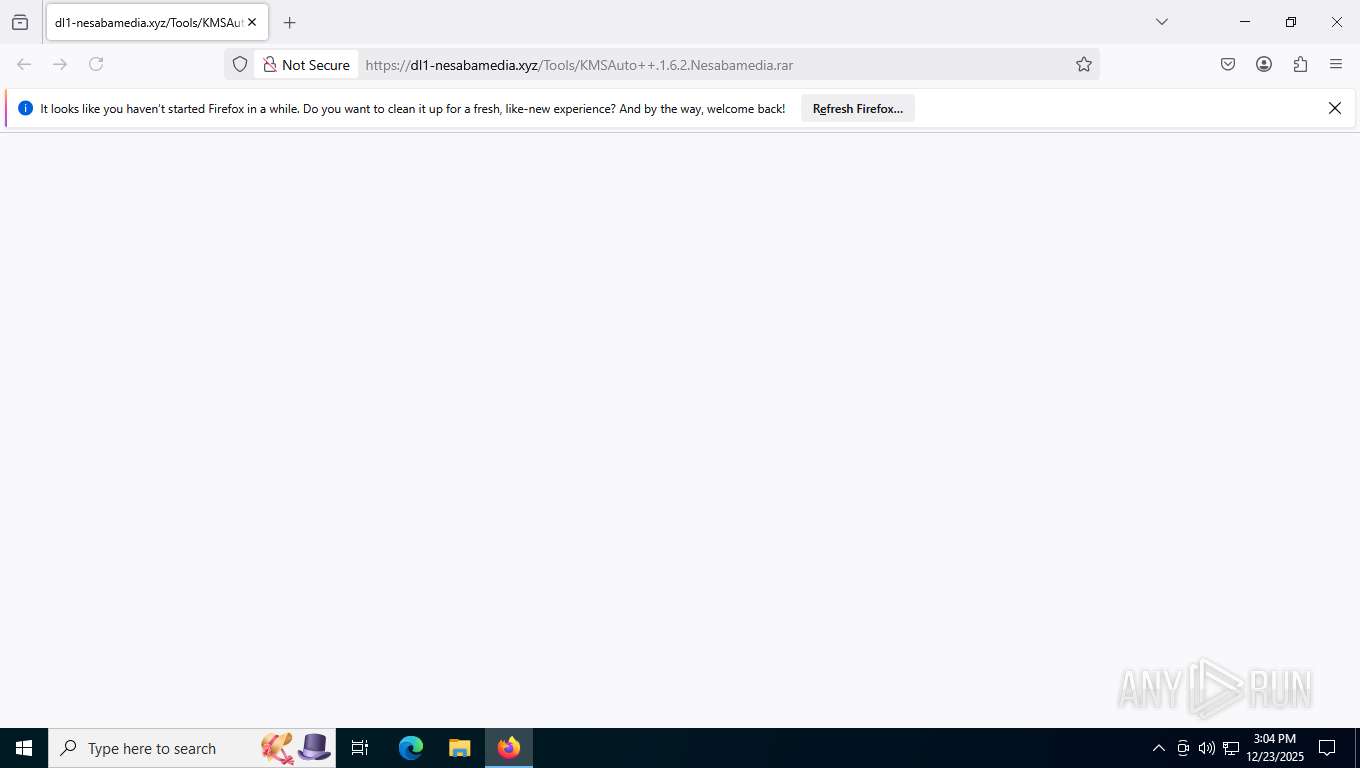
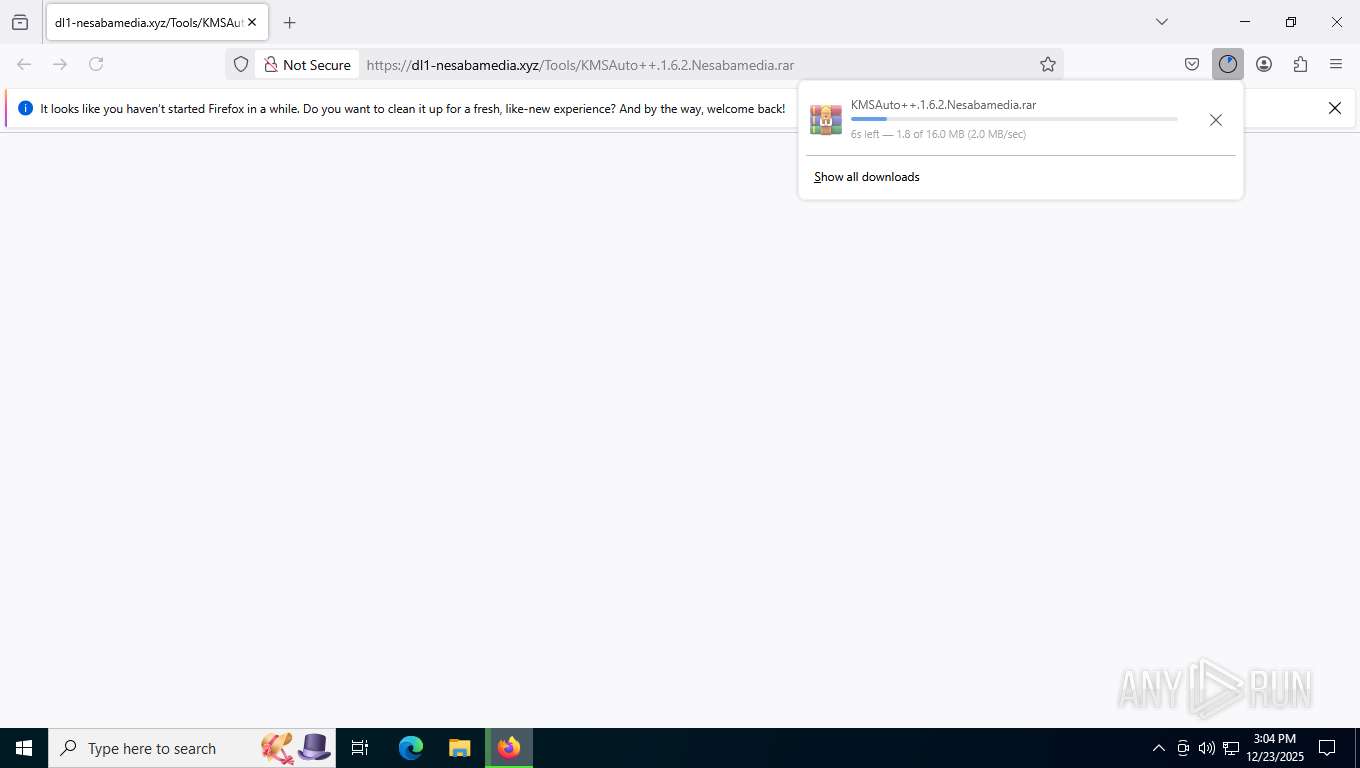
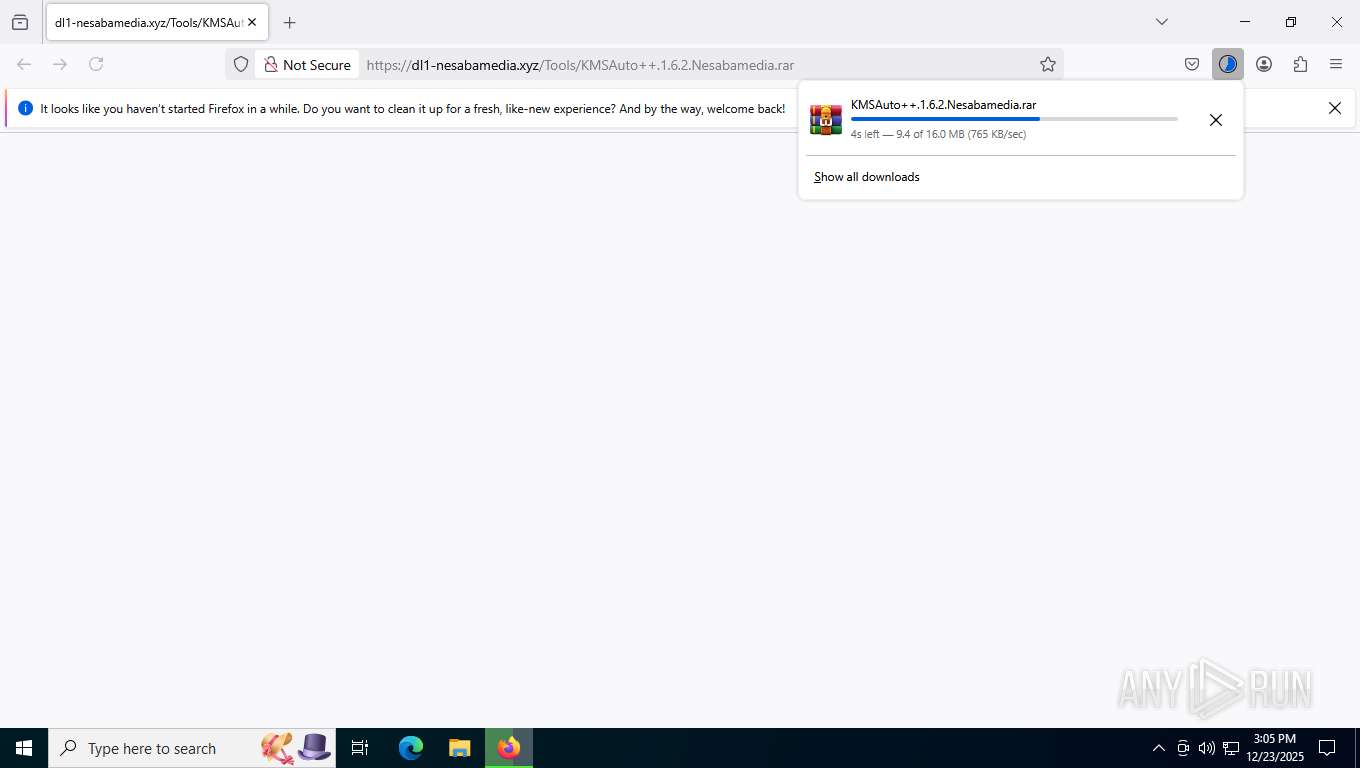
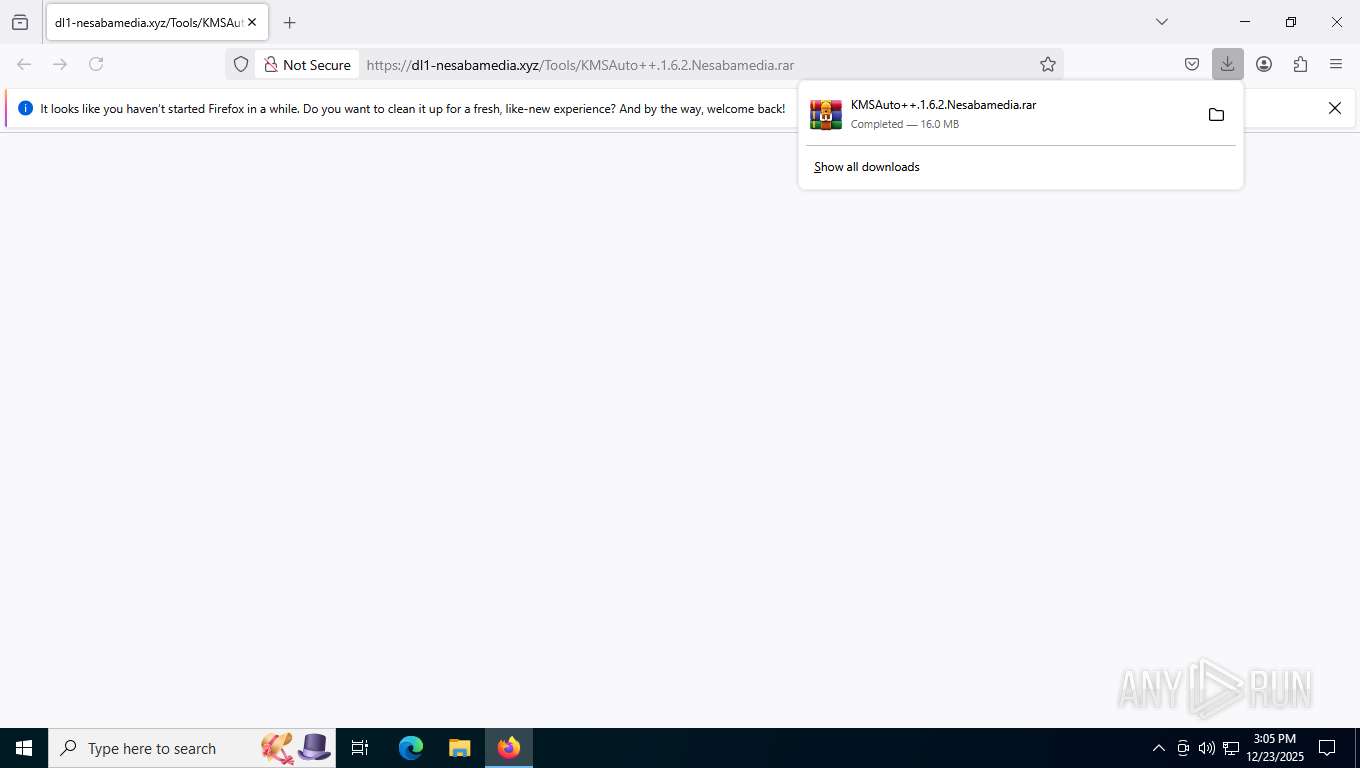
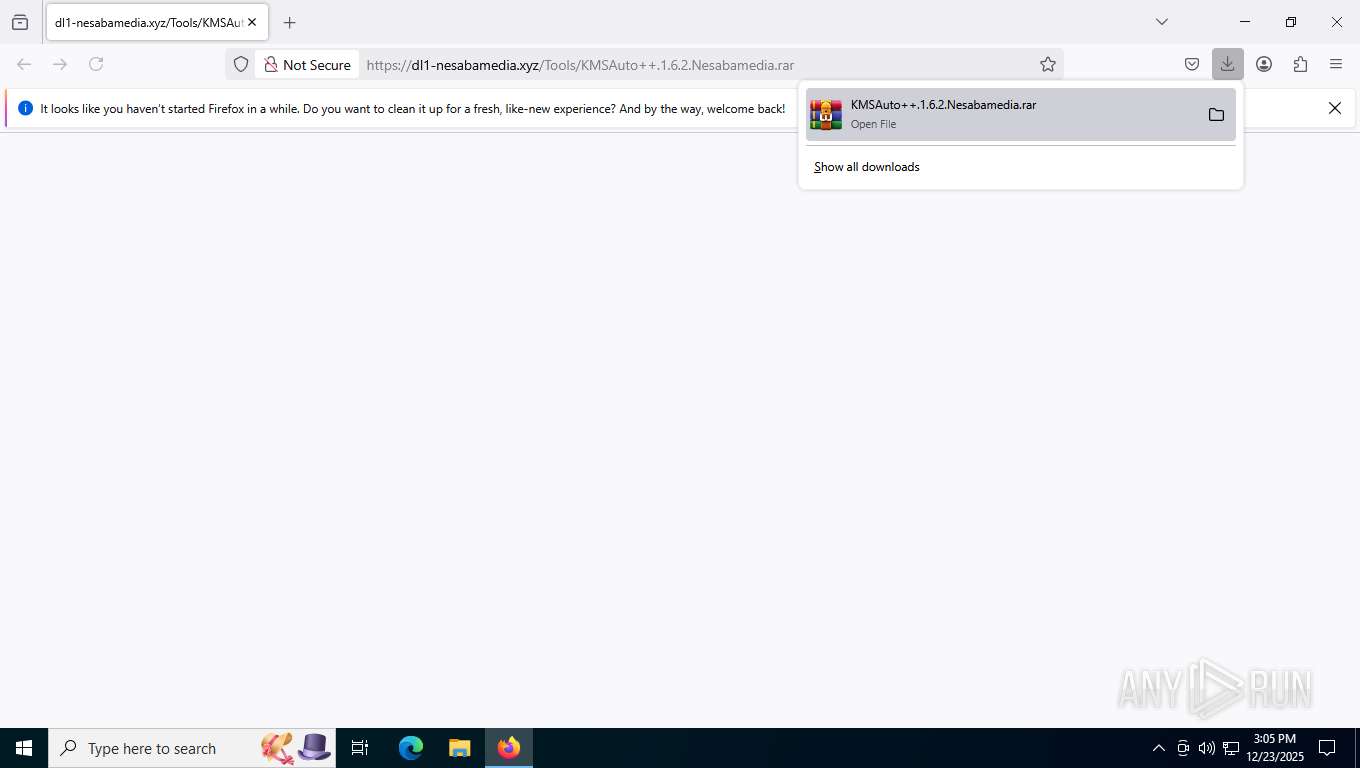
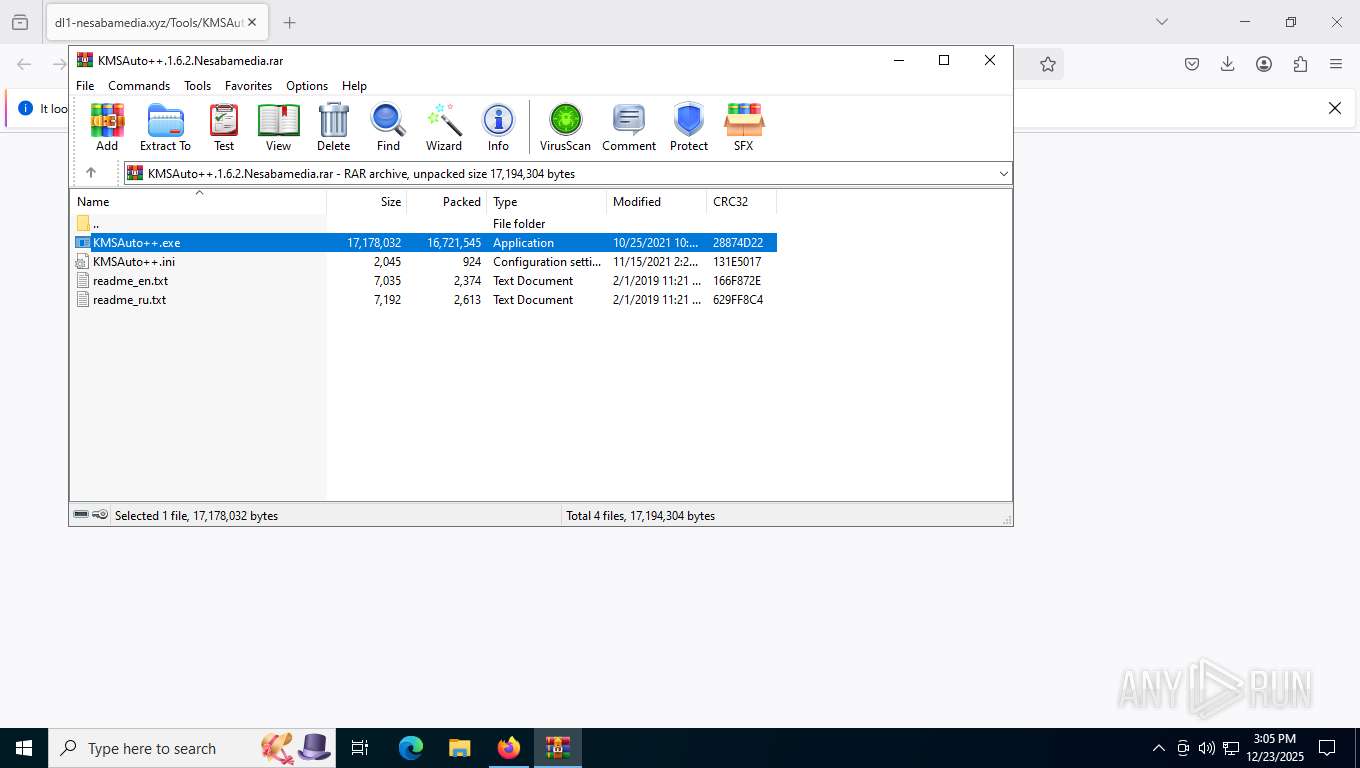
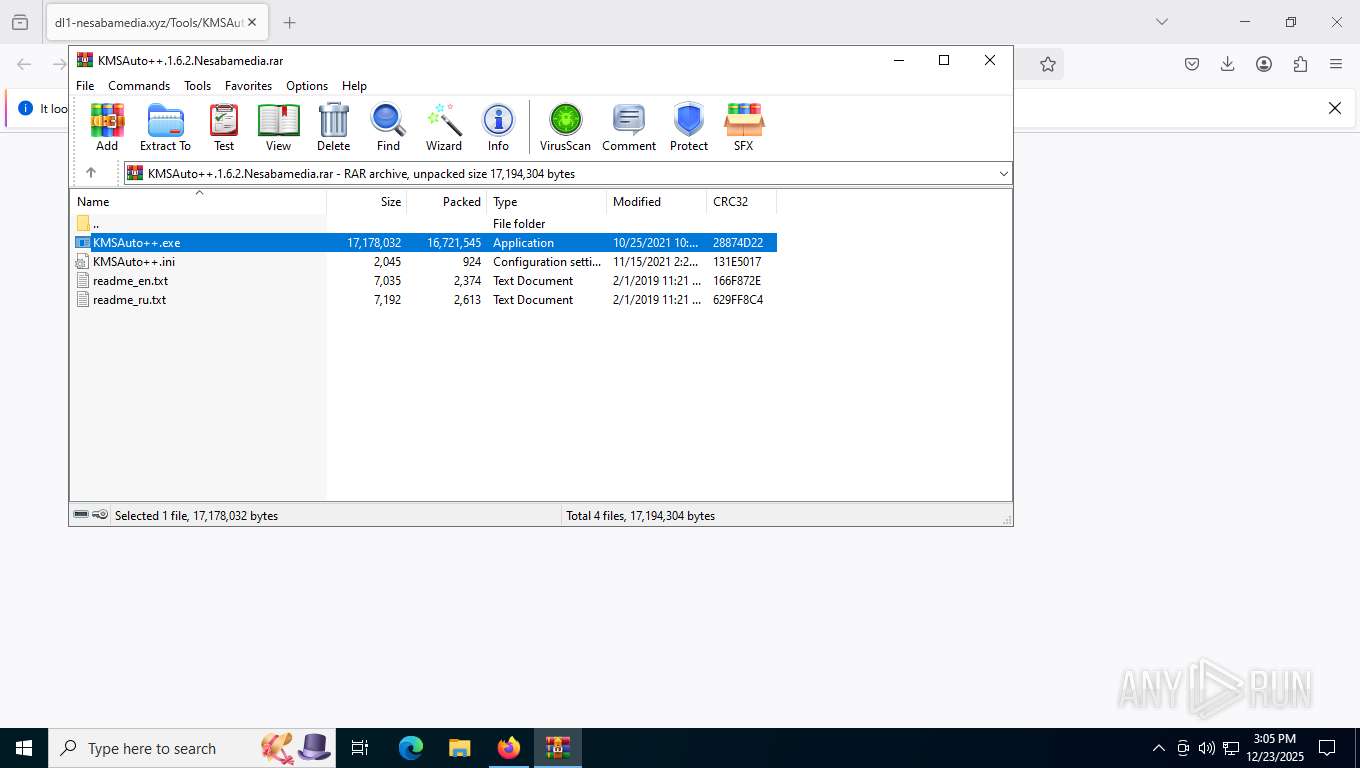
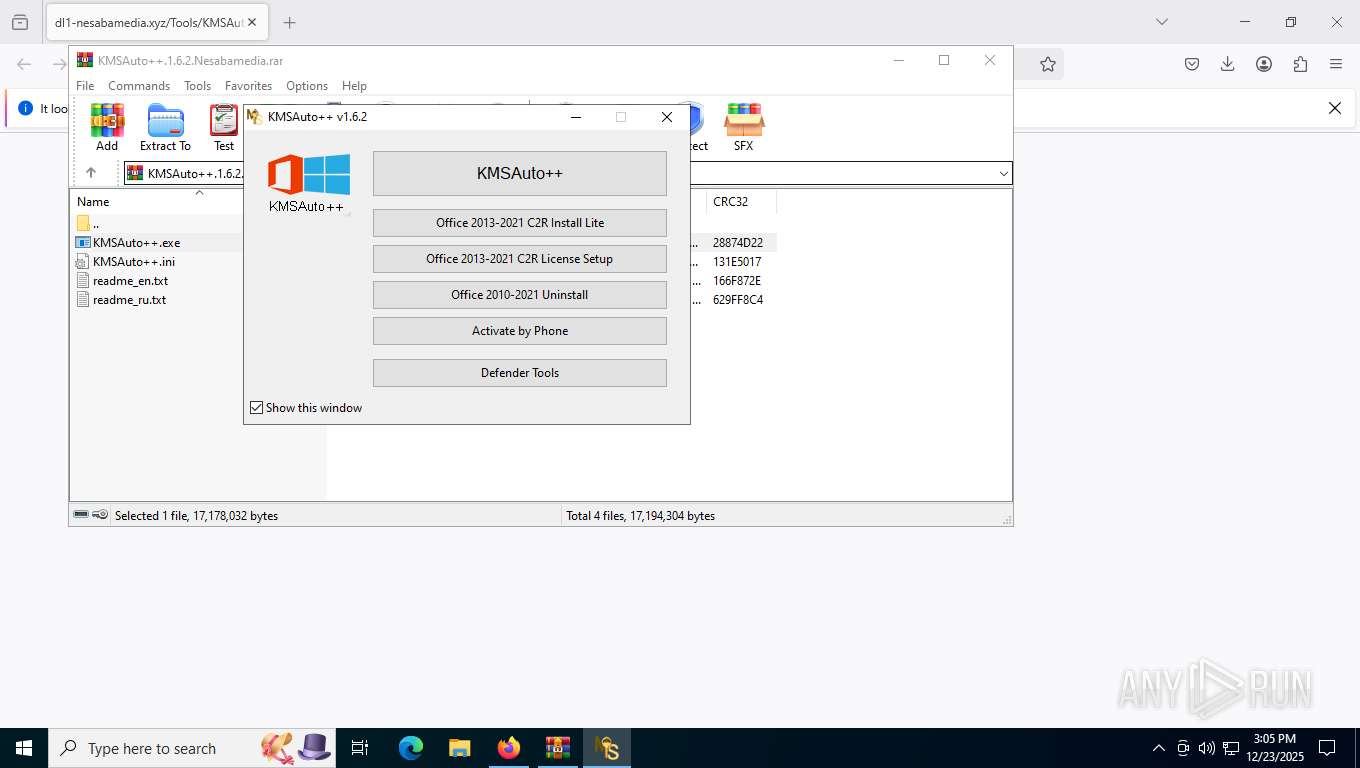
| URL: | https://dl1-nesabamedia.xyz/Tools/KMSAuto++.1.6.2.Nesabamedia.rar |
| Full analysis: | https://app.any.run/tasks/bcb8731b-7458-4cbc-9451-42640ceb7112 |
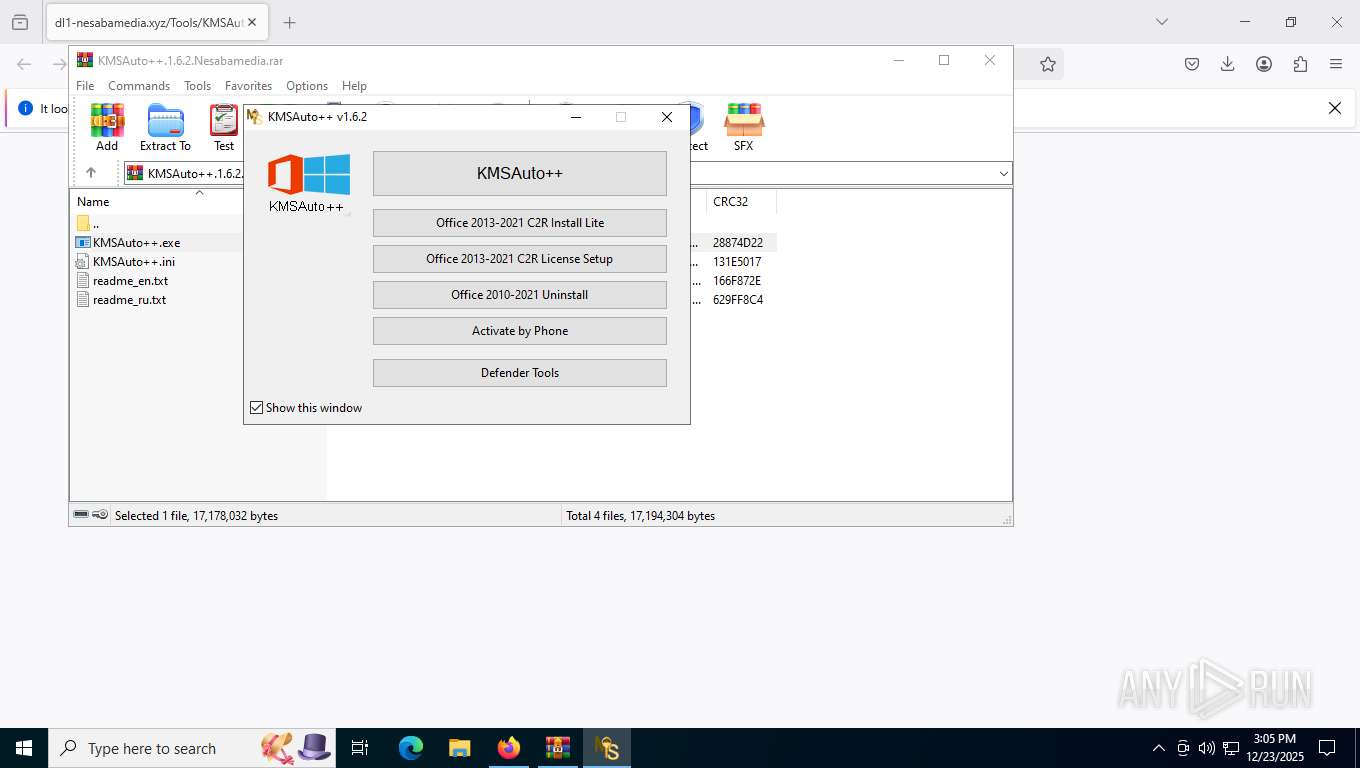
| Verdict: | Malicious activity |
| Analysis date: | December 23, 2025, 20:04:45 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 99420273F4DB6021CAFF3CE637FE6904 |
| SHA1: | 4DDEE428F289FA835F6F9916EAAD90E31161BB7A |
| SHA256: | B8627DC3D1BD2B09F2878437FEEDE2DC751F50F7F8B7D66D54B170169382F408 |
| SSDEEP: | 3:N8RR0DuduMJWKn2kjS3PxX+:2bcoWK2SS3M |
MALICIOUS
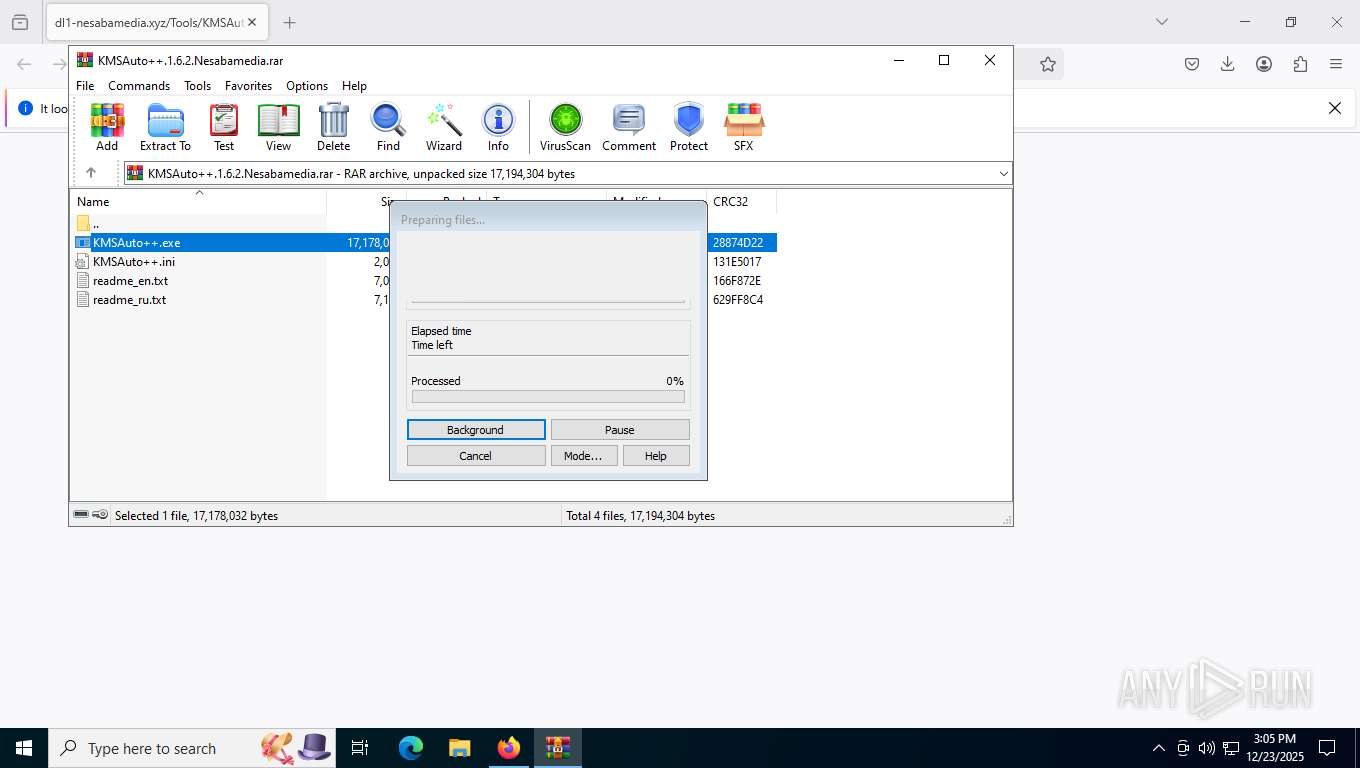
Executing a file with an untrusted certificate
- KMSAuto++.exe (PID: 8244)
- KMSAuto++.exe (PID: 8360)
- signtool.exe (PID: 8440)
- Defender Tools.exe (PID: 4284)
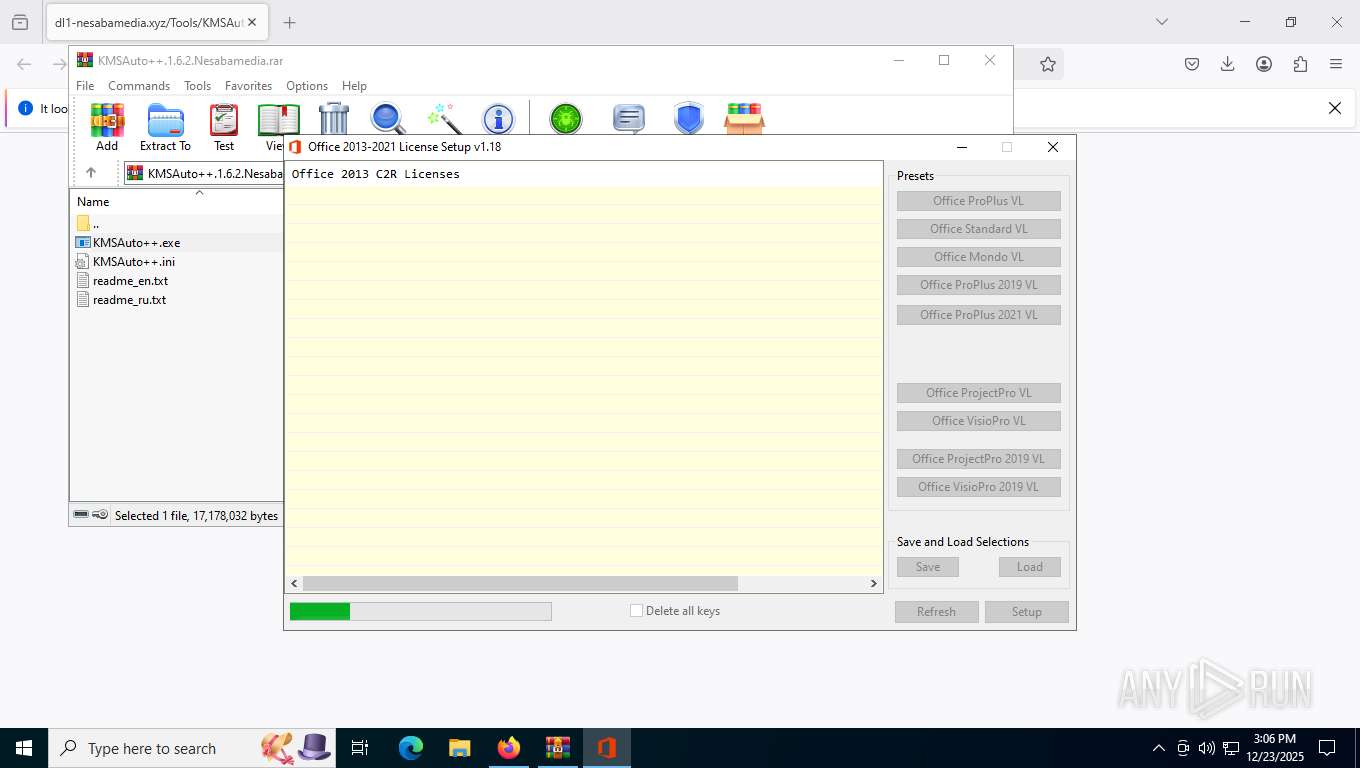
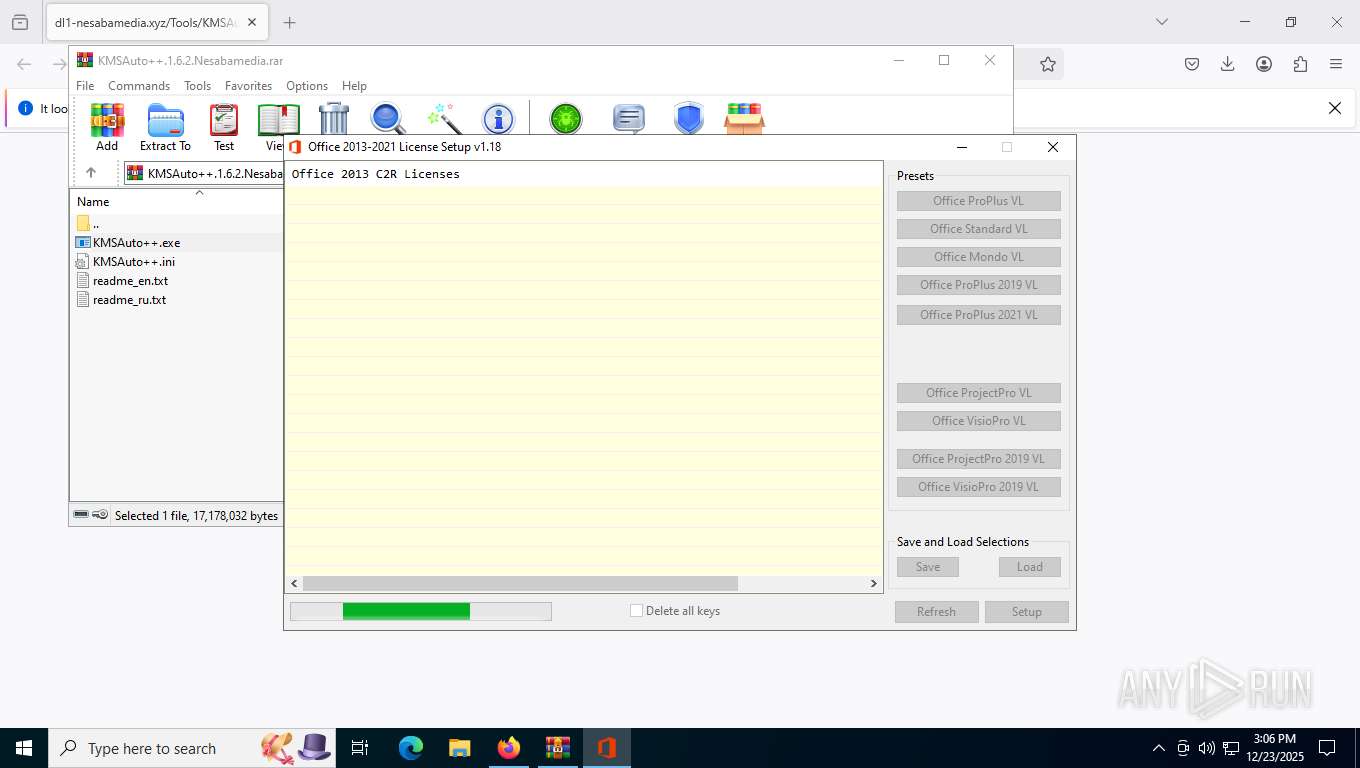
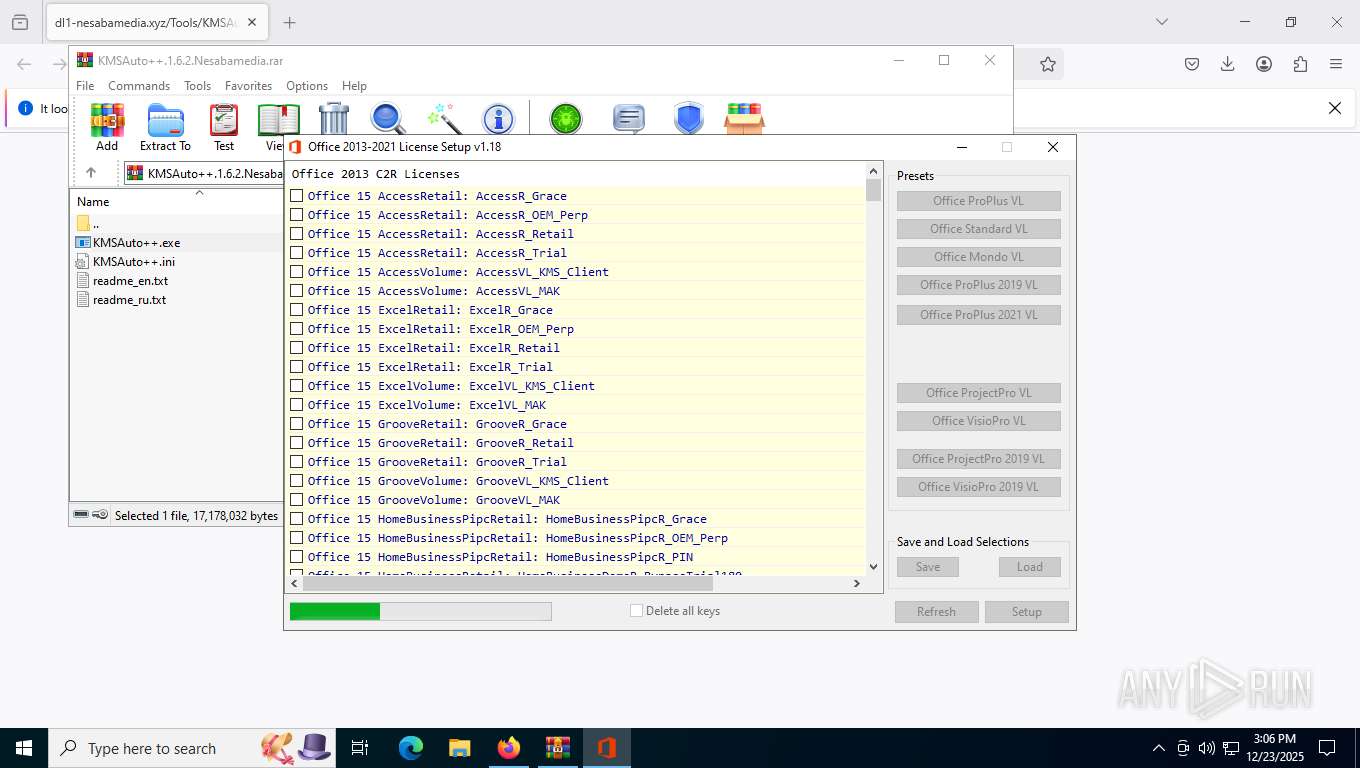
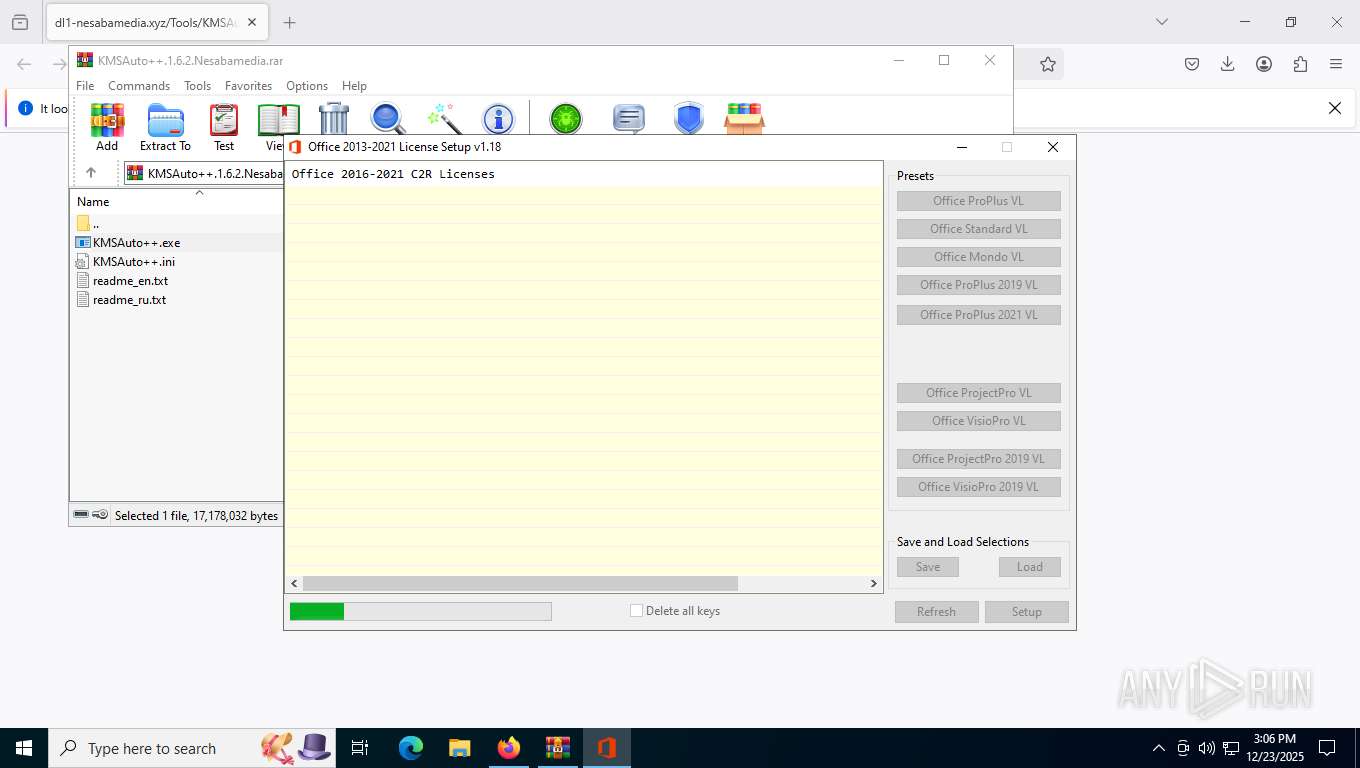
- O15-19LicSetup.exe (PID: 7260)
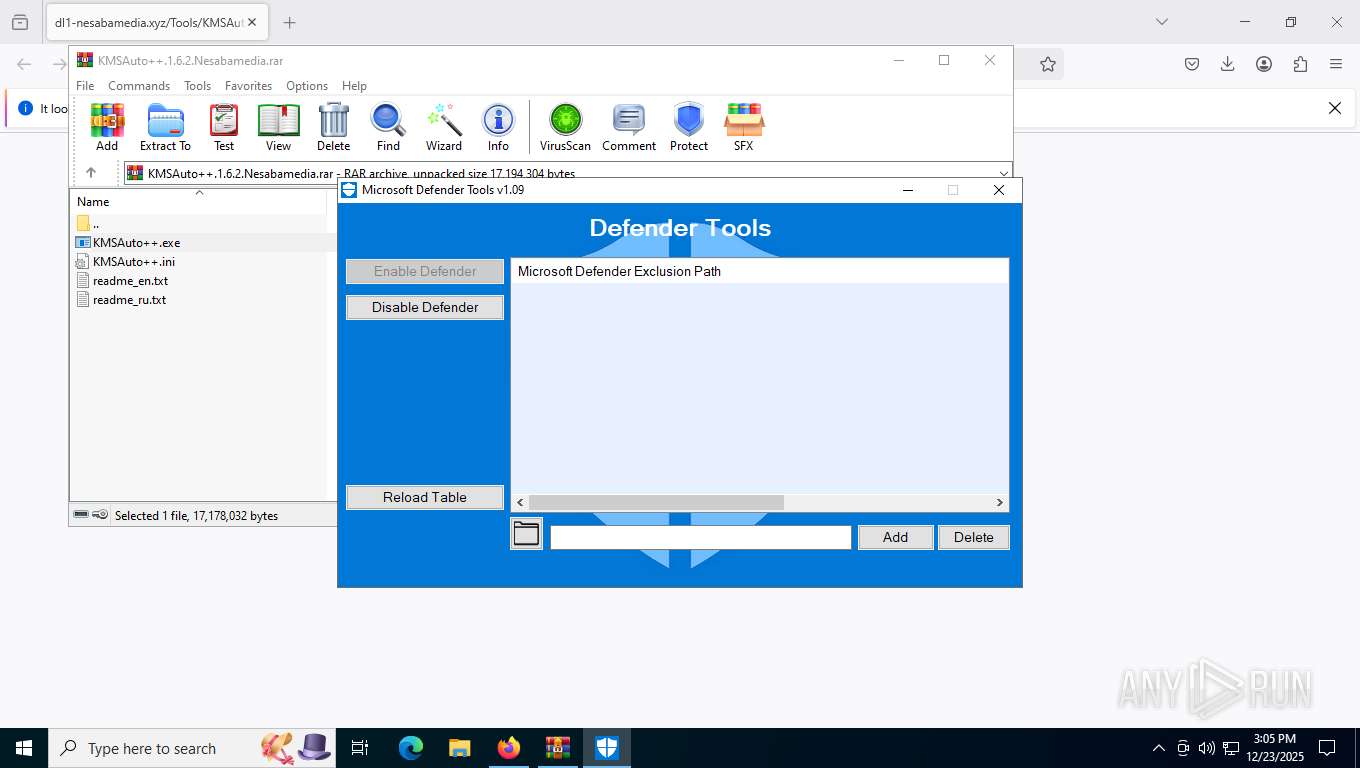
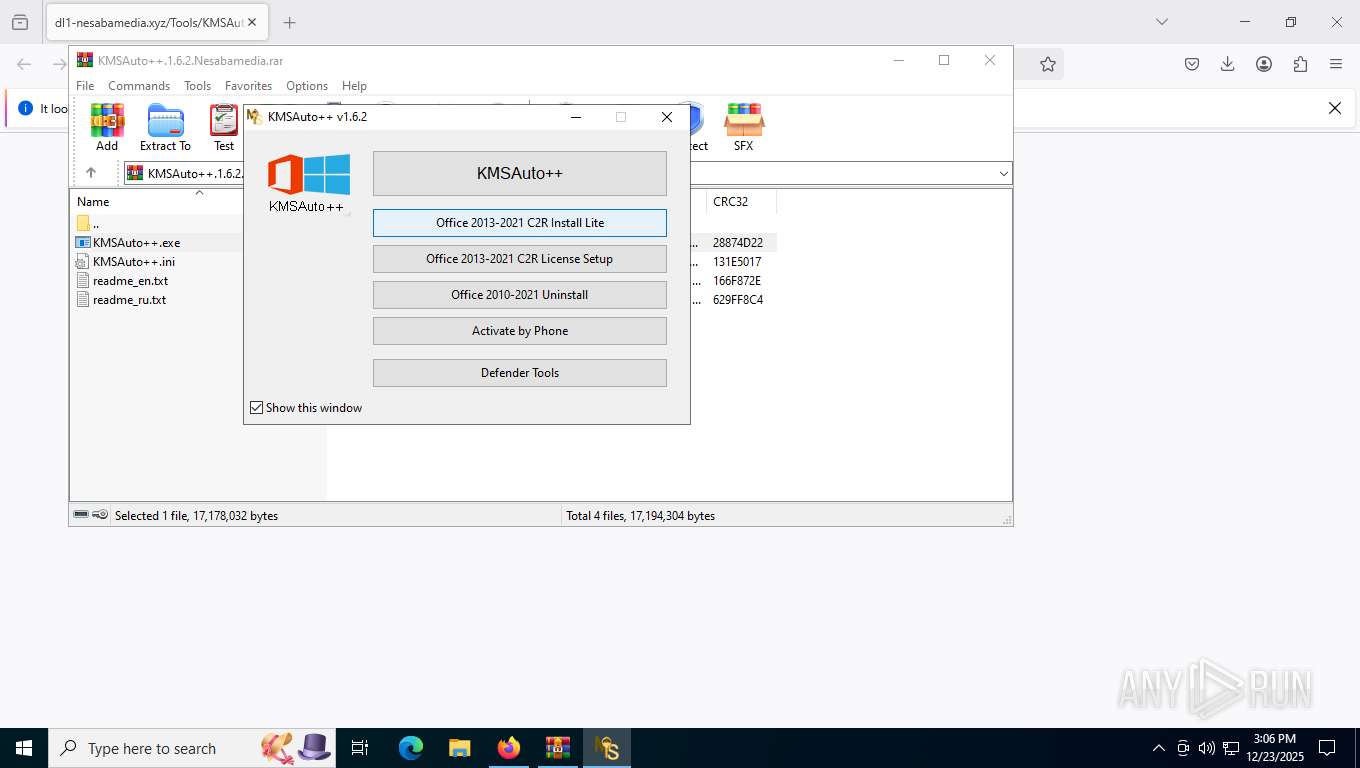
Uses WMIC.EXE to add exclusions to the Windows Defender
- cmd.exe (PID: 8720)
- cmd.exe (PID: 8536)
- cmd.exe (PID: 7480)
- cmd.exe (PID: 6196)
- cmd.exe (PID: 8684)
Changes settings of System certificates
- signtool.exe (PID: 8440)
Deletes shadow copies
- cmd.exe (PID: 9032)
Antivirus name has been found in the command line (generic signature)
- WMIC.exe (PID: 2748)
Disables Windows Defender
- reg.exe (PID: 4332)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 9156)
- signtool.exe (PID: 8440)
Found strings related to reading or modifying Windows Defender settings
- KMSAuto++.exe (PID: 8360)
- Defender Tools.exe (PID: 4284)
Starts CMD.EXE for commands execution
- KMSAuto++.exe (PID: 8360)
- Defender Tools.exe (PID: 4284)
- loader.exe (PID: 8940)
- O15-19LicSetup.exe (PID: 7260)
Adds/modifies Windows certificates
- signtool.exe (PID: 8440)
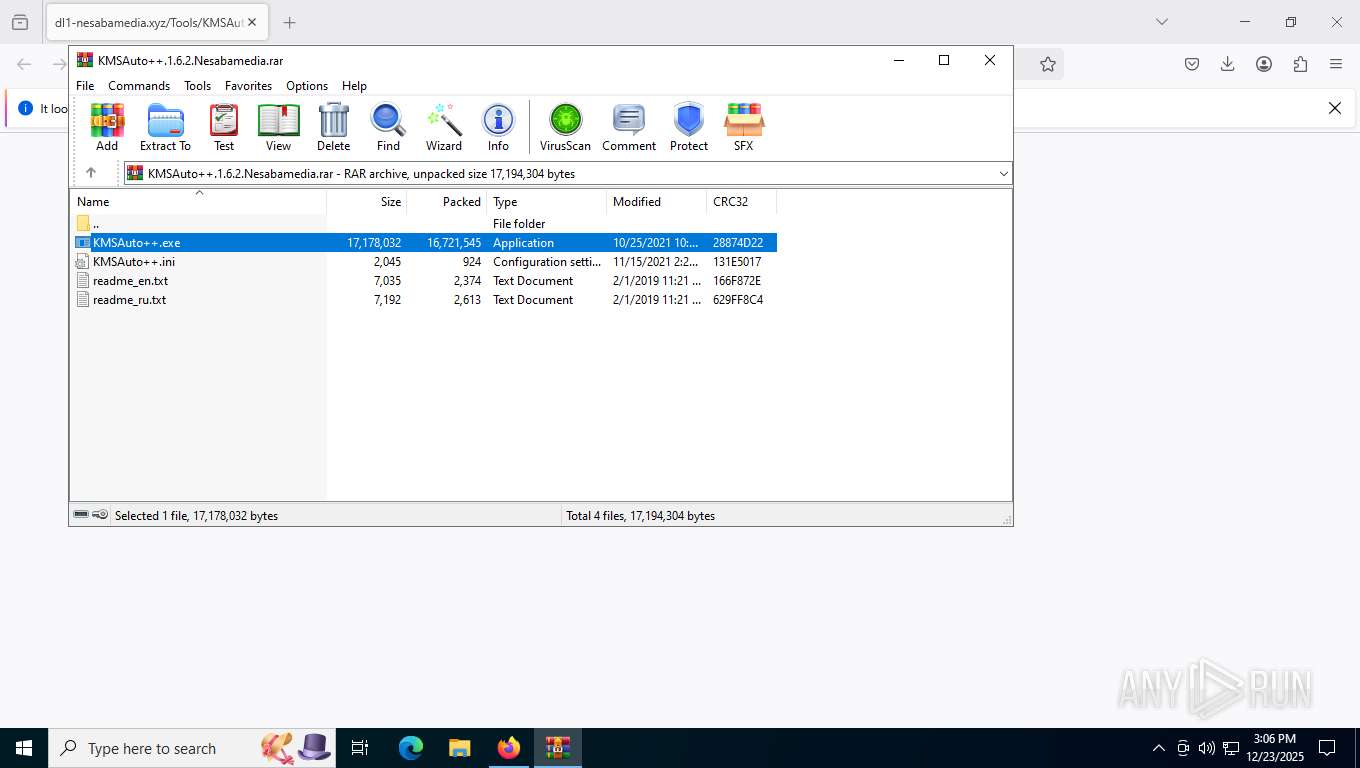
Process drops legitimate windows executable
- KMSAuto++.exe (PID: 8360)
- files.dat (PID: 8412)
Starts a Microsoft application from unusual location
- signtool.exe (PID: 8440)
Executable content was dropped or overwritten
- KMSAuto++.exe (PID: 8360)
- Defender Tools.exe (PID: 4284)
- O15-19LicSetup.exe (PID: 7260)
- files.dat (PID: 8412)
Executing commands from ".cmd" file
- loader.exe (PID: 8940)
Starts SC.EXE for service management
- cmd.exe (PID: 9032)
Uses WMIC.EXE to obtain data on processes
- cmd.exe (PID: 9032)
Windows service management via SC.EXE
- sc.exe (PID: 7480)
- sc.exe (PID: 4476)
- sc.exe (PID: 2740)
- sc.exe (PID: 8724)
- sc.exe (PID: 1772)
- sc.exe (PID: 6344)
Uses WMIC.EXE to obtain service application data
- cmd.exe (PID: 9032)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 9032)
Starts application with an unusual extension
- cmd.exe (PID: 7256)
- cmd.exe (PID: 2360)
There is functionality for taking screenshot (YARA)
- O15-19LicSetup.exe (PID: 7260)
The process drops C-runtime libraries
- files.dat (PID: 8412)
Drops 7-zip archiver for unpacking
- O15-19LicSetup.exe (PID: 7260)
The process executes VB scripts
- cmd.exe (PID: 1956)
Creates FileSystem object to access computer's file system (SCRIPT)
- cscript.exe (PID: 2680)
Gets full path of the running script (SCRIPT)
- cscript.exe (PID: 2680)
Enumerates operating system information (Win32_OperatingSystem) (SCRIPT)
- cscript.exe (PID: 2680)
Accesses computer name via WMI (SCRIPT)
- cscript.exe (PID: 2680)
Accesses WMI object, sets custom ImpersonationLevel (SCRIPT)
- cscript.exe (PID: 2680)
Executes WMI query (SCRIPT)
- cscript.exe (PID: 2680)
Sets XML DOM element text (SCRIPT)
- cscript.exe (PID: 2680)
Gets a collection of all available drive names (SCRIPT)
- cscript.exe (PID: 2680)
Gets the drive type (SCRIPT)
- cscript.exe (PID: 2680)
INFO
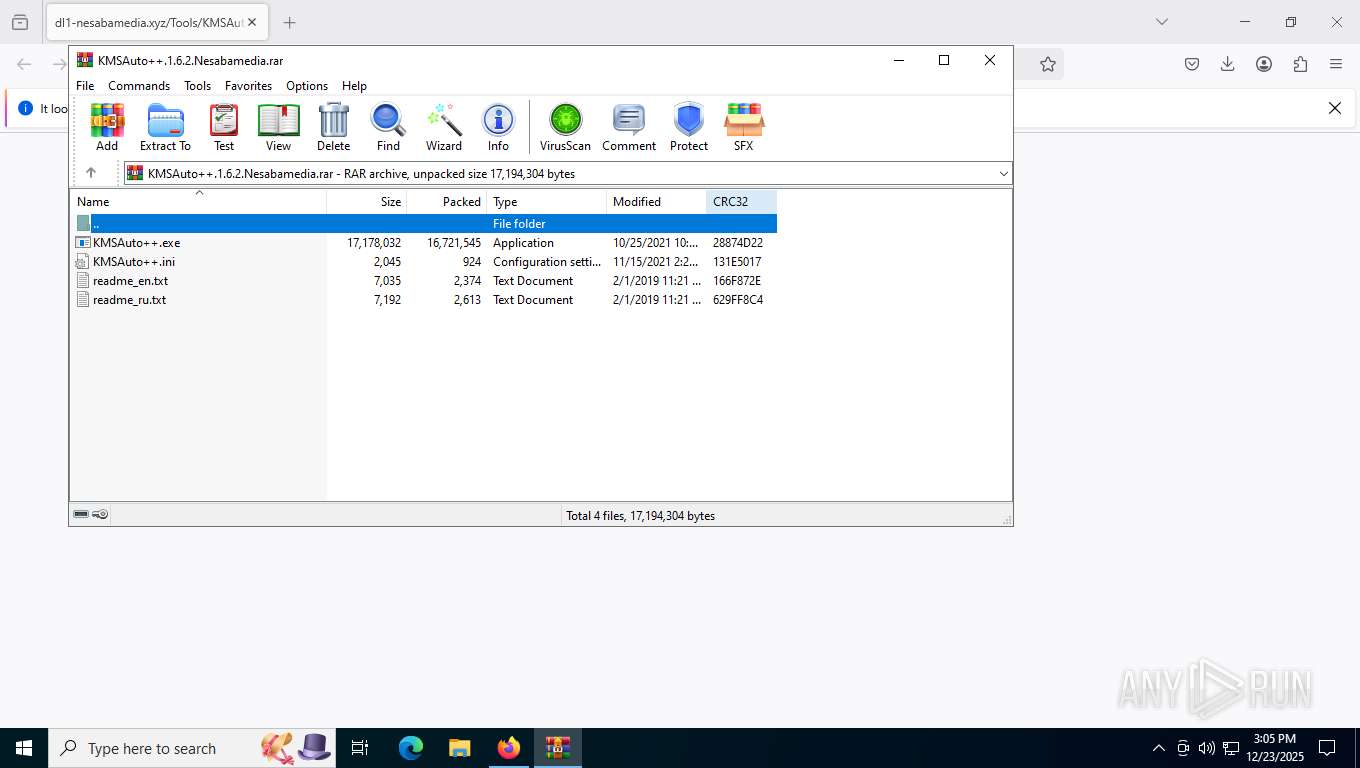
Manual execution by a user
- WinRAR.exe (PID: 9156)
Application launched itself
- firefox.exe (PID: 7540)
- firefox.exe (PID: 7636)
Checks supported languages
- KMSAuto++.exe (PID: 8360)
- signtool.exe (PID: 8440)
- Defender Tools.exe (PID: 4284)
- loader.exe (PID: 8940)
- O15-19LicSetup.exe (PID: 7260)
- files.dat (PID: 8412)
- files.dat (PID: 6580)
Reads Environment values
- KMSAuto++.exe (PID: 8360)
Reads product name
- KMSAuto++.exe (PID: 8360)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 9156)
- firefox.exe (PID: 7636)
Reads the computer name
- KMSAuto++.exe (PID: 8360)
- loader.exe (PID: 8940)
- Defender Tools.exe (PID: 4284)
- O15-19LicSetup.exe (PID: 7260)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 8404)
- WMIC.exe (PID: 8744)
- WMIC.exe (PID: 8844)
- WMIC.exe (PID: 8516)
- WMIC.exe (PID: 8812)
- WMIC.exe (PID: 3656)
- WMIC.exe (PID: 8472)
- WMIC.exe (PID: 2680)
- WMIC.exe (PID: 1352)
- WMIC.exe (PID: 2748)
- WMIC.exe (PID: 3368)
- WMIC.exe (PID: 5628)
- WMIC.exe (PID: 8392)
- WMIC.exe (PID: 8244)
- WMIC.exe (PID: 3048)
- WMIC.exe (PID: 8592)
- cscript.exe (PID: 2680)
Reads the machine GUID from the registry
- signtool.exe (PID: 8440)
Create files in a temporary directory
- KMSAuto++.exe (PID: 8360)
- Defender Tools.exe (PID: 4284)
- O15-19LicSetup.exe (PID: 7260)
- files.dat (PID: 8412)
- files.dat (PID: 6580)
The sample compiled with english language support
- KMSAuto++.exe (PID: 8360)
- O15-19LicSetup.exe (PID: 7260)
- files.dat (PID: 8412)
UPX packer has been detected
- KMSAuto++.exe (PID: 8360)
- O15-19LicSetup.exe (PID: 7260)
Checks proxy server information
- cscript.exe (PID: 2680)
- slui.exe (PID: 8488)
Creates files or folders in the user directory
- cscript.exe (PID: 2680)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
311
Monitored processes
165
Malicious processes
11
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 144 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | reg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 424 | "C:\WINDOWS\Sysnative\reg.exe" query "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Defender" /v DisableAntivirus | C:\Windows\System32\reg.exe | — | KMSAuto++.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 424 | "C:\WINDOWS\Sysnative\reg.exe" query "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Defender" /v DisableAntivirus | C:\Windows\System32\reg.exe | — | KMSAuto++.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 756 | "C:\WINDOWS\Sysnative\reg.exe" query "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Defender" /v DisableAntivirus | C:\Windows\System32\reg.exe | — | KMSAuto++.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1172 | "C:\WINDOWS\Sysnative\reg.exe" query "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Defender" /v DisableAntivirus | C:\Windows\System32\reg.exe | — | KMSAuto++.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1296 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | reg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1312 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | reg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1352 | wmic process where name='smartscreen.exe' delete | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1572 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | reg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1772 | sc config WdNisSvc start=disabled | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Service Control Manager Configuration Tool Exit code: 5 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
15 653
Read events
15 634
Write events
16
Delete events
3
Modification events
| (PID) Process: | (9156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (9156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (9156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (9156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\KMSAuto++.1.6.2.Nesabamedia.rar | |||
| (PID) Process: | (9156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (9156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (9156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (9156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (8360) KMSAuto++.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (8440) signtool.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates |
| Operation: | delete value | Name: | 2B8F1B57330DBBA2D07A6C51F70EE90DDAB9AD8E |
Value: | |||
Executable files
13
Suspicious files
254
Text files
2 332
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7636 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 7636 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-child-current.bin | binary | |
MD5:5152D8F49F1AD4219D935611EFE18437 | SHA256:9A6E50715E3C49A43E3D622EDE7E37ECF0767342B3039B8B0AE25BBE4FF6F66E | |||
| 7636 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7636 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 7636 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7636 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7636 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | text | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 7636 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7636 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:B30329D7D2CF4258C22F500CBEA218FF | SHA256:C5E20431B116E1DABD383C6855A36E6DAF13E1CC125B83D59EF68B4BCEFB02E6 | |||
| 7636 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | text | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
109
TCP/UDP connections
57
DNS requests
100
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7636 | firefox.exe | GET | 101 | 34.107.243.93:443 | https://push.services.mozilla.com/ | unknown | — | — | unknown |
7636 | firefox.exe | GET | 200 | 34.160.144.191:443 | https://content-signature-2.cdn.mozilla.net/g/chains/202402/remote-settings.content-signature.mozilla.org-2025-11-08-08-20-52.chain | unknown | — | 5.18 Kb | unknown |
7636 | firefox.exe | GET | 200 | 104.21.25.118:443 | https://dl1-nesabamedia.xyz/Tools/KMSAuto++.1.6.2.Nesabamedia.rar | unknown | compressed | 128 Kb | unknown |
7636 | firefox.exe | GET | 200 | 34.36.137.203:443 | https://contile.services.mozilla.com/v1/tiles | unknown | text | 5.63 Kb | unknown |
7636 | firefox.exe | GET | 200 | 34.160.144.191:443 | https://content-signature-2.cdn.mozilla.net/g/chains/202402/remote-settings.content-signature.mozilla.org-2025-11-08-08-20-52.chain | unknown | — | 5.18 Kb | unknown |
7636 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | unknown |
7636 | firefox.exe | POST | 200 | 142.250.186.163:80 | http://o.pki.goog/s/wr3/peI | unknown | — | — | whitelisted |
7636 | firefox.exe | POST | 200 | 142.250.186.163:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
7636 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | unknown |
7636 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1600 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6768 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6148 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7636 | firefox.exe | 34.160.144.191:443 | content-signature-2.cdn.mozilla.net | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
7636 | firefox.exe | 34.107.243.93:443 | push.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
7636 | firefox.exe | 142.250.186.163:80 | o.pki.goog | GOOGLE | US | whitelisted |
7636 | firefox.exe | 151.101.193.91:443 | firefox.settings.services.mozilla.com | FASTLY | US | whitelisted |
7636 | firefox.exe | 104.21.25.118:443 | dl1-nesabamedia.xyz | CLOUDFLARENET | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
content-signature-2.cdn.mozilla.net |
| whitelisted |
dl1-nesabamedia.xyz |
| unknown |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| whitelisted |
mc.prod.ads.prod.webservices.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |