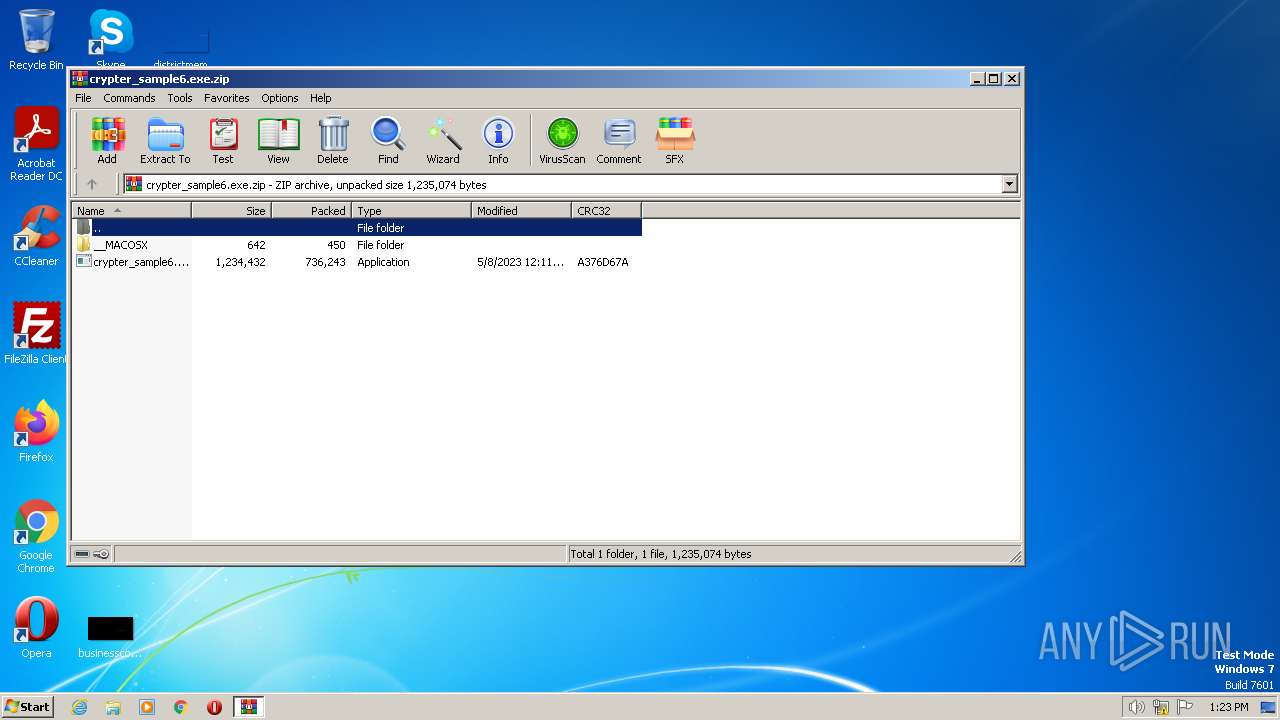
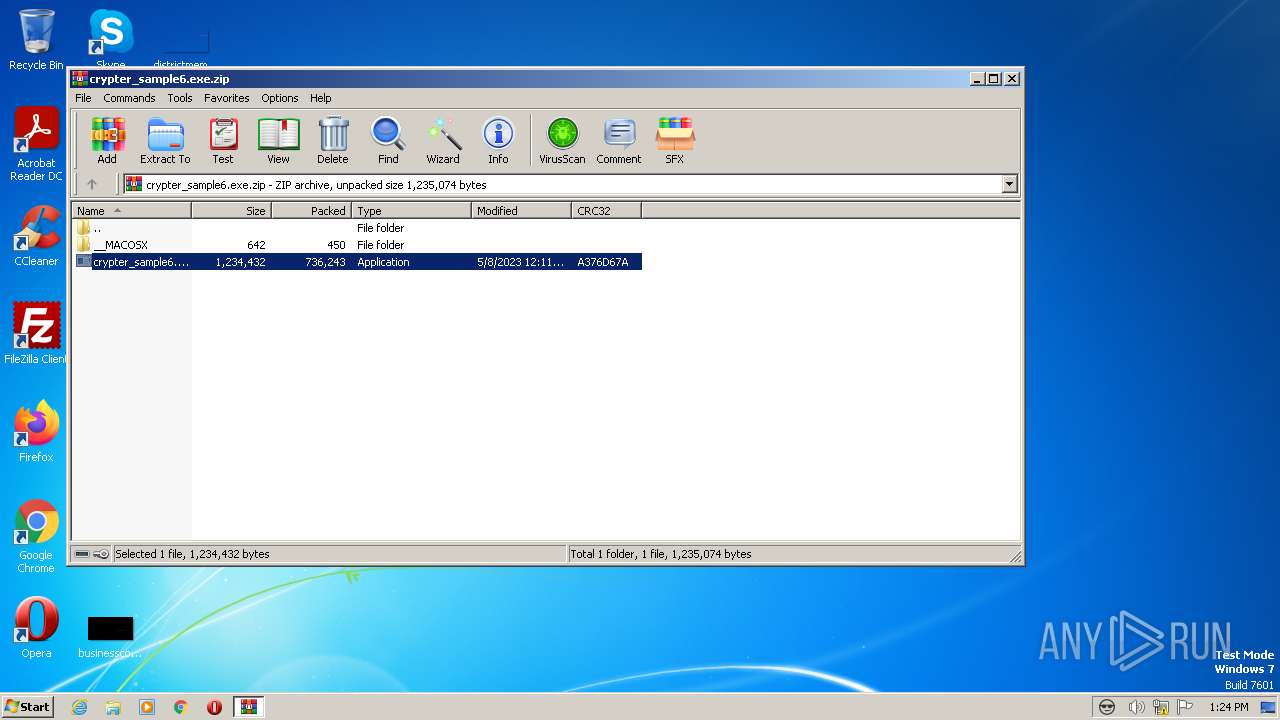
| File name: | crypter_sample6.exe.zip |
| Full analysis: | https://app.any.run/tasks/97f89886-fc28-4c2e-baff-5bb8c593a9bf |
| Verdict: | Malicious activity |
| Analysis date: | May 08, 2023, 12:23:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 96A11F4C51758F1C5E7A31127263A743 |
| SHA1: | E9990FE2B6327569CFEAD89552C41975807CF7B2 |
| SHA256: | B813A491AE178FB68C1449B056010D551A3204F22C6674344B14F21BBD14DE6C |
| SSDEEP: | 12288:r2WsvWhb9UmlTWQbT5n130o1aLHxQtUnfAobGavdcxcyrl3P/gKTg3TezySQ:z+WhhUmWsTl1J1azKtUnfA0jSX3P/pi3 |
MALICIOUS
Actions looks like stealing of personal data
- crypter_sample6.exe (PID: 3660)
SUSPICIOUS
No suspicious indicators.INFO
The process checks LSA protection
- explorer.exe (PID: 3468)
Checks supported languages
- crypter_sample6.exe (PID: 3660)
Reads mouse settings
- crypter_sample6.exe (PID: 3660)
Create files in a temporary directory
- crypter_sample6.exe (PID: 3660)
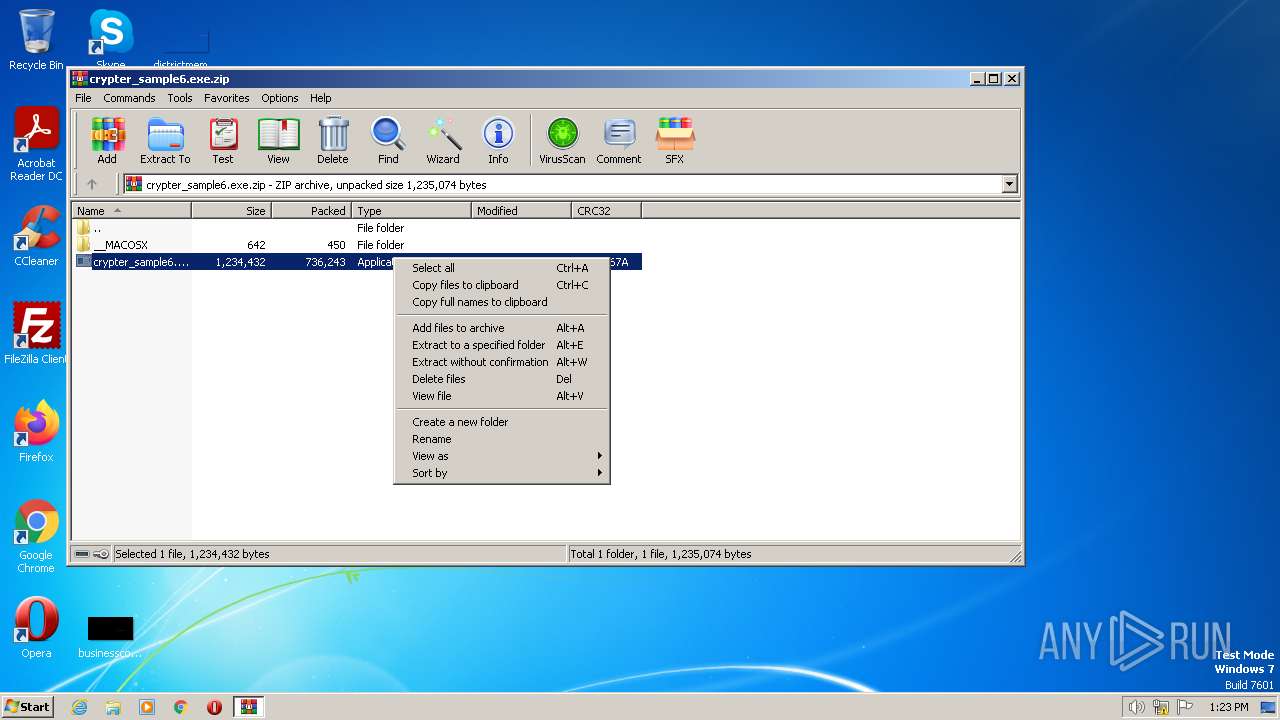
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3308)
Manual execution by a user
- explorer.exe (PID: 3468)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
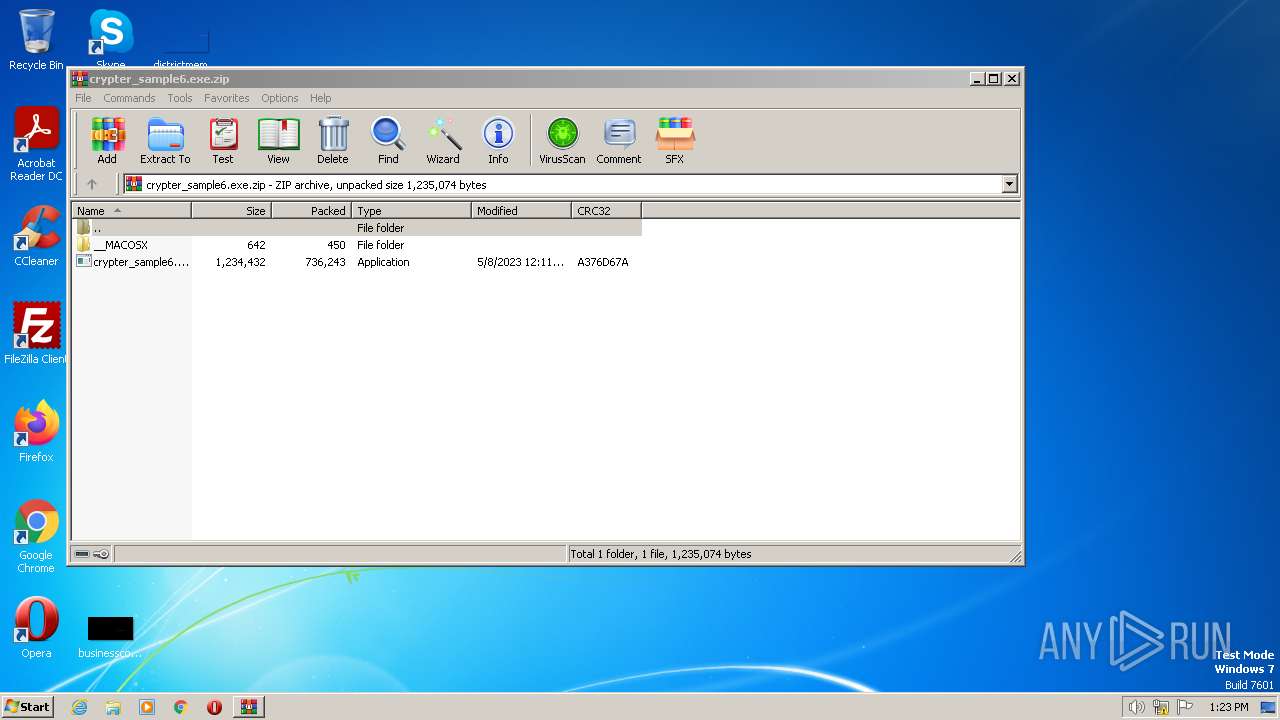
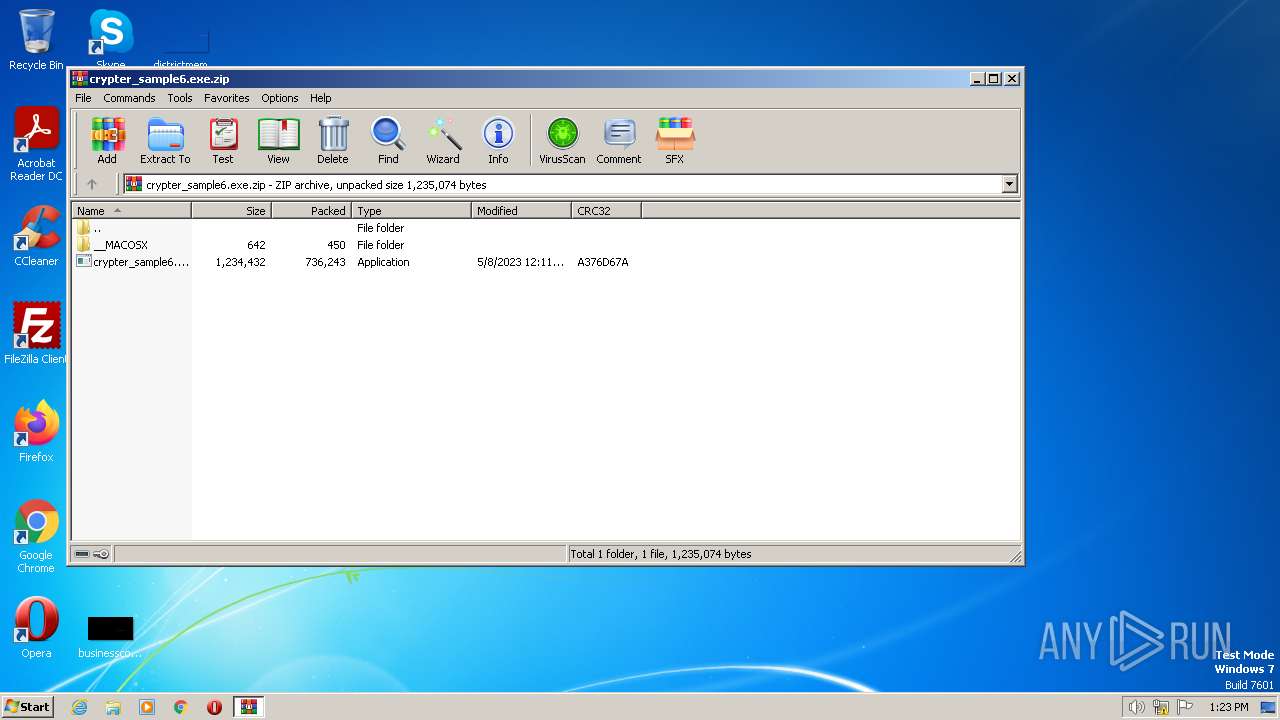
| ZipFileName: | crypter_sample6.exe |
|---|---|
| ZipUncompressedSize: | 1234432 |
| ZipCompressedSize: | - |
| ZipCRC: | 0x00000000 |
| ZipModifyDate: | 2023:05:08 13:11:14 |
| ZipCompression: | Deflated |
| ZipBitFlag: | 0x0008 |
| ZipRequiredVersion: | 20 |
Total processes
39
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
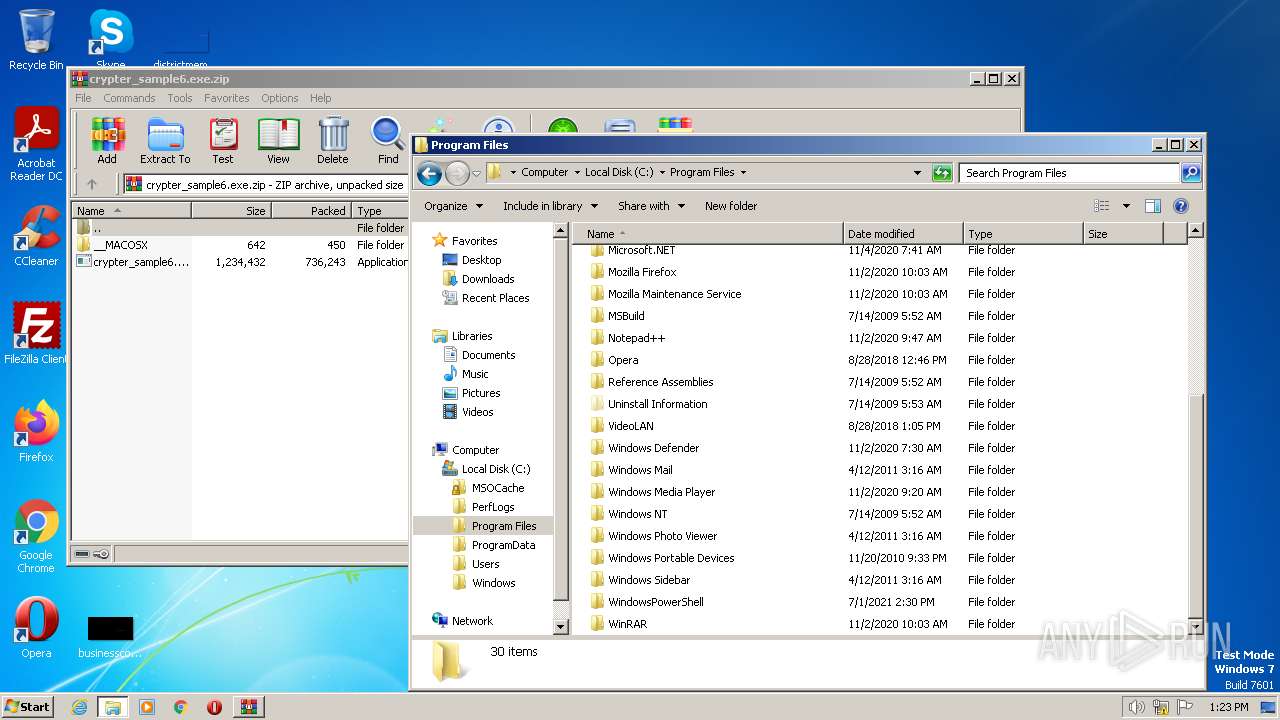
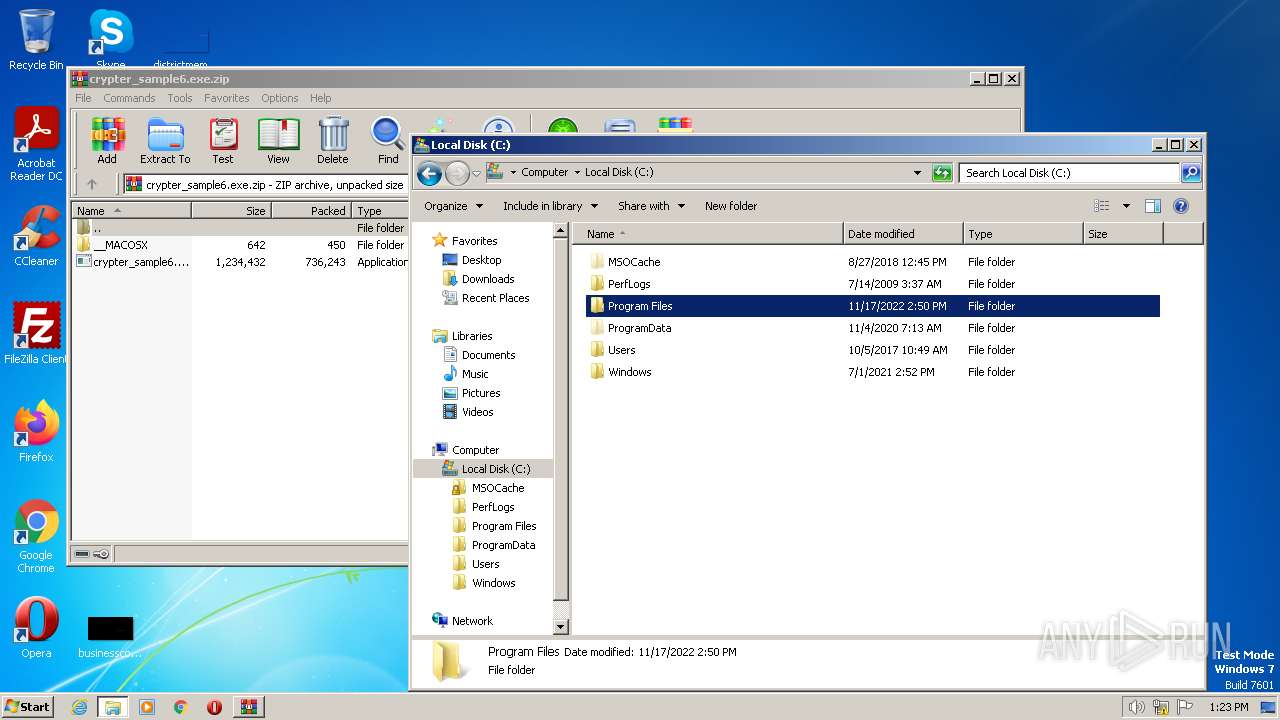
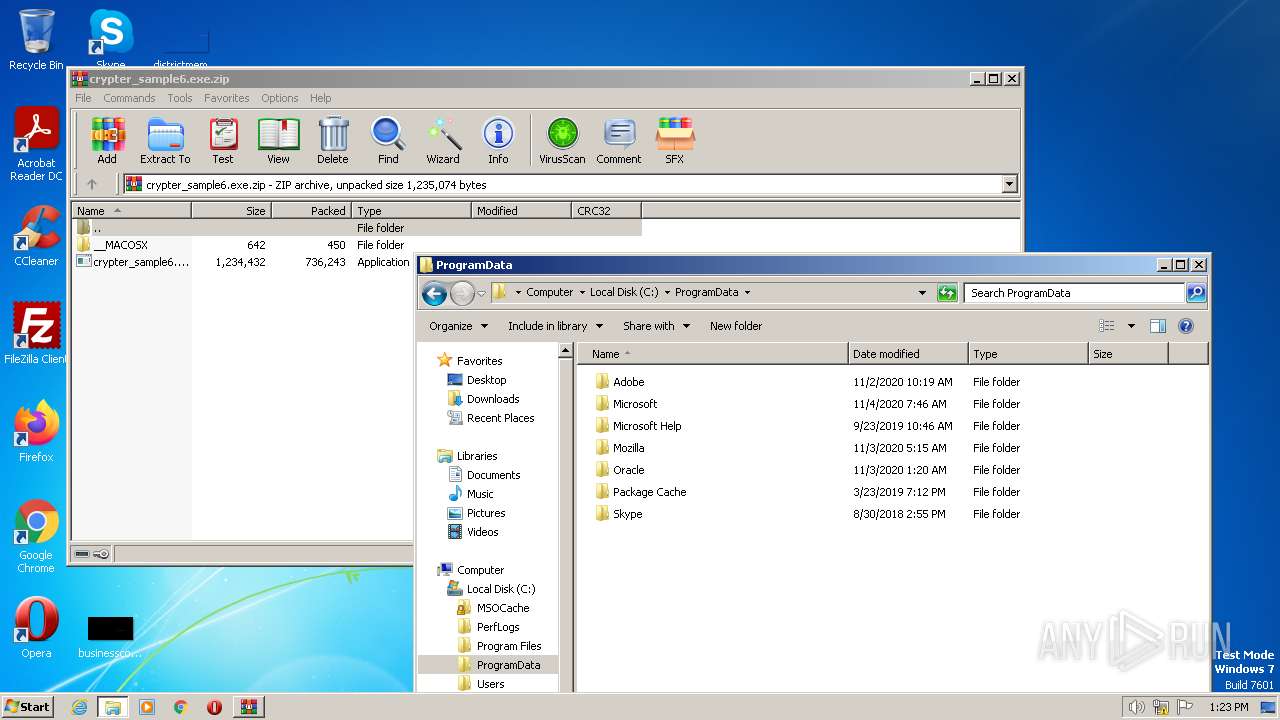
| 3308 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\crypter_sample6.exe.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3468 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
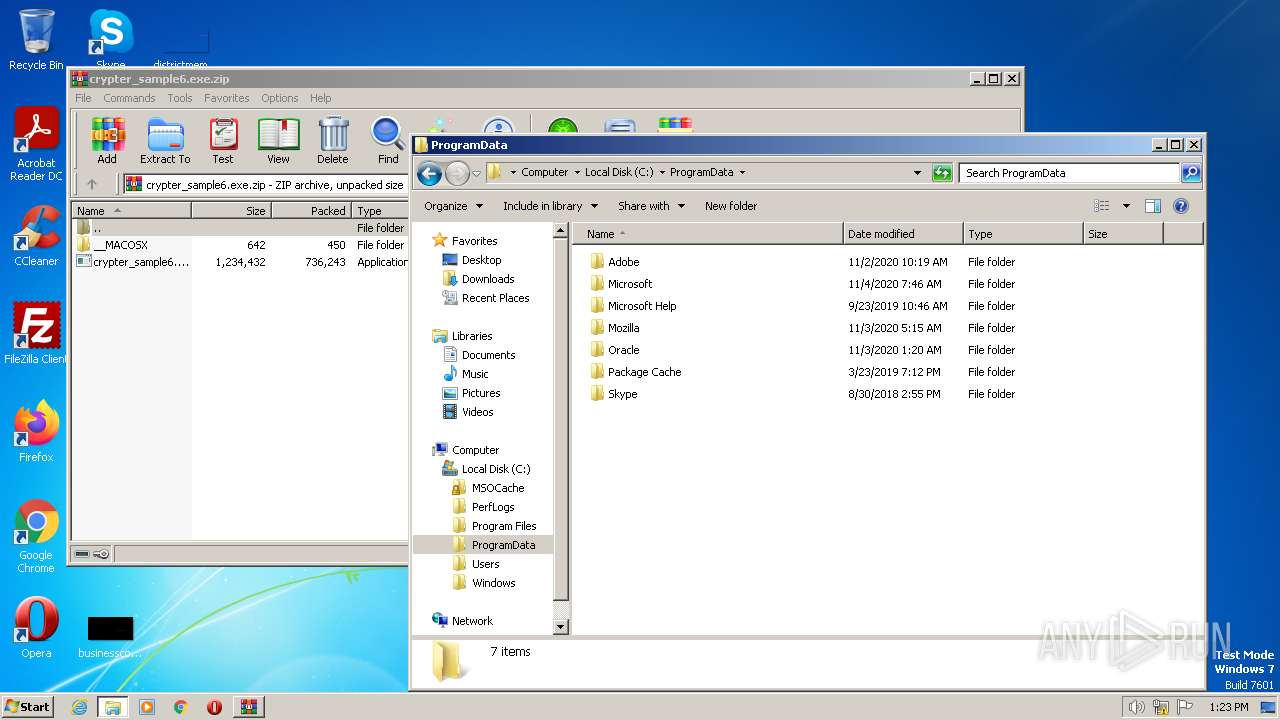
| 3660 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3308.12362\crypter_sample6.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3308.12362\crypter_sample6.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
2 060
Read events
2 028
Write events
32
Delete events
0
Modification events
| (PID) Process: | (3308) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3308) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (3308) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3308) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3308) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3308) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3308) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3308) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3308) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3308) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
2
Suspicious files
2
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3660 | crypter_sample6.exe | C:\Users\admin\AppData\Local\Temp\aut4C96.tmp | image | |
MD5:B4AA50FE518BA842F1072B3390F601F0 | SHA256:066EA7CB7A50B41A746C407D025EEA393E63121B3F48E5E3F6399A77390DA364 | |||
| 3660 | crypter_sample6.exe | C:\Users\admin\AppData\Local\Temp\final.JPG | image | |
MD5:B4AA50FE518BA842F1072B3390F601F0 | SHA256:066EA7CB7A50B41A746C407D025EEA393E63121B3F48E5E3F6399A77390DA364 | |||
| 3308 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3308.12362\crypter_sample6.exe | executable | |
MD5:AC01A77B62FF09DB10E03E42980C1132 | SHA256:7A454F296626A081C5FF88616B7480433D75C43FEE7E003A2028B61D433C018D | |||
| 3308 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3308.12362\__MACOSX\._crypter_sample6.exe | ad | |
MD5:095DB0E1FCFD839037A9228189E8D284 | SHA256:C95F10AFB3C42F7E2276DC09B53FA413B8F748CC44E1AA49944EE5DD0794CA9A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report