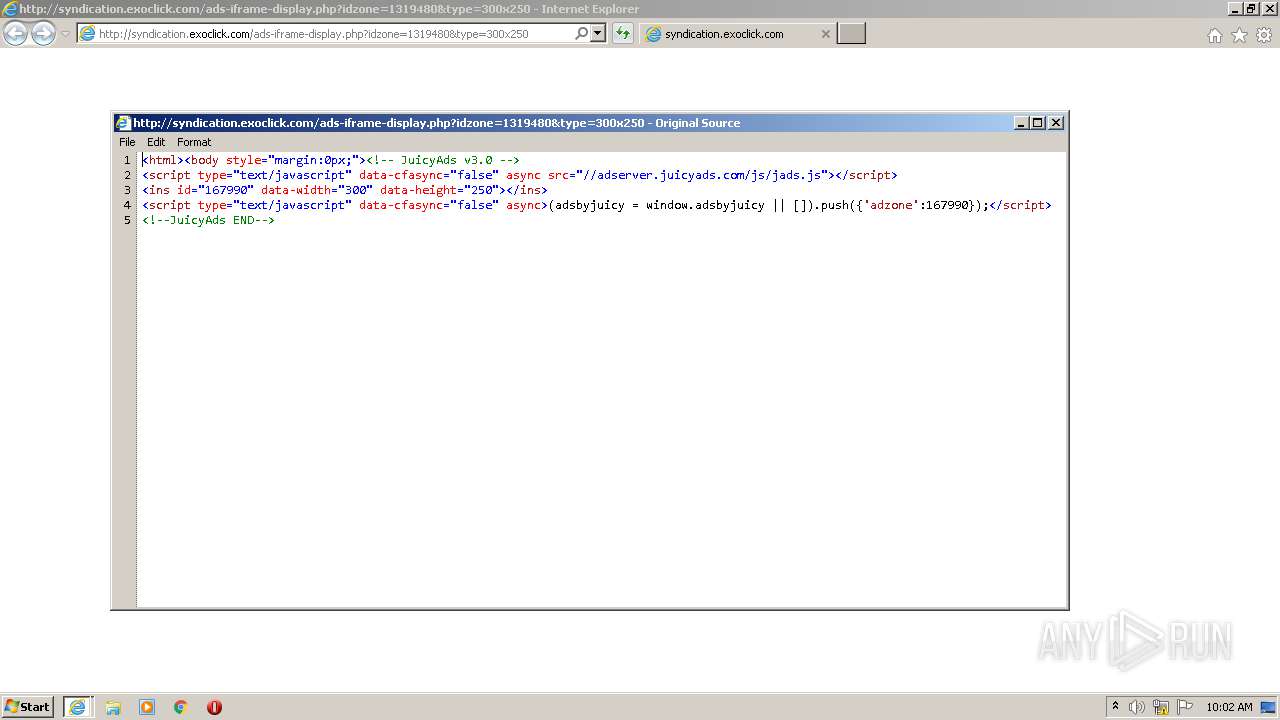
| URL: | http://syndication.exoclick.com/ads-iframe-display.php?idzone=1319480&type=300x250 |
| Full analysis: | https://app.any.run/tasks/77ad78e1-e117-4c36-bbfe-60aa2d6e50df |
| Verdict: | Malicious activity |
| Analysis date: | September 11, 2020, 08:59:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 2C8EFD51DE8F94C993F77B0E0977B14F |
| SHA1: | A0A9B769705CDDE88611F863ACDB51082137D95A |
| SHA256: | B8936E65B13EFDBA4D95C99ED8AA422770AE86F52FD492E0B31756D9AC8D3F5A |
| SSDEEP: | 3:N1KNcL2xLDeHPhKAQgApcLJRAn:COiUHIAQj+JRAn |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 2184)
- iexplore.exe (PID: 668)
- iexplore.exe (PID: 2932)
Changes internet zones settings
- iexplore.exe (PID: 2184)
Application launched itself
- iexplore.exe (PID: 2184)
Creates files in the user directory
- iexplore.exe (PID: 668)
- iexplore.exe (PID: 2932)
- iexplore.exe (PID: 2184)
Reads internet explorer settings
- iexplore.exe (PID: 668)
- iexplore.exe (PID: 2932)
Reads settings of System Certificates
- iexplore.exe (PID: 2184)
Changes settings of System certificates
- iexplore.exe (PID: 2184)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2184)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
41
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 668 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2184 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2184 | "C:\Program Files\Internet Explorer\iexplore.exe" http://syndication.exoclick.com/ads-iframe-display.php?idzone=1319480&type=300x250 | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2932 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2184 CREDAT:1053959 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
1 187
Read events
1 080
Write events
105
Delete events
2
Modification events
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3913339244 | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30836761 | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A3000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
11
Text files
22
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2184 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 668 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\6J4N5XXM.txt | — | |
MD5:— | SHA256:— | |||
| 668 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\SD3J8ZTJ.txt | — | |
MD5:— | SHA256:— | |||
| 2184 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab6D18.tmp | — | |
MD5:— | SHA256:— | |||
| 2184 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar6D19.tmp | — | |
MD5:— | SHA256:— | |||
| 2184 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\ver7A88.tmp | — | |
MD5:— | SHA256:— | |||
| 2184 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\ZF4JMCDG.txt | — | |
MD5:— | SHA256:— | |||
| 2184 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\ZJ3R4WKM.txt | — | |
MD5:— | SHA256:— | |||
| 668 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\ads-iframe-display[1].htm | html | |
MD5:— | SHA256:— | |||
| 668 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\3ID8QLOJ.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
35
DNS requests
14
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
668 | iexplore.exe | GET | 304 | 185.94.236.24:80 | http://adserver.juicyads.com/js/jads.js | NL | — | — | suspicious |
668 | iexplore.exe | GET | 200 | 95.211.229.246:80 | http://syndication.exoclick.com/ads-iframe-display.php?idzone=1319480&type=300x250 | NL | html | 254 b | suspicious |
668 | iexplore.exe | GET | 200 | 185.94.236.24:80 | http://adserver.juicyads.com/adshow.php?adzone=167990 | NL | html | 1.53 Kb | suspicious |
668 | iexplore.exe | GET | 200 | 95.211.229.246:80 | http://syndication.exoclick.com/ads-iframe-display.php?idzone=1319480&type=300x250 | NL | html | 254 b | suspicious |
668 | iexplore.exe | GET | 200 | 69.16.175.10:80 | http://ads.juicyads.me/ads/user1608/ad561143-1598037164.jpg | US | image | 51.5 Kb | malicious |
668 | iexplore.exe | GET | 304 | 69.16.175.42:80 | http://ads.juicyads.me/ads/user1608/ad561143-1598037164.jpg | US | — | — | malicious |
668 | iexplore.exe | GET | 200 | 185.94.236.24:80 | http://adserver.juicyads.com/adshow.php?adzone=167990 | NL | html | 1.72 Kb | suspicious |
668 | iexplore.exe | GET | 200 | 185.94.236.24:80 | http://adserver.juicyads.com/adshow.php?adzone=167990 | NL | html | 1.53 Kb | suspicious |
2184 | iexplore.exe | GET | 404 | 95.211.229.246:80 | http://syndication.exoclick.com/favicon.ico | NL | html | 167 b | suspicious |
668 | iexplore.exe | GET | 200 | 69.16.175.42:80 | http://ads.juicyads.me/1x1.gif | US | image | 43 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
668 | iexplore.exe | 95.211.229.246:80 | syndication.exoclick.com | LeaseWeb Netherlands B.V. | NL | suspicious |
668 | iexplore.exe | 185.94.236.24:80 | adserver.juicyads.com | Mojohost B.v. | NL | unknown |
2184 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2932 | iexplore.exe | 199.241.100.249:80 | ck.juicyads.com | MOJOHOST | US | unknown |
2184 | iexplore.exe | 95.211.229.246:80 | syndication.exoclick.com | LeaseWeb Netherlands B.V. | NL | suspicious |
668 | iexplore.exe | 69.16.175.42:80 | ads.juicyads.me | Highwinds Network Group, Inc. | US | malicious |
2932 | iexplore.exe | 104.232.43.11:443 | www.uk-flashers.net | ColoCrossing | US | suspicious |
2184 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2184 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2184 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
syndication.exoclick.com |
| suspicious |
adserver.juicyads.com |
| suspicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ads.juicyads.me |
| malicious |
ck.juicyads.com |
| whitelisted |
www.uk-flashers.net |
| suspicious |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2932 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2932 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |