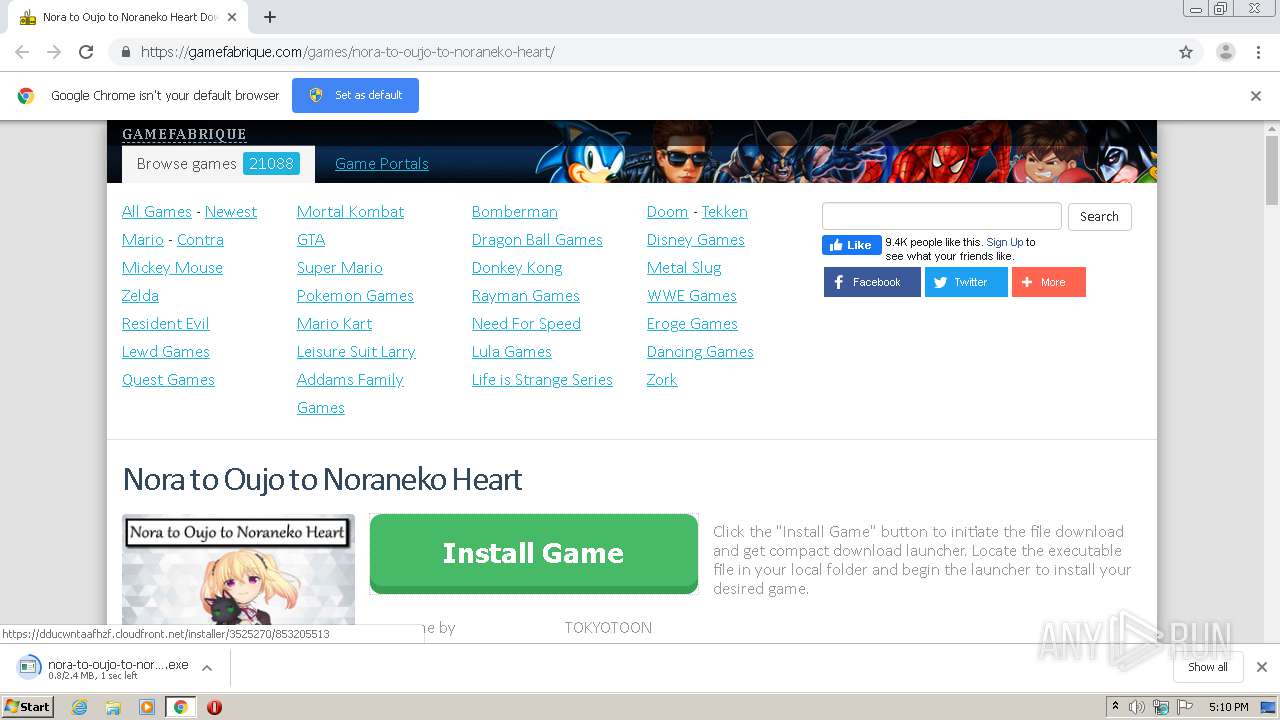
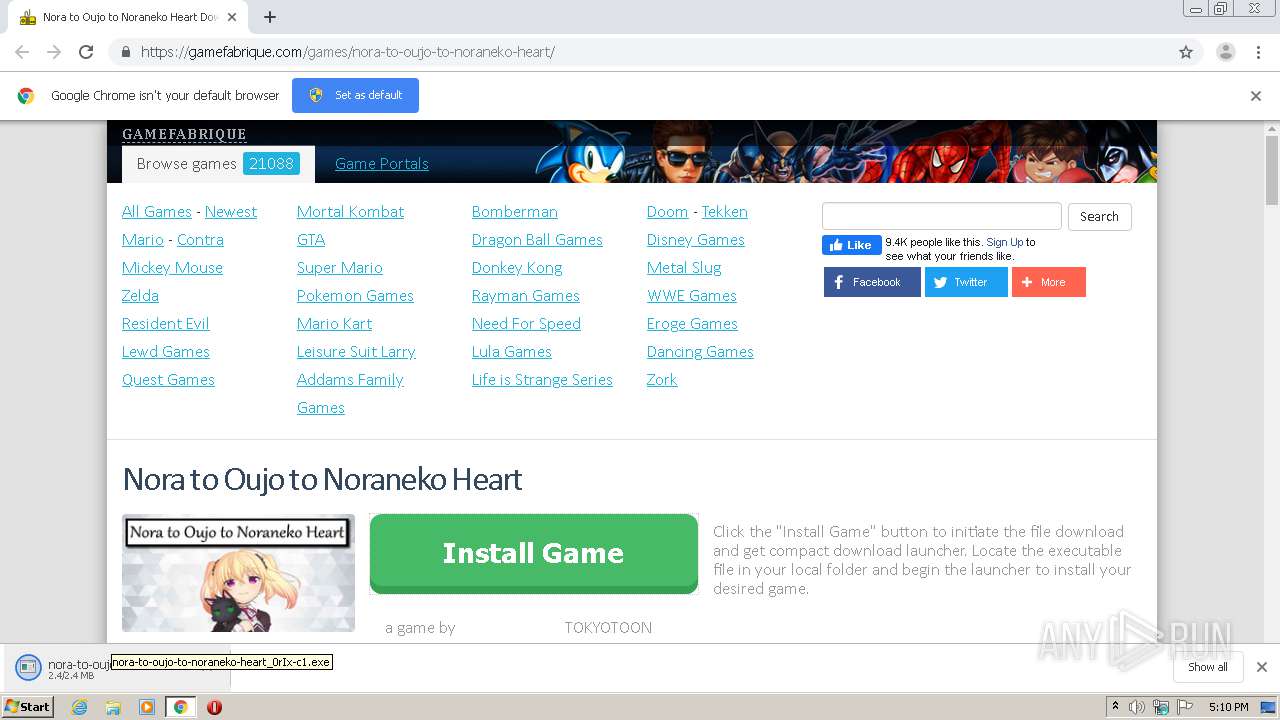
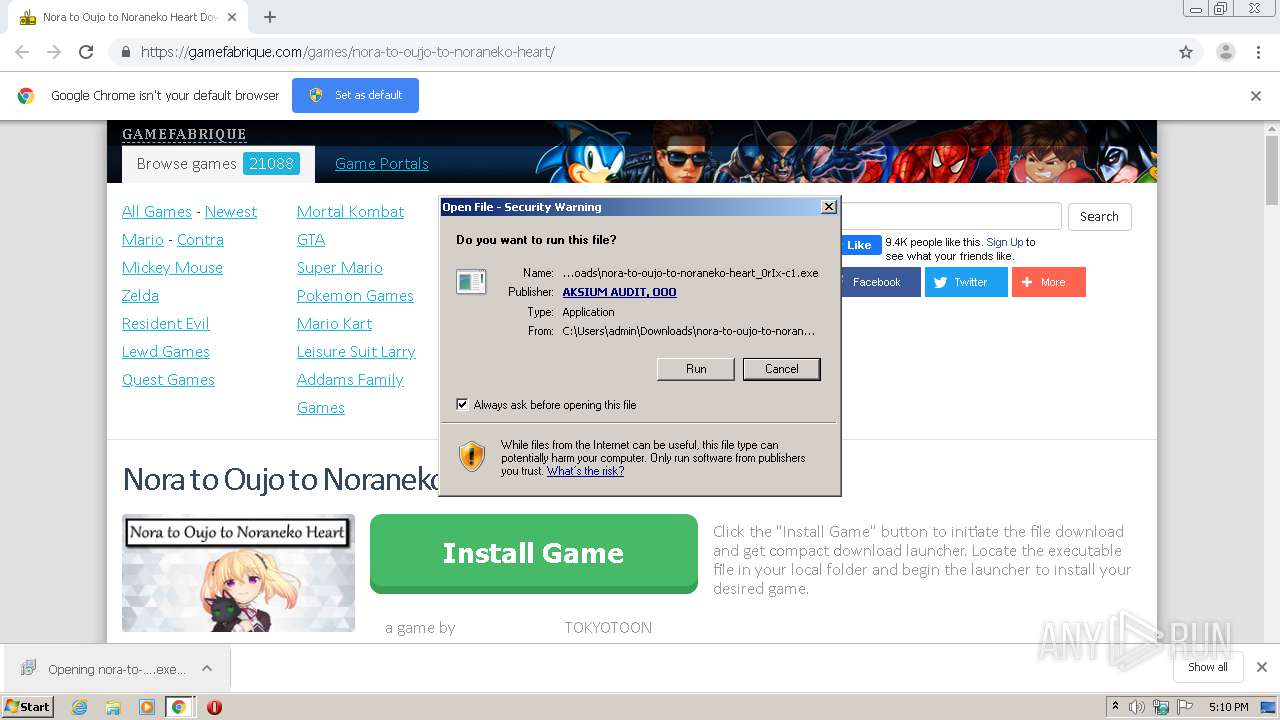
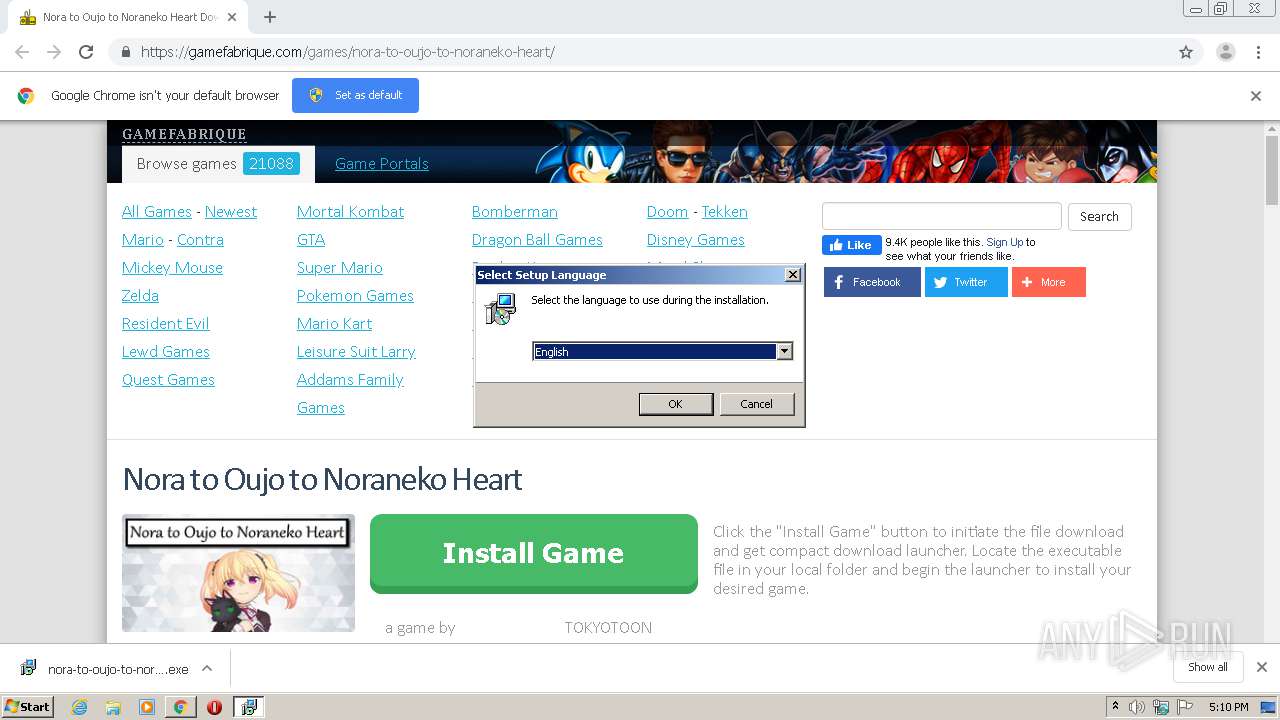
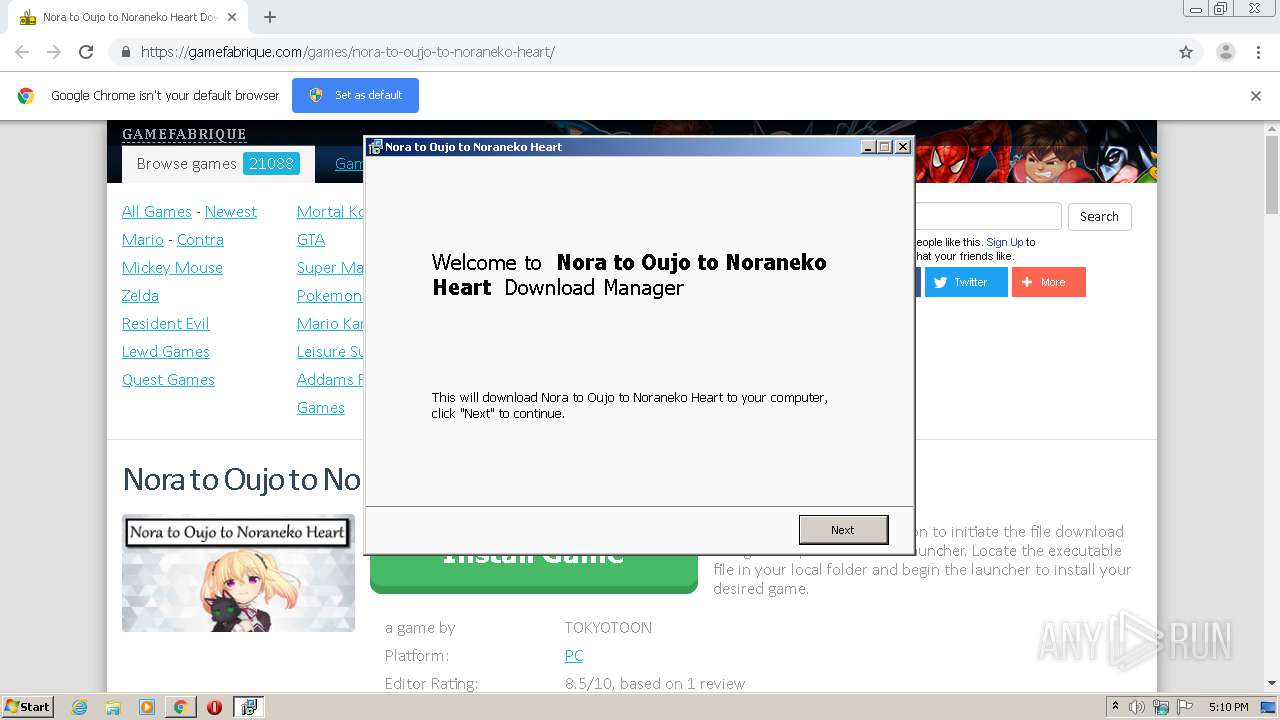
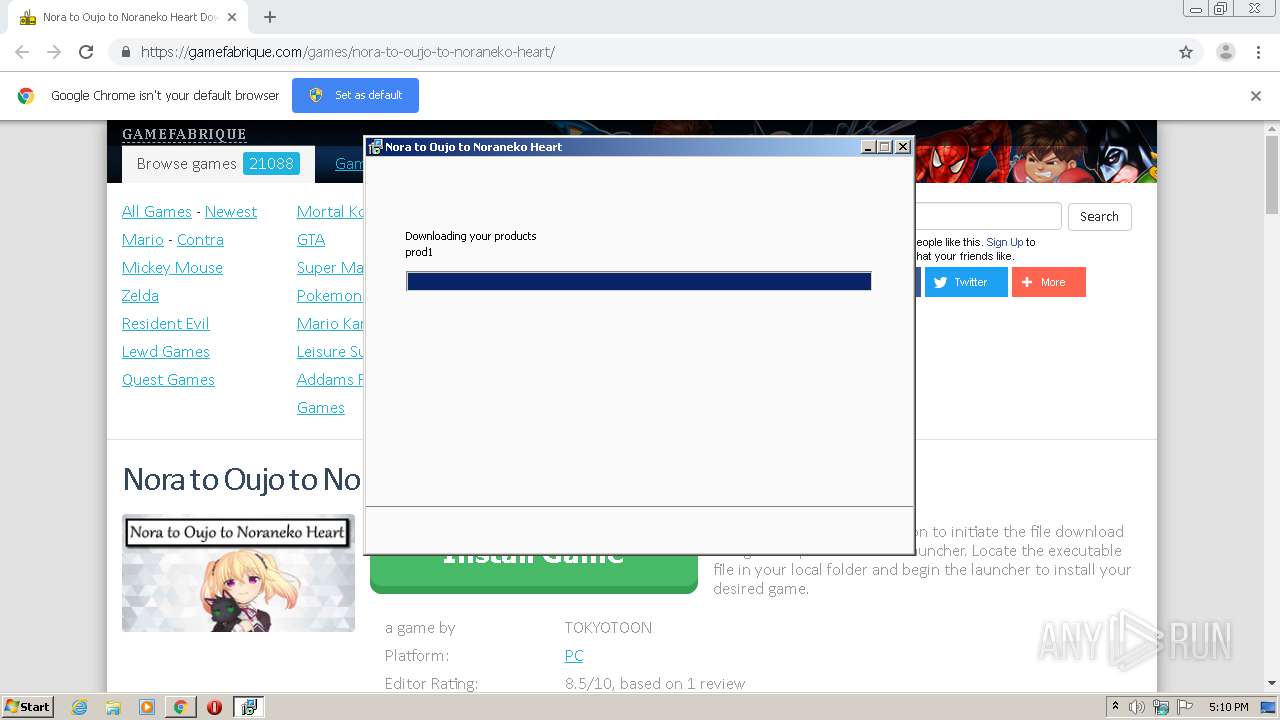
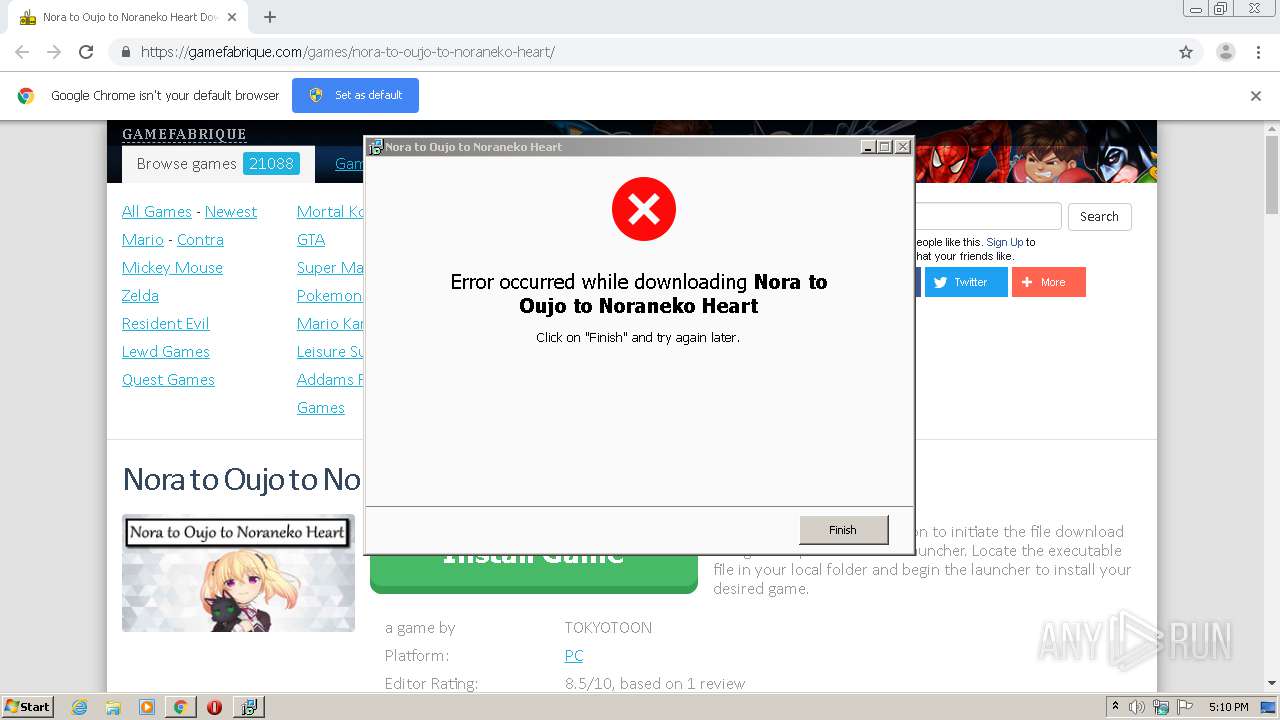
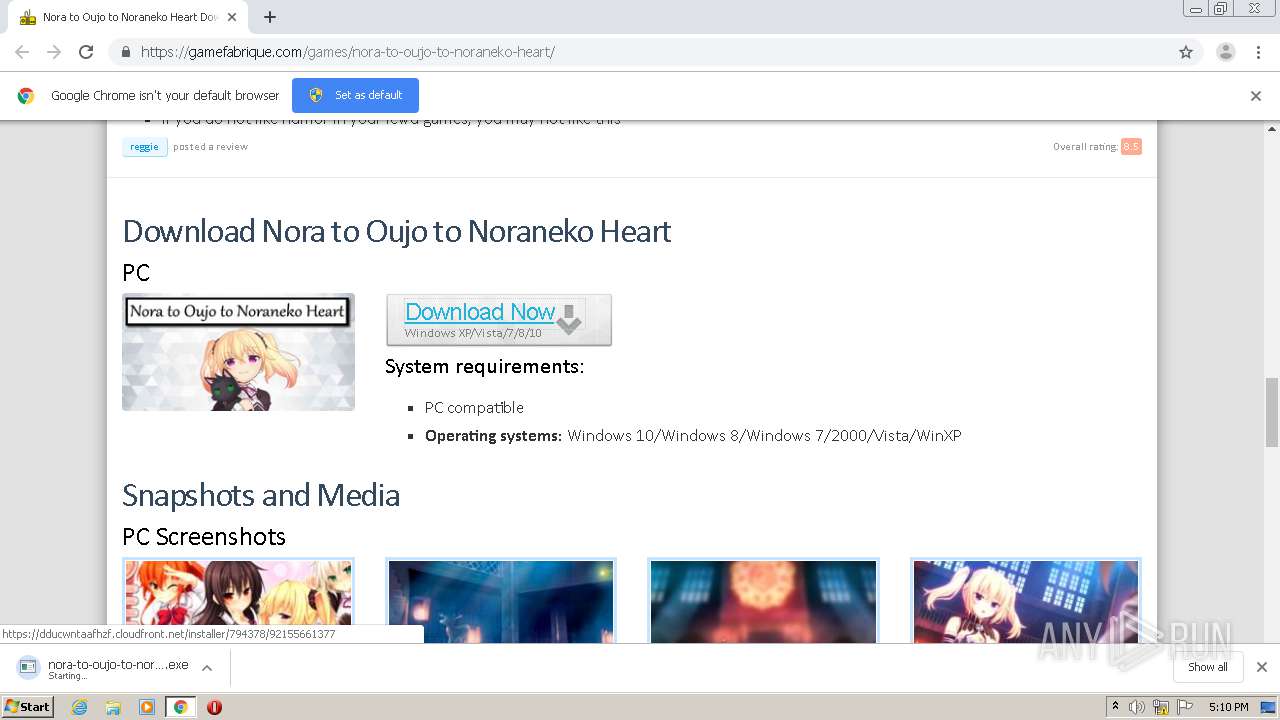
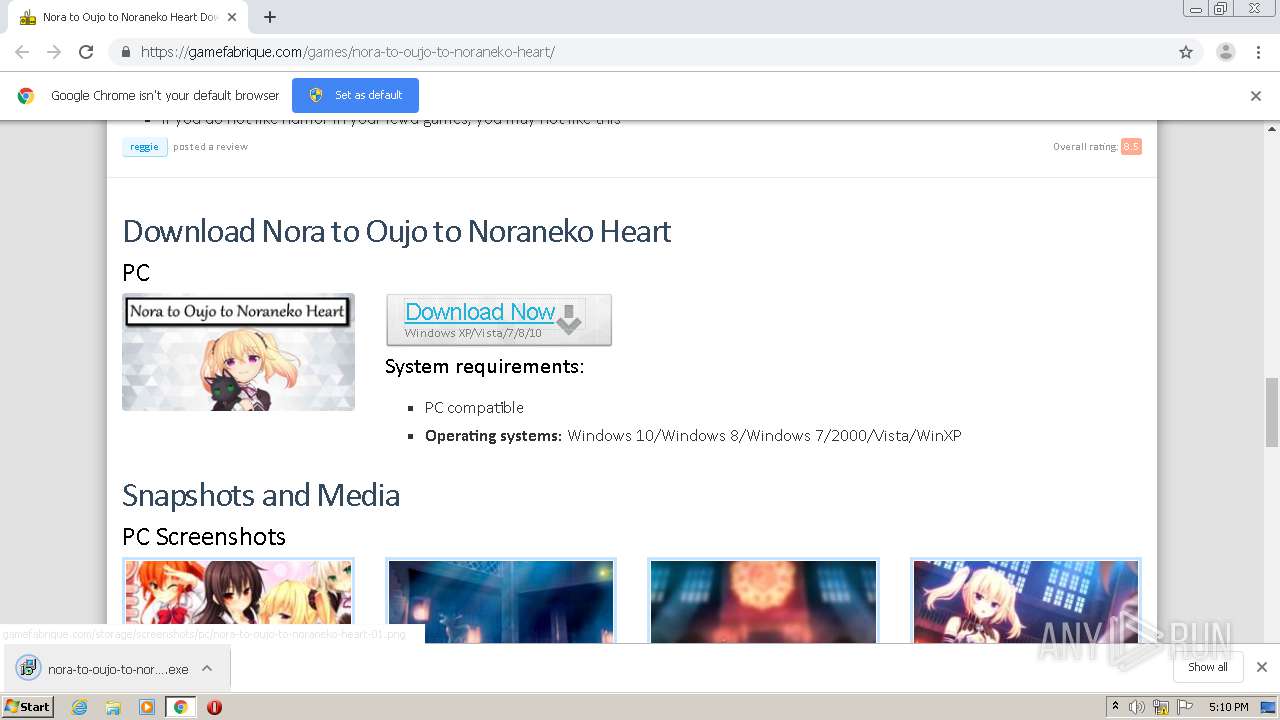
| URL: | https://gamefabrique.com/games/nora-to-oujo-to-noraneko-heart/ |
| Full analysis: | https://app.any.run/tasks/70ea6cc7-4dc6-492e-89a7-5ccbe8bc4660 |
| Verdict: | Malicious activity |
| Analysis date: | March 27, 2021, 17:09:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 2E1A59598768AD062F042A2F9717A425 |
| SHA1: | 13C7834E9439A983CE07AB28792D51CEC7EA8335 |
| SHA256: | B8488D1C1D464C35C0702EC5FB895127145E0C0C4C86C29644BE218DCEC32A75 |
| SSDEEP: | 3:N8l0XMUhGGCEIzK2RK3adHKU0MXRK:22XMPVFK3nzN |
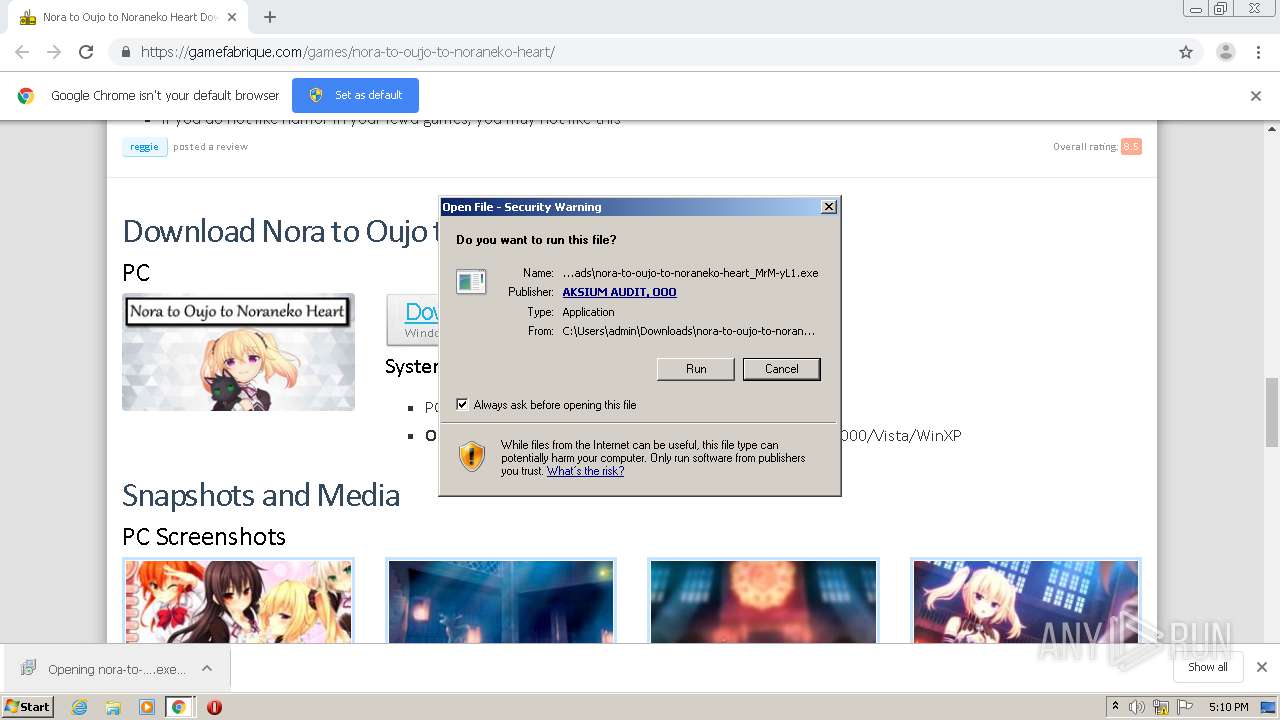
MALICIOUS
Application was dropped or rewritten from another process
- nora-to-oujo-to-noraneko-heart_0rIx-c1.exe (PID: 2920)
- nora-to-oujo-to-noraneko-heart_0rIx-c1.exe (PID: 3964)
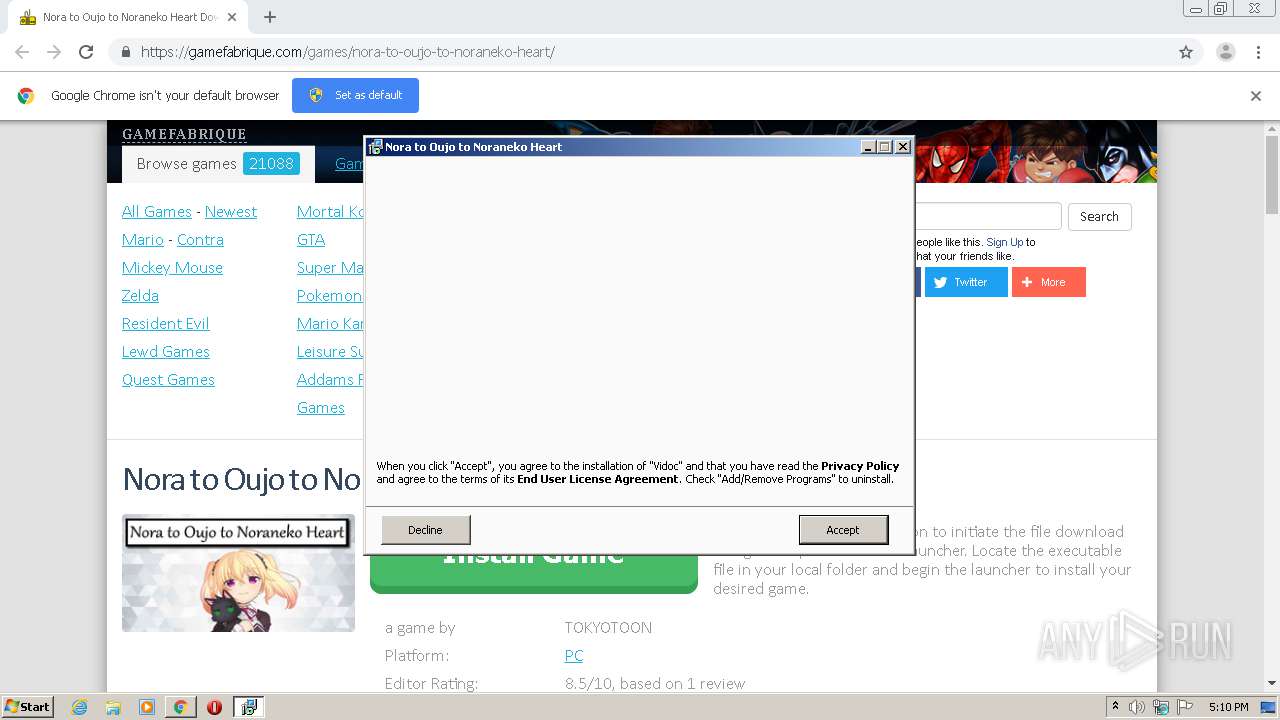
- Vidoc-Downloader-px.exe (PID: 324)
- saBSI.exe (PID: 3656)
Drops executable file immediately after starts
- nora-to-oujo-to-noraneko-heart_0rIx-c1.exe (PID: 2920)
Changes settings of System certificates
- nora-to-oujo-to-noraneko-heart_0rIx-c1.tmp (PID: 956)
- saBSI.exe (PID: 3656)
- Vidoc-Downloader-px.tmp (PID: 2788)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2188)
- nora-to-oujo-to-noraneko-heart_0rIx-c1.exe (PID: 2920)
- nora-to-oujo-to-noraneko-heart_0rIx-c1.exe (PID: 3964)
- nora-to-oujo-to-noraneko-heart_0rIx-c1.tmp (PID: 956)
- Vidoc-Downloader-px.exe (PID: 324)
Reads Windows owner or organization settings
- nora-to-oujo-to-noraneko-heart_0rIx-c1.tmp (PID: 956)
- Vidoc-Downloader-px.tmp (PID: 2788)
Reads the Windows organization settings
- nora-to-oujo-to-noraneko-heart_0rIx-c1.tmp (PID: 956)
- Vidoc-Downloader-px.tmp (PID: 2788)
Drops a file with too old compile date
- nora-to-oujo-to-noraneko-heart_0rIx-c1.tmp (PID: 956)
Drops a file that was compiled in debug mode
- nora-to-oujo-to-noraneko-heart_0rIx-c1.tmp (PID: 956)
Adds / modifies Windows certificates
- nora-to-oujo-to-noraneko-heart_0rIx-c1.tmp (PID: 956)
- saBSI.exe (PID: 3656)
- Vidoc-Downloader-px.tmp (PID: 2788)
Creates files in the program directory
- saBSI.exe (PID: 3656)
INFO
Reads the hosts file
- chrome.exe (PID: 2188)
- chrome.exe (PID: 2204)
Application launched itself
- chrome.exe (PID: 2188)
Reads settings of System Certificates
- chrome.exe (PID: 2188)
Application was dropped or rewritten from another process
- nora-to-oujo-to-noraneko-heart_0rIx-c1.tmp (PID: 4060)
- nora-to-oujo-to-noraneko-heart_0rIx-c1.tmp (PID: 956)
- Vidoc-Downloader-px.tmp (PID: 2788)
Loads dropped or rewritten executable
- nora-to-oujo-to-noraneko-heart_0rIx-c1.tmp (PID: 956)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
62
Monitored processes
22
Malicious processes
4
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 324 | "C:\Users\admin\AppData\Local\Temp\is-FDO2J.tmp\prod1_extract\Vidoc-Downloader-px.exe" /px=2bJ1kfr6wJ7mQ4aMh7T8NfhBpx54zToeNLtlGaxKbmWqVpuu70Kjrd6JlmPVDam2F6Oor24horOS2 /verysilent | C:\Users\admin\AppData\Local\Temp\is-FDO2J.tmp\prod1_extract\Vidoc-Downloader-px.exe | nora-to-oujo-to-noraneko-heart_0rIx-c1.tmp | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: VidocDownloader Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,5571193069399920746,7942754445851064152,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10243692380417502986 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1180 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 956 | "C:\Users\admin\AppData\Local\Temp\is-D78IQ.tmp\nora-to-oujo-to-noraneko-heart_0rIx-c1.tmp" /SL5="$30176,1599450,780800,C:\Users\admin\Downloads\nora-to-oujo-to-noraneko-heart_0rIx-c1.exe" /SPAWNWND=$20178 /NOTIFYWND=$20162 | C:\Users\admin\AppData\Local\Temp\is-D78IQ.tmp\nora-to-oujo-to-noraneko-heart_0rIx-c1.tmp | nora-to-oujo-to-noraneko-heart_0rIx-c1.exe | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Setup/Uninstall Exit code: 2 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1028,5571193069399920746,7942754445851064152,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=11202872365829899610 --mojo-platform-channel-handle=4664 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1472 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1028,5571193069399920746,7942754445851064152,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=11871201306235952696 --mojo-platform-channel-handle=1052 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1740 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,5571193069399920746,7942754445851064152,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17631381886731658860 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3760 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2104 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,5571193069399920746,7942754445851064152,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17631731662413505103 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2348 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2136 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,5571193069399920746,7942754445851064152,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2135949911942817015 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3248 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://gamefabrique.com/games/nora-to-oujo-to-noraneko-heart/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2204 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,5571193069399920746,7942754445851064152,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=4317020752372030957 --mojo-platform-channel-handle=1456 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 853
Read events
1 722
Write events
124
Delete events
7
Modification events
| (PID) Process: | (2188) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2188) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2188) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2188) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2188) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2188-13261338599994000 |
Value: 259 | |||
| (PID) Process: | (2188) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2188) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2188) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2188) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
14
Suspicious files
35
Text files
75
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-605F66E8-88C.pma | — | |
MD5:— | SHA256:— | |||
| 2188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\042445a6-58a0-4f0c-b547-4e77276e9dcd.tmp | — | |
MD5:— | SHA256:— | |||
| 2188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF13450b.TMP | text | |
MD5:D4322EEBAC92D1B8F7A6F5E39F6264B7 | SHA256:A3EEDF21B850DCC7CE5AE04395ECDD2D29DA4EA549C8A185DD9E8B552A87B8C2 | |||
| 2188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:D4322EEBAC92D1B8F7A6F5E39F6264B7 | SHA256:A3EEDF21B850DCC7CE5AE04395ECDD2D29DA4EA549C8A185DD9E8B552A87B8C2 | |||
| 2188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF1345c6.TMP | text | |
MD5:1C97B70A4BAD7C026F79467C7D496AFA | SHA256:C5A02E4984DE3F30DADFC0A89A93F45418C06653C3962EAA94C93909E51D272D | |||
| 2188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT~RF1345e6.TMP | text | |
MD5:74D4DB05A4D3E7263E8AE314DEDD8DF1 | SHA256:67BF9950E818713E054268D40BED61A22D324385CE98E89DDF406A405B870802 | |||
| 2188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:1A89A1BEBE6C843C4FF582E7ED33CA1F | SHA256:65099CA087B66AA8CA420AB121DAAD713E1DB5A61C5A574D9B1C0DF24F012520 | |||
| 2188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF13473d.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
32
DNS requests
23
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3656 | saBSI.exe | 2.18.233.229:443 | sadownload.mcafee.com | Akamai International B.V. | — | whitelisted |
2204 | chrome.exe | 89.248.171.137:443 | gamefabrique.com | Quasi Networks LTD. | SC | suspicious |
2204 | chrome.exe | 142.250.185.173:443 | accounts.google.com | Google Inc. | US | suspicious |
2204 | chrome.exe | 104.18.10.207:443 | stackpath.bootstrapcdn.com | Cloudflare Inc | US | suspicious |
2204 | chrome.exe | 185.60.216.19:443 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
2204 | chrome.exe | 172.217.23.234:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
2204 | chrome.exe | 23.210.248.44:443 | s7.addthis.com | Akamai International B.V. | NL | whitelisted |
2204 | chrome.exe | 142.250.185.238:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2204 | chrome.exe | 2.18.235.40:443 | z.moatads.com | Akamai International B.V. | — | whitelisted |
2204 | chrome.exe | 142.250.185.202:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
gamefabrique.com |
| whitelisted |
accounts.google.com |
| shared |
stackpath.bootstrapcdn.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
connect.facebook.net |
| whitelisted |
s7.addthis.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
z.moatads.com |
| whitelisted |
v1.addthisedge.com |
| shared |
m.addthis.com |
| shared |
Threats
Process | Message |
|---|---|
saBSI.exe | NotComDllGetInterface: DLL not found in install location, looking in current directory |
saBSI.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\is-FDO2J.tmp\prod0_extract\saBSI.exe loading C:\Users\admin\AppData\Local\Temp\is-FDO2J.tmp\prod0_extract\mfeaaca.dll, WinVerifyTrust failed with 80092003
|
saBSI.exe | NotComDllGetInterface: DLL not found in install location, looking in current directory |
saBSI.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\is-FDO2J.tmp\prod0_extract\saBSI.exe loading C:\Users\admin\AppData\Local\Temp\is-FDO2J.tmp\prod0_extract\mfeaaca.dll, WinVerifyTrust failed with 80092003
|
saBSI.exe | NotComDllGetInterface: DLL not found in install location, looking in current directory |
saBSI.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\is-FDO2J.tmp\prod0_extract\saBSI.exe loading C:\Users\admin\AppData\Local\Temp\is-FDO2J.tmp\prod0_extract\mfeaaca.dll, WinVerifyTrust failed with 80092003
|