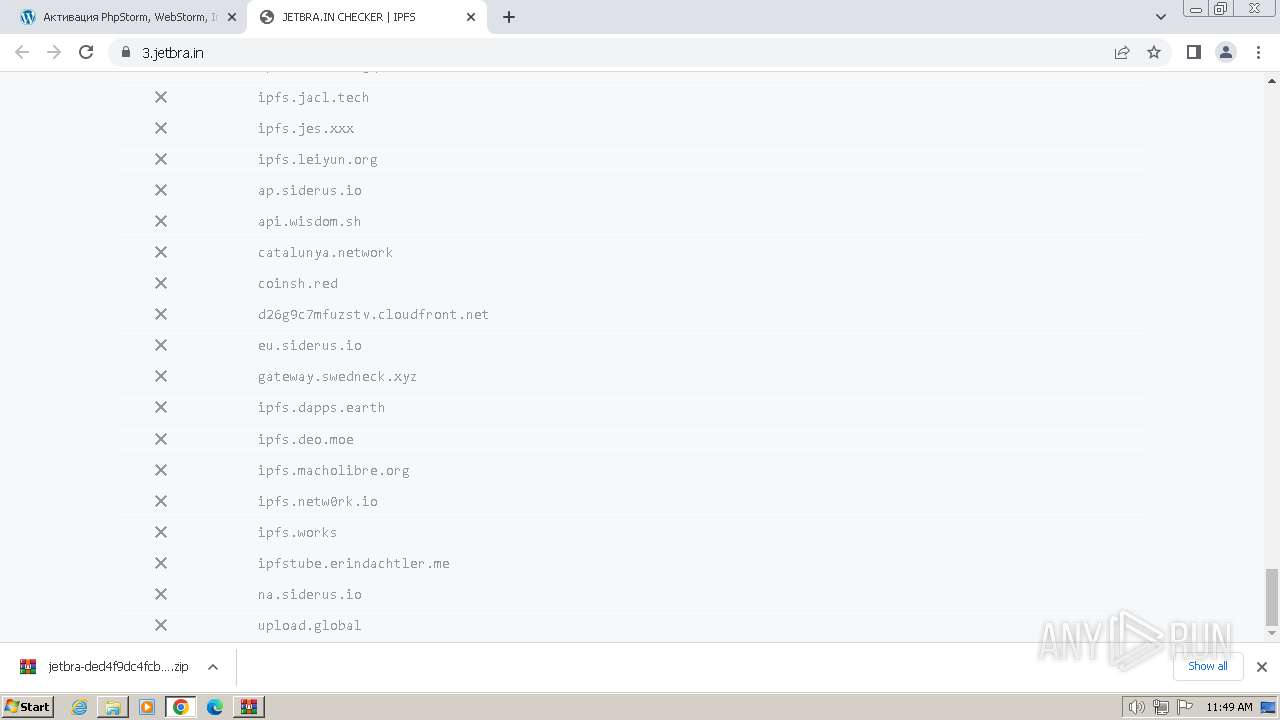
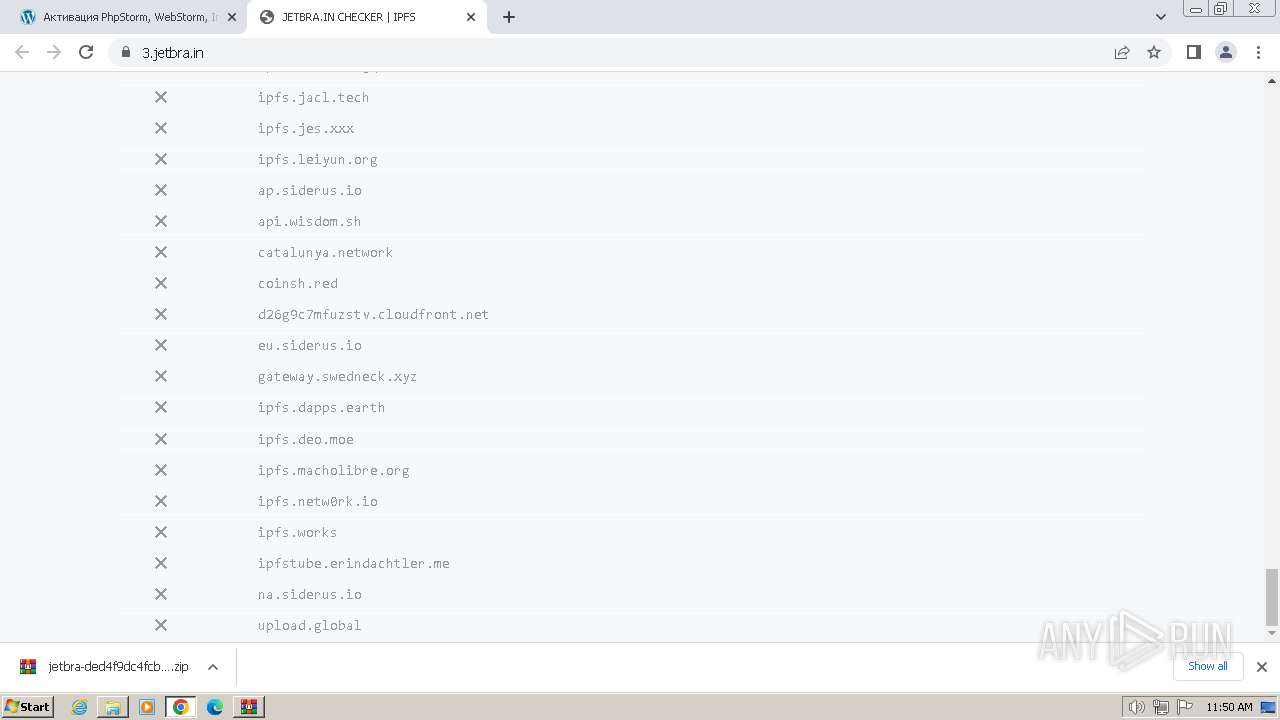
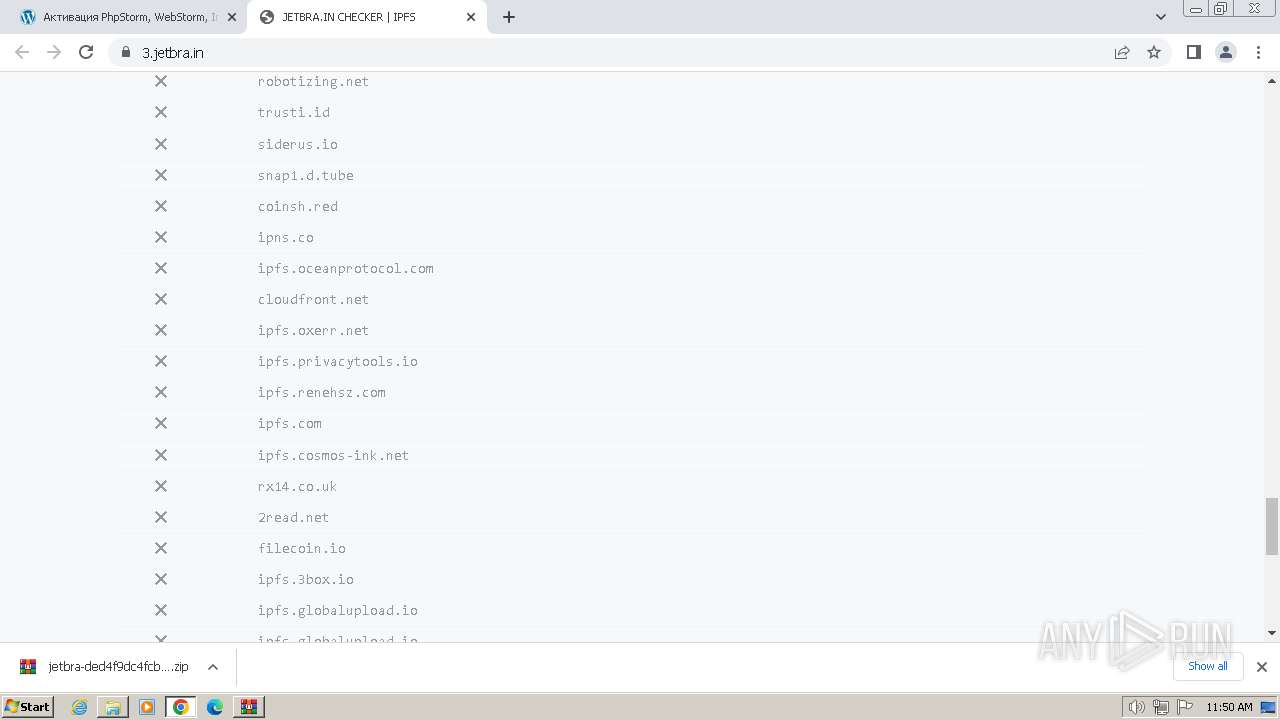
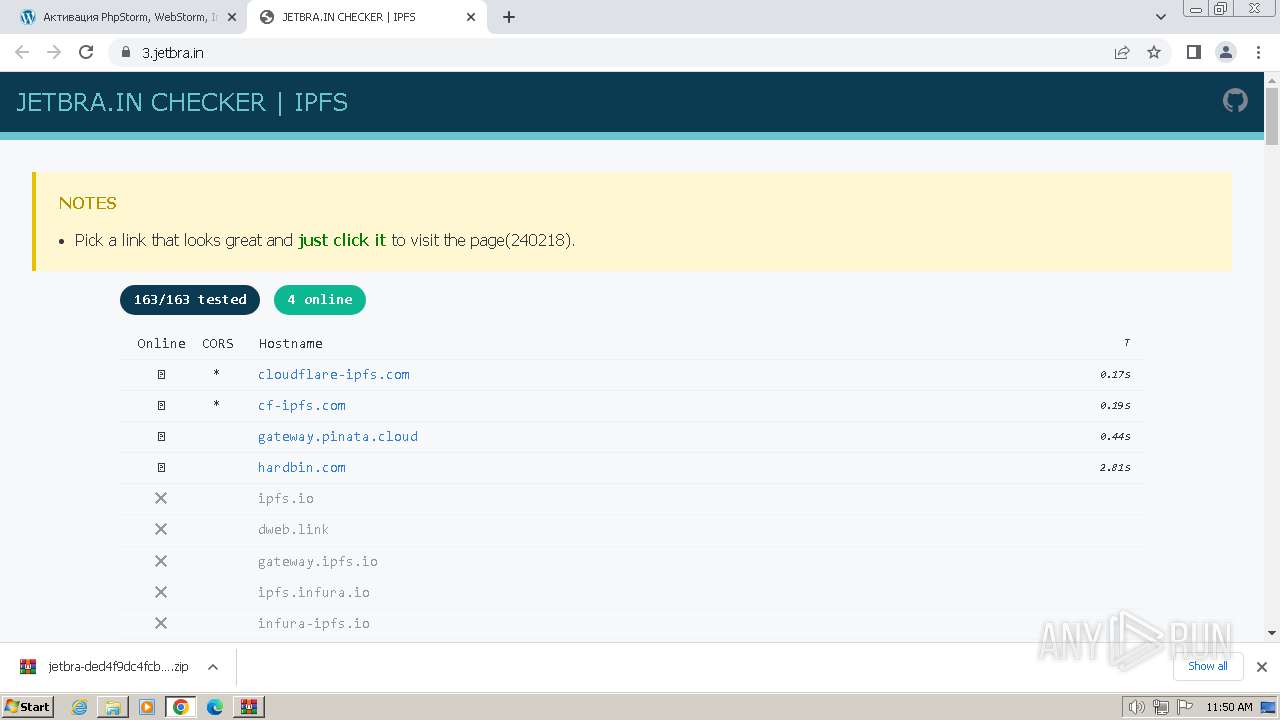
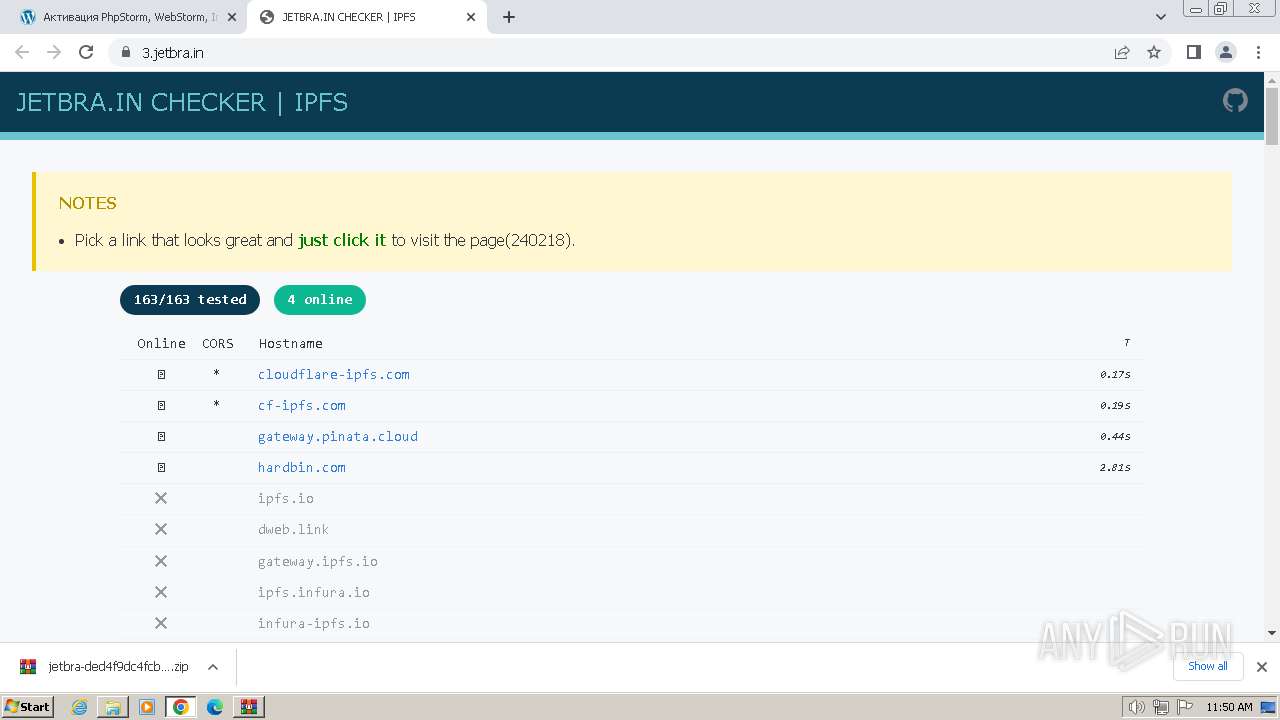
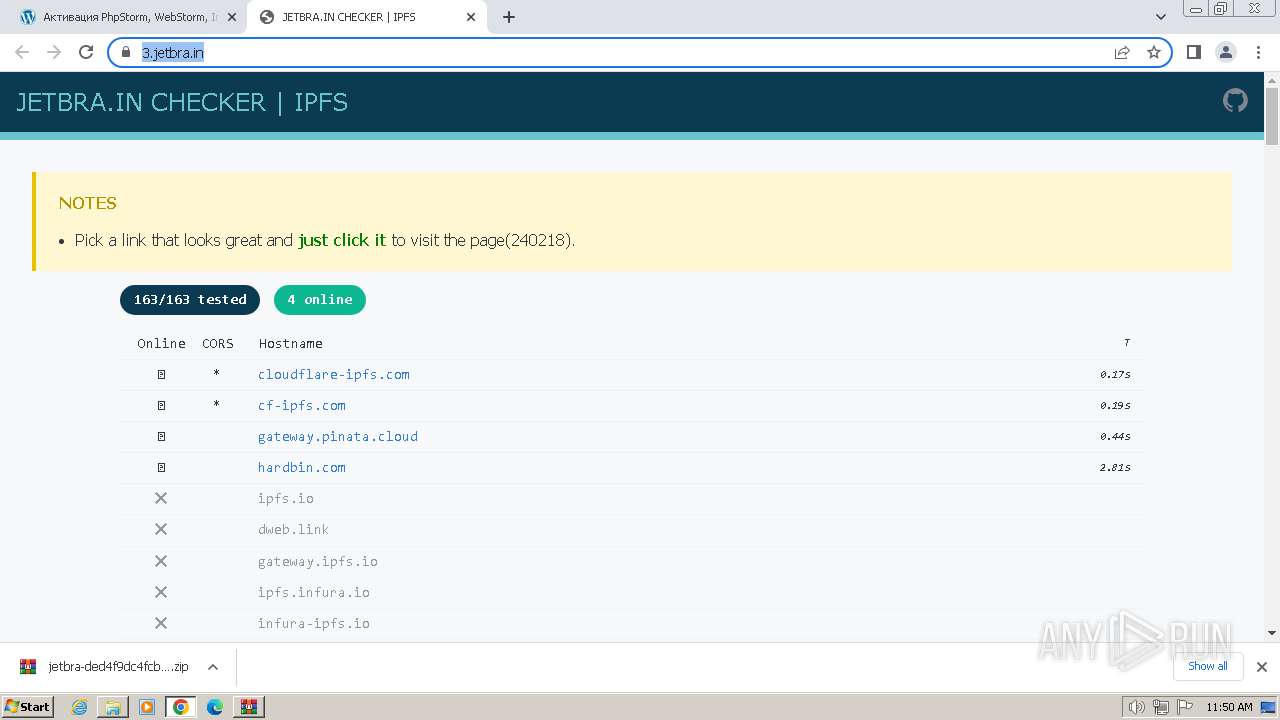
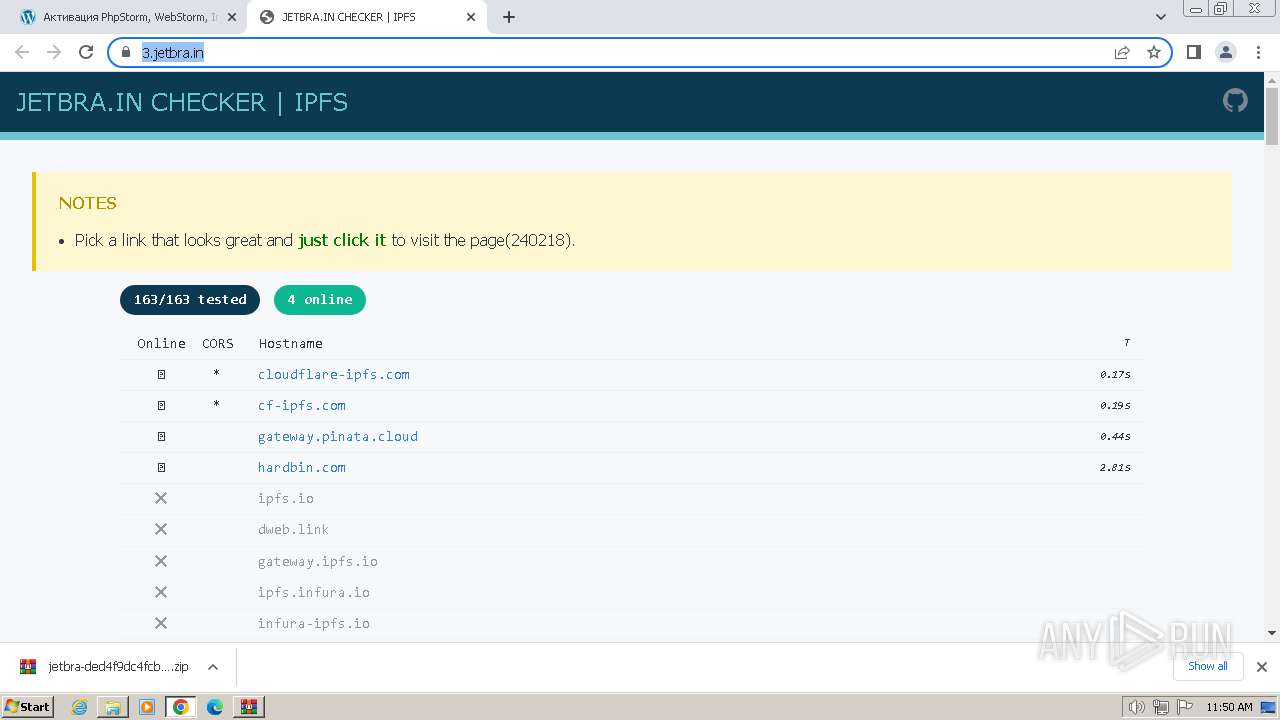
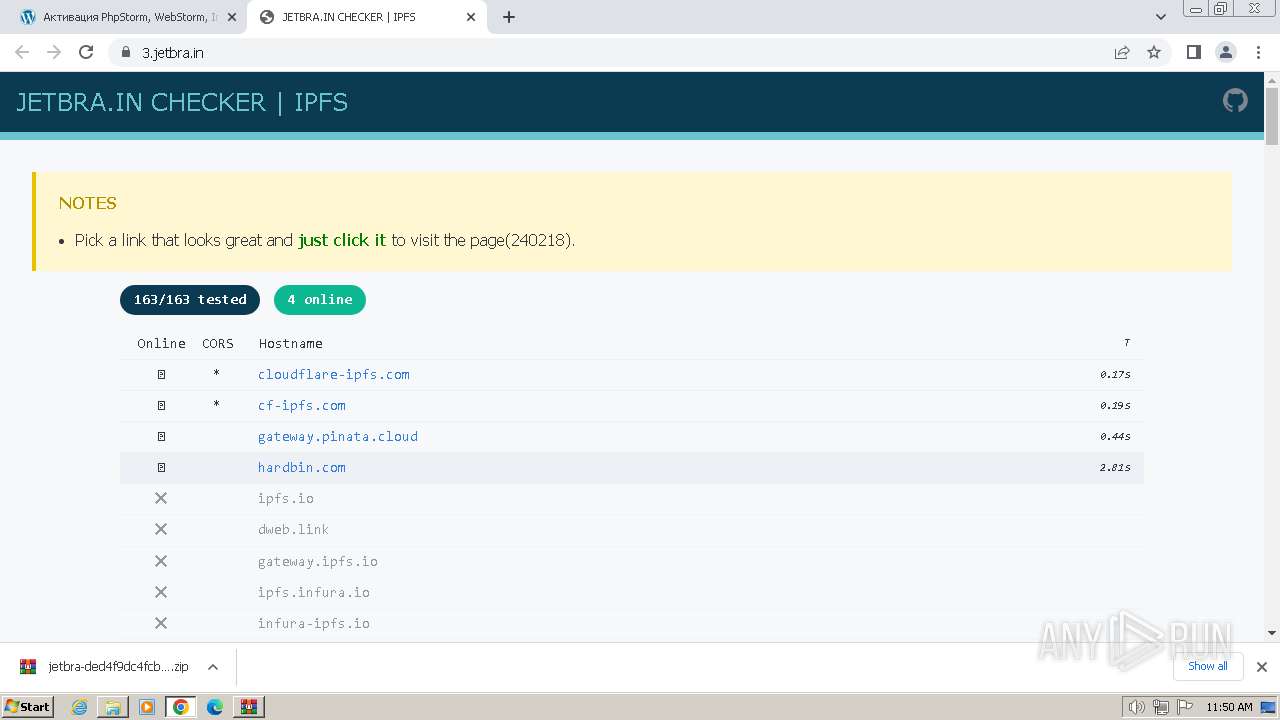
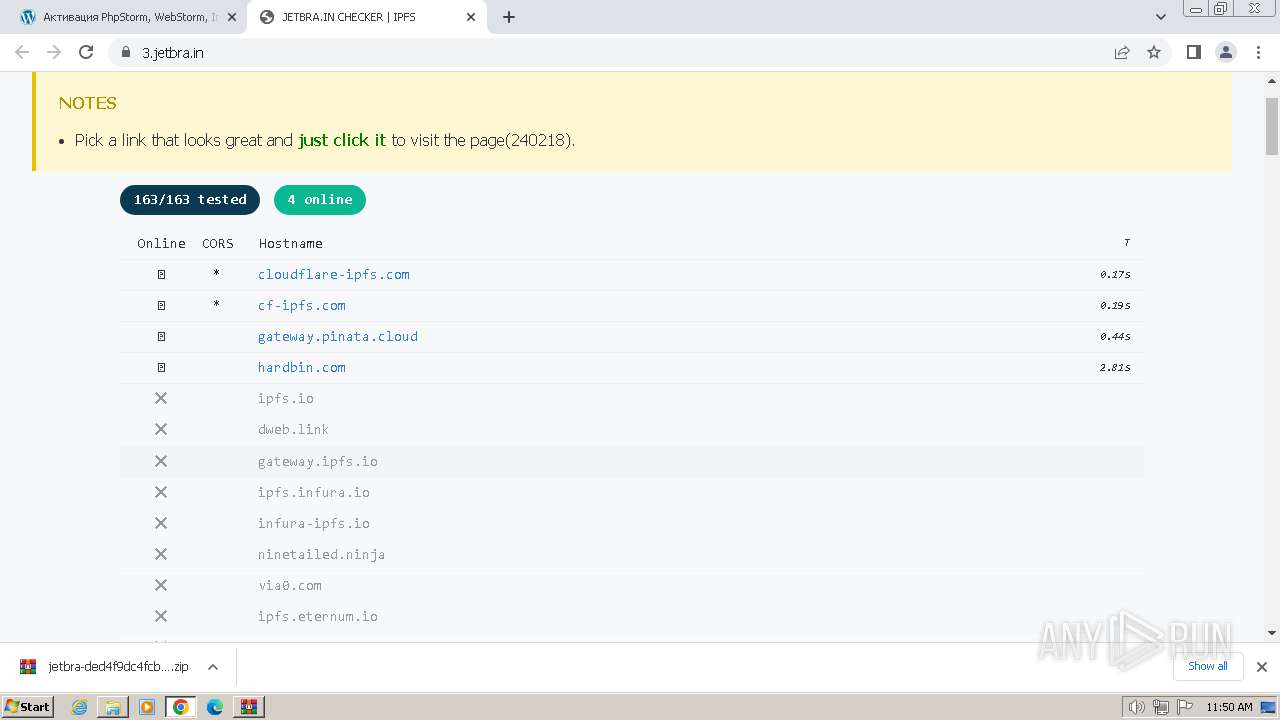
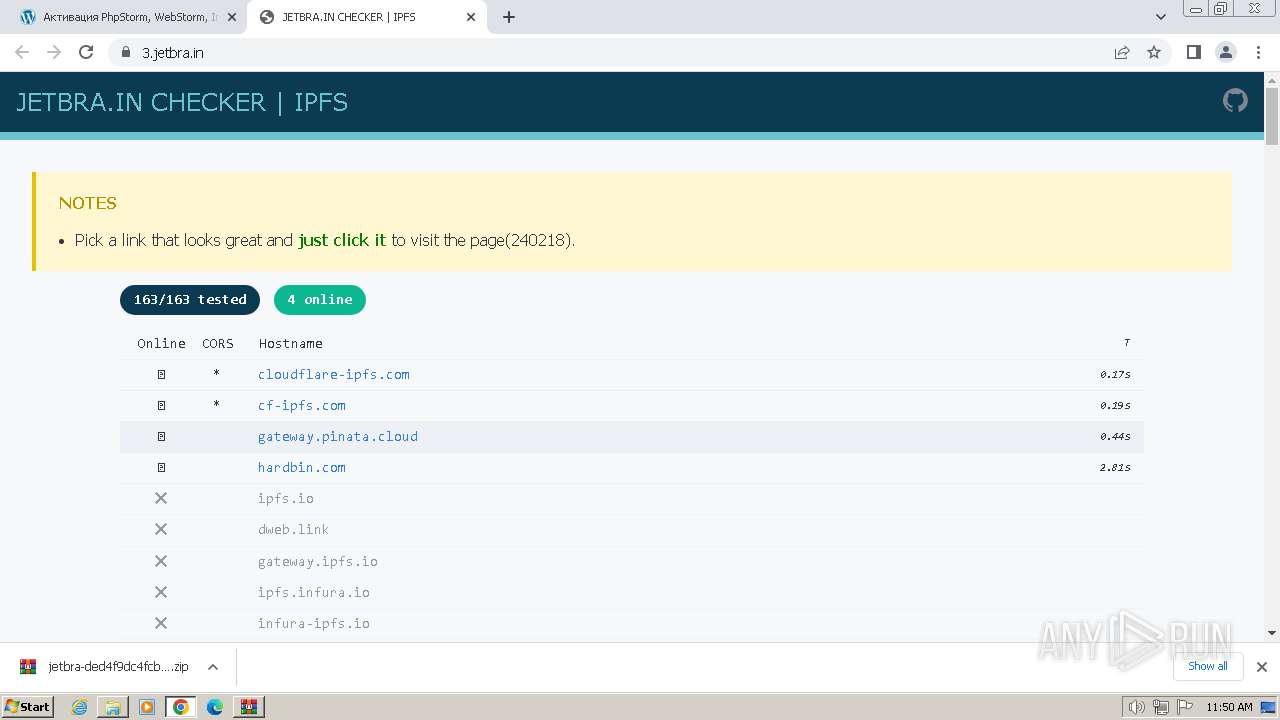
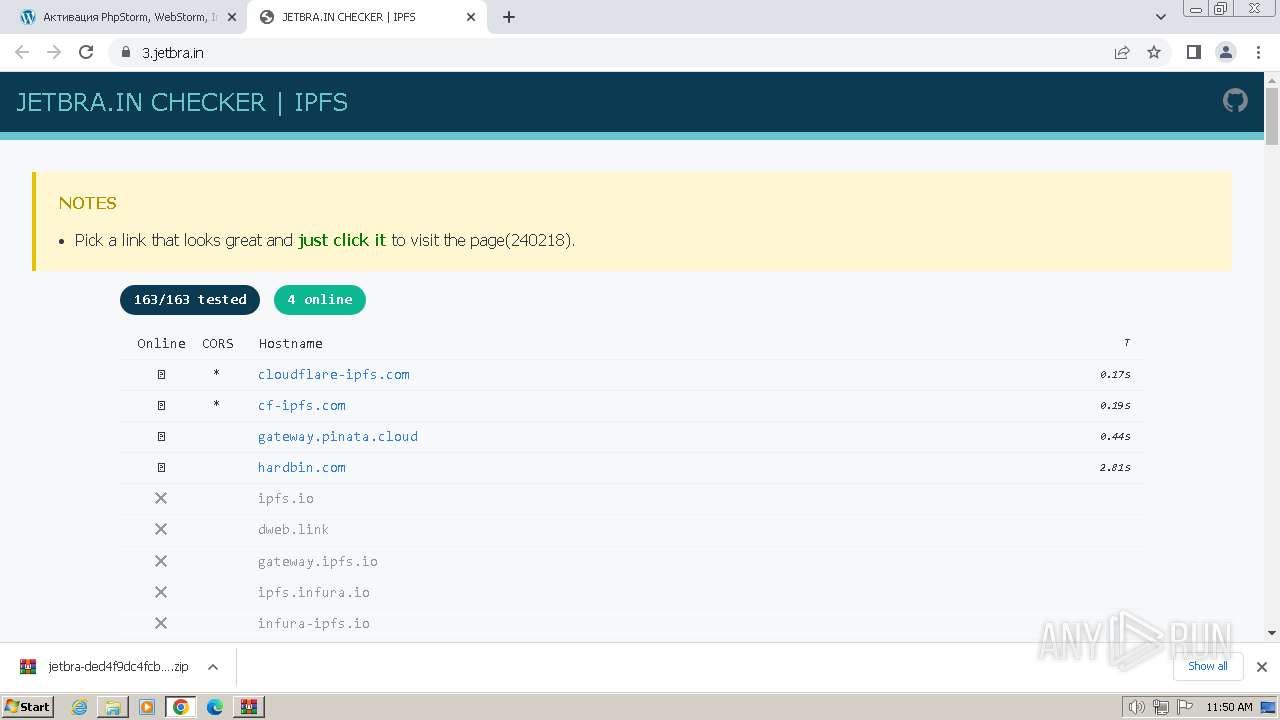
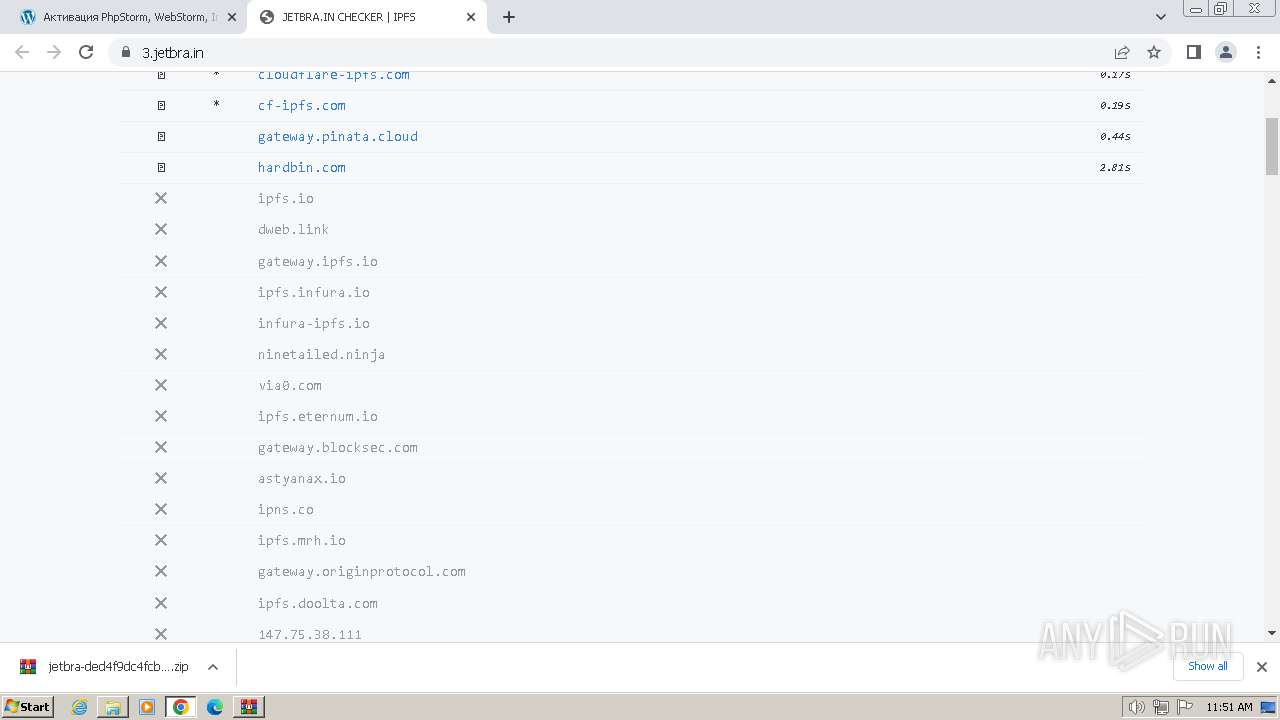
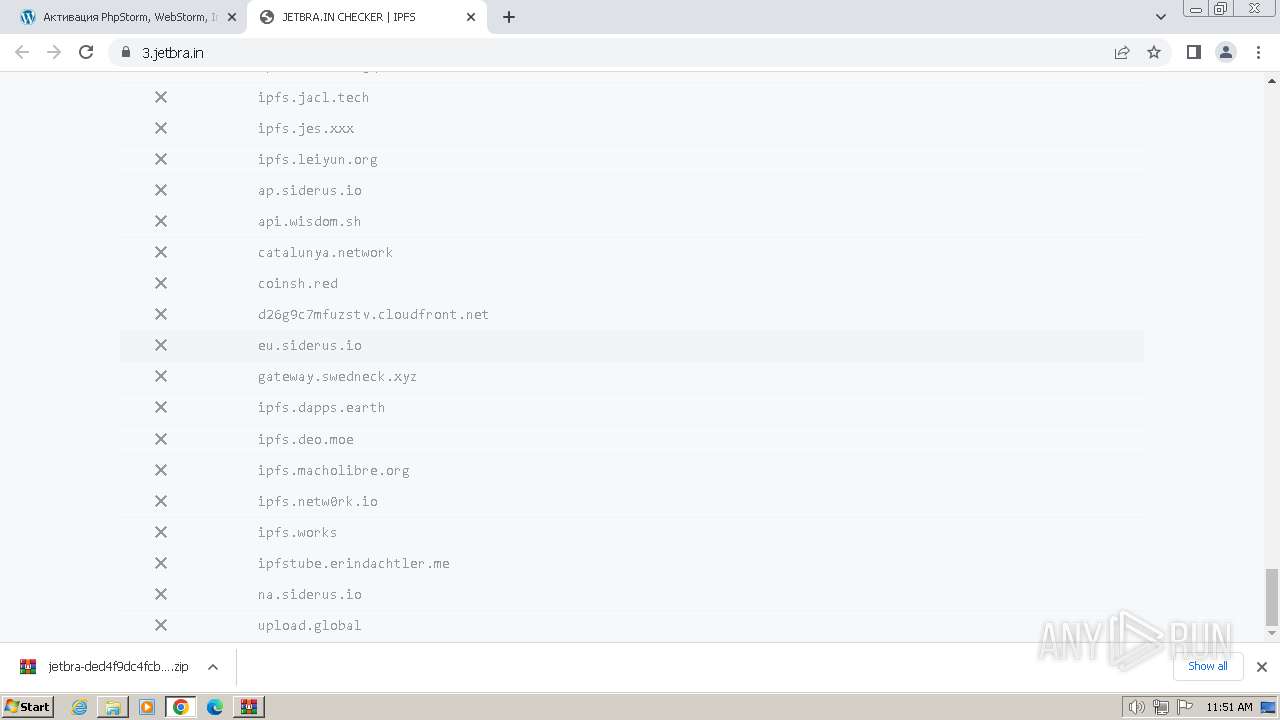
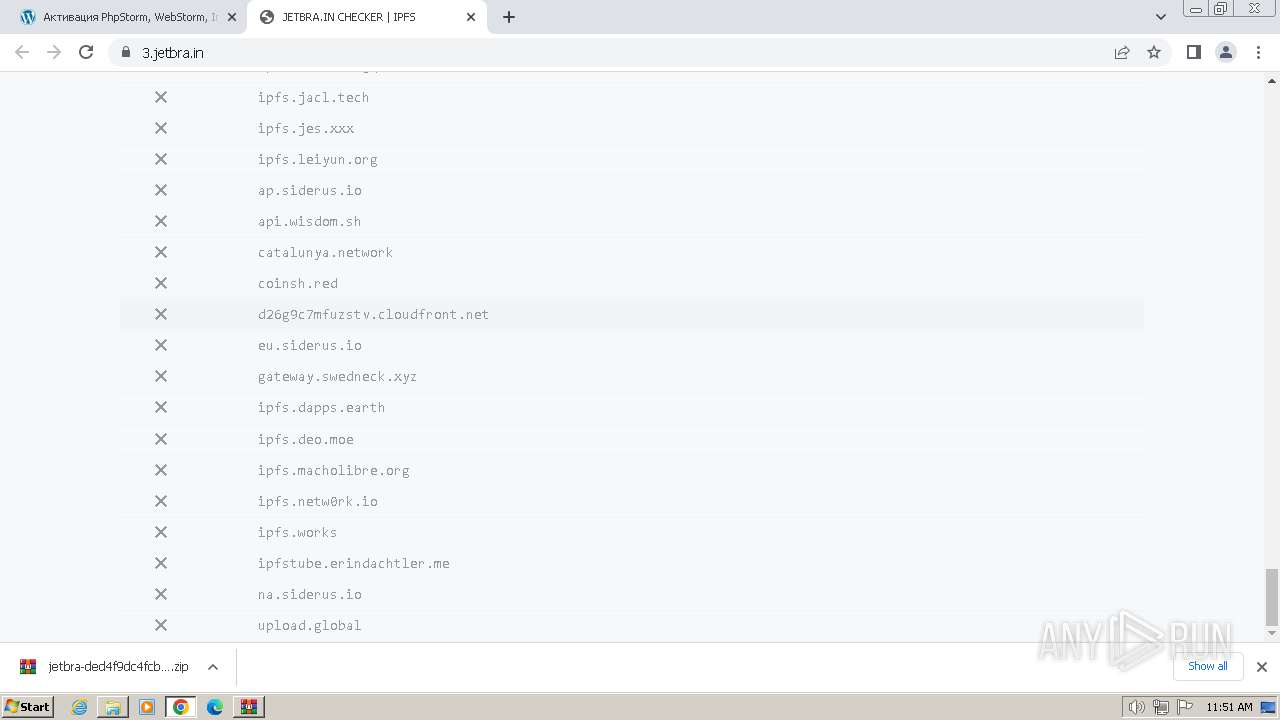
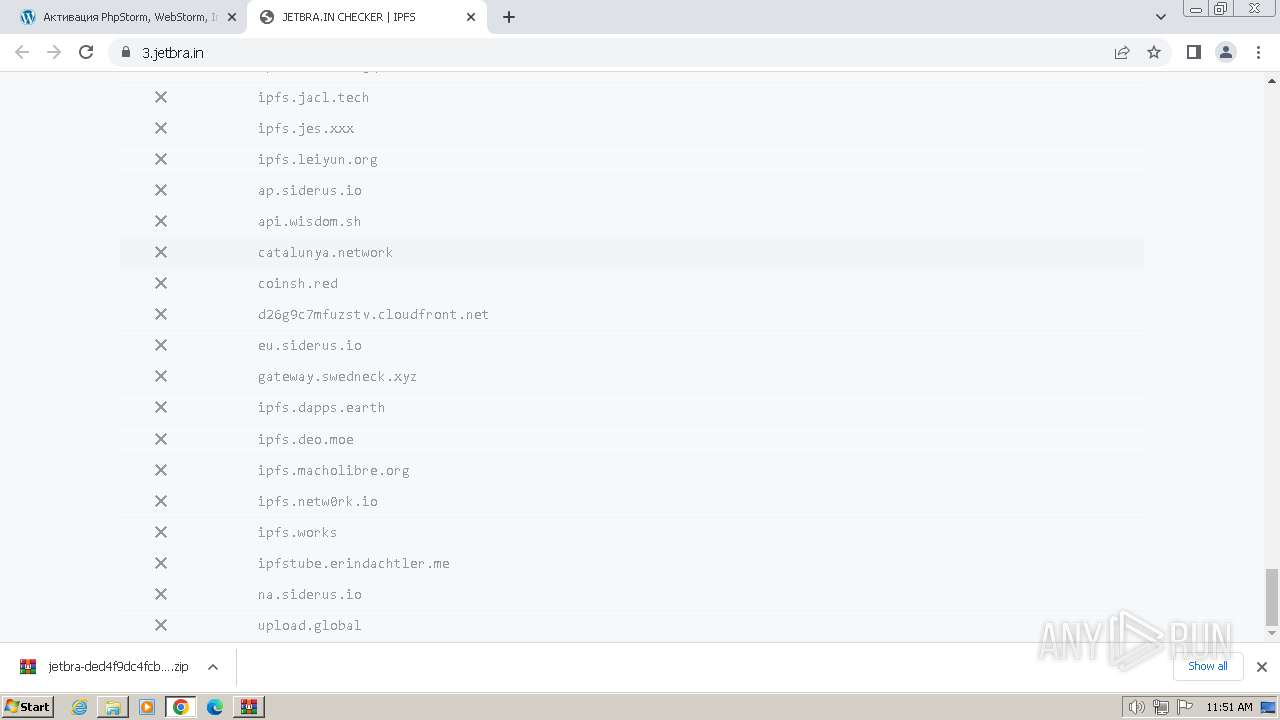
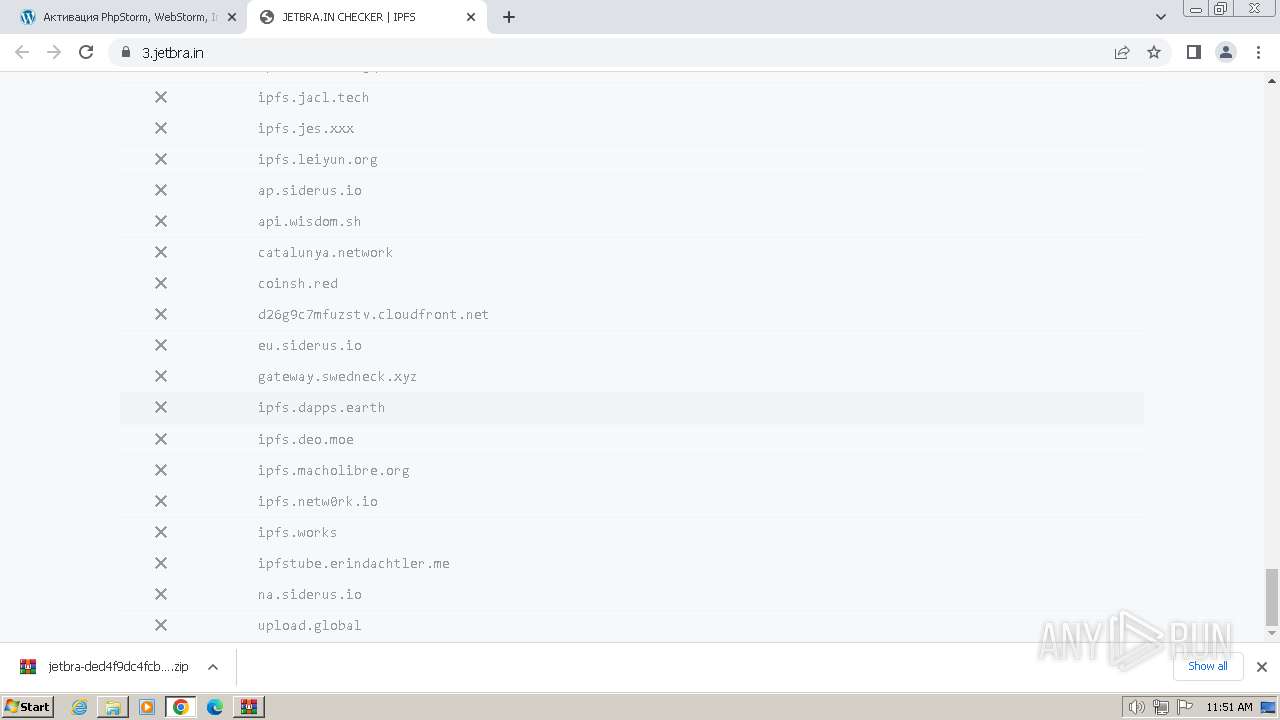
696 | chrome.exe | Potentially Bad Traffic | ET INFO Peer-to-Peer File Sharing Service Domain in DNS Lookup (ipfs .io) |
696 | chrome.exe | Potentially Bad Traffic | ET INFO Peer-to-Peer File Sharing Service Domain in DNS Lookup (ipfs .io) |
696 | chrome.exe | Potentially Bad Traffic | ET INFO Observed Peer-to-Peer File Sharing Service Domain (ipfs .io in TLS SNI) |
696 | chrome.exe | Potentially Bad Traffic | ET INFO Observed Peer-to-Peer File Sharing Service Domain (ipfs .io in TLS SNI) |
696 | chrome.exe | Potentially Bad Traffic | ET INFO Peer-to-Peer File Sharing Service Domain in DNS Lookup (ipfs .io) |
696 | chrome.exe | Potentially Bad Traffic | ET INFO Peer-to-Peer File Sharing Service Domain in DNS Lookup (ipfs .io) |
696 | chrome.exe | Misc activity | ET INFO Peer to Peer File Sharing Service in DNS Lookup (ipfs .infura .io) |
696 | chrome.exe | Misc activity | ET INFO Peer to Peer File Sharing Service in DNS Lookup (ipfs .infura .io) |
696 | chrome.exe | Potentially Bad Traffic | ET INFO Peer-to-Peer File Sharing Service Domain in DNS Lookup (ipfs .io) |
696 | chrome.exe | Potentially Bad Traffic | ET INFO Peer-to-Peer File Sharing Service Domain in DNS Lookup (ipfs .io) |