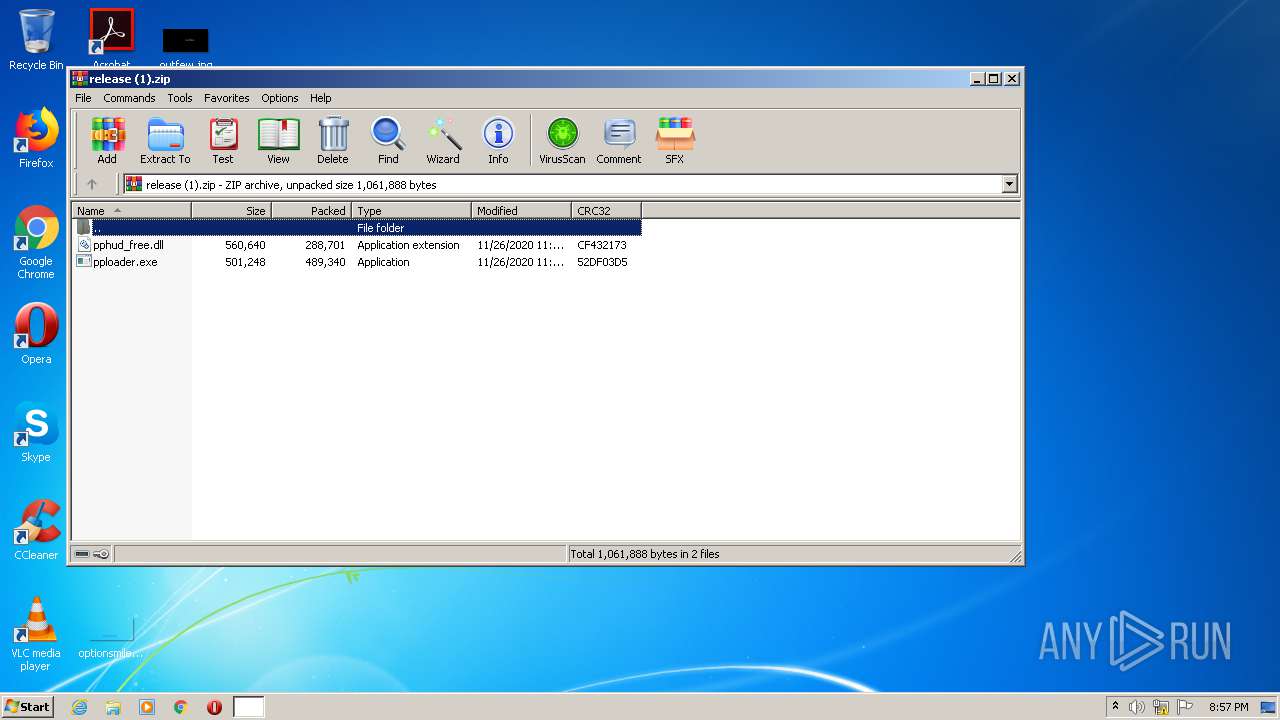
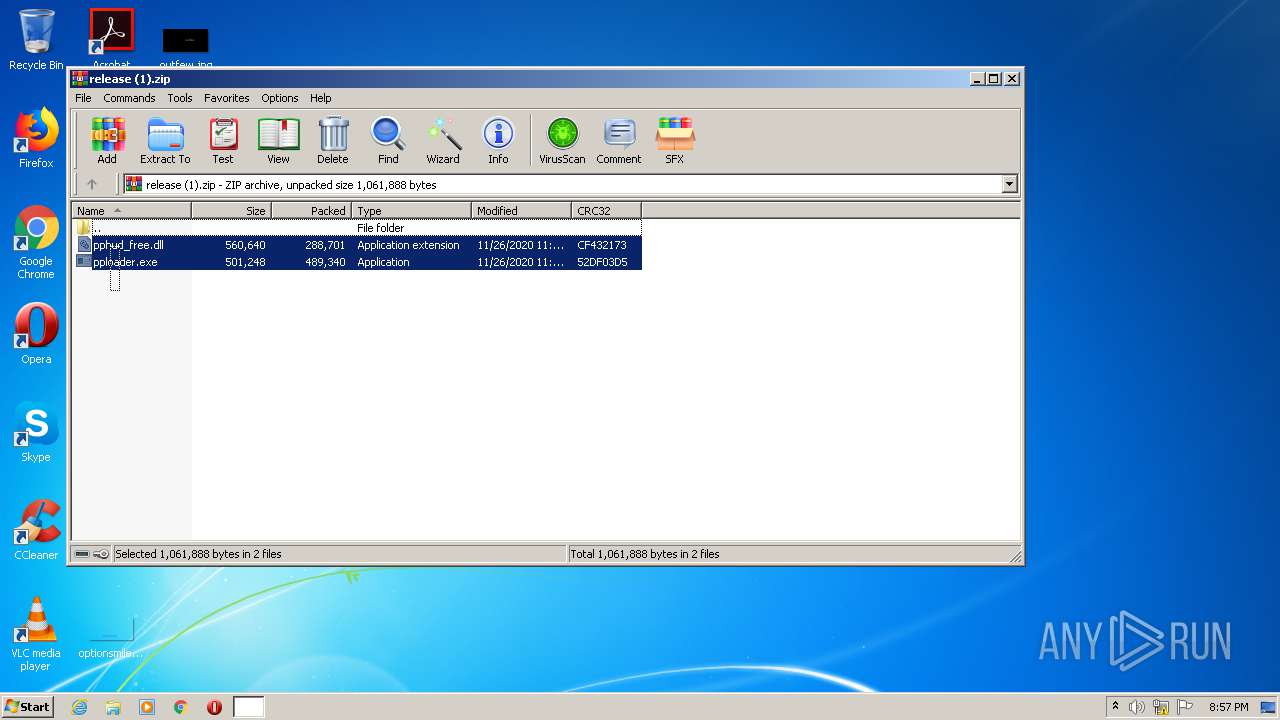
| File name: | release (1).zip |
| Full analysis: | https://app.any.run/tasks/9afb1a4e-6d2c-44ef-a0fd-424e6d4c0c18 |
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2020, 20:57:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 7532D5F7921827C7FE5BE728FF0D73C2 |
| SHA1: | 9565703FF884D756ABC5144BCC88C942215BEBD7 |
| SHA256: | B8C6CF8D262246A435CA46B903C8B499E4F1239D3B670109E33FD747CA4ABD68 |
| SSDEEP: | 12288:wt4M0IhSpL521QYYhjB9o6rzHZmZNvchQNZ97PdiXE6mEIHZmKRBz+gXqH3wVhND:wtj0zpL56fYhjB9o81hCr7sXPmpZmKme |
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3412)
Application was dropped or rewritten from another process
- pploader.exe (PID: 2612)
- pploader.exe (PID: 2140)
SUSPICIOUS
Creates files in the user directory
- pploader.exe (PID: 2612)
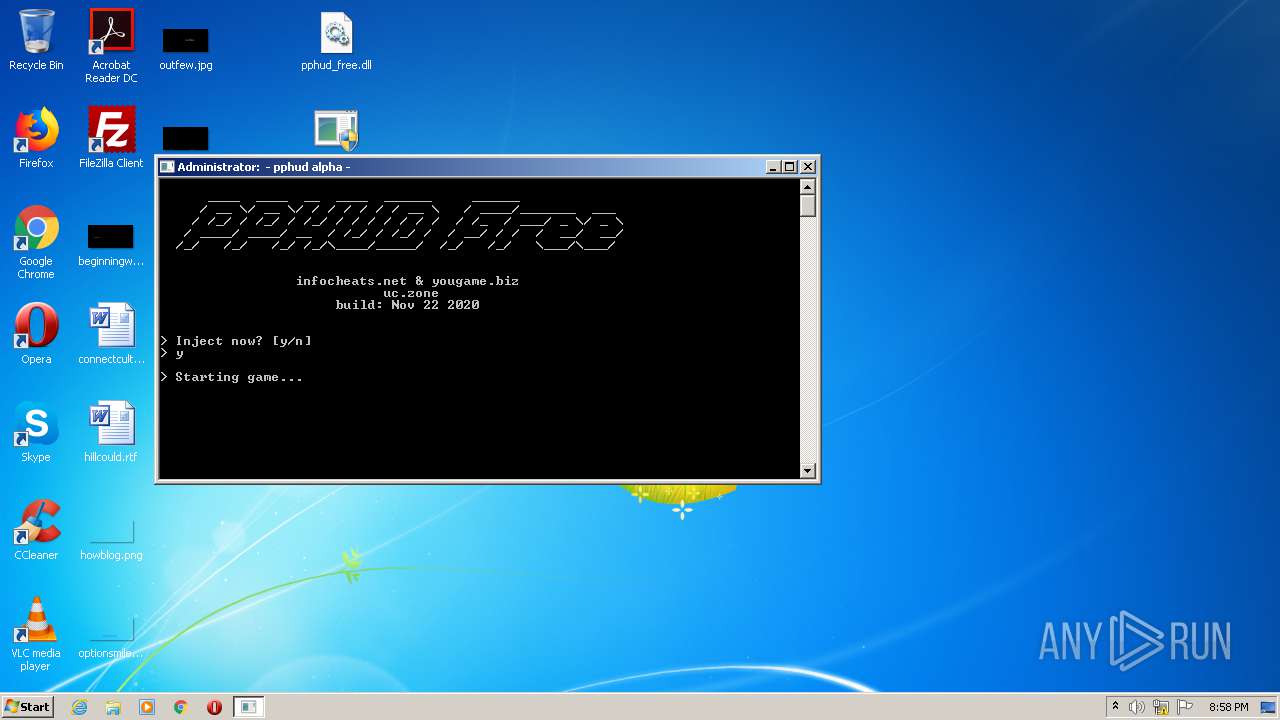
Starts CMD.EXE for commands execution
- pploader.exe (PID: 2612)
Uses RUNDLL32.EXE to load library
- pploader.exe (PID: 2612)
Drops a file with a compile date too recent
- pploader.exe (PID: 2612)
Executable content was dropped or overwritten
- pploader.exe (PID: 2612)
INFO
Manual execution by user
- pploader.exe (PID: 2612)
- pploader.exe (PID: 2140)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:11:26 16:15:21 |
| ZipCRC: | 0x52df03d5 |
| ZipCompressedSize: | 489340 |
| ZipUncompressedSize: | 501248 |
| ZipFileName: | pploader.exe |
Total processes
137
Monitored processes
100
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
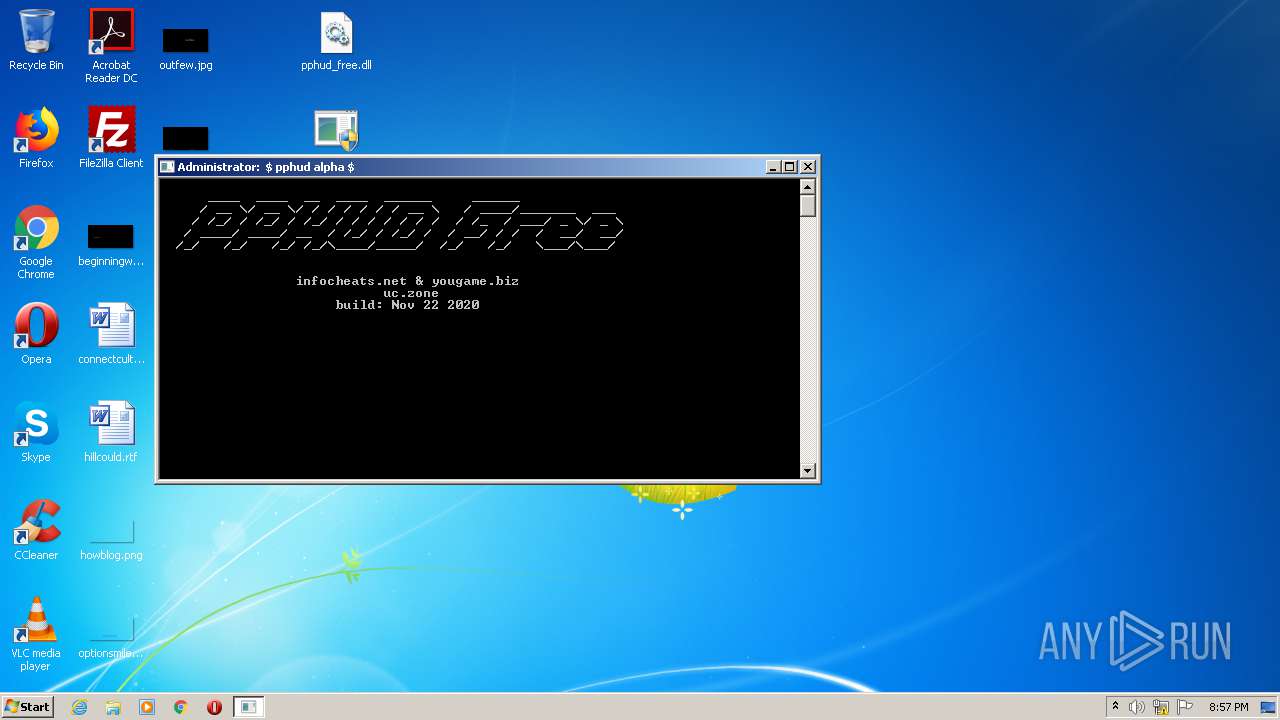
| 180 | C:\Windows\system32\cmd.exe /c title \ pphud alpha \ | C:\Windows\system32\cmd.exe | — | pploader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 616 | C:\Windows\system32\cmd.exe /c title - pphud alpha - | C:\Windows\system32\cmd.exe | — | pploader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 616 | C:\Windows\system32\cmd.exe /c title / pphud alpha / | C:\Windows\system32\cmd.exe | — | pploader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 700 | C:\Windows\system32\cmd.exe /c title / pphud alpha / | C:\Windows\system32\cmd.exe | — | pploader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 756 | C:\Windows\system32\cmd.exe /c title $ pphud alpha $ | C:\Windows\system32\cmd.exe | — | pploader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 936 | C:\Windows\system32\cmd.exe /c title - pphud alpha - | C:\Windows\system32\cmd.exe | — | pploader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 980 | C:\Windows\system32\cmd.exe /c title \ pphud alpha \ | C:\Windows\system32\cmd.exe | — | pploader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1308 | C:\Windows\system32\cmd.exe /c title / pphud alpha / | C:\Windows\system32\cmd.exe | — | pploader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1336 | C:\Windows\system32\cmd.exe /c title / pphud alpha / | C:\Windows\system32\cmd.exe | — | pploader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1348 | C:\Windows\system32\cmd.exe /c title \ pphud alpha \ | C:\Windows\system32\cmd.exe | — | pploader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 095
Read events
1 072
Write events
23
Delete events
0
Modification events
| (PID) Process: | (2696) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2696) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2696) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2696) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\release (1).zip | |||
| (PID) Process: | (2696) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2696) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2696) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2696) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2696) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (2696) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\AppData\Local\Temp | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
1
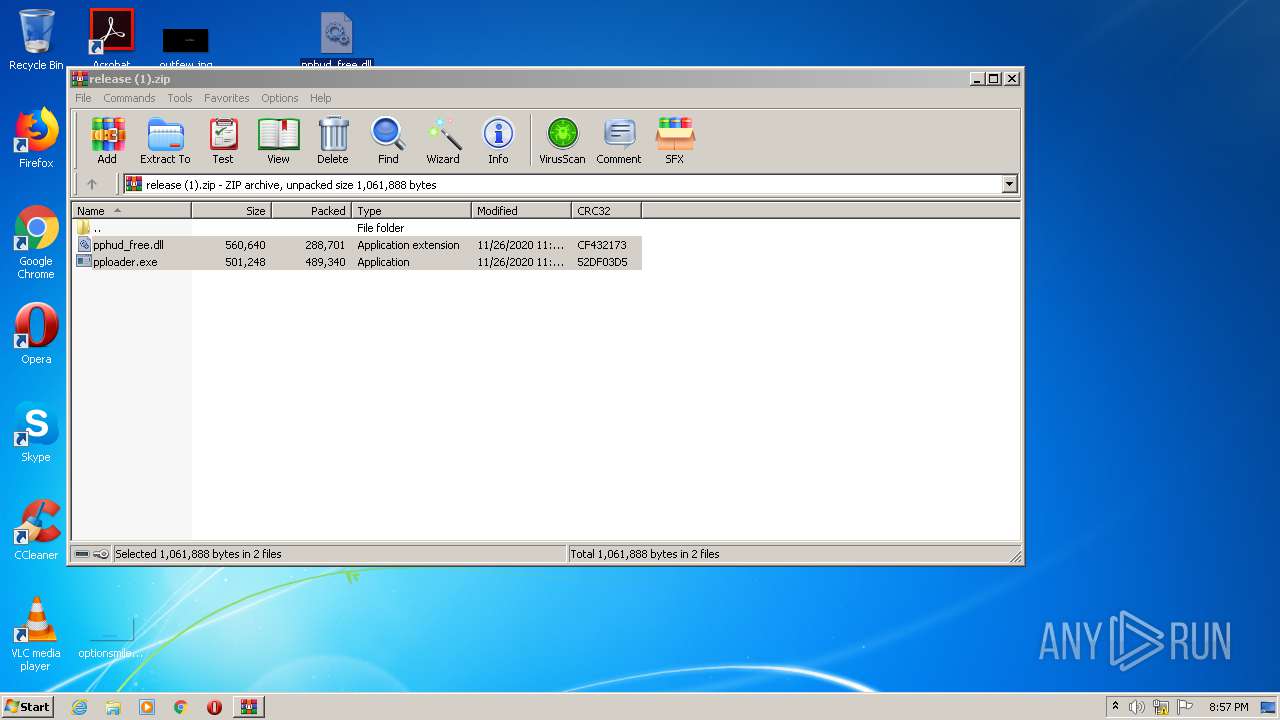
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2696 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2696.27285\pploader.exe | — | |
MD5:— | SHA256:— | |||
| 2696 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2696.27285\pphud_free.dll | — | |
MD5:— | SHA256:— | |||
| 2612 | pploader.exe | C:\Users\admin\AppData\Roaming\pphud-temp\super.dll | executable | |
MD5:— | SHA256:— | |||
| 2612 | pploader.exe | C:\Users\admin\AppData\Roaming\pphud-temp\temp.mid | mid | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report