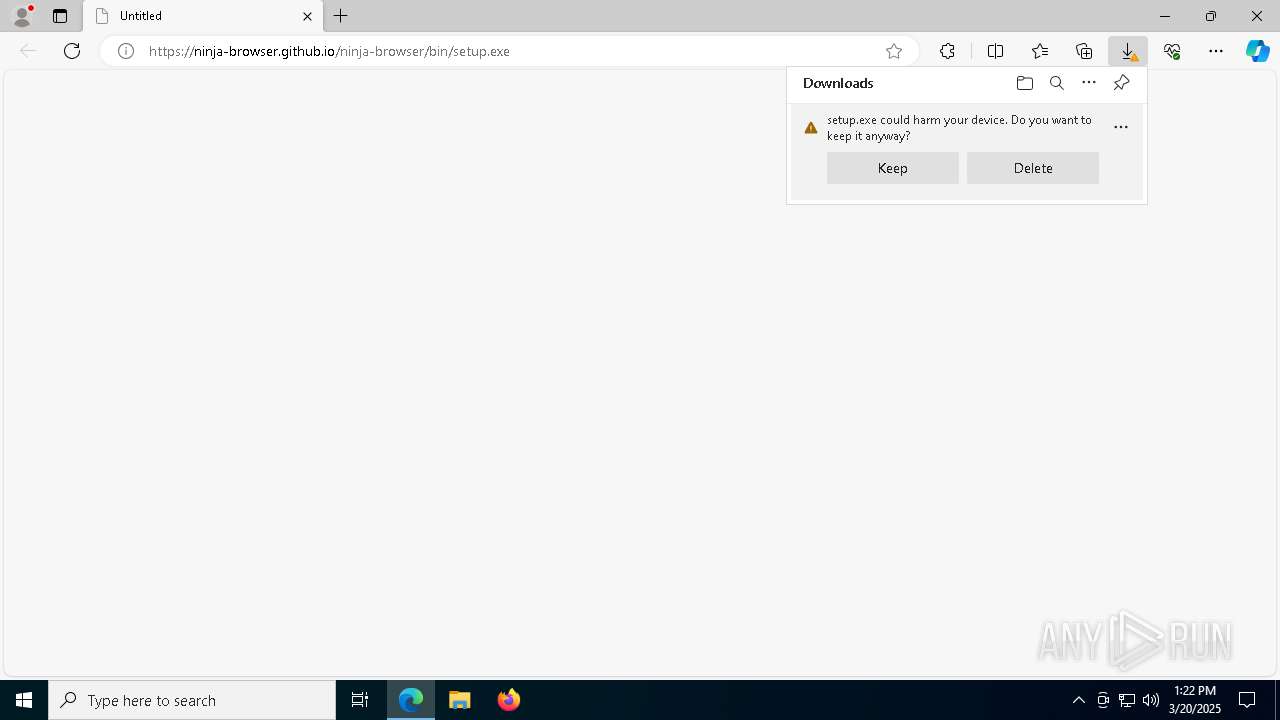
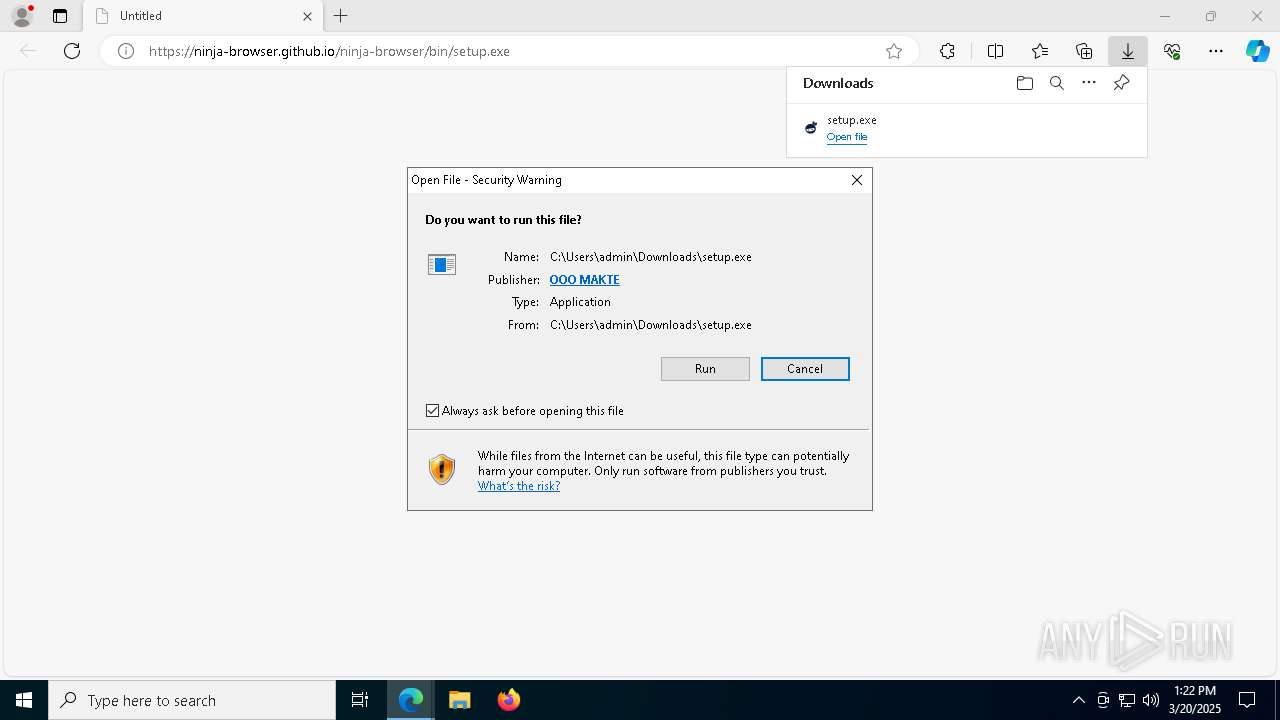
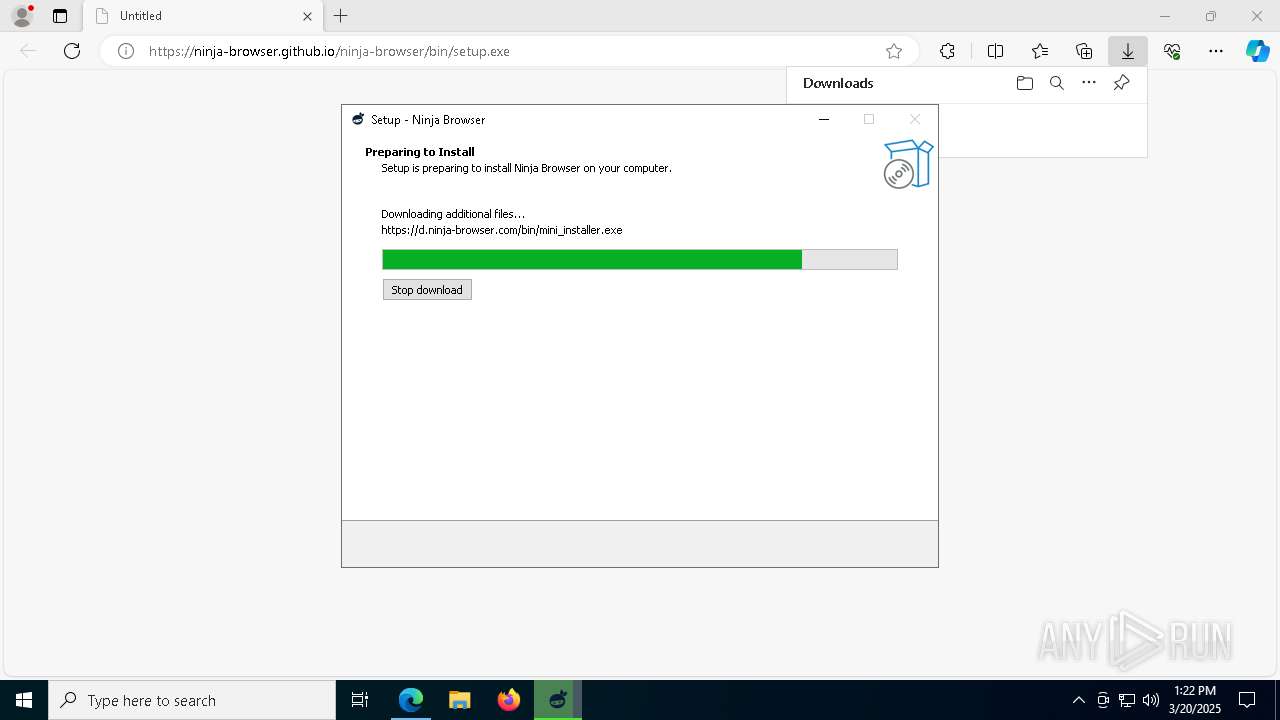
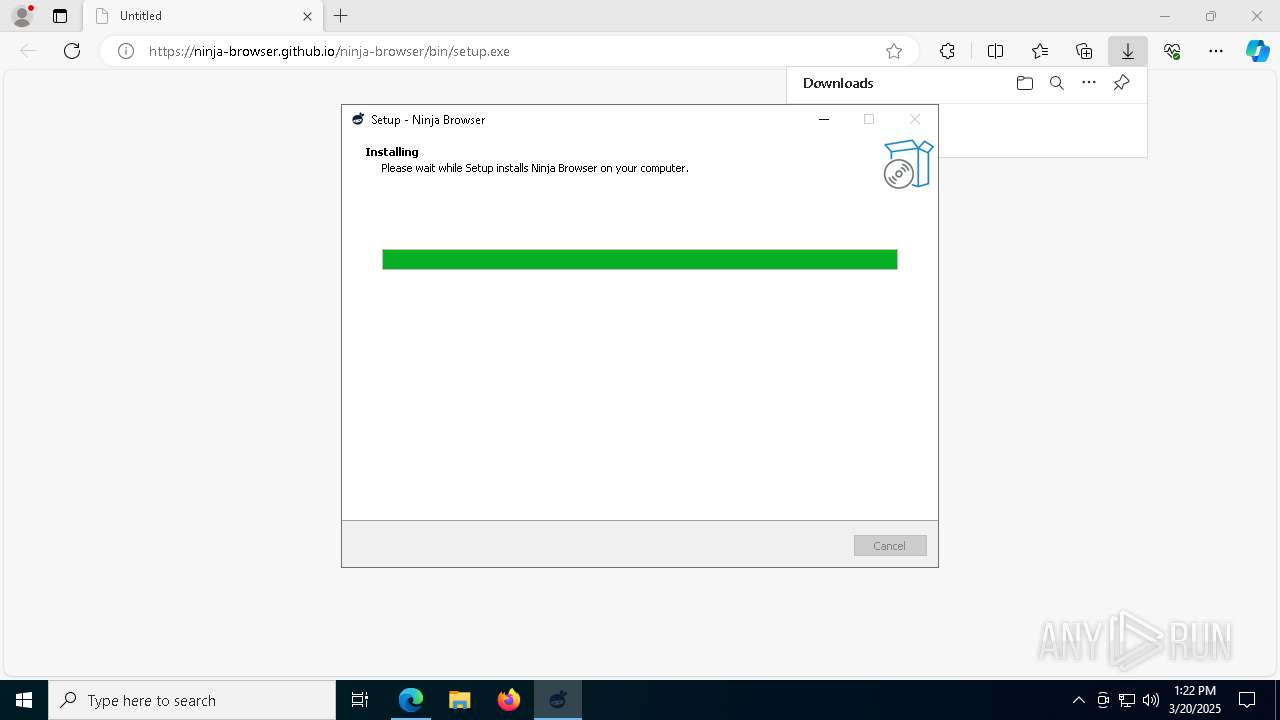
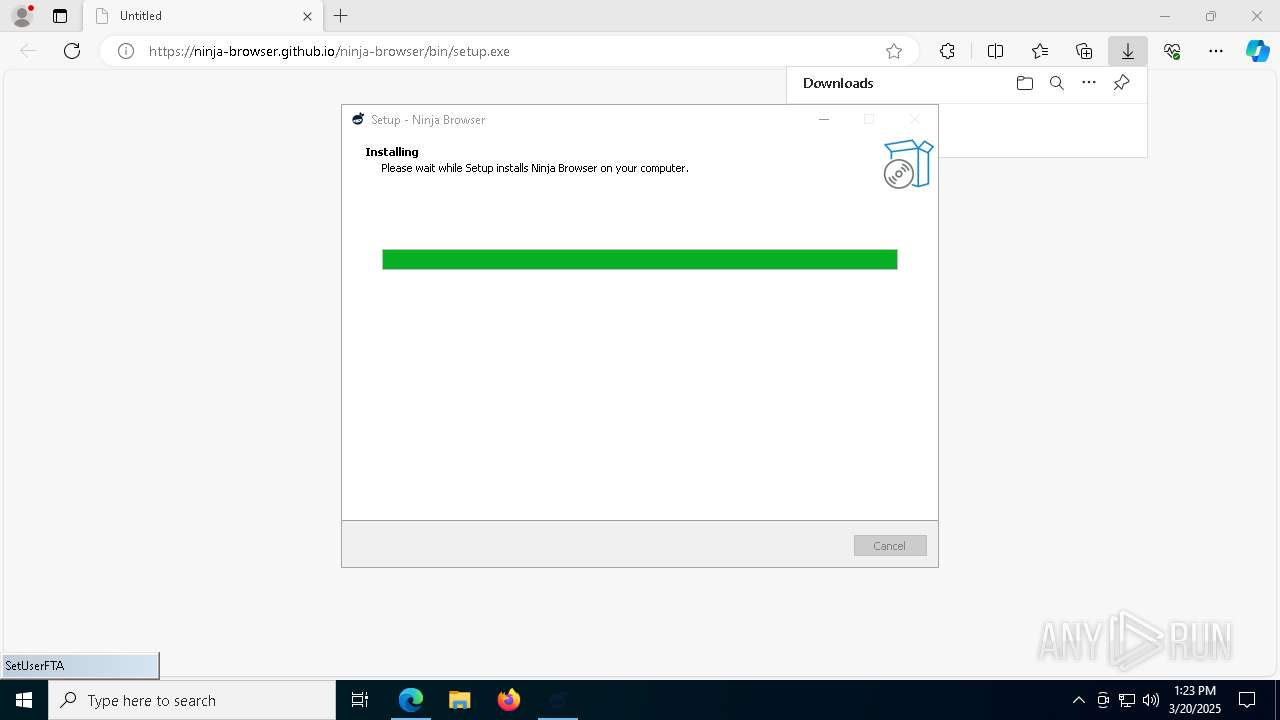
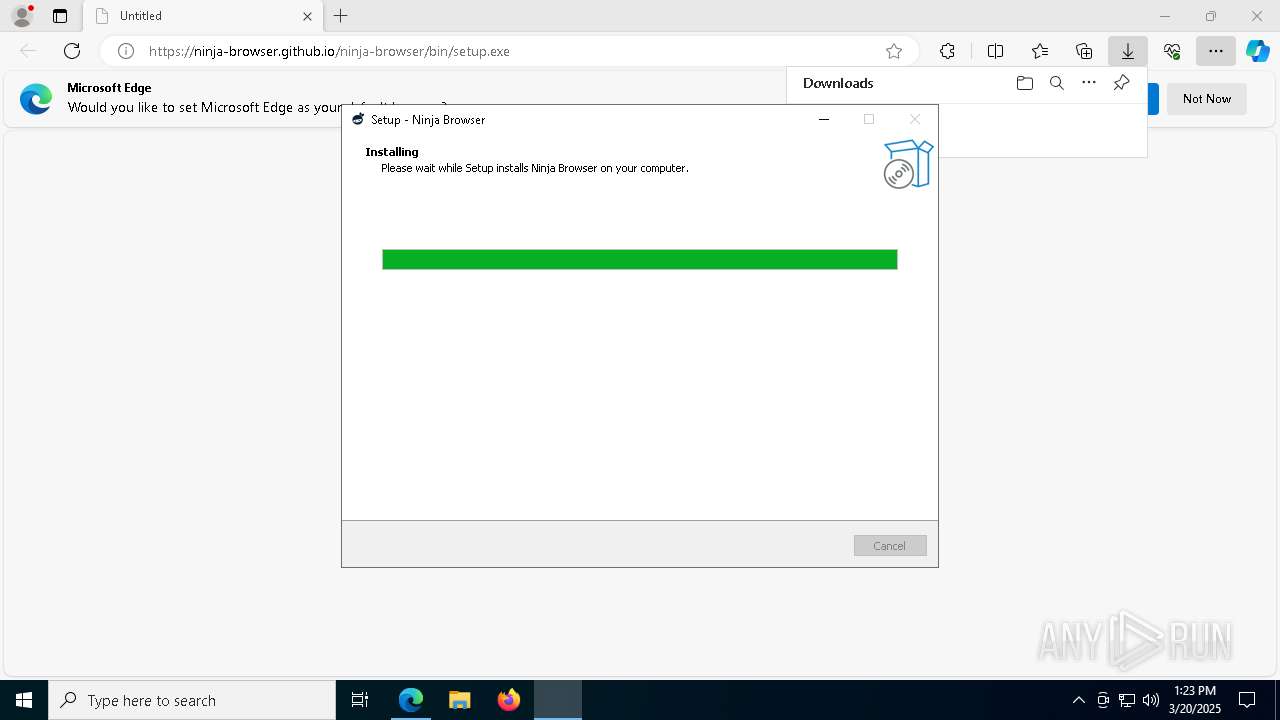
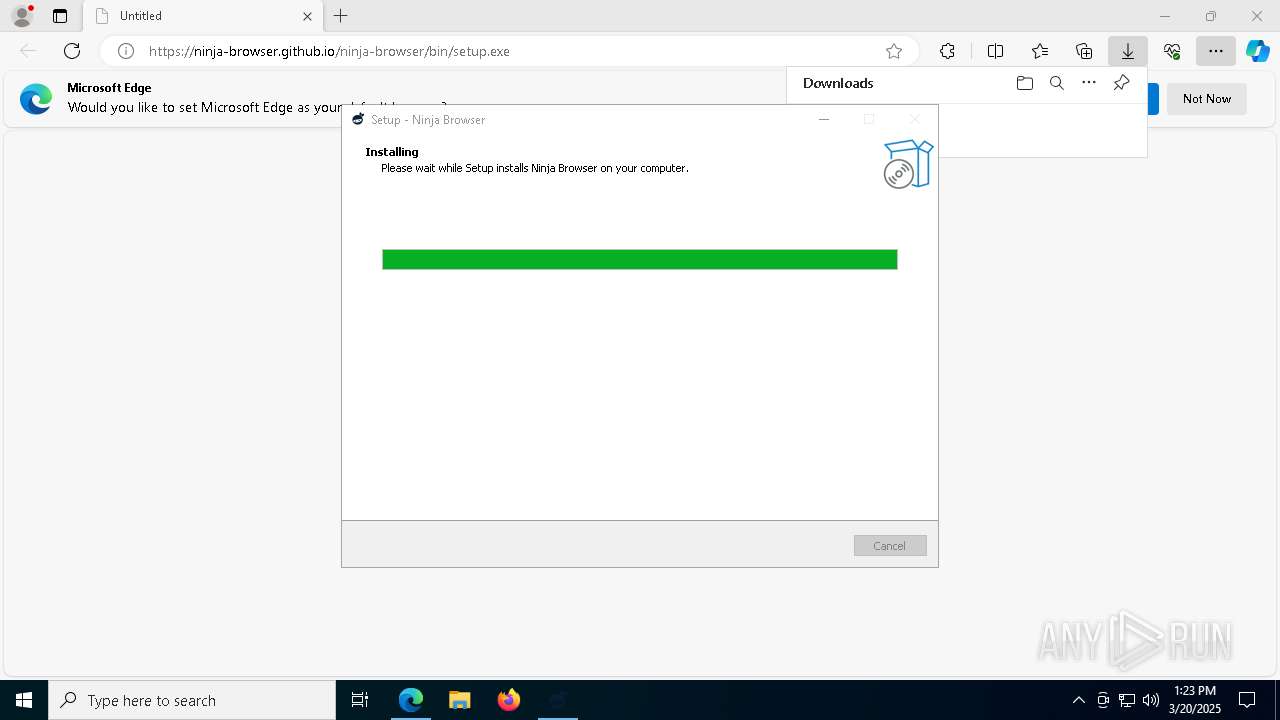
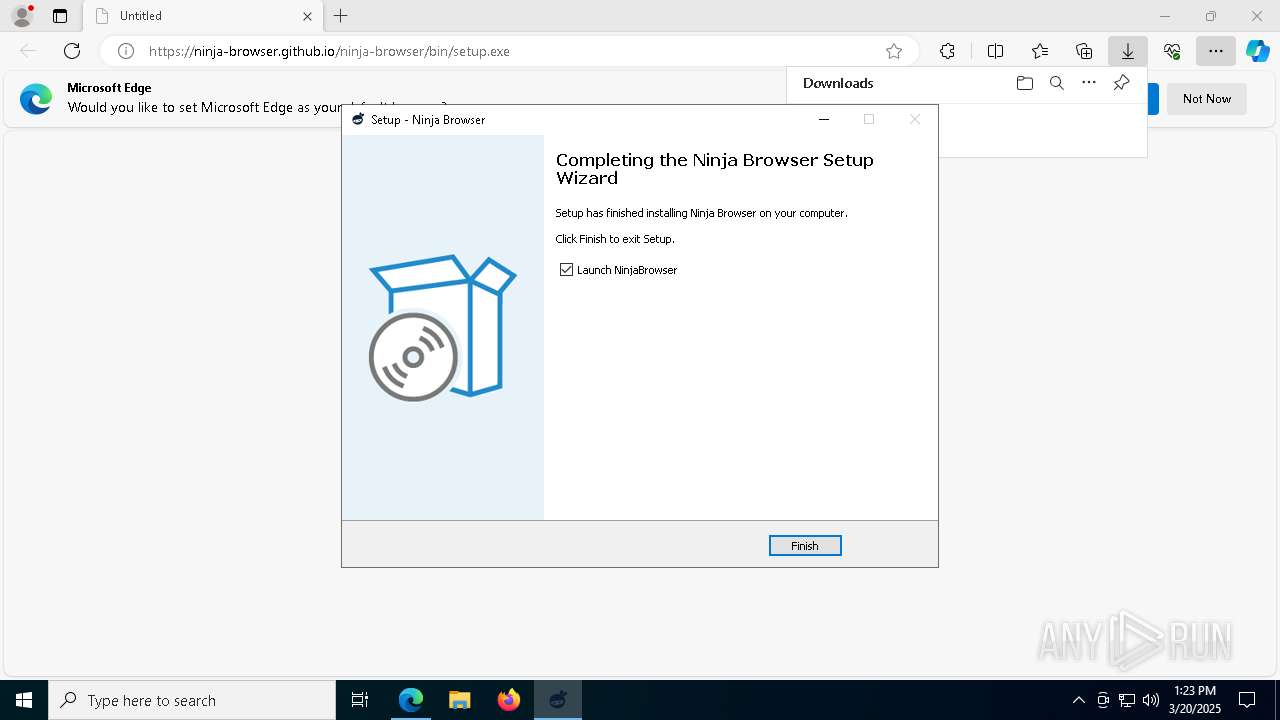
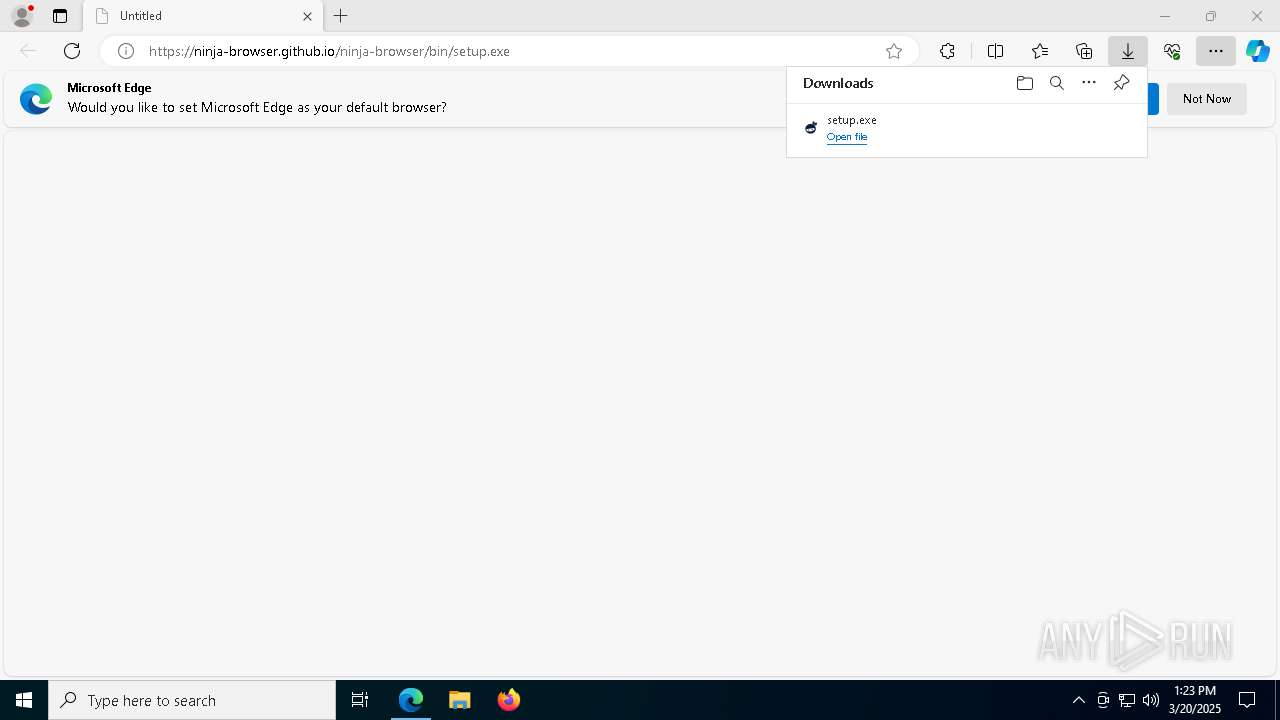
| URL: | https://ninja-browser.github.io/ninja-browser/bin/setup.exe |
| Full analysis: | https://app.any.run/tasks/b5c9b8e0-ce67-4896-8cf5-e9f9a3b8dff9 |
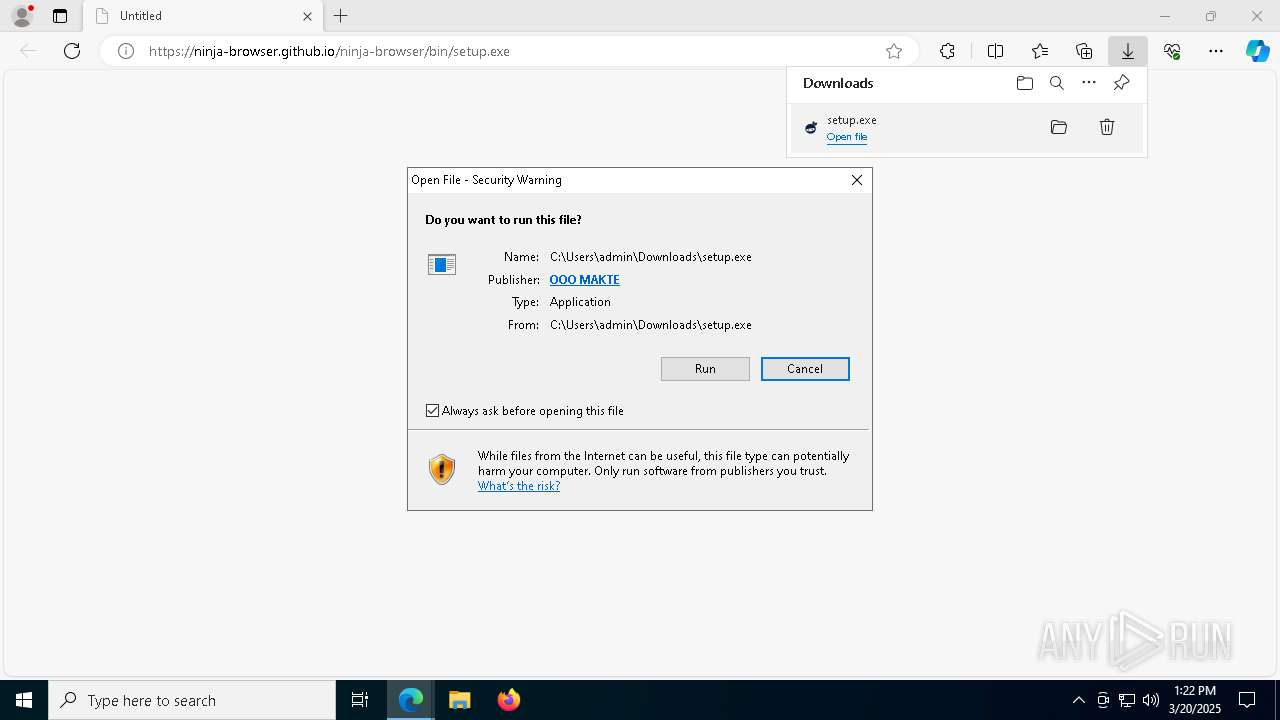
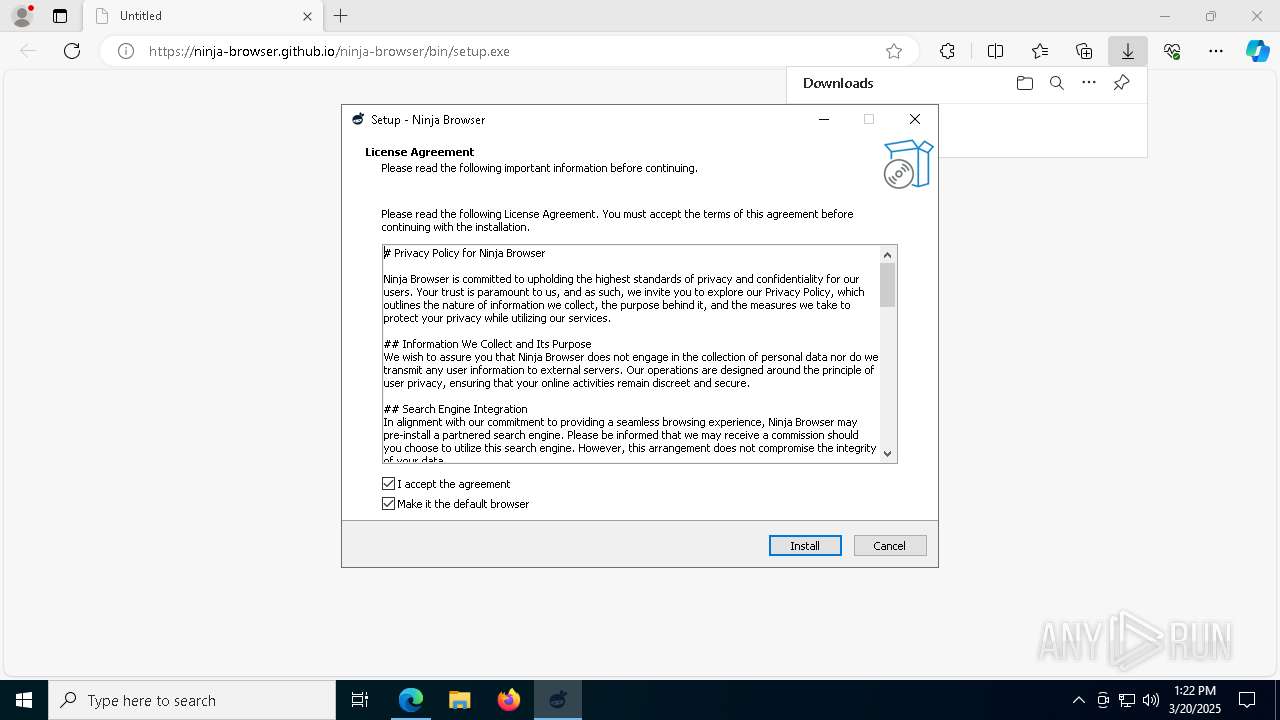
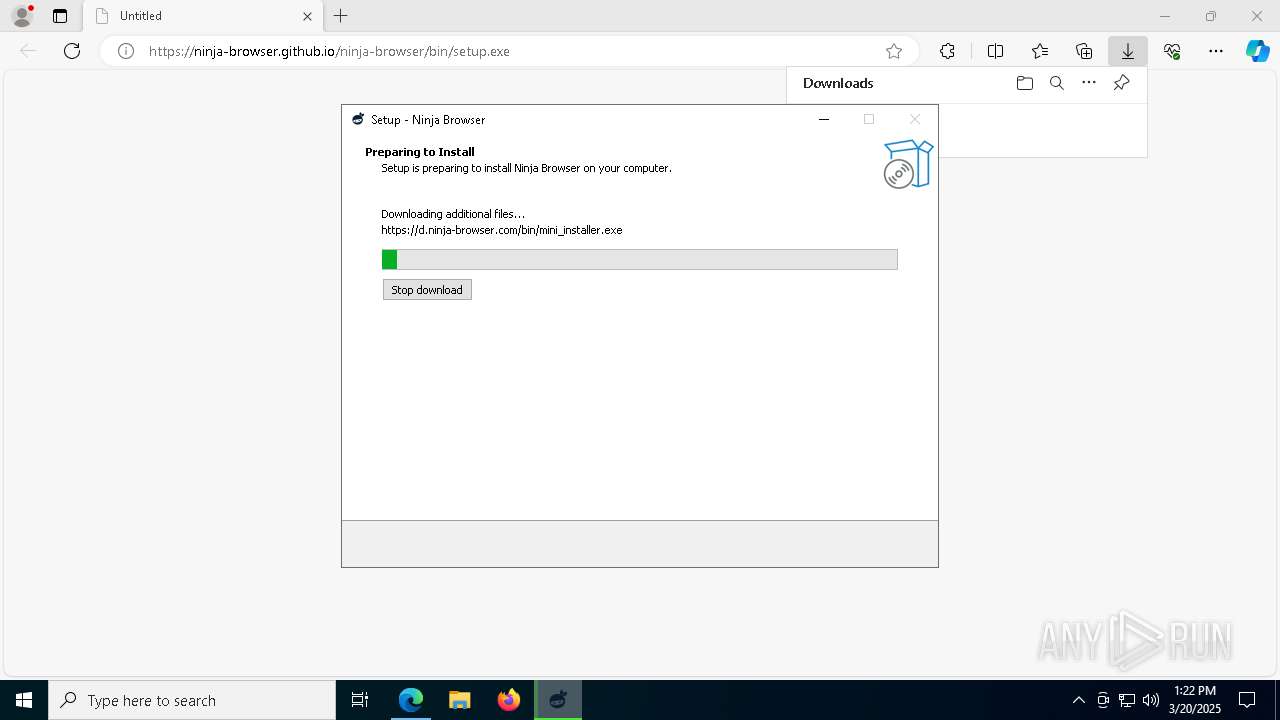
| Verdict: | Malicious activity |
| Analysis date: | March 20, 2025, 13:21:53 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 8E1D9598284DBEFBB35C63FC38DCCD75 |
| SHA1: | CF3E8B8A5428B47723D96EB1A9DCF68E64CEE2AE |
| SHA256: | B8926B7C222A2786E4471BD47342F6892B05C21DA8EBC3F459AC84AF648053DE |
| SSDEEP: | 3:N8CX2MErBzX9+H2VL4A:2CmMEBz0SL4A |
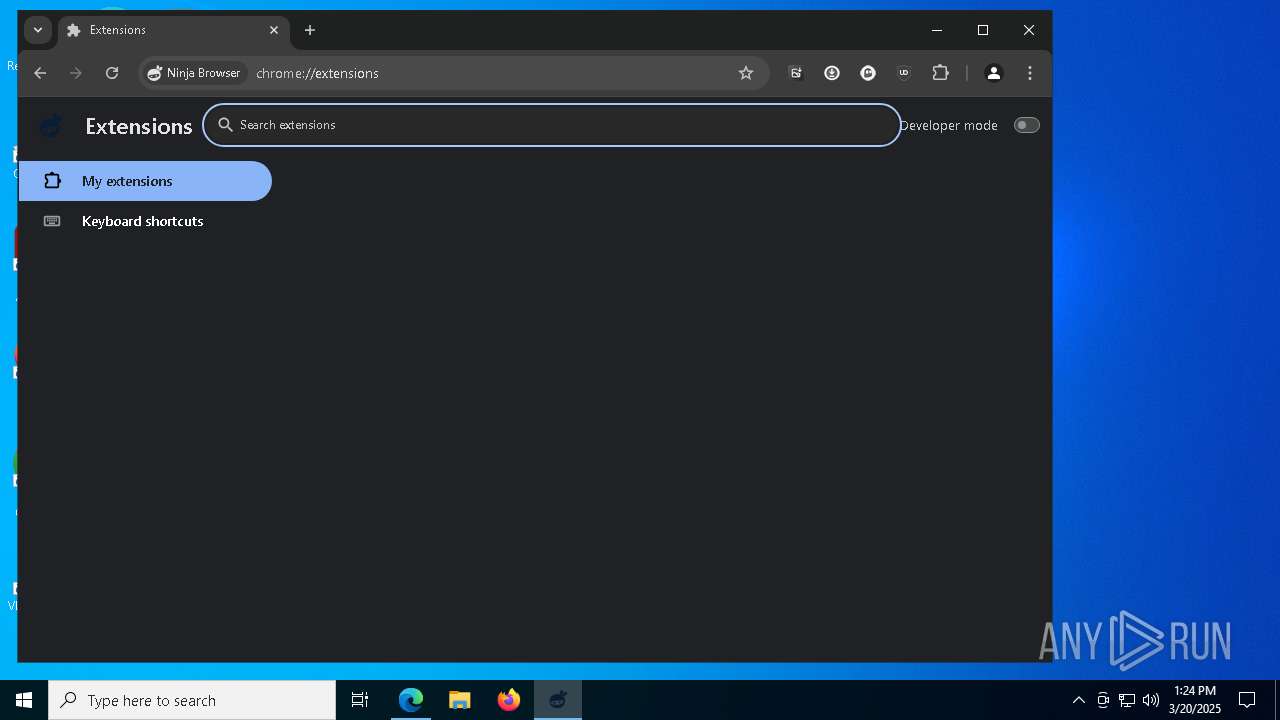
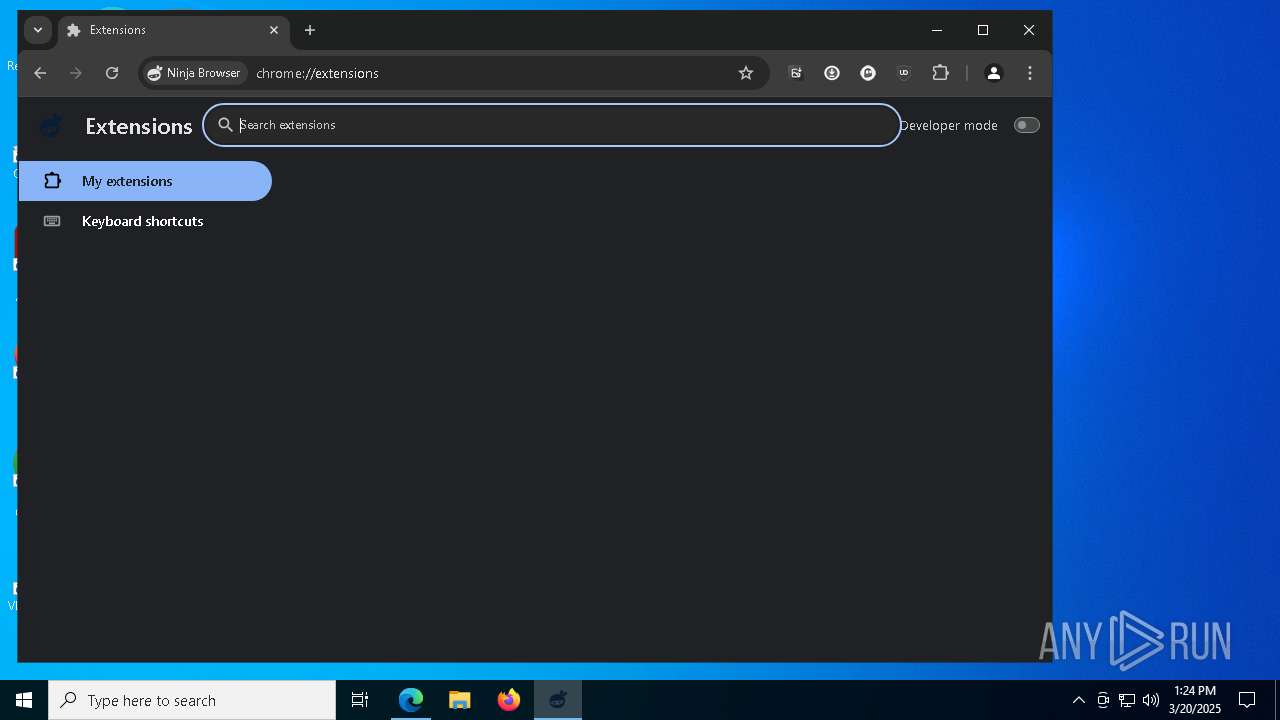
MALICIOUS
PHISHING has been detected (SURICATA)
- svchost.exe (PID: 2196)
- NinjaBrowser.exe (PID: 7144)
Changes the autorun value in the registry
- setup.exe (PID: 8100)
Uses Task Scheduler to run other applications
- setup.tmp (PID: 8700)
Uses Task Scheduler to autorun other applications
- setup.tmp (PID: 8700)
Creates a new registry key or changes the value of an existing one (SCRIPT)
- mshta.exe (PID: 5328)
- mshta.exe (PID: 8916)
- mshta.exe (PID: 7152)
SUSPICIOUS
Creates file in the systems drive root
- msedge.exe (PID: 6032)
- chromium.exe (PID: 6656)
- setup.exe (PID: 8100)
- chromium.exe (PID: 6676)
Executable content was dropped or overwritten
- setup.exe (PID: 8684)
- setup.tmp (PID: 8700)
- chromium.exe (PID: 6656)
- setup.exe (PID: 8100)
- chromium.exe (PID: 6676)
- setup.exe (PID: 1388)
- setup.exe (PID: 8540)
Reads the Windows owner or organization settings
- setup.tmp (PID: 8700)
Creates a software uninstall entry
- setup.exe (PID: 8100)
Application launched itself
- setup.exe (PID: 8100)
- NinjaBrowser.exe (PID: 2092)
- chrmstp.exe (PID: 3032)
Searches for installed software
- setup.exe (PID: 8276)
- setup.exe (PID: 1388)
- setup.exe (PID: 8100)
- chrmstp.exe (PID: 3032)
- chrmstp.exe (PID: 4736)
There is functionality for taking screenshot (YARA)
- setup.exe (PID: 8100)
Reads security settings of Internet Explorer
- setup.tmp (PID: 8556)
- chrmstp.exe (PID: 4736)
INFO
Checks supported languages
- identity_helper.exe (PID: 5988)
- setup.exe (PID: 8540)
- setup.exe (PID: 8684)
- setup.tmp (PID: 8700)
- chromium.exe (PID: 6656)
- setup.exe (PID: 8100)
- setup.exe (PID: 8276)
- chromium.exe (PID: 6676)
- setup.exe (PID: 1388)
- def.exe (PID: 8220)
- def.exe (PID: 7824)
- NinjaBrowser.exe (PID: 2092)
- NinjaBrowser.exe (PID: 9196)
- def.exe (PID: 8776)
- def.exe (PID: 9036)
- setup.tmp (PID: 8556)
- NinjaBrowser.exe (PID: 8092)
- NinjaBrowser.exe (PID: 4000)
- NinjaBrowser.exe (PID: 2236)
- NinjaBrowser.exe (PID: 5172)
- NinjaBrowser.exe (PID: 4212)
- NinjaBrowser.exe (PID: 8400)
- NinjaBrowser.exe (PID: 5228)
- NinjaBrowser.exe (PID: 5116)
- NinjaBrowser.exe (PID: 8456)
- NinjaBrowser.exe (PID: 668)
- NinjaBrowser.exe (PID: 2908)
- NinjaBrowser.exe (PID: 8428)
- NinjaBrowser.exe (PID: 4188)
- NinjaBrowser.exe (PID: 5964)
- NinjaBrowser.exe (PID: 856)
- NinjaBrowser.exe (PID: 8464)
- NinjaBrowser.exe (PID: 1532)
- NinjaBrowser.exe (PID: 5640)
- NinjaBrowser.exe (PID: 516)
- NinjaBrowser.exe (PID: 8868)
- NinjaBrowser.exe (PID: 6244)
- NinjaBrowser.exe (PID: 8772)
- NinjaBrowser.exe (PID: 8856)
- NinjaBrowser.exe (PID: 9036)
- NinjaBrowser.exe (PID: 3124)
- NinjaBrowser.exe (PID: 8848)
- NinjaBrowser.exe (PID: 7940)
- NinjaBrowser.exe (PID: 7988)
- NinjaBrowser.exe (PID: 9044)
- NinjaBrowser.exe (PID: 8836)
- NinjaBrowser.exe (PID: 3192)
- NinjaBrowser.exe (PID: 2780)
- NinjaBrowser.exe (PID: 8768)
- NinjaBrowser.exe (PID: 8504)
- NinjaBrowser.exe (PID: 5408)
- NinjaBrowser.exe (PID: 5072)
- NinjaBrowser.exe (PID: 8212)
- NinjaBrowser.exe (PID: 8928)
- NinjaBrowser.exe (PID: 444)
- NinjaBrowser.exe (PID: 8484)
- NinjaBrowser.exe (PID: 644)
- NinjaBrowser.exe (PID: 9076)
- NinjaBrowser.exe (PID: 5404)
- NinjaBrowser.exe (PID: 536)
- NinjaBrowser.exe (PID: 8208)
- NinjaBrowser.exe (PID: 1184)
- NinjaBrowser.exe (PID: 6740)
- NinjaBrowser.exe (PID: 8988)
- NinjaBrowser.exe (PID: 7244)
- NinjaBrowser.exe (PID: 7888)
- NinjaBrowser.exe (PID: 4464)
- NinjaBrowser.exe (PID: 1568)
- NinjaBrowser.exe (PID: 8440)
- NinjaBrowser.exe (PID: 9048)
- NinjaBrowser.exe (PID: 8908)
- NinjaBrowser.exe (PID: 8952)
- chrmstp.exe (PID: 4736)
- NinjaBrowser.exe (PID: 8740)
- chrmstp.exe (PID: 3032)
- NinjaBrowser.exe (PID: 7972)
- NinjaBrowser.exe (PID: 1184)
- NinjaBrowser.exe (PID: 6228)
- NinjaBrowser.exe (PID: 8436)
- NinjaBrowser.exe (PID: 8260)
- NinjaBrowser.exe (PID: 5964)
- NinjaBrowser.exe (PID: 5244)
- NinjaBrowser.exe (PID: 4108)
- NinjaBrowser.exe (PID: 2692)
- NinjaBrowser.exe (PID: 8484)
Reads Environment values
- identity_helper.exe (PID: 5988)
Reads the computer name
- identity_helper.exe (PID: 5988)
- setup.tmp (PID: 8700)
- chromium.exe (PID: 6656)
- setup.exe (PID: 8100)
- setup.exe (PID: 8276)
- chromium.exe (PID: 6676)
- setup.tmp (PID: 8556)
- def.exe (PID: 8220)
- def.exe (PID: 7824)
- NinjaBrowser.exe (PID: 2092)
- NinjaBrowser.exe (PID: 9196)
- NinjaBrowser.exe (PID: 7144)
- def.exe (PID: 8776)
- def.exe (PID: 9036)
- setup.exe (PID: 8684)
- NinjaBrowser.exe (PID: 7972)
- chrmstp.exe (PID: 4736)
Executable content was dropped or overwritten
- msedge.exe (PID: 6032)
- msedge.exe (PID: 7340)
- msedge.exe (PID: 132)
Create files in a temporary directory
- setup.exe (PID: 8684)
- setup.tmp (PID: 8700)
- chromium.exe (PID: 6656)
- chromium.exe (PID: 6676)
- setup.exe (PID: 8540)
- def.exe (PID: 8220)
- def.exe (PID: 904)
- def.exe (PID: 7824)
- NinjaBrowser.exe (PID: 2092)
Application launched itself
- msedge.exe (PID: 6032)
Detects InnoSetup installer (YARA)
- setup.exe (PID: 8540)
- setup.tmp (PID: 8556)
- setup.exe (PID: 8684)
- setup.tmp (PID: 8700)
Reads the software policy settings
- setup.tmp (PID: 8700)
- slui.exe (PID: 4608)
- slui.exe (PID: 4220)
Compiled with Borland Delphi (YARA)
- setup.exe (PID: 8540)
- setup.exe (PID: 8684)
- setup.tmp (PID: 8556)
- setup.tmp (PID: 8700)
Checks proxy server information
- setup.tmp (PID: 8700)
- slui.exe (PID: 4220)
- NinjaBrowser.exe (PID: 2092)
Creates files in the program directory
- setup.tmp (PID: 8700)
- setup.exe (PID: 8100)
- setup.exe (PID: 8276)
- setup.exe (PID: 1388)
The sample compiled with english language support
- setup.tmp (PID: 8700)
- chromium.exe (PID: 6656)
- setup.exe (PID: 8100)
- chromium.exe (PID: 6676)
- setup.exe (PID: 1388)
- msedge.exe (PID: 132)
Autorun file from Registry key
- setup.exe (PID: 8100)
Creates files or folders in the user directory
- setup.exe (PID: 8276)
- NinjaBrowser.exe (PID: 2092)
- NinjaBrowser.exe (PID: 7144)
- NinjaBrowser.exe (PID: 8764)
Process checks computer location settings
- setup.tmp (PID: 8556)
- NinjaBrowser.exe (PID: 4000)
- NinjaBrowser.exe (PID: 5172)
- NinjaBrowser.exe (PID: 5404)
- NinjaBrowser.exe (PID: 8208)
- NinjaBrowser.exe (PID: 6228)
- NinjaBrowser.exe (PID: 4464)
- NinjaBrowser.exe (PID: 8988)
- NinjaBrowser.exe (PID: 644)
- NinjaBrowser.exe (PID: 8440)
- NinjaBrowser.exe (PID: 8908)
- NinjaBrowser.exe (PID: 8740)
- NinjaBrowser.exe (PID: 8436)
- NinjaBrowser.exe (PID: 8260)
- NinjaBrowser.exe (PID: 5244)
- NinjaBrowser.exe (PID: 5964)
- NinjaBrowser.exe (PID: 2692)
- NinjaBrowser.exe (PID: 4108)
Autorun file from Task Scheduler
- setup.tmp (PID: 8700)
Reads Internet Explorer settings
- mshta.exe (PID: 4040)
- mshta.exe (PID: 5328)
- mshta.exe (PID: 8916)
- mshta.exe (PID: 7852)
- mshta.exe (PID: 7152)
- mshta.exe (PID: 8932)
Reads the machine GUID from the registry
- NinjaBrowser.exe (PID: 2092)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
304
Monitored processes
164
Malicious processes
18
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6788 --field-trial-handle=2404,i,2594607558125089899,12555236603759678903,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 444 | "C:\Program Files (x86)\NinjaBrowser\NinjaBrowser\Application\NinjaBrowser.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --field-trial-handle=8744,i,5994755855194034930,9835256788319953294,262144 --variations-seed-version --mojo-platform-channel-handle=8920 /prefetch:8 | C:\Program Files (x86)\NinjaBrowser\NinjaBrowser\Application\NinjaBrowser.exe | — | NinjaBrowser.exe | |||||||||||
User: admin Company: The Ninja Browser Authors Integrity Level: LOW Description: Ninja Browser Exit code: 0 Version: 133.0.6613.124 Modules
| |||||||||||||||
| 516 | "C:\Program Files (x86)\NinjaBrowser\NinjaBrowser\Application\NinjaBrowser.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --field-trial-handle=5632,i,5994755855194034930,9835256788319953294,262144 --variations-seed-version --mojo-platform-channel-handle=5696 /prefetch:8 | C:\Program Files (x86)\NinjaBrowser\NinjaBrowser\Application\NinjaBrowser.exe | — | NinjaBrowser.exe | |||||||||||
User: admin Company: The Ninja Browser Authors Integrity Level: LOW Description: Ninja Browser Exit code: 0 Version: 133.0.6613.124 Modules
| |||||||||||||||
| 536 | "C:\Program Files (x86)\NinjaBrowser\NinjaBrowser\Application\NinjaBrowser.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --field-trial-handle=10756,i,5994755855194034930,9835256788319953294,262144 --variations-seed-version --mojo-platform-channel-handle=6736 /prefetch:8 | C:\Program Files (x86)\NinjaBrowser\NinjaBrowser\Application\NinjaBrowser.exe | — | NinjaBrowser.exe | |||||||||||
User: admin Company: The Ninja Browser Authors Integrity Level: LOW Description: Ninja Browser Exit code: 0 Version: 133.0.6613.124 Modules
| |||||||||||||||
| 644 | "C:\Program Files (x86)\NinjaBrowser\NinjaBrowser\Application\NinjaBrowser.exe" --type=renderer --extension-process --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=57 --field-trial-handle=8816,i,5994755855194034930,9835256788319953294,262144 --variations-seed-version --mojo-platform-channel-handle=7536 /prefetch:2 | C:\Program Files (x86)\NinjaBrowser\NinjaBrowser\Application\NinjaBrowser.exe | — | NinjaBrowser.exe | |||||||||||
User: admin Company: The Ninja Browser Authors Integrity Level: LOW Description: Ninja Browser Exit code: 0 Version: 133.0.6613.124 Modules
| |||||||||||||||
| 660 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4368 --field-trial-handle=2404,i,2594607558125089899,12555236603759678903,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 668 | "C:\Program Files (x86)\NinjaBrowser\NinjaBrowser\Application\NinjaBrowser.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --field-trial-handle=5636,i,5994755855194034930,9835256788319953294,262144 --variations-seed-version --mojo-platform-channel-handle=4960 /prefetch:8 | C:\Program Files (x86)\NinjaBrowser\NinjaBrowser\Application\NinjaBrowser.exe | — | NinjaBrowser.exe | |||||||||||
User: admin Company: The Ninja Browser Authors Integrity Level: LOW Description: Ninja Browser Exit code: 0 Version: 133.0.6613.124 Modules
| |||||||||||||||
| 728 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4384 --field-trial-handle=2404,i,2594607558125089899,12555236603759678903,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 736 | "schtasks" /Create /F /SC ONLOGON /TN "NinjaBrowserUpdateLog" /RL HIGHEST /TR "'C:\Program Files (x86)\NinjaBrowser\2003132309\updater.exe' /VERYSILENT /SUPPRESSMSGBOXES" | C:\Windows\SysWOW64\schtasks.exe | — | setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 856 | "C:\Program Files (x86)\NinjaBrowser\NinjaBrowser\Application\NinjaBrowser.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --field-trial-handle=5144,i,5994755855194034930,9835256788319953294,262144 --variations-seed-version --mojo-platform-channel-handle=5268 /prefetch:8 | C:\Program Files (x86)\NinjaBrowser\NinjaBrowser\Application\NinjaBrowser.exe | — | NinjaBrowser.exe | |||||||||||
User: admin Company: The Ninja Browser Authors Integrity Level: LOW Description: Ninja Browser Exit code: 0 Version: 133.0.6613.124 Modules
| |||||||||||||||
Total events
19 142
Read events
18 667
Write events
433
Delete events
42
Modification events
| (PID) Process: | (4944) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4944) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4944) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4944) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (4944) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (4944) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (6032) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6032) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6032) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6032) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
38
Suspicious files
1 257
Text files
1 004
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b76b.TMP | — | |
MD5:— | SHA256:— | |||
| 6032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b76b.TMP | — | |
MD5:— | SHA256:— | |||
| 6032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b76b.TMP | — | |
MD5:— | SHA256:— | |||
| 6032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b77a.TMP | — | |
MD5:— | SHA256:— | |||
| 6032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b77a.TMP | — | |
MD5:— | SHA256:— | |||
| 6032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
53
TCP/UDP connections
70
DNS requests
97
Threats
22
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.194:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
672 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6032 | msedge.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/gsgccr45evcodesignca2020/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBQaCbVYh07WONuW4e63Ydlu4AlbDAQUJZ3Q%2FFkJhmPF7POxEztXHAOSNhECDB4WVKmt8yfHHrQPdw%3D%3D | unknown | — | — | whitelisted |
6032 | msedge.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/codesigningrootr45/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQVFZP5vqhCrtRN5SWf40Rn6NM1IAQUHwC%2FRoAK%2FHg5t6W0Q9lWULvOljsCEHe9DgW3WQu2HUdhUx4%2Fde0%3D | unknown | — | — | whitelisted |
5608 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c269ced-c74b-4e70-9b58-6e7999b292c0?P1=1742990954&P2=404&P3=2&P4=L3conSUwGLPsUWAxtMaEdrMvWbIN35BUNAmtQxotU9yY1pDheD6zHGtnv%2fWSF5fyWCp%2b0z3H1Jy5D5%2fiH7lK7g%3d%3d | unknown | — | — | whitelisted |
8740 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8740 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5608 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c269ced-c74b-4e70-9b58-6e7999b292c0?P1=1742990954&P2=404&P3=2&P4=L3conSUwGLPsUWAxtMaEdrMvWbIN35BUNAmtQxotU9yY1pDheD6zHGtnv%2fWSF5fyWCp%2b0z3H1Jy5D5%2fiH7lK7g%3d%3d | unknown | — | — | whitelisted |
5608 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c269ced-c74b-4e70-9b58-6e7999b292c0?P1=1742990954&P2=404&P3=2&P4=L3conSUwGLPsUWAxtMaEdrMvWbIN35BUNAmtQxotU9yY1pDheD6zHGtnv%2fWSF5fyWCp%2b0z3H1Jy5D5%2fiH7lK7g%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.194:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6032 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7340 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7340 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7340 | msedge.exe | 216.58.206.35:443 | update.googleapis.com | GOOGLE | US | whitelisted |
7340 | msedge.exe | 185.199.111.153:443 | ninja-browser.github.io | FASTLY | US | shared |
7340 | msedge.exe | 92.123.104.32:443 | edgeservices.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
ninja-browser.github.io |
| unknown |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
edgeservices.bing.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain by CrossDomain ( .ninja-browser .com) |
7144 | NinjaBrowser.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7144 | NinjaBrowser.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7144 | NinjaBrowser.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7144 | NinjaBrowser.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7144 | NinjaBrowser.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7144 | NinjaBrowser.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7144 | NinjaBrowser.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7144 | NinjaBrowser.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7144 | NinjaBrowser.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |