| File name: | sample_136.zip |
| Full analysis: | https://app.any.run/tasks/30fb2e7b-aad2-45a7-8a1b-1e6993c409c1 |
| Verdict: | Malicious activity |
| Analysis date: | June 12, 2019, 11:35:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | AD102E58A3C52637BF1BEAC8615F6152 |
| SHA1: | C9842851B8A465D1C0D5770F790C0466263FB117 |
| SHA256: | B8ECF6C24837A9E826BF00DC0201F133001C3DB5DB62EA03A5E9B4C8454505FD |
| SSDEEP: | 192:oy3r8t/M8UtEjJI1WhqaTF3Md66NbidrYPLrW03mhvlwf:Mt/hUteJJ/SbqrYzq0W5lwf |
MALICIOUS
Application was dropped or rewritten from another process
- sample_136.exe (PID: 3980)
Actions looks like stealing of personal data
- sample_136.exe (PID: 3980)
Writes to a start menu file
- sample_136.exe (PID: 3980)
Modifies files in Chrome extension folder
- sample_136.exe (PID: 3980)
SUSPICIOUS
Uses TASKKILL.EXE to kill process
- sample_136.exe (PID: 3980)
Writes to a desktop.ini file (may be used to cloak folders)
- sample_136.exe (PID: 3980)
INFO
Manual execution by user
- sample_136.exe (PID: 3980)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2018:05:01 18:48:23 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | sample_136/ |
Total processes
40
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1492 | taskkill /F /IM clisvc.exe | C:\Windows\system32\taskkill.exe | — | sample_136.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1520 | taskkill /F /IM pasvc.exe | C:\Windows\system32\taskkill.exe | — | sample_136.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
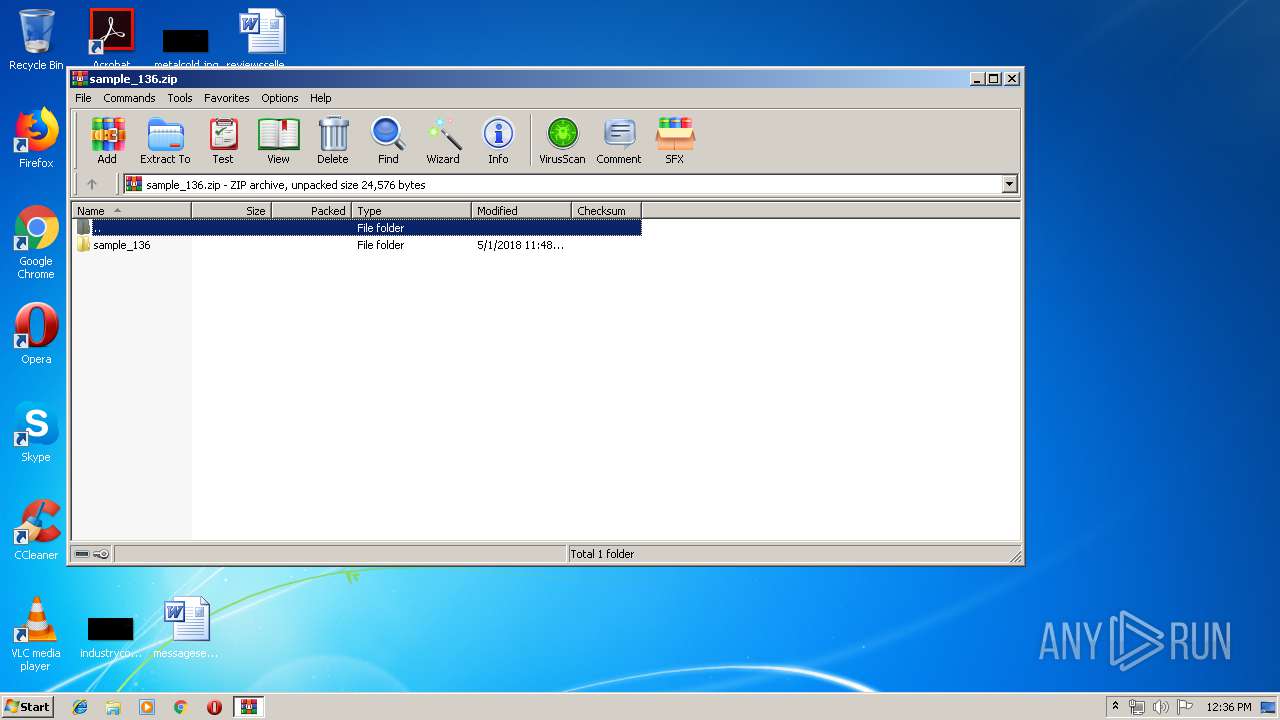
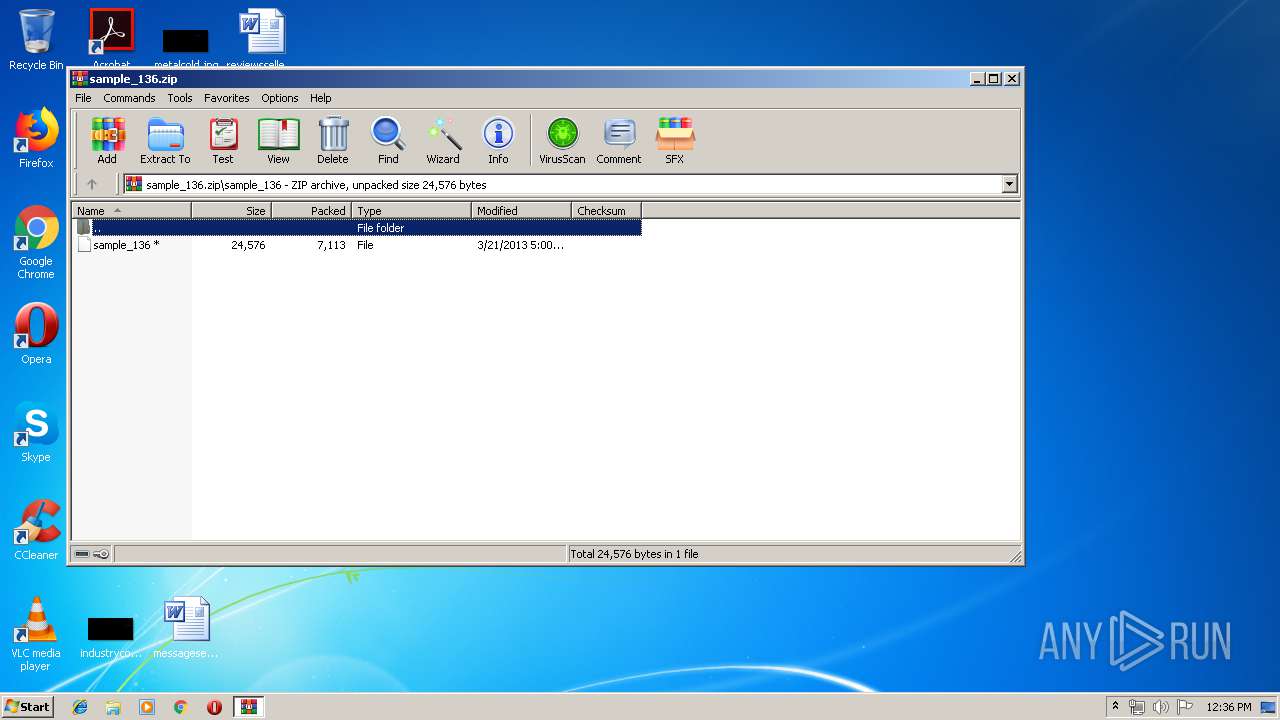
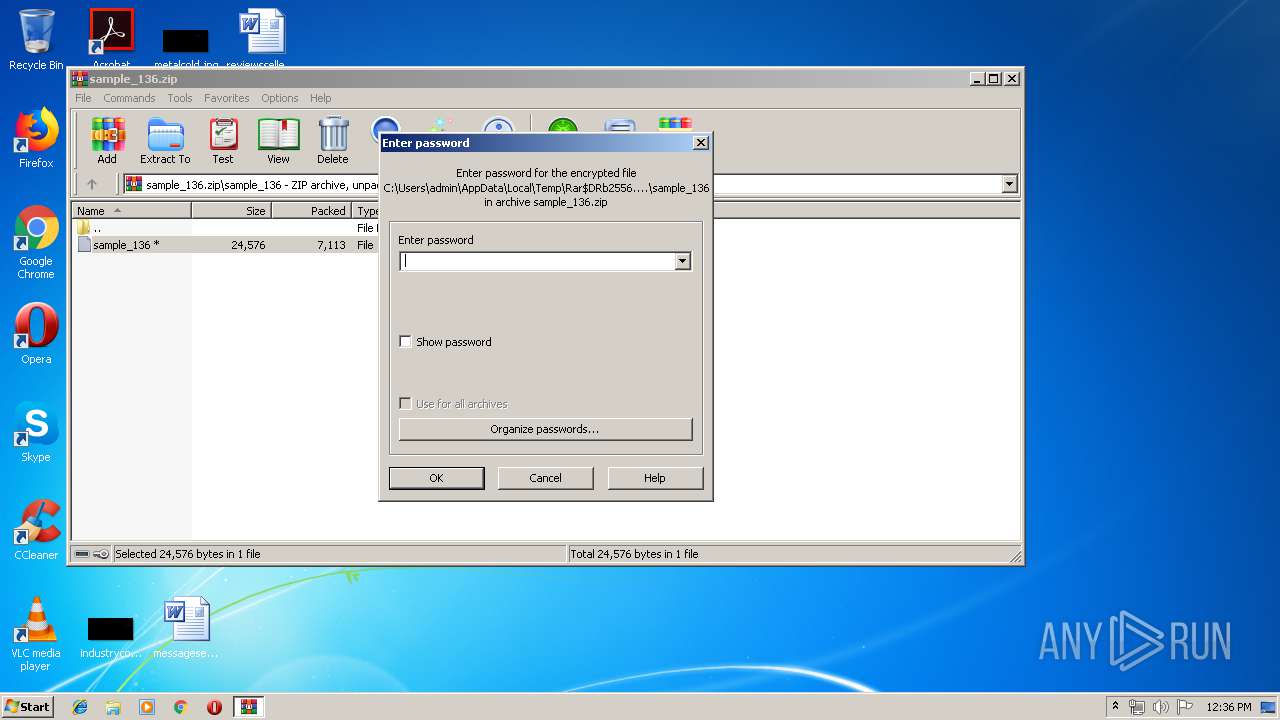
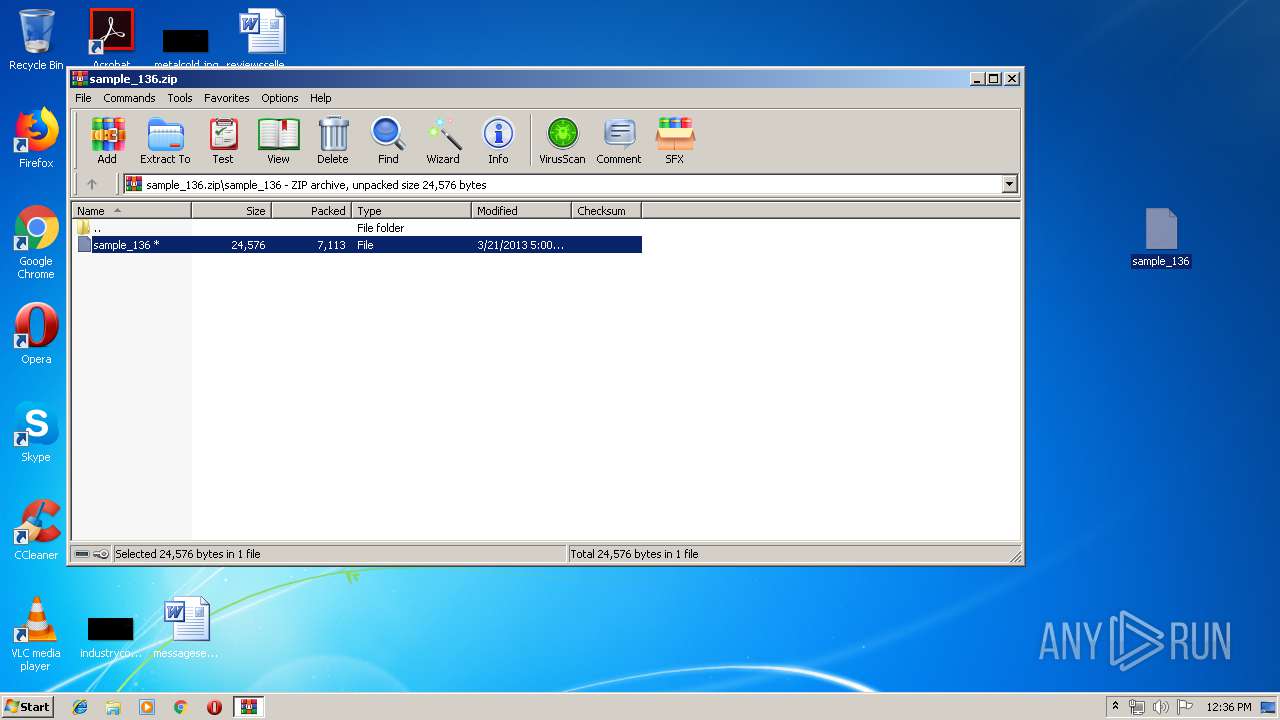
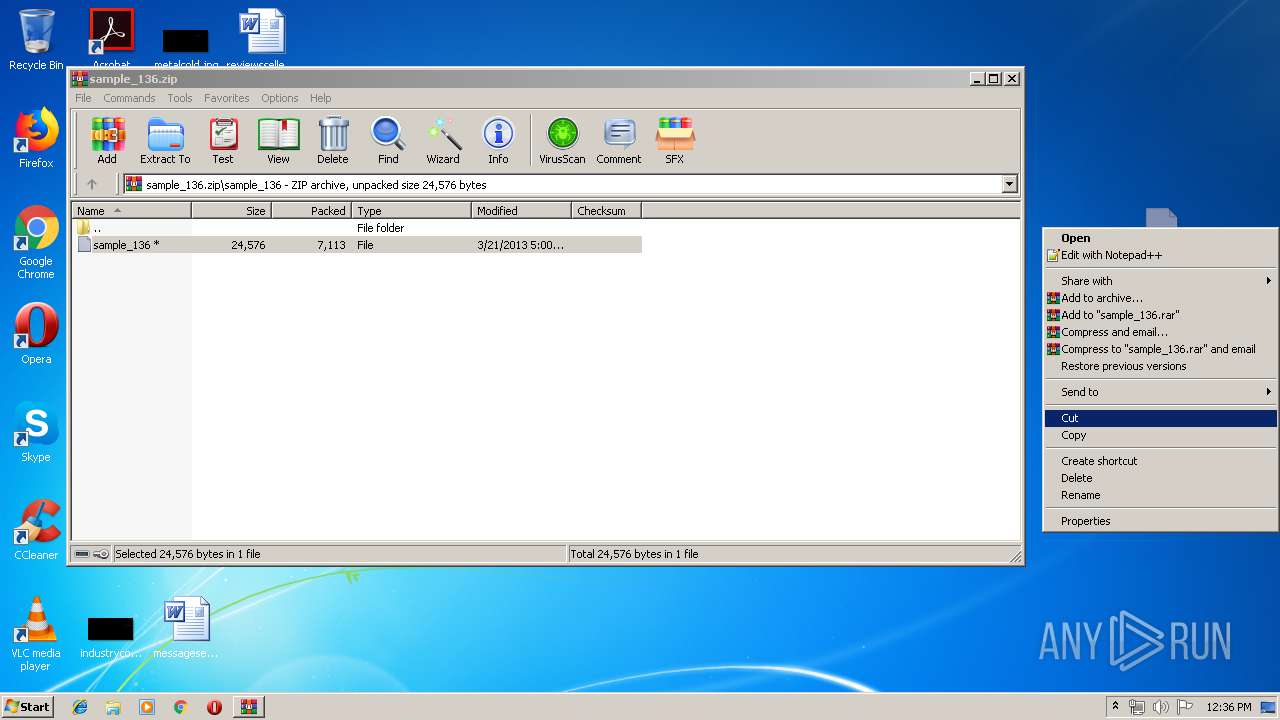
| 2556 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\sample_136.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3980 | "C:\Users\admin\Desktop\sample_136.exe" | C:\Users\admin\Desktop\sample_136.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
436
Read events
427
Write events
9
Delete events
0
Modification events
| (PID) Process: | (2556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2556) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\sample_136.zip | |||
| (PID) Process: | (2556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
0
Suspicious files
13
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2556 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2556.38707\sample_136\sample_136 | — | |
MD5:— | SHA256:— | |||
| 3980 | sample_136.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\desktop.ini | — | |
MD5:— | SHA256:— | |||
| 3980 | sample_136.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | — | |
MD5:— | SHA256:— | |||
| 3980 | sample_136.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\IconCacheRdr.dat | — | |
MD5:— | SHA256:— | |||
| 3980 | sample_136.exe | C:\Users\admin\AppData\Local\Adobe\AcroCef\DC\Acrobat\Cache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3980 | sample_136.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\IconCacheRdr65536.dat | — | |
MD5:— | SHA256:— | |||
| 3980 | sample_136.exe | C:\Users\admin\AppData\Local\Adobe\AcroCef\DC\Acrobat\Cache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3980 | sample_136.exe | C:\Users\admin\AppData\Local\Adobe\AcroCef\DC\Acrobat\Cache\data_2 | — | |
MD5:— | SHA256:— | |||
| 3980 | sample_136.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\SharedDataEvents | — | |
MD5:— | SHA256:— | |||
| 3980 | sample_136.exe | C:\Users\admin\AppData\LocalLow\Adobe\Acrobat\DC\ReaderMessages | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report