| File name: | phish_alert_sp2_2.0.0.0 (84).eml |
| Full analysis: | https://app.any.run/tasks/263e2c18-a508-45c3-8073-73cf7516abfd |
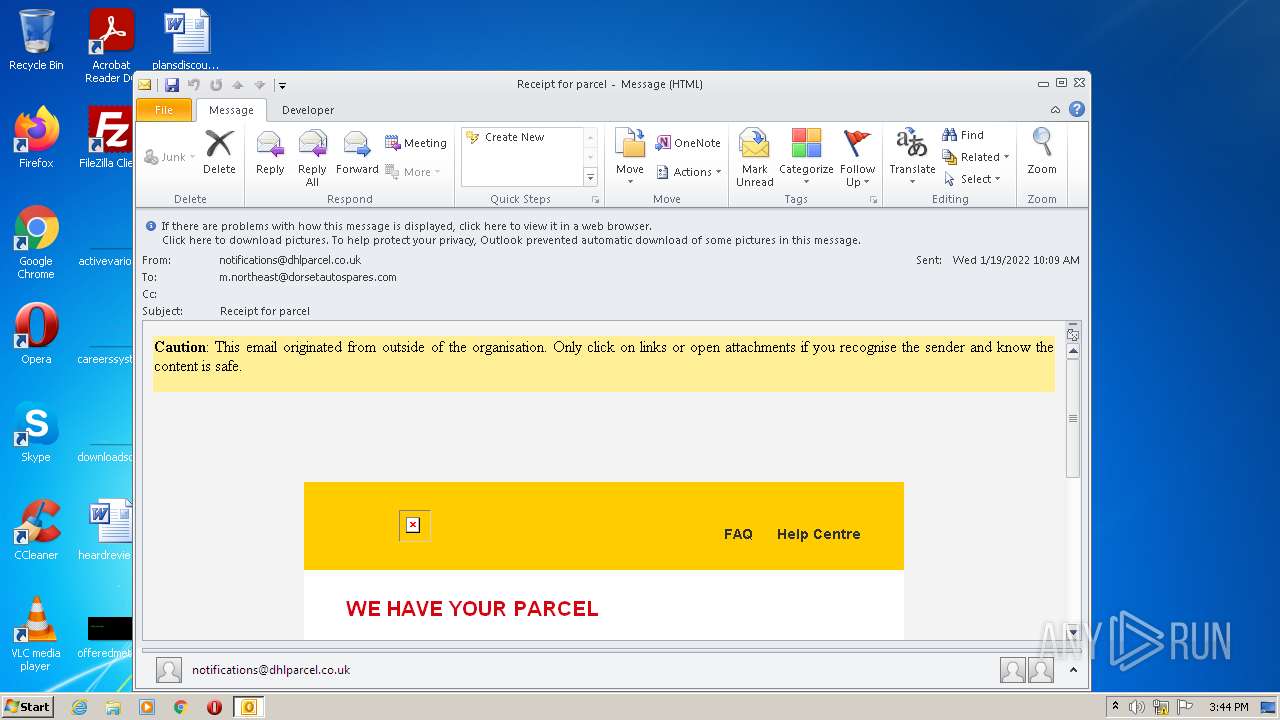
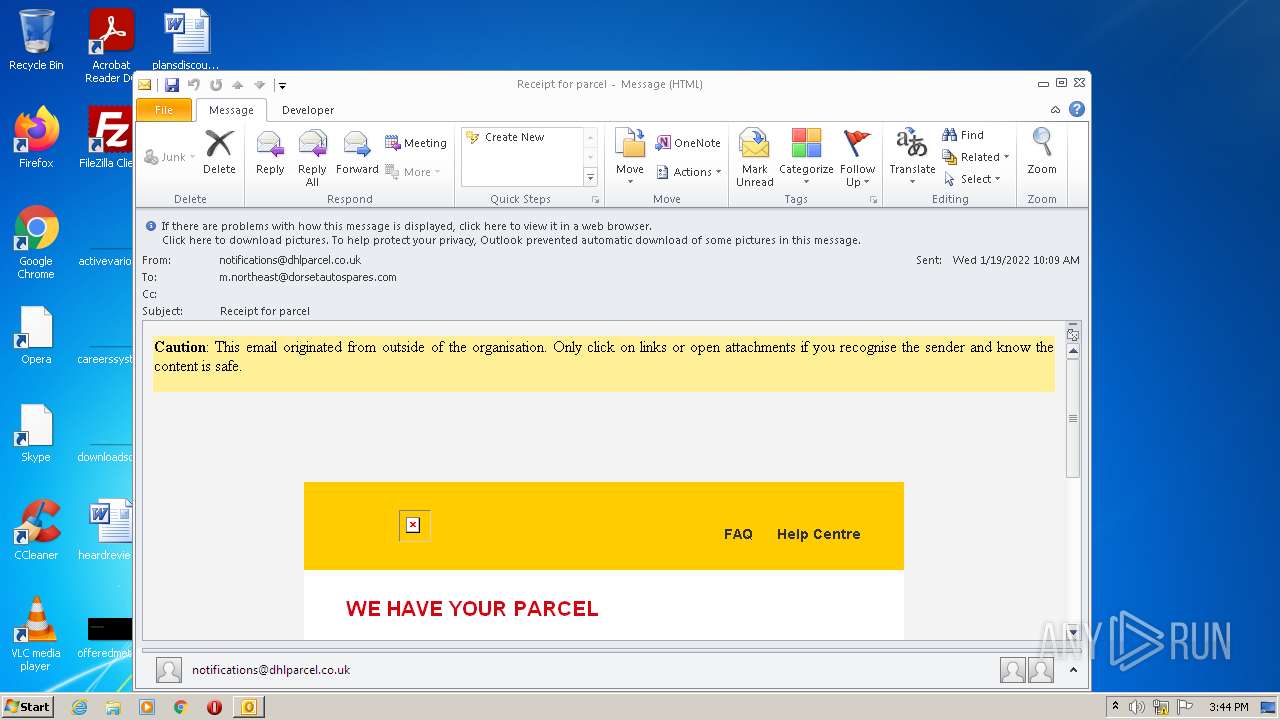
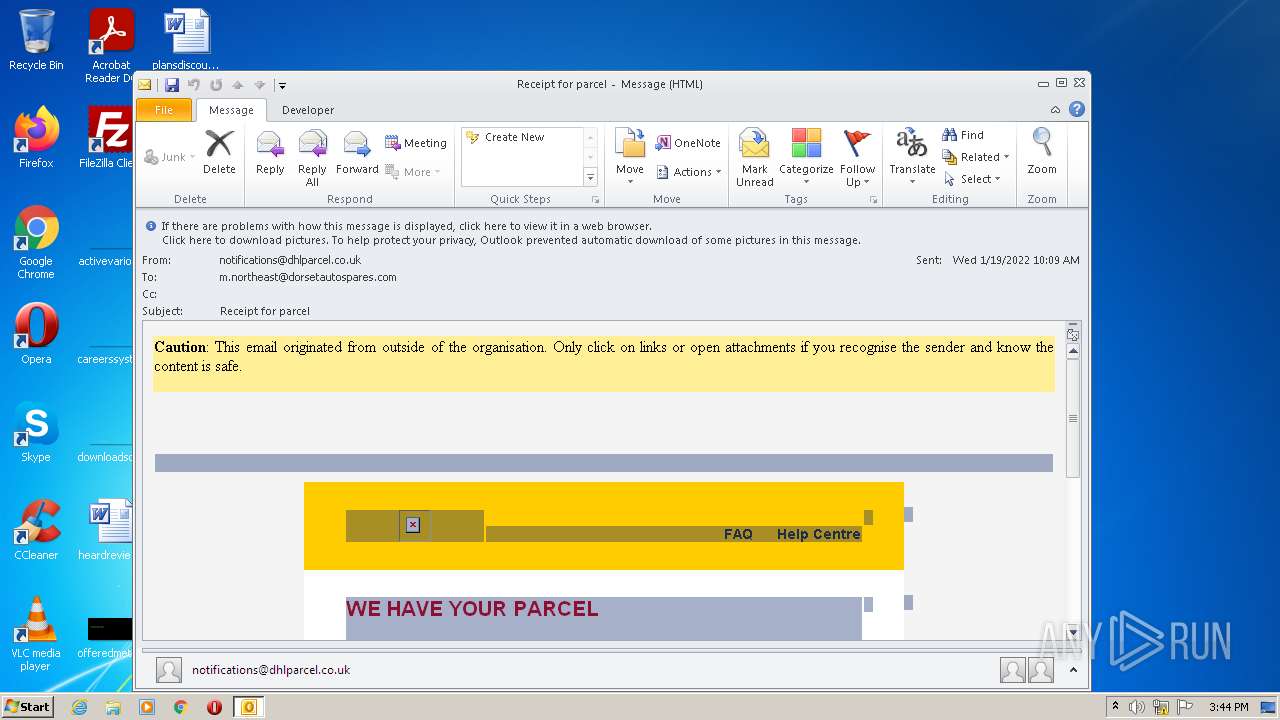
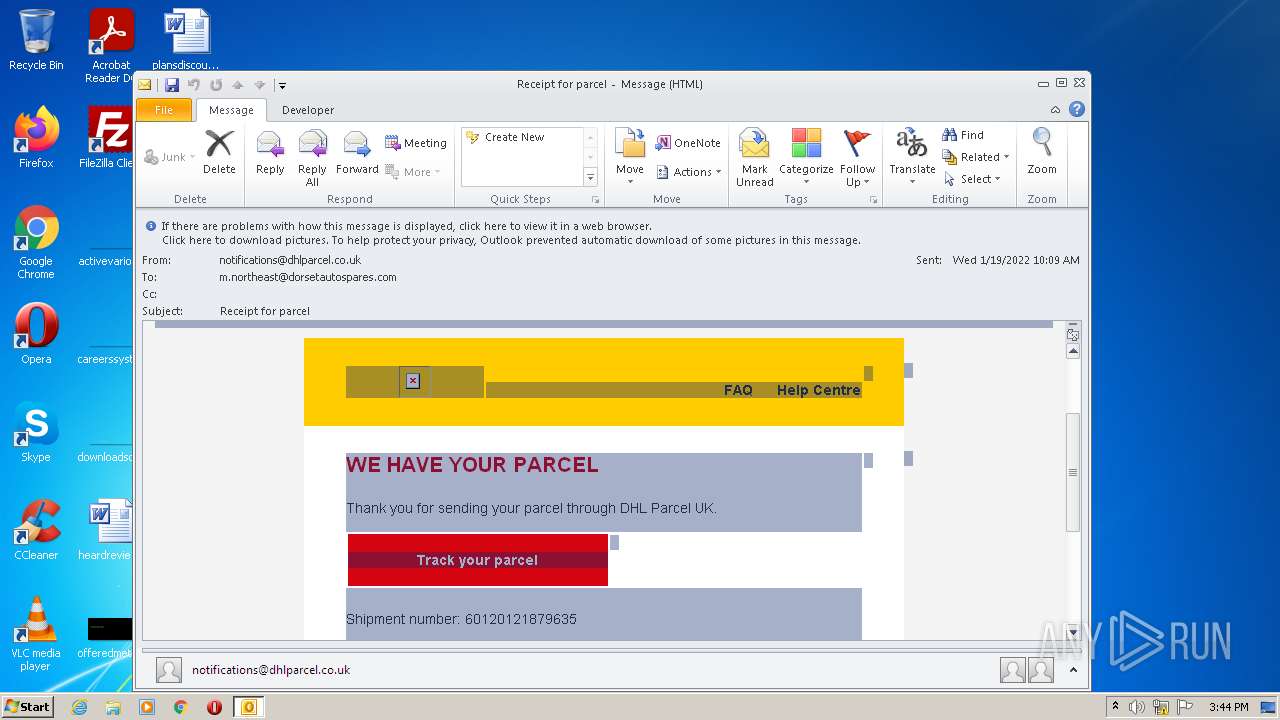
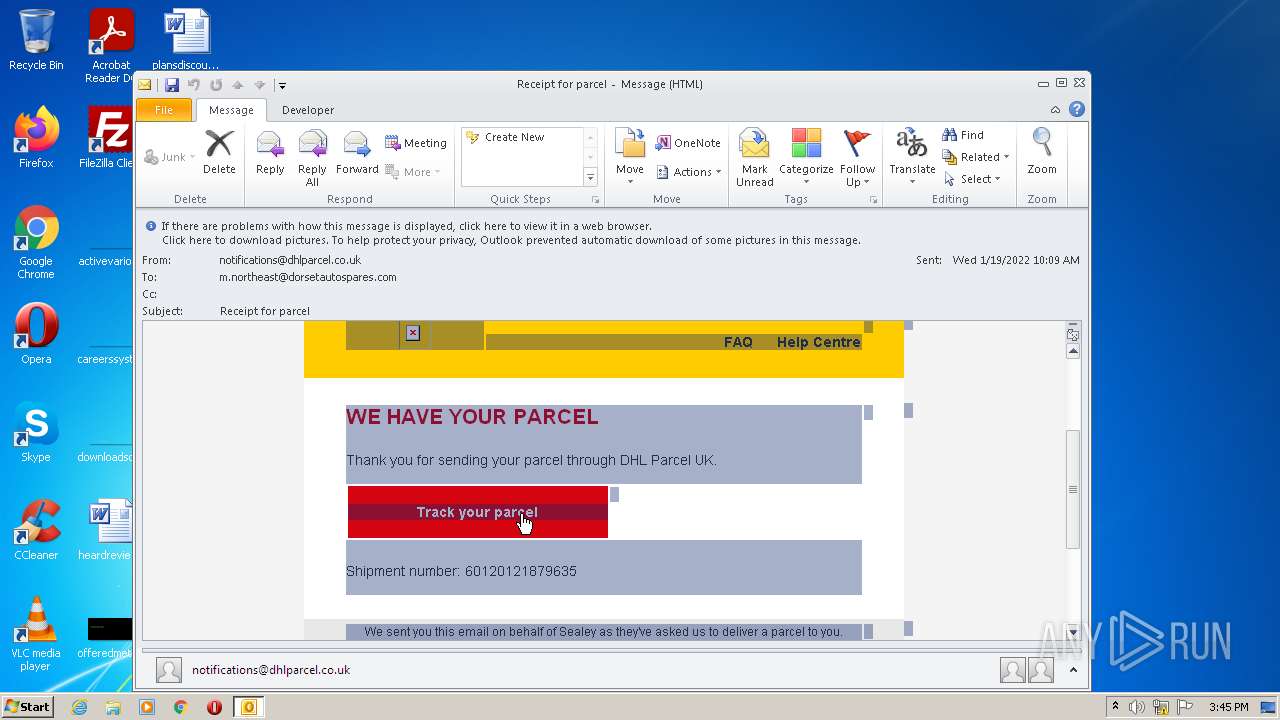
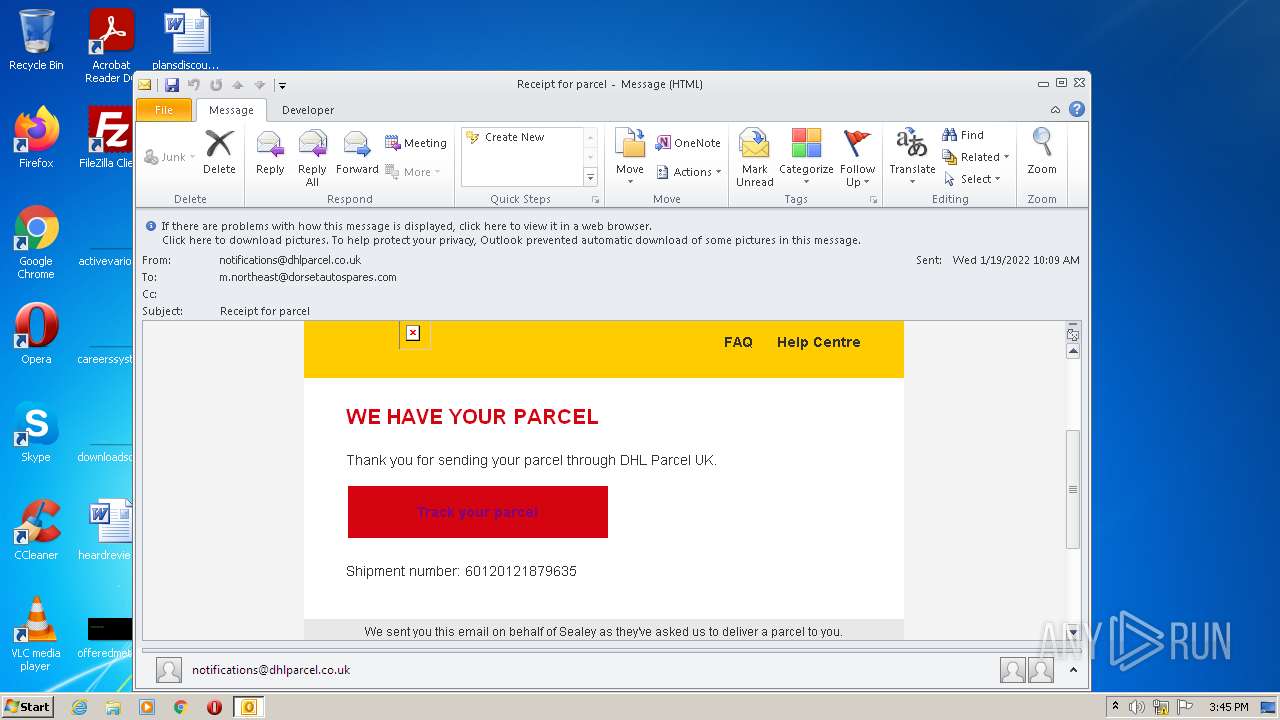
| Verdict: | Malicious activity |
| Analysis date: | January 24, 2022, 15:44:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 114D42ADEE4CBD7C3160EEACBF203D69 |
| SHA1: | 4D1356EF053853A9179178AC4B22FEA75394BE3D |
| SHA256: | B8F595BAED3C5A1E77E6BC6716289DE3507544C4F2BD556A22E7AD324DA60729 |
| SSDEEP: | 384:KnOpfzvDlUbNrz1BjnUsLi4e/9ahYo3drPcog5MNEUZB8cUGSOJN9WpW2c+:rzvRxD1xRJlp |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 2788)
Reads internet explorer settings
- OUTLOOK.EXE (PID: 2788)
Reads Microsoft Outlook installation path
- OUTLOOK.EXE (PID: 2788)
Reads the computer name
- OUTLOOK.EXE (PID: 2788)
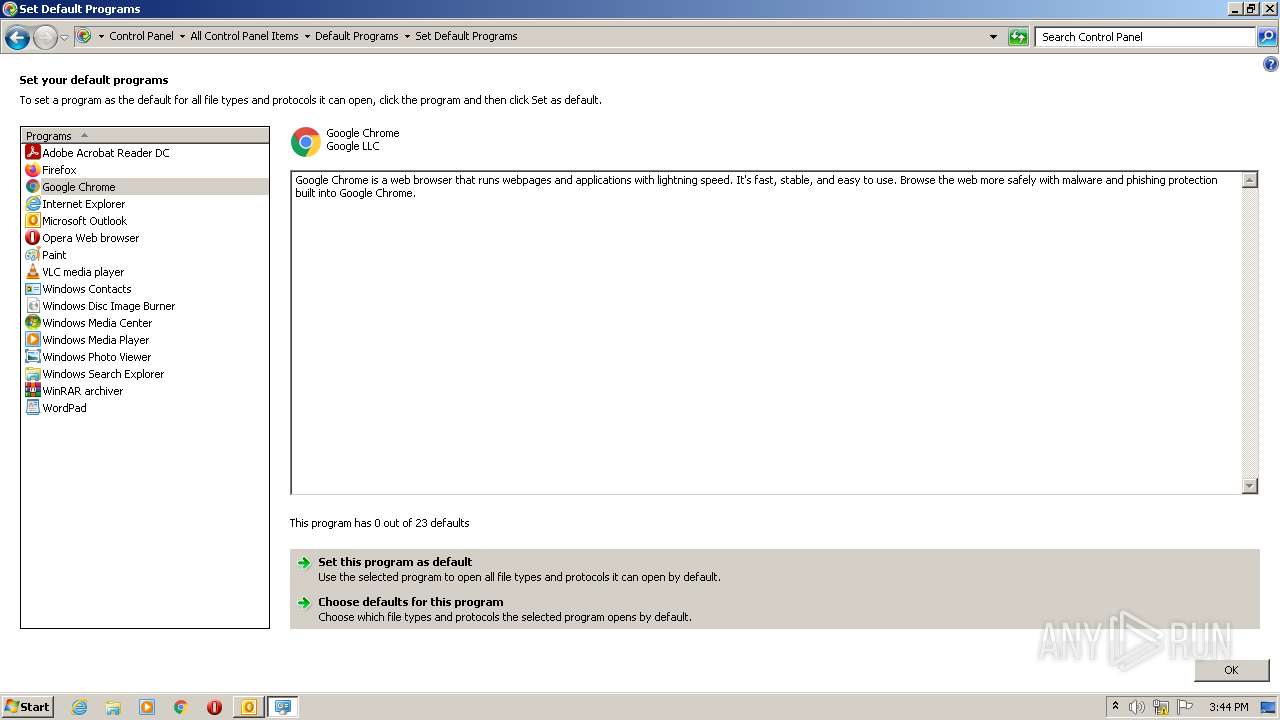
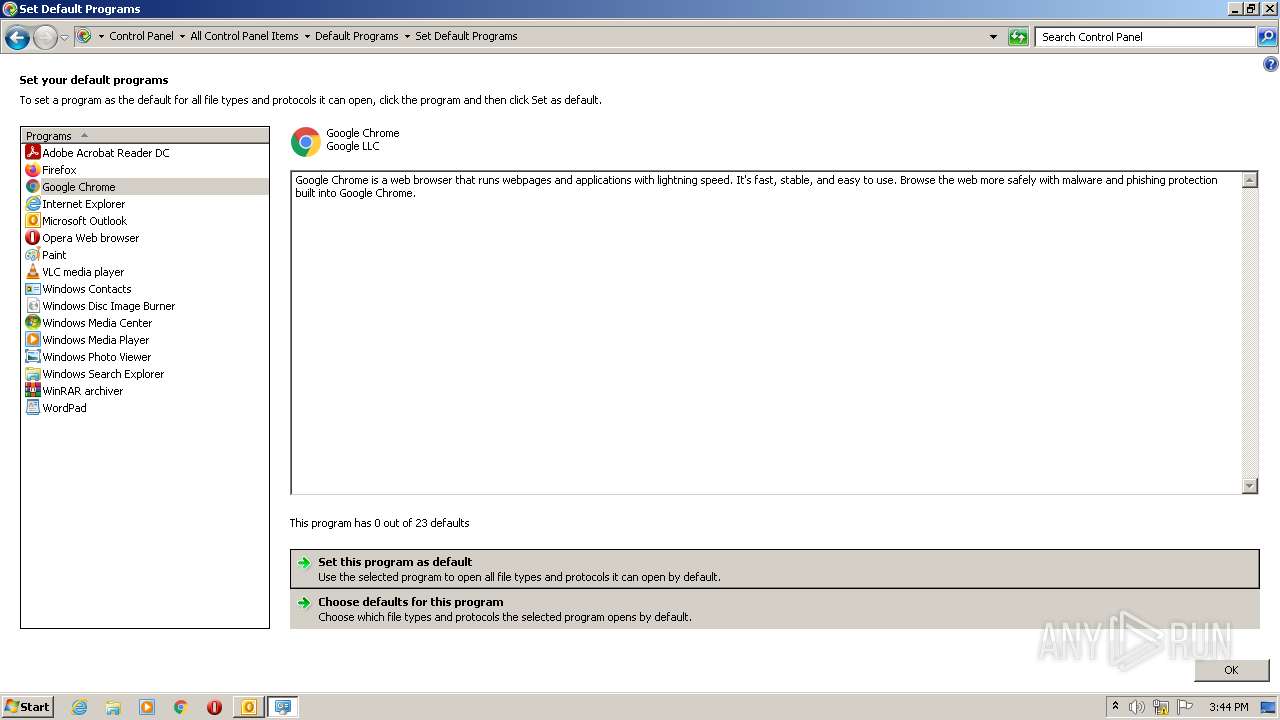
Searches for installed software
- OUTLOOK.EXE (PID: 2788)
Checks supported languages
- OUTLOOK.EXE (PID: 2788)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3884)
INFO
Reads the computer name
- control.exe (PID: 672)
- chrome.exe (PID: 3884)
- chrome.exe (PID: 3428)
- chrome.exe (PID: 1304)
- chrome.exe (PID: 3932)
- chrome.exe (PID: 748)
- chrome.exe (PID: 600)
Checks supported languages
- control.exe (PID: 672)
- chrome.exe (PID: 3884)
- chrome.exe (PID: 1304)
- chrome.exe (PID: 940)
- chrome.exe (PID: 3428)
- chrome.exe (PID: 2980)
- chrome.exe (PID: 2928)
- chrome.exe (PID: 2336)
- chrome.exe (PID: 3480)
- chrome.exe (PID: 3932)
- chrome.exe (PID: 748)
- chrome.exe (PID: 600)
- chrome.exe (PID: 3216)
- chrome.exe (PID: 2488)
- chrome.exe (PID: 3140)
- chrome.exe (PID: 2088)
- chrome.exe (PID: 3272)
Reads the hosts file
- chrome.exe (PID: 3884)
- chrome.exe (PID: 3428)
Application launched itself
- chrome.exe (PID: 3884)
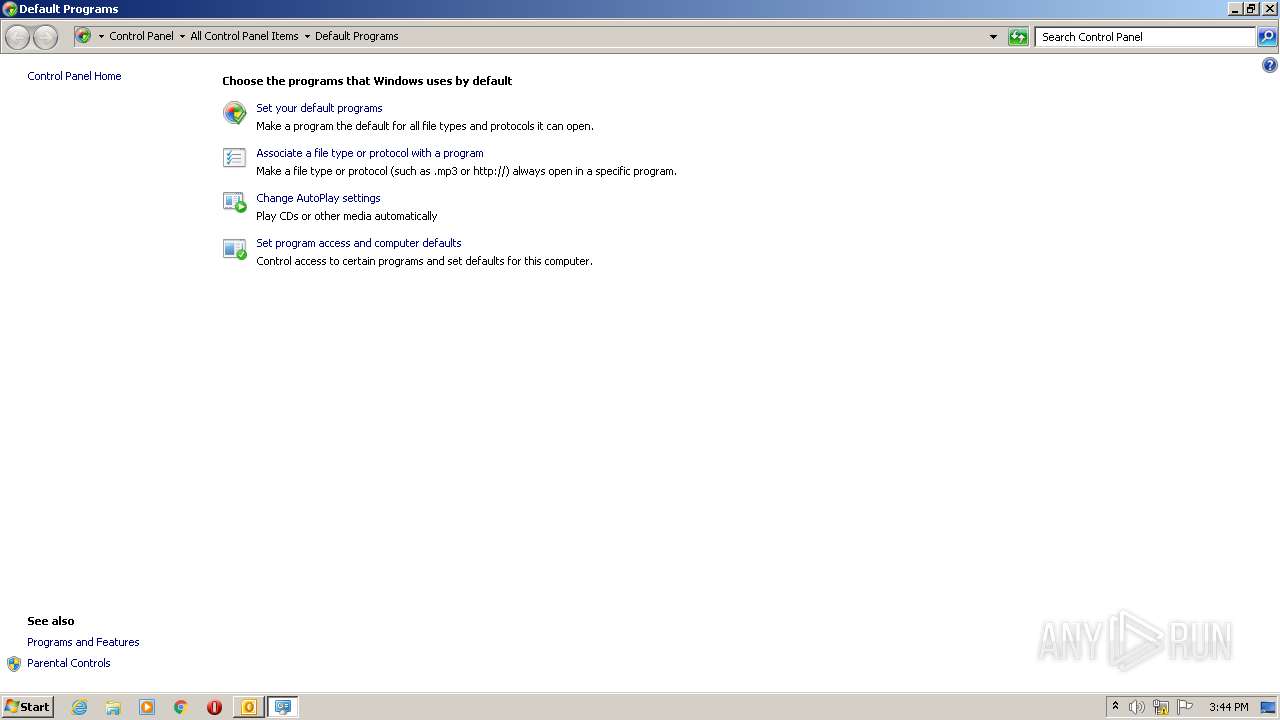
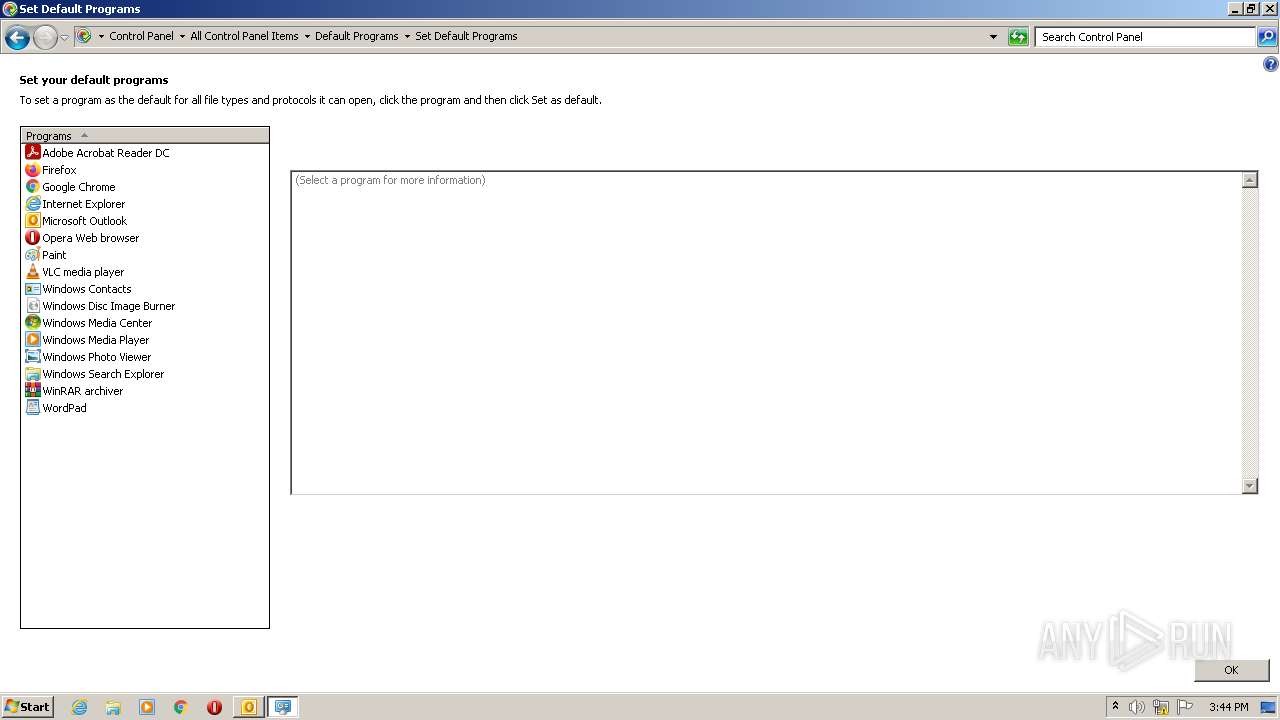
Manual execution by user
- control.exe (PID: 672)
Reads settings of System Certificates
- chrome.exe (PID: 3428)
Changes settings of System certificates
- chrome.exe (PID: 3428)
Reads the date of Windows installation
- chrome.exe (PID: 748)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2788)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
57
Monitored processes
18
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1116,11312840598581214962,12771358818982966601,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3168 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 672 | "C:\Windows\system32\control.exe" /name Microsoft.DefaultPrograms | C:\Windows\system32\control.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Control Panel Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1116,11312840598581214962,12771358818982966601,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3144 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6f4bd988,0x6f4bd998,0x6f4bd9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1116,11312840598581214962,12771358818982966601,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1132 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1116,11312840598581214962,12771358818982966601,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2968 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1116,11312840598581214962,12771358818982966601,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=536 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1116,11312840598581214962,12771358818982966601,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=876 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2788 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\phish_alert_sp2_2.0.0.0 (84).eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1116,11312840598581214962,12771358818982966601,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1916 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
12 751
Read events
12 106
Write events
624
Delete events
21
Modification events
| (PID) Process: | (2788) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2788) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2788) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2788) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2788) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2788) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2788) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2788) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2788) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (2788) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
159
Text files
113
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2788 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR3464.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2788 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 3884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61EEC97F-F2C.pma | — | |
MD5:— | SHA256:— | |||
| 2788 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 2788 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2788 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_Calendar_2_29308233B8A8C84A9458524C40823C66.dat | xml | |
MD5:B21ED3BD946332FF6EBC41A87776C6BB | SHA256:B1AAC4E817CD10670B785EF8E5523C4A883F44138E50486987DC73054A46F6F4 | |||
| 2788 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\{35333FF0-6170-4212-A81D-F8FB9D4C4530}\{1C306CB1-771E-4B4B-A902-86E897877F5B}.png | image | |
MD5:4C61C12EDBC453D7AE184976E95258E1 | SHA256:296526F9A716C1AA91BA5D6F69F0EB92FDF79C2CB2CFCF0CEB22B7CCBC27035F | |||
| 2788 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_WorkHours_1_3EE0E6CA1B9ED14BB94BFE4EF9DE9456.dat | xml | |
MD5:807EF0FC900FEB3DA82927990083D6E7 | SHA256:4411E7DC978011222764943081500FFF0E43CBF7CCD44264BD1AB6306CA68913 | |||
| 2788 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_AvailabilityOptions_2_83B0030A84431842A829EDC5E18E08CB.dat | xml | |
MD5:EEAA832C12F20DE6AAAA9C7B77626E72 | SHA256:C4C9A90F2C961D9EE79CF08FBEE647ED7DE0202288E876C7BAAD00F4CA29CA16 | |||
| 2788 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_ConversationPrefs_2_04F80C5073D30248947319C4E30CF29E.dat | xml | |
MD5:57F30B1BCA811C2FCB81F4C13F6A927B | SHA256:612BAD93621991CB09C347FF01EC600B46617247D5C041311FF459E247D8C2D3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
52
DNS requests
30
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
884 | svchost.exe | HEAD | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/mhzu72vkczhlmfqomqnf35nvau_2765/jflookgnkcckhobaglndicnbbgbonegd_2765_all_jdd5fasdwpeesmnmtivieegk2a.crx3 | US | — | — | whitelisted |
884 | svchost.exe | HEAD | 200 | 74.125.105.8:80 | http://r3---sn-aigl6ns6.gvt1.com/edgedl/release2/chrome_component/mhzu72vkczhlmfqomqnf35nvau_2765/jflookgnkcckhobaglndicnbbgbonegd_2765_all_jdd5fasdwpeesmnmtivieegk2a.crx3?cms_redirect=yes&mh=Vt&mip=85.203.46.147&mm=28&mn=sn-aigl6ns6&ms=nvh&mt=1643038820&mv=m&mvi=3&pl=25&shardbypass=yes&smhost=r3---sn-aigl6nl7.gvt1.com | US | — | — | whitelisted |
2788 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
3428 | chrome.exe | GET | 204 | 172.217.18.99:80 | http://www.gstatic.com/generate_204 | US | — | — | whitelisted |
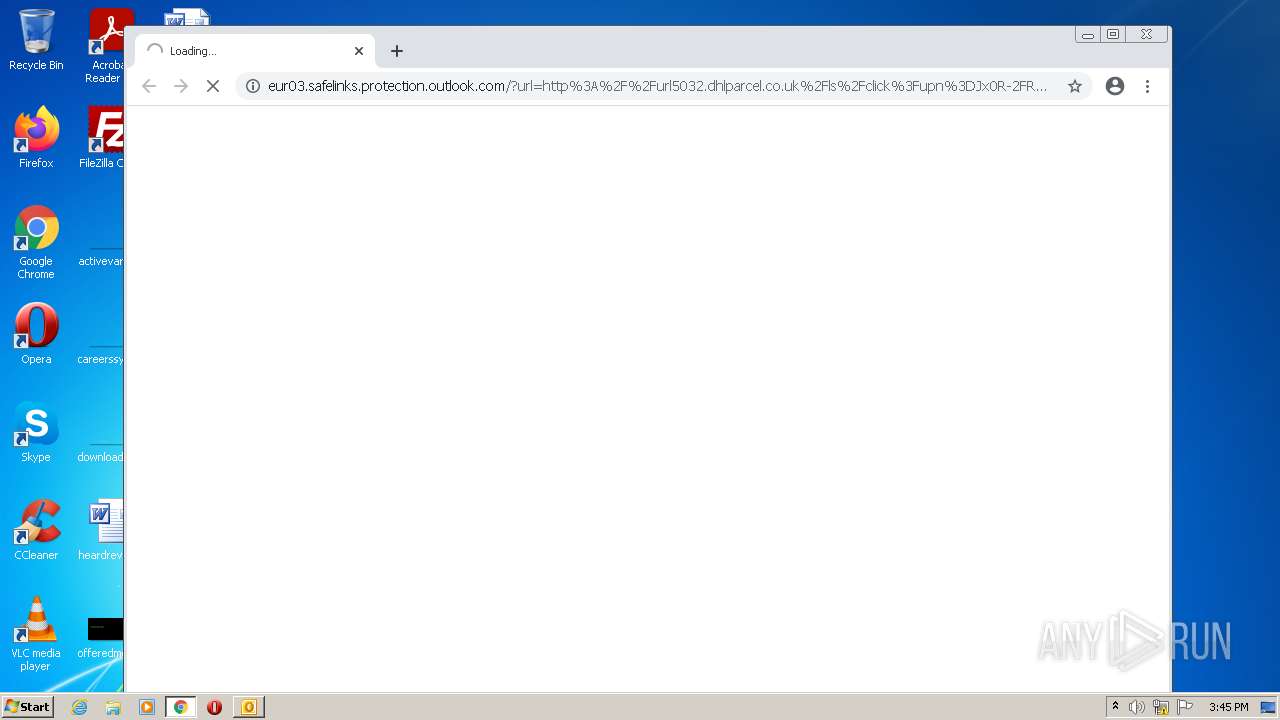
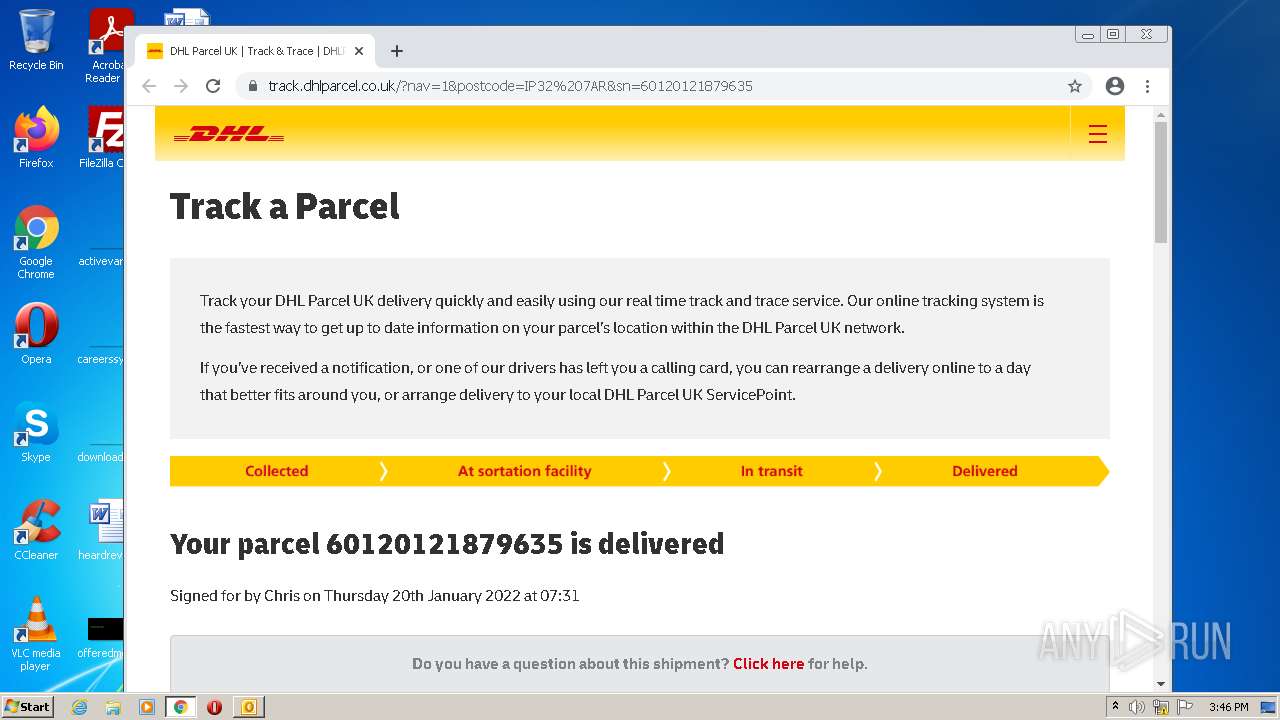
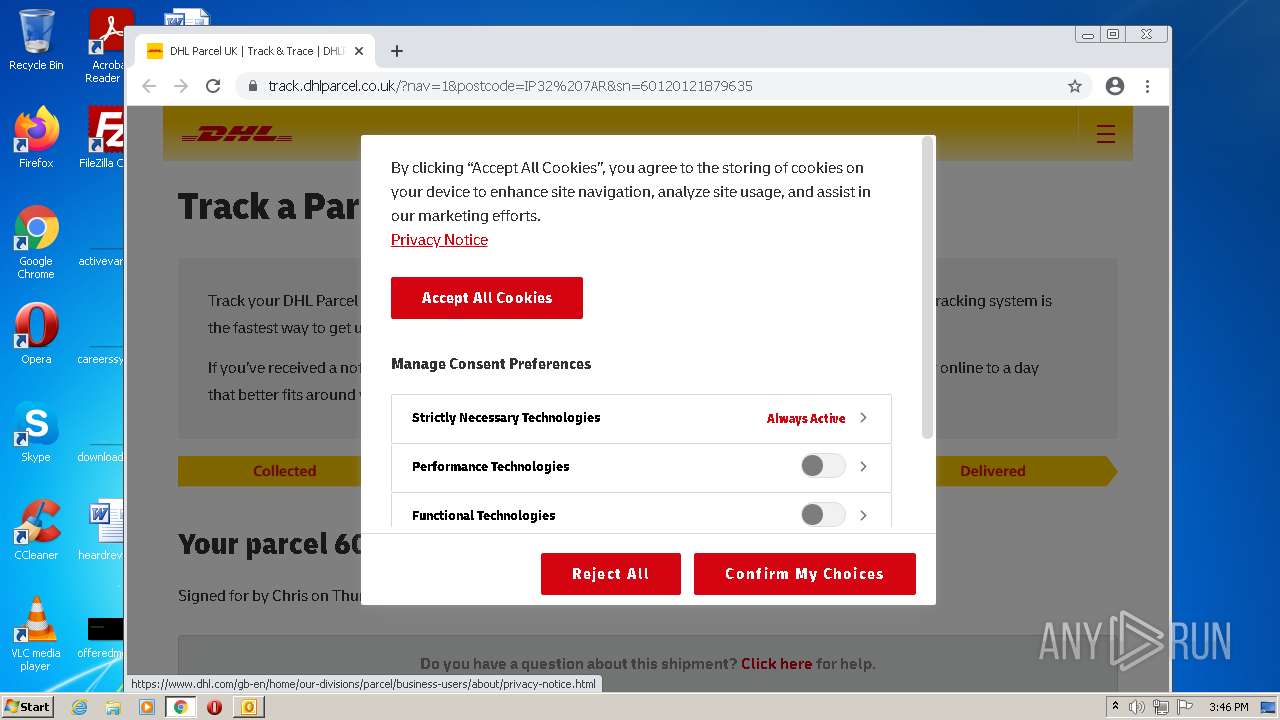
3428 | chrome.exe | GET | 302 | 167.89.123.124:80 | http://url5032.dhlparcel.co.uk/ls/click?upn=Jx0R-2FRxfM1xa6etTK8InfHP7uT9ST1z0hxyew7gUDTgfKlQwJFk0-2BNSPS2l6uP4j9VDH_YToGFXjpXR-2F-2BFtYqrwgPjbIMoCBlnKmAP6oKYfzNiebjdMp0MJBMEgx8g0irUX666OlixJrlAsFuPoGZplAv7tCqT7tuoAWM3YF708cyHuAFqwZ7QDluKIyHdFAIuM73wQ4UX-2BZ0sL89qS3cXzYYnGx0h2PRcGbXShHKaWOc8Qysu0GwWTL1AC6fQZ9gXurPtEzyXiWeZ7RulxbLOFm2hpUnOtqlAPjYg9Pqe-2BYuoZ14im2OkxB-2FBP4jEbCh9xLN9WUTs3htx8t-2Fq2mICbQxsytJFplZPgU1rLxUj6OlwFZ4Bt21nCQe5FwKG0ZPdPJ7Kcz1K6ug-2BCU5xW3MLYf5Q-2FEZLUF7Txb2AbdbJLt5FsE-3D | US | html | 57 b | suspicious |
884 | svchost.exe | GET | 206 | 74.125.105.8:80 | http://r3---sn-aigl6ns6.gvt1.com/edgedl/release2/chrome_component/mhzu72vkczhlmfqomqnf35nvau_2765/jflookgnkcckhobaglndicnbbgbonegd_2765_all_jdd5fasdwpeesmnmtivieegk2a.crx3?cms_redirect=yes&mh=Vt&mip=85.203.46.147&mm=28&mn=sn-aigl6ns6&ms=nvh&mt=1643038820&mv=m&mvi=3&pl=25&shardbypass=yes&smhost=r3---sn-aigl6nl7.gvt1.com | US | binary | 5.66 Kb | whitelisted |
884 | svchost.exe | GET | 302 | 142.250.186.142:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/mhzu72vkczhlmfqomqnf35nvau_2765/jflookgnkcckhobaglndicnbbgbonegd_2765_all_jdd5fasdwpeesmnmtivieegk2a.crx3 | US | html | 561 b | whitelisted |
884 | svchost.exe | GET | 206 | 74.125.105.8:80 | http://r3---sn-aigl6ns6.gvt1.com/edgedl/release2/chrome_component/mhzu72vkczhlmfqomqnf35nvau_2765/jflookgnkcckhobaglndicnbbgbonegd_2765_all_jdd5fasdwpeesmnmtivieegk2a.crx3?cms_redirect=yes&mh=Vt&mip=85.203.46.147&mm=28&mn=sn-aigl6ns6&ms=nvh&mt=1643038820&mv=m&mvi=3&pl=25&shardbypass=yes&smhost=r3---sn-aigl6nl7.gvt1.com | US | binary | 510 b | whitelisted |
884 | svchost.exe | GET | 206 | 74.125.105.8:80 | http://r3---sn-aigl6ns6.gvt1.com/edgedl/release2/chrome_component/mhzu72vkczhlmfqomqnf35nvau_2765/jflookgnkcckhobaglndicnbbgbonegd_2765_all_jdd5fasdwpeesmnmtivieegk2a.crx3?cms_redirect=yes&mh=Vt&mip=85.203.46.147&mm=28&mn=sn-aigl6ns6&ms=nvh&mt=1643038820&mv=m&mvi=3&pl=25&shardbypass=yes&smhost=r3---sn-aigl6nl7.gvt1.com | US | binary | 9.52 Kb | whitelisted |
884 | svchost.exe | GET | 302 | 142.250.186.142:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/mhzu72vkczhlmfqomqnf35nvau_2765/jflookgnkcckhobaglndicnbbgbonegd_2765_all_jdd5fasdwpeesmnmtivieegk2a.crx3 | US | html | 561 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3428 | chrome.exe | 80.195.114.22:443 | track.dhlparcel.co.uk | Virgin Media Limited | GB | suspicious |
3428 | chrome.exe | 172.217.16.138:443 | maps.googleapis.com | Google Inc. | US | whitelisted |
2788 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3428 | chrome.exe | 142.250.185.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
3428 | chrome.exe | 142.250.186.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
3428 | chrome.exe | 142.250.185.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
— | — | 142.250.185.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
— | — | 142.250.185.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
— | — | 142.250.186.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
3428 | chrome.exe | 142.250.184.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
eur03.safelinks.protection.outlook.com |
| whitelisted |
accounts.google.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
url5032.dhlparcel.co.uk |
| suspicious |
i.dhlparcel.co.uk |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |