| File name: | test.dll |
| Full analysis: | https://app.any.run/tasks/59f59403-1c5c-4e33-a456-6d33847a3b72 |
| Verdict: | Malicious activity |
| Analysis date: | May 04, 2020, 18:25:48 |
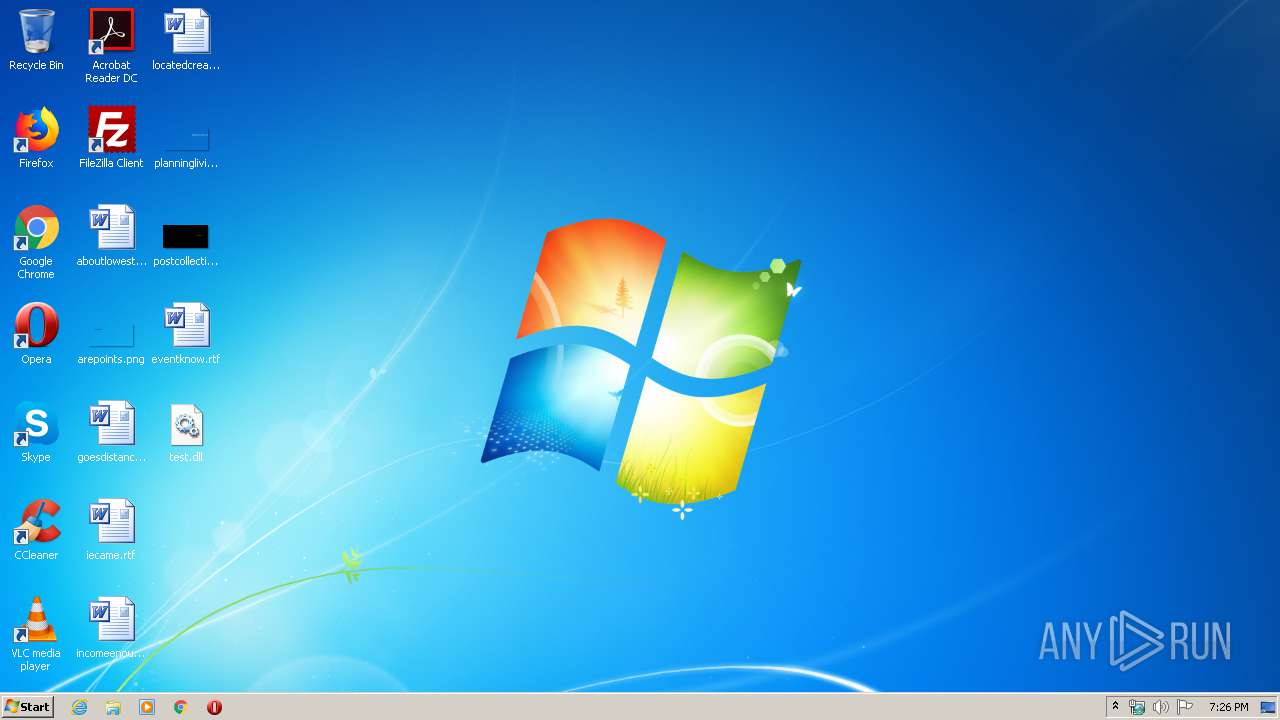
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (DLL) (GUI) Intel 80386, for MS Windows |
| MD5: | 26444BC9A2C00F8DCCE3B6814225A891 |
| SHA1: | 080328D869BB544611F65CEDC1A551FEBFFD2F6F |
| SHA256: | B8F12721930C48B2D6270F80B974E8BD536690906F5A0BAC496EEEA0E83EF750 |
| SSDEEP: | 12288:8H5gTJILzxNqQOYwjPpAskwjhx8VngEifKLKzrEqxsBbQgs14SlQ:8uJIL9NROYOPpAbyhmVnFDLwxChhxZ |
MALICIOUS
Loads dropped or rewritten executable
- explorer.exe (PID: 372)
- rundll32.exe (PID: 280)
Actions looks like stealing of personal data
- explorer.exe (PID: 372)
Runs app for hidden code execution
- explorer.exe (PID: 372)
SUSPICIOUS
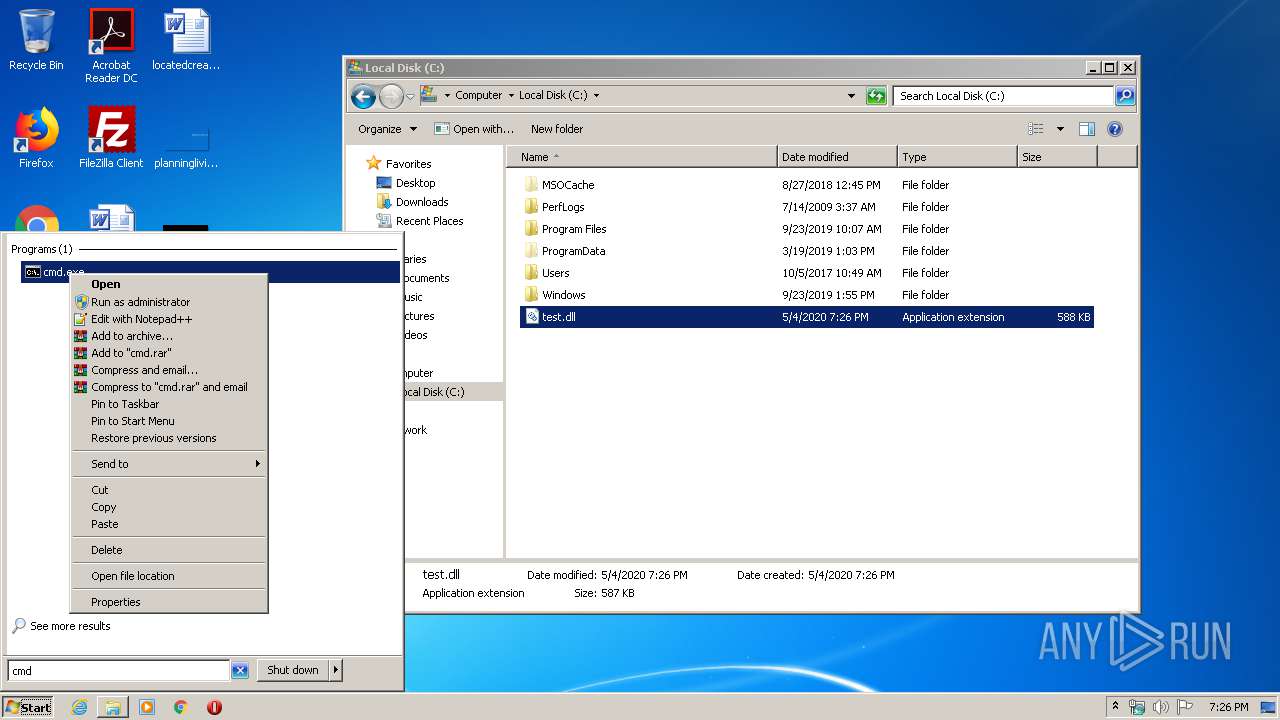
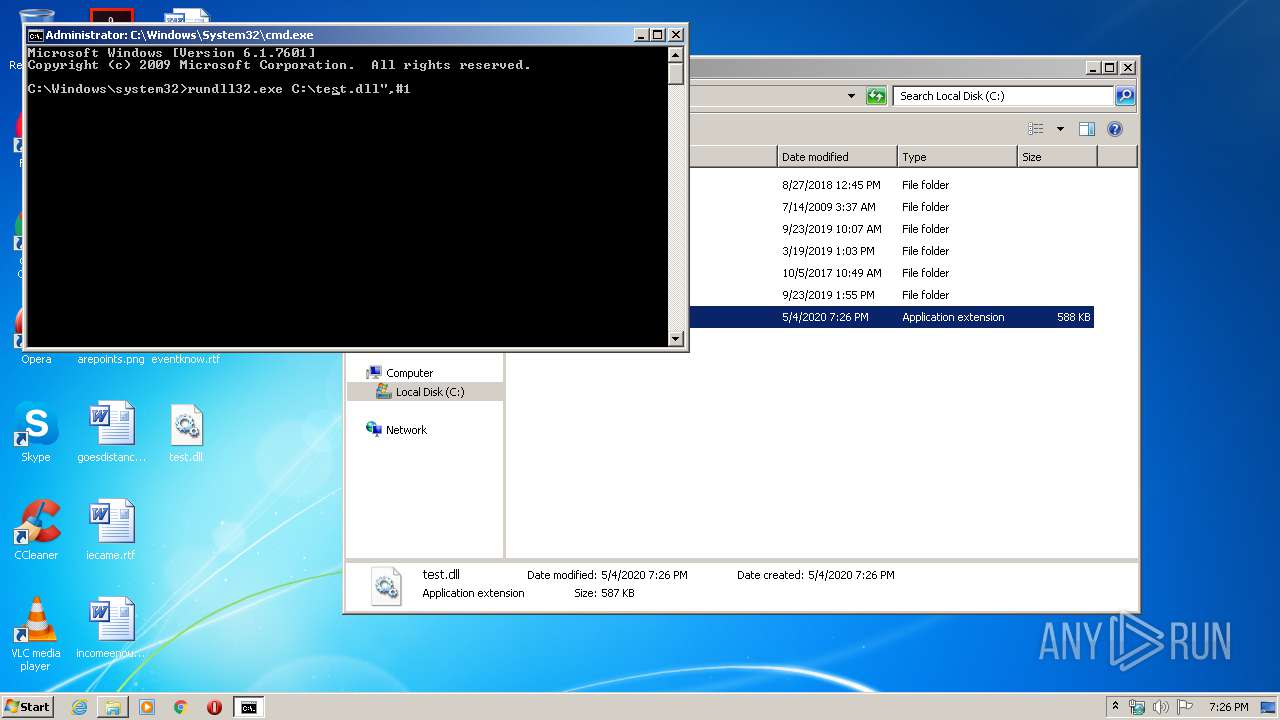
Uses RUNDLL32.EXE to load library
- explorer.exe (PID: 372)
- cmd.exe (PID: 2220)
Executed via COM
- DllHost.exe (PID: 1852)
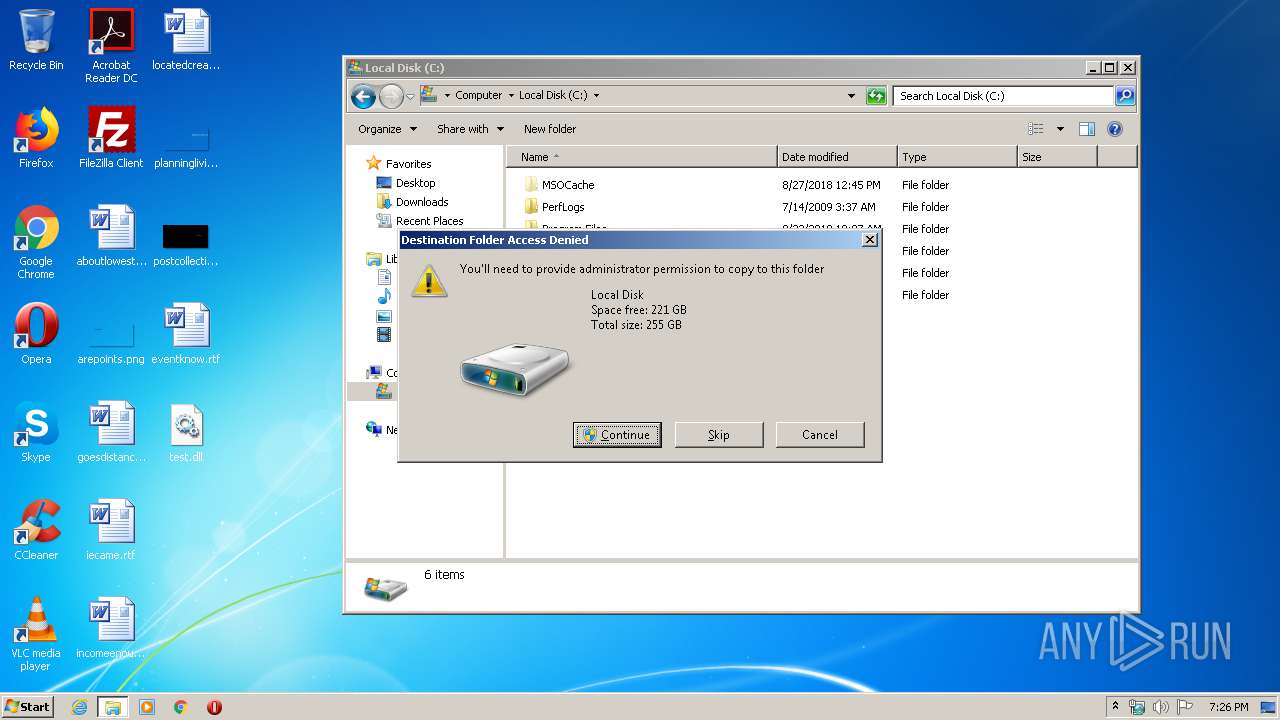
Executable content was dropped or overwritten
- DllHost.exe (PID: 1852)
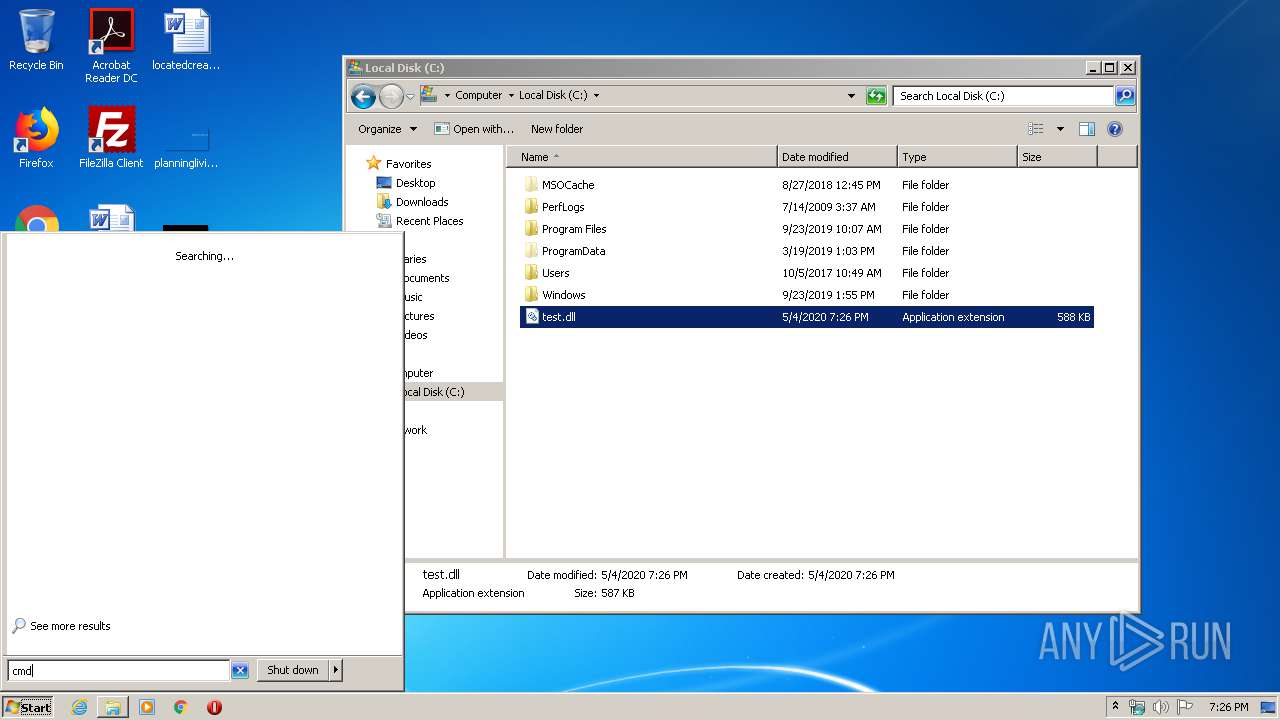
Starts CMD.EXE for commands execution
- explorer.exe (PID: 372)
INFO
Loads main object executable
- rundll32.exe (PID: 3756)
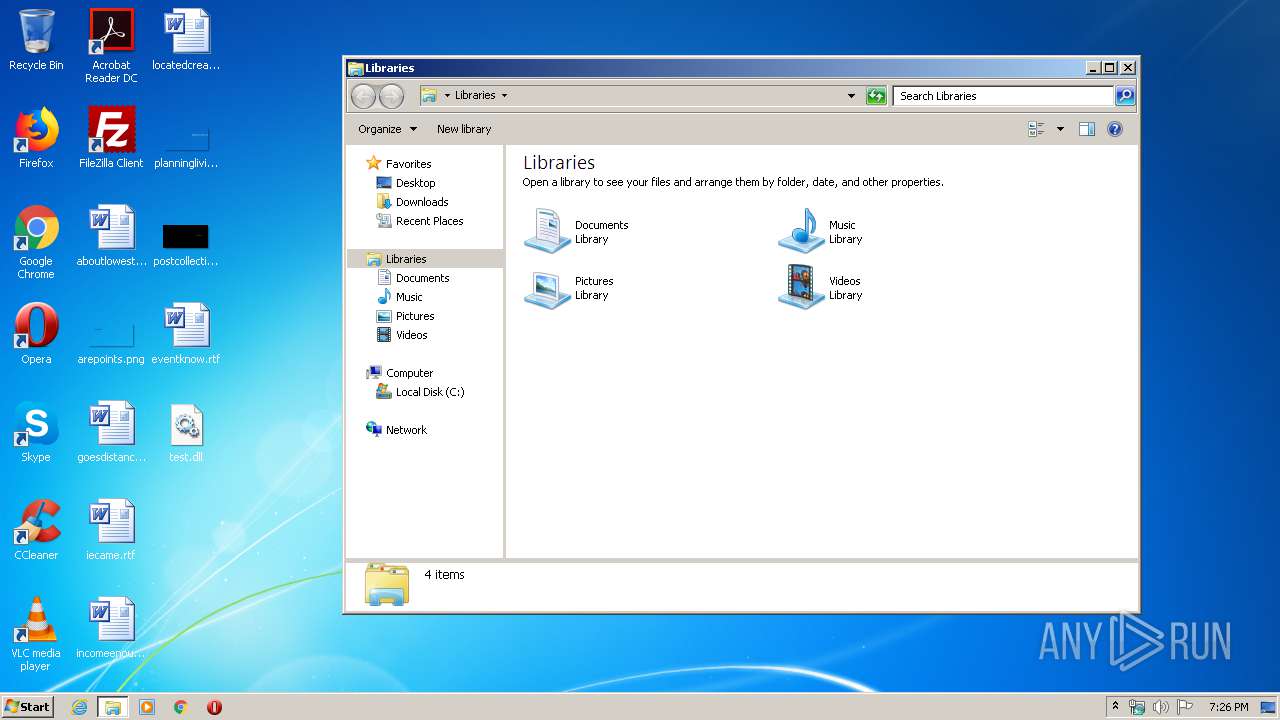
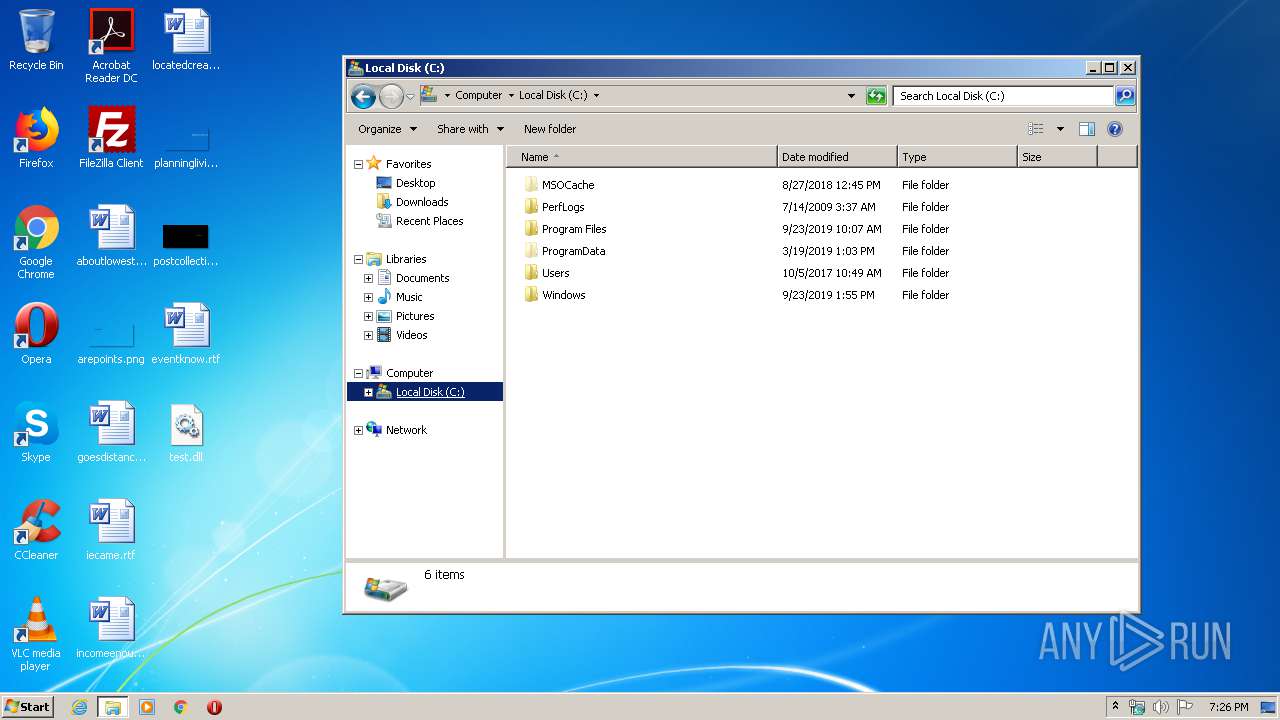
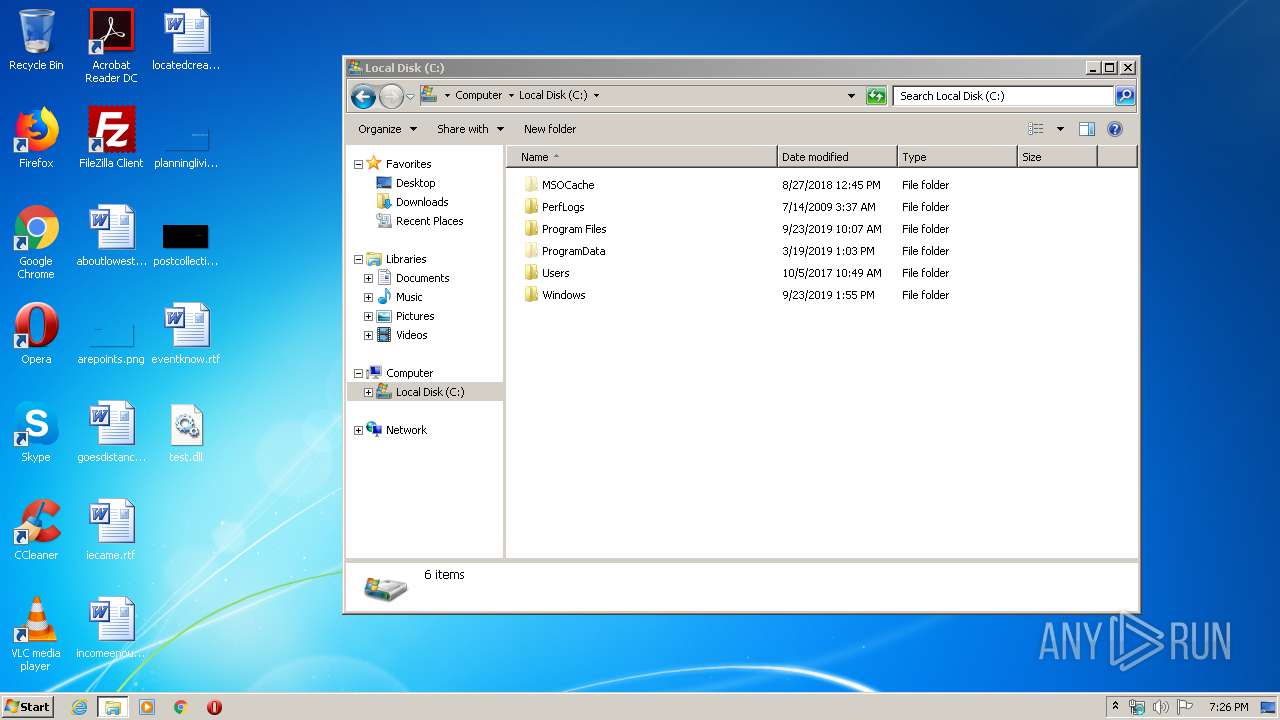
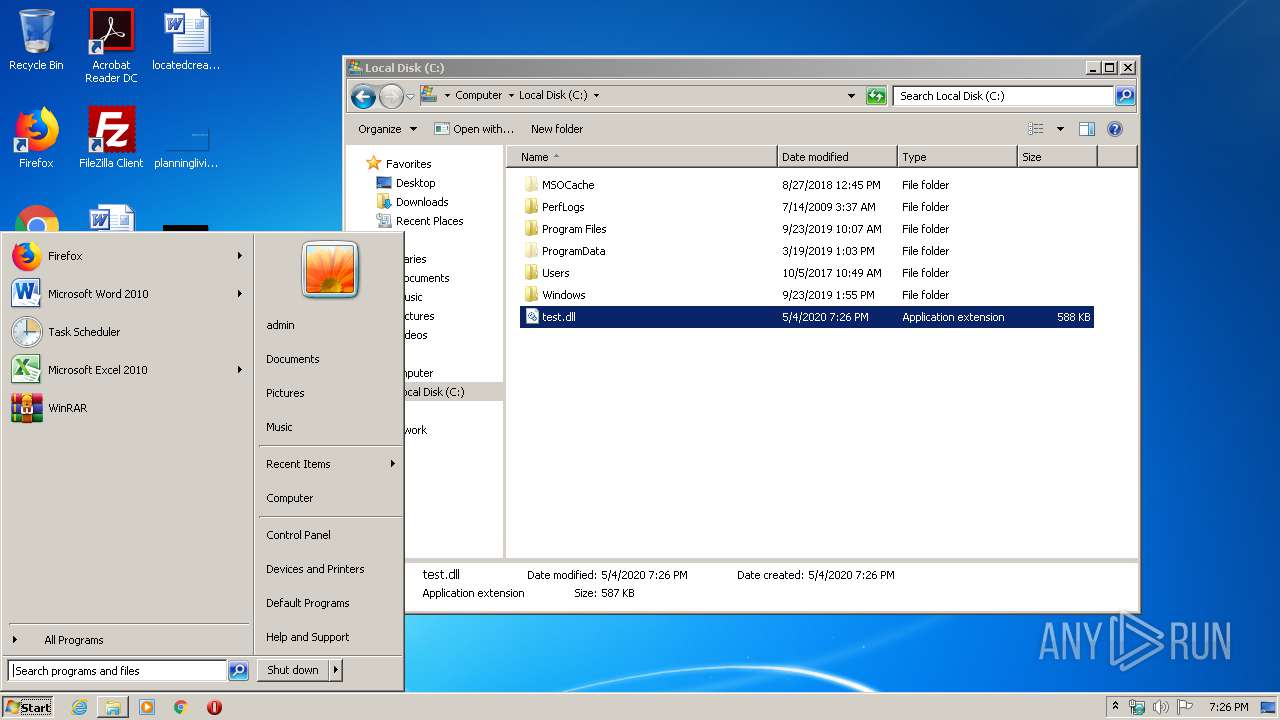
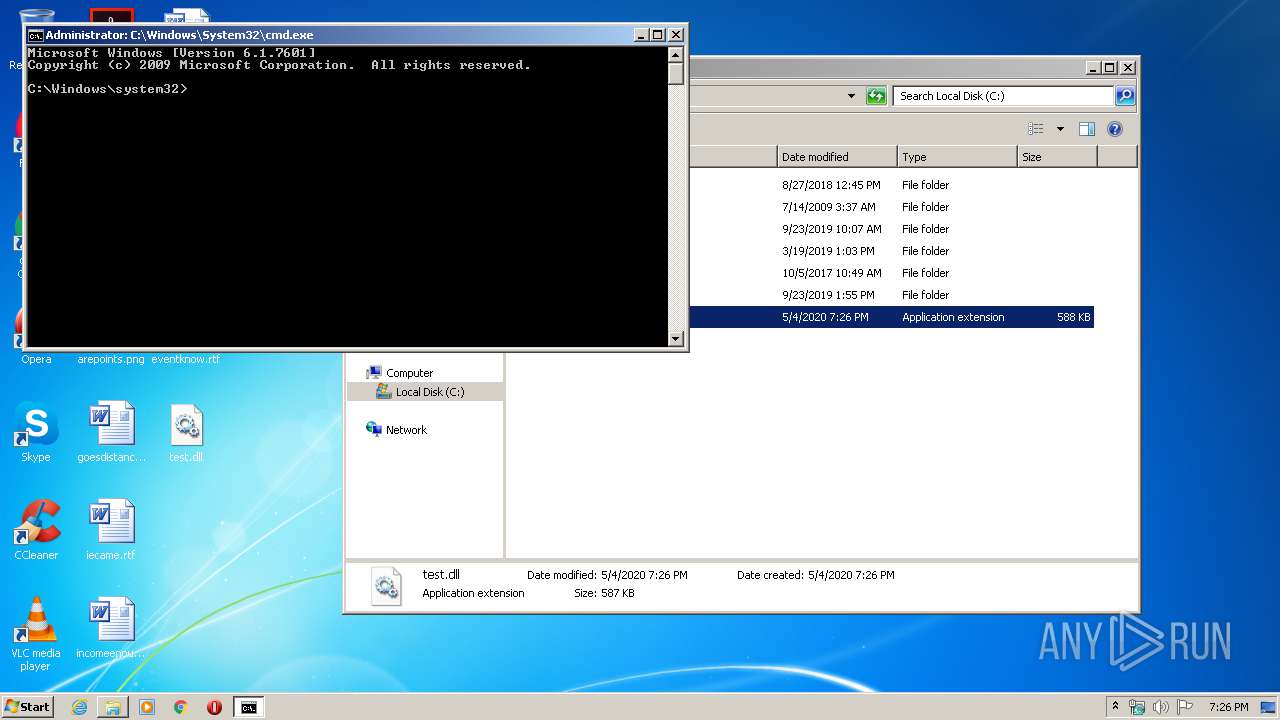
Manual execution by user
- explorer.exe (PID: 3872)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:03:20 21:28:01+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 49152 |
| InitializedDataSize: | 24064 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xcbca |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 20-Mar-2018 20:28:01 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 20-Mar-2018 20:28:01 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000BE72 | 0x0000C000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.58912 |
.rdata | 0x0000D000 | 0x000025A4 | 0x00002600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.12418 |
.data | 0x00010000 | 0x00002948 | 0x00001E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.98092 |
.fff0 | 0x00013000 | 0x00081BD0 | 0x00081C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.7521 |
.reloc | 0x00095000 | 0x00000880 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.00381 |
Imports
ADVAPI32.dll |
AVICAP32.dll |
KERNEL32.dll |
MSVCP60.dll |
MSVCRT.dll |
PSAPI.DLL |
SHELL32.dll |
USER32.dll |
WS2_32.dll |
WTSAPI32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
BAPI1 | 1 | 0x00006989 |
BAPI2 | 2 | 0x00006989 |
BAPI3 | 3 | 0x00006989 |
GDIS1 | 4 | 0x00006949 |
GDIS2 | 5 | 0x00006949 |
GDIS3 | 6 | 0x00006949 |
Show | 7 | 0x000069C4 |
Total processes
48
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 280 | rundll32.exe "C:\test.dll",#1 | C:\Windows\system32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 372 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1852 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2220 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3756 | "C:\Windows\System32\rundll32.exe" "C:\Users\admin\Desktop\test.dll", BAPI1 | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3872 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 337
Read events
1 114
Write events
223
Delete events
0
Modification events
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | {S38OS404-1Q43-42S2-9305-67QR0O28SP23}\rkcybere.rkr |
Value: 000000000B00000018000000868F0F00000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF6042697C4122D60100000000 | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000004100000050000000F6CB25000B00000018000000868F0F007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E00650078006500000010D4A005399C747620B2370600030000600000000500000020B5370620B2370634D4A005DE9C747620B237060000000005030000080000000D0300003CD4A005AF02000018B2370664D4A0054319D276C7B43706A0AC10035E00000018B23706E098DB07AF020000B8F9D17610BFFC0210BFFC0274D4A0056419D276E098DB07A0AC10030CD9A005BF43D276E098DB070000000000000000FFFFFFFF000000000000000000000000A0AC1003B8AC1003A0AC1003E2AC10030000000000000000000000000000D276D8E81A03E095100358D9A005BF43D276D8E81A030000000000000000FFFFFFFF000000000000000000000000E0951003F8951003E095100322961003B102000086BDF40318D5A00533ABC477869DA611090C00001027000003000000485602004CD5A005F8AAC4774856020086BDF4036CD5A005603F1102ECD5A00500000000A4010000B60300000A0000001A0000000800000074D5A005FDE1C375E40700006CD5A005E4070500040012001A000A00B6030A006042697C4122D6019CD5A00557C1D57688D5A005ECD5A00562C1D576E4070500010004000B00000018000000868F0F007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E00650078006500000010D4A005399C747620B2370600030000600000000500000020B5370620B2370634D4A005DE9C747620B237060000000005030000080000000D0300003CD4A005AF02000018B2370664D4A0054319D276C7B43706A0AC10035E00000018B23706E098DB07AF020000B8F9D17610BFFC0210BFFC0274D4A0056419D276E098DB07A0AC10030CD9A005BF43D276E098DB070000000000000000FFFFFFFF000000000000000000000000A0AC1003B8AC1003A0AC1003E2AC10030000000000000000000000000000D276D8E81A03E095100358D9A005BF43D276D8E81A030000000000000000FFFFFFFF000000000000000000000000E0951003F8951003E095100322961003B102000086BDF40318D5A00533ABC477869DA611090C00001027000003000000485602004CD5A005F8AAC4774856020086BDF4036CD5A005603F1102ECD5A00500000000A4010000B60300000A0000001A0000000800000074D5A005FDE1C375E40700006CD5A005E4070500040012001A000A00B6030A006042697C4122D6019CD5A00557C1D57688D5A005ECD5A00562C1D576E4070500010004000B00000018000000868F0F007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E00650078006500000010D4A005399C747620B2370600030000600000000500000020B5370620B2370634D4A005DE9C747620B237060000000005030000080000000D0300003CD4A005AF02000018B2370664D4A0054319D276C7B43706A0AC10035E00000018B23706E098DB07AF020000B8F9D17610BFFC0210BFFC0274D4A0056419D276E098DB07A0AC10030CD9A005BF43D276E098DB070000000000000000FFFFFFFF000000000000000000000000A0AC1003B8AC1003A0AC1003E2AC10030000000000000000000000000000D276D8E81A03E095100358D9A005BF43D276D8E81A030000000000000000FFFFFFFF000000000000000000000000E0951003F8951003E095100322961003B102000086BDF40318D5A00533ABC477869DA611090C00001027000003000000485602004CD5A005F8AAC4774856020086BDF4036CD5A005603F1102ECD5A00500000000A4010000B60300000A0000001A0000000800000074D5A005FDE1C375E40700006CD5A005E4070500040012001A000A00B6030A006042697C4122D6019CD5A00557C1D57688D5A005ECD5A00562C1D576E407050001000400 | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | {9R3995NO-1S9P-4S13-O827-48O24O6P7174}\GnfxOne\Jvaqbjf Rkcybere.yax |
Value: 000000000B000000000000000A000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF6042697C4122D60100000000 | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000002300000000000000220000000B000000000000000A0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C00570069006E0064006F007700730020004500780070006C006F007200650072002E006C006E006B00000034D4A005DE9C747620B237060000000005030000080000000D0300003CD4A005AF02000018B2370664D4A0054319D276C7B43706A0AC10035E00000018B23706E098DB07AF020000B8F9D17610BFFC0210BFFC0274D4A0056419D276E098DB07A0AC10030CD9A005BF43D276E098DB070000000000000000FFFFFFFF000000000000000000000000A0AC1003B8AC1003A0AC1003E2AC10030000000000000000000000000000D276D8E81A03E095100358D9A005BF43D276D8E81A030000000000000000FFFFFFFF000000000000000000000000E0951003F8951003E095100322961003B102000086BDF40318D5A00533ABC477869DA611090C00001027000003000000485602004CD5A005F8AAC4774856020086BDF4036CD5A005484A1102ECD5A00500000000A4010000B60300000A0000001A0000000800000074D5A005FDE1C375E40700006CD5A005E4070500040012001A000A00B6030A006042697C4122D6019CD5A00557C1D57688D5A005ECD5A00562C1D576E4070500010004000B000000000000000A0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C00570069006E0064006F007700730020004500780070006C006F007200650072002E006C006E006B00000034D4A005DE9C747620B237060000000005030000080000000D0300003CD4A005AF02000018B2370664D4A0054319D276C7B43706A0AC10035E00000018B23706E098DB07AF020000B8F9D17610BFFC0210BFFC0274D4A0056419D276E098DB07A0AC10030CD9A005BF43D276E098DB070000000000000000FFFFFFFF000000000000000000000000A0AC1003B8AC1003A0AC1003E2AC10030000000000000000000000000000D276D8E81A03E095100358D9A005BF43D276D8E81A030000000000000000FFFFFFFF000000000000000000000000E0951003F8951003E095100322961003B102000086BDF40318D5A00533ABC477869DA611090C00001027000003000000485602004CD5A005F8AAC4774856020086BDF4036CD5A005484A1102ECD5A00500000000A4010000B60300000A0000001A0000000800000074D5A005FDE1C375E40700006CD5A005E4070500040012001A000A00B6030A006042697C4122D6019CD5A00557C1D57688D5A005ECD5A00562C1D576E4070500010004000B000000000000000A0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C00570069006E0064006F007700730020004500780070006C006F007200650072002E006C006E006B00000034D4A005DE9C747620B237060000000005030000080000000D0300003CD4A005AF02000018B2370664D4A0054319D276C7B43706A0AC10035E00000018B23706E098DB07AF020000B8F9D17610BFFC0210BFFC0274D4A0056419D276E098DB07A0AC10030CD9A005BF43D276E098DB070000000000000000FFFFFFFF000000000000000000000000A0AC1003B8AC1003A0AC1003E2AC10030000000000000000000000000000D276D8E81A03E095100358D9A005BF43D276D8E81A030000000000000000FFFFFFFF000000000000000000000000E0951003F8951003E095100322961003B102000086BDF40318D5A00533ABC477869DA611090C00001027000003000000485602004CD5A005F8AAC4774856020086BDF4036CD5A005484A1102ECD5A00500000000A4010000B60300000A0000001A0000000800000074D5A005FDE1C375E40700006CD5A005E4070500040012001A000A00B6030A006042697C4122D6019CD5A00557C1D57688D5A005ECD5A00562C1D576E407050001000400 | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | {9R3995NO-1S9P-4S13-O827-48O24O6P7174}\GnfxOne\Jvaqbjf Rkcybere.yax |
Value: 000000000B000000000000000B000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF6042697C4122D60100000000 | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000002300000000000000230000000B000000000000000B0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C00570069006E0064006F007700730020004500780070006C006F007200650072002E006C006E006B0000006C006E006B00000034D4A005DE9C747620B237060000000005030000080000000D0300003CD4A005AF02000018B2370664D4A0054319D276C7B43706A0AC10035E00000018B23706E098DB07AF020000B8F9D17610BFFC0210BFFC0274D4A0056419D276E098DB07A0AC10030CD9A005BF43D276E098DB070000000000000000FFFFFFFF000000000000000000000000A0AC1003B8AC1003A0AC1003E2AC10030000000000000000000000000000D276D8E81A03E095100358D9A005BF43D276D8E81A030000000000000000FFFFFFFF000000000000000000000000E0951003F8951003E095100322961003B102000086BDF40318D5A00533ABC477869DA611090C00001027000003000000485602004CD5A005F8AAC4774856020086BDF4036CD5A005484A1102ECD5A00500000000A4010000ACD50000906849AF5CD5A0058291D276ACD5A00560D5A0052795D27600000000D44E110288D5A005CD94D276D44E110234D6A005484A1102E194D27600000000484A110234D6A00590D5A0050B000000000000000B0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C00570069006E0064006F007700730020004500780070006C006F007200650072002E006C006E006B0000006C006E006B00000034D4A005DE9C747620B237060000000005030000080000000D0300003CD4A005AF02000018B2370664D4A0054319D276C7B43706A0AC10035E00000018B23706E098DB07AF020000B8F9D17610BFFC0210BFFC0274D4A0056419D276E098DB07A0AC10030CD9A005BF43D276E098DB070000000000000000FFFFFFFF000000000000000000000000A0AC1003B8AC1003A0AC1003E2AC10030000000000000000000000000000D276D8E81A03E095100358D9A005BF43D276D8E81A030000000000000000FFFFFFFF000000000000000000000000E0951003F8951003E095100322961003B102000086BDF40318D5A00533ABC477869DA611090C00001027000003000000485602004CD5A005F8AAC4774856020086BDF4036CD5A005484A1102ECD5A00500000000A4010000ACD50000906849AF5CD5A0058291D276ACD5A00560D5A0052795D27600000000D44E110288D5A005CD94D276D44E110234D6A005484A1102E194D27600000000484A110234D6A00590D5A0050B000000000000000B0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C00570069006E0064006F007700730020004500780070006C006F007200650072002E006C006E006B0000006C006E006B00000034D4A005DE9C747620B237060000000005030000080000000D0300003CD4A005AF02000018B2370664D4A0054319D276C7B43706A0AC10035E00000018B23706E098DB07AF020000B8F9D17610BFFC0210BFFC0274D4A0056419D276E098DB07A0AC10030CD9A005BF43D276E098DB070000000000000000FFFFFFFF000000000000000000000000A0AC1003B8AC1003A0AC1003E2AC10030000000000000000000000000000D276D8E81A03E095100358D9A005BF43D276D8E81A030000000000000000FFFFFFFF000000000000000000000000E0951003F8951003E095100322961003B102000086BDF40318D5A00533ABC477869DA611090C00001027000003000000485602004CD5A005F8AAC4774856020086BDF4036CD5A005484A1102ECD5A00500000000A4010000ACD50000906849AF5CD5A0058291D276ACD5A00560D5A0052795D27600000000D44E110288D5A005CD94D276D44E110234D6A005484A1102E194D27600000000484A110234D6A00590D5A005 | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 02000000010000000A0000000700000009000000080000000000000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Toolbar |
| Operation: | write | Name: | Locked |
Value: 1 | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1852 | DllHost.exe | C:\test.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report