| File name: | 4ee074eeb36c226268874c700027ed29 |
| Full analysis: | https://app.any.run/tasks/c545f195-08a1-4eb7-9c9f-954853bc108e |
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2020, 10:55:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 4EE074EEB36C226268874C700027ED29 |
| SHA1: | 74CA5DC263BE68E4D0C1F9A7C2BCC2F38982C958 |
| SHA256: | B89EAD1ED1D1FA822D5C37F3910E9E08E7BD48681BD099B3337AFB7AF92F0954 |
| SSDEEP: | 6144:9FfwIWuOGVY81tES6A6Z7u4ESs/kyZRf6qT:zNZOGVY81tES6X2SKZUqT |
MALICIOUS
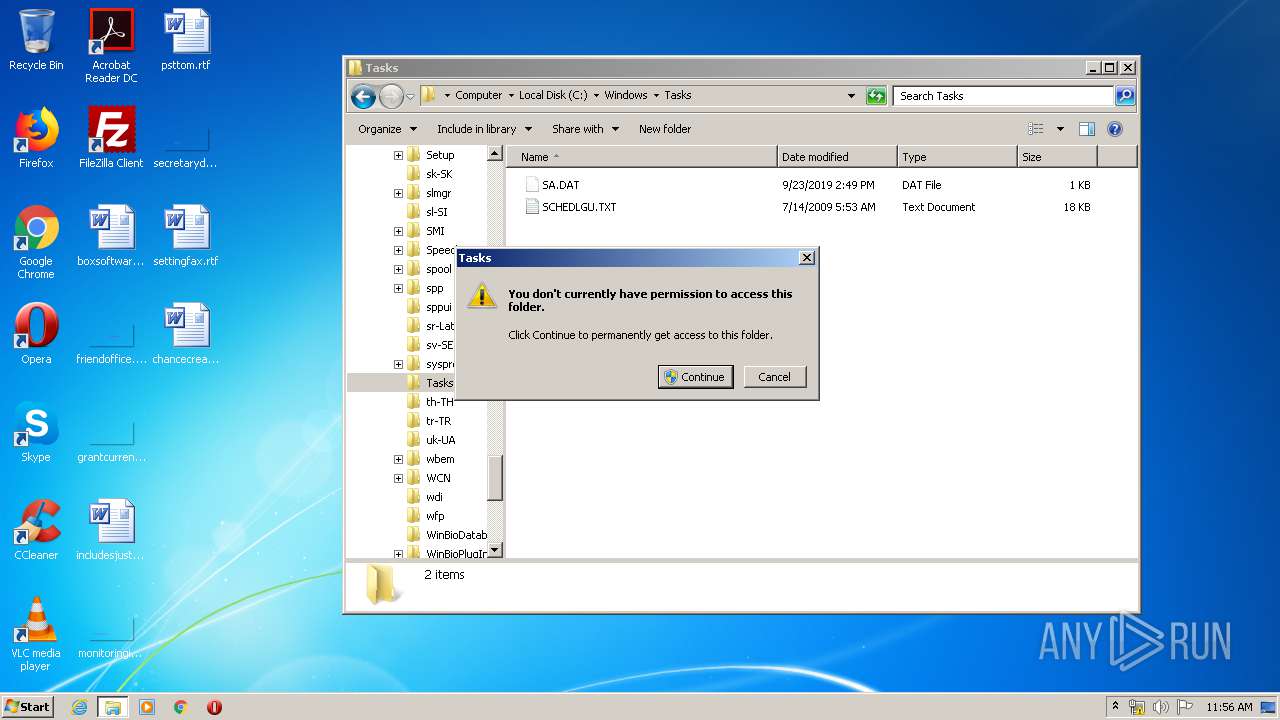
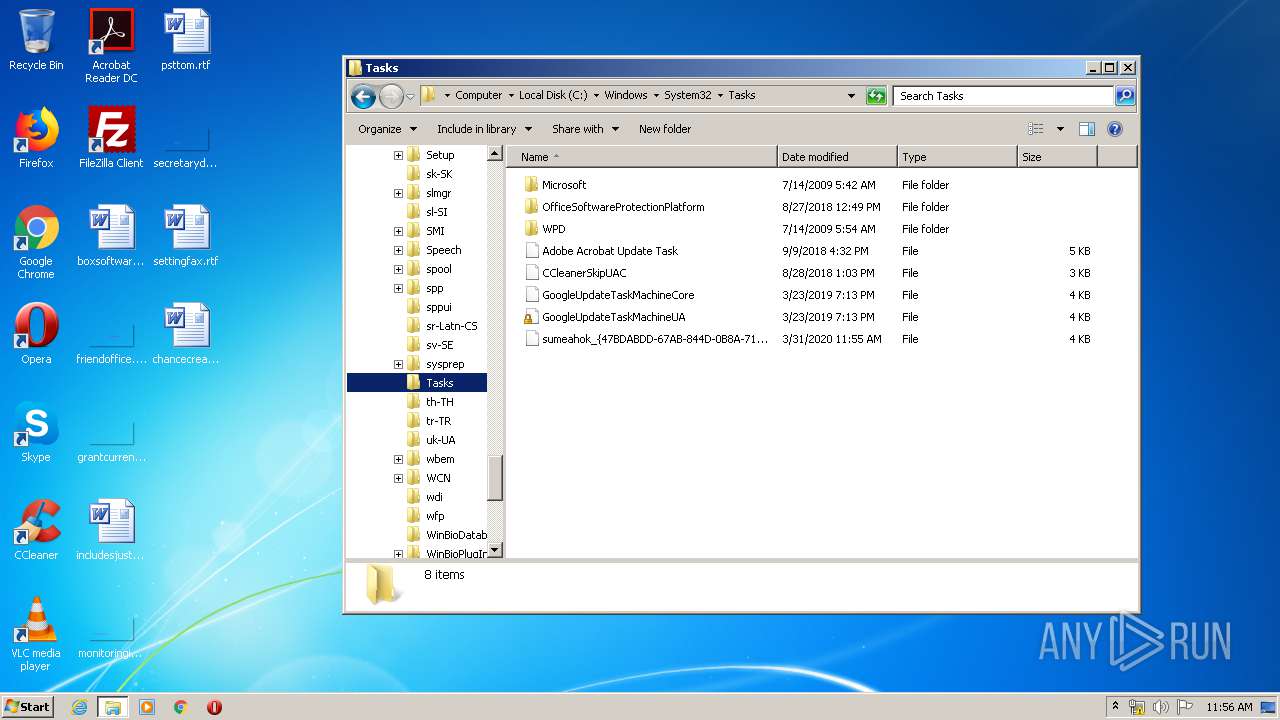
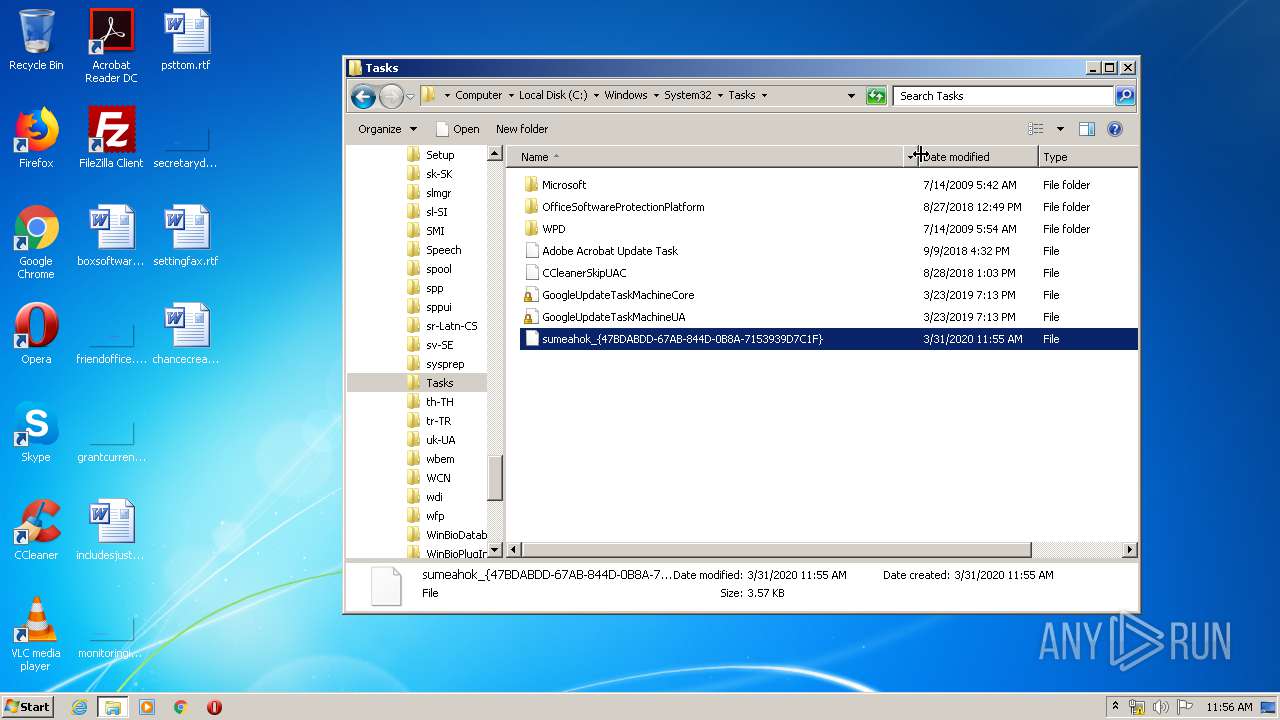
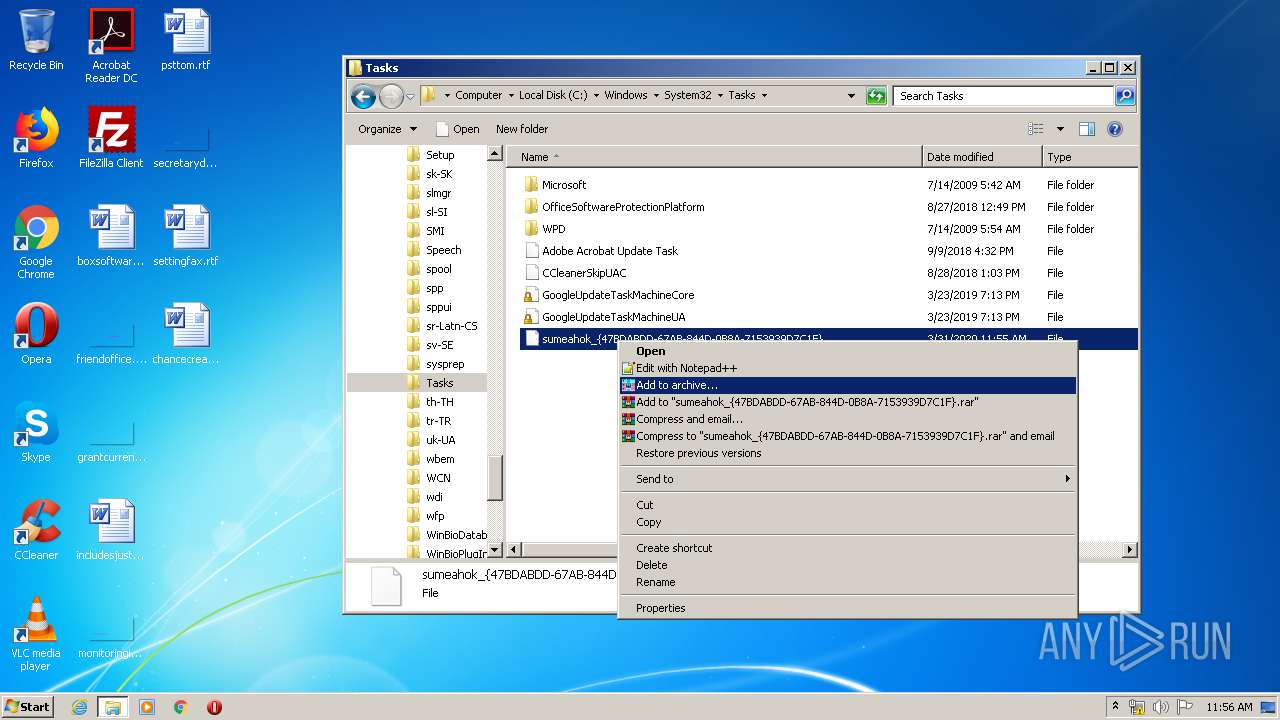
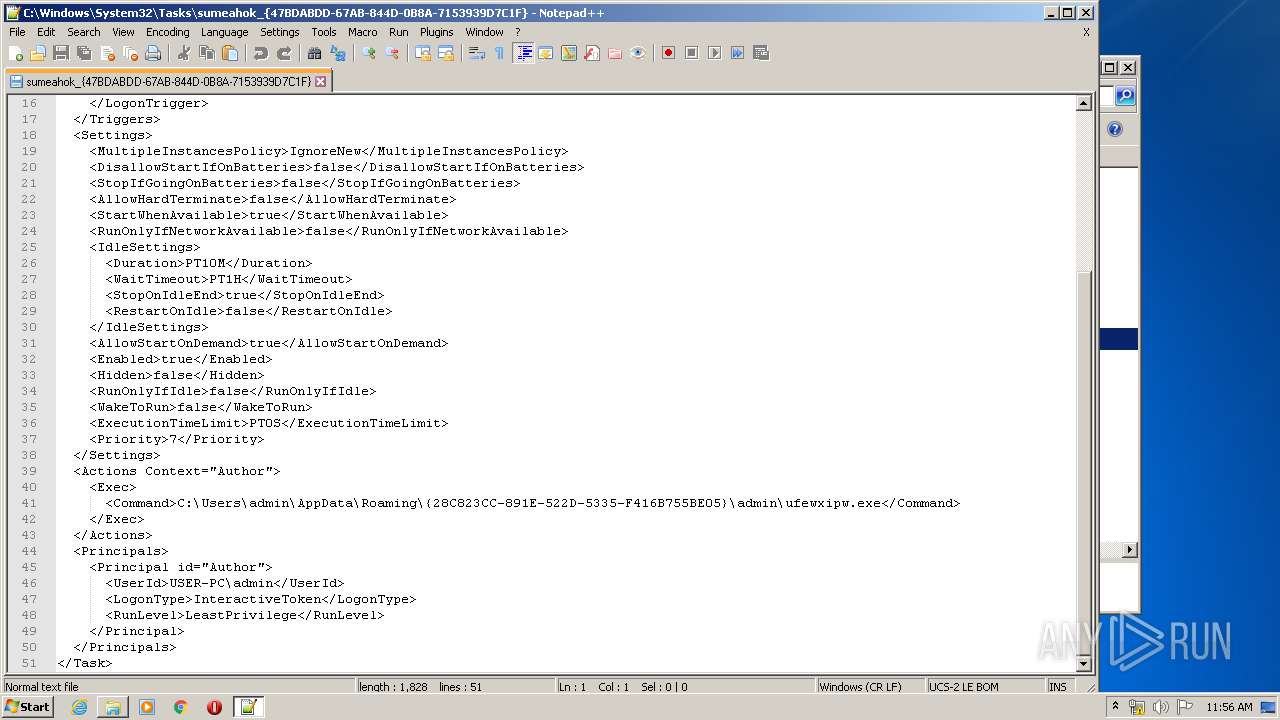
Loads the Task Scheduler COM API
- svchost.exe (PID: 3288)
Uses SVCHOST.EXE for hidden code execution
- 4ee074eeb36c226268874c700027ed29.exe (PID: 944)
Loads dropped or rewritten executable
- svchost.exe (PID: 3288)
Actions looks like stealing of personal data
- svchost.exe (PID: 3288)
SUSPICIOUS
Creates files in the user directory
- svchost.exe (PID: 3288)
- 4ee074eeb36c226268874c700027ed29.exe (PID: 944)
- notepad++.exe (PID: 3052)
Starts application with an unusual extension
- cmd.exe (PID: 2120)
Starts CMD.EXE for commands execution
- svchost.exe (PID: 3288)
Executable content was dropped or overwritten
- svchost.exe (PID: 3288)
Reads the cookies of Google Chrome
- svchost.exe (PID: 3288)
Executed via COM
- DllHost.exe (PID: 2768)
Reads the cookies of Mozilla Firefox
- svchost.exe (PID: 3288)
INFO
Reads settings of System Certificates
- 4ee074eeb36c226268874c700027ed29.exe (PID: 944)
Manual execution by user
- notepad++.exe (PID: 3052)
- explorer.exe (PID: 3064)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2011:03:24 13:01:10+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 128512 |
| InitializedDataSize: | 77824 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x7040 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 7.5.59.19 |
| ProductVersionNumber: | 7.5.59.19 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Realgood DaySmart Software Hold Corporation |
| FileDescription: | Realgood DaySmart Software Hold Read yes |
| FileVersion: | 7.5.59.19 built by: 54338 |
| InternalName: | Whatsm.exe |
| LegalCopyright: | © Realgood DaySmart Software Hold Corporation. All rights reserved. |
| OriginalFileName: | Whatsm.exe |
| ProductName: | Realgood DaySmart Software Hold ®Realgood DaySmart Software Hold ® 2016 |
| ProductVersion: | 7.5.59.19 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Mar-2011 12:01:10 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Realgood DaySmart Software Hold Corporation |
| FileDescription: | Realgood DaySmart Software Hold Read yes |
| FileVersion: | 7.5.59.19 built by: 54338 |
| InternalName: | Whatsm.exe |
| LegalCopyright: | © Realgood DaySmart Software Hold Corporation. All rights reserved. |
| OriginalFilename: | Whatsm.exe |
| ProductName: | Realgood DaySmart Software Hold ®Realgood DaySmart Software Hold ® 2016 |
| ProductVersion: | 7.5.59.19 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 24-Mar-2011 12:01:10 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001F491 | 0x0001F600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.29289 |
.rdata | 0x00021000 | 0x0000CADC | 0x0000CC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.66686 |
.data | 0x0002E000 | 0x0001A668 | 0x00002400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.67378 |
.rsrc | 0x00049000 | 0x0000062C | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.49009 |
.reloc | 0x0004A000 | 0x00003742 | 0x00003800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.4673 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.79597 | 346 | Latin 1 / Western European | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.dll |
USER32.dll |
ole32.dll |
Total processes
46
Monitored processes
8
Malicious processes
2
Suspicious processes
0
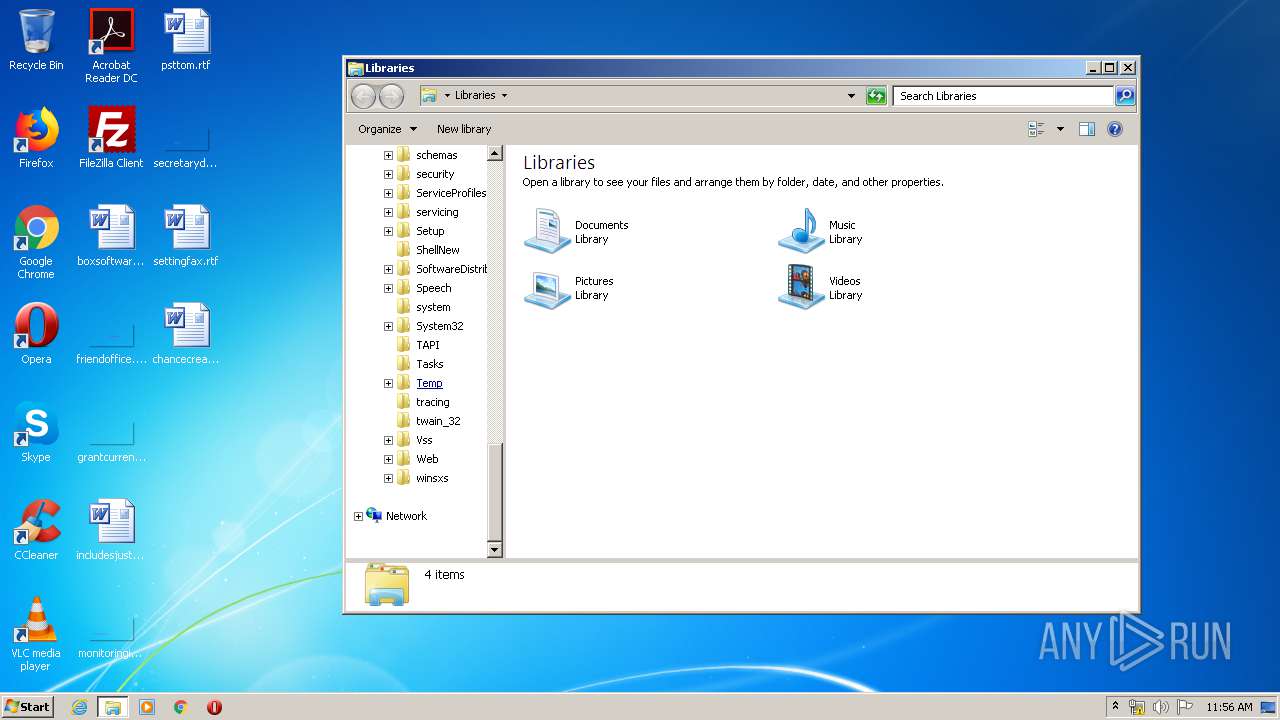
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 944 | "C:\Users\admin\AppData\Local\Temp\4ee074eeb36c226268874c700027ed29.exe" | C:\Users\admin\AppData\Local\Temp\4ee074eeb36c226268874c700027ed29.exe | explorer.exe | ||||||||||||
User: admin Company: Realgood DaySmart Software Hold Corporation Integrity Level: MEDIUM Description: Realgood DaySmart Software Hold Read yes Exit code: 0 Version: 7.5.59.19 built by: 54338 Modules
| |||||||||||||||
| 2120 | cmd /c chcp | C:\windows\system32\cmd.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2768 | C:\Windows\system32\DllHost.exe /Processid:{4D111E08-CBF7-4F12-A926-2C7920AF52FC} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2896 | chcp | C:\Windows\system32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
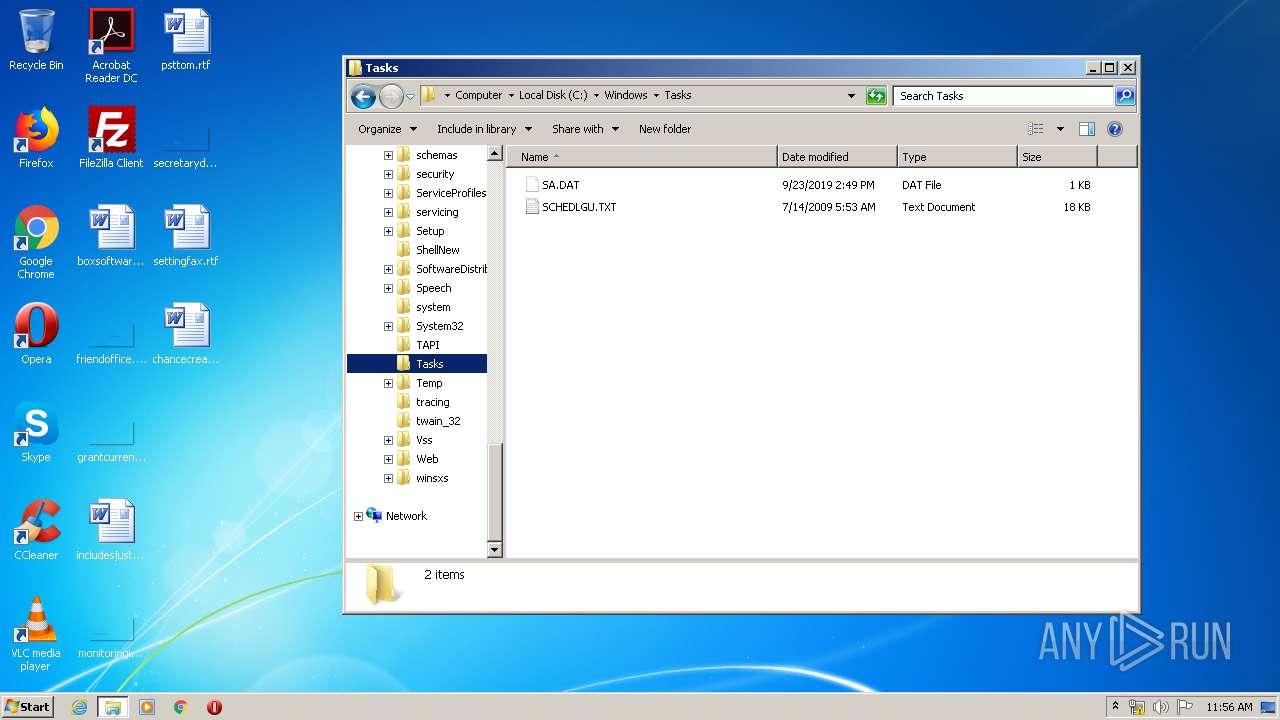
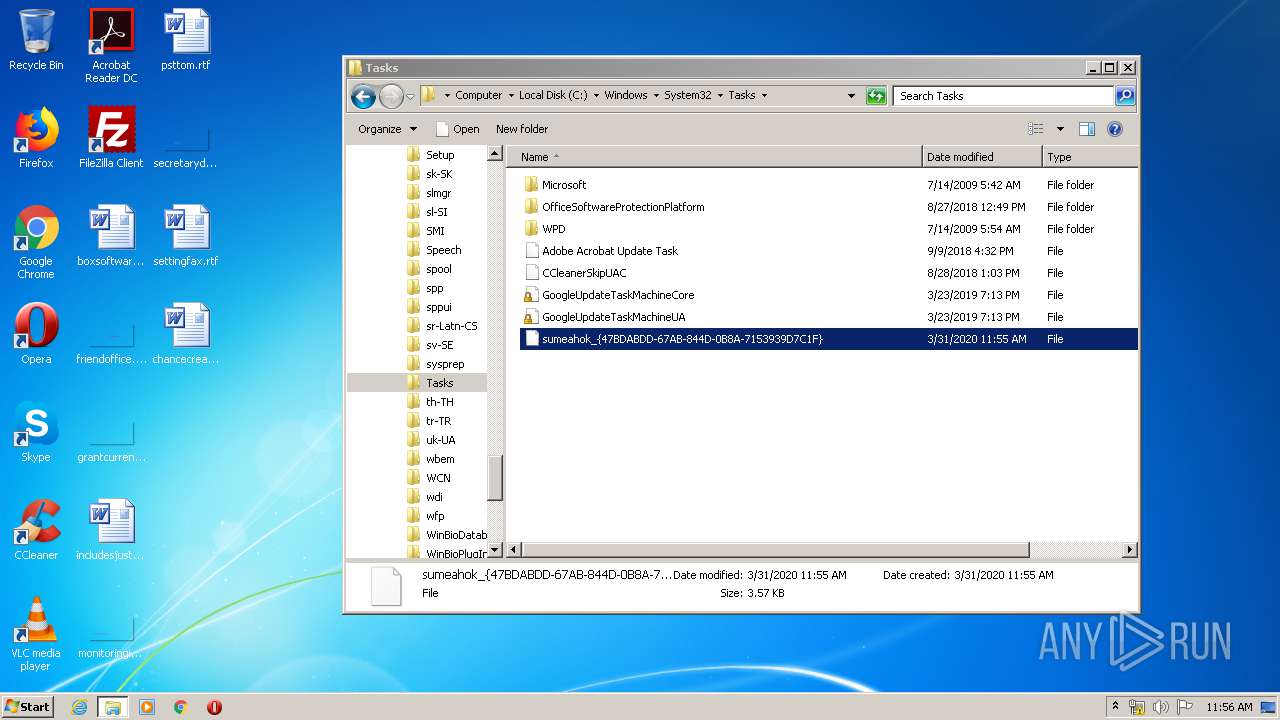
| 3052 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Windows\System32\Tasks\sumeahok_{47BDABDD-67AB-844D-0B8A-7153939D7C1F}" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.51 Modules
| |||||||||||||||
| 3064 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3072 | "C:\Program Files\Notepad++\updater\gup.exe" -v7.51 | C:\Program Files\Notepad++\updater\gup.exe | notepad++.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: GUP : a free (LGPL) Generic Updater Exit code: 0 Version: 4.1 Modules
| |||||||||||||||
| 3288 | C:\windows\system32\svchost.exe | C:\windows\system32\svchost.exe | 4ee074eeb36c226268874c700027ed29.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
207
Read events
169
Write events
38
Delete events
0
Modification events
| (PID) Process: | (944) 4ee074eeb36c226268874c700027ed29.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3052) notepad++.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3052) notepad++.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3052) notepad++.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3288) svchost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3288) svchost.exe | Key: | HKEY_CLASSES_ROOT\CLSID\{992A484C-A4BB-FF00-CB05-2CAB204CD4F5} |
| Operation: | write | Name: | |
Value: A82E0FC9ECD9C460AB5E936347B594035840BC0450FB27EAFC2DE7A63FE828D3DADFE9F9A2638B37A6845BF2D5F801861CDFC5156C4566535C6F59C383835765D00985B41164F40B04369BCA2DE2F0D4D6F6C118F42C7A1F9B47D42D2DFAE8313AD46D540C86763549E906DCDB1EC0EE3BD3E4EAF6C2FCC79497050DAD41D86081AABDCE5AA426510A313A4AC87DE69286B0ACD207ED600A0C71284BCD77E6FEE9B6BDCA59ED33514638284DDD7DE69286B0ACD207EA660E463F3C5AC07189FE81AABDCE5AA426510F37255FCA71E59187BBA59059E9261F1C3A2051A91E89 | |||
| (PID) Process: | (3288) svchost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3288) svchost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3288) svchost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
2
Suspicious files
9
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 944 | 4ee074eeb36c226268874c700027ed29.exe | C:\Users\admin\AppData\Local\Temp\CabBB59.tmp | — | |
MD5:— | SHA256:— | |||
| 944 | 4ee074eeb36c226268874c700027ed29.exe | C:\Users\admin\AppData\Local\Temp\TarBB5A.tmp | — | |
MD5:— | SHA256:— | |||
| 944 | 4ee074eeb36c226268874c700027ed29.exe | C:\Users\admin\AppData\Local\Temp\CabBB7A.tmp | — | |
MD5:— | SHA256:— | |||
| 944 | 4ee074eeb36c226268874c700027ed29.exe | C:\Users\admin\AppData\Local\Temp\TarBB7B.tmp | — | |
MD5:— | SHA256:— | |||
| 944 | 4ee074eeb36c226268874c700027ed29.exe | C:\Users\admin\AppData\Local\Temp\CabBE0D.tmp | — | |
MD5:— | SHA256:— | |||
| 944 | 4ee074eeb36c226268874c700027ed29.exe | C:\Users\admin\AppData\Local\Temp\TarBE0E.tmp | — | |
MD5:— | SHA256:— | |||
| 944 | 4ee074eeb36c226268874c700027ed29.exe | C:\Users\admin\AppData\Local\Temp\CabCAD0.tmp | — | |
MD5:— | SHA256:— | |||
| 944 | 4ee074eeb36c226268874c700027ed29.exe | C:\Users\admin\AppData\Local\Temp\TarCAD1.tmp | — | |
MD5:— | SHA256:— | |||
| 944 | 4ee074eeb36c226268874c700027ed29.exe | C:\Users\admin\AppData\Local\Temp\CabCBDC.tmp | — | |
MD5:— | SHA256:— | |||
| 944 | 4ee074eeb36c226268874c700027ed29.exe | C:\Users\admin\AppData\Local\Temp\TarCBDD.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
9
DNS requests
5
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3288 | svchost.exe | GET | 304 | 23.55.163.58:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | — | — | whitelisted |
3288 | svchost.exe | GET | 304 | 23.55.163.58:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | — | — | whitelisted |
3288 | svchost.exe | GET | 304 | 23.55.163.58:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | — | — | whitelisted |
3288 | svchost.exe | GET | 304 | 23.55.163.58:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | — | — | whitelisted |
944 | 4ee074eeb36c226268874c700027ed29.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.0 Kb | whitelisted |
944 | 4ee074eeb36c226268874c700027ed29.exe | GET | 304 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.0 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
944 | 4ee074eeb36c226268874c700027ed29.exe | 89.33.246.122:443 | beradocolon.top | M247 Ltd | RO | unknown |
3072 | gup.exe | 104.31.88.28:443 | notepad-plus-plus.org | Cloudflare Inc | US | shared |
3288 | svchost.exe | 89.33.246.122:443 | beradocolon.top | M247 Ltd | RO | unknown |
3288 | svchost.exe | 23.55.163.58:80 | www.download.windowsupdate.com | Akamai International B.V. | US | unknown |
944 | 4ee074eeb36c226268874c700027ed29.exe | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
beradocolon.top |
| unknown |
www.download.windowsupdate.com |
| whitelisted |
notepad-plus-plus.org |
| whitelisted |
filacolonel.pw |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
944 | 4ee074eeb36c226268874c700027ed29.exe | Not Suspicious Traffic | ET POLICY OpenSSL Demo CA - Internet Widgits Pty (O) |
3288 | svchost.exe | Not Suspicious Traffic | ET POLICY OpenSSL Demo CA - Internet Widgits Pty (O) |
3288 | svchost.exe | Not Suspicious Traffic | ET POLICY OpenSSL Demo CA - Internet Widgits Pty (O) |
3288 | svchost.exe | Not Suspicious Traffic | ET POLICY OpenSSL Demo CA - Internet Widgits Pty (O) |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
3288 | svchost.exe | Not Suspicious Traffic | ET POLICY OpenSSL Demo CA - Internet Widgits Pty (O) |
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|