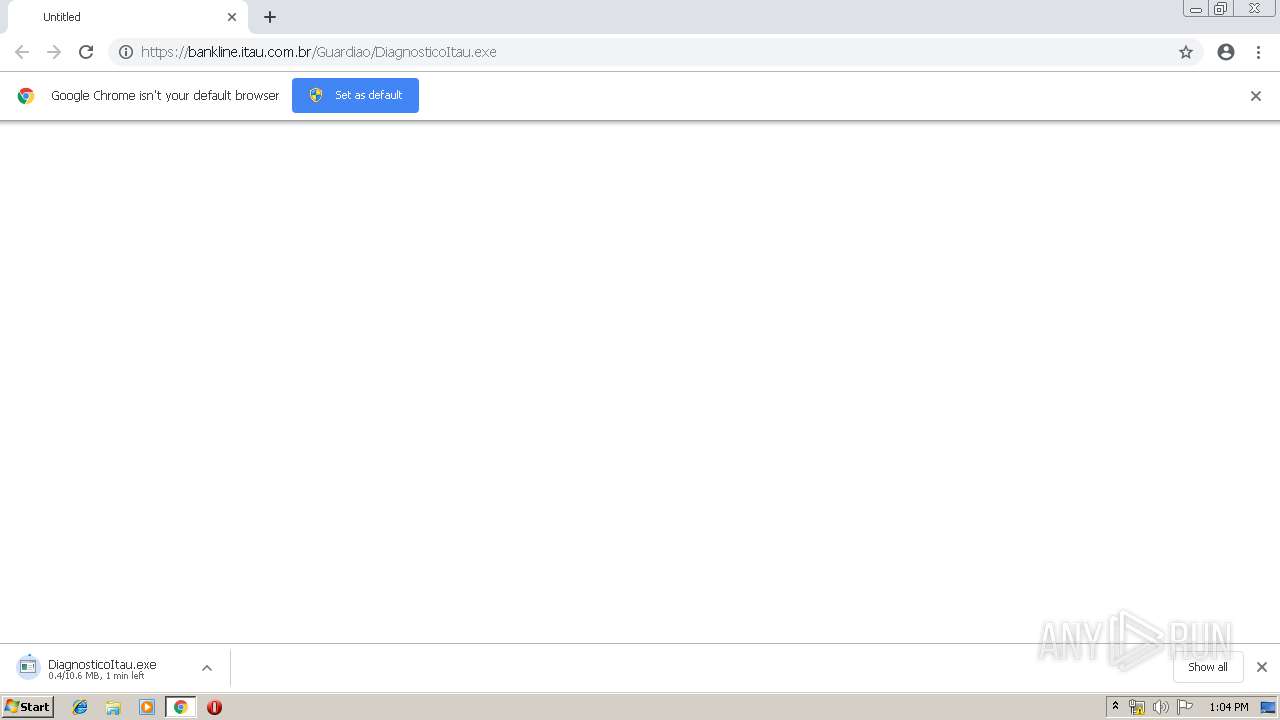
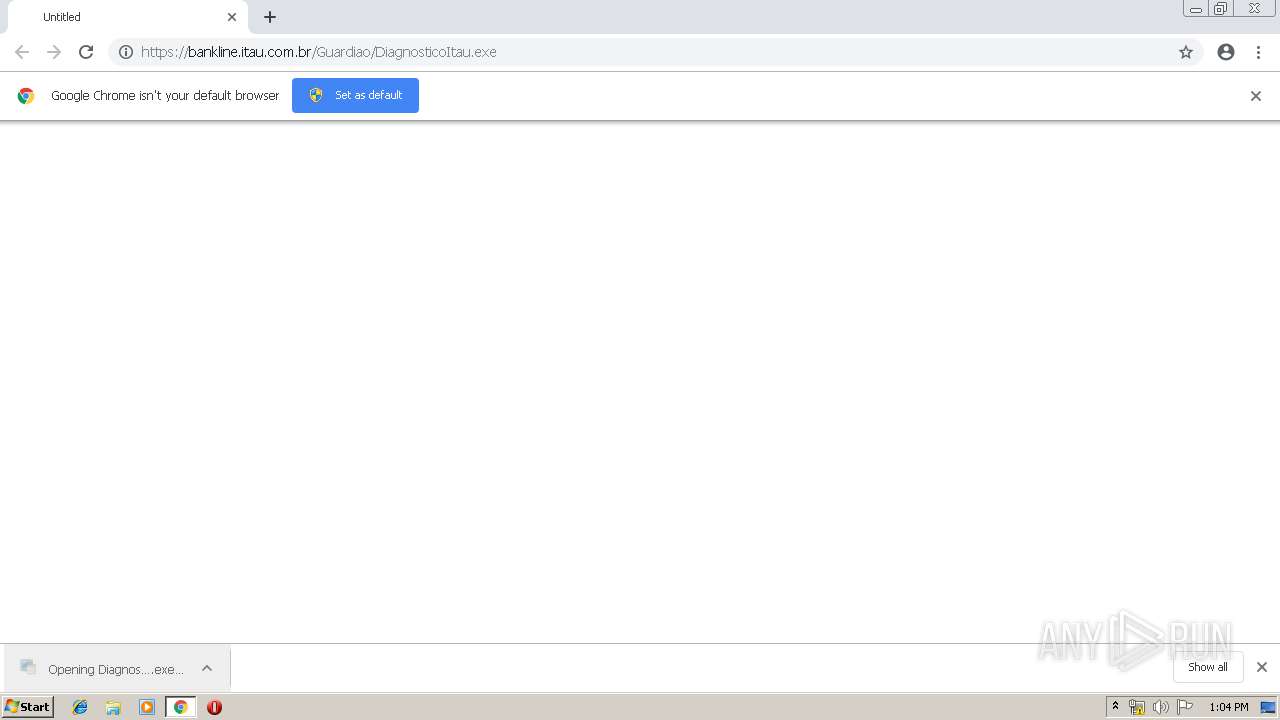
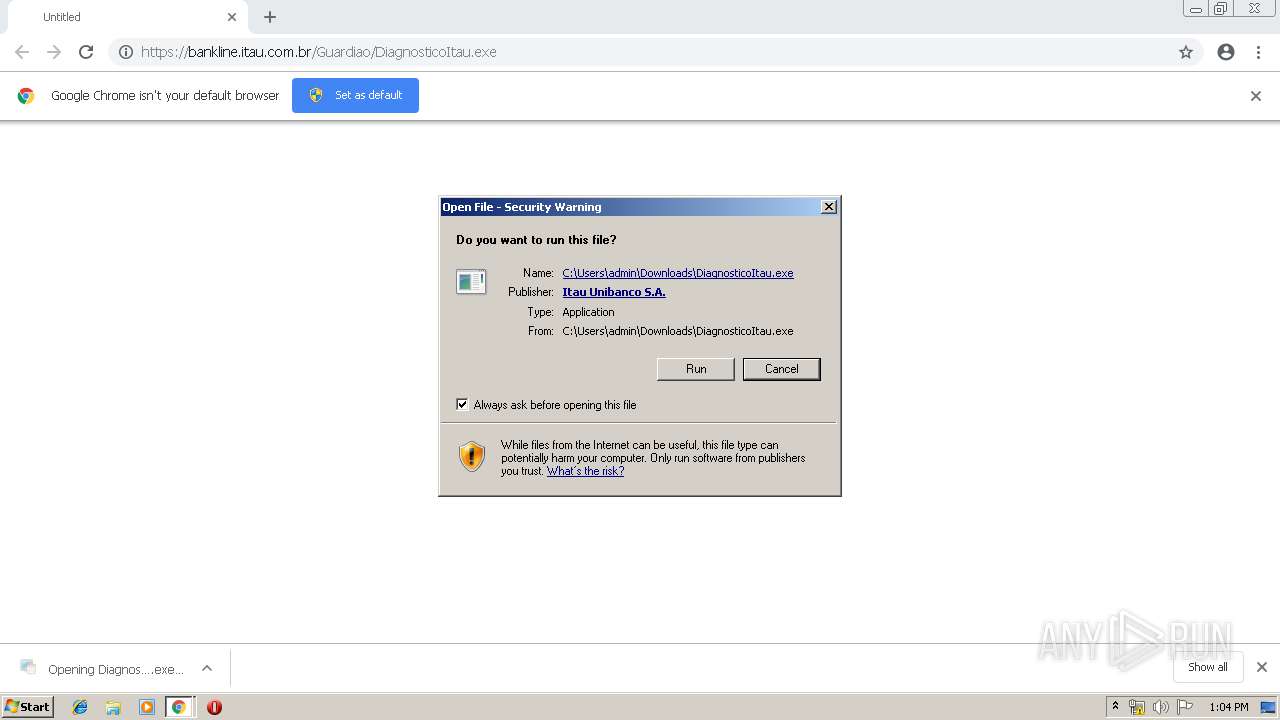
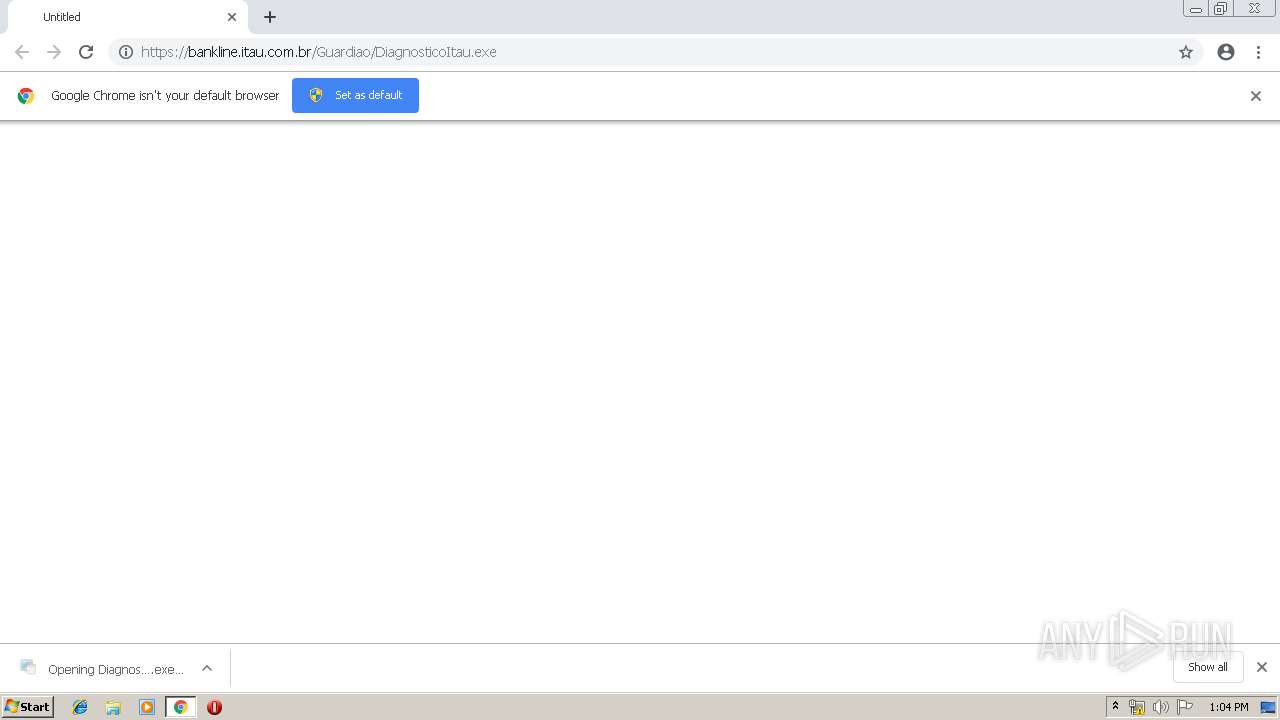
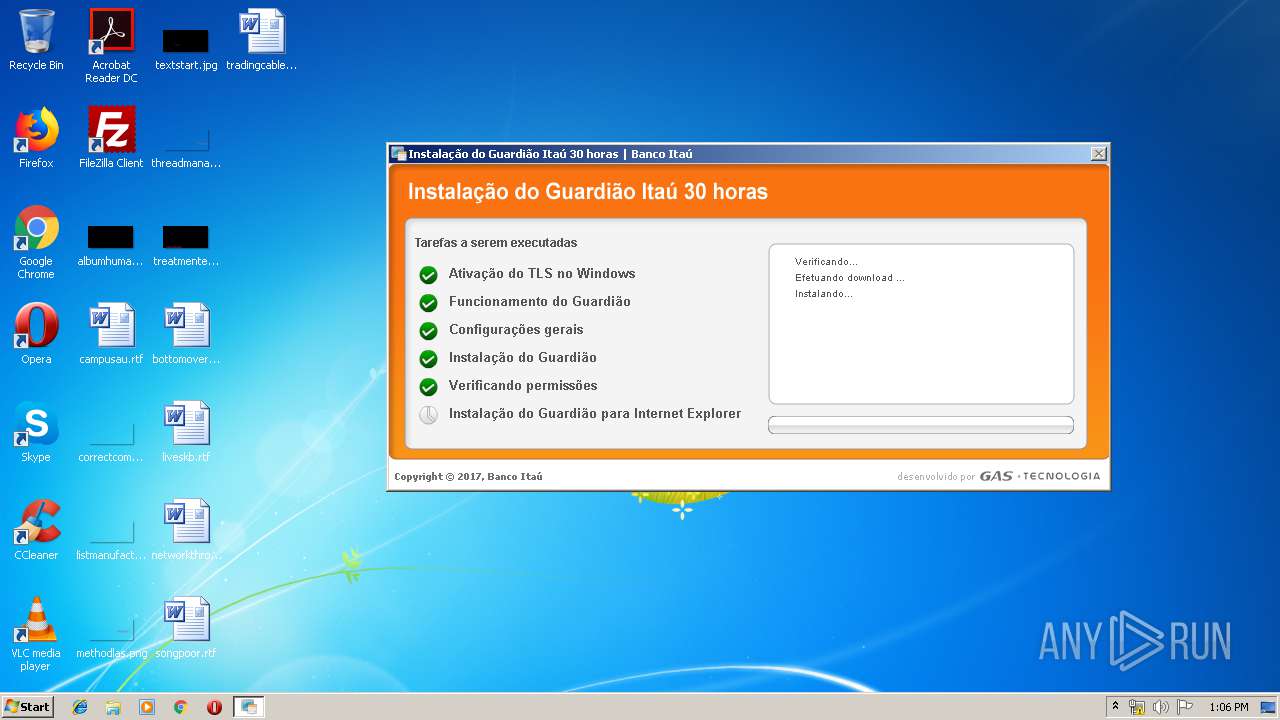
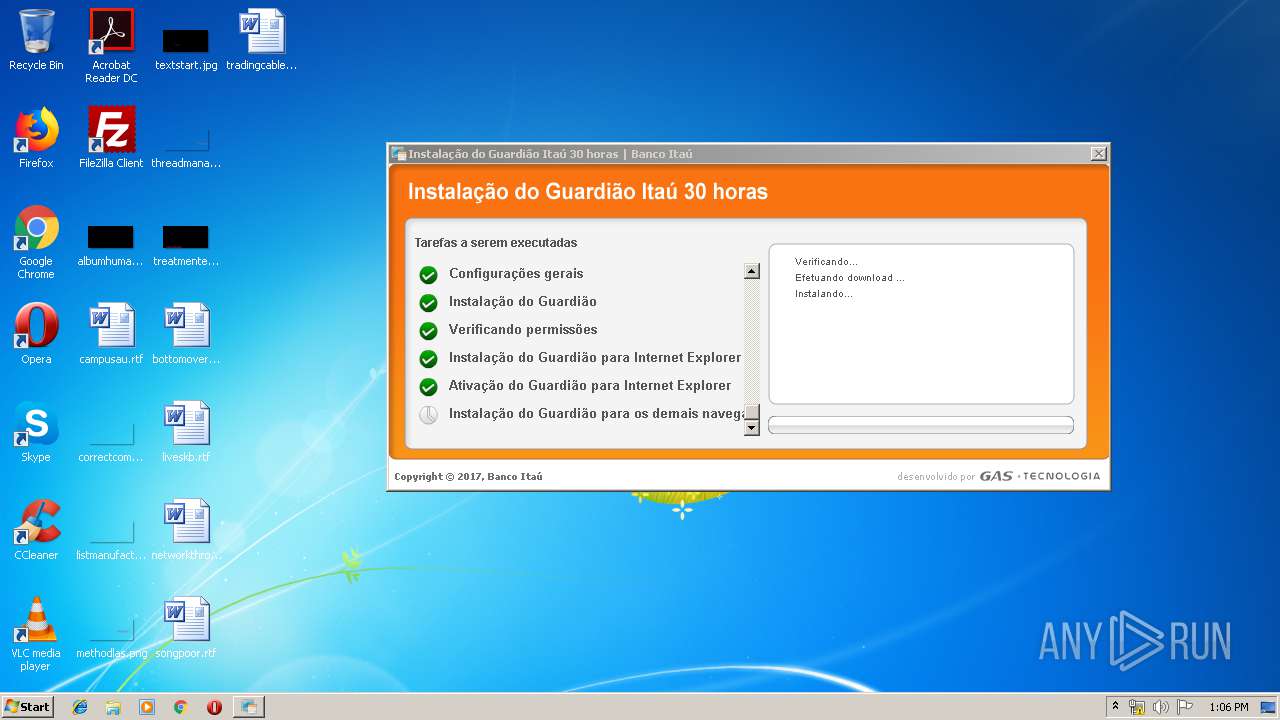
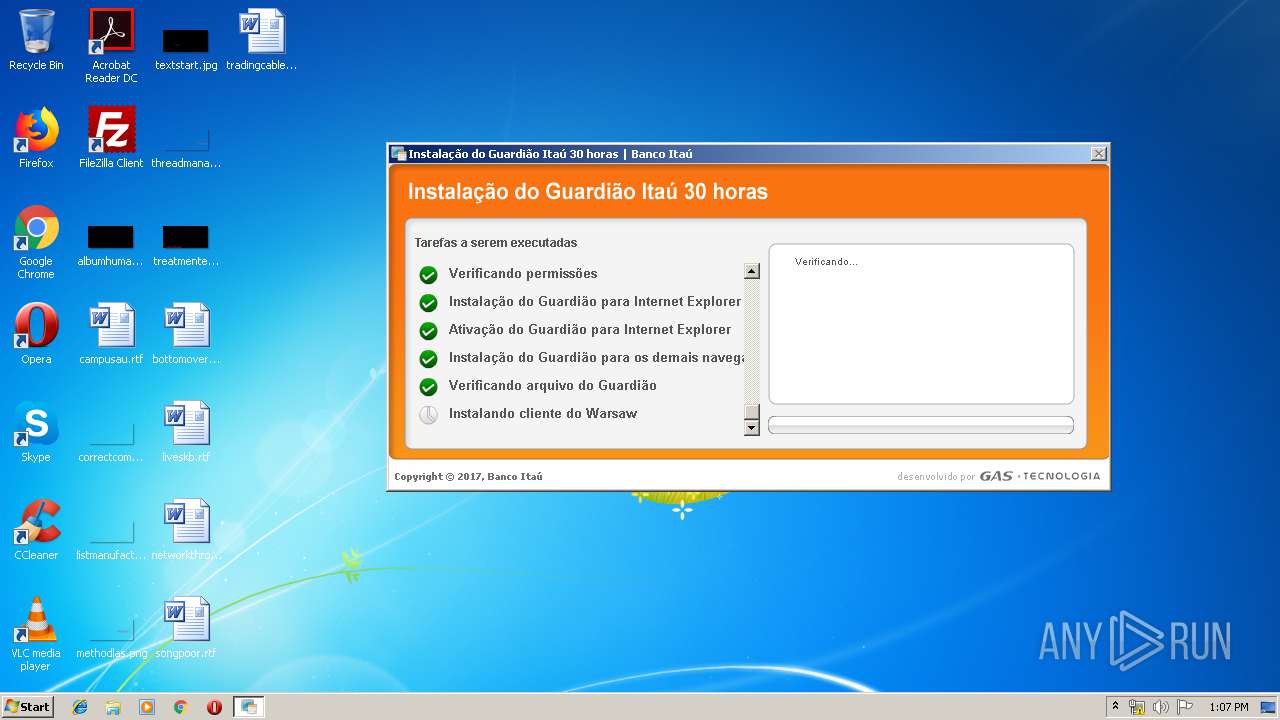
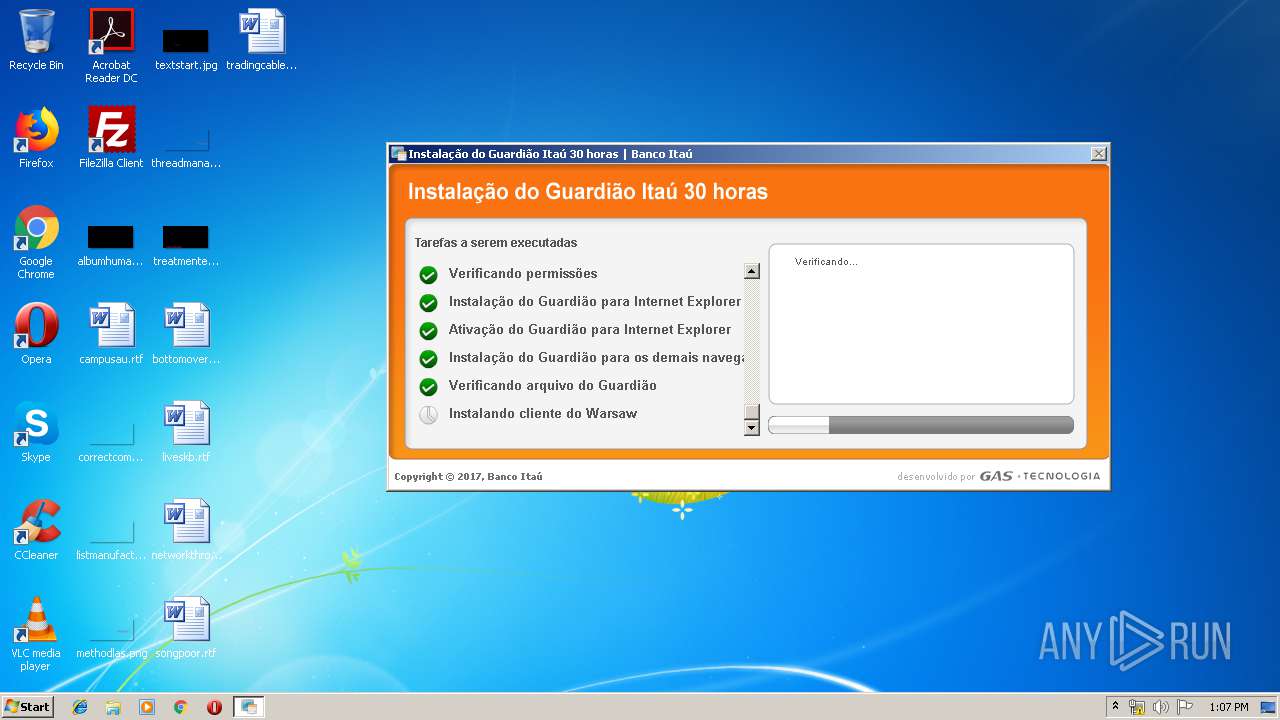
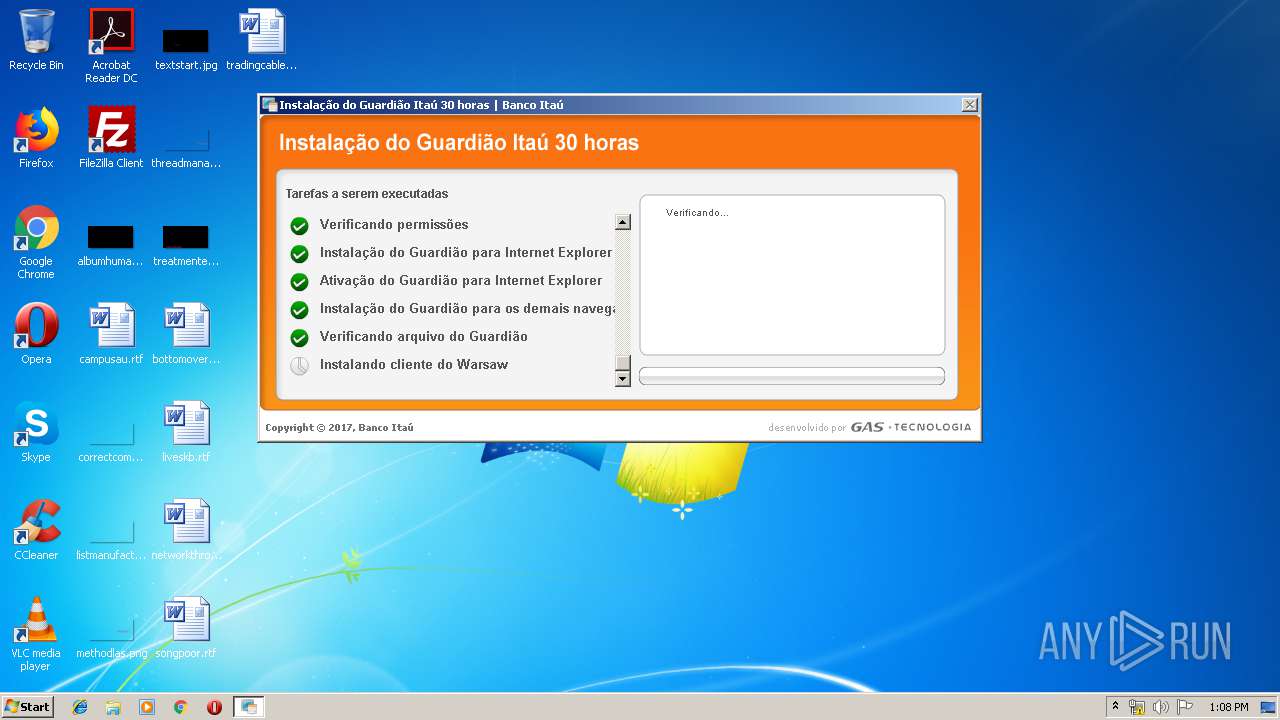
| URL: | https://bankline.itau.com.br/Guardiao/DiagnosticoItau.exe |
| Full analysis: | https://app.any.run/tasks/4d7febe5-c9bf-45aa-84d9-f2a252040ef2 |
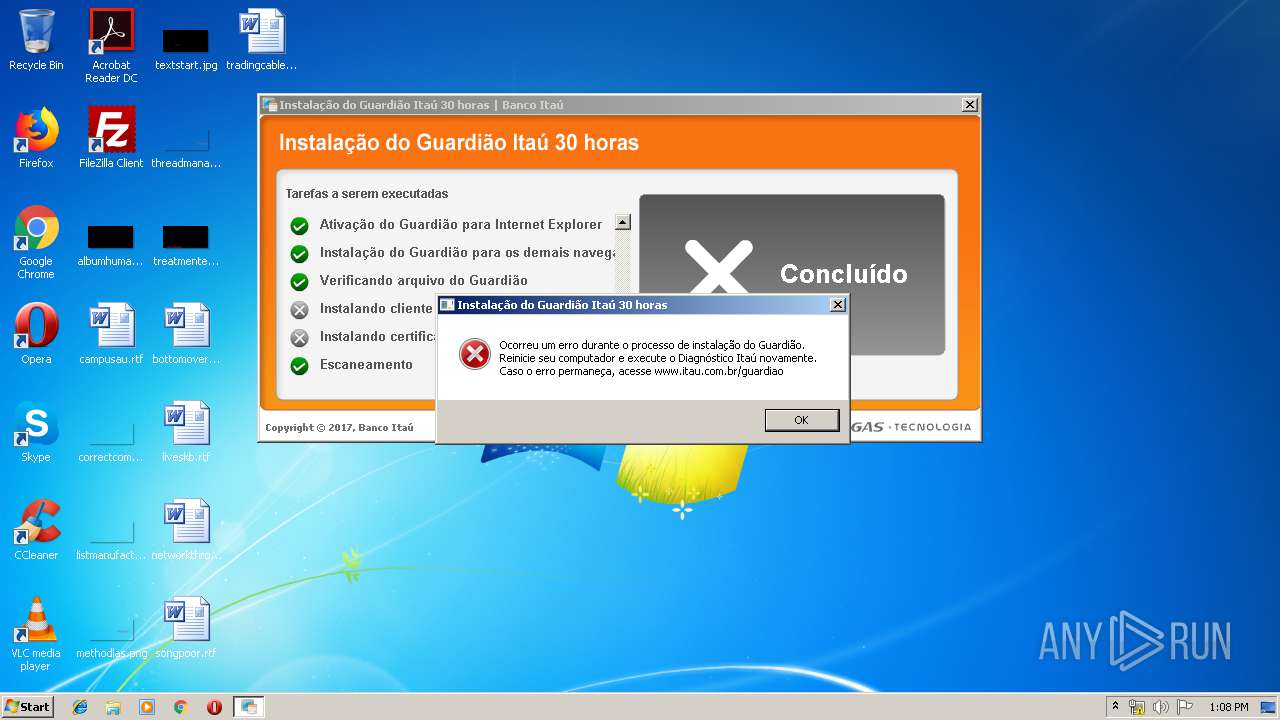
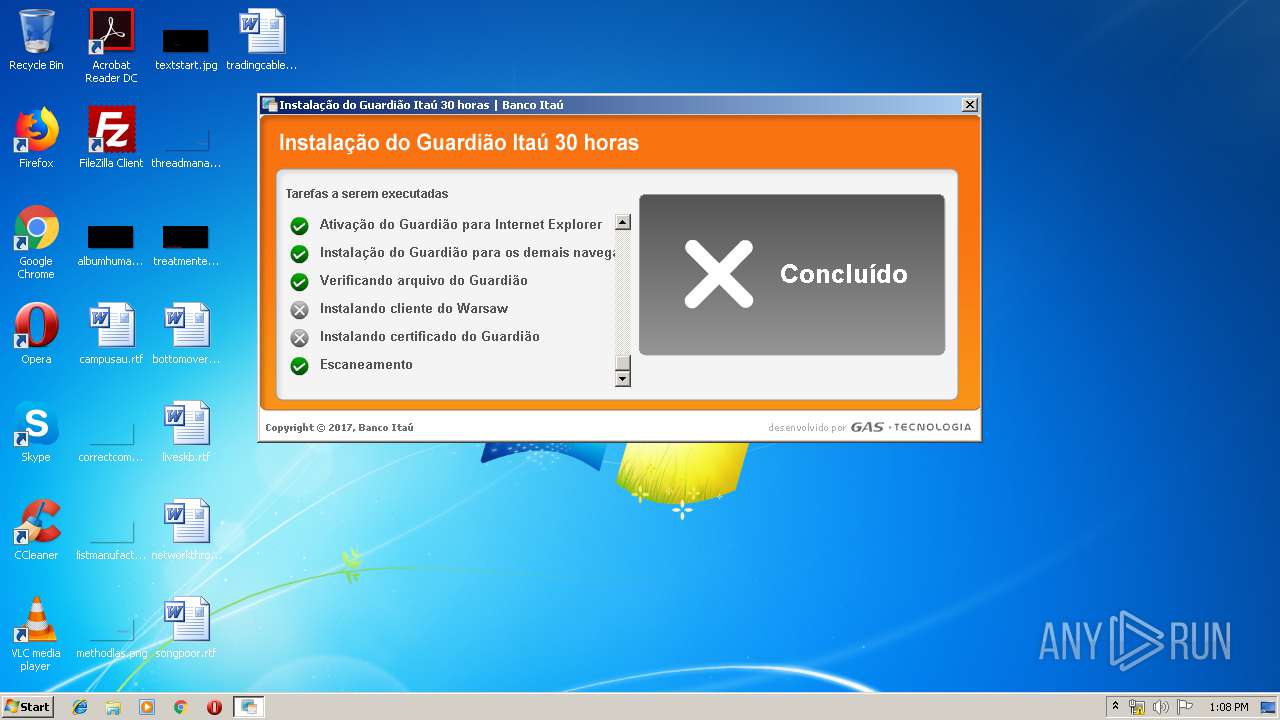
| Verdict: | Malicious activity |
| Analysis date: | May 01, 2019, 12:03:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 576151112AE2FF9992D390BCDE32B276 |
| SHA1: | 0E8119EBF85EF93B6650C91A23751B04333D1AD7 |
| SHA256: | B88A71100218F4BE0518F31F5B7BF54AE65EDE1A78C55B8B3D9DE17357291234 |
| SSDEEP: | 3:N87CyQsKIz+0CLNRB5Jn:2eyQsKIz8LB |
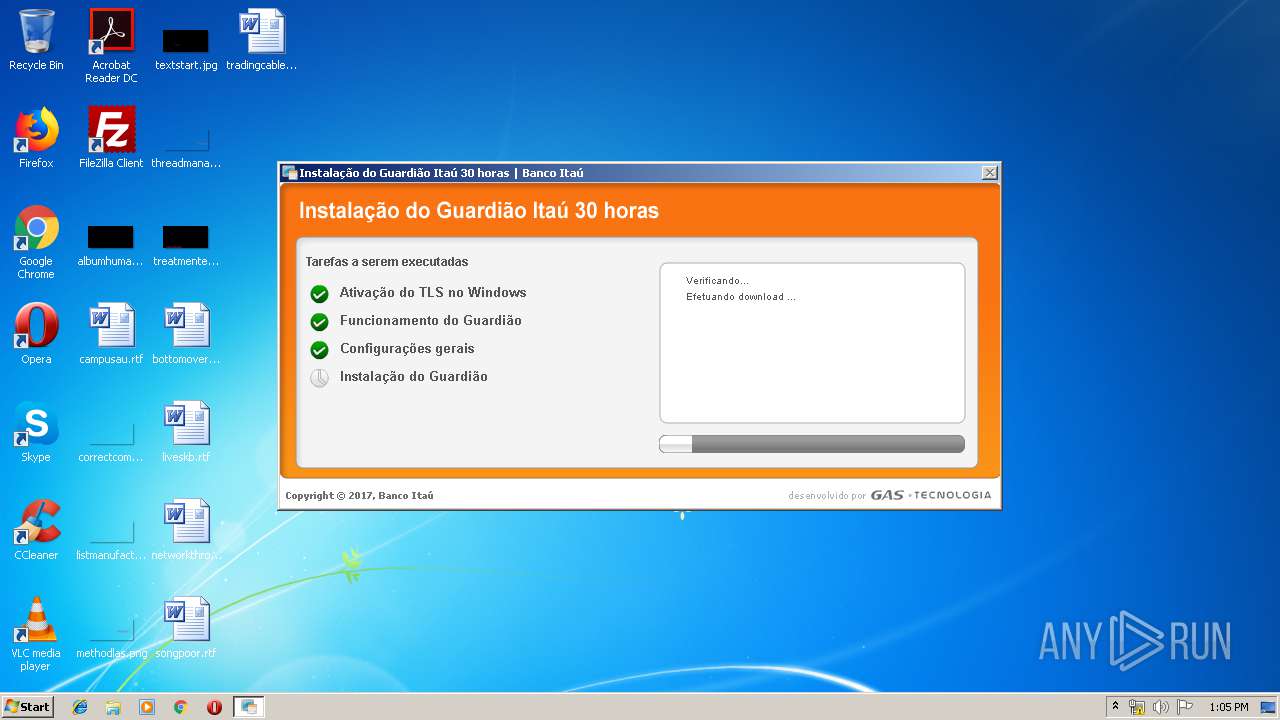
MALICIOUS
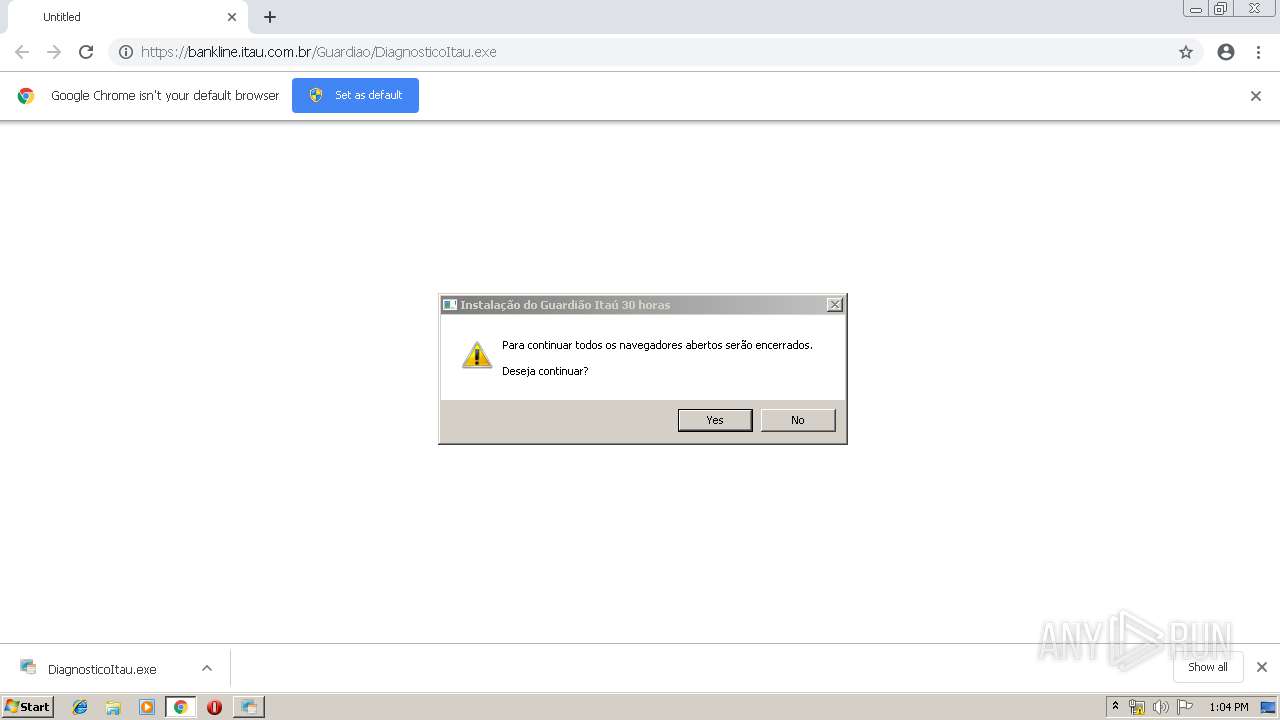
Application was dropped or rewritten from another process
- DiagnosticoItau.exe (PID: 2648)
- DiagnosticoItau.exe (PID: 3744)
- DiagnosticoItau.exe (PID: 3372)
- sf.exe (PID: 1464)
- GbpSetupUni.exe (PID: 2796)
- GbpSetupUni.tmp (PID: 4028)
- GbpDist.exe (PID: 3488)
- GbpSv.exe (PID: 3896)
- GbpSv.exe (PID: 2608)
- GbpSv.exe (PID: 2632)
- warsaw_setup_32.exe (PID: 4004)
- get_version.exe (PID: 912)
- warsaw_setup_32.tmp (PID: 2548)
- core.exe (PID: 612)
- core.exe (PID: 2928)
- core.exe (PID: 4012)
- impersonate.exe (PID: 3564)
- corefixer.exe (PID: 2620)
- wsffcmgr.exe (PID: 3464)
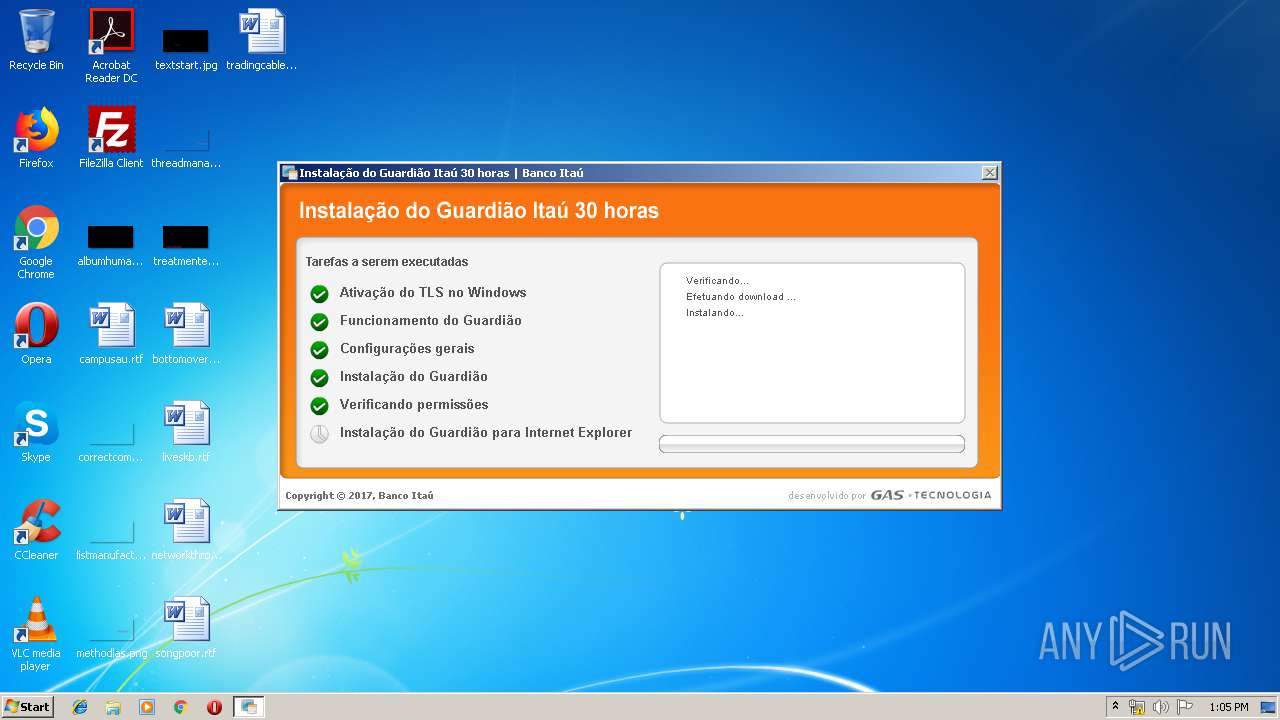
Loads the Task Scheduler COM API
- sf.exe (PID: 1464)
- corefixer.exe (PID: 2620)
Changes settings of System certificates
- sf.exe (PID: 1464)
- DiagnosticoItau.exe (PID: 3744)
- core.exe (PID: 612)
Loads dropped or rewritten executable
- GbpSetupUni.tmp (PID: 4028)
- GbpDist.exe (PID: 3488)
- windanr.exe (PID: 3844)
- dwm.exe (PID: 1980)
- DiagnosticoItau.exe (PID: 2648)
- explorer.exe (PID: 116)
- GbpSv.exe (PID: 2632)
- rundll32.exe (PID: 1640)
- core.exe (PID: 612)
- rundll32.exe (PID: 2400)
- core.exe (PID: 4012)
- core.exe (PID: 2928)
Runs injected code in another process
- GbpSv.exe (PID: 2608)
Application was injected by another process
- explorer.exe (PID: 116)
- dwm.exe (PID: 1980)
- windanr.exe (PID: 3844)
Changes internet zones settings
- DiagnosticoItau.exe (PID: 2648)
- DiagnosticoItau.exe (PID: 3744)
SUSPICIOUS
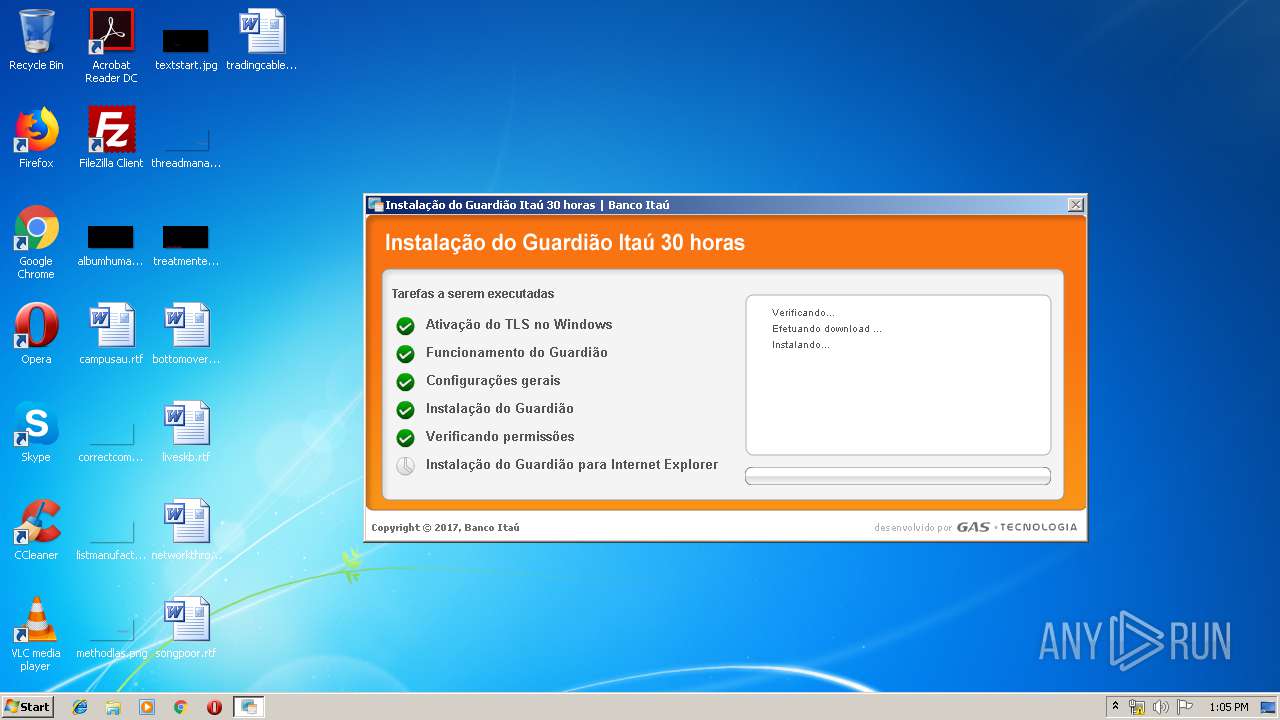
Creates files in the driver directory
- DiagnosticoItau.exe (PID: 3744)
- GbpDist.exe (PID: 3488)
- GbpSv.exe (PID: 2608)
- warsaw_setup_32.tmp (PID: 2548)
- DrvInst.exe (PID: 1664)
- core.exe (PID: 612)
Removes files from Windows directory
- DiagnosticoItau.exe (PID: 3744)
- firefox.exe (PID: 988)
- GbpSetupUni.exe (PID: 2796)
- cmd.exe (PID: 3996)
- warsaw_setup_32.tmp (PID: 2548)
- warsaw_setup_32.exe (PID: 4004)
- DrvInst.exe (PID: 1664)
- core.exe (PID: 612)
- GbpSetupUni.tmp (PID: 4028)
Application launched itself
- DiagnosticoItau.exe (PID: 2648)
- core.exe (PID: 612)
- cmd.exe (PID: 2504)
Creates files in the program directory
- DiagnosticoItau.exe (PID: 2648)
- sf.exe (PID: 1464)
- GbpSv.exe (PID: 2608)
- warsaw_setup_32.tmp (PID: 2548)
- rundll32.exe (PID: 2400)
- core.exe (PID: 612)
- GbpDist.exe (PID: 3488)
- DiagnosticoItau.exe (PID: 3744)
Executable content was dropped or overwritten
- DiagnosticoItau.exe (PID: 2648)
- GbpSetupUni.exe (PID: 2796)
- GbpSetupUni.tmp (PID: 4028)
- GbpDist.exe (PID: 3488)
- GbpSv.exe (PID: 2608)
- chrome.exe (PID: 904)
- warsaw_setup_32.exe (PID: 4004)
- warsaw_setup_32.tmp (PID: 2548)
- core.exe (PID: 612)
- DrvInst.exe (PID: 1664)
- DiagnosticoItau.exe (PID: 3744)
Creates files in the Windows directory
- sf.exe (PID: 1464)
- DiagnosticoItau.exe (PID: 3744)
- firefox.exe (PID: 988)
- GbpSetupUni.exe (PID: 2796)
- warsaw_setup_32.exe (PID: 4004)
- GbpDist.exe (PID: 3488)
- GbpSetupUni.tmp (PID: 4028)
- GbpSv.exe (PID: 2608)
- warsaw_setup_32.tmp (PID: 2548)
- get_version.exe (PID: 912)
- cmd.exe (PID: 2504)
- DrvInst.exe (PID: 1664)
- core.exe (PID: 612)
Adds / modifies Windows certificates
- DiagnosticoItau.exe (PID: 3744)
Creates or modifies windows services
- GbpSv.exe (PID: 2608)
- core.exe (PID: 612)
Uses TASKLIST.EXE to search for running browsers
- cmd.exe (PID: 408)
- cmd.exe (PID: 3580)
- cmd.exe (PID: 1720)
- cmd.exe (PID: 788)
Creates COM task schedule object
- GbpDist.exe (PID: 3488)
Starts CMD.EXE for commands execution
- GbpSetupUni.tmp (PID: 4028)
- warsaw_setup_32.tmp (PID: 2548)
- cmd.exe (PID: 2504)
Starts SC.EXE for service management
- warsaw_setup_32.tmp (PID: 2548)
Creates a software uninstall entry
- warsaw_setup_32.tmp (PID: 2548)
Uses RUNDLL32.EXE to load library
- impersonate.exe (PID: 3564)
- warsaw_setup_32.tmp (PID: 2548)
Reads Windows owner or organization settings
- warsaw_setup_32.tmp (PID: 2548)
Reads the Windows organization settings
- warsaw_setup_32.tmp (PID: 2548)
Uses TASKLIST.EXE to query information about running processes
- cmd.exe (PID: 3072)
- cmd.exe (PID: 2504)
Searches for installed software
- DrvInst.exe (PID: 1664)
Creates files in the user directory
- wsffcmgr.exe (PID: 3464)
Loads DLL from Mozilla Firefox
- wsffcmgr.exe (PID: 3464)
- DiagnosticoItau.exe (PID: 3744)
INFO
Application launched itself
- chrome.exe (PID: 904)
- firefox.exe (PID: 988)
Reads CPU info
- firefox.exe (PID: 988)
Creates files in the user directory
- chrome.exe (PID: 904)
Changes settings of System certificates
- DrvInst.exe (PID: 1664)
- DrvInst.exe (PID: 3232)
Low-level read access rights to disk partition
- vssvc.exe (PID: 1000)
Reads settings of System Certificates
- core.exe (PID: 612)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
109
Monitored processes
61
Malicious processes
21
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 272 | tasklist /? | C:\Windows\system32\tasklist.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Lists the current running tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 408 | C:\Windows\SYSTEM32\cmd.exe /c "C:\Windows\TEMP\sch_install_ca.bat" | C:\Windows\SYSTEM32\cmd.exe | — | taskeng.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 9009 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 612 | "C:\Program Files\Diebold\Warsaw\core.exe" | C:\Program Files\Diebold\Warsaw\core.exe | services.exe | ||||||||||||
User: SYSTEM Company: GAS Tecnologia LTDA Integrity Level: SYSTEM Description: GAS Tecnologia - Core Exit code: 0 Version: 2.8.4.40536 Modules
| |||||||||||||||
| 788 | C:\Windows\SYSTEM32\cmd.exe /c "C:\Windows\TEMP\sch_install_ca.bat" | C:\Windows\SYSTEM32\cmd.exe | — | taskeng.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 9009 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 904 | "C:\Program Files\Google\Chrome\Application\chrome.exe" https://bankline.itau.com.br/Guardiao/DiagnosticoItau.exe | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 912 | "C:\Windows\TEMP\is-JFE1H.tmp\get_version.exe" "C:\Program Files\Diebold\Warsaw\features.dat" "C:\Windows\TEMP\is-JFE1H.tmp\version.txt" | C:\Windows\TEMP\is-JFE1H.tmp\get_version.exe | — | warsaw_setup_32.tmp | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 988 | "C:\Program Files\Mozilla Firefox\firefox.exe" -silent | C:\Program Files\Mozilla Firefox\firefox.exe | DiagnosticoItau.exe | ||||||||||||
User: SYSTEM Company: Mozilla Corporation Integrity Level: SYSTEM Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=952,9332770073607561232,3046645075391327176,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=18444125332851323553 --mojo-platform-channel-handle=3528 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1000 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 454
Read events
1 889
Write events
547
Delete events
18
Modification events
| (PID) Process: | (2340) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 904-13201185845427000 |
Value: 259 | |||
| (PID) Process: | (904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 904-13201185845427000 |
Value: 259 | |||
Executable files
97
Suspicious files
1 624
Text files
352
Unknown types
80
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\375708df-ab3f-4d46-8000-92c534fa8ff9.tmp | — | |
MD5:— | SHA256:— | |||
| 904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
56
DNS requests
7
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
904 | chrome.exe | 172.217.16.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
904 | chrome.exe | 200.196.152.202:443 | bankline.itau.com.br | Itau Unibanco S.A. | BR | unknown |
904 | chrome.exe | 216.58.207.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
904 | chrome.exe | 172.217.18.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
904 | chrome.exe | 172.217.16.196:443 | www.google.com | Google Inc. | US | whitelisted |
904 | chrome.exe | 172.217.22.110:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2648 | DiagnosticoItau.exe | 2.21.37.100:443 | guardiao.itau.com.br | GTT Communications Inc. | FR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
bankline.itau.com.br |
| unknown |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
guardiao.itau.com.br |
| suspicious |