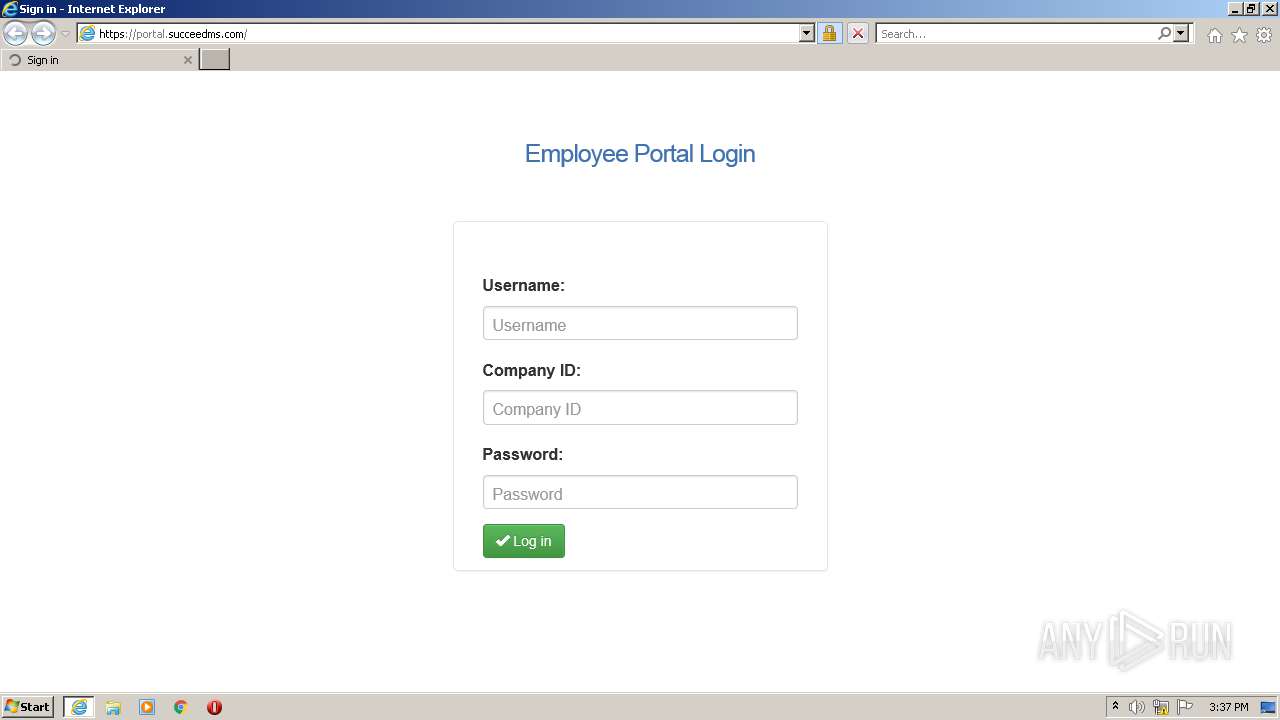
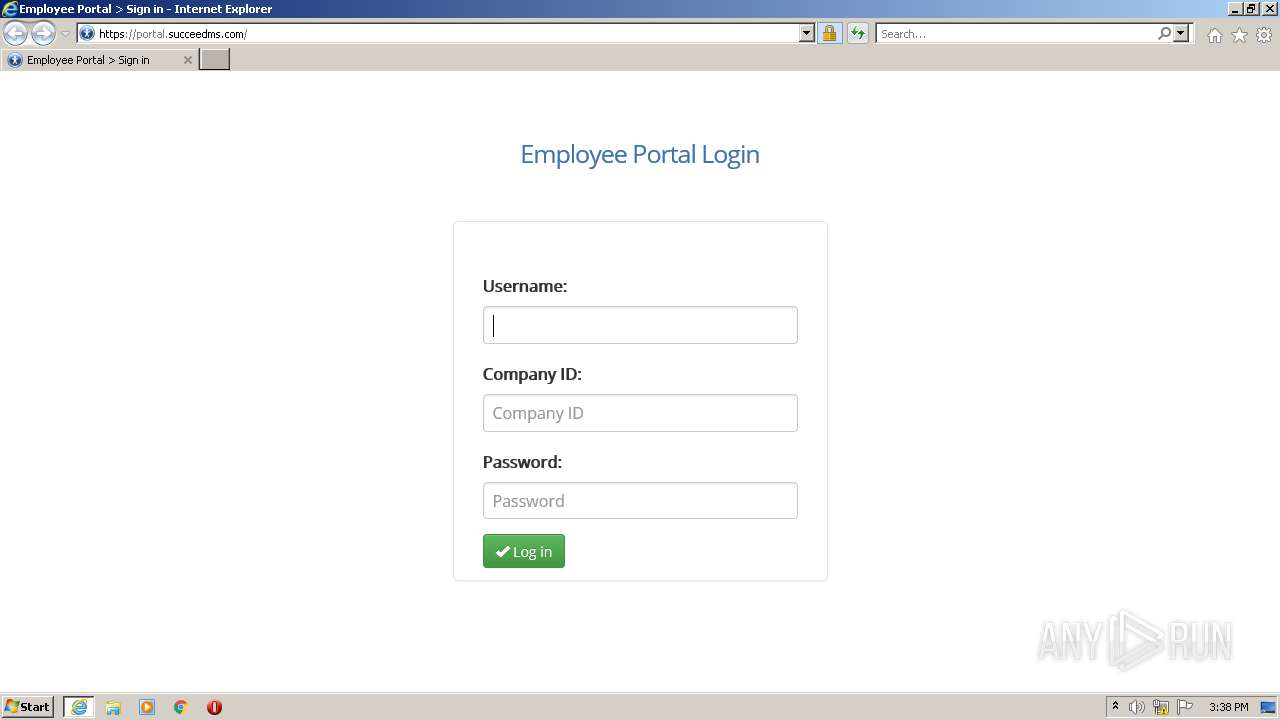
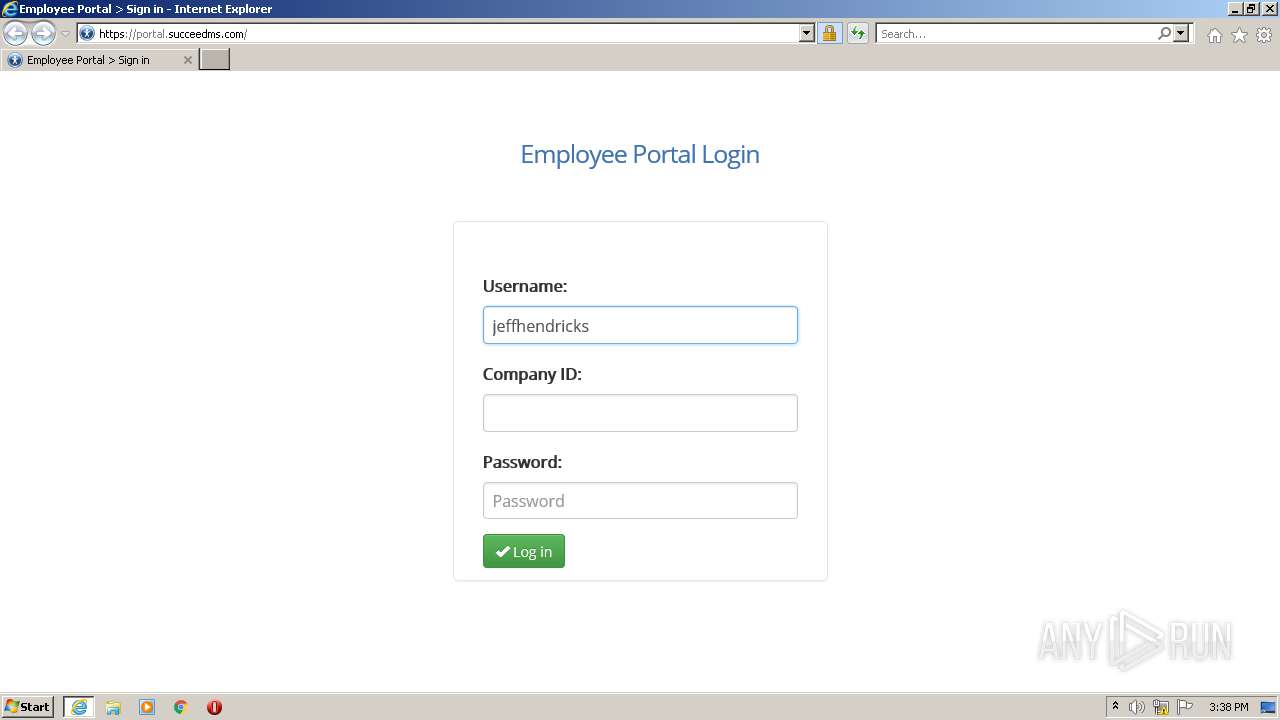
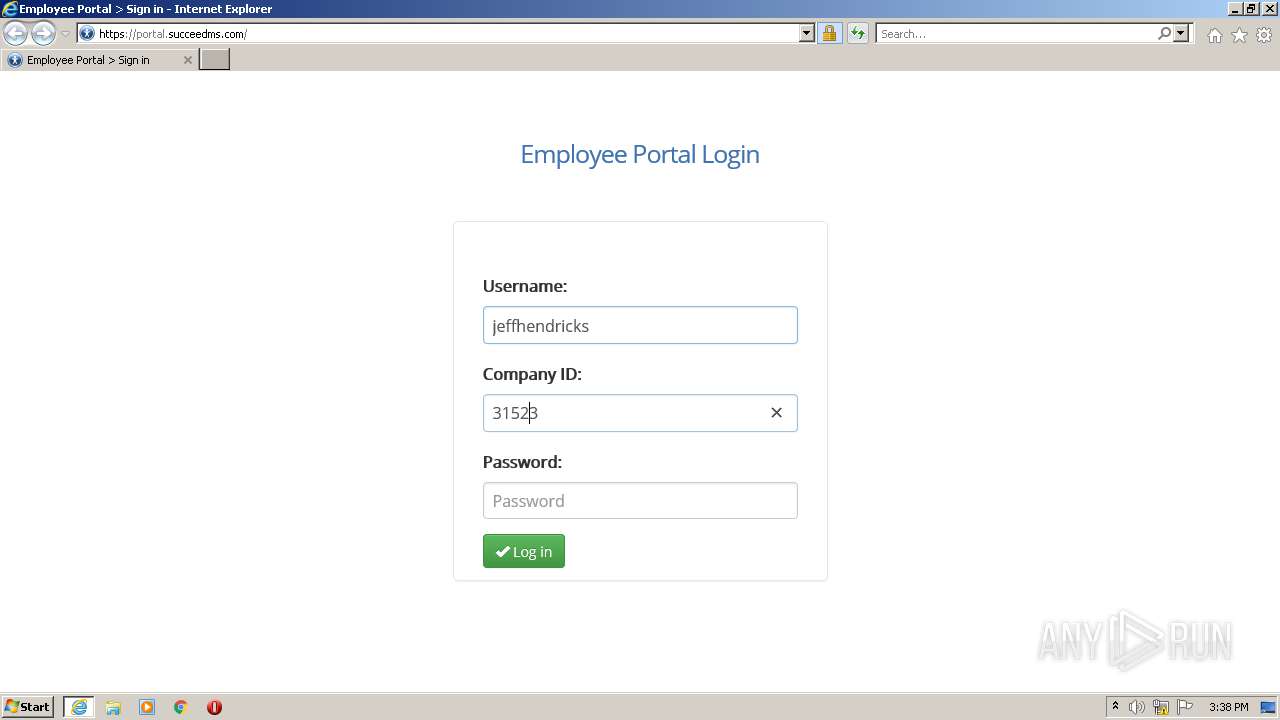
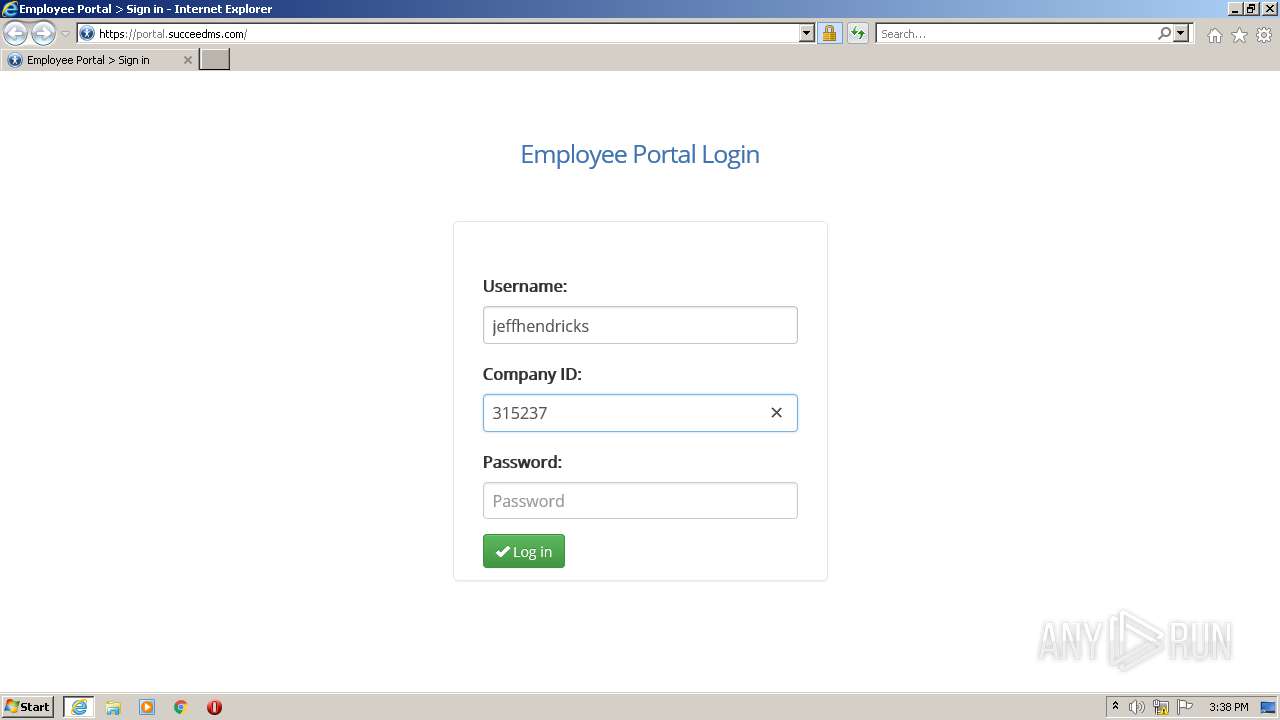
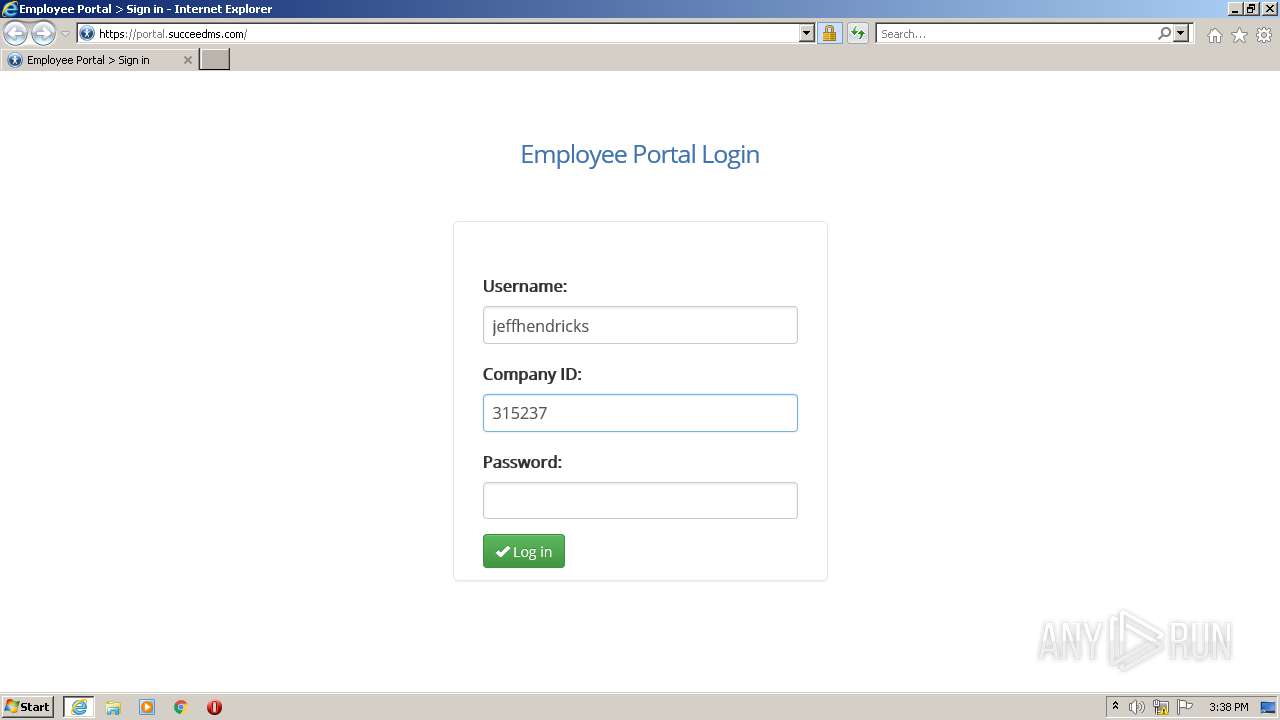
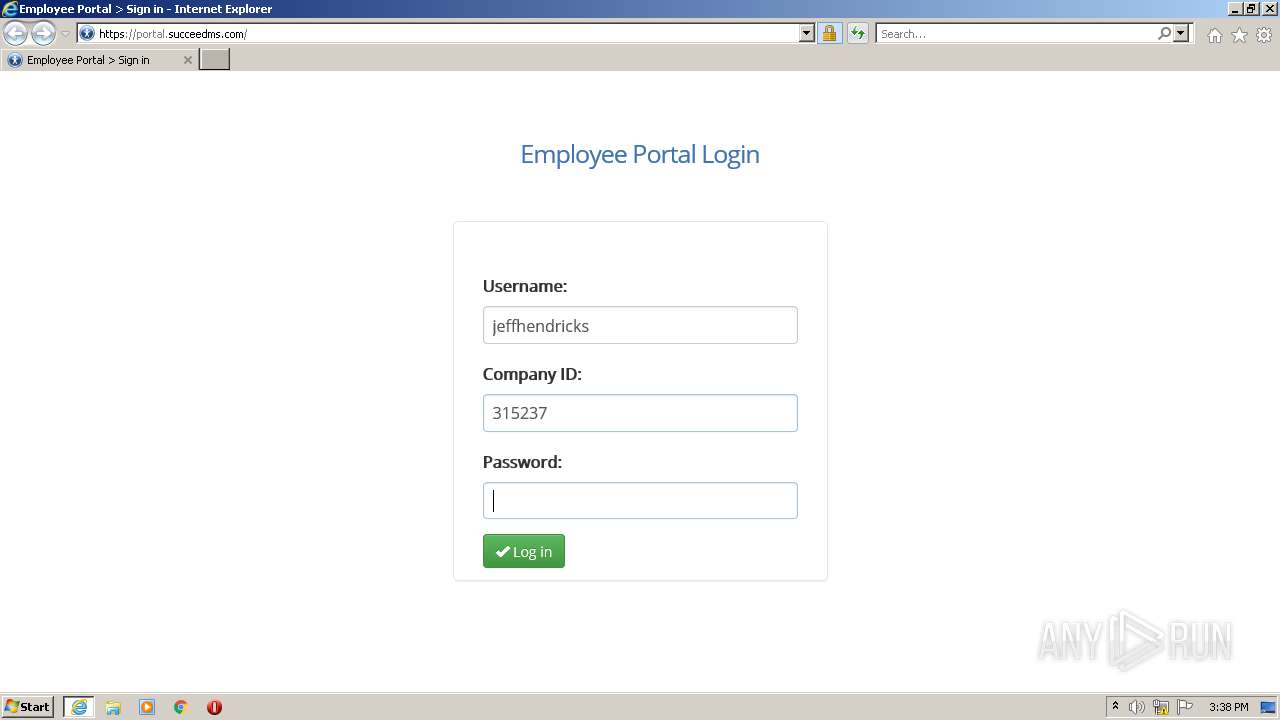
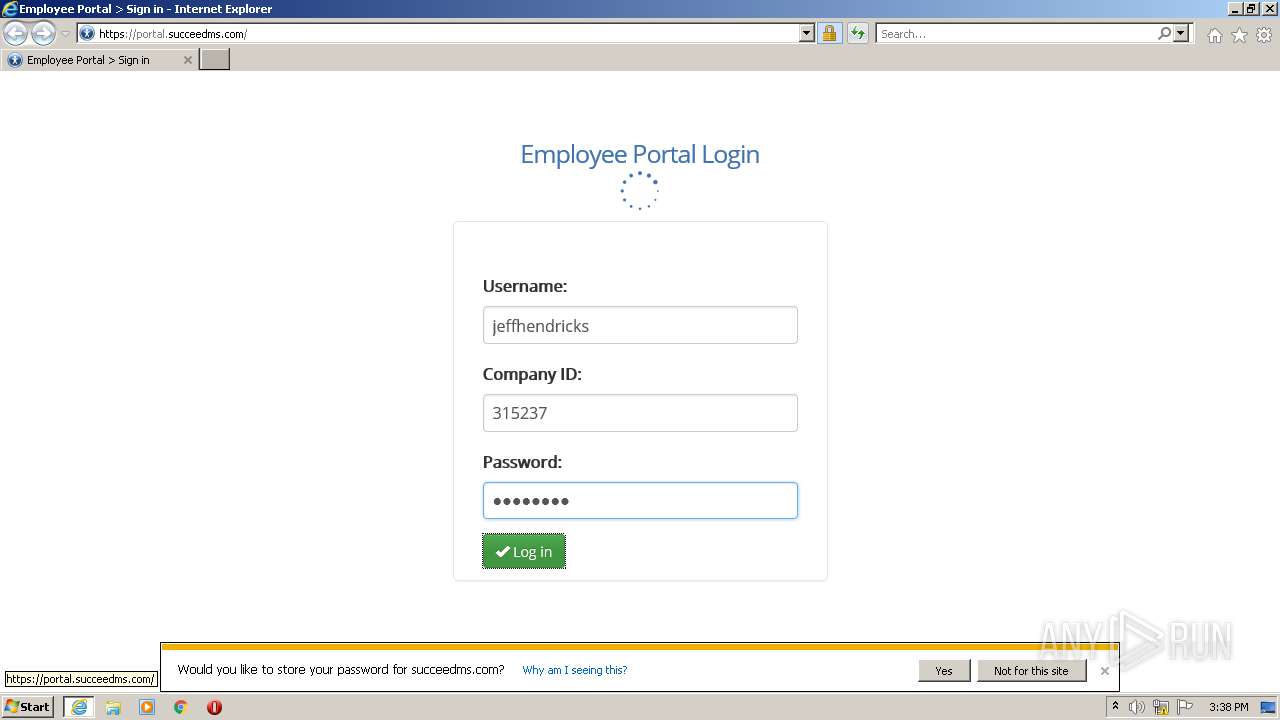
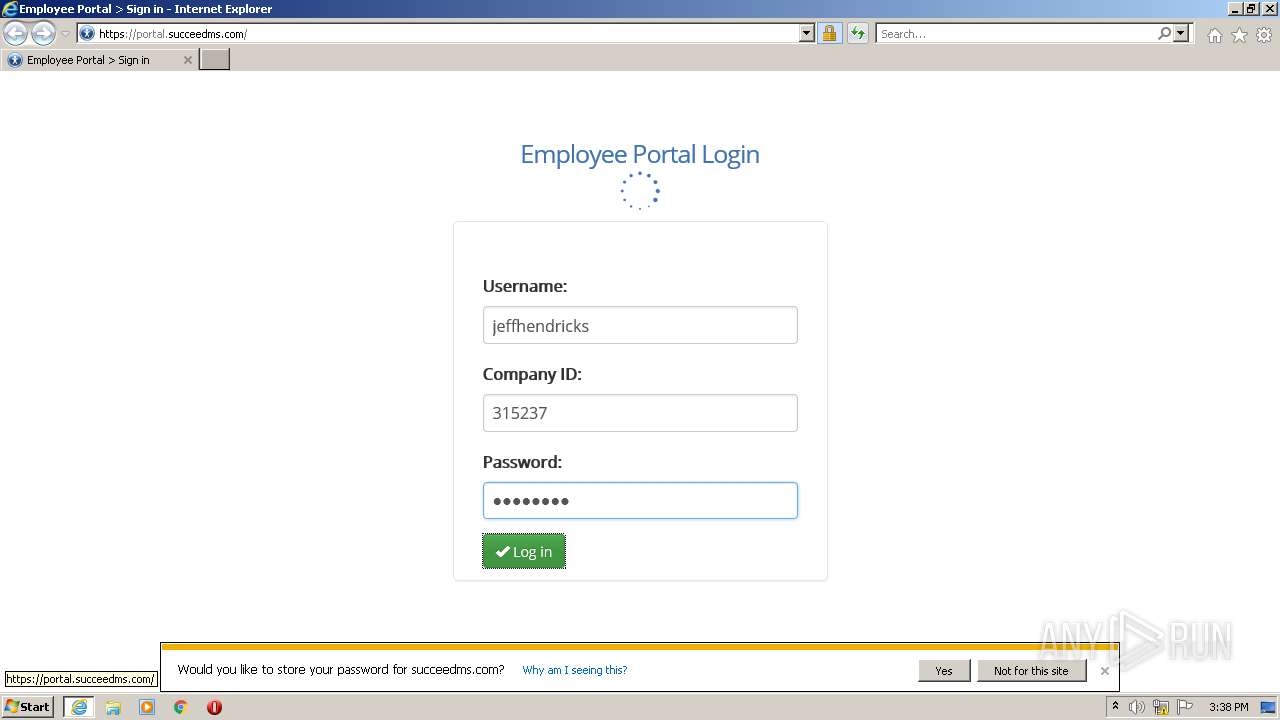
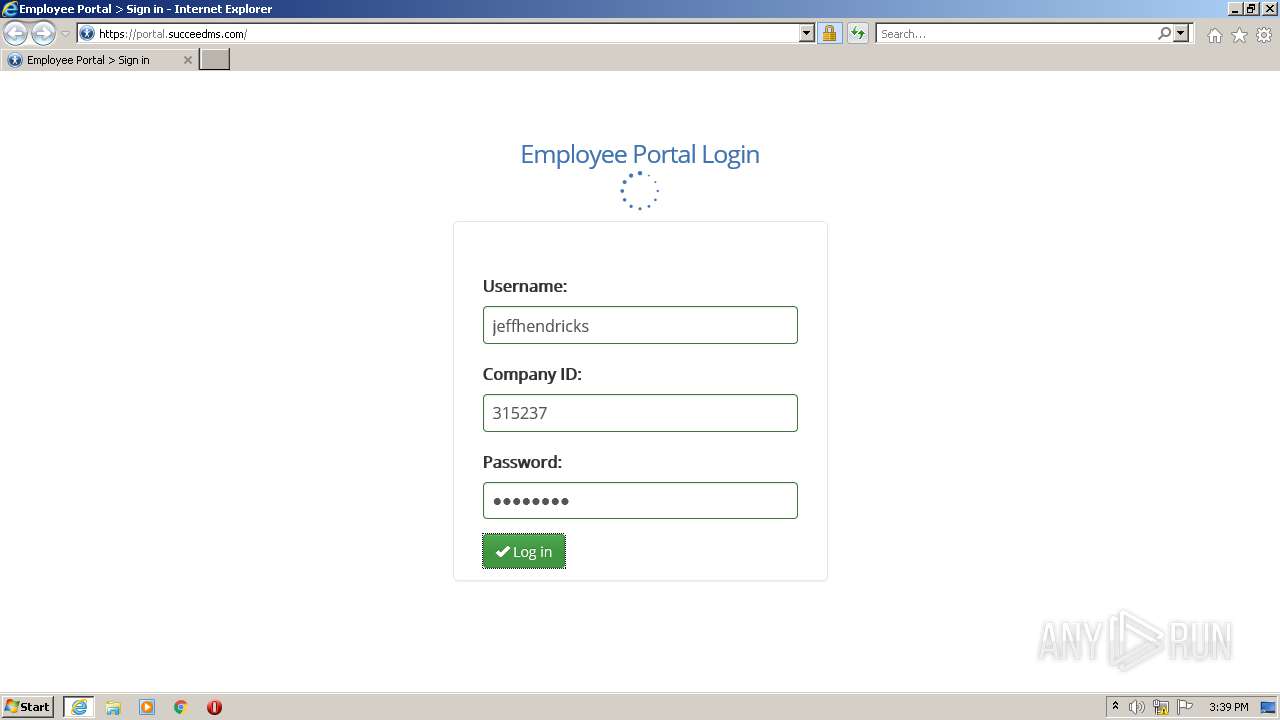
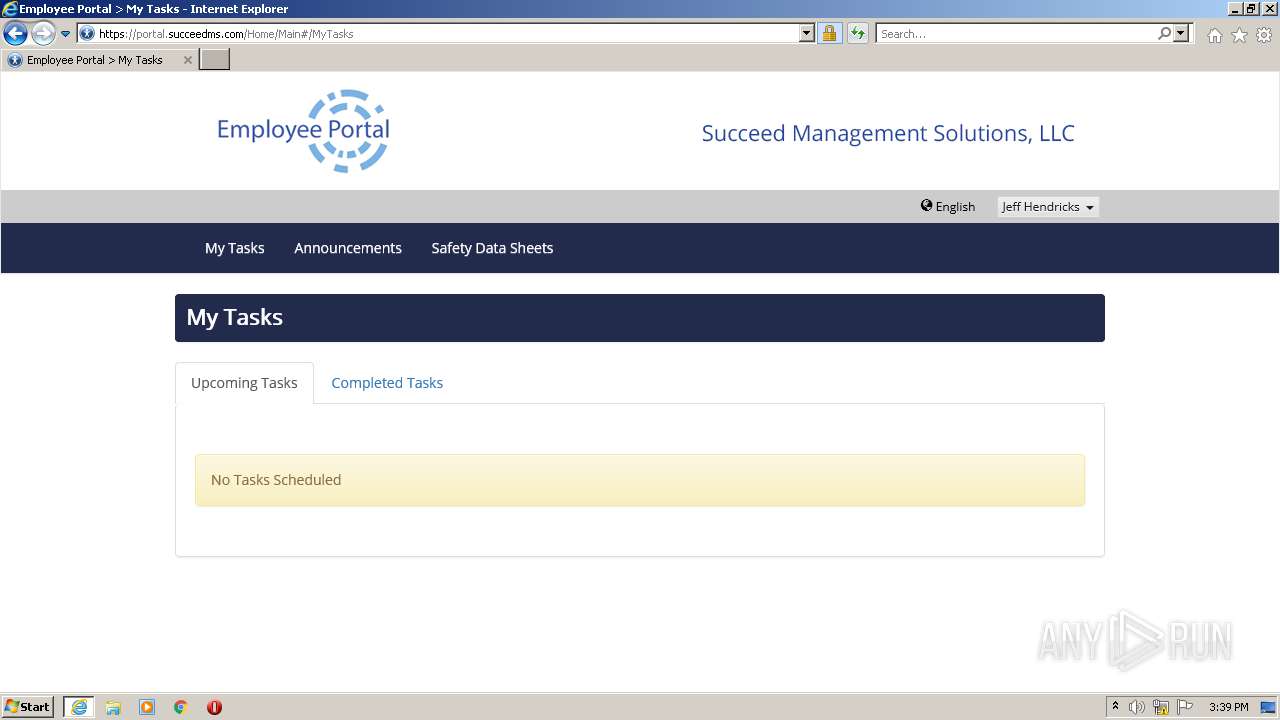
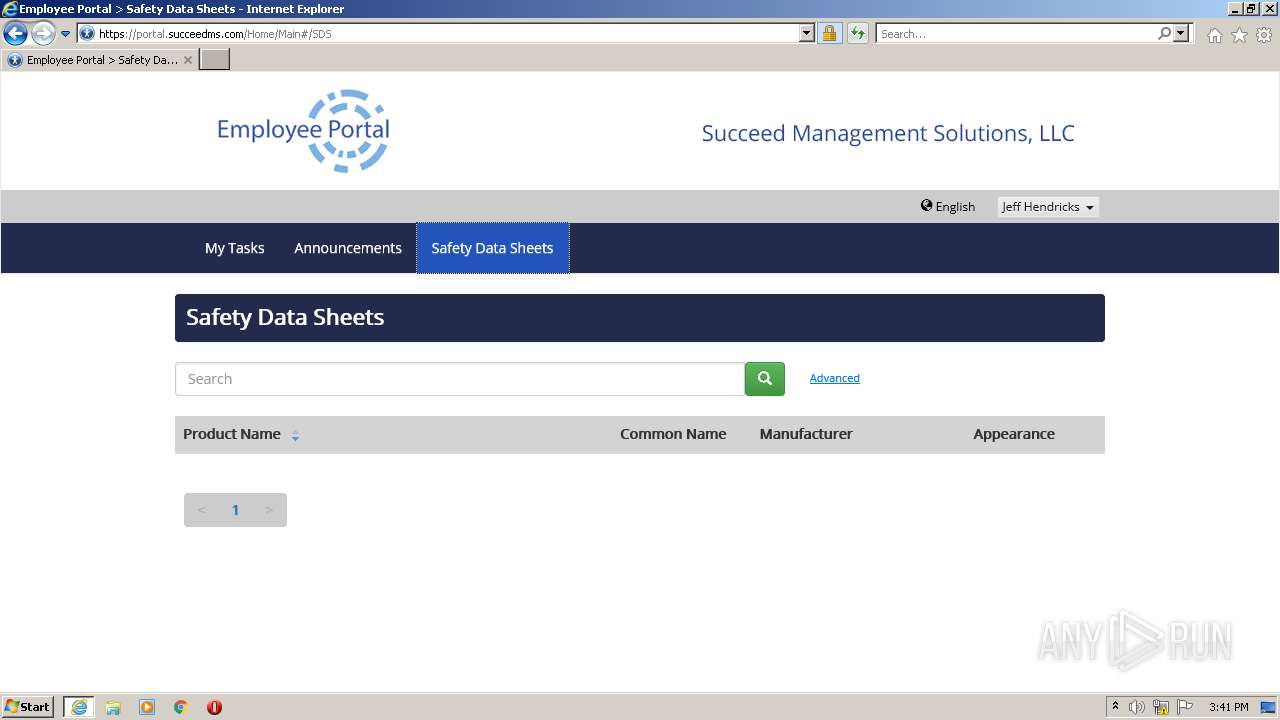
| URL: | https://portal.succeedms.com/ |
| Full analysis: | https://app.any.run/tasks/c2d5f517-3f4e-4c23-9a61-31cb2b446120 |
| Verdict: | Malicious activity |
| Analysis date: | September 09, 2021, 14:37:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F8B659A5C4C80AA518DB026E30CFB383 |
| SHA1: | 6D76B4B06E7F305DBEBB1597BBCE8C3F0B9D8E08 |
| SHA256: | B8E6B716F294C2D5ABAF406CC37D41DFCDAA92BA90EB12CB75957E0375C5D192 |
| SSDEEP: | 3:N8OaLX3cKIKn:2OaLcKIK |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 1788)
INFO
Reads the computer name
- iexplore.exe (PID: 2312)
- iexplore.exe (PID: 1788)
Checks supported languages
- iexplore.exe (PID: 1788)
- iexplore.exe (PID: 2312)
Creates files in the user directory
- iexplore.exe (PID: 1788)
- iexplore.exe (PID: 2312)
Application launched itself
- iexplore.exe (PID: 2312)
Checks Windows Trust Settings
- iexplore.exe (PID: 1788)
- iexplore.exe (PID: 2312)
Changes settings of System certificates
- iexplore.exe (PID: 2312)
Reads settings of System Certificates
- iexplore.exe (PID: 1788)
- iexplore.exe (PID: 2312)
Reads internet explorer settings
- iexplore.exe (PID: 1788)
Changes internet zones settings
- iexplore.exe (PID: 2312)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2312)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
38
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1788 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2312 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2312 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://portal.succeedms.com/" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
16 244
Read events
16 048
Write events
190
Delete events
6
Modification events
| (PID) Process: | (2312) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2312) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 966205728 | |||
| (PID) Process: | (2312) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30909832 | |||
| (PID) Process: | (2312) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2312) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30909832 | |||
| (PID) Process: | (2312) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2312) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2312) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2312) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2312) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
24
Text files
78
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1788 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:49C3876AA451AAF9D9934EA88A223400 | SHA256:38F1A897716A3A8087E5281DAD160C276CF44A1914920412322233EAB0EC3229 | |||
| 2312 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\82CB34DD3343FE727DF8890D352E0D8F | binary | |
MD5:517B08CD094B28CA2E4D641FAA299406 | SHA256:586E3839A91F622276F4B9EC62725BE5FC940BD153A4F95C0FA18BB2602AD904 | |||
| 2312 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\82CB34DD3343FE727DF8890D352E0D8F | der | |
MD5:D940C14E391C59AC47AEEA71066E99A7 | SHA256:D89ED4CE9037D19506D36317A3BF1103563816FAB55233B9056F0BC8C2AAEA85 | |||
| 1788 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\572BF21E454637C9F000BE1AF9B1E1A9 | binary | |
MD5:BE26AF54736F40F9693EFA35A74B6D3C | SHA256:BF677115CC99D49787B6DC32FE4EE1BC5CACB9EE0C700AE4B0D8D9D739BCEF9C | |||
| 1788 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\029936AD7ED2B71DC64888606F28E089 | binary | |
MD5:0E4849E212BB63D8AE2B7453643A98B8 | SHA256:CB24F0D7F6264C31660856A74A29936948E1FD47E634761E970D1BD51C0341B8 | |||
| 1788 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\3538626A1FCCCA43C7E18F220BDD9B02 | binary | |
MD5:6D004084C43972C0AD93B7F1AEC59F00 | SHA256:7F9F7E2FB897AA775AAB6BA39F9FF07F1246EEC5C0AD95BBBFFAE6FBA8F93127 | |||
| 1788 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\572BF21E454637C9F000BE1AF9B1E1A9 | der | |
MD5:748981814E37F858D2E8C17A555A99CC | SHA256:3BB1E994F4AC78F1BD30EEFD834695EF1B80D8D0BB56156DCE4B95DA34AF3AF3 | |||
| 1788 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | binary | |
MD5:18AEC40E3D262AC389C15B2D29F9D29B | SHA256:2CB5406D96A2259AEBCEE24915B1A04B26889C07675879ED39108D4EE30304DF | |||
| 1788 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | der | |
MD5:DD8BB22FC8495C946C4D1FF088EA977D | SHA256:1669C755ECB1A8708FD0489F15B36886462226BB0BB0E38ED29370447E5EB6F0 | |||
| 1788 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\3538626A1FCCCA43C7E18F220BDD9B02 | der | |
MD5:E9C2F6CD530C8C3015458128BAE3A05D | SHA256:CD50D784F2622CF38B2D092D084FA74771C4F766D47128625361AF2310AD520B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
97
DNS requests
38
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2312 | iexplore.exe | GET | 200 | 69.16.175.42:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?cca6da343724d2fe | US | compressed | 4.70 Kb | whitelisted |
1788 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
1788 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://crl.usertrust.com/USERTrustRSACertificationAuthority.crl | US | der | 978 b | whitelisted |
2312 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 7.68 Kb | whitelisted |
1788 | iexplore.exe | GET | 200 | 69.16.175.42:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?1c2162e379144e6a | US | compressed | 4.70 Kb | whitelisted |
1788 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEA6Vm6qUV0DKrY1ea1WOpUM%3D | US | der | 471 b | whitelisted |
1788 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://crl.comodoca.com/AAACertificateServices.crl | US | der | 506 b | whitelisted |
1788 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECECoiPocQg4ugJ6qNVMihUbI%3D | US | der | 471 b | whitelisted |
1788 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
1788 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1788 | iexplore.exe | 205.209.56.185:443 | portal.succeedms.com | Latisys-Denver, LLC | US | unknown |
1788 | iexplore.exe | 69.16.175.42:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | malicious |
1788 | iexplore.exe | 151.139.128.14:80 | ocsp.comodoca.com | Highwinds Network Group, Inc. | US | suspicious |
2312 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2312 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2312 | iexplore.exe | 69.16.175.42:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | malicious |
1788 | iexplore.exe | 142.250.186.138:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1788 | iexplore.exe | 69.16.175.10:443 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | malicious |
1788 | iexplore.exe | 104.16.18.94:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
portal.succeedms.com |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.comodoca.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
crl.usertrust.com |
| whitelisted |