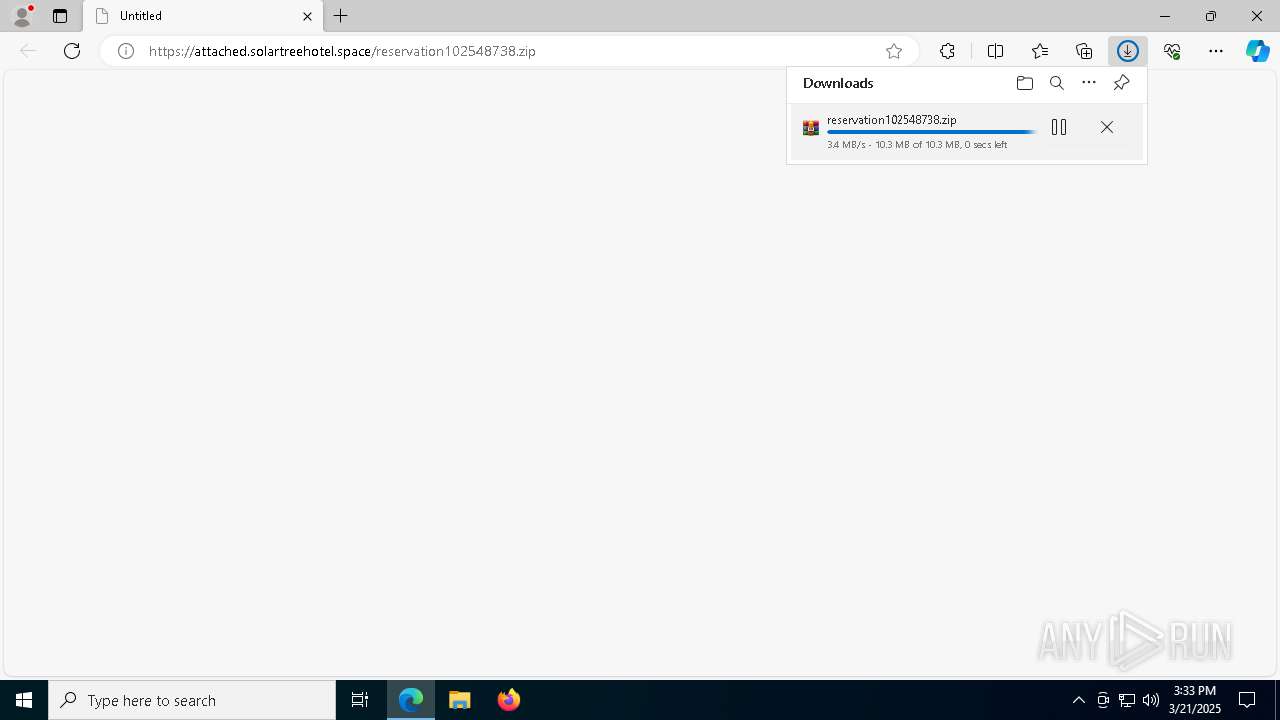
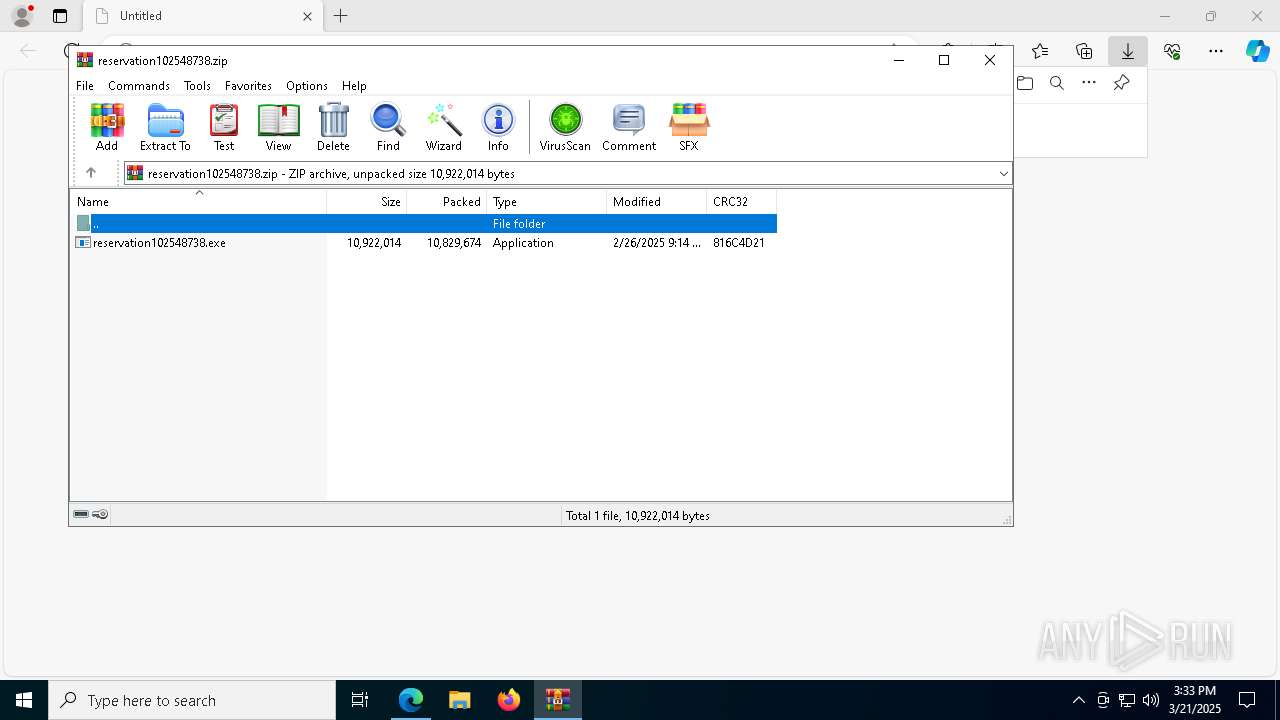
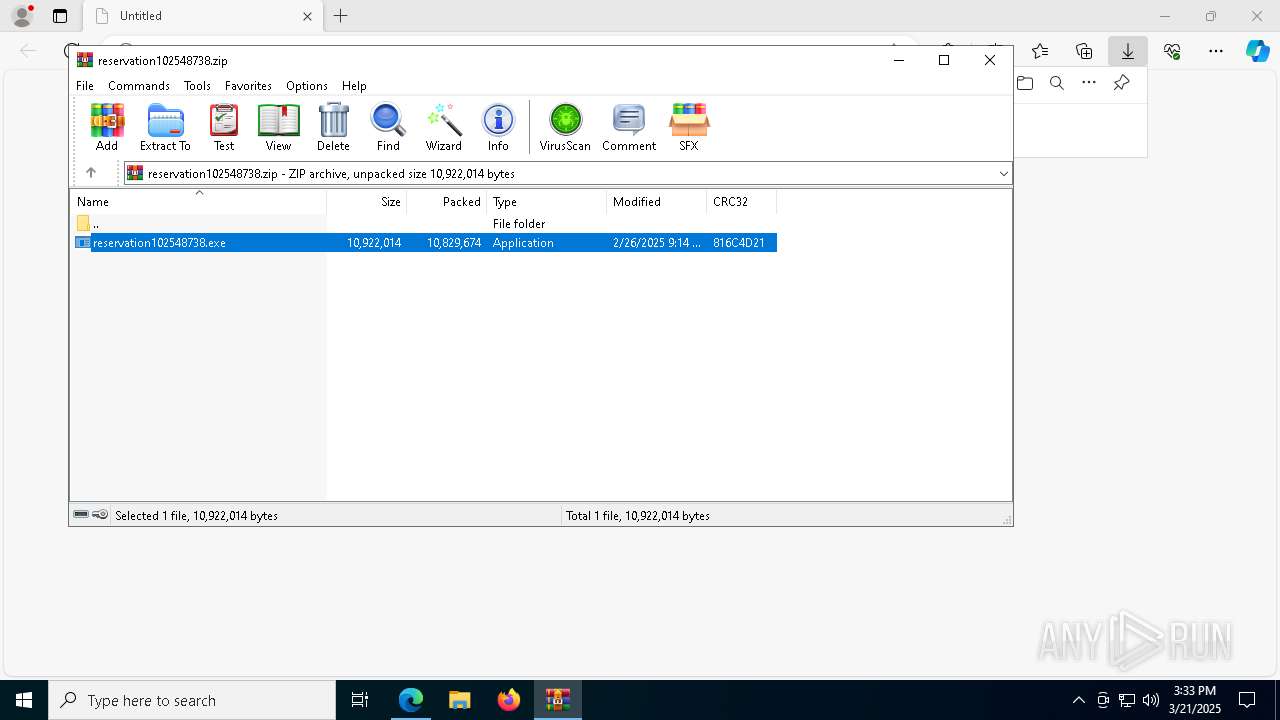
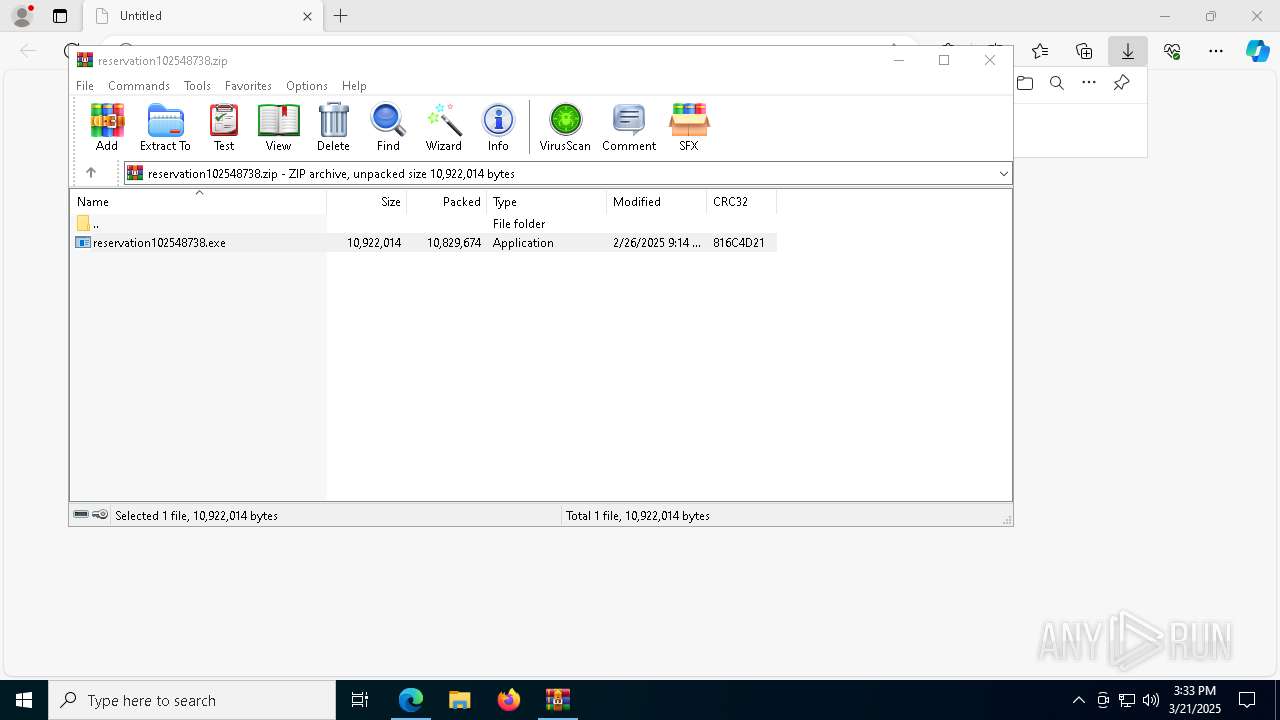
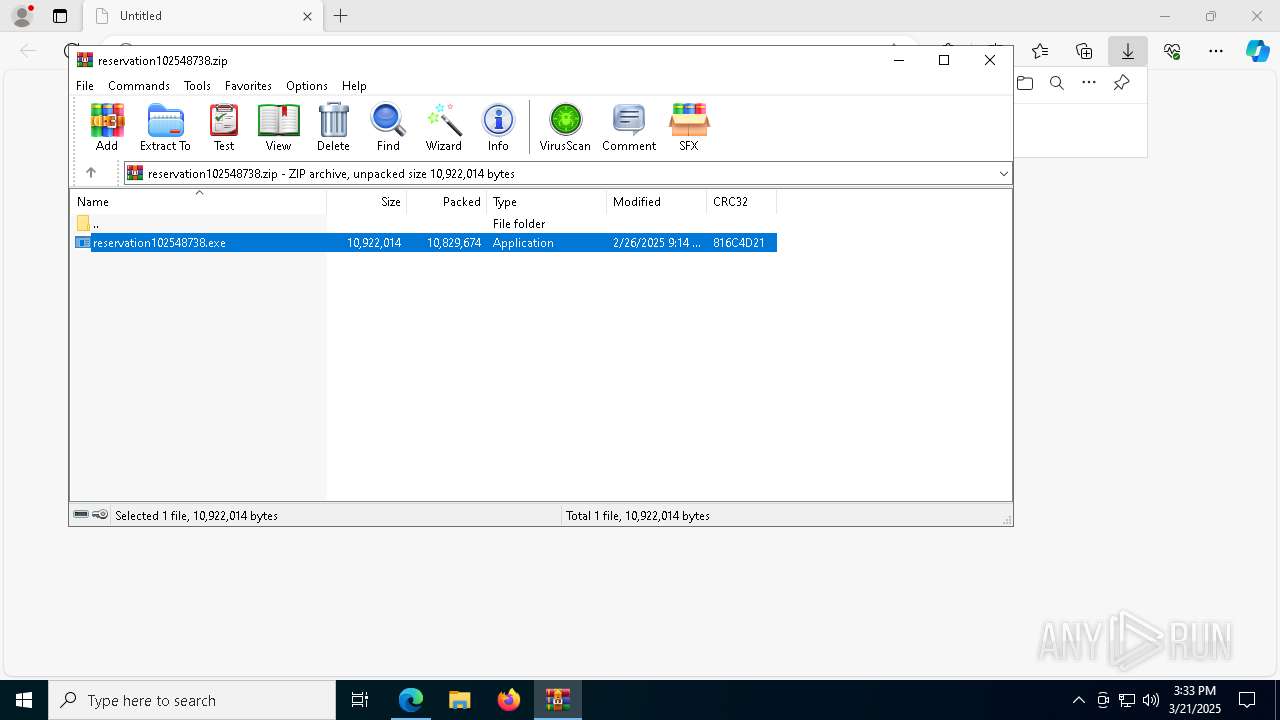
| URL: | https://attached.solartreehotel.space/reservation102548738.zip |
| Full analysis: | https://app.any.run/tasks/a36cbe47-cff3-48b1-a2d7-c177acd9e863 |
| Verdict: | Malicious activity |
| Analysis date: | March 21, 2025, 15:32:54 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | ACA04AACDFDB5A39DC99A7BEFFAFDC52 |
| SHA1: | 63A59098A74C3E2849B3ED17025DAA2A9AAD3A17 |
| SHA256: | B869E16594F2086E25D1927DA576EE2AFF18CBEA57BE7C33133E66EADE93F115 |
| SSDEEP: | 3:N8qTRKmJ6AFd4DdrUn:2qTRt6kO9U |
MALICIOUS
Executing a file with an untrusted certificate
- reservation102548738.exe (PID: 4336)
- reservation102548738.exe (PID: 1228)
- reservation102548738.exe (PID: 976)
- reservation102548738.exe (PID: 4120)
- reservation102548738.exe (PID: 8960)
- reservation102548738.exe (PID: 668)
Connects to the CnC server
- SynTPEnh.exe (PID: 8372)
SUSPICIOUS
Executable content was dropped or overwritten
- reservation102548738.tmp (PID: 1020)
- reservation102548738.exe (PID: 4336)
- reservation102548738.exe (PID: 1228)
- reservation102548738.tmp (PID: 2236)
- reservation102548738.tmp (PID: 8948)
- reservation102548738.exe (PID: 4120)
- reservation102548738.tmp (PID: 4988)
- reservation102548738.tmp (PID: 4996)
- reservation102548738.exe (PID: 976)
- reservation102548738.exe (PID: 8960)
- reservation102548738.tmp (PID: 1132)
- reservation102548738.exe (PID: 668)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 3884)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 5064)
Process drops SQLite DLL files
- msiexec.exe (PID: 5064)
The process drops C-runtime libraries
- msiexec.exe (PID: 5064)
Process drops legitimate windows executable
- msiexec.exe (PID: 5064)
Connects to unusual port
- SynTPEnh.exe (PID: 8372)
Mutex name with non-standard characters
- SynTPEnh.exe (PID: 8372)
- SynTPEnh.exe (PID: 1328)
- SynTPEnh.exe (PID: 9208)
Contacting a server suspected of hosting an CnC
- SynTPEnh.exe (PID: 8372)
INFO
Reads the computer name
- identity_helper.exe (PID: 8632)
- msiexec.exe (PID: 4892)
- reservation102548738.tmp (PID: 8948)
- reservation102548738.tmp (PID: 4988)
- reservation102548738.tmp (PID: 1132)
Reads Environment values
- identity_helper.exe (PID: 8632)
Checks supported languages
- reservation102548738.tmp (PID: 1020)
- identity_helper.exe (PID: 8632)
- reservation102548738.tmp (PID: 2236)
- msiexec.exe (PID: 4892)
- msiexec.exe (PID: 5064)
- reservation102548738.tmp (PID: 4988)
- reservation102548738.tmp (PID: 1132)
Reads Microsoft Office registry keys
- msedge.exe (PID: 2284)
Create files in a temporary directory
- reservation102548738.exe (PID: 4336)
- reservation102548738.tmp (PID: 1020)
- reservation102548738.tmp (PID: 2236)
- reservation102548738.exe (PID: 4120)
Application launched itself
- msedge.exe (PID: 2284)
The sample compiled with chinese language support
- reservation102548738.tmp (PID: 1020)
- reservation102548738.tmp (PID: 2236)
- reservation102548738.tmp (PID: 8948)
- reservation102548738.tmp (PID: 4988)
- reservation102548738.tmp (PID: 4996)
- reservation102548738.tmp (PID: 1132)
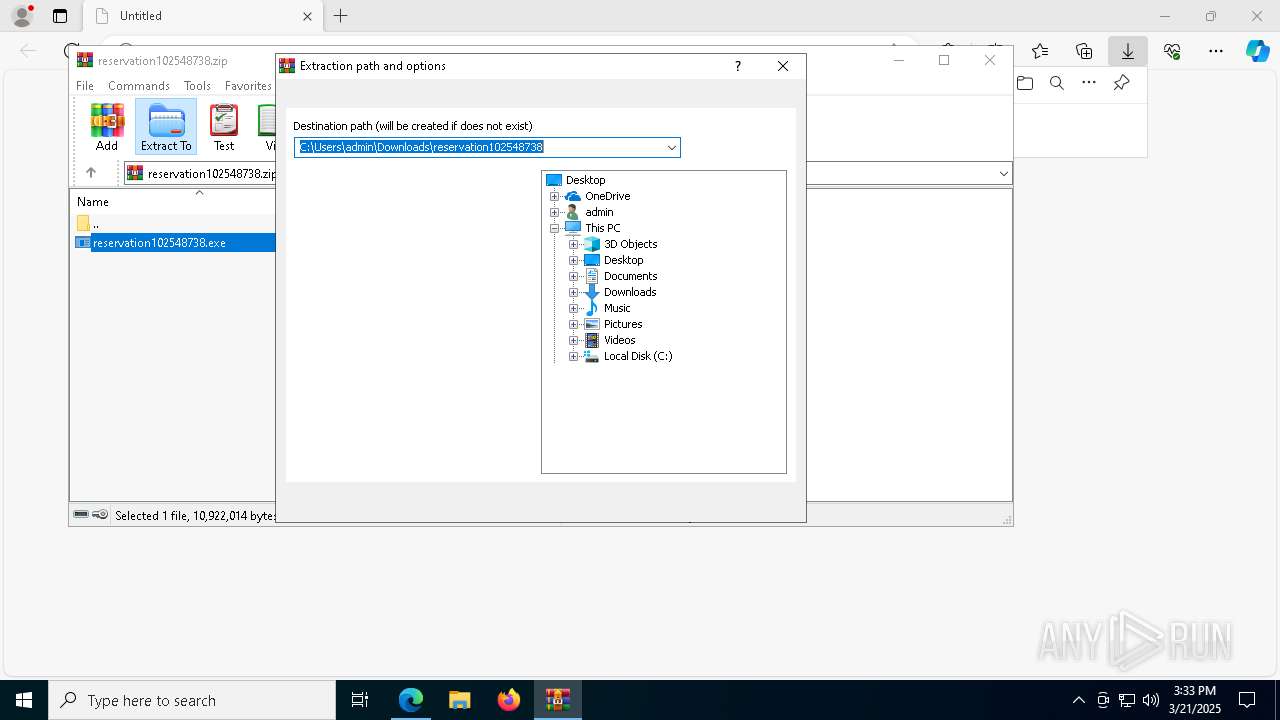
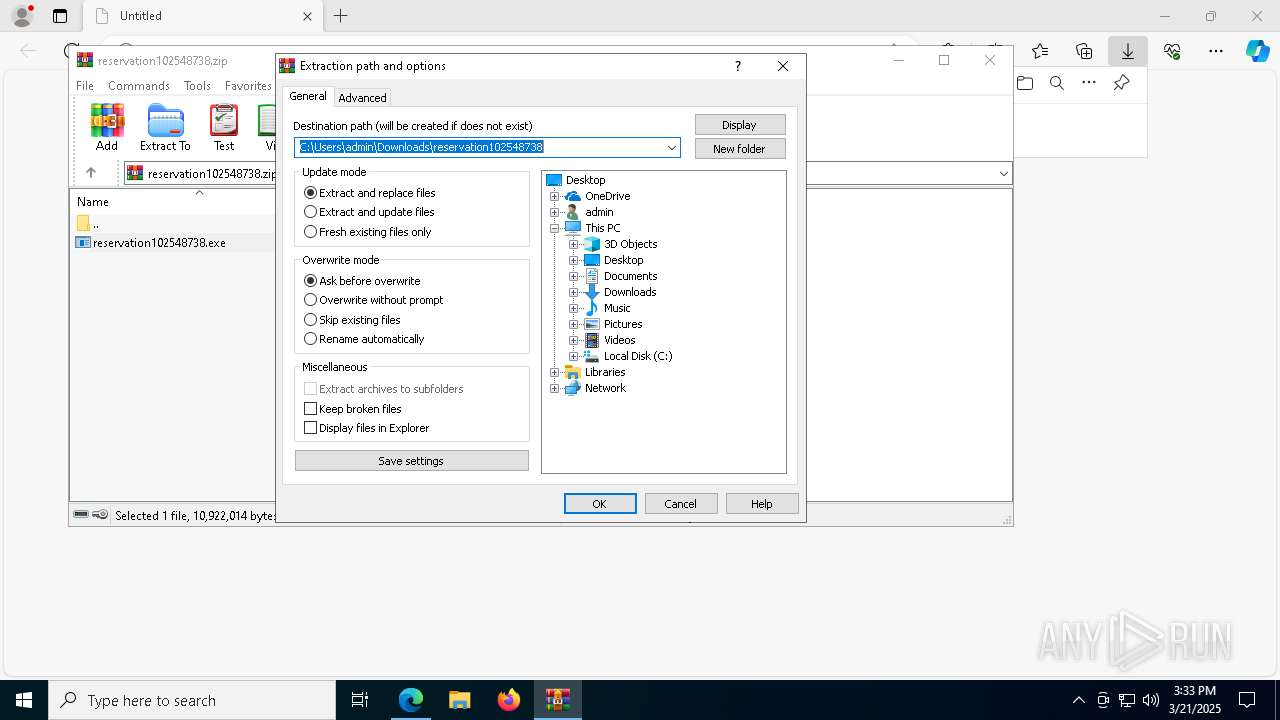
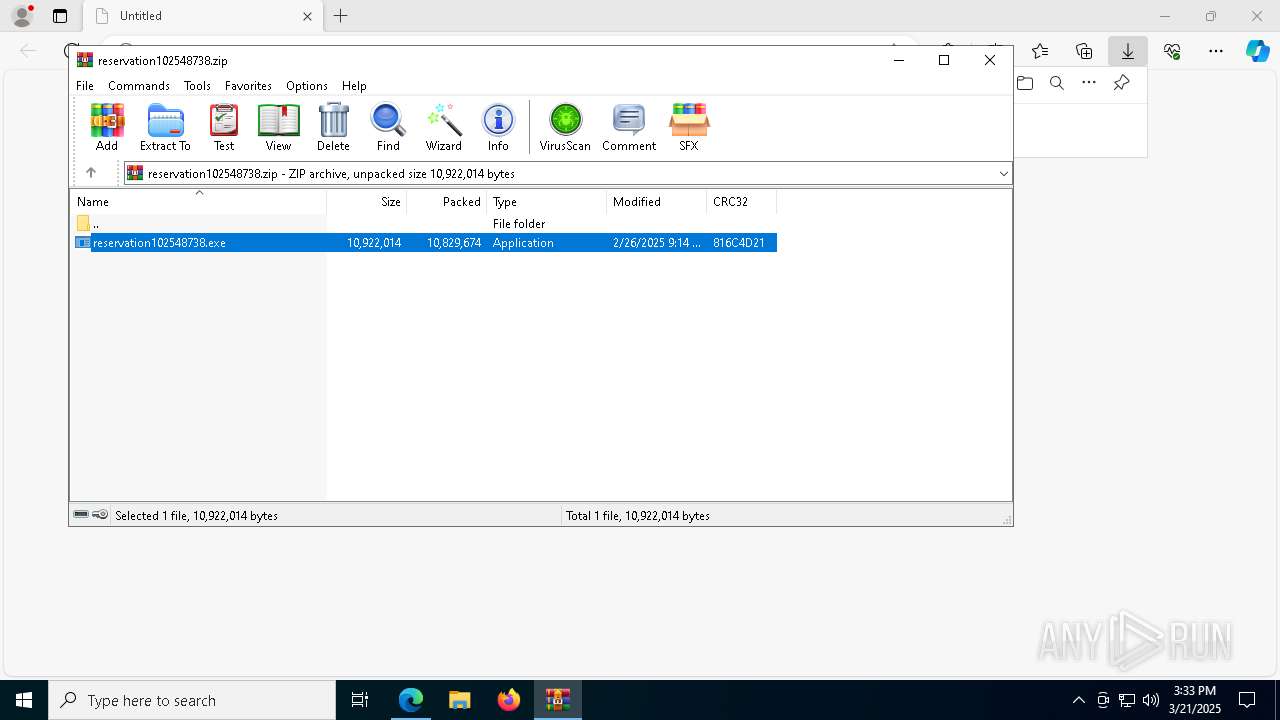
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3884)
- msiexec.exe (PID: 5064)
Reads CPU info
- reservation102548738.tmp (PID: 2236)
- reservation102548738.tmp (PID: 8948)
- reservation102548738.tmp (PID: 1132)
The sample compiled with russian language support
- msiexec.exe (PID: 5064)
The sample compiled with english language support
- msiexec.exe (PID: 5064)
Creates files or folders in the user directory
- msiexec.exe (PID: 5064)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
186
Monitored processes
52
Malicious processes
9
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 668 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3884.4353\reservation102548738.exe" /verysilent /sp- | C:\Users\admin\AppData\Local\Temp\Rar$EXa3884.4353\reservation102548738.exe | reservation102548738.tmp | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: SynTPEnh Exit code: 0 Version: Modules
| |||||||||||||||
| 976 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3884.2364\reservation102548738.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3884.2364\reservation102548738.exe | WinRAR.exe | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: SynTPEnh Exit code: 1 Version: Modules
| |||||||||||||||
| 1020 | "C:\Users\admin\AppData\Local\Temp\is-UQ44T.tmp\reservation102548738.tmp" /SL5="$30214,10502123,143360,C:\Users\admin\AppData\Local\Temp\Rar$EXa3884.389\reservation102548738.exe" | C:\Users\admin\AppData\Local\Temp\is-UQ44T.tmp\reservation102548738.tmp | reservation102548738.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 1 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1132 | "C:\Users\admin\AppData\Local\Temp\is-D0UE5.tmp\reservation102548738.tmp" /SL5="$902EE,10502123,143360,C:\Users\admin\AppData\Local\Temp\Rar$EXa3884.4353\reservation102548738.exe" /verysilent /sp- | C:\Users\admin\AppData\Local\Temp\is-D0UE5.tmp\reservation102548738.tmp | reservation102548738.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1180 | "msiexec.exe" -i "C:\Users\admin\AppData\Local\Temp\is-59NL9.tmp\SynTPEnh.msi" -qn | C:\Windows\SysWOW64\msiexec.exe | — | reservation102548738.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1228 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3884.389\reservation102548738.exe" /verysilent /sp- | C:\Users\admin\AppData\Local\Temp\Rar$EXa3884.389\reservation102548738.exe | reservation102548738.tmp | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: SynTPEnh Exit code: 0 Version: Modules
| |||||||||||||||
| 1328 | "C:\Users\admin\AppData\Local\Programs\SynTP\SynTPEnh.exe" | C:\Users\admin\AppData\Local\Programs\SynTP\SynTPEnh.exe | — | msiexec.exe | |||||||||||
User: admin Company: ООО «САФИБ» Integrity Level: MEDIUM Description: Ассистент 5 Exit code: 0 Version: 5.4.2304.2501 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2236 | "C:\Users\admin\AppData\Local\Temp\is-51GN7.tmp\reservation102548738.tmp" /SL5="$40214,10502123,143360,C:\Users\admin\AppData\Local\Temp\Rar$EXa3884.389\reservation102548738.exe" /verysilent /sp- | C:\Users\admin\AppData\Local\Temp\is-51GN7.tmp\reservation102548738.tmp | reservation102548738.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2284 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://attached.solartreehotel.space/reservation102548738.zip" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
14 731
Read events
14 461
Write events
231
Delete events
39
Modification events
| (PID) Process: | (2284) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2284) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2284) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2284) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2284) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 9B05C540728F2F00 | |||
| (PID) Process: | (2284) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 2F81CA40728F2F00 | |||
| (PID) Process: | (2284) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262796 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D04346AE-3194-48B3-854F-588F5AF81F8C} | |||
| (PID) Process: | (2284) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262796 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E23D5BD2-2CF5-45FF-84B2-A07339631FAE} | |||
| (PID) Process: | (2284) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: CECBEB40728F2F00 | |||
| (PID) Process: | (2284) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
Executable files
66
Suspicious files
112
Text files
32
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10bc3d.TMP | — | |
MD5:— | SHA256:— | |||
| 2284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10bc3d.TMP | — | |
MD5:— | SHA256:— | |||
| 2284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10bc3d.TMP | — | |
MD5:— | SHA256:— | |||
| 2284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10bc4d.TMP | — | |
MD5:— | SHA256:— | |||
| 2284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10bc7c.TMP | — | |
MD5:— | SHA256:— | |||
| 2284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
40
DNS requests
42
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8392 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
8372 | SynTPEnh.exe | GET | 200 | 193.29.224.106:80 | http://earlydawn.top/sx7/update.php?id=230165314&stat=b8f16a645ef6ab21a1633b3d1414d281 | unknown | — | — | malicious |
8812 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8372 | SynTPEnh.exe | GET | 200 | 193.29.224.106:80 | http://earlydawn.top/sx7/update.php?id=230165314&stat=b8f16a645ef6ab21a1633b3d1414d281 | unknown | — | — | malicious |
8372 | SynTPEnh.exe | GET | 200 | 193.29.224.106:80 | http://earlydawn.top/sx7/update.php?id=230165314&stat=b8f16a645ef6ab21a1633b3d1414d281 | unknown | — | — | malicious |
8812 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7344 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2284 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7344 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7344 | msedge.exe | 13.107.246.60:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7344 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7344 | msedge.exe | 195.161.68.210:443 | attached.solartreehotel.space | JSC RTComm.RU | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
attached.solartreehotel.space |
| unknown |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
8372 | SynTPEnh.exe | Malware Command and Control Activity Detected | ET MALWARE Win32.Spy/TVRat Checkin |
8372 | SynTPEnh.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
8372 | SynTPEnh.exe | Malware Command and Control Activity Detected | ET MALWARE SpyAgent C&C Activity (Request) |
8372 | SynTPEnh.exe | Malware Command and Control Activity Detected | ET MALWARE Win32.Spy/TVRat Checkin |
8372 | SynTPEnh.exe | Malware Command and Control Activity Detected | ET MALWARE SpyAgent C&C Activity (Request) |
8372 | SynTPEnh.exe | Malware Command and Control Activity Detected | ET MALWARE Win32.Spy/TVRat Checkin |
8372 | SynTPEnh.exe | Malware Command and Control Activity Detected | ET MALWARE SpyAgent C&C Activity (Request) |