| File name: | Discord Raider.exe |
| Full analysis: | https://app.any.run/tasks/b5a22d85-1aa7-466b-810b-8068b96a3152 |
| Verdict: | Suspicious activity |
| Analysis date: | January 01, 2020, 22:07:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 56B16CE0F9B95C3F6B983F04F132F4A0 |
| SHA1: | 98E83BD1B5B54A979F5FC70A12E1B3BC8FB2DE0A |
| SHA256: | B8DAB563675724B76666688C6C82046EB4893E5B15141A7473310BBE8B1ECC7C |
| SSDEEP: | 196608:5BOtfNqAorD4J5q1FYU0/WXPcJZiiMI59is2q:5ScfIW1FYvTKiMs9c |
MALICIOUS
Loads dropped or rewritten executable
- Discord Raider.exe (PID: 616)
SUSPICIOUS
Application launched itself
- Discord Raider.exe (PID: 956)
Executable content was dropped or overwritten
- Discord Raider.exe (PID: 956)
Loads Python modules
- Discord Raider.exe (PID: 616)
INFO
Dropped object may contain Bitcoin addresses
- Discord Raider.exe (PID: 956)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (54.3) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (34.8) |
| .exe | | | Win32 Executable (generic) (5.6) |
| .exe | | | Generic Win/DOS Executable (2.5) |
| .exe | | | DOS Executable Generic (2.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:07:09 16:22:19+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 128000 |
| InitializedDataSize: | 205312 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x790a |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 09-Jul-2019 14:22:19 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 09-Jul-2019 14:22:19 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001F3B4 | 0x0001F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.66635 |
.rdata | 0x00021000 | 0x0000B0EC | 0x0000B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.10031 |
.data | 0x0002D000 | 0x0000E680 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.94098 |
.gfids | 0x0003C000 | 0x000000B8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.86637 |
.rsrc | 0x0003D000 | 0x00024B90 | 0x00024C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.91663 |
.reloc | 0x00062000 | 0x000017D0 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.64245 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
0 | 1.98048 | 20 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
1 | 5.29896 | 1029 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 6.05629 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 5.5741 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 7.95079 | 37019 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 5.29119 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 5.43869 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 5.89356 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
101 | 2.71858 | 104 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
Imports
KERNEL32.dll |
WS2_32.dll |
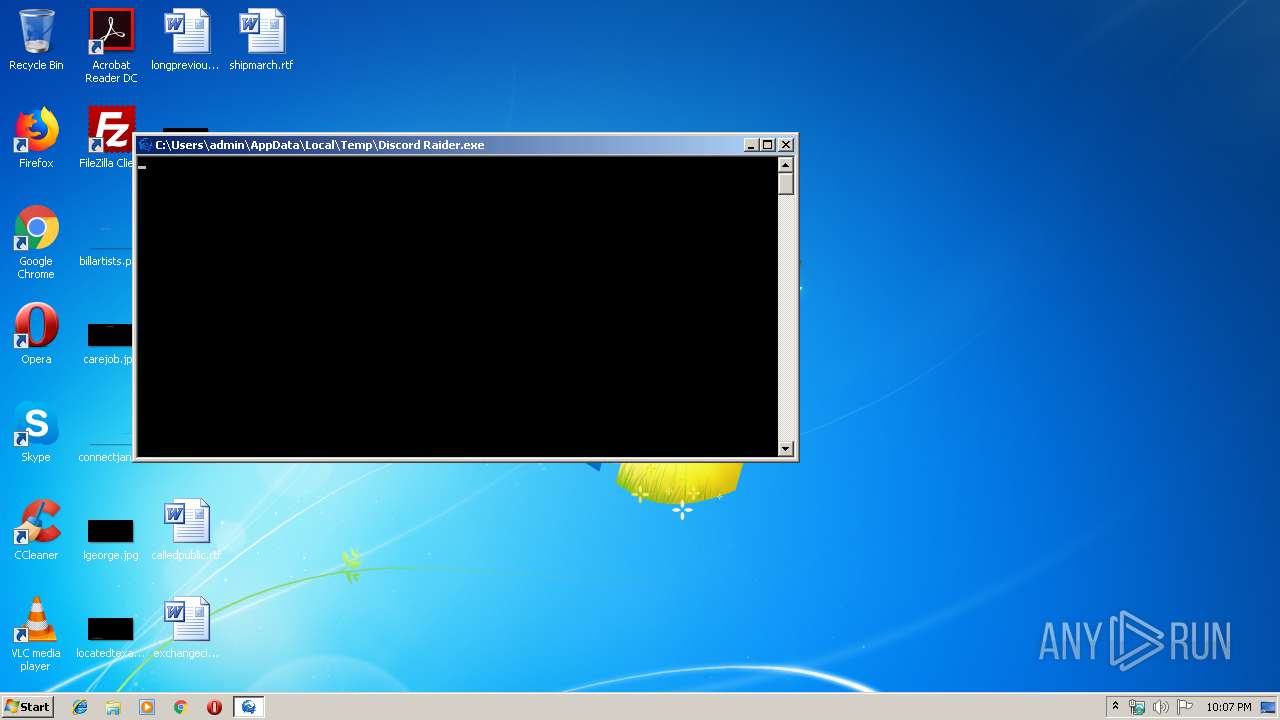
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 616 | "C:\Users\admin\AppData\Local\Temp\Discord Raider.exe" | C:\Users\admin\AppData\Local\Temp\Discord Raider.exe | Discord Raider.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 4294967295 Modules
| |||||||||||||||
| 956 | "C:\Users\admin\AppData\Local\Temp\Discord Raider.exe" | C:\Users\admin\AppData\Local\Temp\Discord Raider.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 4294967295 Modules
| |||||||||||||||
Total events
9
Read events
9
Write events
0
Delete events
0
Modification events
Executable files
18
Suspicious files
1
Text files
12
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 956 | Discord Raider.exe | C:\Users\admin\AppData\Local\Temp\_MEI9562\_decimal.pyd | executable | |
MD5:2A22A7C58067BED977EE3656D1818F69 | SHA256:6FBECEB84331902154A5F81573228149AE9FCB3E6A814ABEA99589DE09FCC433 | |||
| 956 | Discord Raider.exe | C:\Users\admin\AppData\Local\Temp\_MEI9562\export.exe.manifest | xml | |
MD5:— | SHA256:— | |||
| 956 | Discord Raider.exe | C:\Users\admin\AppData\Local\Temp\_MEI9562\base_library.zip | compressed | |
MD5:— | SHA256:— | |||
| 956 | Discord Raider.exe | C:\Users\admin\AppData\Local\Temp\_MEI9562\_cffi_backend.cp37-win32.pyd | executable | |
MD5:9C57FA6BD22B8DCA861E767384E428E4 | SHA256:2DBA673A4701D68FB85054F64A22C4C249C4FB8C7BA0B8CAE8383BBCC9F8D762 | |||
| 956 | Discord Raider.exe | C:\Users\admin\AppData\Local\Temp\_MEI9562\cryptography\hazmat\bindings\_constant_time.cp37-win32.pyd | executable | |
MD5:F217E40FD967C5DA98C27EEBA10711D6 | SHA256:D86E08F86E1095BBFEE98E1816D489D0A7F57B9CDD3BE0AE2FAE10F40E9BDDB6 | |||
| 956 | Discord Raider.exe | C:\Users\admin\AppData\Local\Temp\_MEI9562\_queue.pyd | executable | |
MD5:4F38EB31E85412B5BB3CC955F7A83CFB | SHA256:326F00F00DABF86B33325B8F6344A141AEFB2A56BA5C173D2EFE175EFA72058B | |||
| 956 | Discord Raider.exe | C:\Users\admin\AppData\Local\Temp\_MEI9562\_socket.pyd | executable | |
MD5:86D72934A494121978EF74C8B8ACA5A4 | SHA256:24657ECFDE063412C941AAA6A085341D45ECF4C0153B37B7476459835CCB3CBB | |||
| 956 | Discord Raider.exe | C:\Users\admin\AppData\Local\Temp\_MEI9562\_ssl.pyd | executable | |
MD5:6E8D415D50D8292DBFB479447AC09C27 | SHA256:5B616AF730AA15A75558AFA50E725C7D4D4E5B22BBFFD348DF2239425CFEADD0 | |||
| 956 | Discord Raider.exe | C:\Users\admin\AppData\Local\Temp\_MEI9562\cryptography\hazmat\bindings\_openssl.cp37-win32.pyd | executable | |
MD5:6060B0D2596BFBEC7C2E3C16D5237686 | SHA256:0B192A88494F19C5D099C2F7937534830DDDDE40745C30A0B1A0F24A96A2AA04 | |||
| 956 | Discord Raider.exe | C:\Users\admin\AppData\Local\Temp\_MEI9562\unicodedata.pyd | executable | |
MD5:C184941D097BF03782CC74B785E6DADA | SHA256:95C2E7B6BB25A0BEB8A5C0376CEED33098D9991CDA0414F844F5B9B506167891 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
3
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
616 | Discord Raider.exe | 54.225.169.250:443 | api.ipify.org | Amazon.com, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.ipify.org |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
616 | Discord Raider.exe | Misc activity | SUSPICIOUS [PTsecurity] ipify.org External IP Check |
616 | Discord Raider.exe | Misc activity | SUSPICIOUS [PTsecurity] ipify.org External IP Check |
1 ETPRO signatures available at the full report