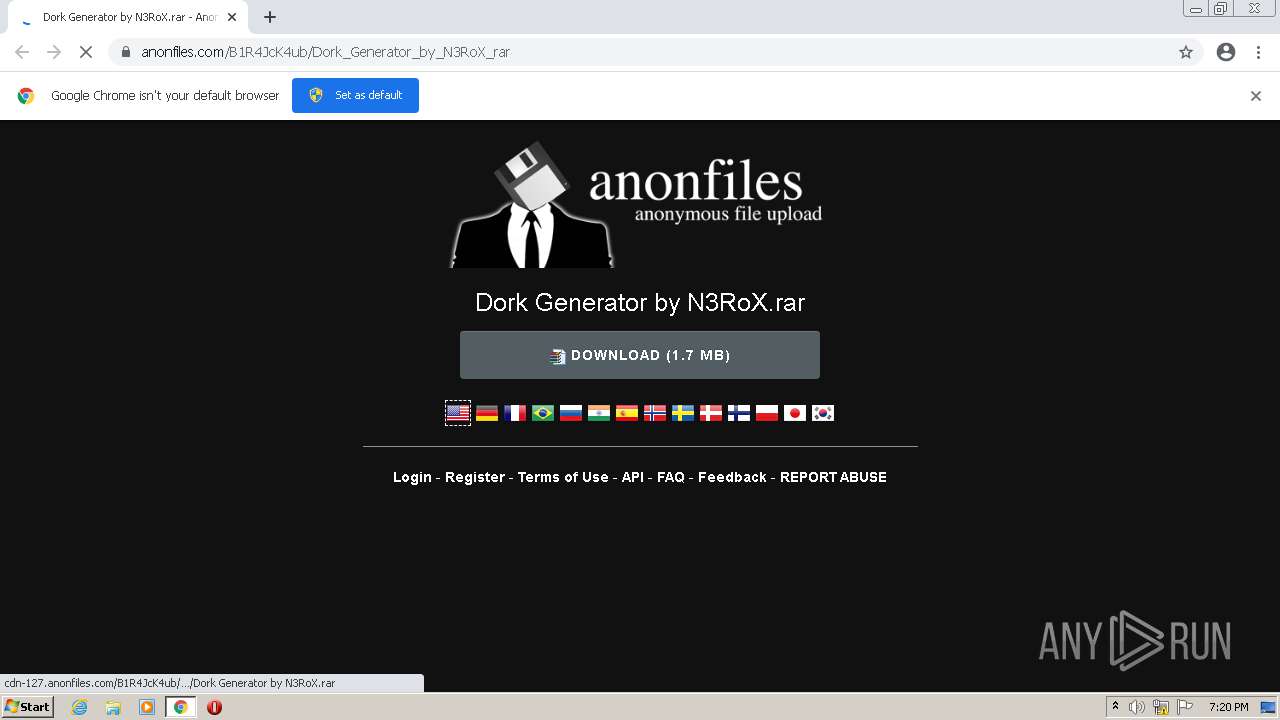
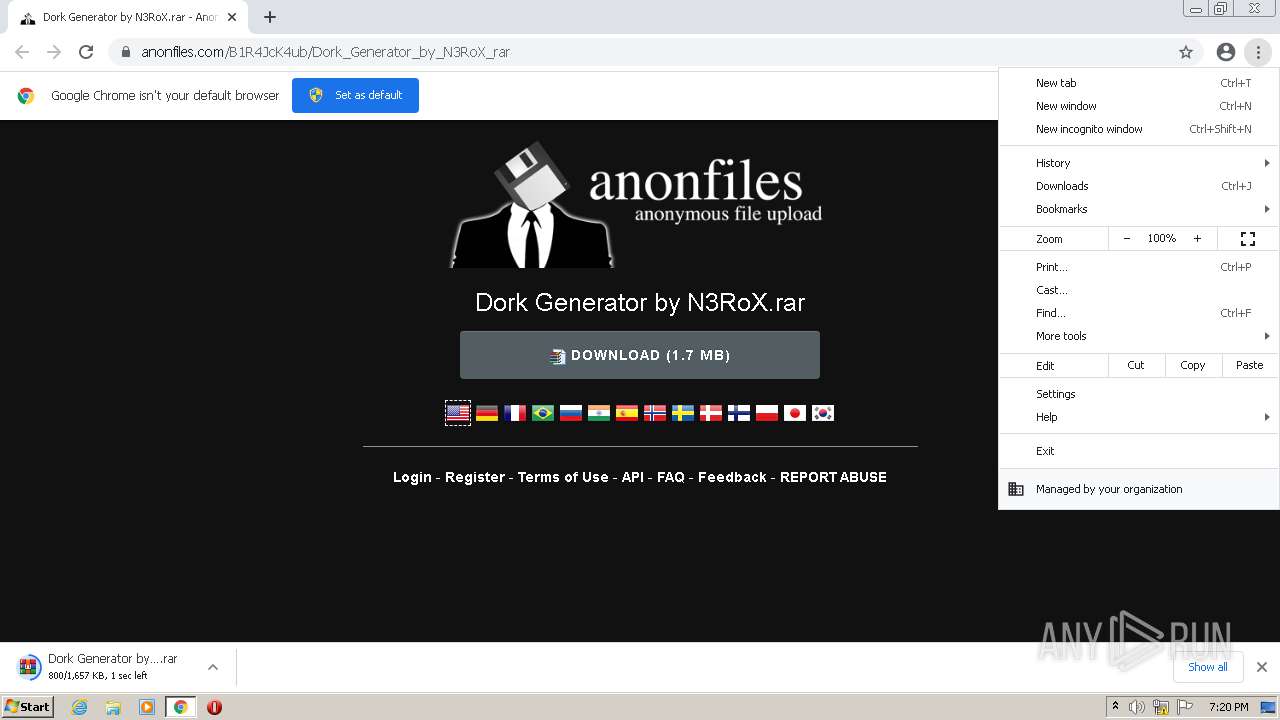
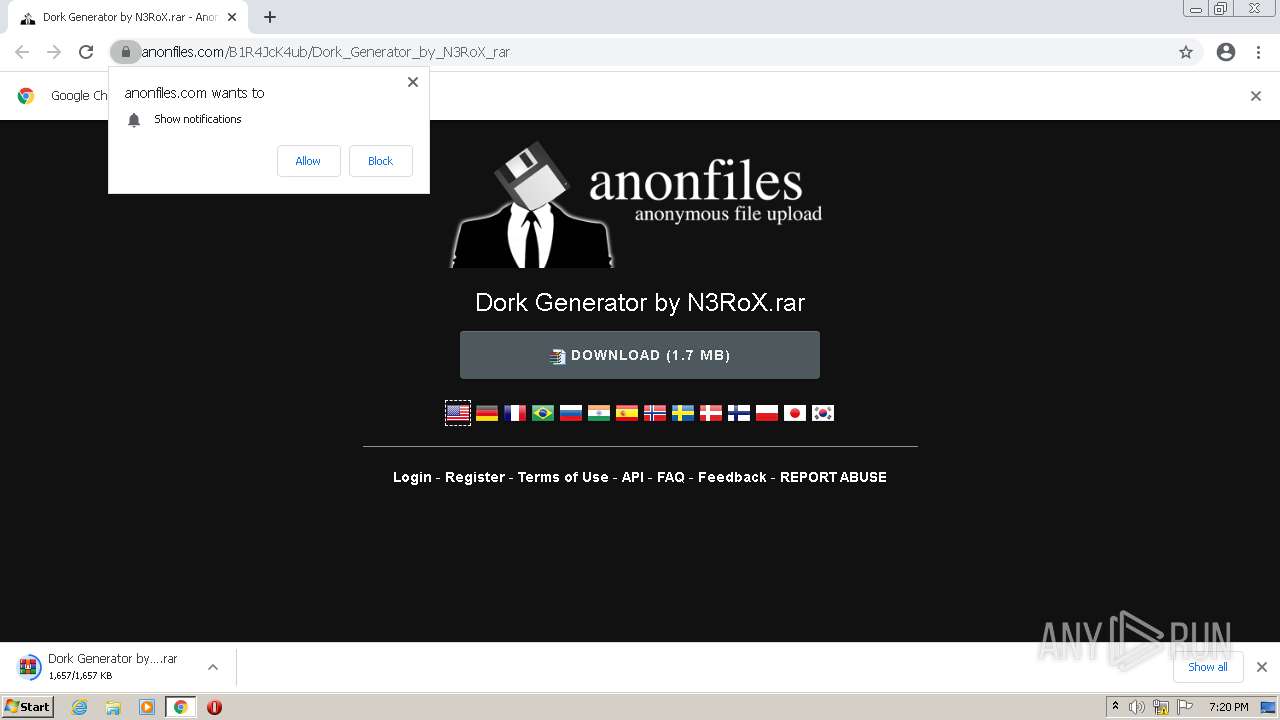
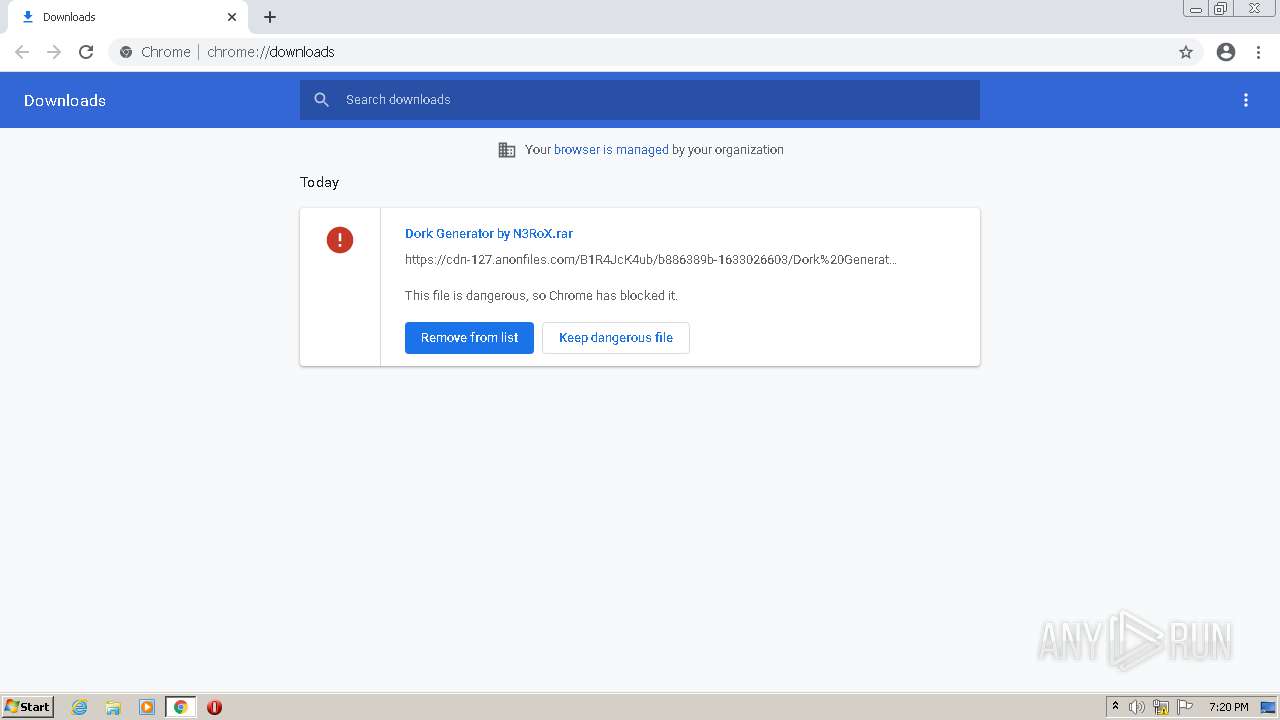
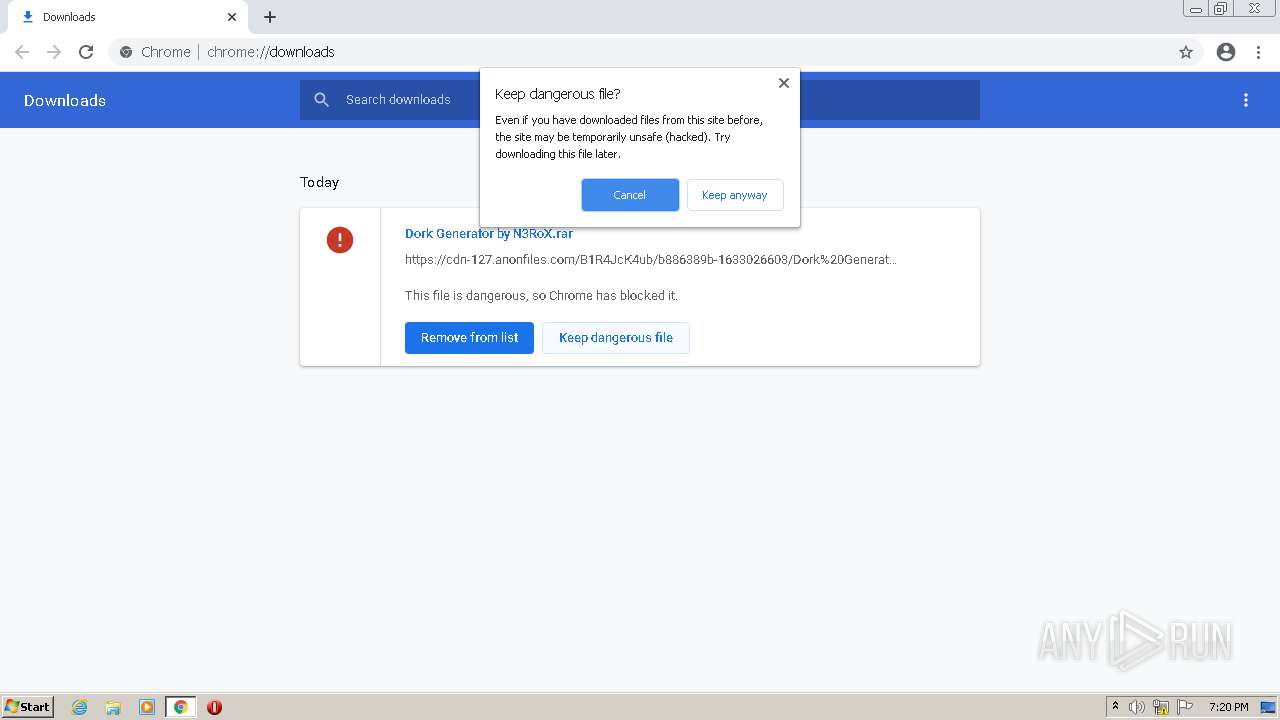
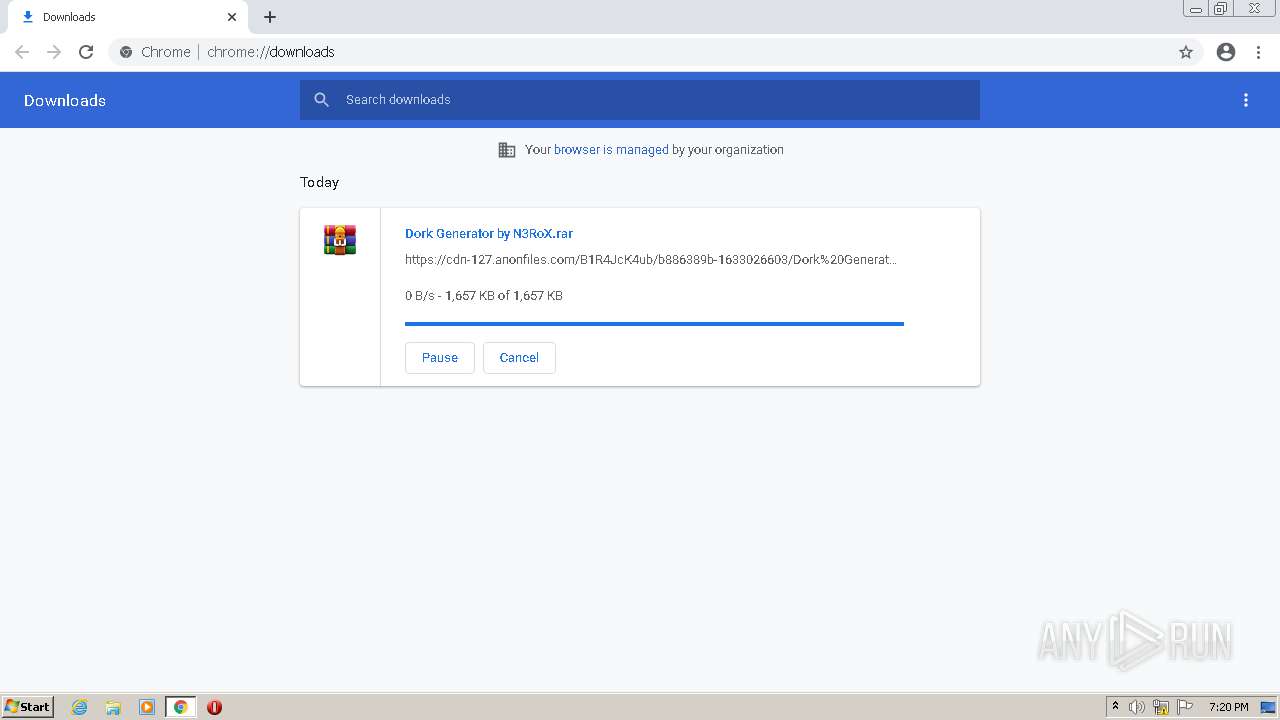
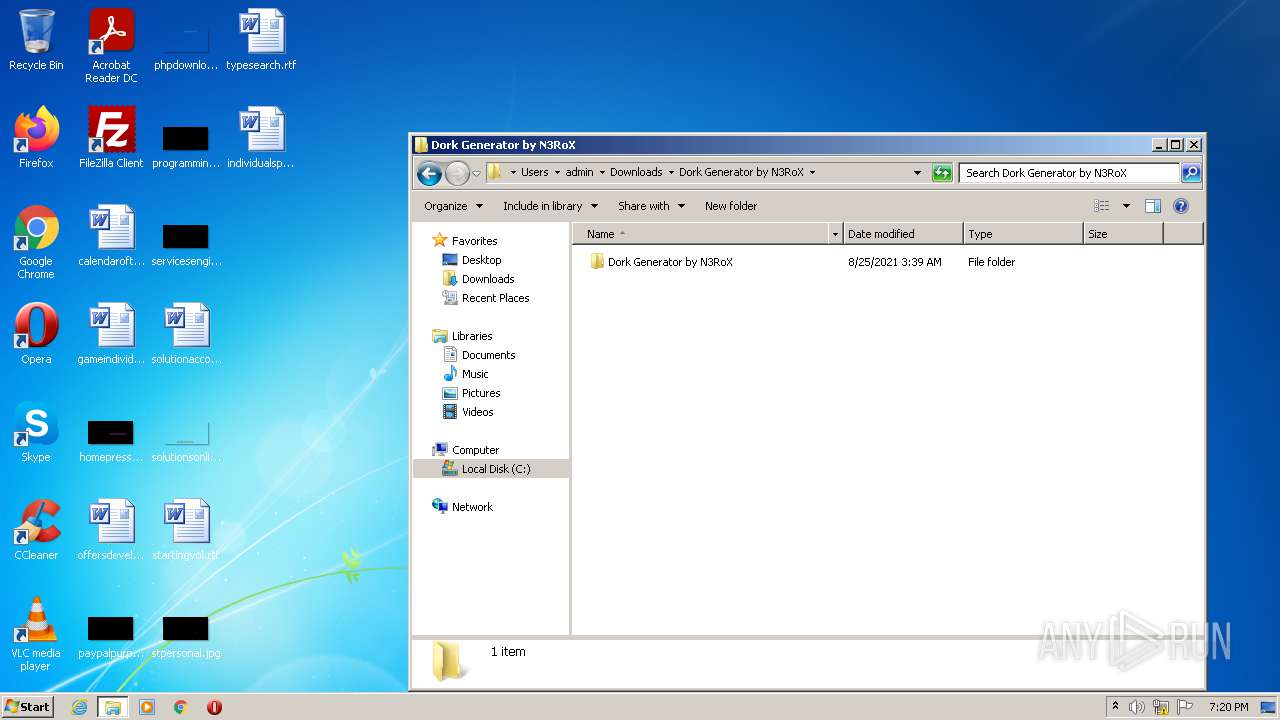
| URL: | https://anonfiles.com/B1R4JcK4ub/Dork_Generator_by_N3RoX_rar |
| Full analysis: | https://app.any.run/tasks/9757385e-790c-4e40-a876-5881e25d9c40 |
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2021, 18:19:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 0CA457347D636333E3A9E3B57A27DD99 |
| SHA1: | F817EB95D46A969F9C46AD94D2559B2C7EE74D74 |
| SHA256: | B8C3E9CEFB92A363E66395A55EC7956FEF474BCE43C5E39937FD67286F75782D |
| SSDEEP: | 3:N8M2DvGeQH6M1fX:2M2Dee/OfX |
MALICIOUS
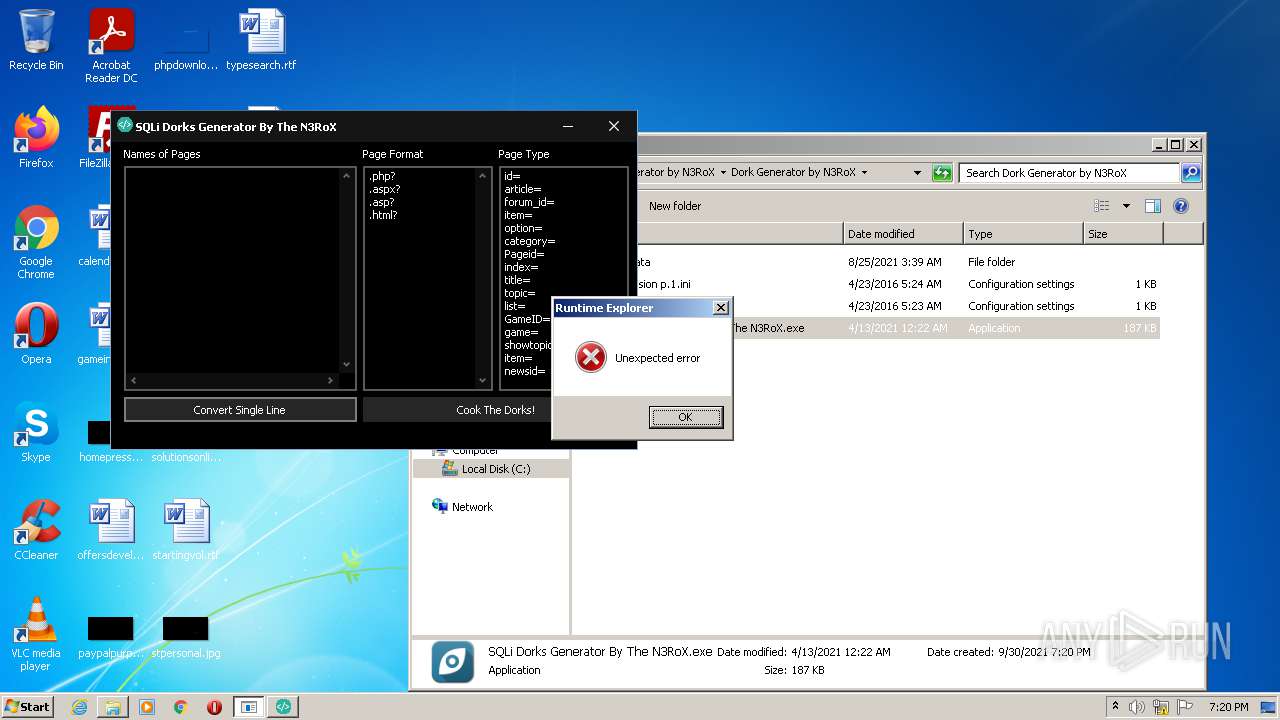
Drops executable file immediately after starts
- WinRAR.exe (PID: 2264)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 2552)
- Launcher.exe (PID: 4000)
Application was dropped or rewritten from another process
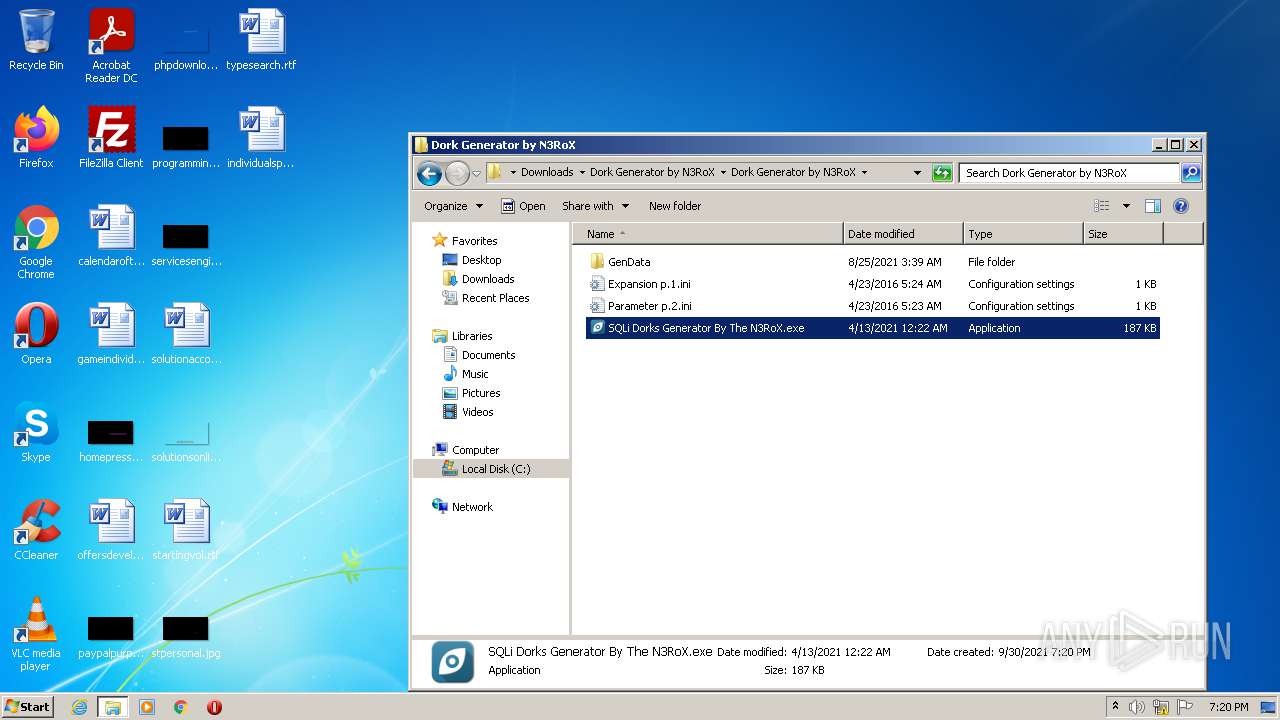
- SQLi Dorks Generator By The N3RoX.exe (PID: 3448)
- Launcher.exe (PID: 4000)
- SQLi.exe (PID: 2504)
- Runtime Explorer.exe (PID: 2460)
- Secure System Shell.exe (PID: 968)
- Windows Services.exe (PID: 3632)
Writes to a start menu file
- Launcher.exe (PID: 4000)
Changes the autorun value in the registry
- Launcher.exe (PID: 4000)
SUSPICIOUS
Reads the computer name
- WinRAR.exe (PID: 2264)
- Launcher.exe (PID: 4000)
- SQLi Dorks Generator By The N3RoX.exe (PID: 3448)
- SQLi.exe (PID: 2504)
- Windows Services.exe (PID: 3632)
- Secure System Shell.exe (PID: 968)
- powershell.exe (PID: 2780)
Checks supported languages
- WinRAR.exe (PID: 2264)
- Launcher.exe (PID: 4000)
- powershell.exe (PID: 2780)
- SQLi Dorks Generator By The N3RoX.exe (PID: 3448)
- SQLi.exe (PID: 2504)
- Runtime Explorer.exe (PID: 2460)
- Windows Services.exe (PID: 3632)
- Secure System Shell.exe (PID: 968)
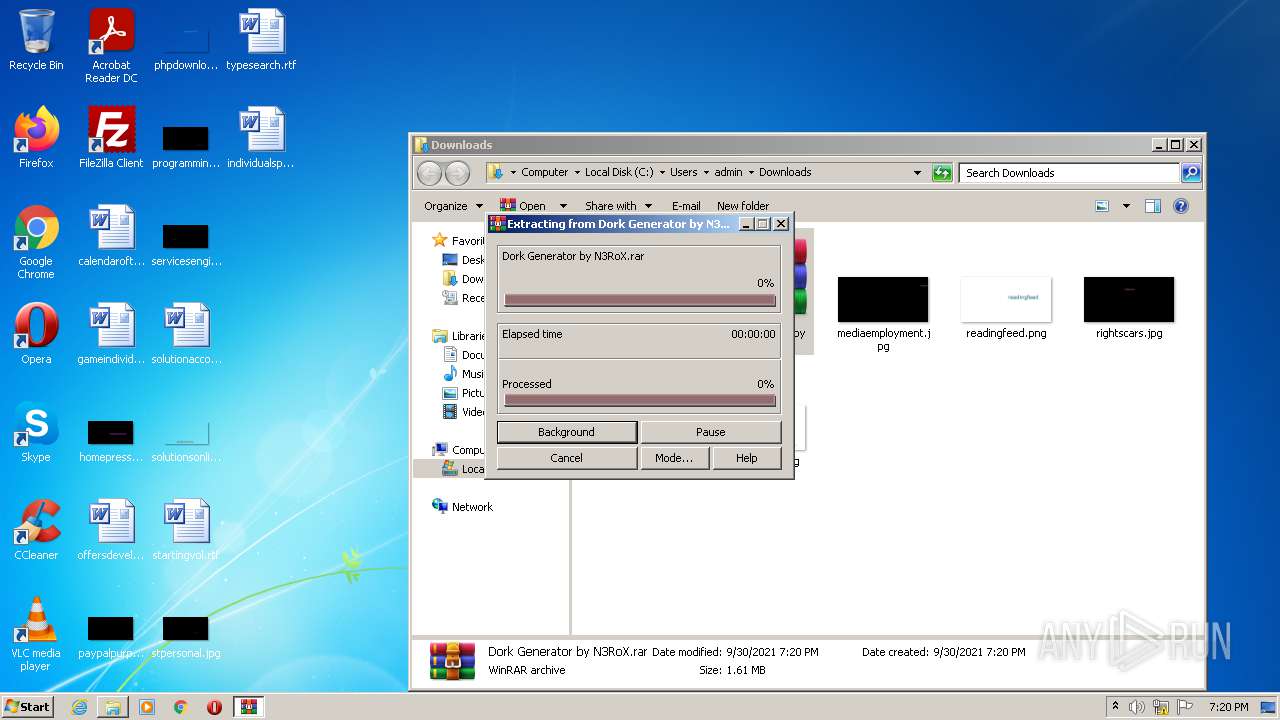
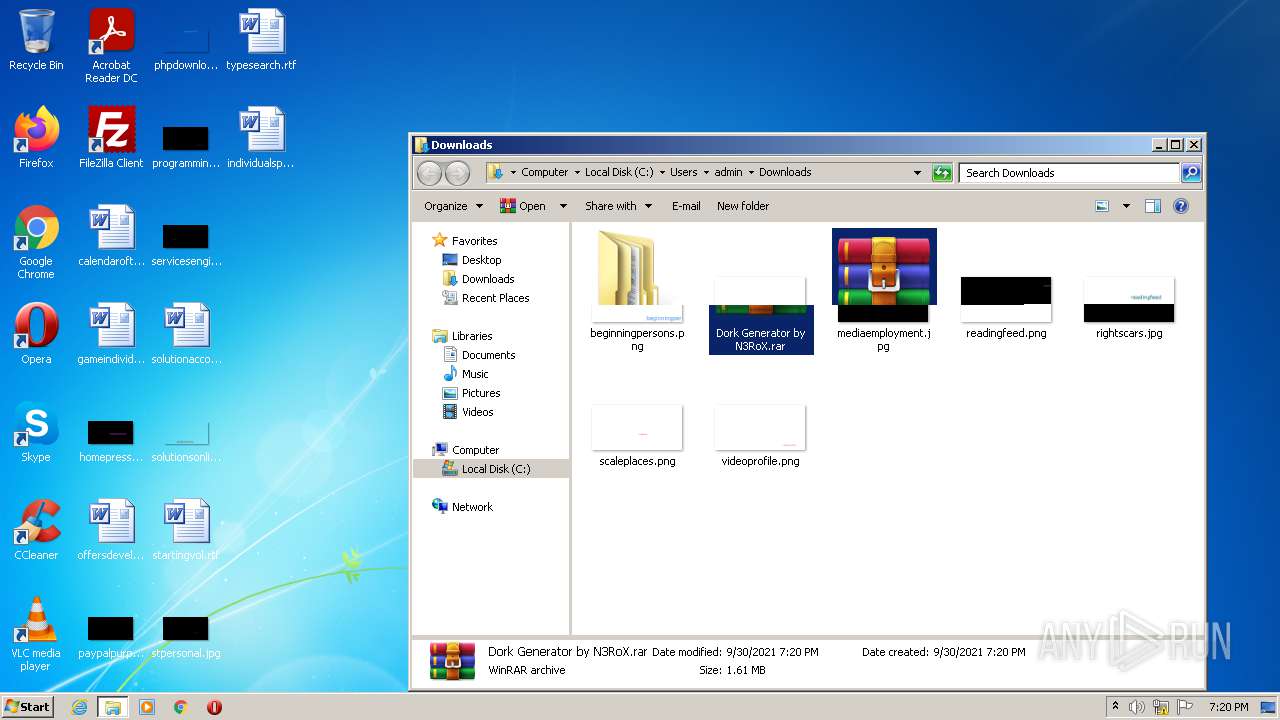
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2264)
- Launcher.exe (PID: 4000)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 2264)
Executes PowerShell scripts
- Launcher.exe (PID: 4000)
Reads the date of Windows installation
- powershell.exe (PID: 2780)
Creates files in the Windows directory
- Launcher.exe (PID: 4000)
Creates files in the user directory
- Launcher.exe (PID: 4000)
- powershell.exe (PID: 2780)
INFO
Reads the computer name
- chrome.exe (PID: 3348)
- chrome.exe (PID: 3312)
- chrome.exe (PID: 1040)
- chrome.exe (PID: 2664)
- chrome.exe (PID: 3628)
- chrome.exe (PID: 1028)
Checks supported languages
- chrome.exe (PID: 3076)
- chrome.exe (PID: 1040)
- chrome.exe (PID: 3636)
- chrome.exe (PID: 3260)
- chrome.exe (PID: 1028)
- chrome.exe (PID: 3348)
- chrome.exe (PID: 3312)
- chrome.exe (PID: 3628)
- chrome.exe (PID: 2664)
- chrome.exe (PID: 2920)
- chrome.exe (PID: 1284)
- chrome.exe (PID: 4076)
Reads the hosts file
- chrome.exe (PID: 2664)
- chrome.exe (PID: 3348)
Application launched itself
- chrome.exe (PID: 2664)
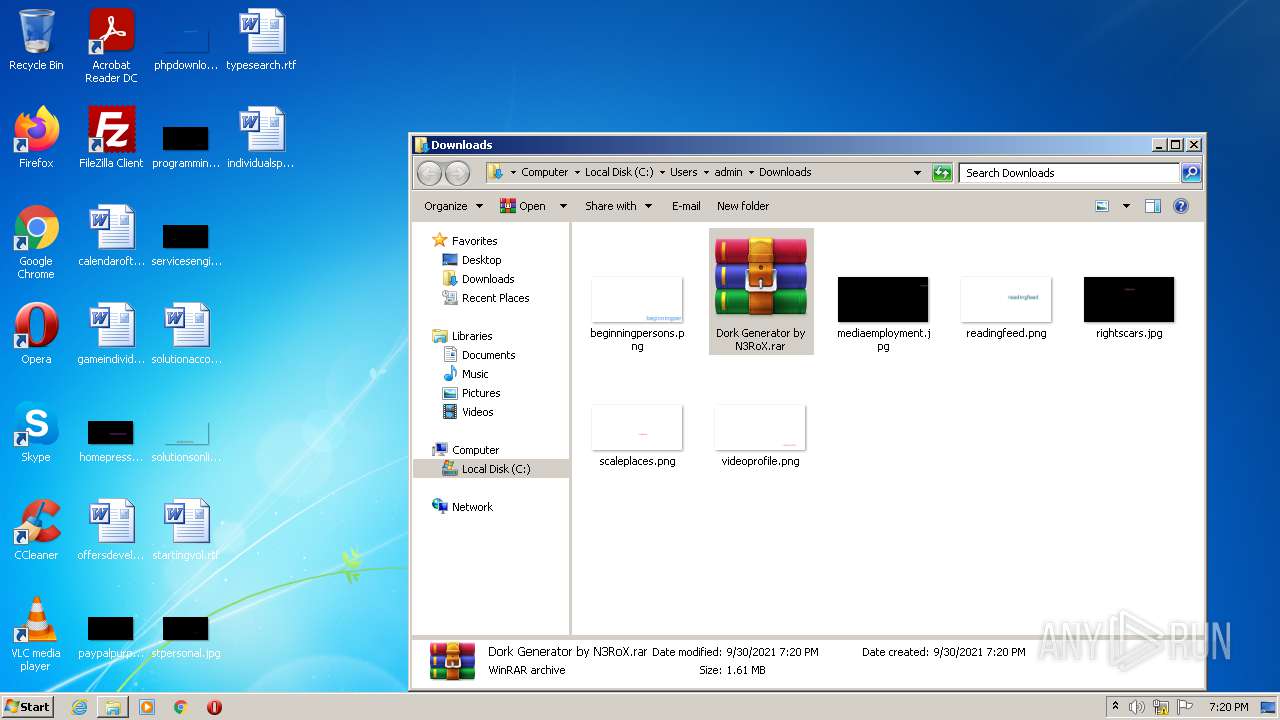
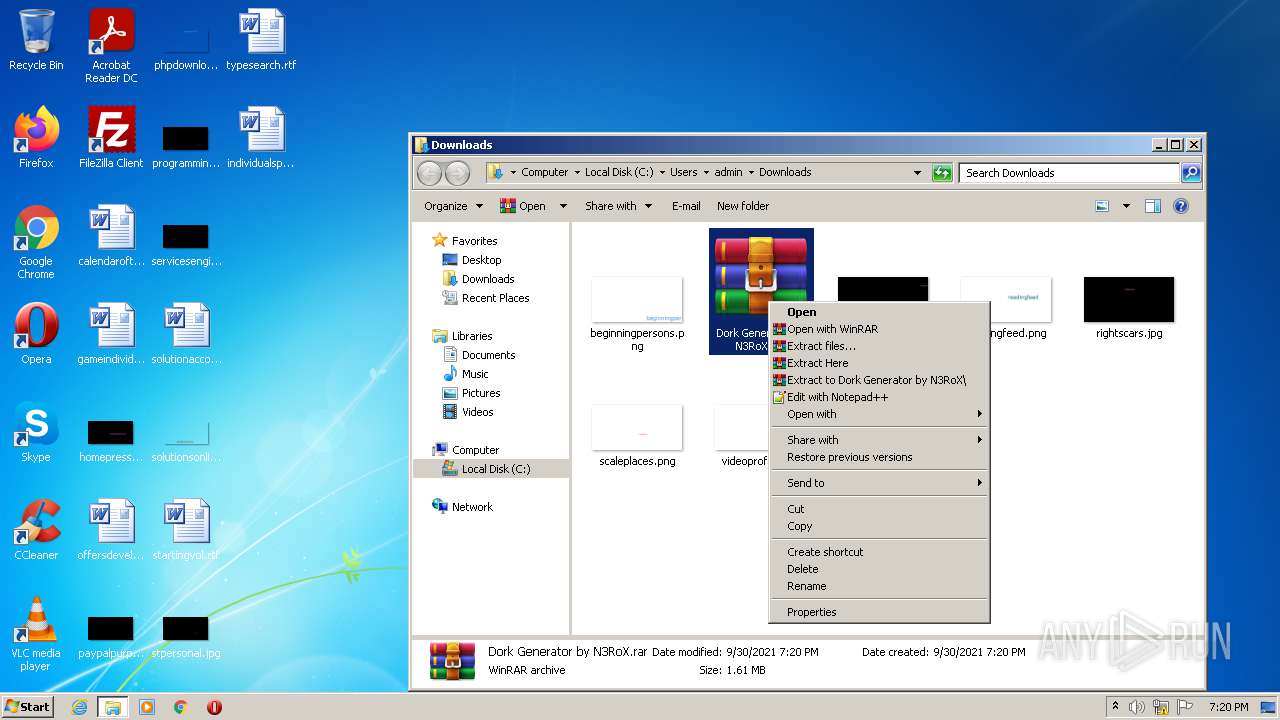
Manual execution by user
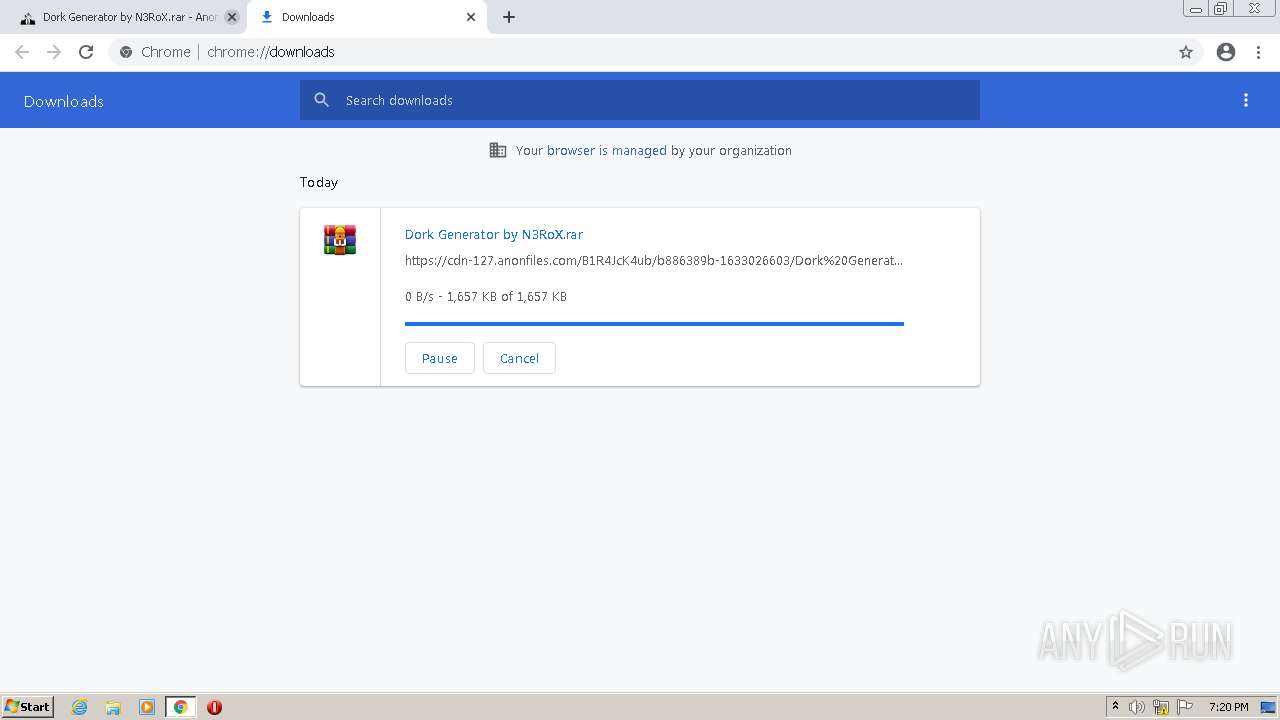
- WinRAR.exe (PID: 2264)
- SQLi Dorks Generator By The N3RoX.exe (PID: 3448)
Reads settings of System Certificates
- chrome.exe (PID: 3348)
Dropped object may contain Bitcoin addresses
- Launcher.exe (PID: 4000)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
61
Monitored processes
21
Malicious processes
5
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 968 | "C:\Windows\IMF\Secure System Shell.exe" | C:\Windows\IMF\Secure System Shell.exe | — | Windows Services.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Secure System Shell Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1008,7450351198556544690,16601541744720005607,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3048 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1008,7450351198556544690,16601541744720005607,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=2660 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,7450351198556544690,16601541744720005607,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1840 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2264 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\Dork Generator by N3RoX.rar" "C:\Users\admin\Downloads\Dork Generator by N3RoX\" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2460 | "C:\Windows\IMF\Runtime Explorer.exe" | C:\Windows\IMF\Runtime Explorer.exe | — | Windows Services.exe | |||||||||||
User: admin Company: Microsoft Windows Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2504 | "C:\Users\admin\Downloads\Dork Generator by N3RoX\Dork Generator by N3RoX\GenData\SQLi.exe" | C:\Users\admin\Downloads\Dork Generator by N3RoX\Dork Generator by N3RoX\GenData\SQLi.exe | SQLi Dorks Generator By The N3RoX.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2552 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
| 2664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://anonfiles.com/B1R4JcK4ub/Dork_Generator_by_N3RoX_rar" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2780 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" add-mppreference -exclusionpath C:\Windows\IMF\ | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Launcher.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 6.2.9200.16398 (win8_gdr_oobssr.120820-1900) Modules
| |||||||||||||||
Total events
13 316
Read events
13 167
Write events
149
Delete events
0
Modification events
| (PID) Process: | (2664) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2664) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2664) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2664) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2664) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2664) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2664) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2664) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2664) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2664) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
10
Suspicious files
54
Text files
95
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6155FFD0-A68.pma | — | |
MD5:— | SHA256:— | |||
| 2664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF122f94.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 2664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF122f84.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 2664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF122fa3.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 2664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 2664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 2664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 2664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\1b6fd7c6-1049-49f0-9eab-0235c0891f39.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 2664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 2664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
26
DNS requests
13
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3348 | chrome.exe | GET | 200 | 67.27.235.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?93dcb336f33ddabe | US | compressed | 59.7 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3348 | chrome.exe | 142.250.185.78:443 | clients2.google.com | Google Inc. | US | whitelisted |
3348 | chrome.exe | 172.64.109.28:443 | anonfiles.com | Cloudflare Inc | US | suspicious |
3348 | chrome.exe | 54.235.172.58:443 | baconaces.pro | Amazon.com, Inc. | US | suspicious |
3348 | chrome.exe | 142.250.74.46:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
3348 | chrome.exe | 142.250.184.237:443 | accounts.google.com | Google Inc. | US | suspicious |
3348 | chrome.exe | 67.27.235.126:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
3348 | chrome.exe | 13.225.87.82:443 | cbuacategic.xyz | — | US | unknown |
3348 | chrome.exe | 151.101.194.217:443 | vjs.zencdn.net | Fastly | US | suspicious |
3348 | chrome.exe | 44.195.137.121:443 | baconaces.pro | University of California, San Diego | US | shared |
3348 | chrome.exe | 18.66.121.162:443 | djv99sxoqpv11.cloudfront.net | Massachusetts Institute of Technology | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
anonfiles.com |
| shared |
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
vjs.zencdn.net |
| whitelisted |
djv99sxoqpv11.cloudfront.net |
| shared |
baconaces.pro |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
cbuacategic.xyz |
| suspicious |
cdn-127.anonfiles.com |
| suspicious |
cireideau.xyz |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3348 | chrome.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
3348 | chrome.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |