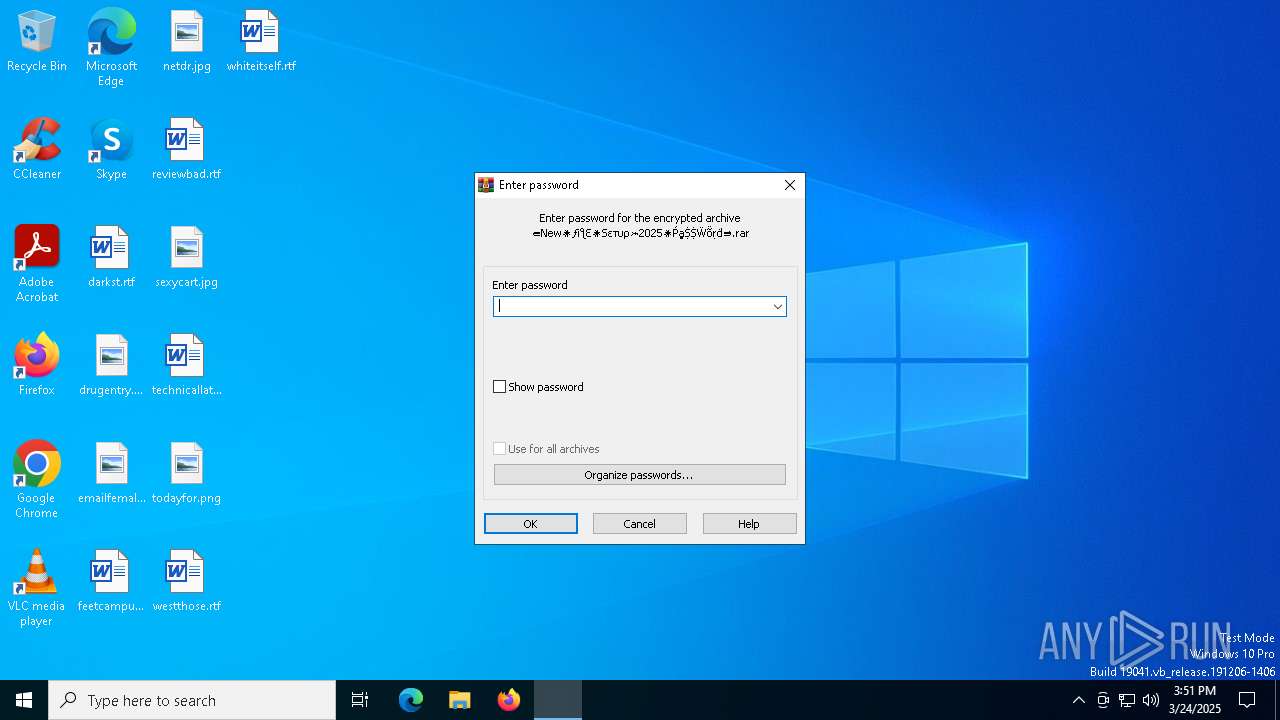
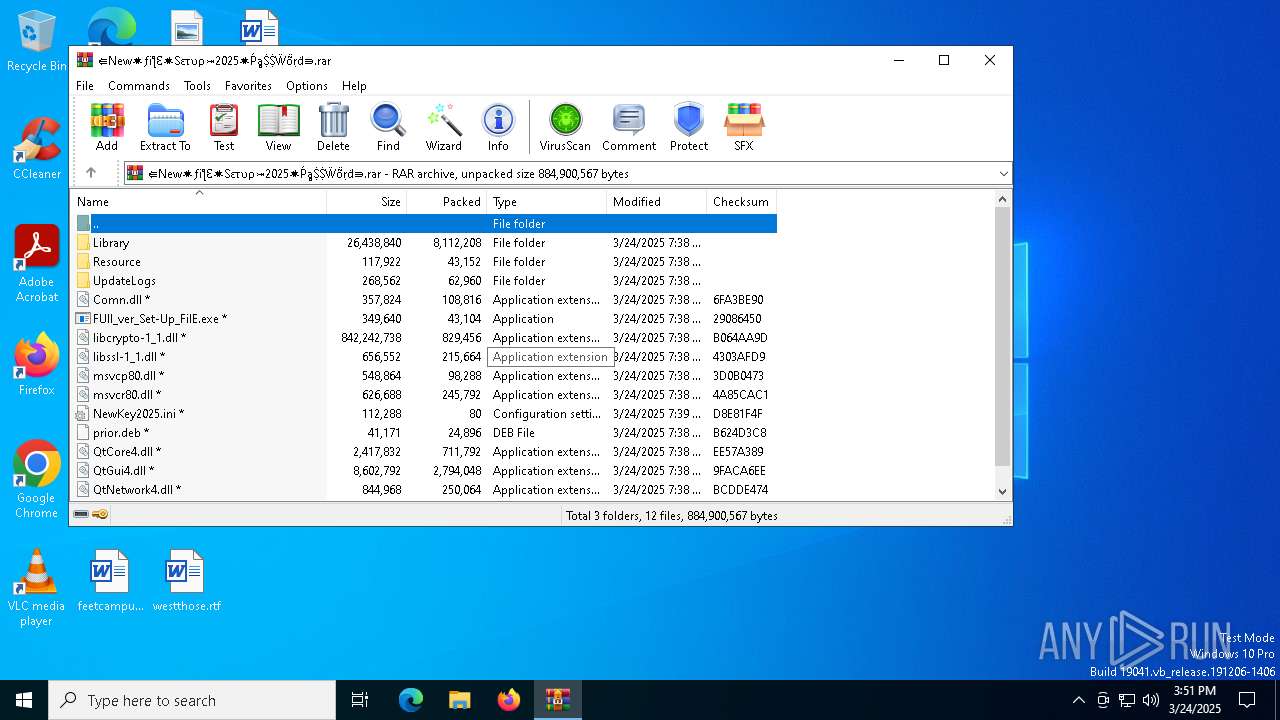
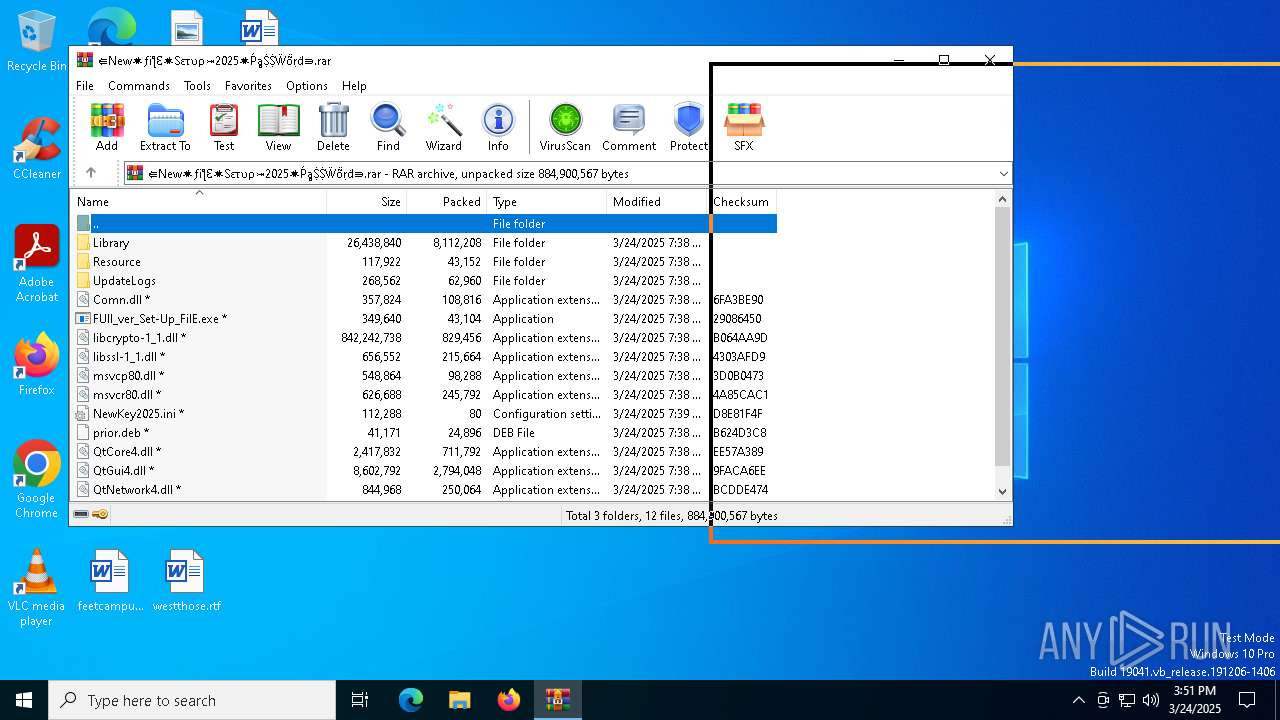
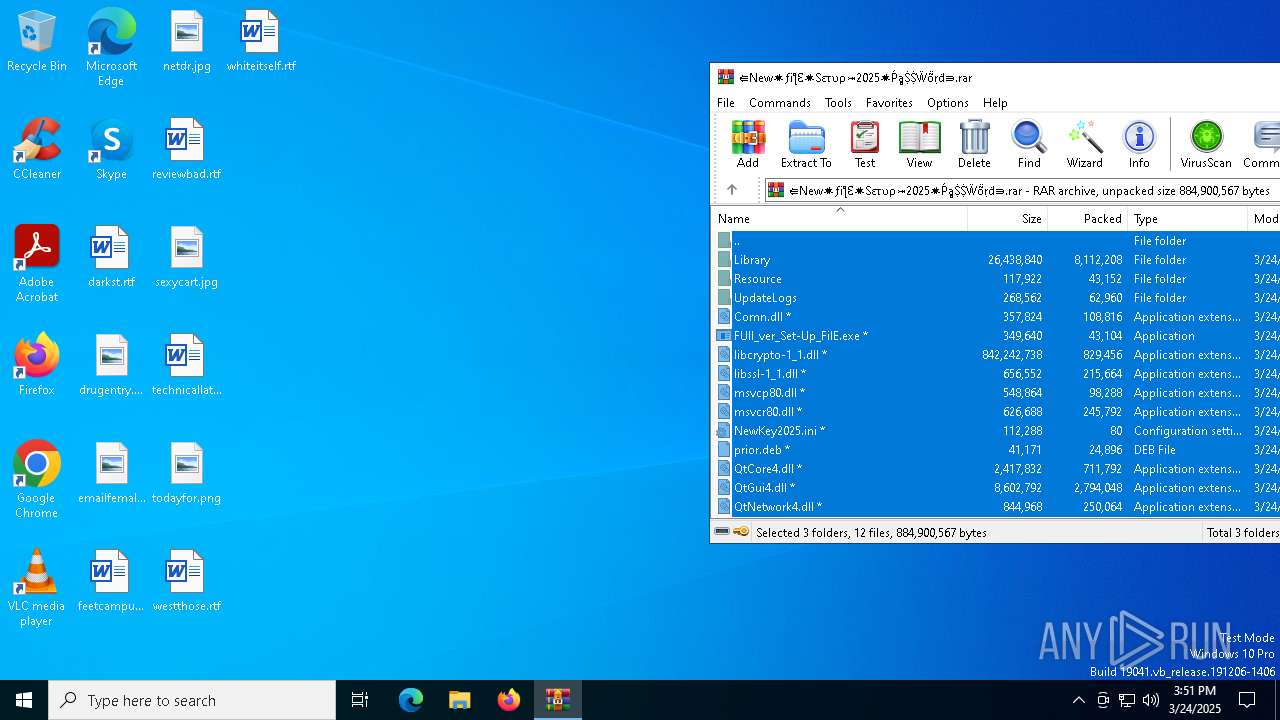
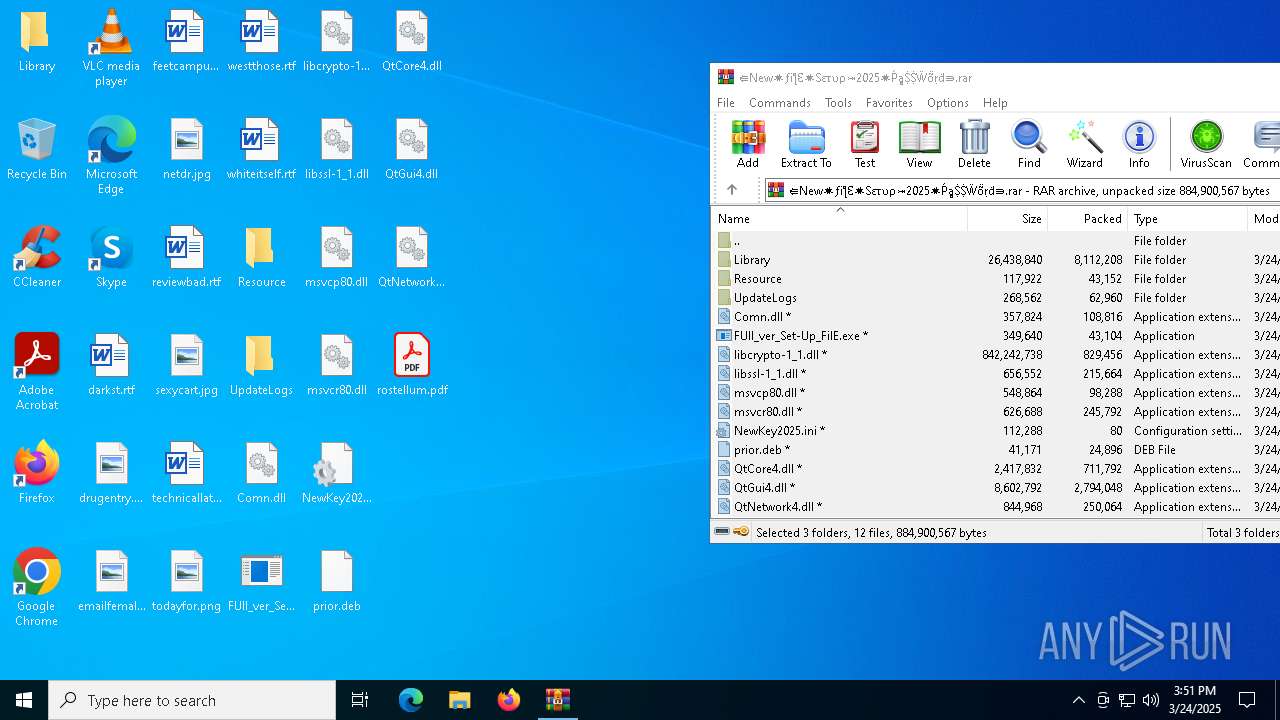
| File name: | ⇚New✷ƒiƪƐ✷Sετυρ⤖2025✷ṔḁṨṨẄṏṛḋ⇛.rar |
| Full analysis: | https://app.any.run/tasks/131d5f59-7c82-47f6-b0d8-772d3f819976 |
| Verdict: | Malicious activity |
| Analysis date: | March 24, 2025, 15:50:49 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 24E836A8F2670643AC5B542D67DC0E85 |
| SHA1: | CDD3CDE23F86ADA81F49D7AF6EB861B41410D856 |
| SHA256: | B885C6296CDB0003305ACC46F4DAF9168678D2216132C6328EC1E675899B0C52 |
| SSDEEP: | 196608:YTWO+DAL3pfYxmD9EmCFAWSP6EMcS+FVdUy3MTP:YWO+m3ixE5CFXSCEMcSUsIaP |
MALICIOUS
Known privilege escalation attack
- dllhost.exe (PID: 8096)
SUSPICIOUS
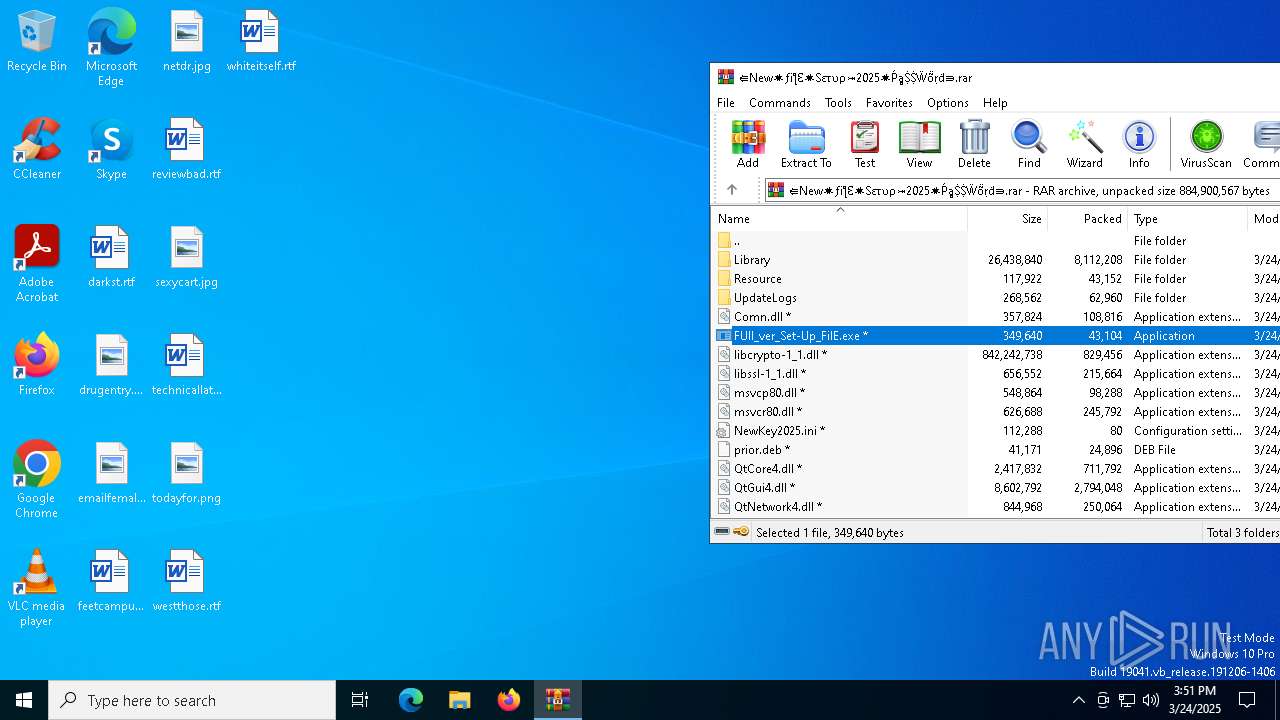
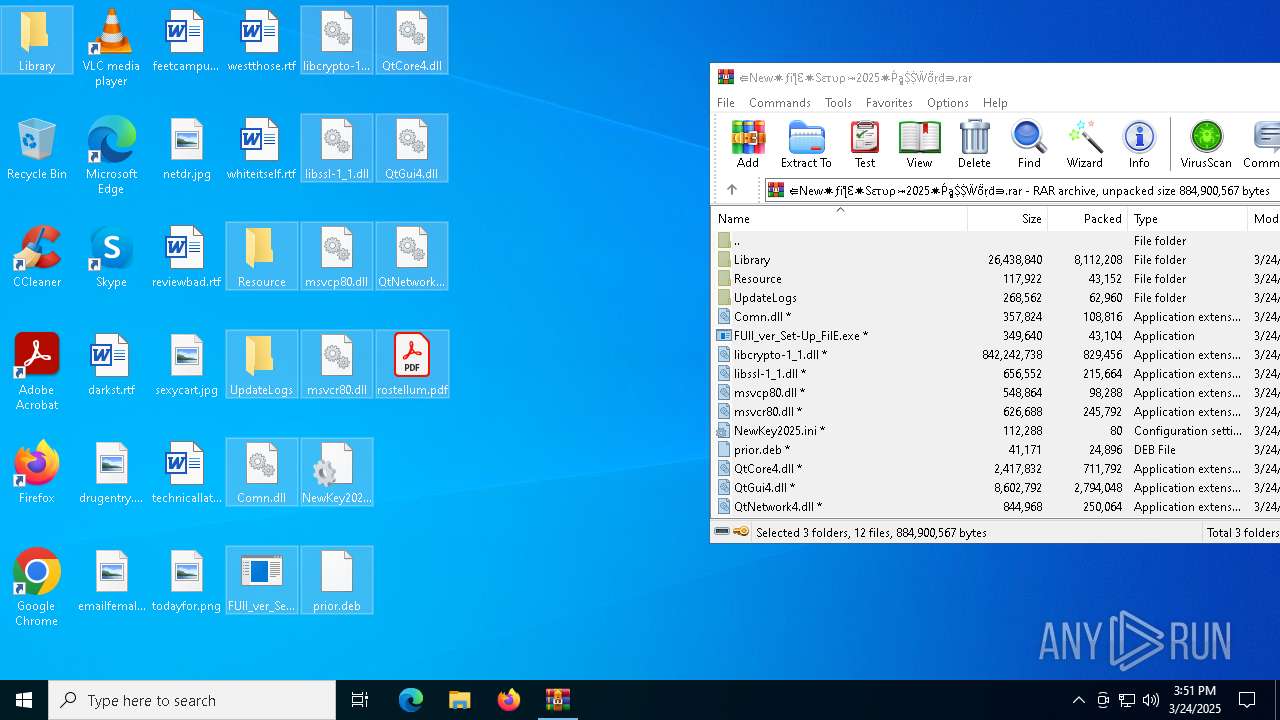
Process drops legitimate windows executable
- WinRAR.exe (PID: 7548)
- FUll_ver_Set-Up_FilE.exe (PID: 456)
Executable content was dropped or overwritten
- FUll_ver_Set-Up_FilE.exe (PID: 456)
The process drops C-runtime libraries
- FUll_ver_Set-Up_FilE.exe (PID: 456)
Starts application with an unusual extension
- FUll_ver_Set-Up_FilE.exe (PID: 456)
- FUll_ver_Set-Up_FilE.exe (PID: 8168)
INFO
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 7836)
- BackgroundTransferHost.exe (PID: 8084)
- BackgroundTransferHost.exe (PID: 668)
- BackgroundTransferHost.exe (PID: 8188)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 8084)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 8084)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 8084)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7548)
The sample compiled with english language support
- WinRAR.exe (PID: 7548)
- FUll_ver_Set-Up_FilE.exe (PID: 456)
The sample compiled with russian language support
- WinRAR.exe (PID: 7548)
Manual execution by a user
- FUll_ver_Set-Up_FilE.exe (PID: 456)
Checks supported languages
- FUll_ver_Set-Up_FilE.exe (PID: 456)
- more.com (PID: 1660)
Creates files in the program directory
- FUll_ver_Set-Up_FilE.exe (PID: 456)
Create files in a temporary directory
- FUll_ver_Set-Up_FilE.exe (PID: 8168)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|
Total processes
144
Monitored processes
15
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | "C:\Users\admin\Desktop\FUll_ver_Set-Up_FilE.exe" | C:\Users\admin\Desktop\FUll_ver_Set-Up_FilE.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 668 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1660 | C:\WINDOWS\SysWOW64\more.com | C:\Windows\SysWOW64\more.com | — | FUll_ver_Set-Up_FilE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: More Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4452 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5544 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | more.com | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5588 | "C:\WINDOWS\system32\svchost.exe" | C:\Windows\SysWOW64\svchost.exe | — | MSBuild.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 7288 | C:\WINDOWS\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | — | FUll_ver_Set-Up_FilE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: MSBuild.exe Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
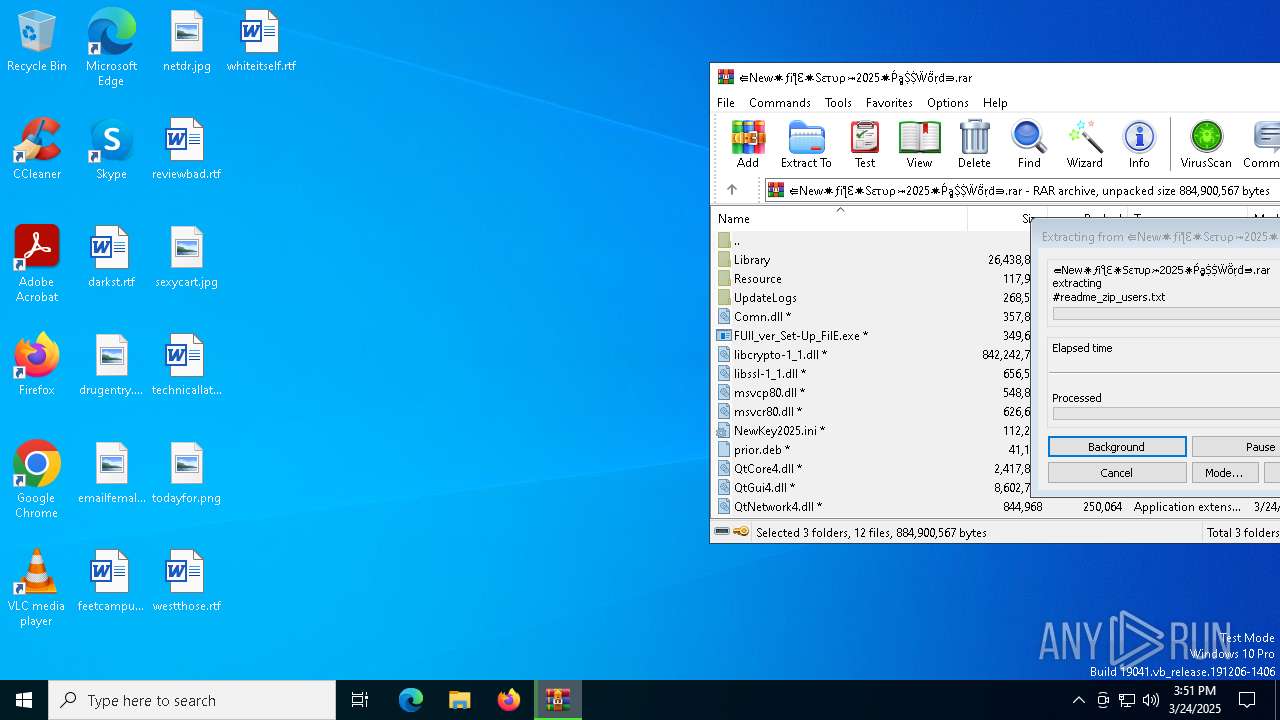
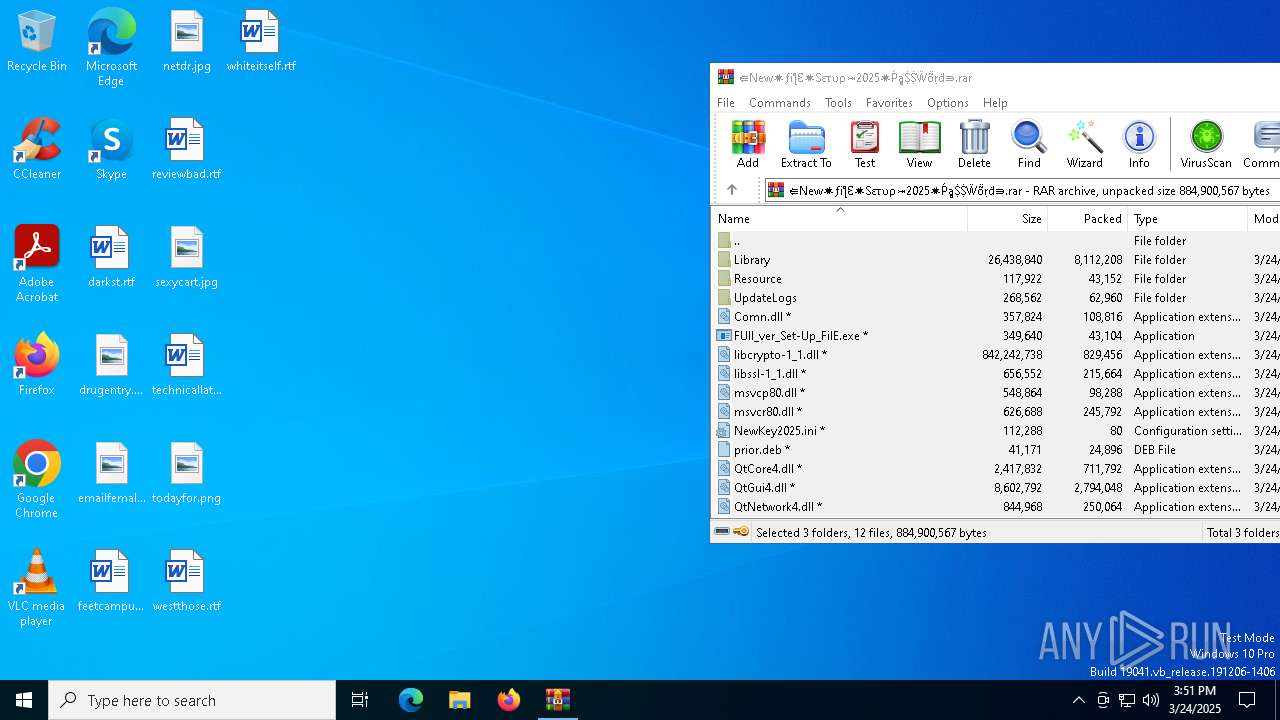
| 7548 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\⇚New✷ƒiƪƐ✷Sετυρ⤖2025✷ṔḁṨṨẄṏṛḋ⇛.rar | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 7836 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8056 | C:\WINDOWS\SysWOW64\more.com | C:\Windows\SysWOW64\more.com | — | FUll_ver_Set-Up_FilE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: More Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
4 111
Read events
4 089
Write events
22
Delete events
0
Modification events
| (PID) Process: | (7548) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7548) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7548) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7548) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\⇚New✷ƒiƪƐ✷Sετυρ⤖2025✷ṔḁṨṨẄṏṛḋ⇛.rar | |||
| (PID) Process: | (7548) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7548) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7548) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7548) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7836) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7836) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
54
Suspicious files
17
Text files
79
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8084 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\c89ab5d4-e30f-4929-94a5-9d3772d3384c.down_data | — | |
MD5:— | SHA256:— | |||
| 7548 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb7548.28937\UpdateLogs\DisplayLanguageNames.zh_HK.txt | — | |
MD5:— | SHA256:— | |||
| 8084 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:4872BABAF39AA62B8D32695EBB7E9173 | SHA256:2EE85DF86EE29BBEB3DCA81AA29B6DE204F605A2769B84C728A329178A2D0999 | |||
| 8084 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\c89ab5d4-e30f-4929-94a5-9d3772d3384c.dbe20f7c-d743-430c-9235-625fb0e6ab38.down_meta | binary | |
MD5:2FCBF28E0FEEA2C32AD085A924A01738 | SHA256:5FE1776AA935C36440C174F056A0734862196D85091A5D57730A99EE7DCACA54 | |||
| 7548 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb7548.28937\UpdateLogs\8859-14.txt | text | |
MD5:FA40746824C8B2361C6E7D390B16C468 | SHA256:79143EE49AB465F2317B9D3ADE16F07EC6CF6314506426FA5B366A6E742FC15A | |||
| 8084 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\0497932a-f8f1-4697-872f-51bad0228e3f.dbe20f7c-d743-430c-9235-625fb0e6ab38.down_meta | binary | |
MD5:2FCBF28E0FEEA2C32AD085A924A01738 | SHA256:5FE1776AA935C36440C174F056A0734862196D85091A5D57730A99EE7DCACA54 | |||
| 7548 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb7548.28937\UpdateLogs\build_trimpath_cgo.txt | text | |
MD5:B8AE160D1782E6223E76EC47A59D9AE4 | SHA256:5E152A0B43DAC652C8379E914B705F856903DCFE739DDDE9CB6406B0835DADF2 | |||
| 8084 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\0497932a-f8f1-4697-872f-51bad0228e3f.up_meta_secure | binary | |
MD5:5B6BDC5599704C9981C0CC10277979E9 | SHA256:F16756E7715AD262F7CE5BEEDE3BFF57B36CB080F3E3F797C94802C384C932E6 | |||
| 7548 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb7548.28937\UpdateLogs\cover_main_import_path.txt | text | |
MD5:DE5BE568AF2B7D048420219B486F80A9 | SHA256:332A7F41E43A0CDFB918CB7CC5573BD8F9DF67DBE84EB1D9A76962E133A01A82 | |||
| 7548 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb7548.28937\UpdateLogs\#readme_zip_users.txt | text | |
MD5:2EF0A97D6D07E95231A4A97EF0CA1CA2 | SHA256:6DCB836ECC67489FB16C3DB0AE3195E69085AC4FD88D4C6DF3AF54D0C612FBFE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
24
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.183:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
8084 | BackgroundTransferHost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7728 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7728 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.183:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.190.159.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.54.109.203:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.159.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5332 | backgroundTaskHost.exe | 20.223.36.55:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |