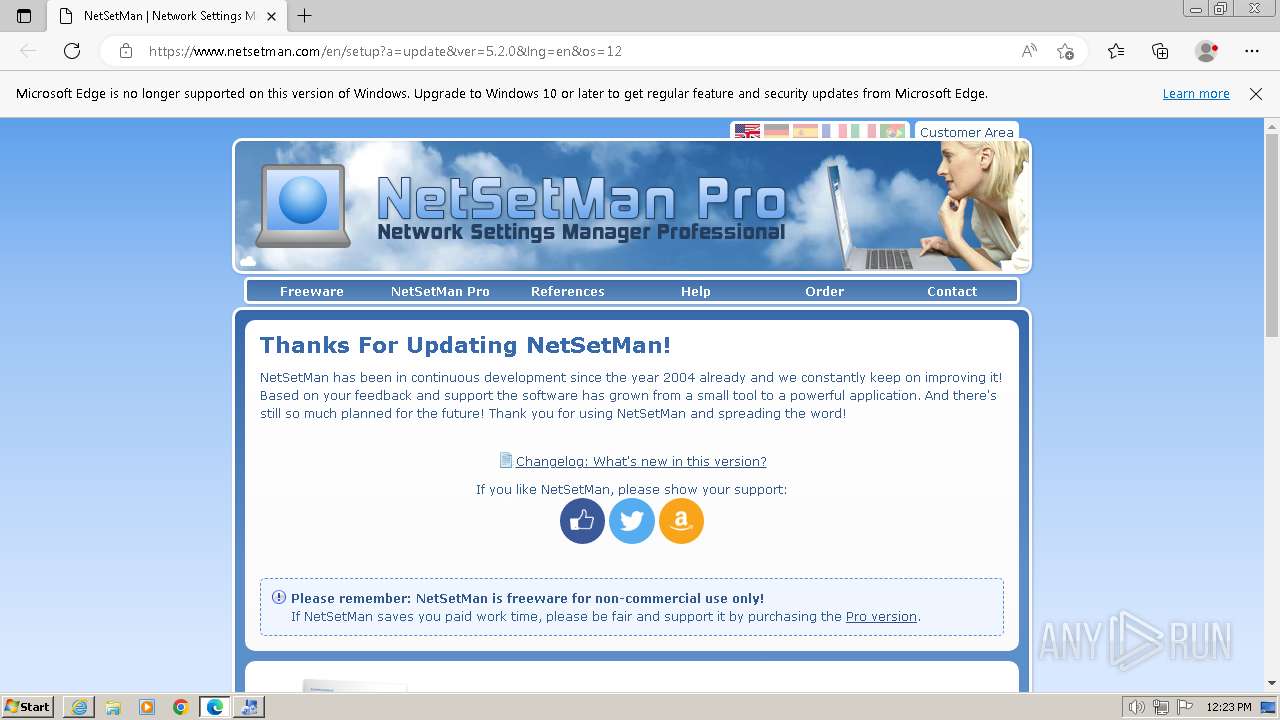
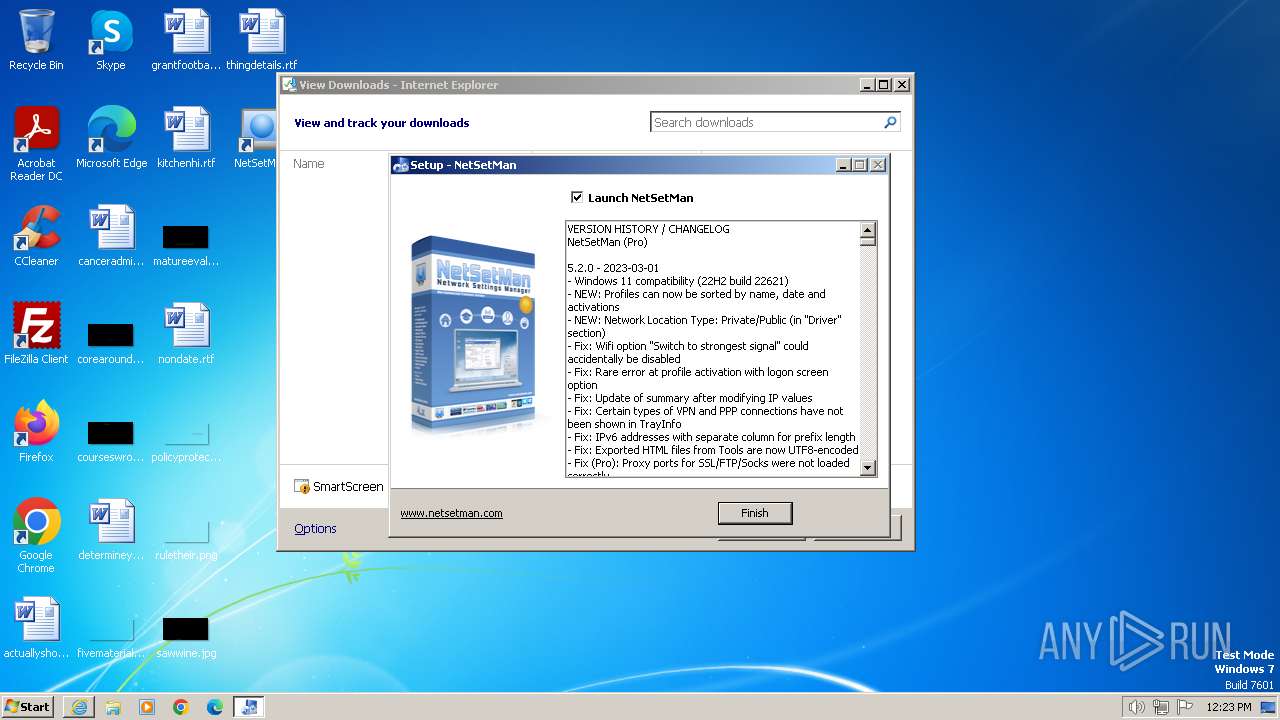
| URL: | https://www.netsetman.com/netsetman.exe |
| Full analysis: | https://app.any.run/tasks/71ff4db3-c323-4d14-9243-378cd7c3e761 |
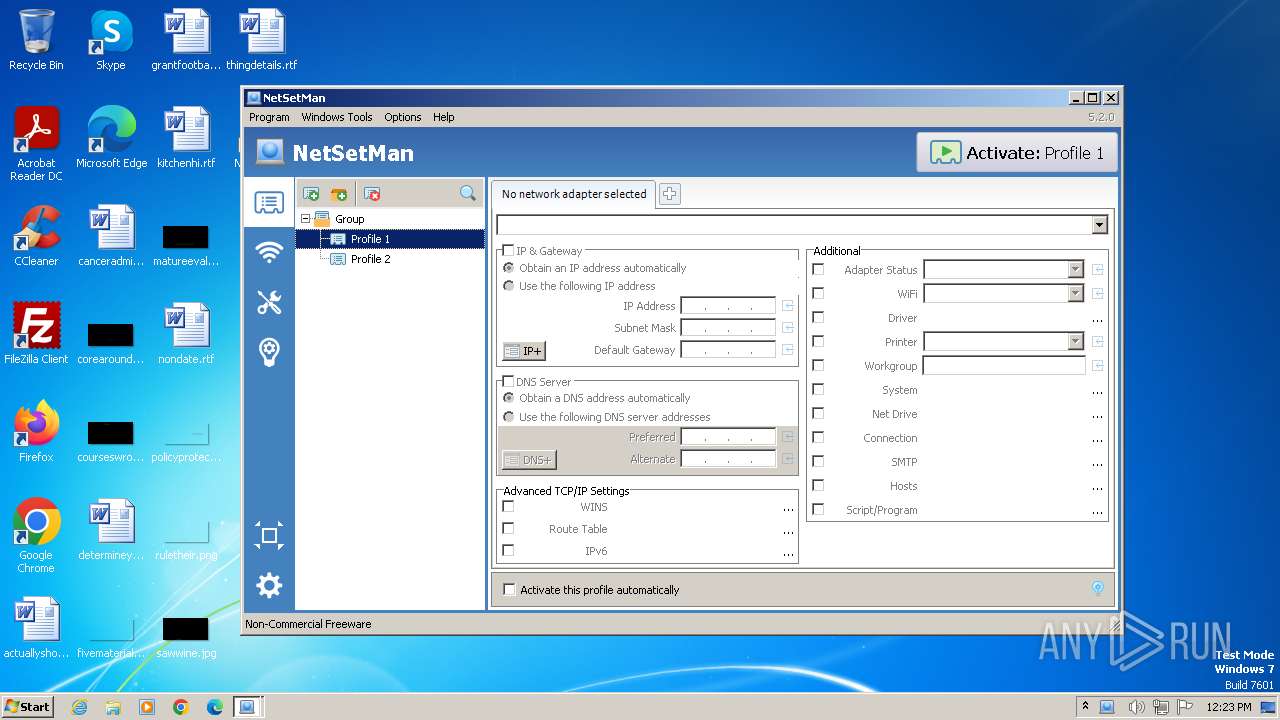
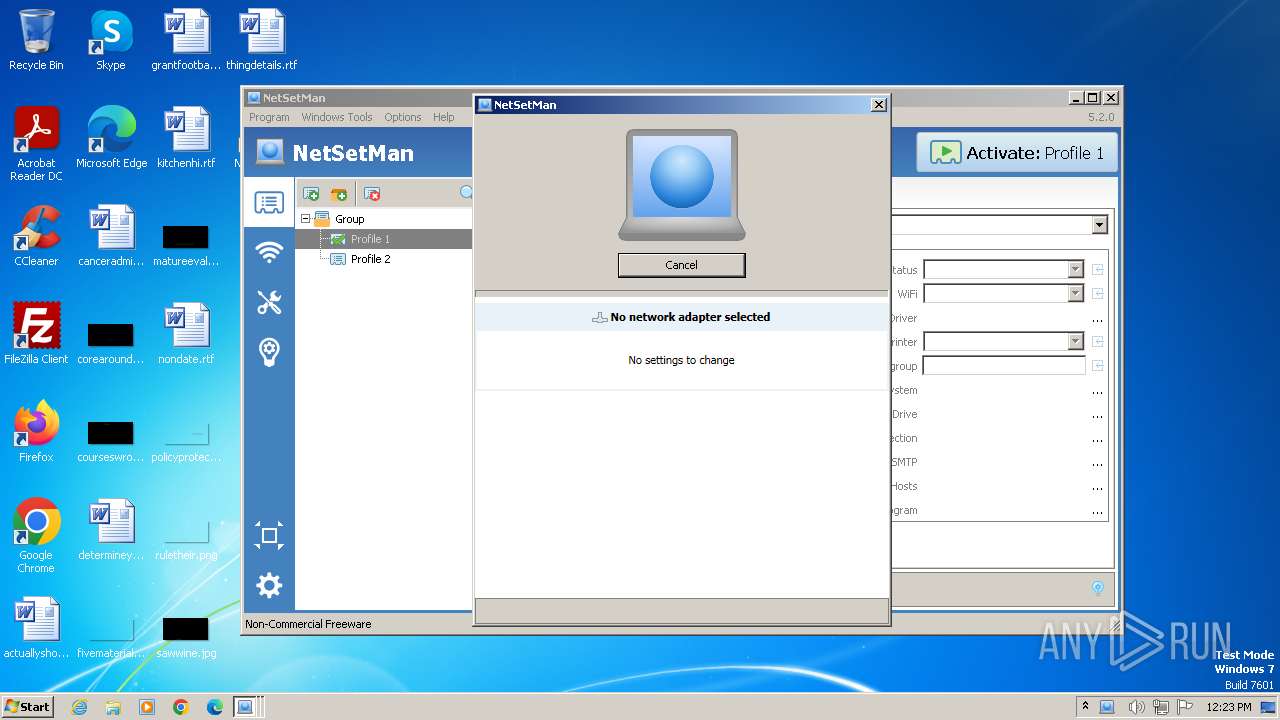
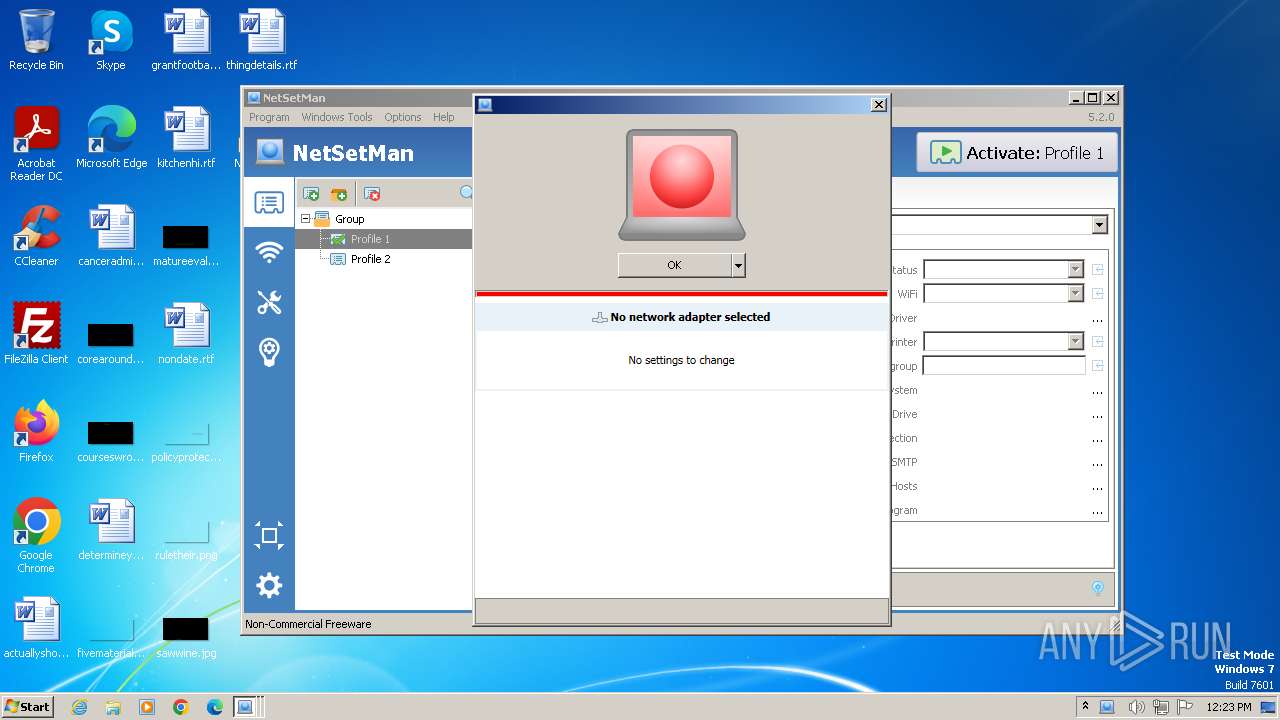
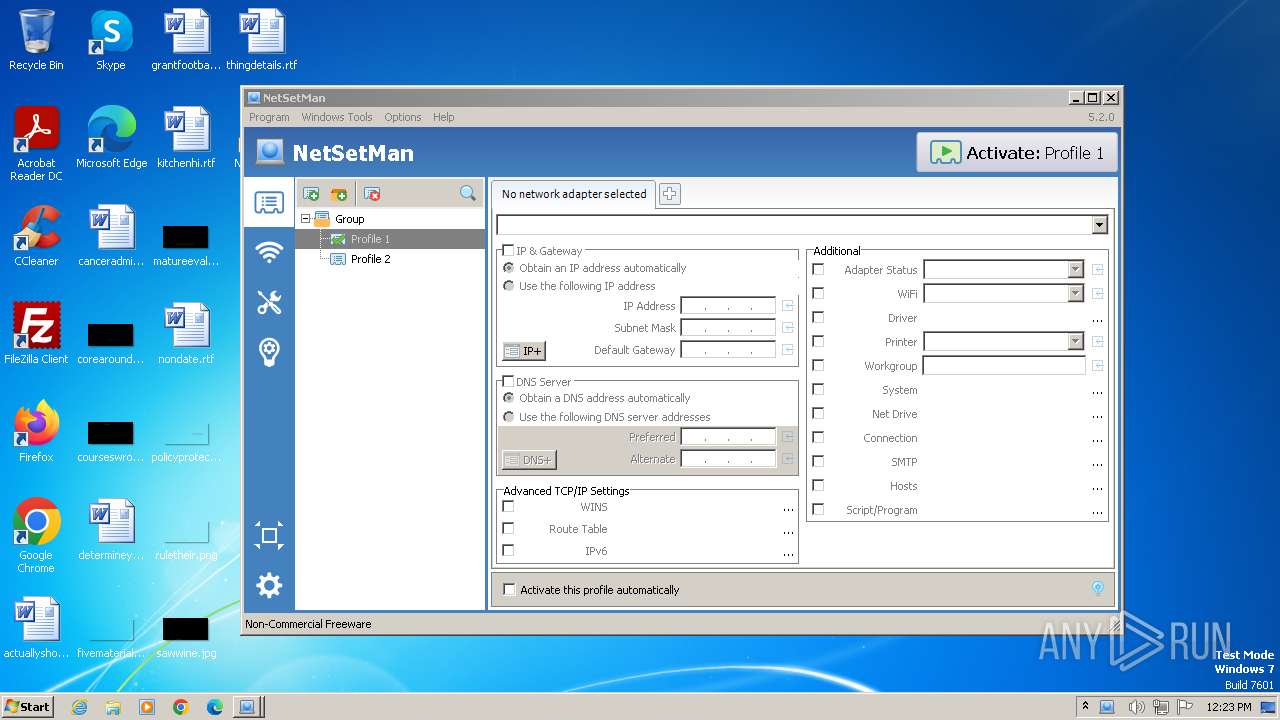
| Verdict: | Malicious activity |
| Analysis date: | January 02, 2024, 12:22:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A76FE85FBCC0B8F775518D09BDA25BF0 |
| SHA1: | FAEFD4B01339EE91AED25623A289D57E6C7FC5C8 |
| SHA256: | B8D4681E15408942461260A44750617AB0E14E38DE3428885EF0416F8115CA89 |
| SSDEEP: | 3:N8DSL0wALLLKKL0WALLLNn:2OL01LSKorF |
MALICIOUS
Actions looks like stealing of personal data
- netsetman_setup_520.tmp (PID: 1736)
Starts NET.EXE for service management
- net.exe (PID: 1192)
- cmd.exe (PID: 1388)
- net.exe (PID: 2432)
- netsetman_setup_520.tmp (PID: 1736)
- netsetman.exe (PID: 3312)
- net.exe (PID: 3532)
- net.exe (PID: 3808)
- netsetman.exe (PID: 3680)
- net.exe (PID: 3304)
- netsetman.exe (PID: 3452)
SUSPICIOUS
Reads the Windows owner or organization settings
- netsetman_setup_520.tmp (PID: 1736)
Uses TASKKILL.EXE to kill process
- netsetman_setup_520.tmp (PID: 1736)
Reads the Internet Settings
- netsetman_setup_520.tmp (PID: 1736)
- netsetman_setup_520.tmp (PID: 1216)
- netsetman.exe (PID: 3452)
- netsetman.exe (PID: 3680)
- netsetman.exe (PID: 3312)
Searches for installed software
- netsetman_setup_520.tmp (PID: 1736)
- netsetman.exe (PID: 3312)
- netsetman.exe (PID: 3680)
Creates or modifies Windows services
- nsmservice.exe (PID: 2668)
Starts CMD.EXE for commands execution
- nsmservice.exe (PID: 2668)
Checks Windows Trust Settings
- nsmservice.exe (PID: 1852)
- netsetman.exe (PID: 3680)
- netsetman.exe (PID: 3312)
Reads settings of System Certificates
- netsetman.exe (PID: 3312)
- netsetman.exe (PID: 3680)
Reads security settings of Internet Explorer
- netsetman.exe (PID: 3680)
- netsetman.exe (PID: 3312)
Adds/modifies Windows certificates
- netsetman.exe (PID: 3680)
- nsmservice.exe (PID: 1852)
INFO
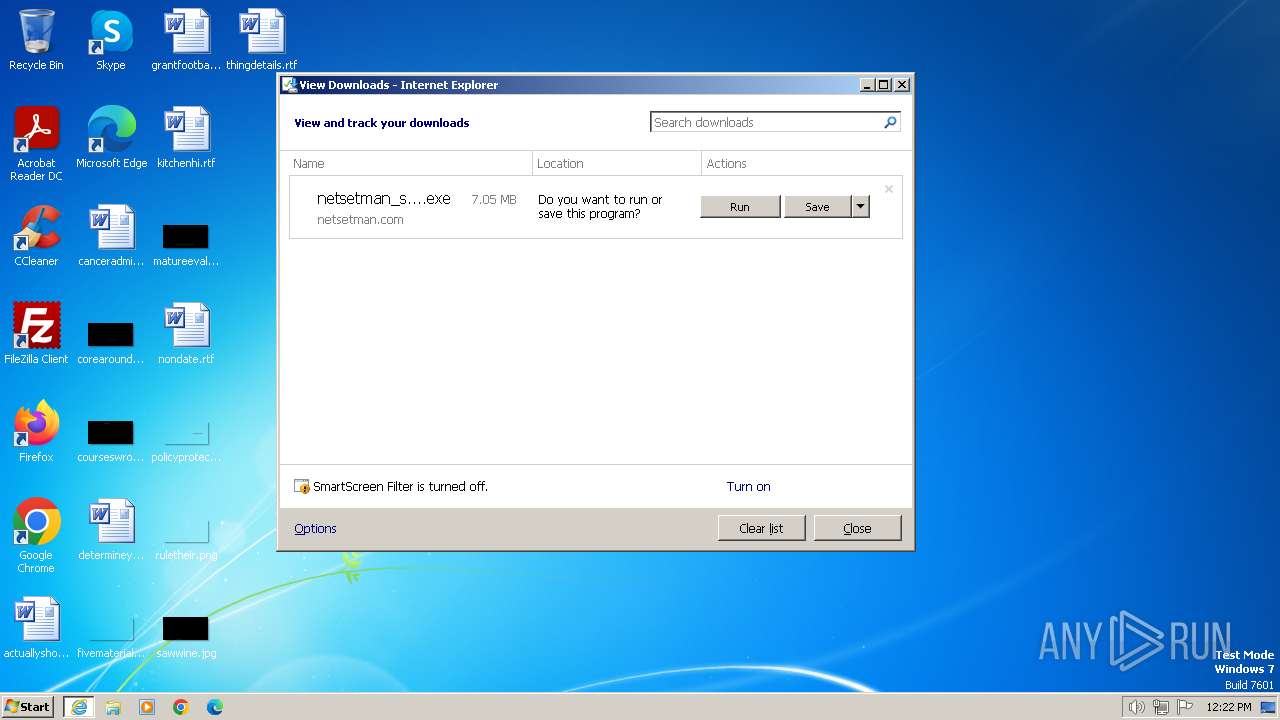
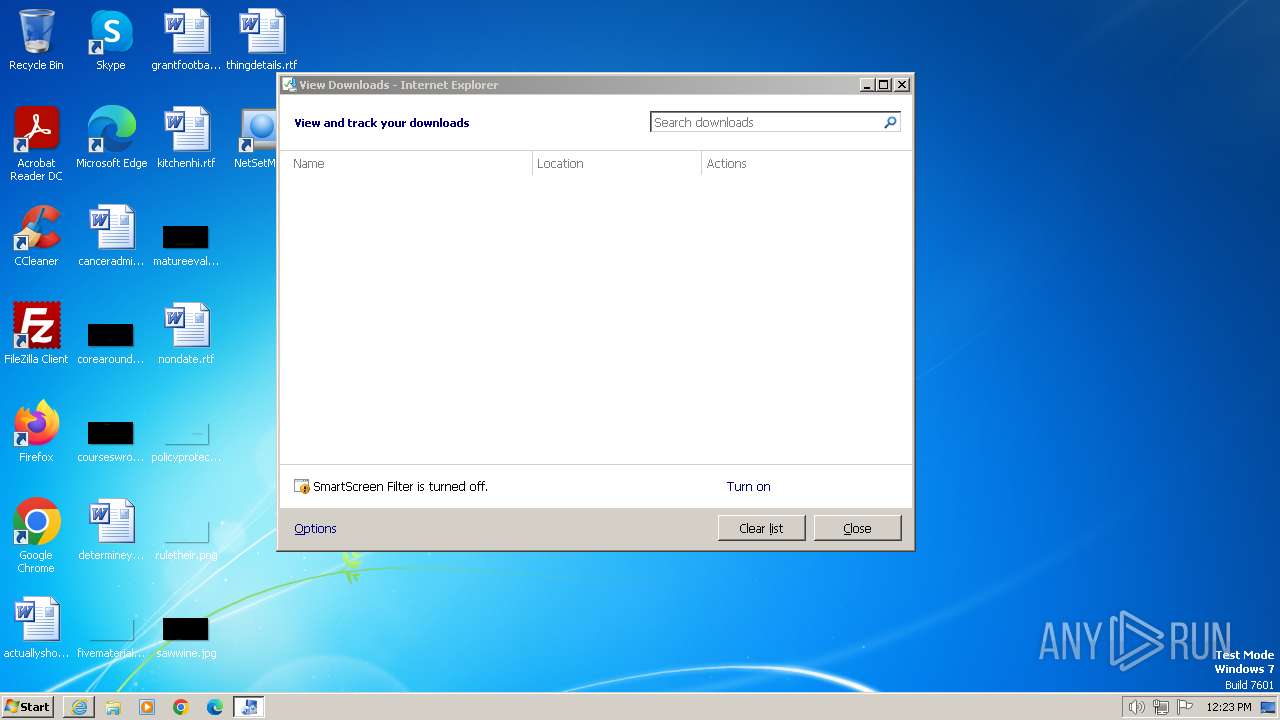
The process uses the downloaded file
- iexplore.exe (PID: 2124)
Application launched itself
- iexplore.exe (PID: 2124)
- msedge.exe (PID: 2332)
Checks supported languages
- netsetman_setup_520.exe (PID: 1864)
- netsetman_setup_520.tmp (PID: 1216)
- netsetman_setup_520.exe (PID: 848)
- netsetman_setup_520.tmp (PID: 1736)
- netsetman.exe (PID: 3312)
- nsmservice.exe (PID: 2668)
- nsmservice.exe (PID: 1852)
- netsetman.exe (PID: 3452)
- netsetman.exe (PID: 3680)
Drops the executable file immediately after the start
- iexplore.exe (PID: 1288)
- netsetman_setup_520.exe (PID: 1864)
- iexplore.exe (PID: 2124)
- netsetman_setup_520.exe (PID: 848)
- netsetman_setup_520.tmp (PID: 1736)
Reads the computer name
- netsetman_setup_520.tmp (PID: 1216)
- netsetman_setup_520.tmp (PID: 1736)
- nsmservice.exe (PID: 1852)
- nsmservice.exe (PID: 2668)
- netsetman.exe (PID: 3312)
- netsetman.exe (PID: 3452)
- netsetman.exe (PID: 3680)
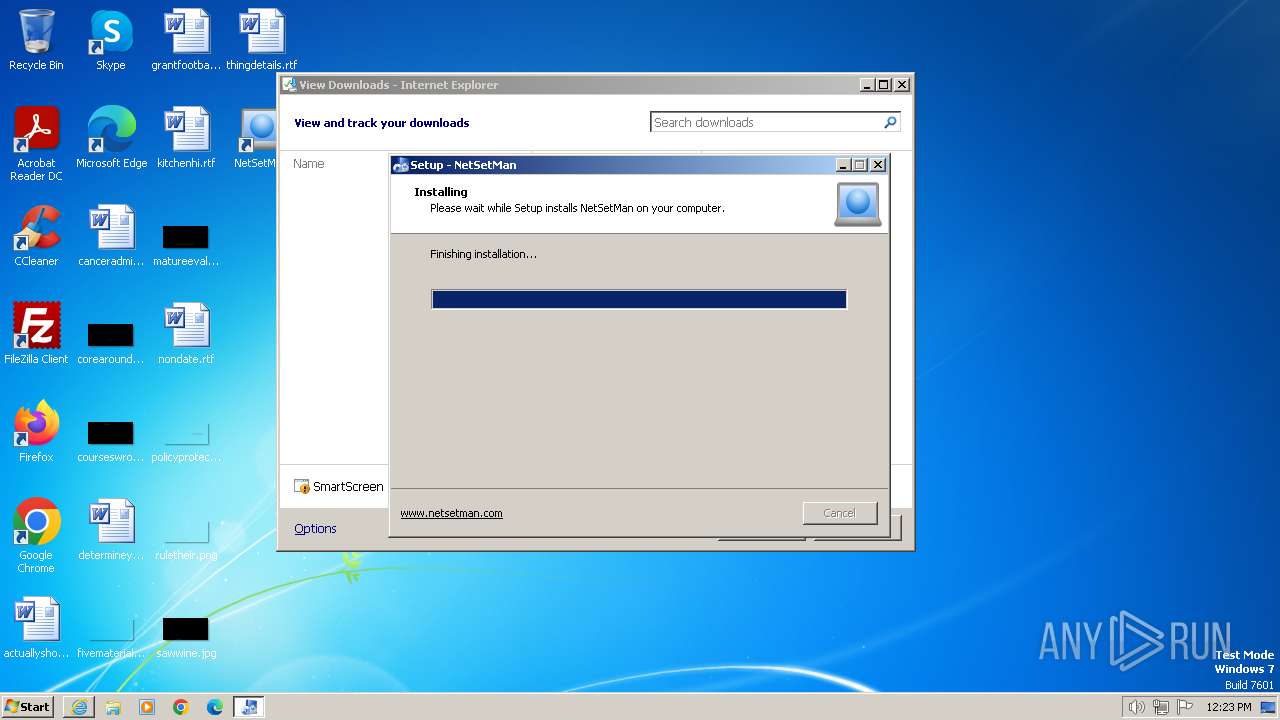
Create files in a temporary directory
- netsetman_setup_520.exe (PID: 1864)
- netsetman_setup_520.exe (PID: 848)
Creates files in the program directory
- netsetman_setup_520.tmp (PID: 1736)
- netsetman.exe (PID: 3312)
Executes as Windows Service
- nsmservice.exe (PID: 1852)
Reads the machine GUID from the registry
- nsmservice.exe (PID: 1852)
- netsetman.exe (PID: 3680)
- netsetman.exe (PID: 3312)
Checks proxy server information
- netsetman.exe (PID: 3680)
- netsetman.exe (PID: 3312)
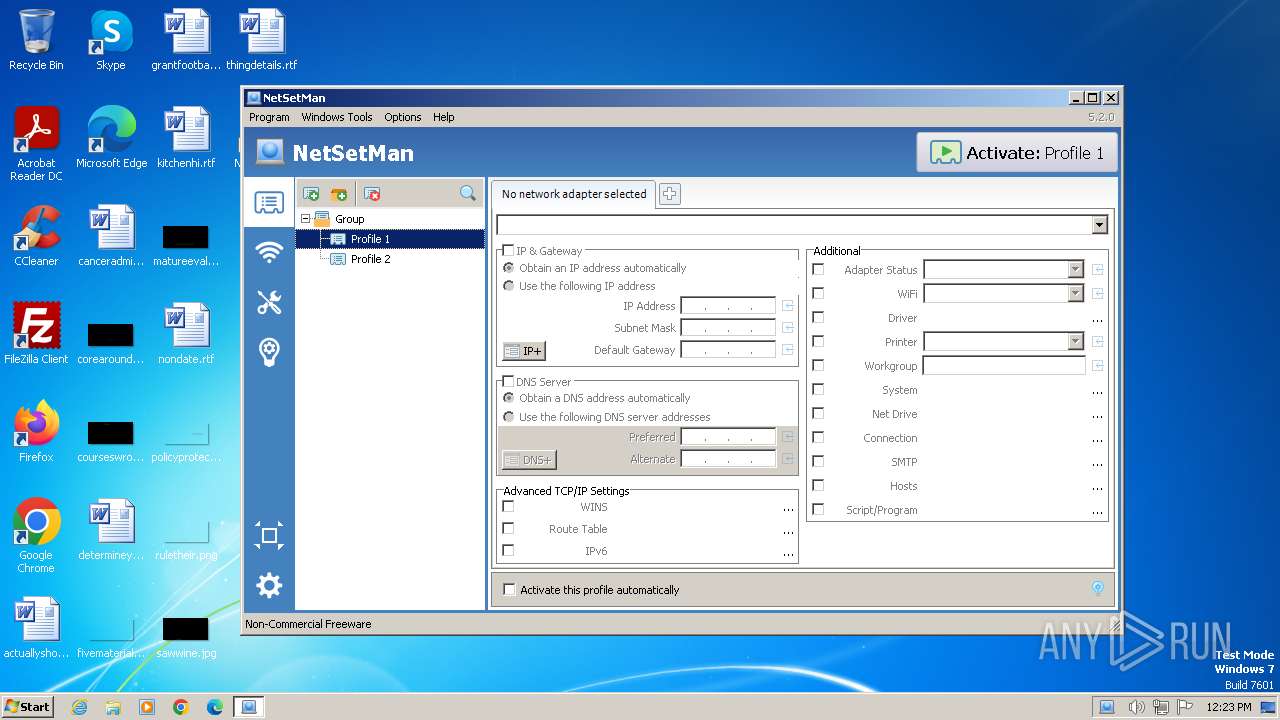
Manual execution by a user
- netsetman.exe (PID: 3452)
Reads Environment values
- netsetman.exe (PID: 3312)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
79
Monitored processes
34
Malicious processes
5
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
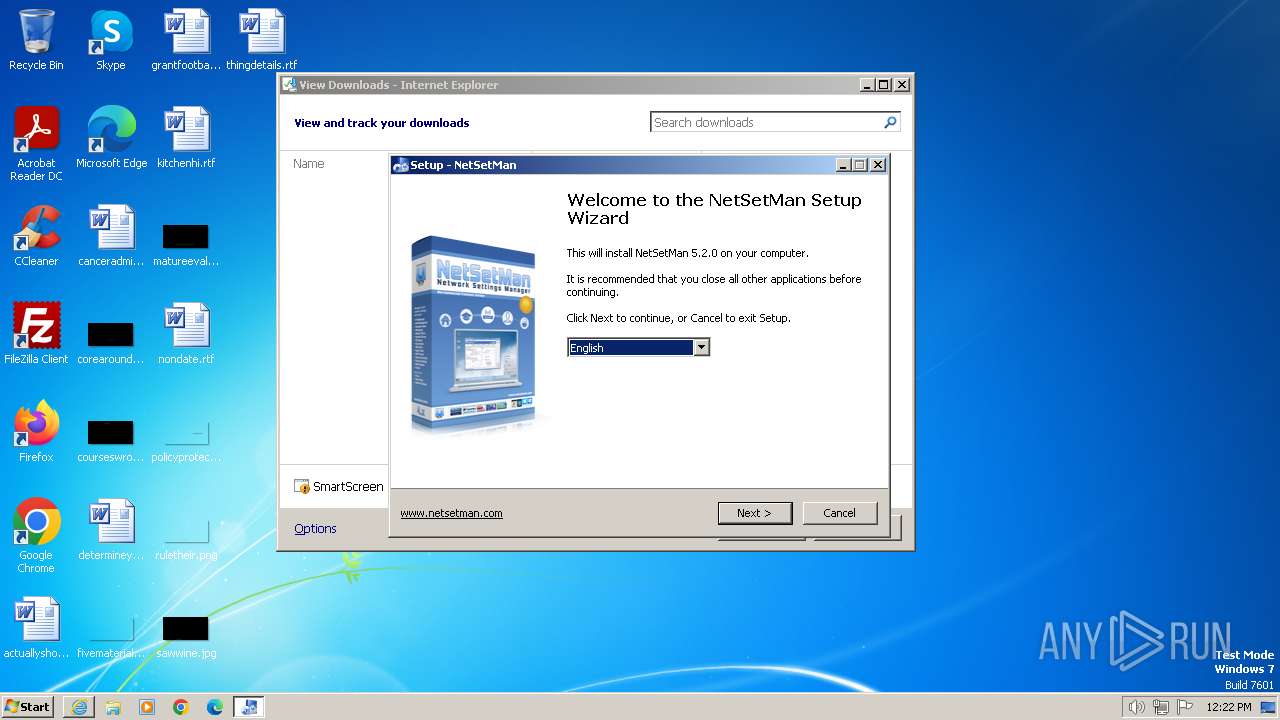
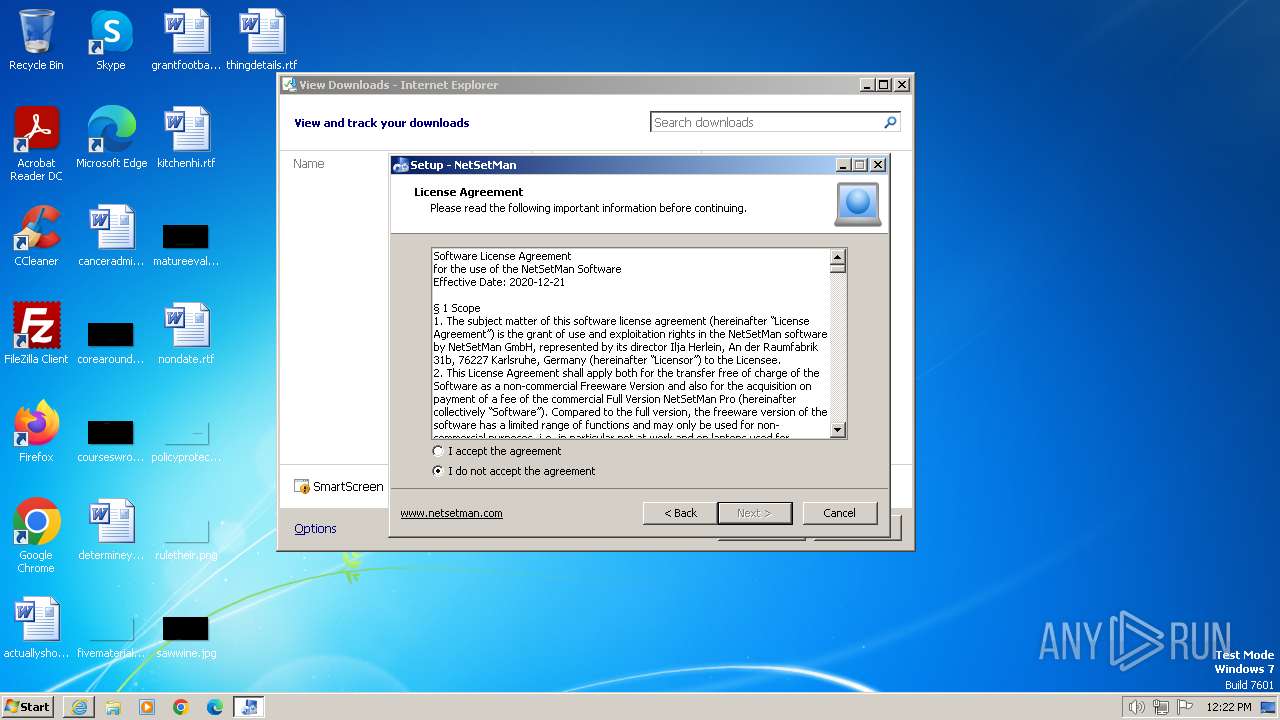
| 848 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\netsetman_setup_520.exe" /SPAWNWND=$40134 /NOTIFYWND=$3014A | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\netsetman_setup_520.exe | netsetman_setup_520.tmp | ||||||||||||
User: admin Company: NetSetMan GmbH Integrity Level: HIGH Description: NetSetMan Setup Exit code: 0 Version: 5.2.0 Modules
| |||||||||||||||
| 1192 | "C:\Windows\system32\net.exe" start nsmService | C:\Windows\System32\net.exe | — | netsetman_setup_520.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1216 | "C:\Users\admin\AppData\Local\Temp\is-NU7FN.tmp\netsetman_setup_520.tmp" /SL5="$3014A,6377473,829952,C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\netsetman_setup_520.exe" | C:\Users\admin\AppData\Local\Temp\is-NU7FN.tmp\netsetman_setup_520.tmp | — | netsetman_setup_520.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1288 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2124 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1388 | cmd.exe /c net start nsmService | C:\Windows\System32\cmd.exe | — | nsmservice.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1736 | "C:\Users\admin\AppData\Local\Temp\is-SO01S.tmp\netsetman_setup_520.tmp" /SL5="$50140,6377473,829952,C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\netsetman_setup_520.exe" /SPAWNWND=$40134 /NOTIFYWND=$3014A | C:\Users\admin\AppData\Local\Temp\is-SO01S.tmp\netsetman_setup_520.tmp | netsetman_setup_520.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1852 | "C:\Program Files\NetSetMan\nsmservice.exe" | C:\Program Files\NetSetMan\nsmservice.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 1860 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1400 --field-trial-handle=1312,i,14024119839490609619,8568127945090696483,131072 /prefetch:3 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1864 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\netsetman_setup_520.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\netsetman_setup_520.exe | — | iexplore.exe | |||||||||||
User: admin Company: NetSetMan GmbH Integrity Level: MEDIUM Description: NetSetMan Setup Exit code: 0 Version: 5.2.0 Modules
| |||||||||||||||
| 2124 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.netsetman.com/netsetman.exe" | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
27 773
Read events
27 571
Write events
191
Delete events
11
Modification events
| (PID) Process: | (2124) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (2124) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (2124) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (2124) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2124) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2124) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2124) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2124) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2124) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2124) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
11
Suspicious files
75
Text files
262
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1288 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_89854CA6A0F0936A4D2ECA78845CEA25 | binary | |
MD5:88FEE9E767E7487E28A872FC2E08C3CC | SHA256:9306C1247FE87945B496CC56395E7F5E3C661A4C25BC4B55F66EC626C7C8ADBC | |||
| 1288 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\ATU0HOGY.txt | text | |
MD5:57852CC2F18572AB16643D260F26C932 | SHA256:C751FDDD128BC254C97F95C05A4B0D44DC7D0B37DB3D534448D740090C7BECF6 | |||
| 1288 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\9DP3O7Y4.txt | text | |
MD5:1C51BA0493E3DDA154B95DBFCAE5F0DA | SHA256:AA6F6AE39AC166F17AEF4ACA1B4AEFAFE05BC0FF8B26E1ABFD34DFCDD0D41257 | |||
| 1288 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\netsetman[1].htm | html | |
MD5:9430C7BA1C98FEEECDA3D1688D8B072B | SHA256:3302D0343B2A1FE6E2F2FA0C710ECDC3E5298D285E8D4BD8FA0292F9B77E4203 | |||
| 1288 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\netsetman_setup_520[1].exe | executable | |
MD5:20AD52295CAE4536DE6E9869A0639E54 | SHA256:AE16FD2FB95B66EB6C8E29220B15660721A6F1E41CDA9F27772CFEEFDB259E08 | |||
| 2124 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\netsetman_setup_520.exe.5fuvru2.partial:Zone.Identifier | text | |
MD5:FBCCF14D504B7B2DBCB5A5BDA75BD93B | SHA256:EACD09517CE90D34BA562171D15AC40D302F0E691B439F91BE1B6406E25F5913 | |||
| 2124 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFC073E377345A4DDB.TMP | binary | |
MD5:139B8BE2BB551E1D37A65BE40514C711 | SHA256:5CBEA228C43C403590C3B0CB4E4A1A13BAE54E8CB5AE47E4505F5CC27C7E9295 | |||
| 2124 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{A074BA71-A969-11EE-AE0A-12A9866C77DE}.dat | binary | |
MD5:E010B2B2137DF72333E3A8B89B4C557F | SHA256:272AB311601CA15C6A7873411509FE144A1CD4FCC0A51DED3E834BCFD369500F | |||
| 1864 | netsetman_setup_520.exe | C:\Users\admin\AppData\Local\Temp\is-NU7FN.tmp\netsetman_setup_520.tmp | executable | |
MD5:5217FE653FFF26227A7BC81CC4FC751E | SHA256:77C0B204E110072C74A24ECC244055470B030947FEB2118DBDE30DAEB0FCAC30 | |||
| 1288 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
26
DNS requests
25
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1288 | iexplore.exe | GET | 200 | 23.53.40.72:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?608cb4ab6d3f68d3 | DE | compressed | 4.66 Kb | unknown |
1288 | iexplore.exe | GET | 200 | 23.53.40.72:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?f6bf34dbb61e71d7 | DE | compressed | 4.66 Kb | unknown |
1288 | iexplore.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEFZnHQTqT5lMbxCBR1nSdZQ%3D | unknown | binary | 1.42 Kb | unknown |
1288 | iexplore.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSr83eyJy3njhjVpn5bEpfc6MXawQQUOuEJhtTPGcKWdnRJdtzgNcZjY5oCEDW%2BdGOMs%2BneKAVwt5eAs2c%3D | US | binary | 978 b | unknown |
1288 | iexplore.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSL5xwzjg4BhTSGENp0Rttj68psLQQUTUrvxEazEq1PTpqxWeJRqwgQeAgCEGOfJT2MZ0kNQY7S24gFbXk%3D | unknown | binary | 281 b | unknown |
1080 | svchost.exe | GET | 304 | 23.53.40.82:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?503c317279212ca4 | DE | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1288 | iexplore.exe | 85.13.135.165:443 | www.netsetman.com | Neue Medien Muennich GmbH | DE | unknown |
1288 | iexplore.exe | 23.53.40.72:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
1288 | iexplore.exe | 104.18.38.233:80 | ocsp.comodoca.com | CLOUDFLARENET | — | shared |
1288 | iexplore.exe | 172.64.149.23:80 | ocsp.comodoca.com | CLOUDFLARENET | US | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1860 | msedge.exe | 85.13.135.165:443 | www.netsetman.com | Neue Medien Muennich GmbH | DE | unknown |
2332 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1860 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.netsetman.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
nav-edge.smartscreen.microsoft.com |
| whitelisted |
data-edge.smartscreen.microsoft.com |
| whitelisted |
stats.netsetman.com |
| unknown |
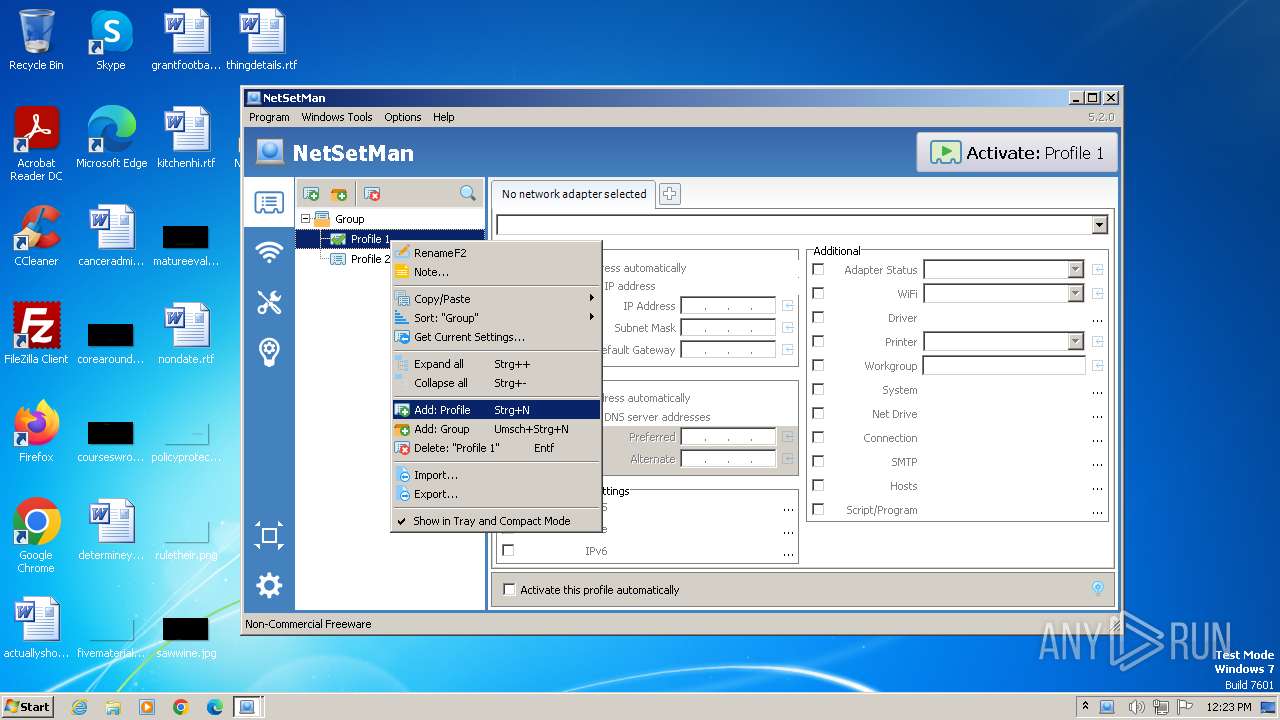
Threats
Process | Message |
|---|---|
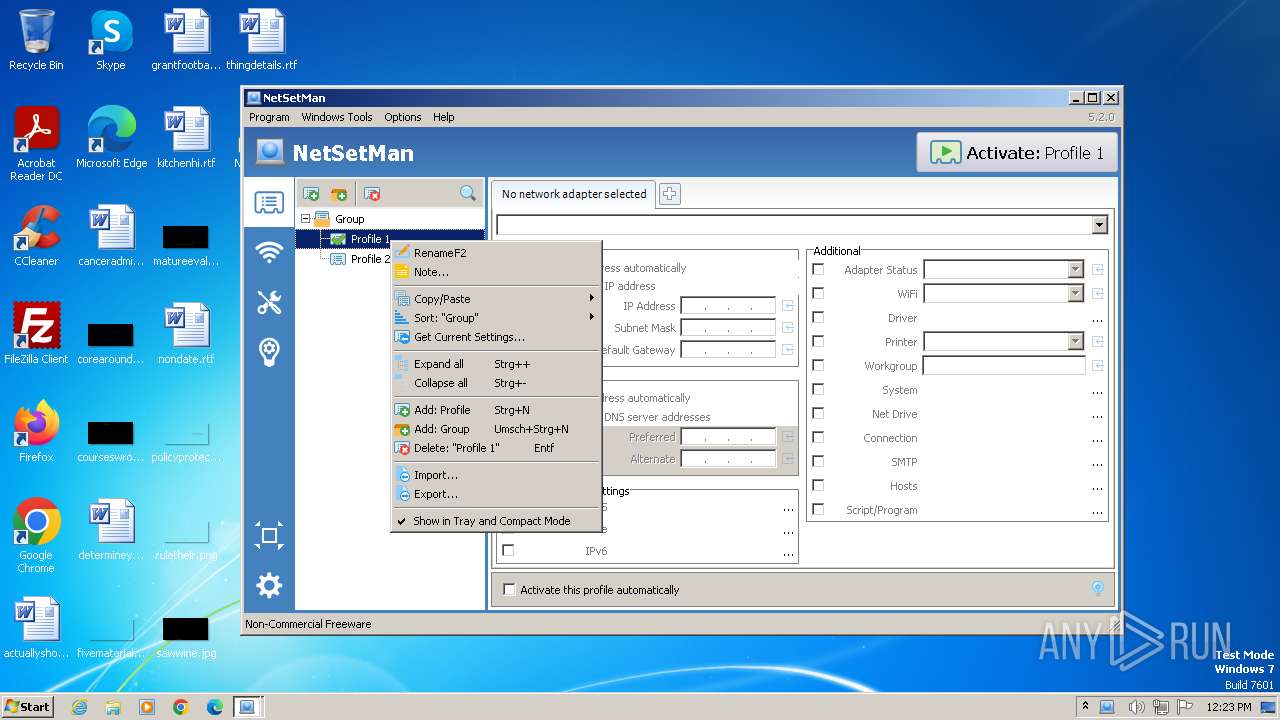
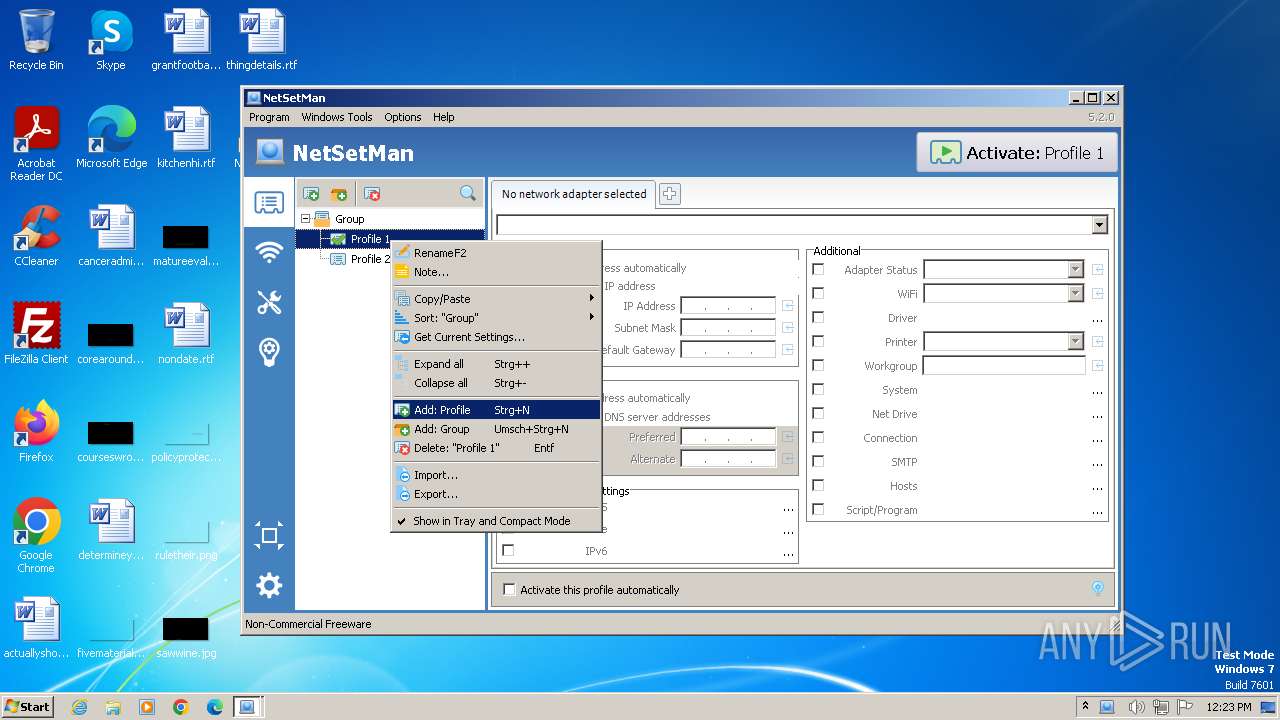
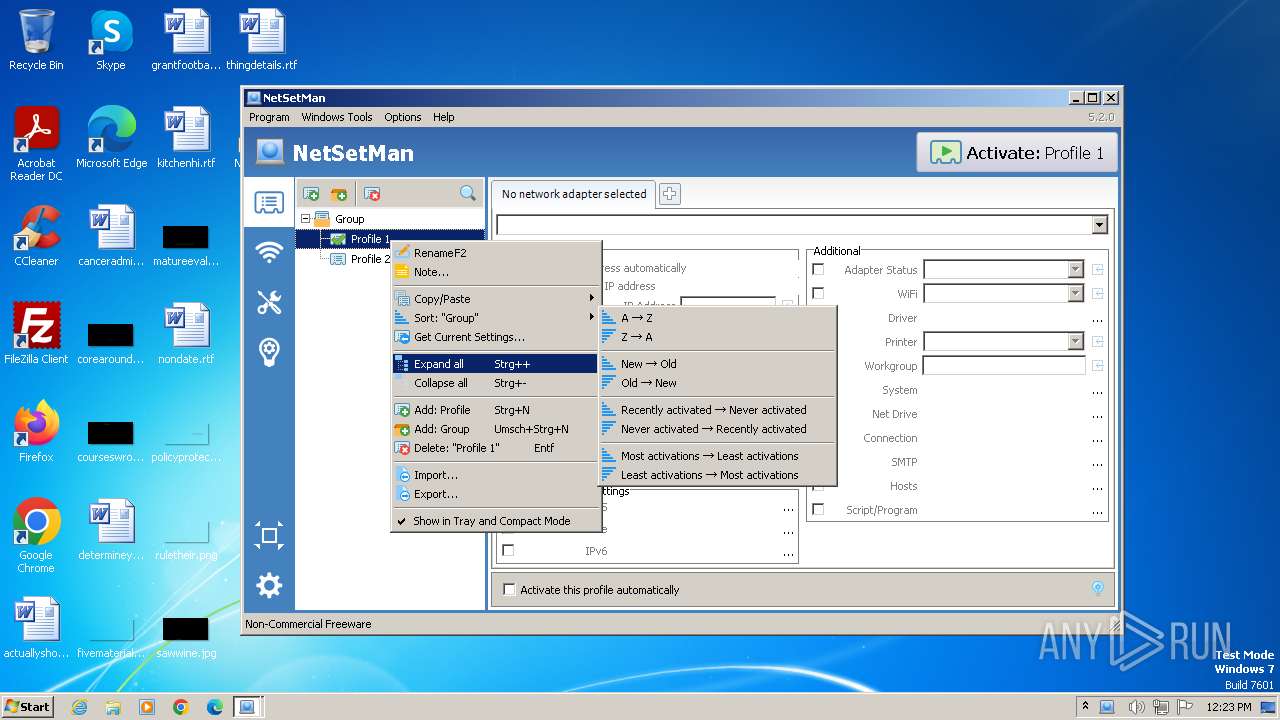
netsetman.exe | WM_MENUSELECT |
netsetman.exe | select |
netsetman.exe | select |
netsetman.exe | WM_MENUSELECT |
netsetman.exe | select |
netsetman.exe | WM_MENUSELECT |
netsetman.exe | select |
netsetman.exe | WM_MENUSELECT |
netsetman.exe | select |
netsetman.exe | WM_MENUSELECT |