| File name: | Solaris.exe |
| Full analysis: | https://app.any.run/tasks/928bf5d5-019a-4d04-9721-485c19a14a44 |
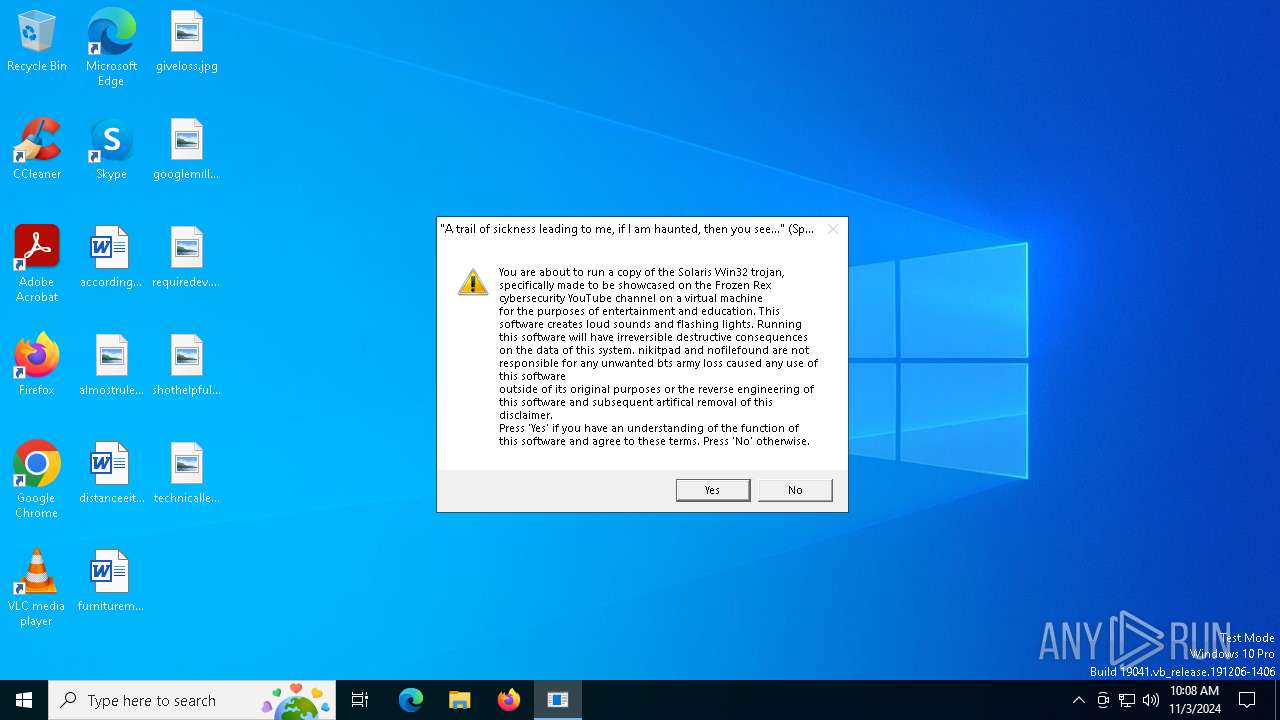
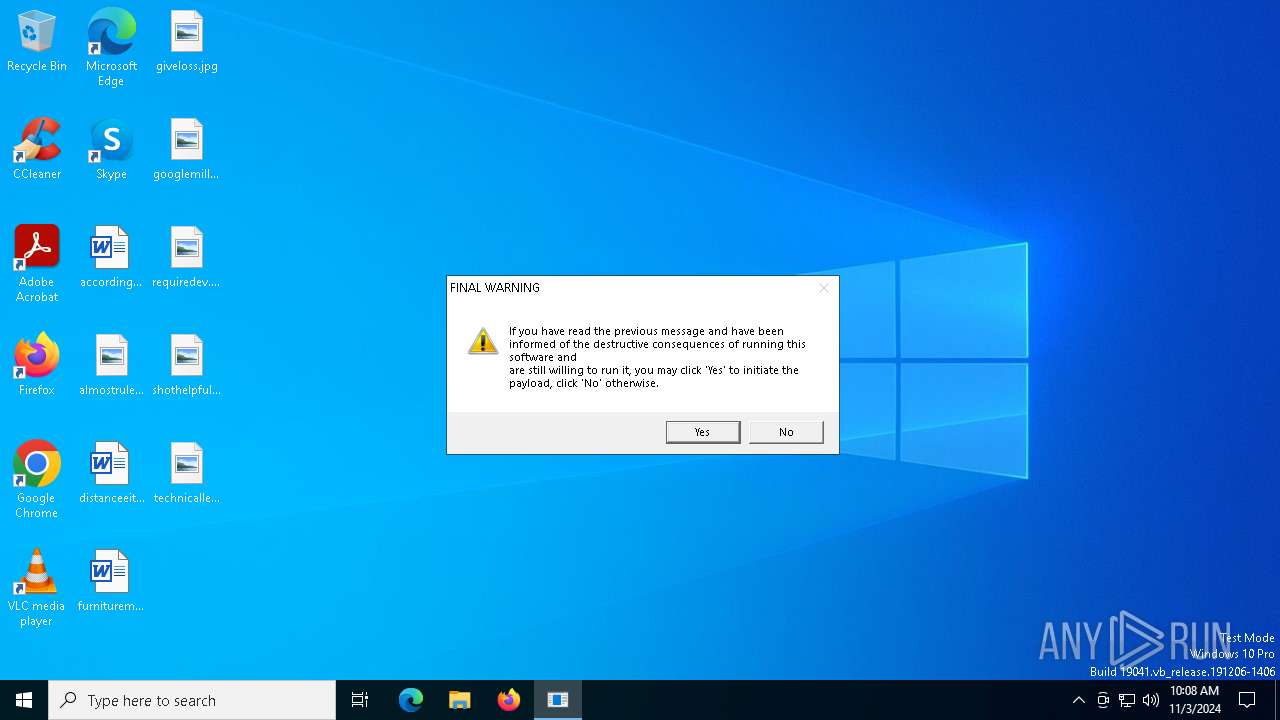
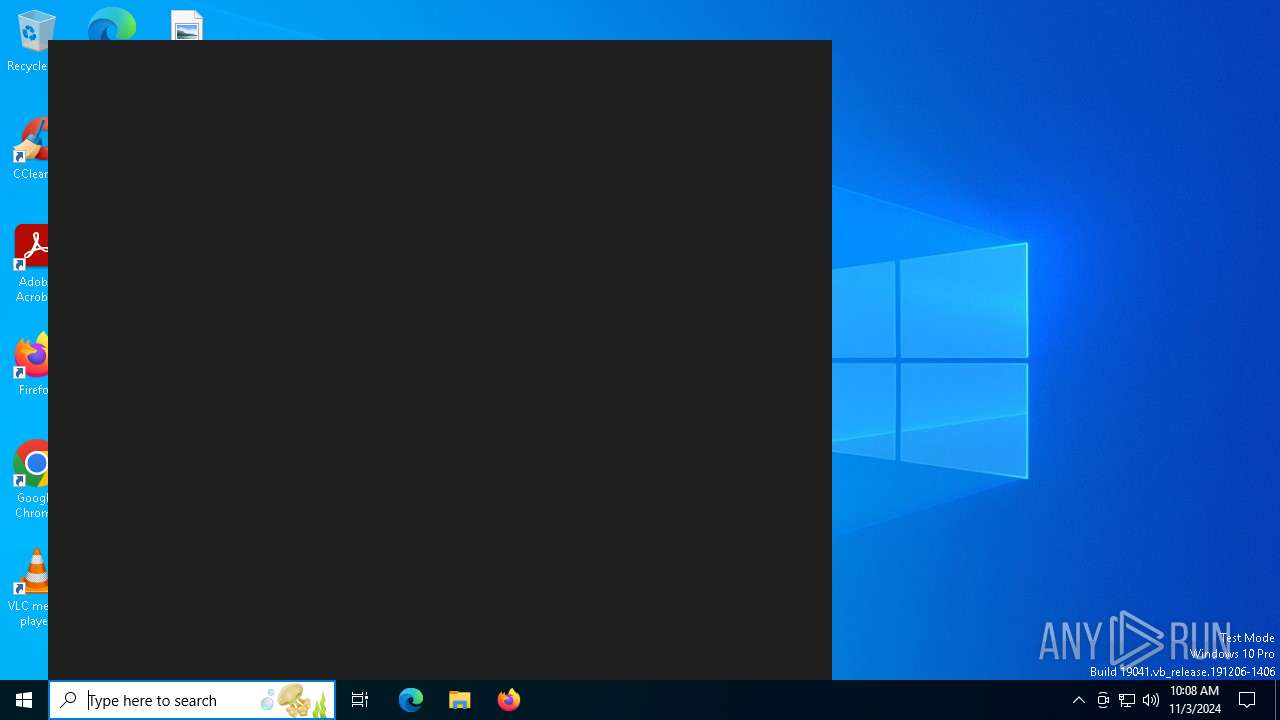
| Verdict: | Malicious activity |
| Analysis date: | November 03, 2024, 10:08:31 |
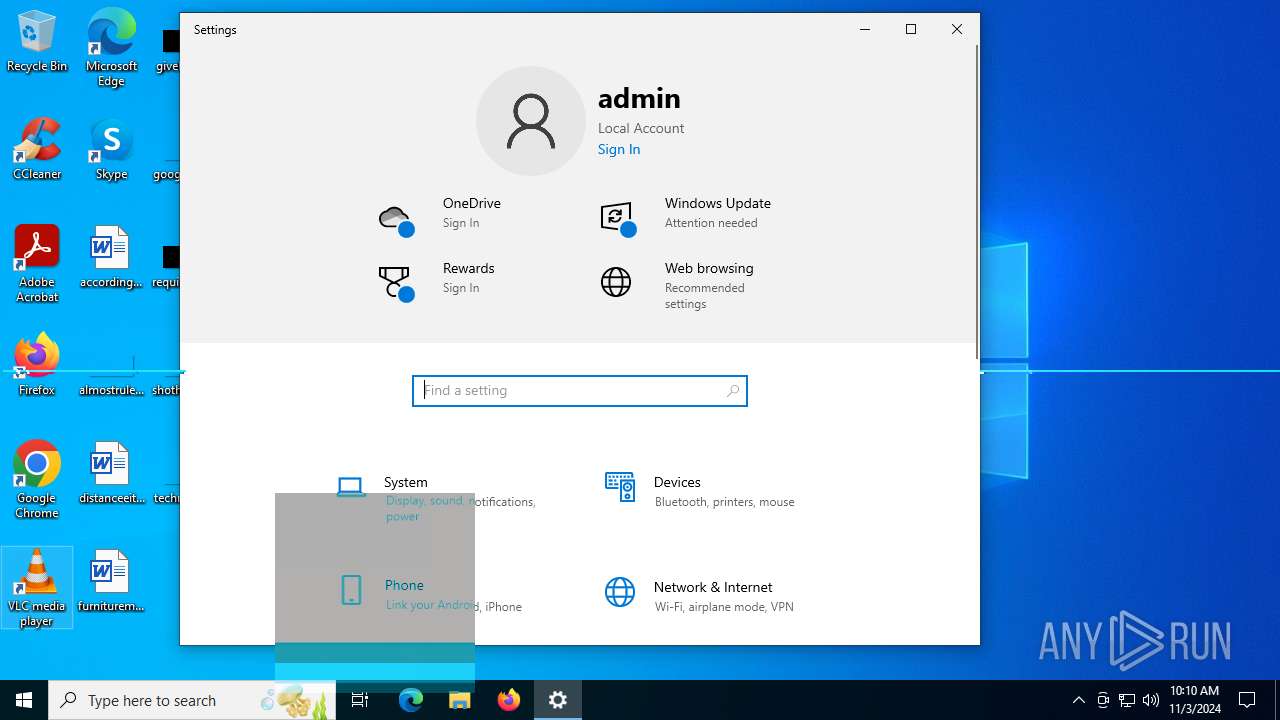
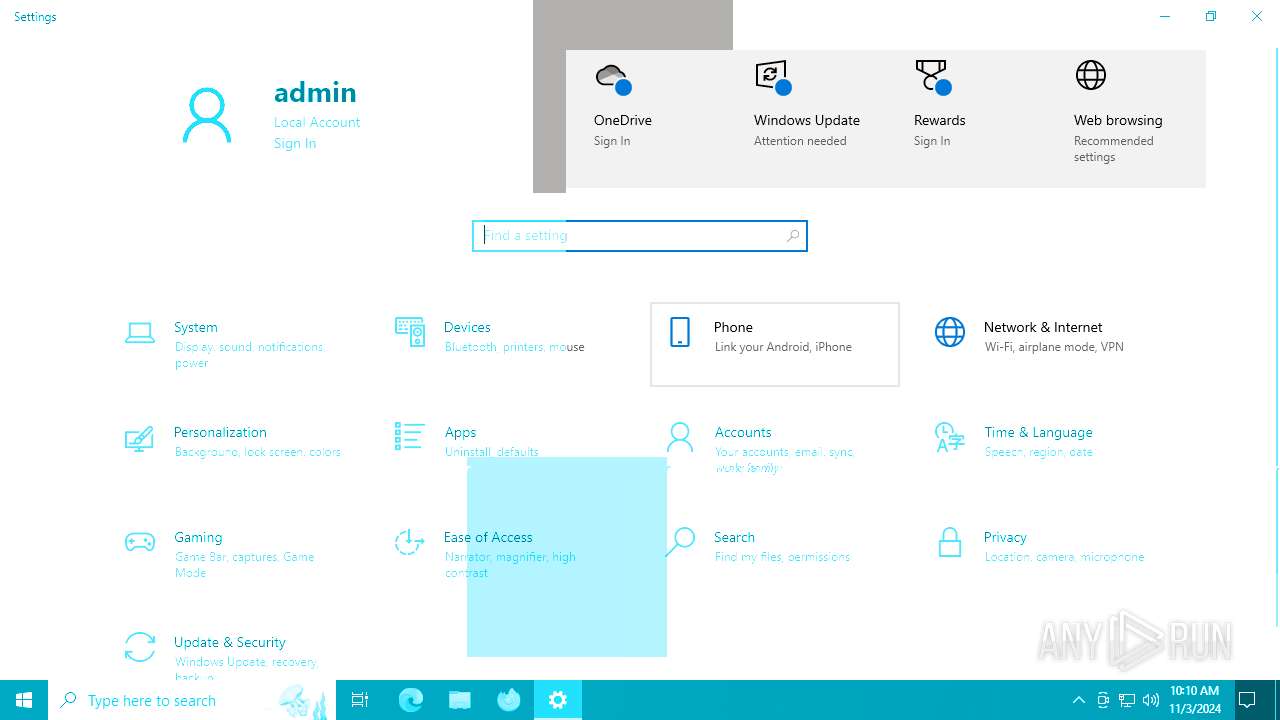
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | FF8E7B3A5CA1D2851C559A2BE62EFEF7 |
| SHA1: | F2777DC2B2E3C54166070322C4C63EF2276CF16B |
| SHA256: | B8C74A0C68697BD1ED5D362007823E01CB7911D30C3B6682BFA51837D638DE72 |
| SSDEEP: | 49152:gd6uAE5yz/q7hJ5UyBS+eNUbkWy0tymlEN9rLVCVoT4i+c:gd663lEN9rLk3 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Application launched itself
- Solaris.exe (PID: 5084)
Reads security settings of Internet Explorer
- Solaris.exe (PID: 5084)
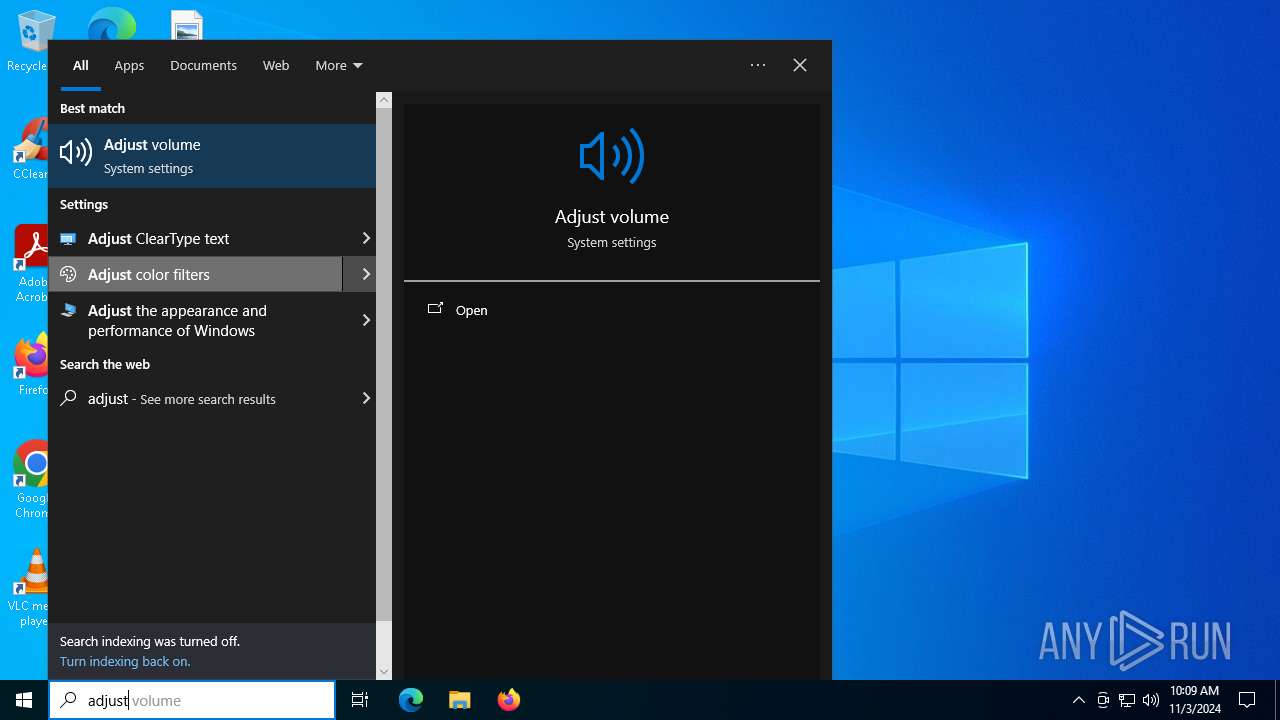
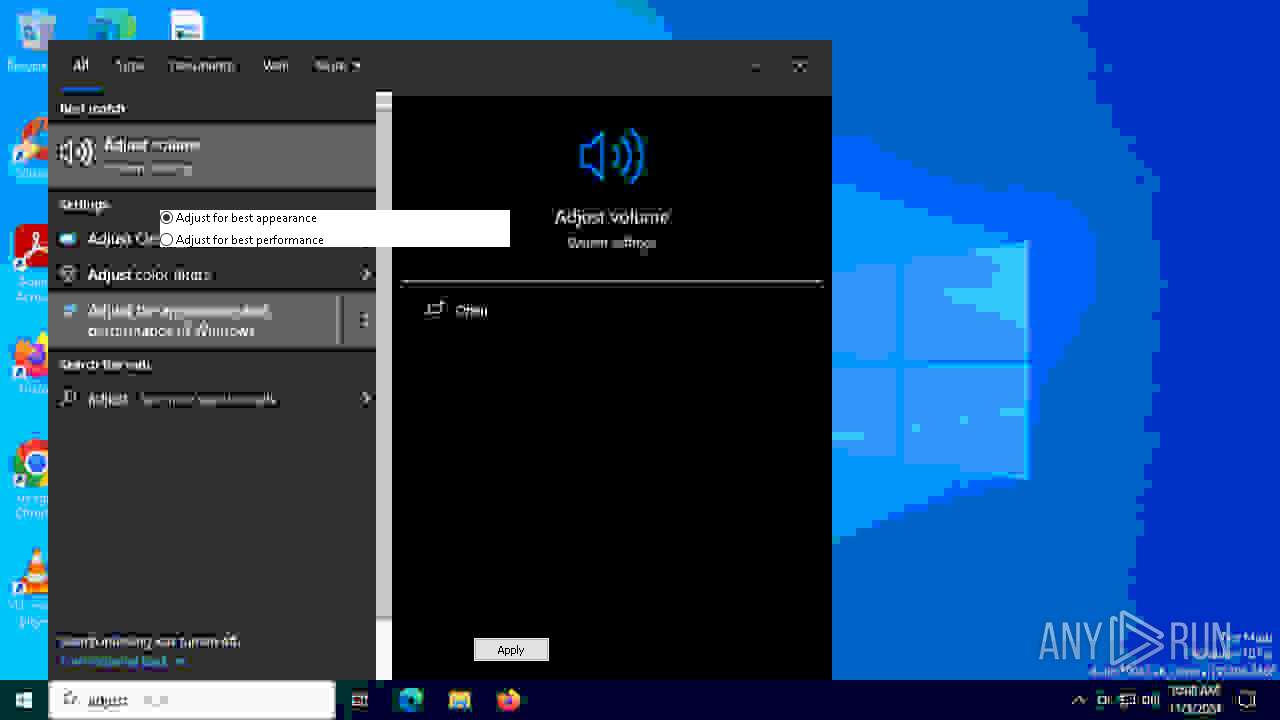
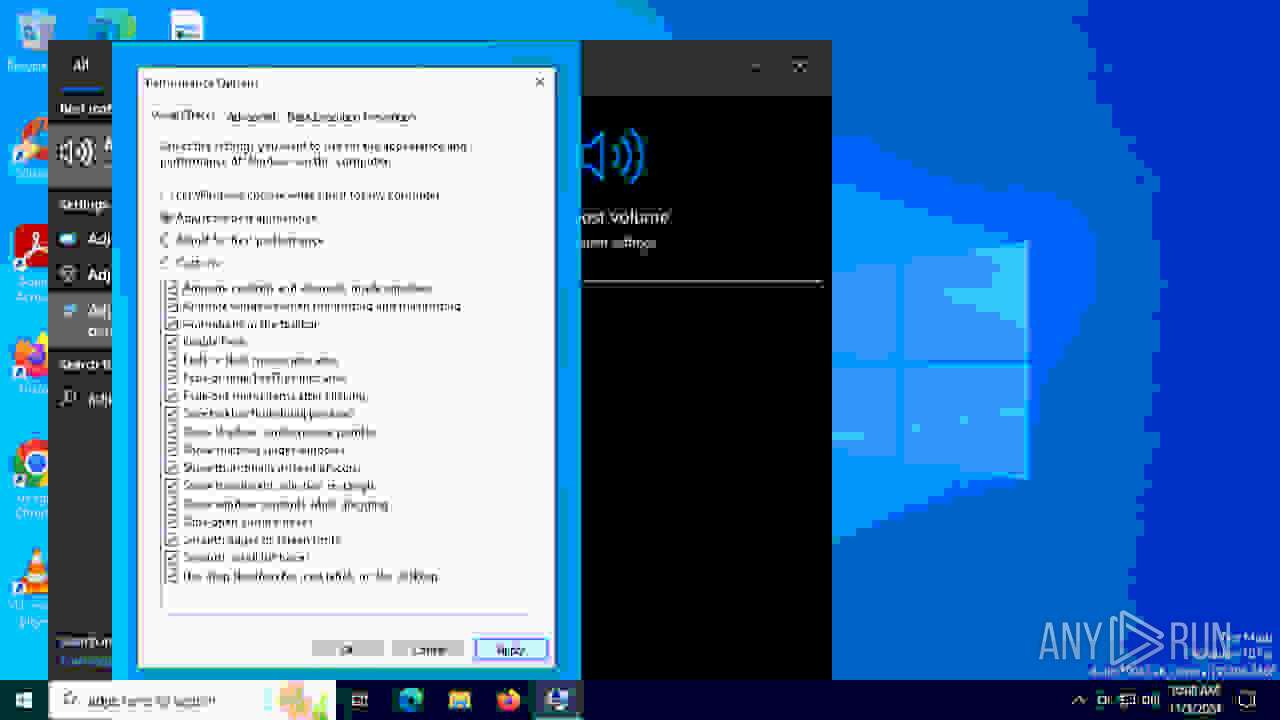
The process executes via Task Scheduler
- SystemPropertiesPerformance.exe (PID: 6768)
INFO
Process checks computer location settings
- Solaris.exe (PID: 5084)
Checks supported languages
- Solaris.exe (PID: 1396)
- Solaris.exe (PID: 6896)
- Solaris.exe (PID: 1748)
- Solaris.exe (PID: 4812)
- Solaris.exe (PID: 5084)
- Solaris.exe (PID: 6228)
- Solaris.exe (PID: 3108)
- Solaris.exe (PID: 2864)
The process uses the downloaded file
- Solaris.exe (PID: 5084)
Reads the computer name
- Solaris.exe (PID: 6896)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:06:08 20:02:05+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 111104 |
| InitializedDataSize: | 2967552 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xe4cb |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
153
Monitored processes
11
Malicious processes
1
Suspicious processes
0
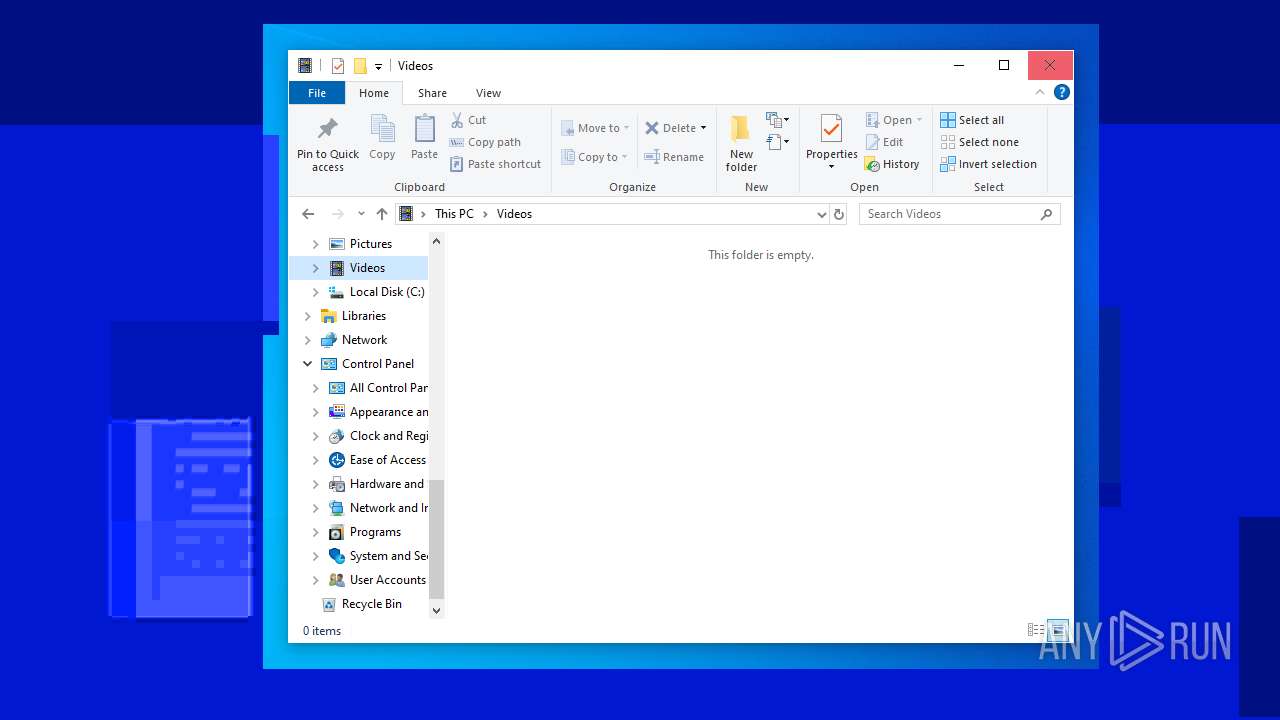
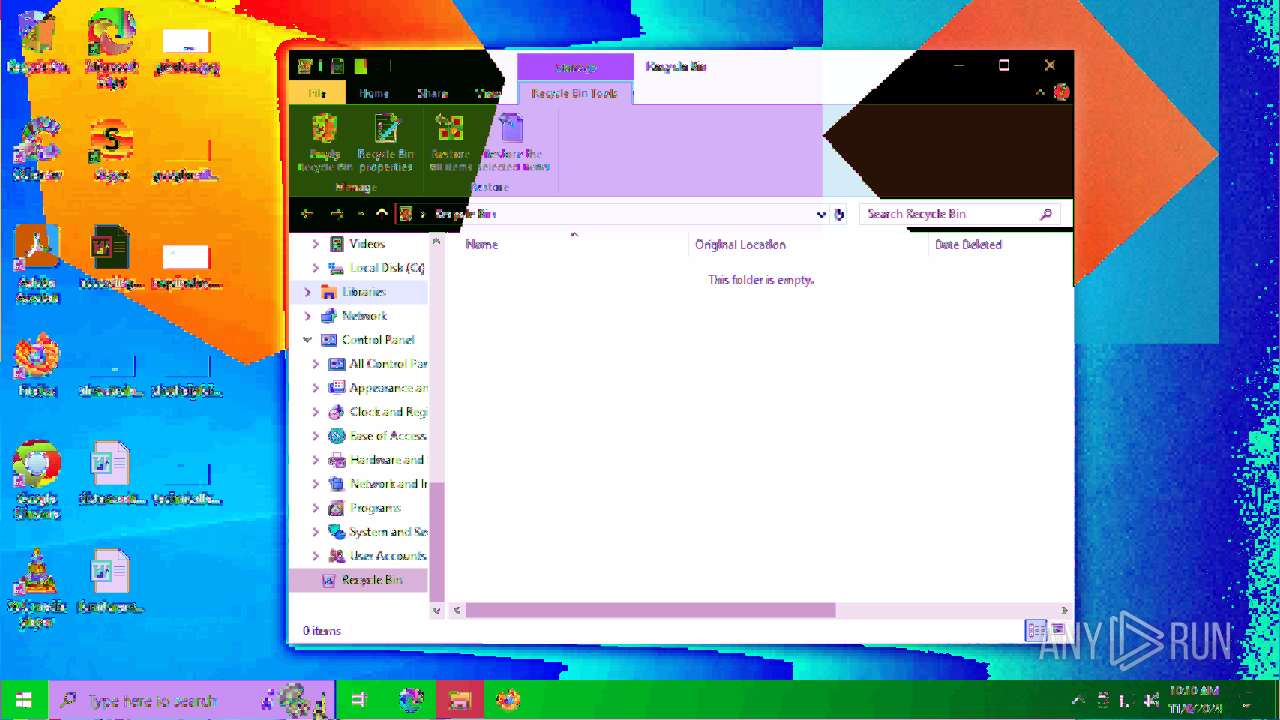
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1396 | "C:\Users\admin\AppData\Local\Temp\Solaris.exe" /watchdog | C:\Users\admin\AppData\Local\Temp\Solaris.exe | — | Solaris.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 1748 | "C:\Users\admin\AppData\Local\Temp\Solaris.exe" /watchdog | C:\Users\admin\AppData\Local\Temp\Solaris.exe | — | Solaris.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 2864 | "C:\Users\admin\AppData\Local\Temp\Solaris.exe" /watchdog | C:\Users\admin\AppData\Local\Temp\Solaris.exe | — | Solaris.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 3108 | "C:\Users\admin\AppData\Local\Temp\Solaris.exe" /watchdog | C:\Users\admin\AppData\Local\Temp\Solaris.exe | — | Solaris.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 3828 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4508 | "C:\Users\admin\AppData\Local\Temp\Solaris.exe" | C:\Users\admin\AppData\Local\Temp\Solaris.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 4812 | "C:\Users\admin\AppData\Local\Temp\Solaris.exe" /watchdog | C:\Users\admin\AppData\Local\Temp\Solaris.exe | — | Solaris.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 5084 | "C:\Users\admin\AppData\Local\Temp\Solaris.exe" | C:\Users\admin\AppData\Local\Temp\Solaris.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 6228 | "C:\Users\admin\AppData\Local\Temp\Solaris.exe" /watchdog | C:\Users\admin\AppData\Local\Temp\Solaris.exe | — | Solaris.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 6768 | "C:\WINDOWS\system32\SystemPropertiesPerformance.exe" | C:\Windows\System32\SystemPropertiesPerformance.exe | RuntimeBroker.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change Computer Performance Settings Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 182
Read events
1 180
Write events
2
Delete events
0
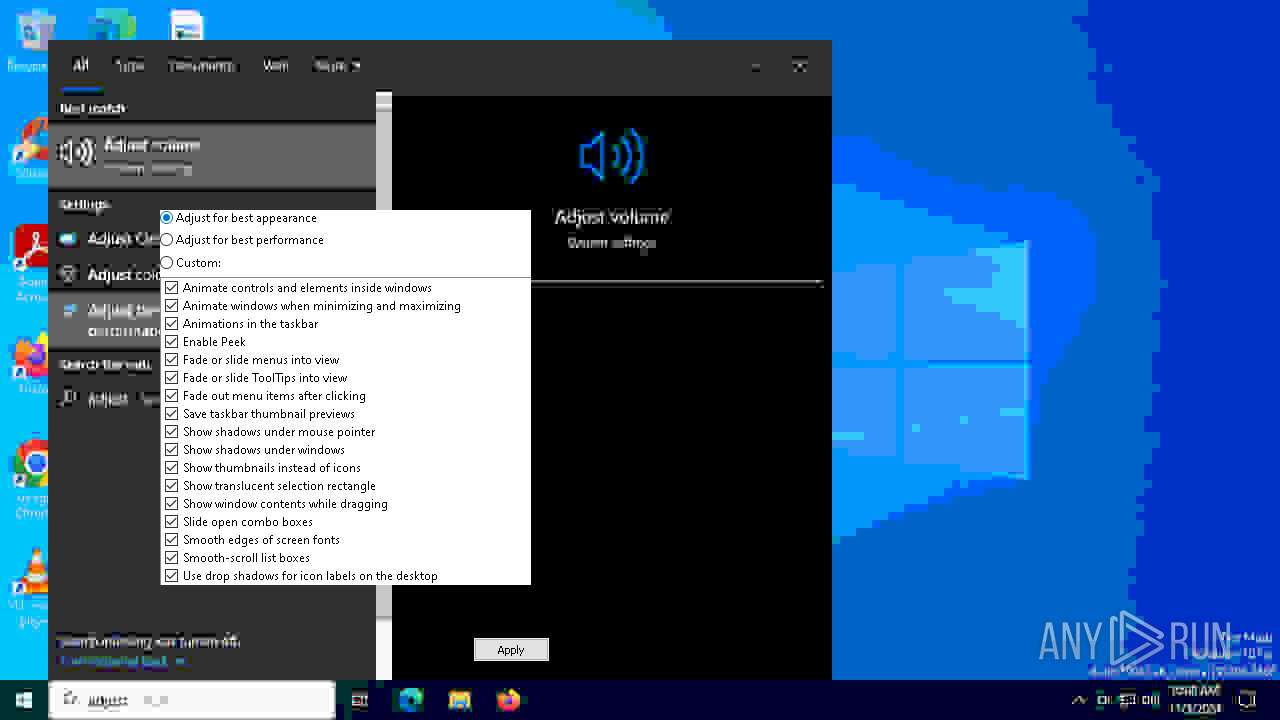
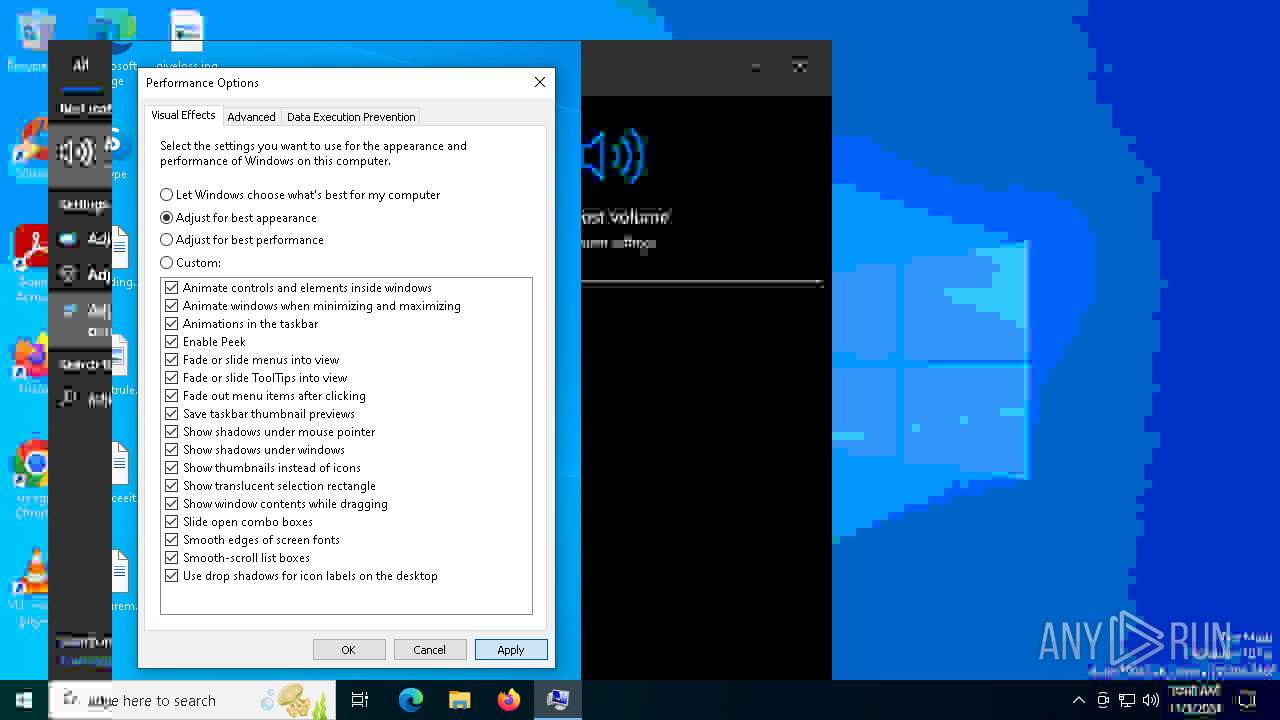
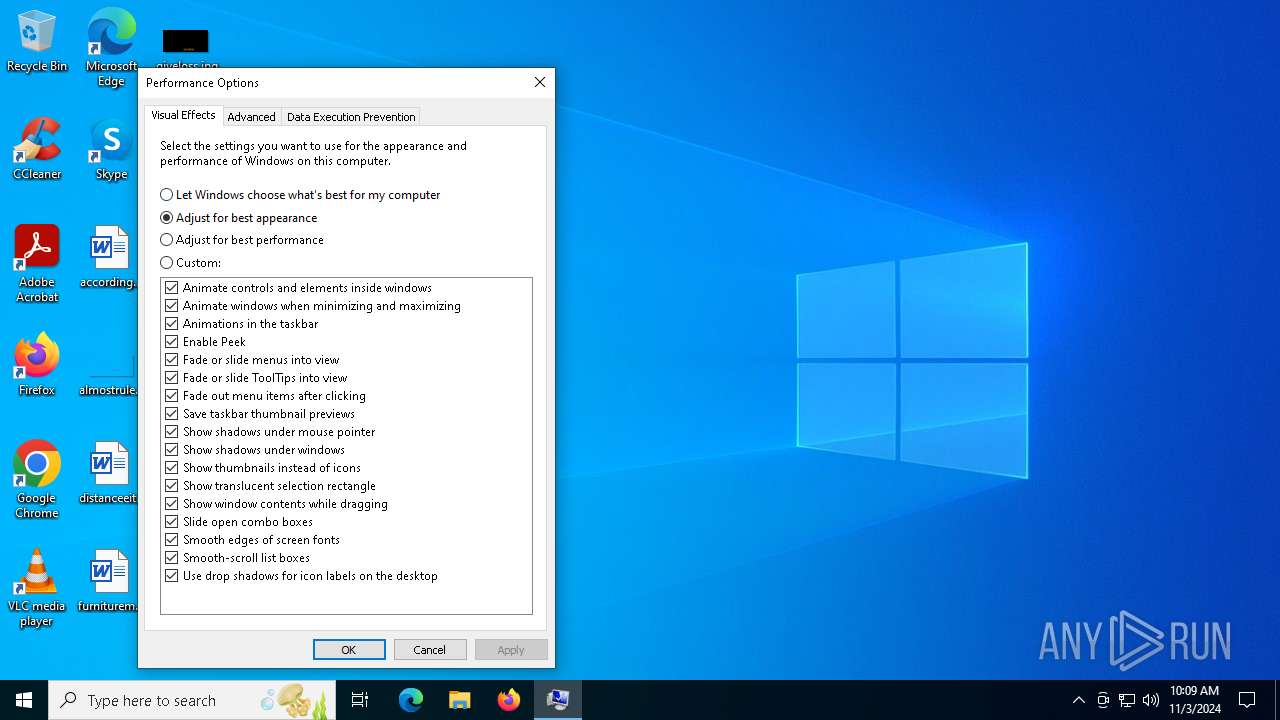
Modification events
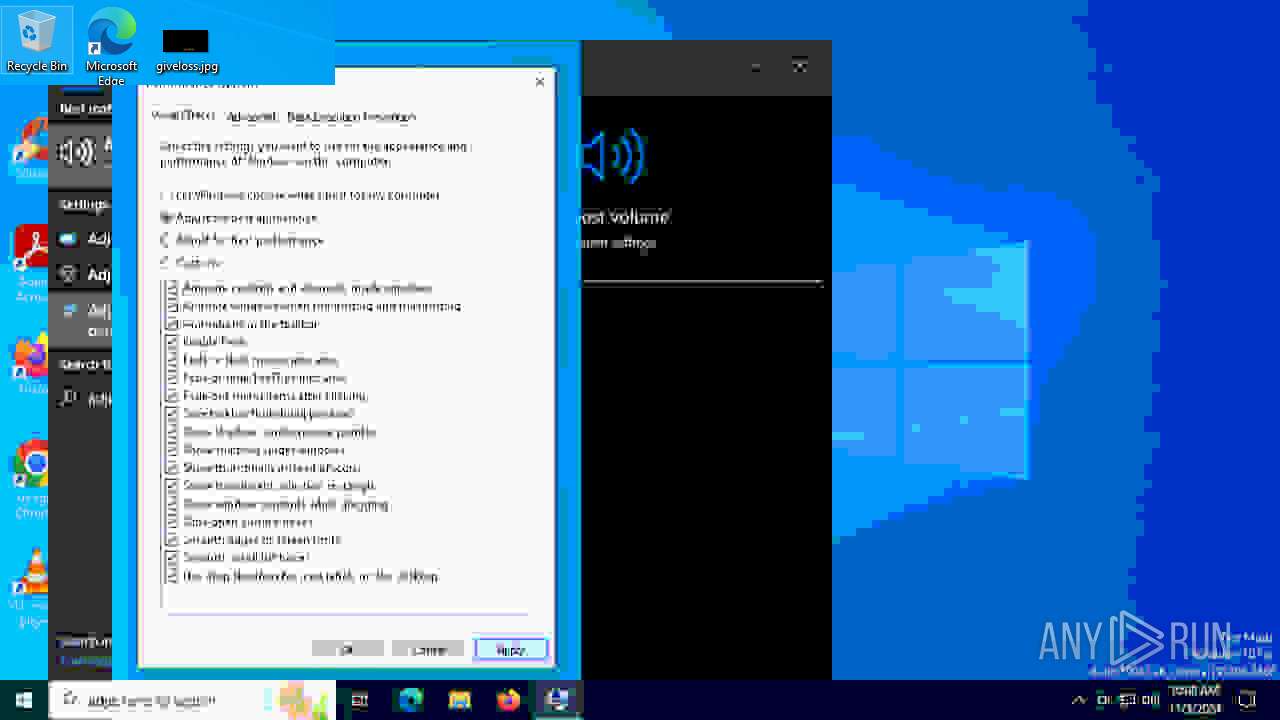
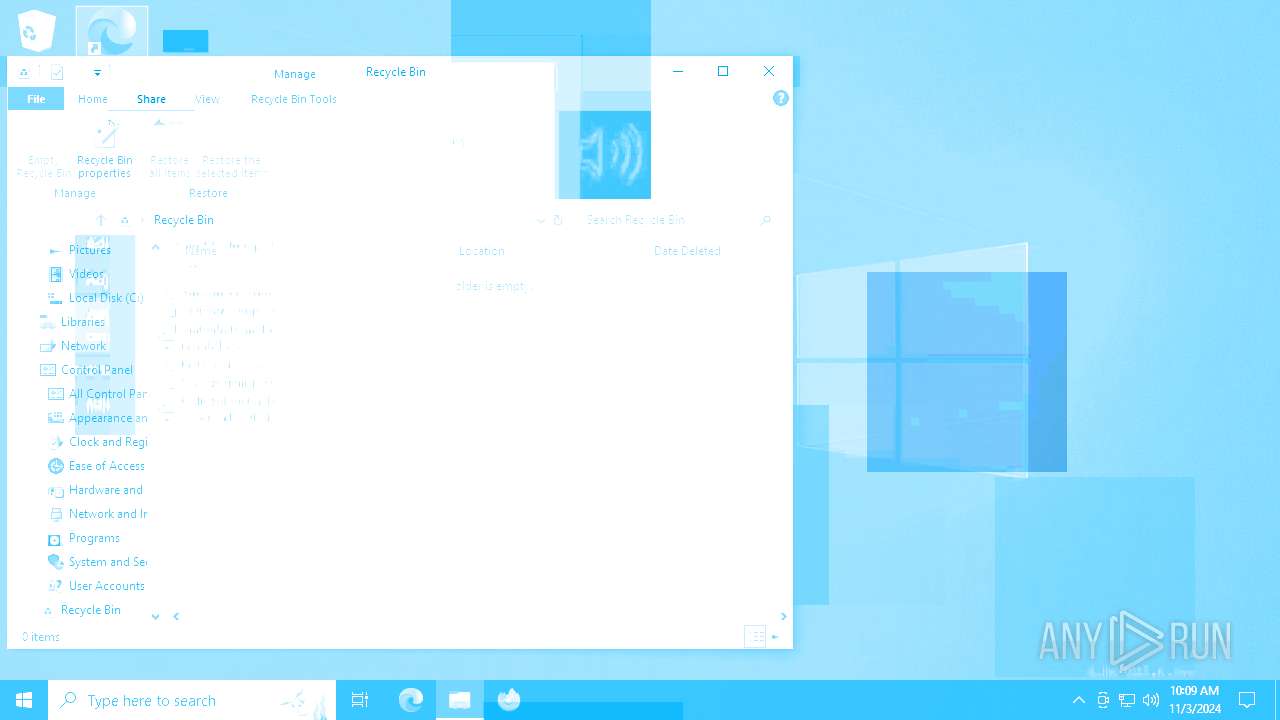
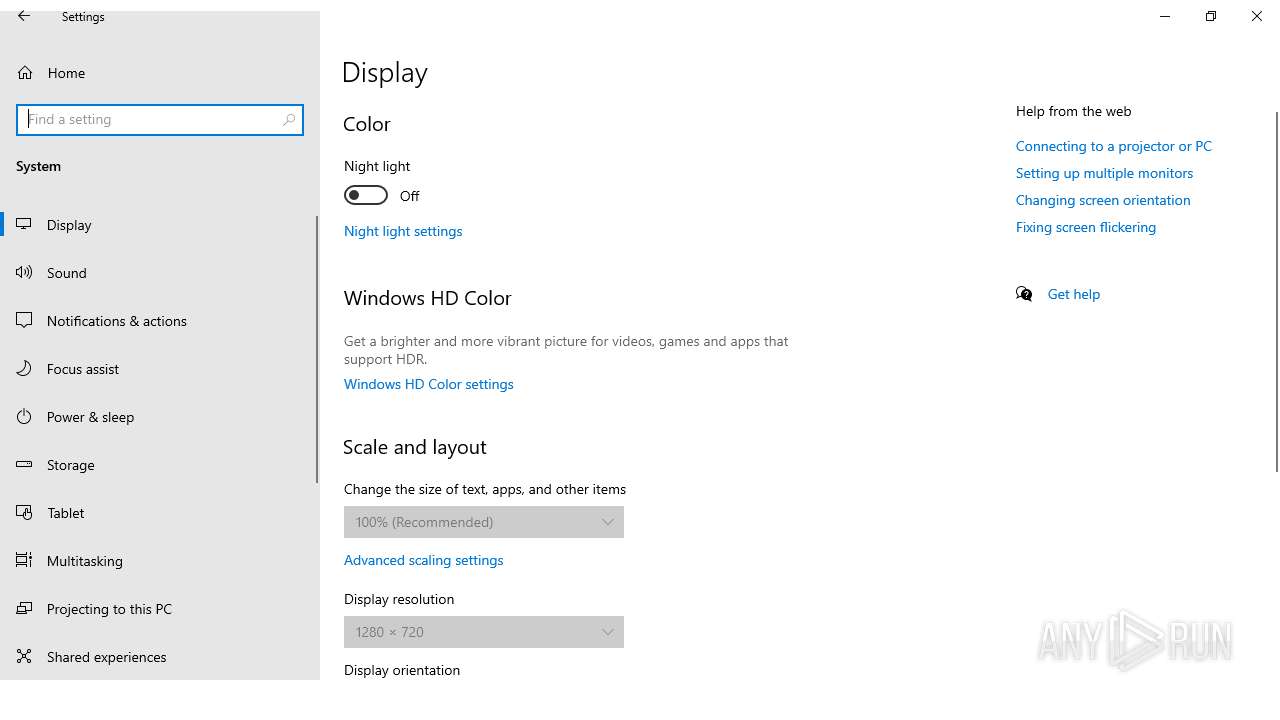
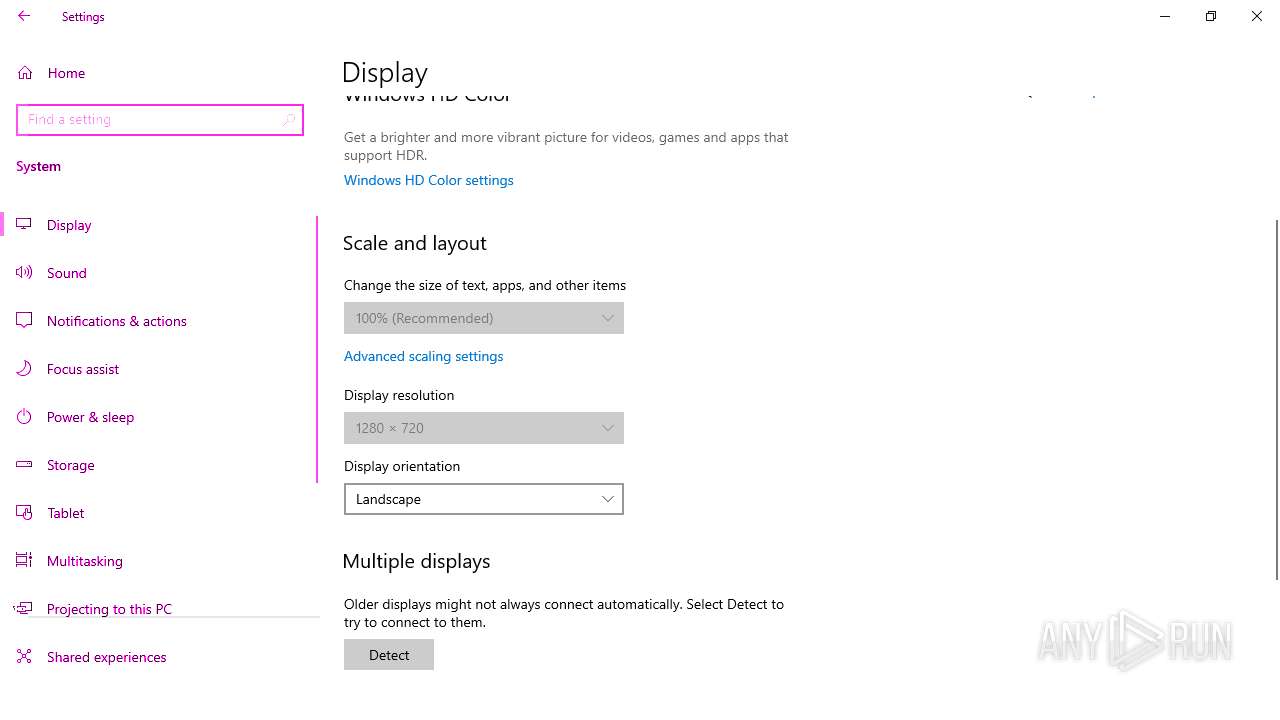
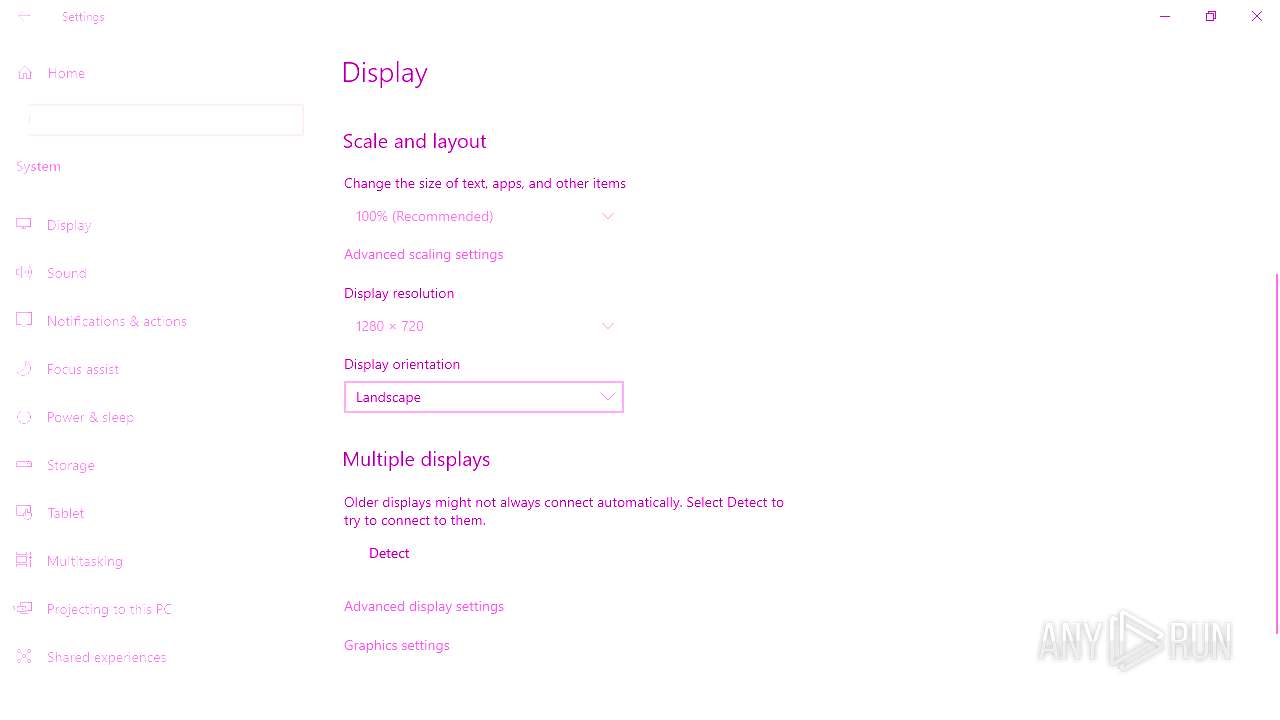
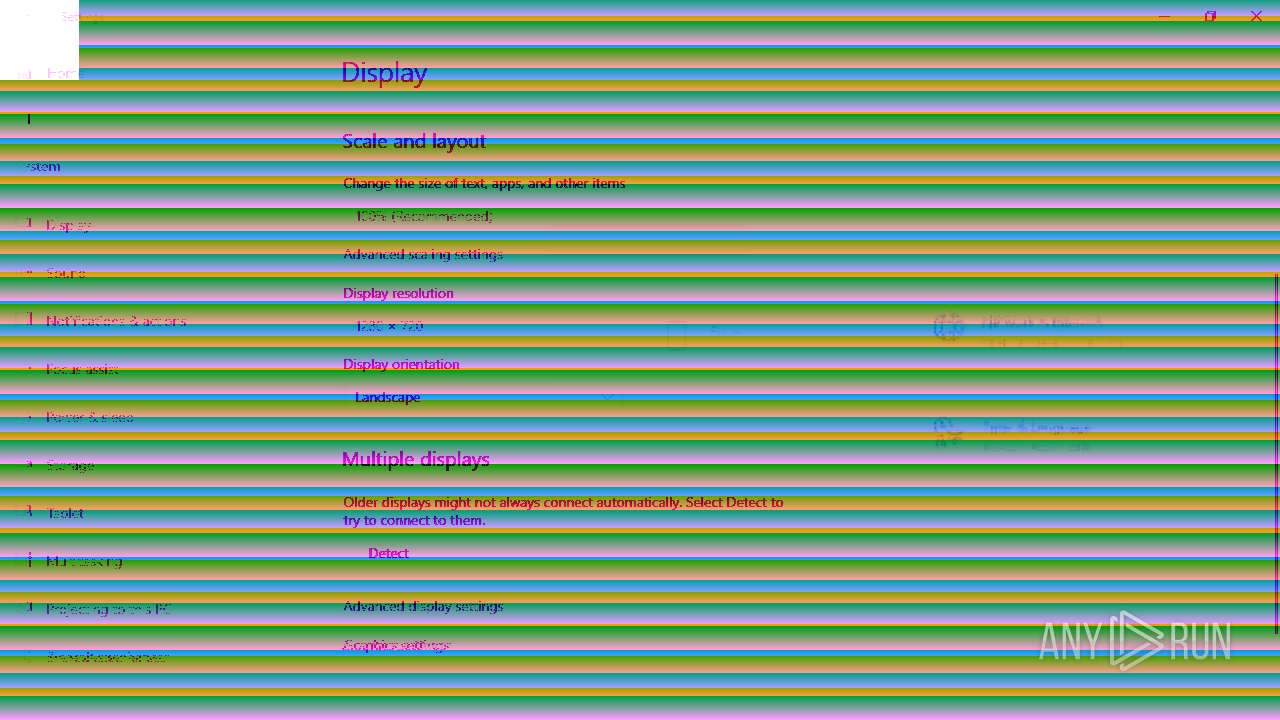
| (PID) Process: | (6768) SystemPropertiesPerformance.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | ShellState |
Value: 240000003728000000000000000000000000000001000000130000000000000062000000 | |||
| (PID) Process: | (6768) SystemPropertiesPerformance.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\VisualEffects |
| Operation: | write | Name: | VisualFXSetting |
Value: 1 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6896 | Solaris.exe | \Device\Harddisk0\DR0 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
58
DNS requests
31
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 313 b | whitelisted |
5600 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.37.237.227:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
2724 | SIHClient.exe | GET | 200 | 23.32.185.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | BR | binary | 418 b | whitelisted |
2724 | SIHClient.exe | GET | 200 | 23.32.185.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | BR | binary | 408 b | whitelisted |
4432 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | US | binary | 471 b | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | US | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6944 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
7060 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5488 | MoUsoCoreWorker.exe | 23.37.237.227:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4360 | SearchApp.exe | 2.16.204.144:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4360 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
r.bing.com |
| whitelisted |