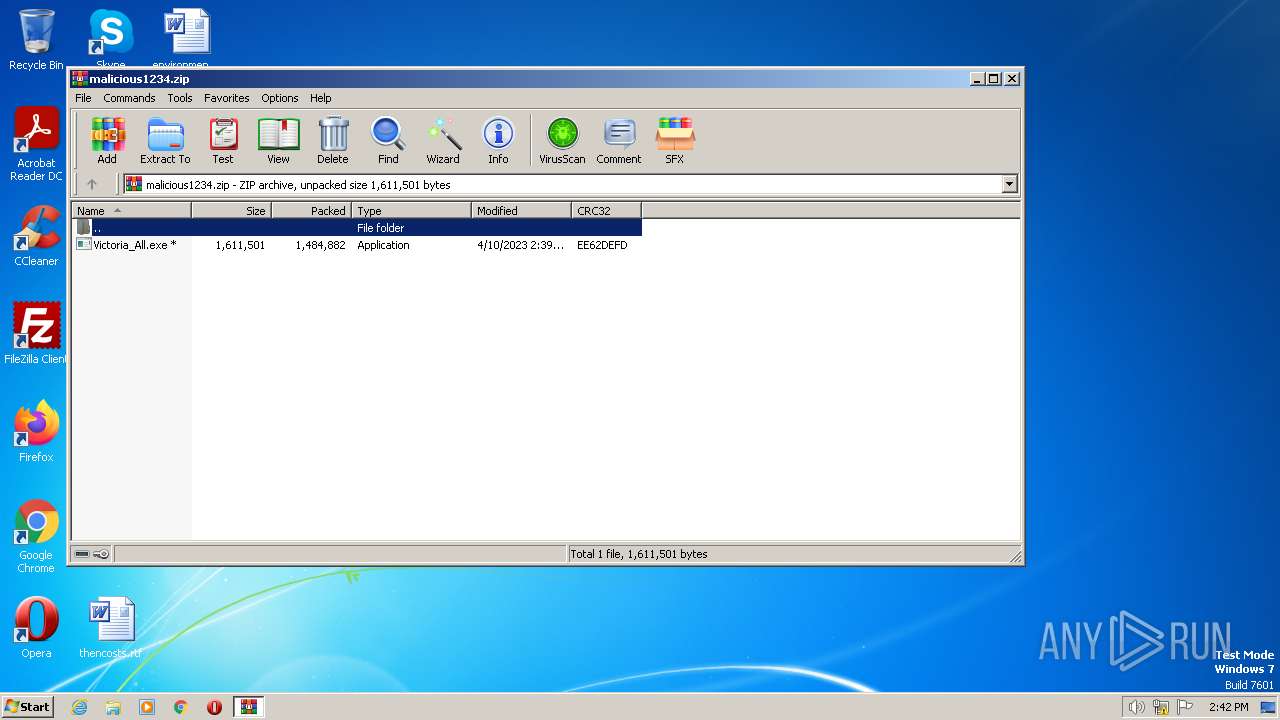
| File name: | malicious1234.zip |
| Full analysis: | https://app.any.run/tasks/b38f8323-e7e8-4a09-9b7b-05046df78cc0 |
| Verdict: | Malicious activity |
| Analysis date: | April 10, 2023, 13:41:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | F46B5C75A31F295B110CED0E561F9185 |
| SHA1: | 8139B1C135D59F57AE9990322E303F542DC9D78D |
| SHA256: | B80264DC7387DBA162AFE4315B369223A1DA760769051260CF9FB448B1CC650E |
| SSDEEP: | 24576:CWVw3wkr9BP+u2ISJ1d6MTfuWaHejEbkWxTcxkGFkP/Yj9mzOMEJ1fawSN0GY:3w3wkr9BPh2IK8wkG+HzrEJ4wSN0GY |
MALICIOUS
Drops the executable file immediately after the start
- Victoria_All.exe (PID: 3772)
- Victoria.exe (PID: 3156)
Application was dropped or rewritten from another process
- Victoria_All.exe (PID: 3772)
- Victoria.exe (PID: 2272)
- Victoria.exe (PID: 1588)
- Victoria.exe (PID: 3156)
- hidcon.exe (PID: 3852)
Creates a writable file the system directory
- Victoria.exe (PID: 3156)
SUSPICIOUS
Executable content was dropped or overwritten
- Victoria_All.exe (PID: 3772)
- Victoria.exe (PID: 3156)
Reads the Internet Settings
- Victoria_All.exe (PID: 3772)
- cmd.exe (PID: 2120)
Executing commands from a ".bat" file
- hidcon.exe (PID: 3852)
Starts CMD.EXE for commands execution
- hidcon.exe (PID: 3852)
Drops a system driver (possible attempt to evade defenses)
- Victoria.exe (PID: 3156)
- Victoria_All.exe (PID: 3772)
Drops a file with too old compile date
- Victoria.exe (PID: 3156)
- Victoria_All.exe (PID: 3772)
Creates files in the driver directory
- Victoria.exe (PID: 3156)
INFO
Drops the executable file immediately after the start
- WinRAR.exe (PID: 2808)
Checks supported languages
- Victoria_All.exe (PID: 3772)
- Victoria.exe (PID: 3156)
- hidcon.exe (PID: 3852)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2808)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 2808)
- Victoria.exe (PID: 3156)
- Victoria_All.exe (PID: 3772)
Reads the computer name
- Victoria_All.exe (PID: 3772)
- Victoria.exe (PID: 3156)
Create files in a temporary directory
- Victoria_All.exe (PID: 3772)
- Victoria.exe (PID: 3156)
The process checks LSA protection
- cmd.exe (PID: 2120)
- Victoria_All.exe (PID: 3772)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipFileName: | Victoria_All.exe |
|---|---|
| ZipUncompressedSize: | 1611501 |
| ZipCompressedSize: | 1484882 |
| ZipCRC: | 0xee62defd |
| ZipModifyDate: | 2023:04:10 13:39:22 |
| ZipCompression: | Deflated |
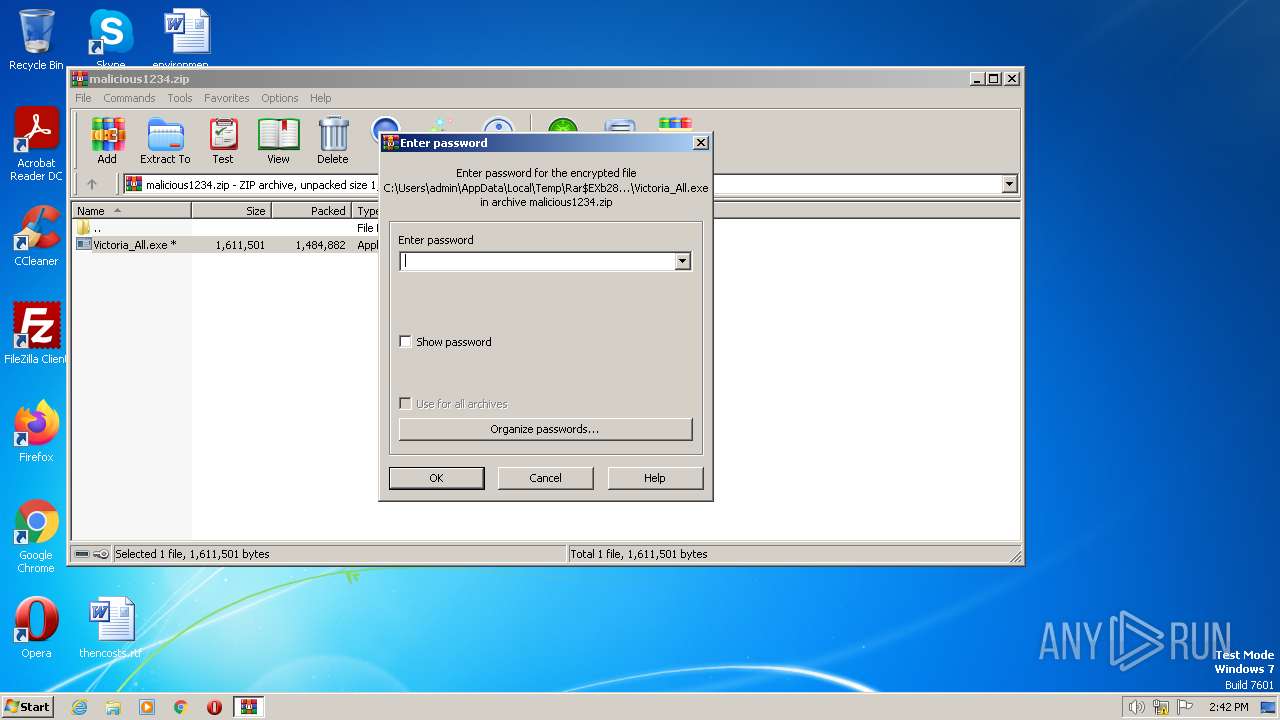
| ZipBitFlag: | 0x0001 |
| ZipRequiredVersion: | 20 |
Total processes
46
Monitored processes
7
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1588 | Victoria.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\Victoria.exe | — | cmd.exe | |||||||||||
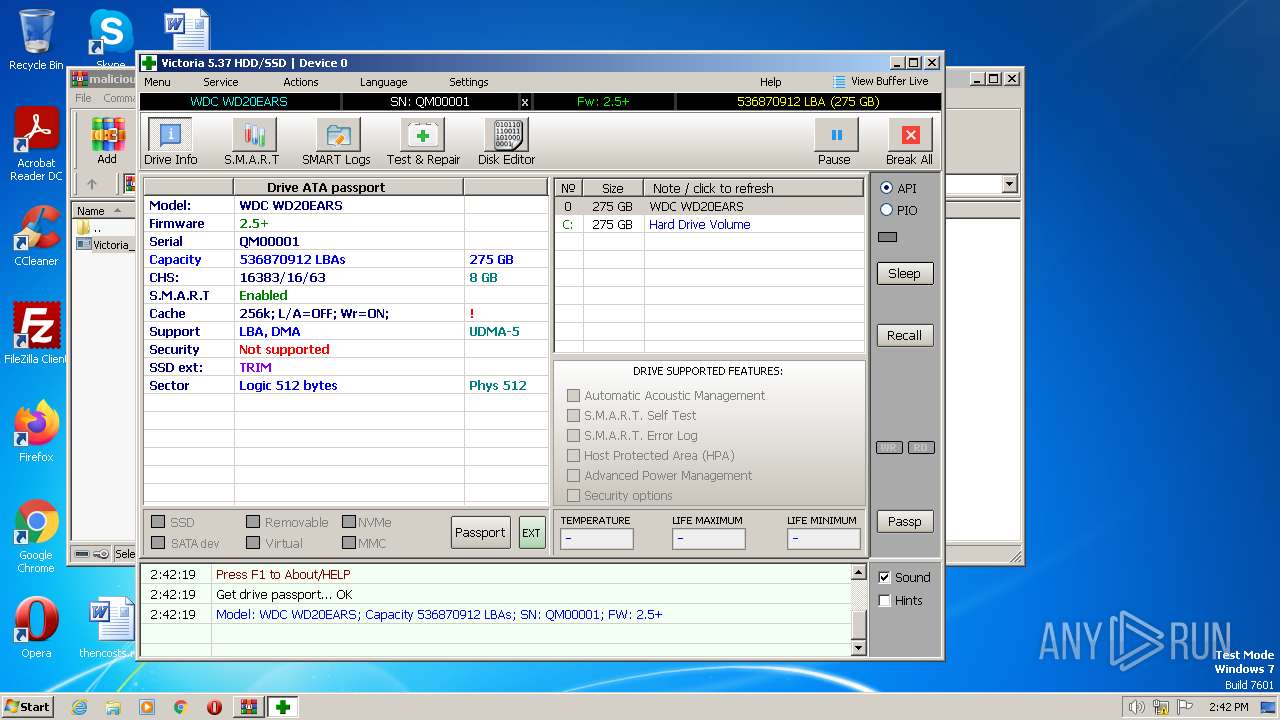
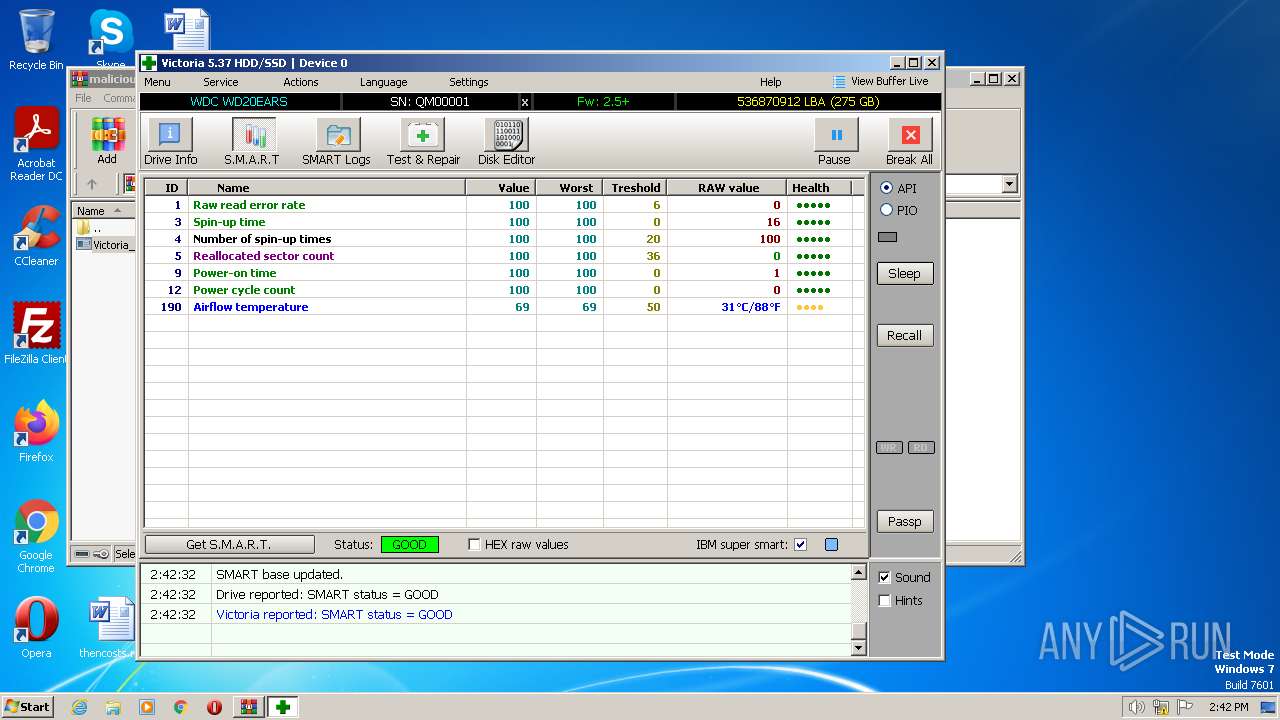
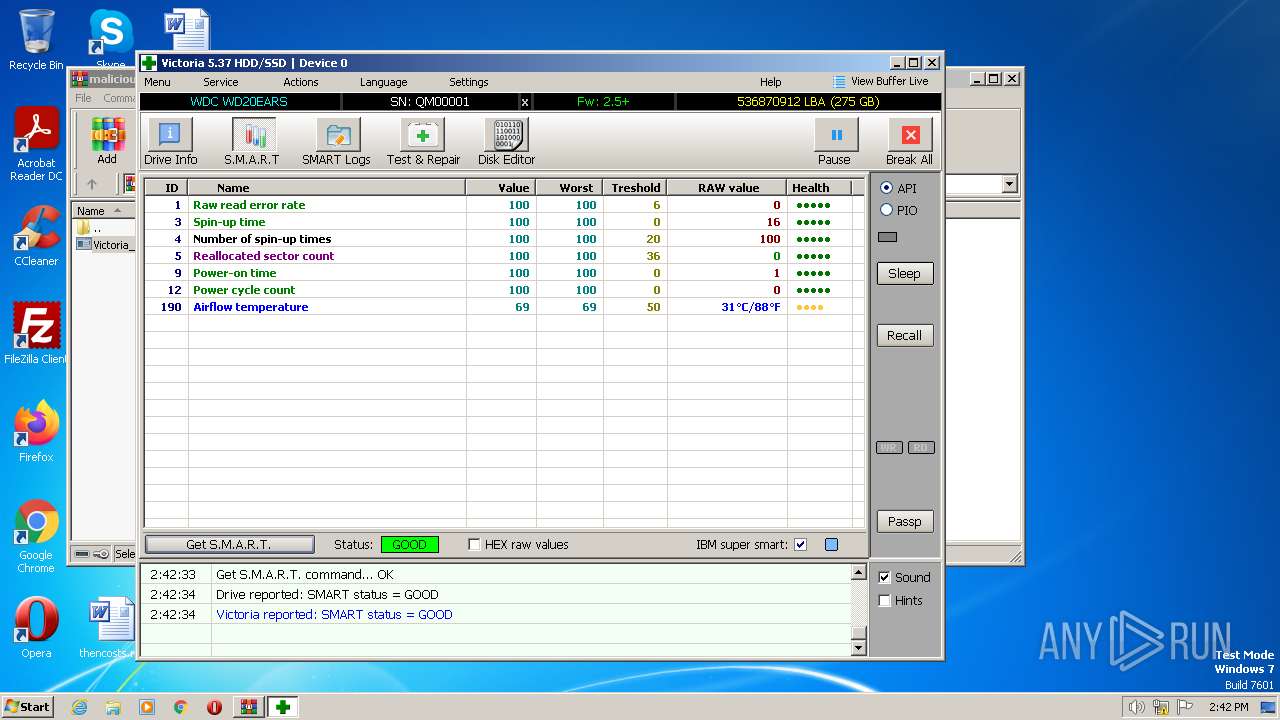
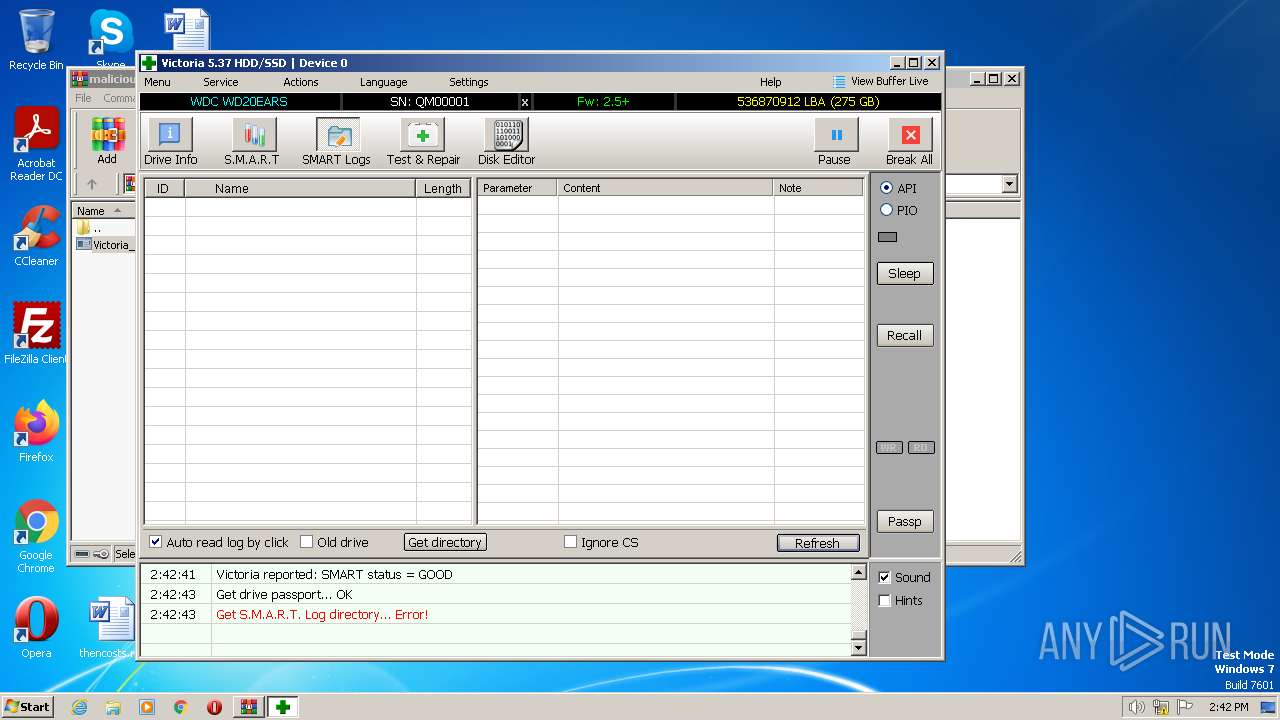
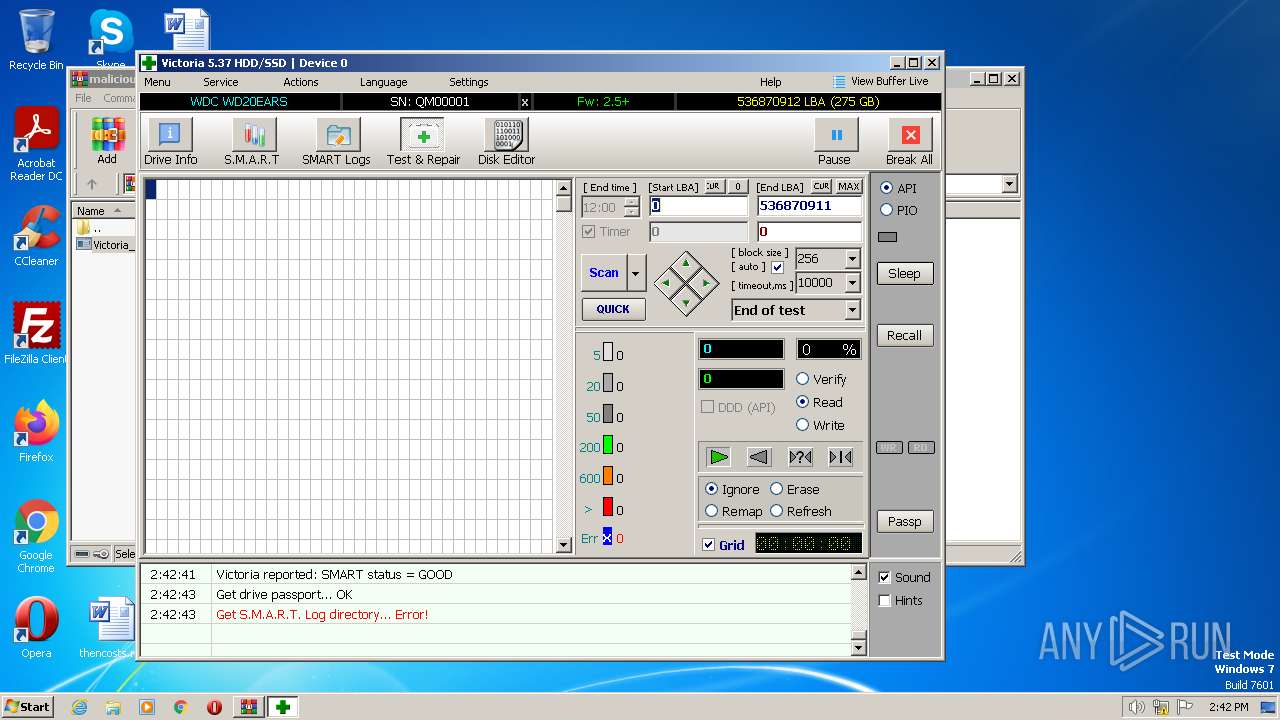
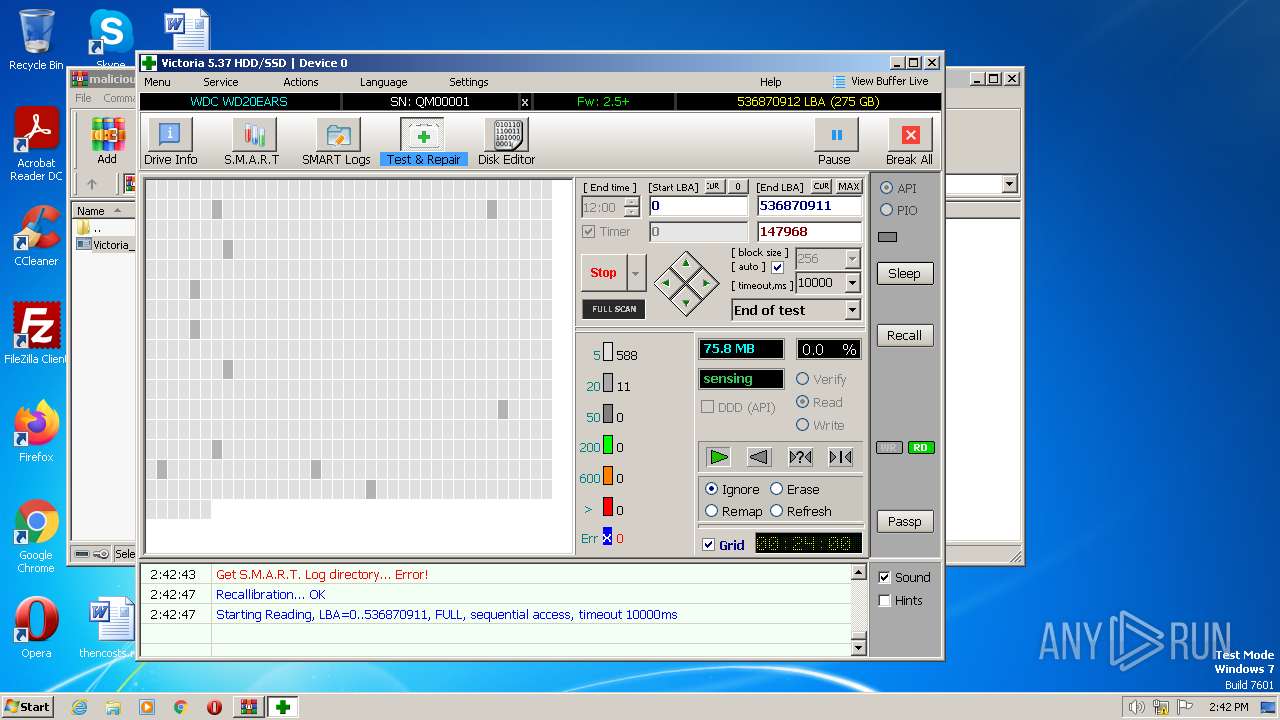
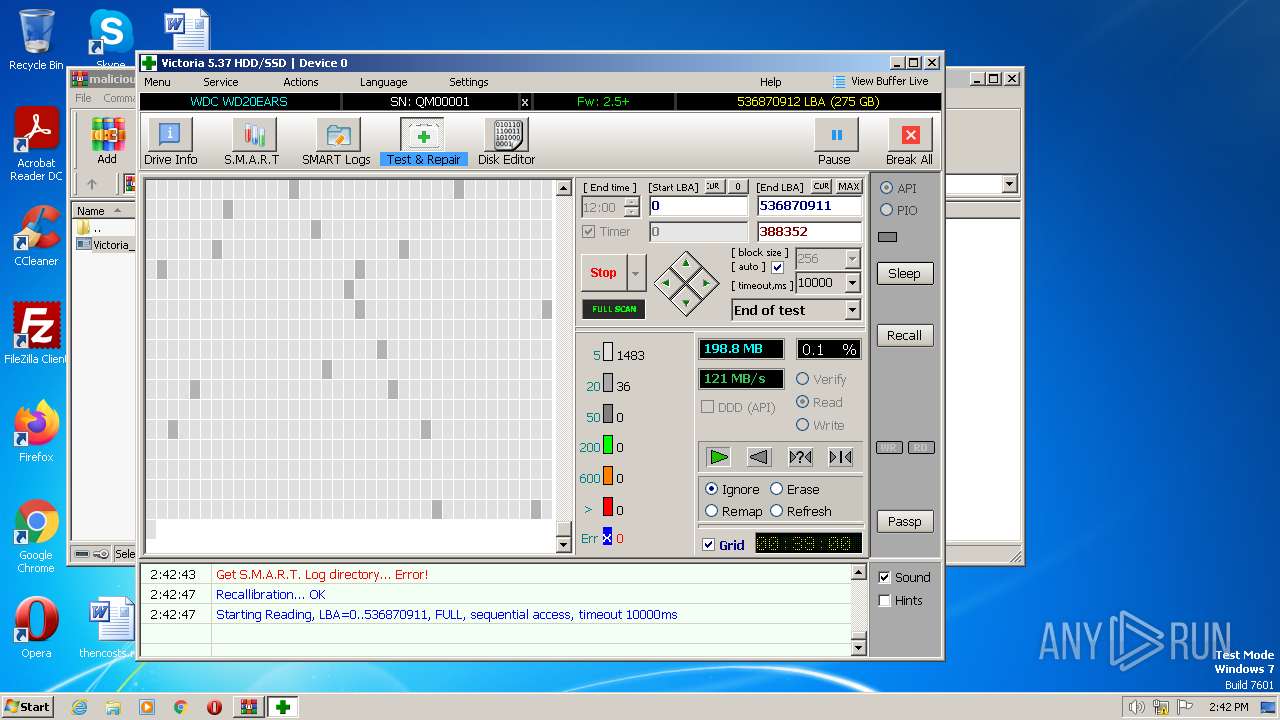
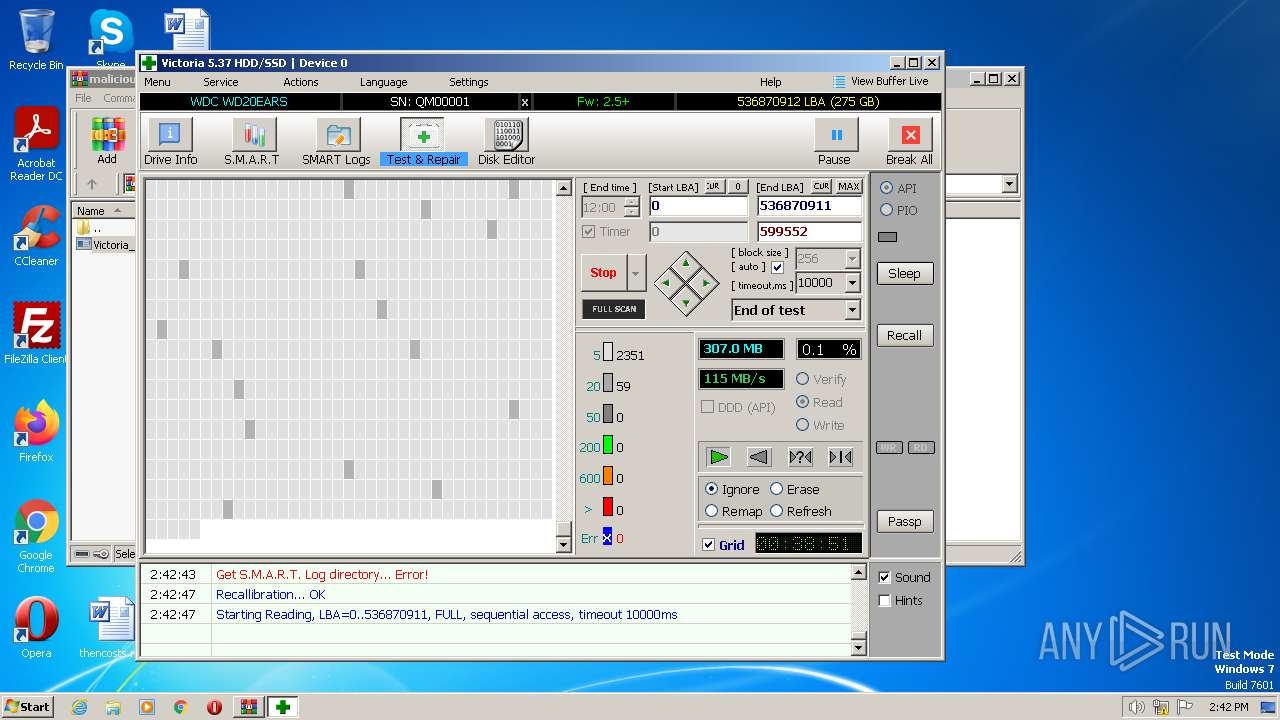
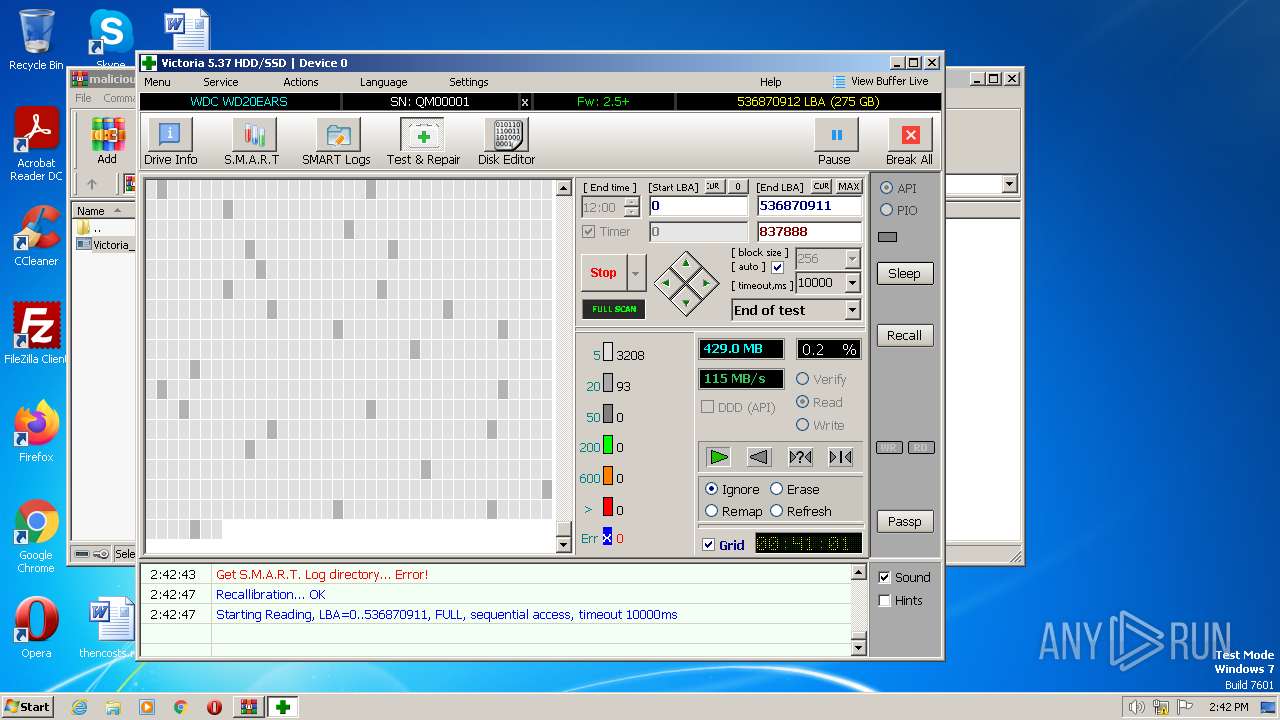
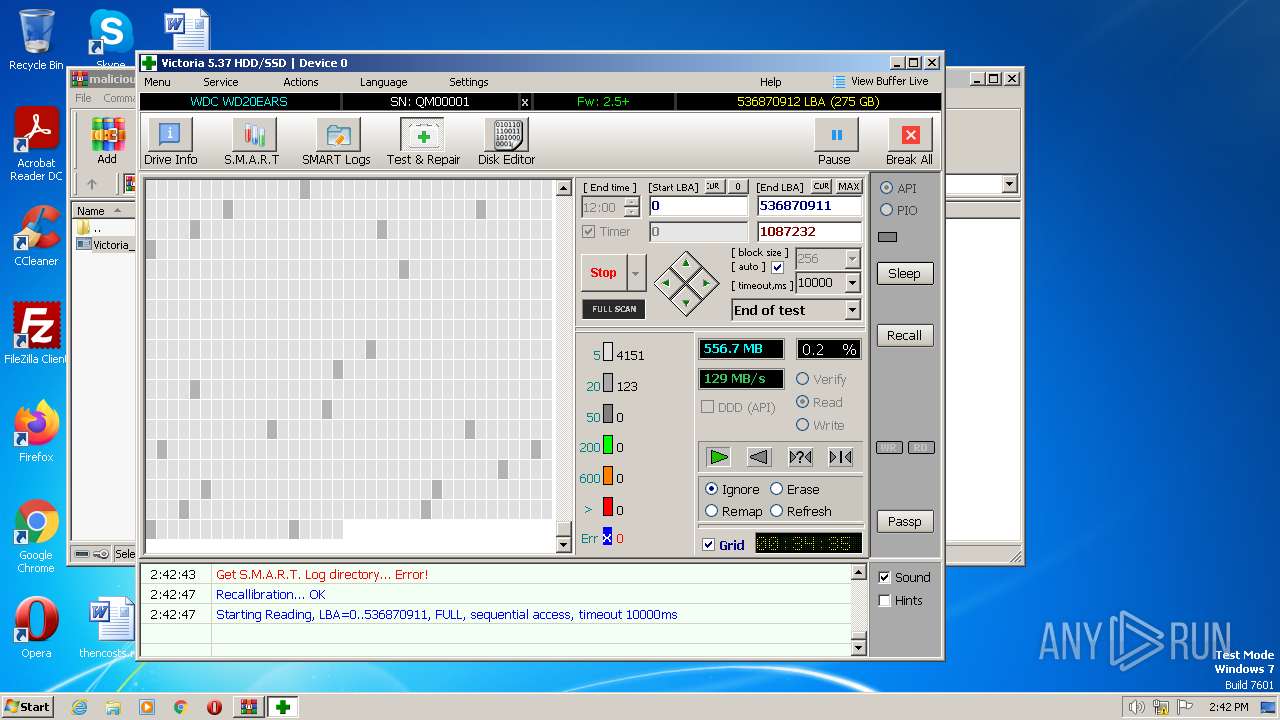
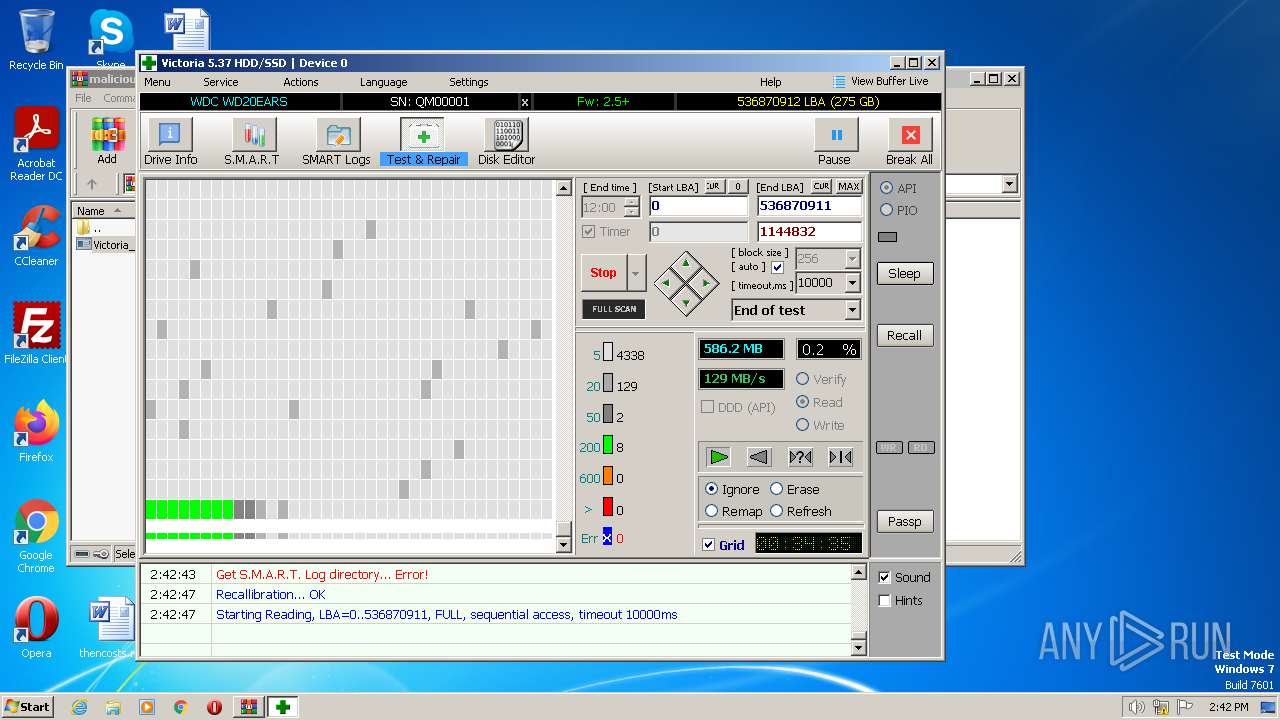
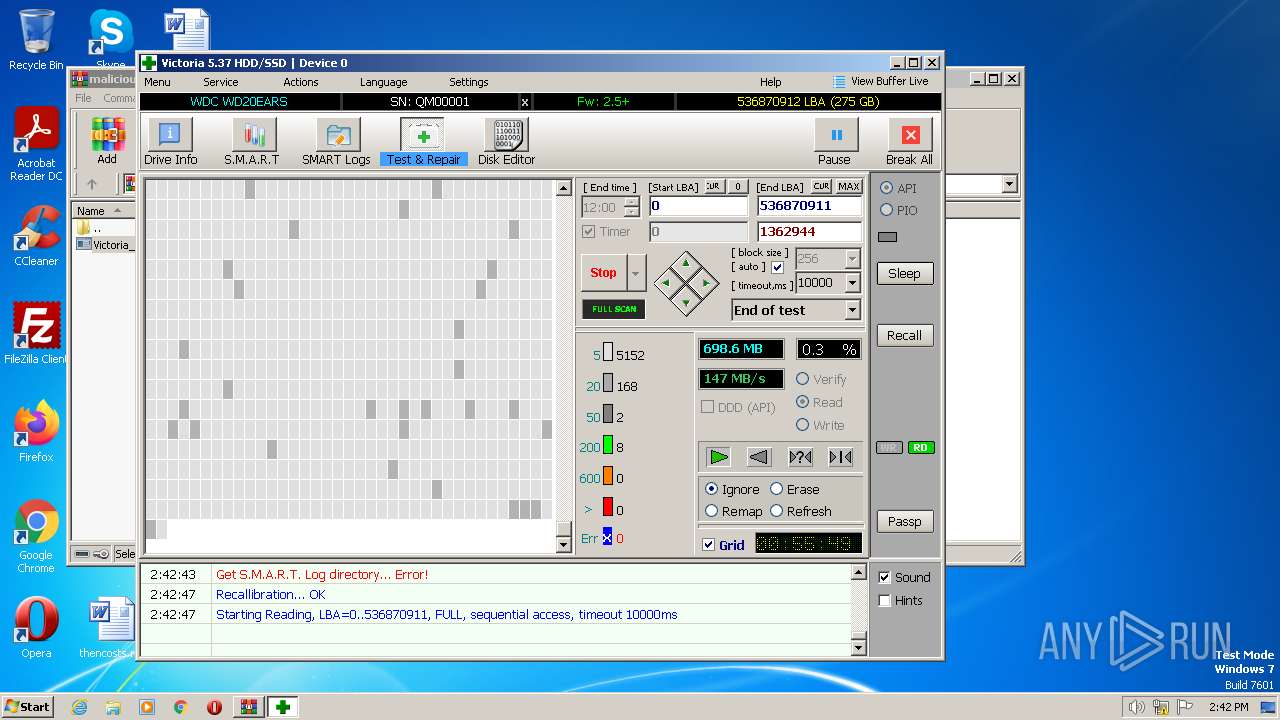
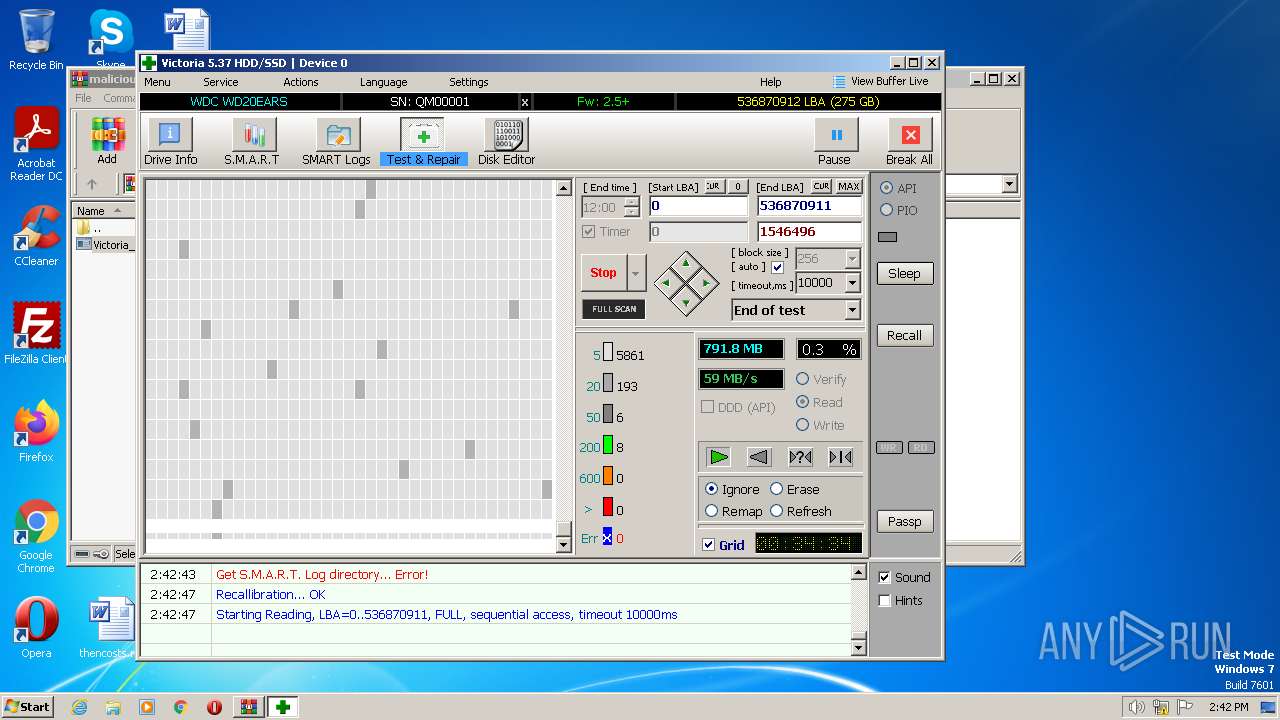
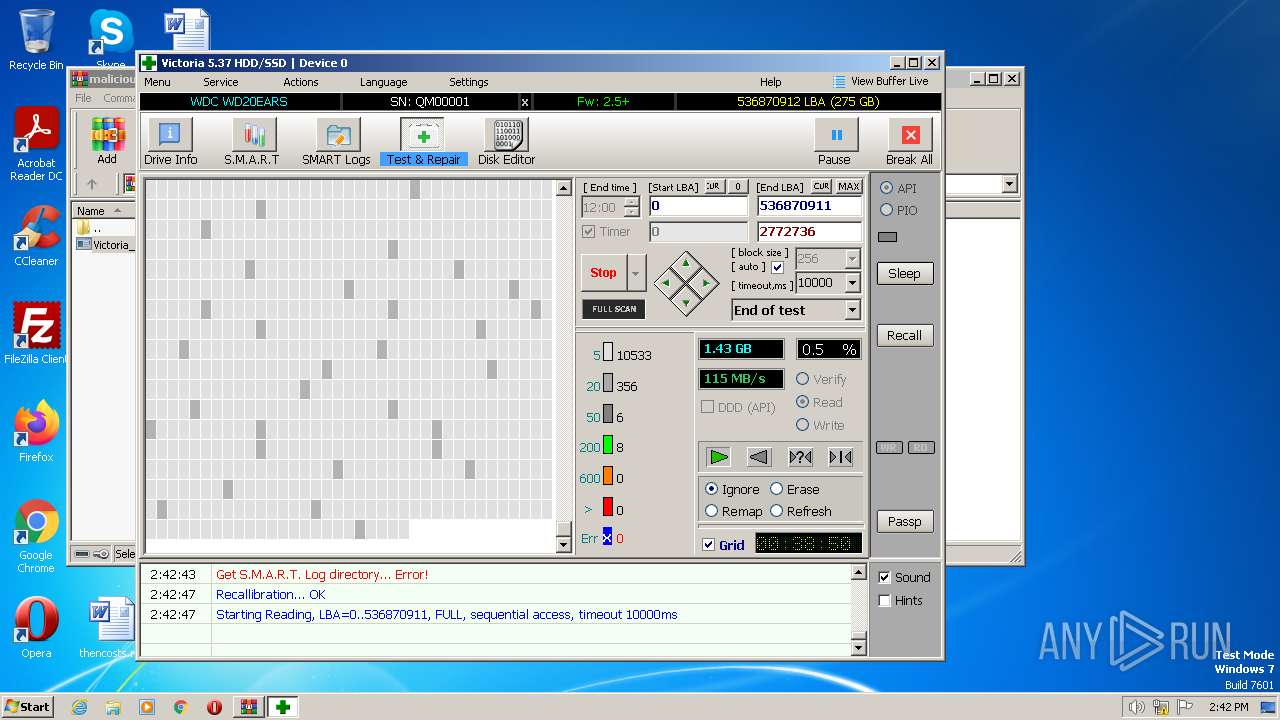
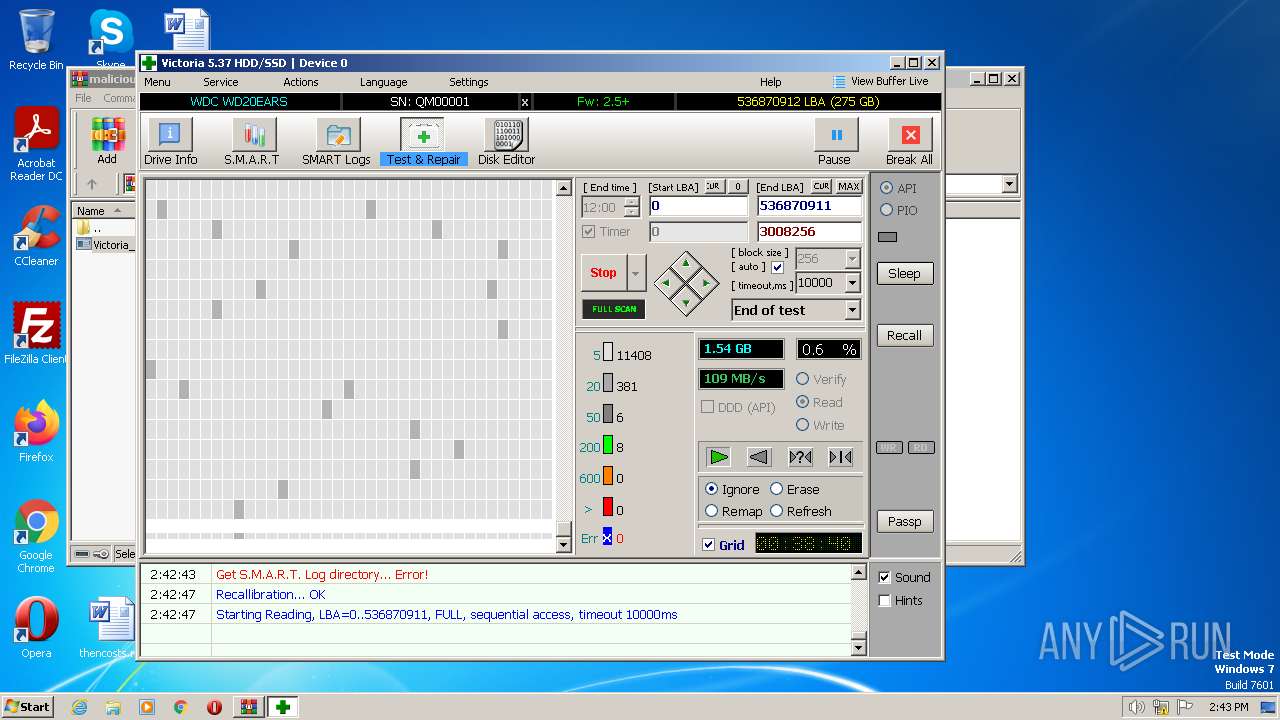
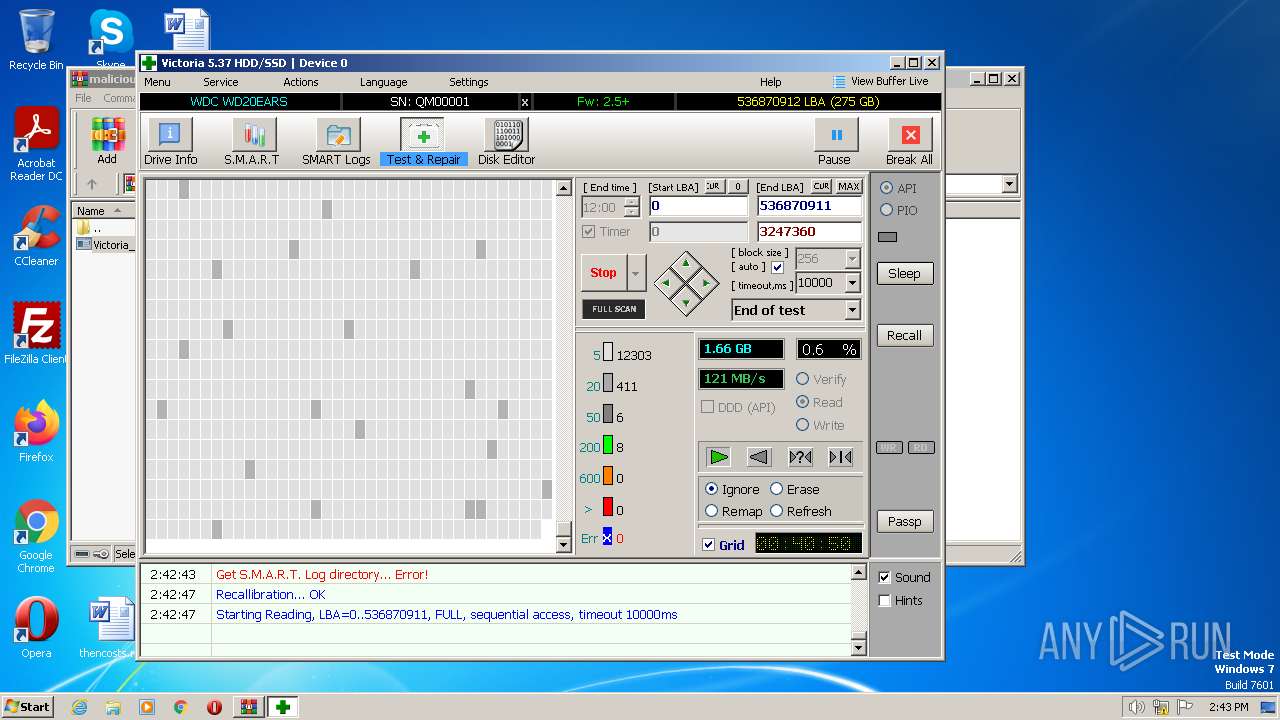
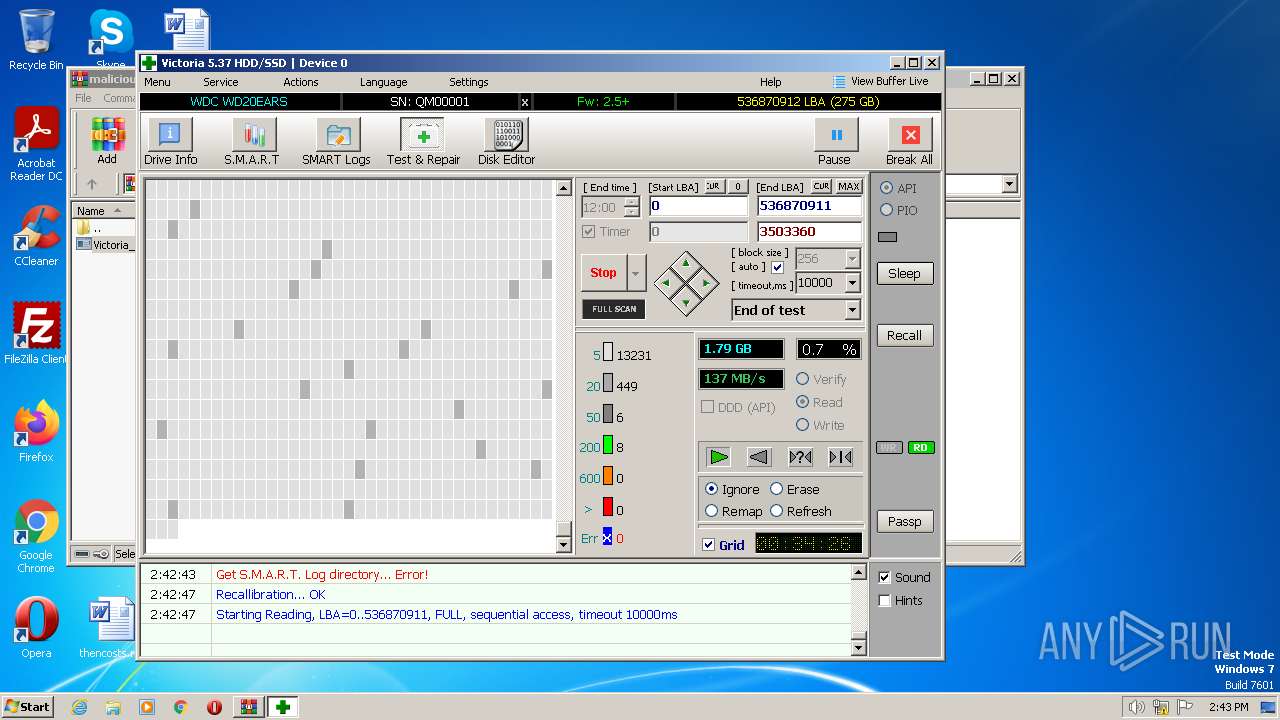
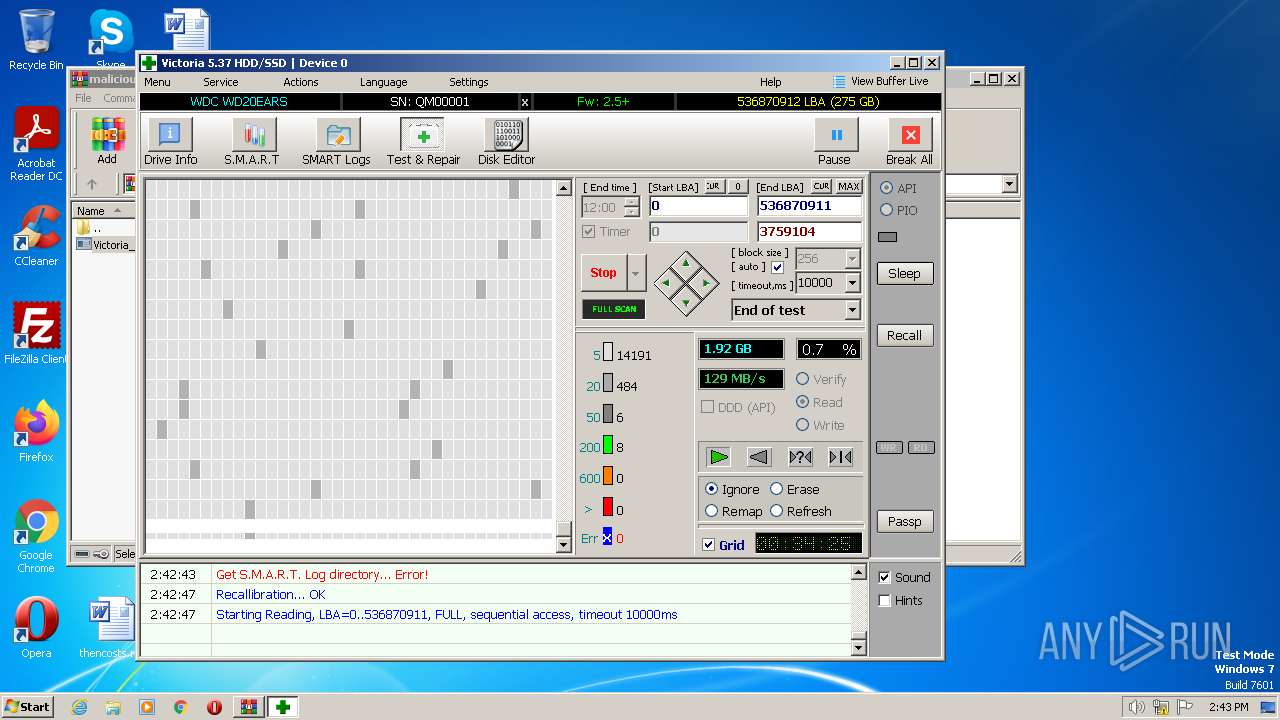
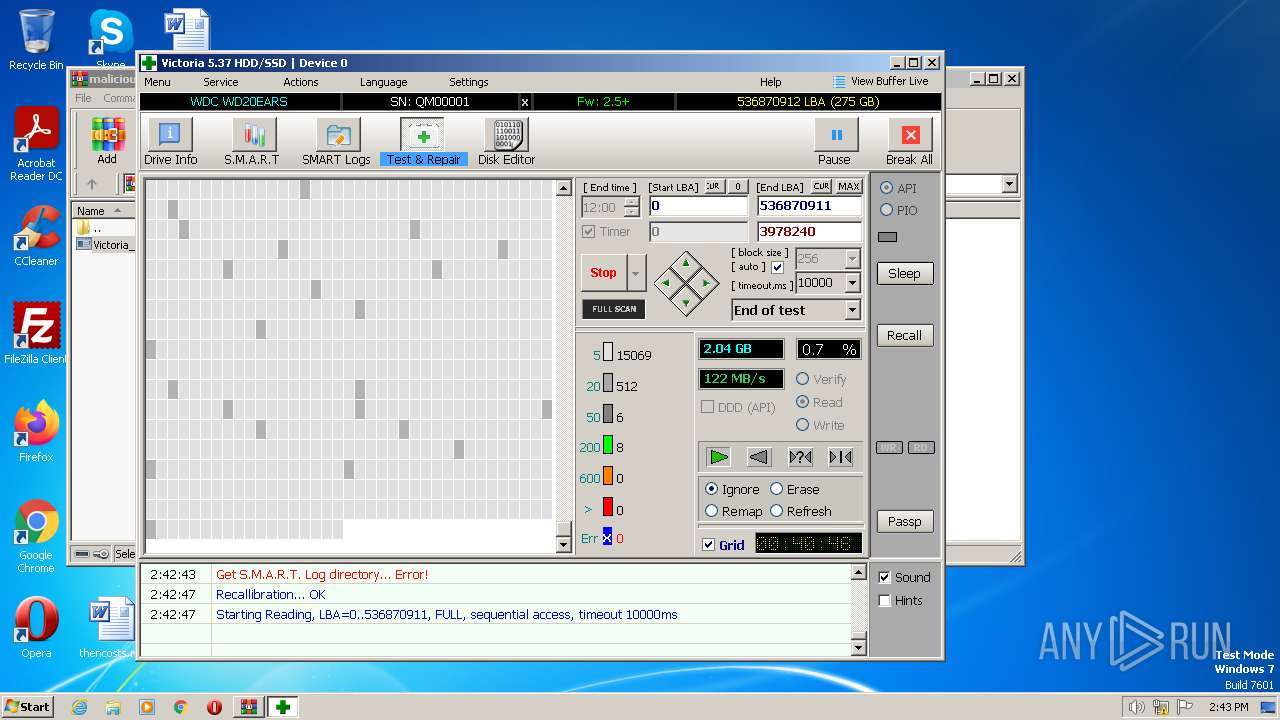
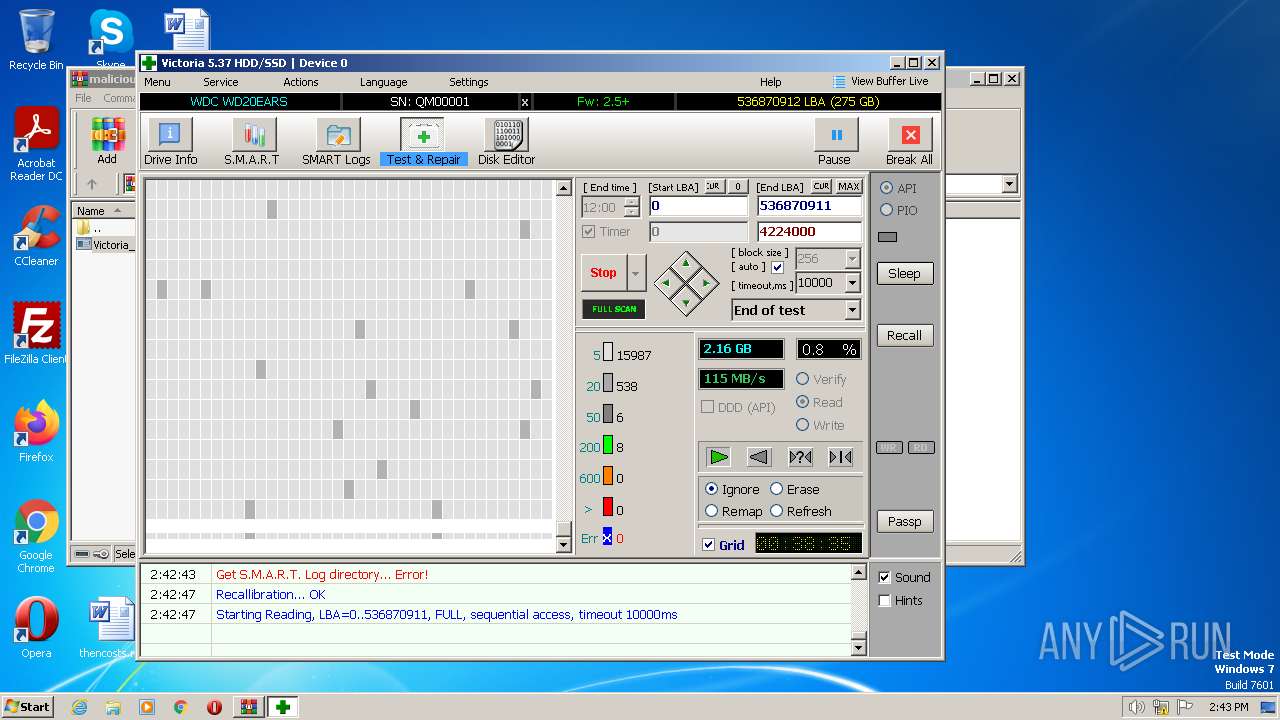
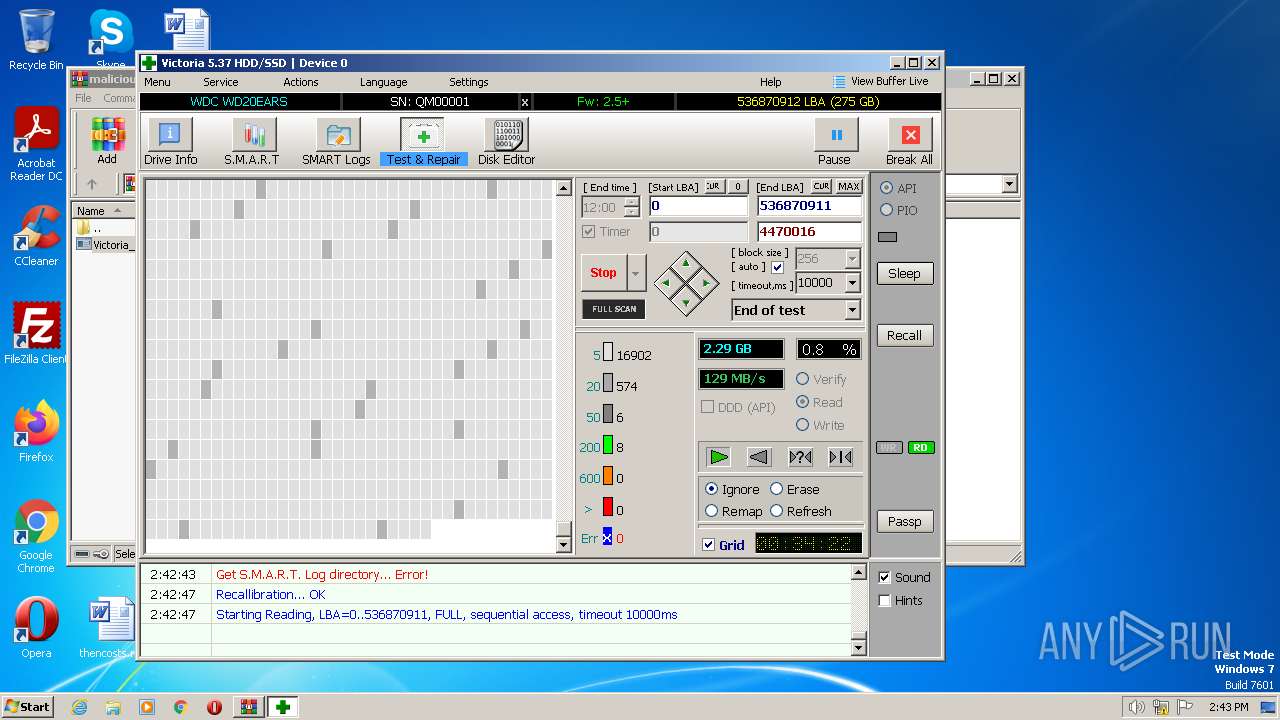
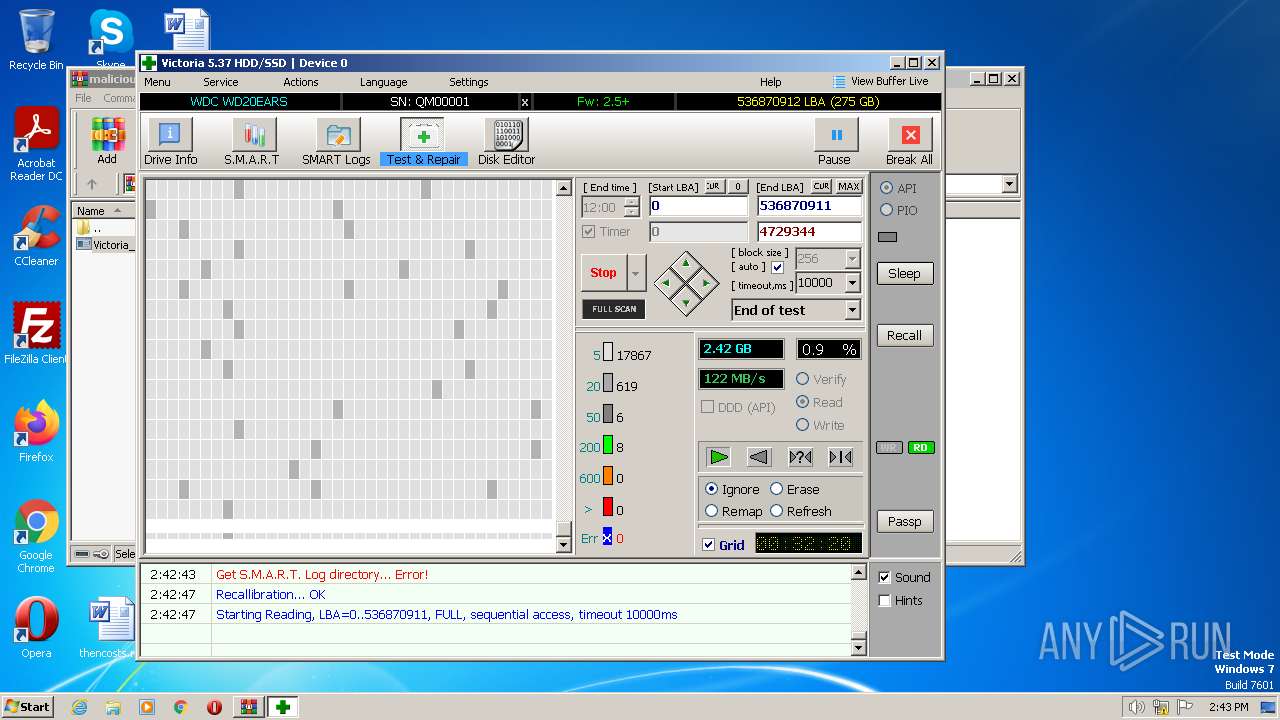
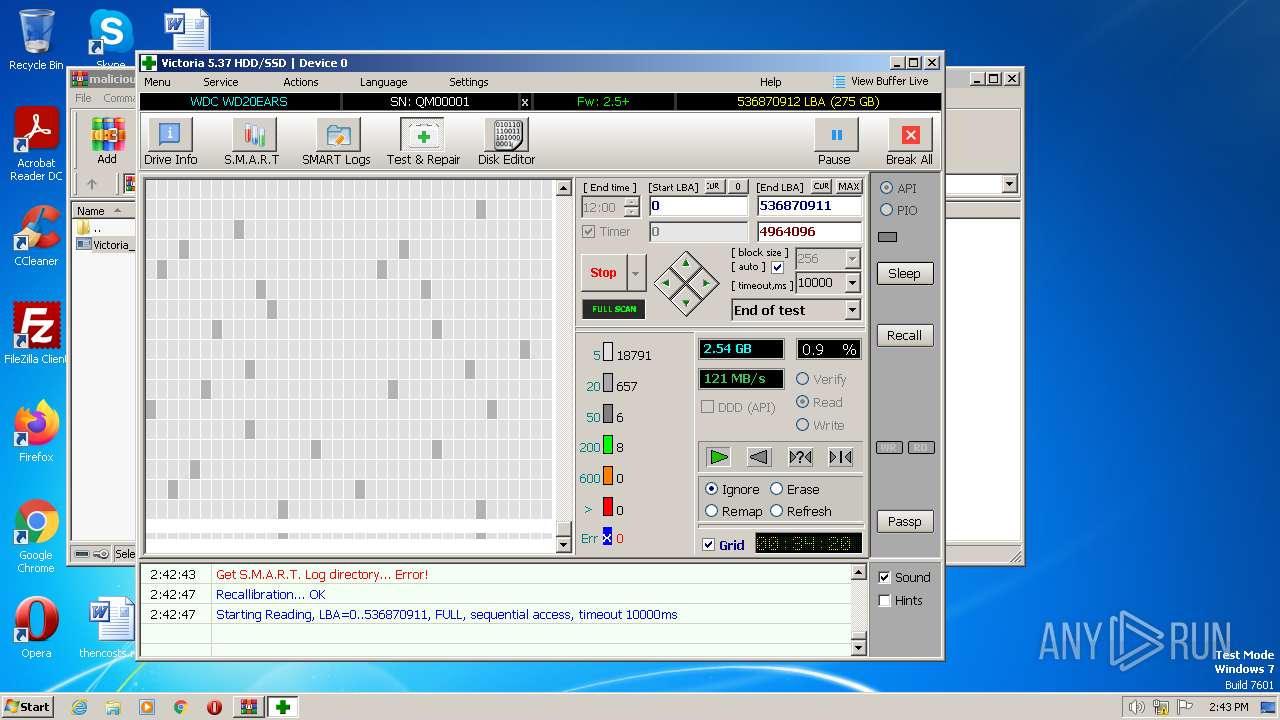
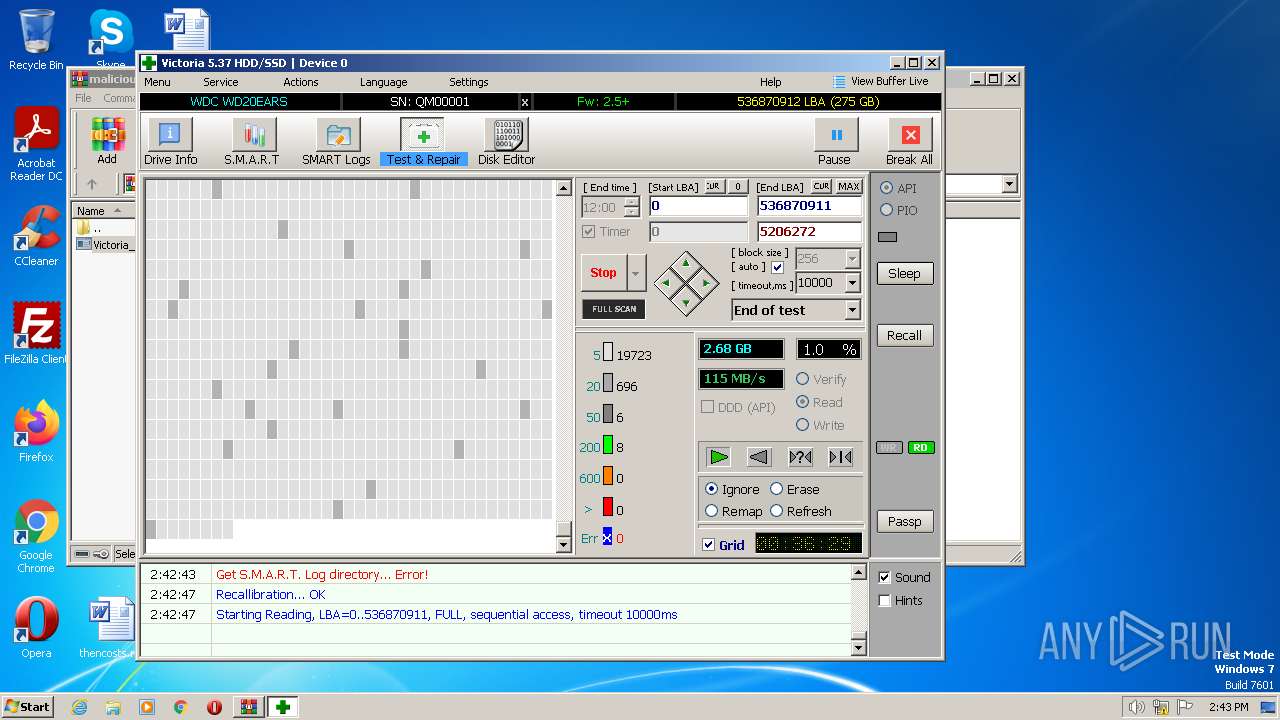
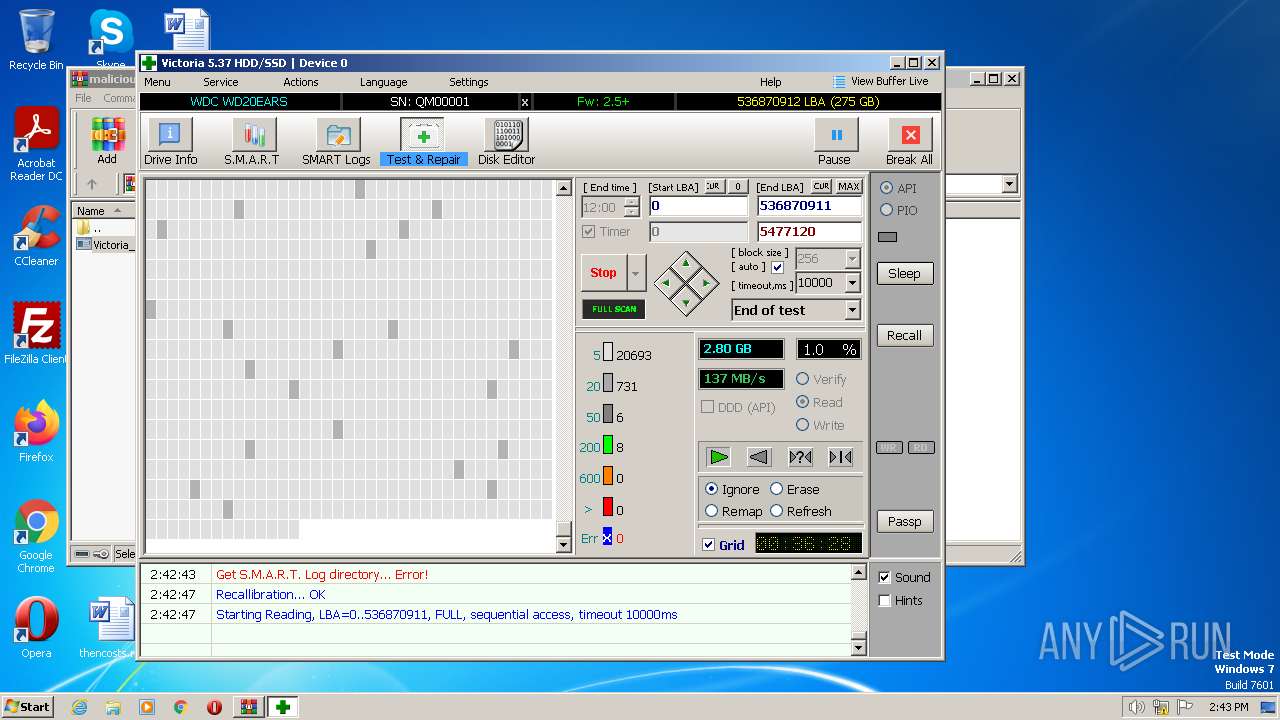
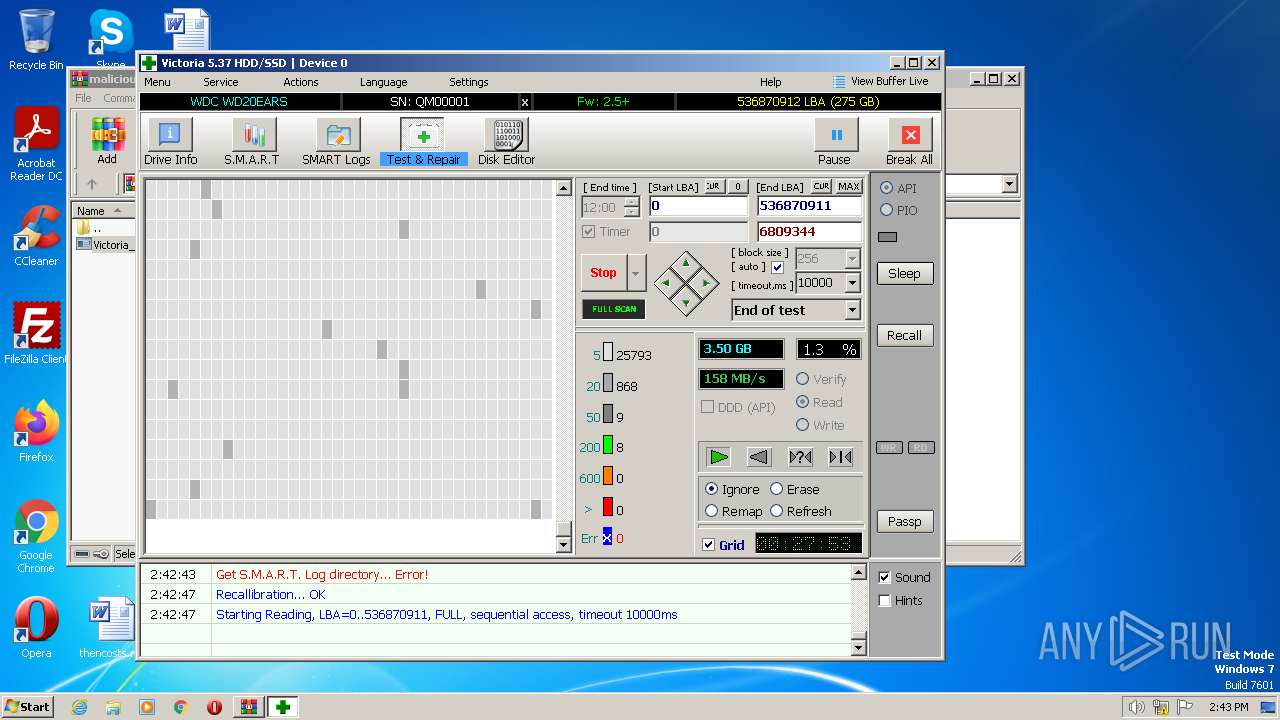
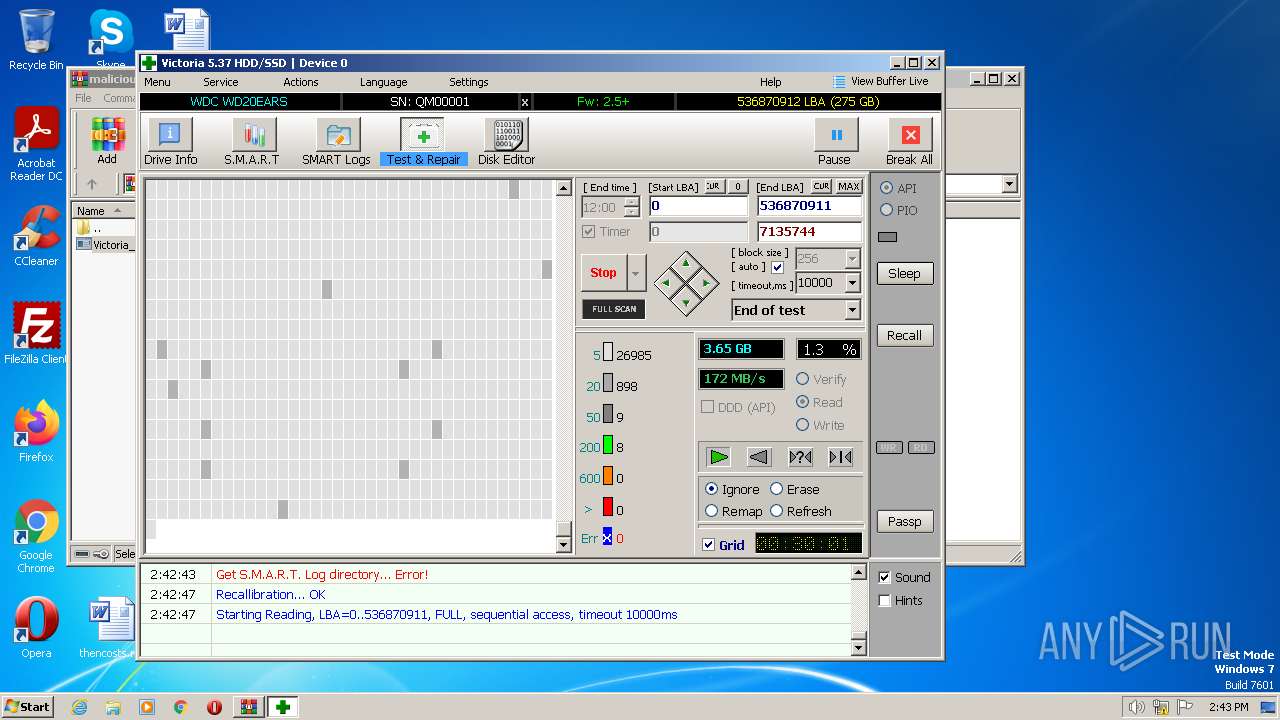
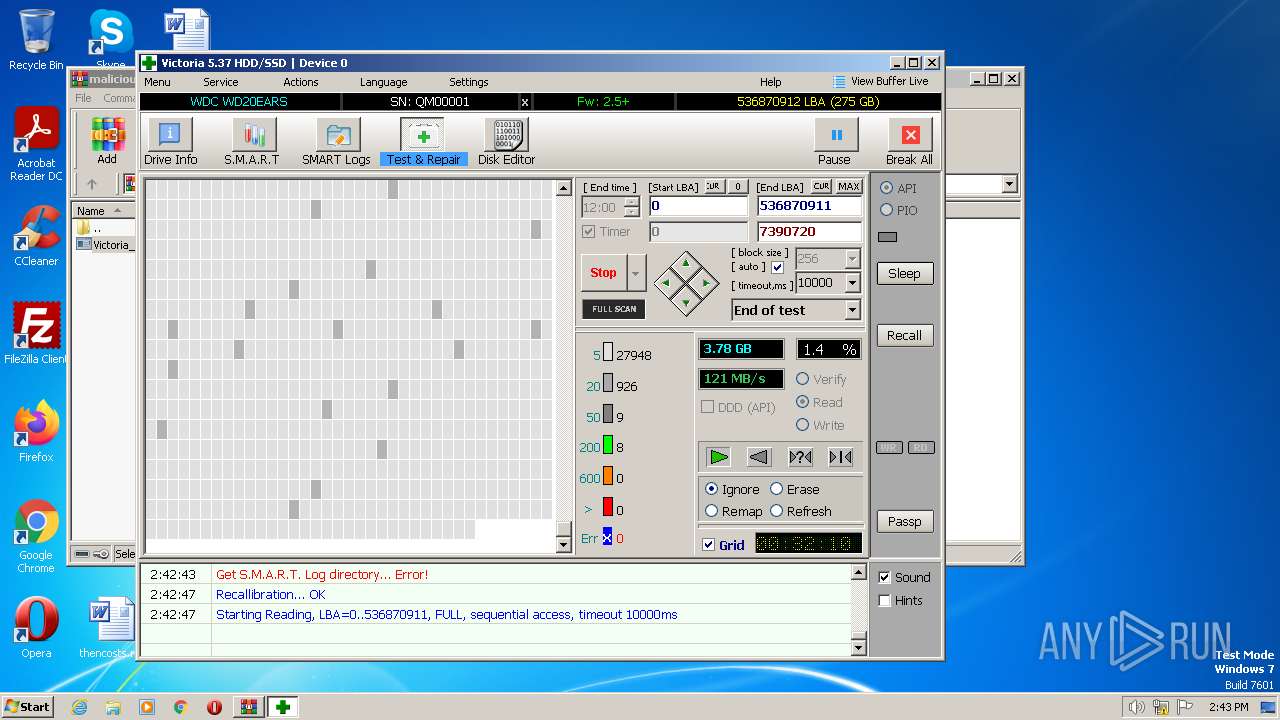
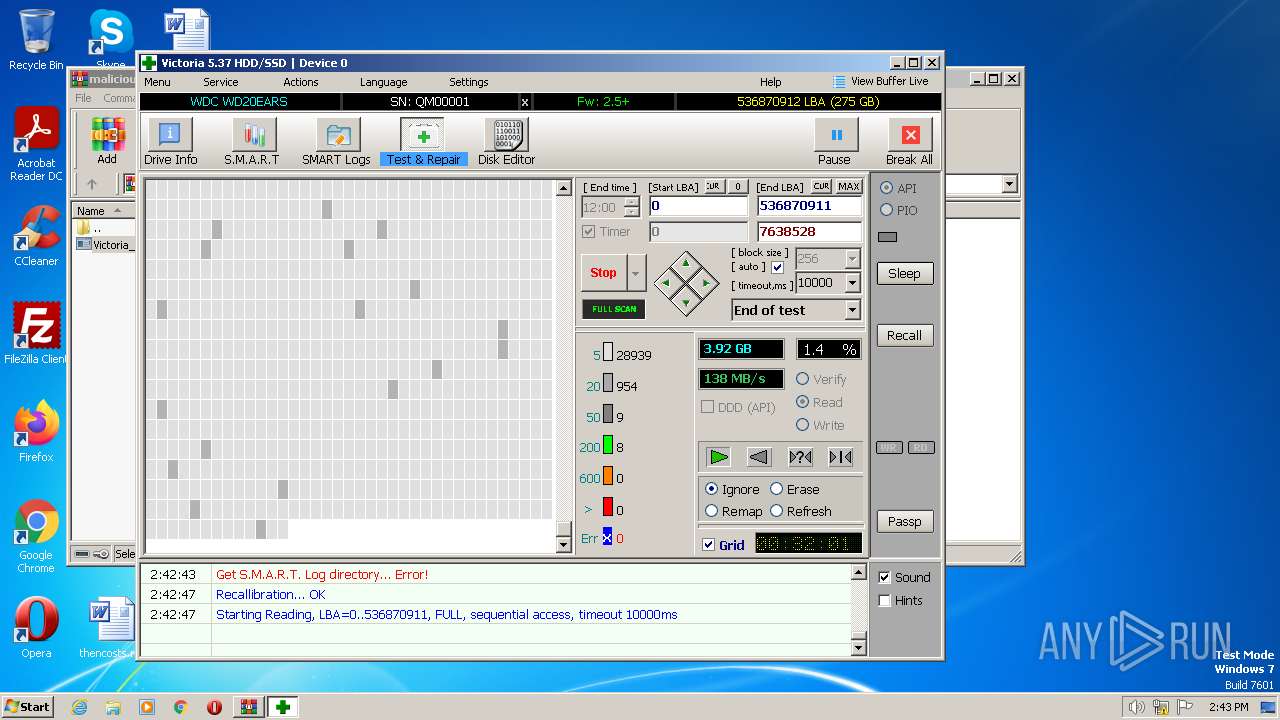
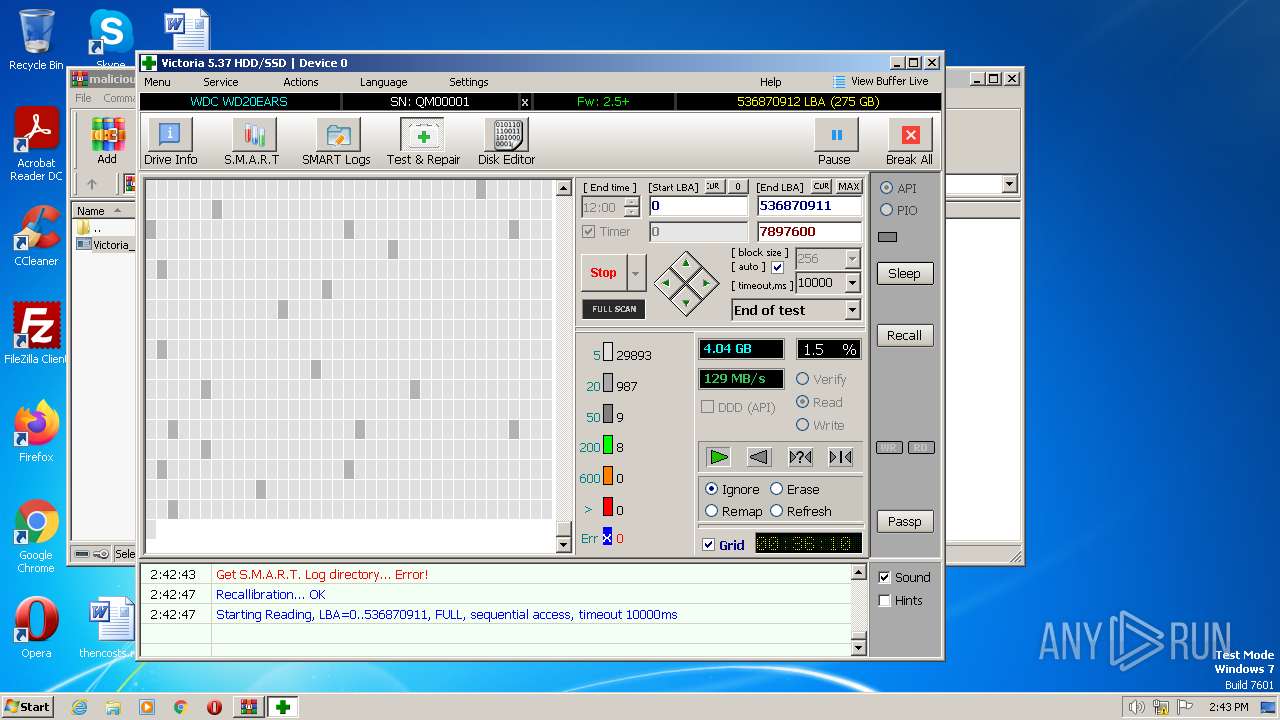
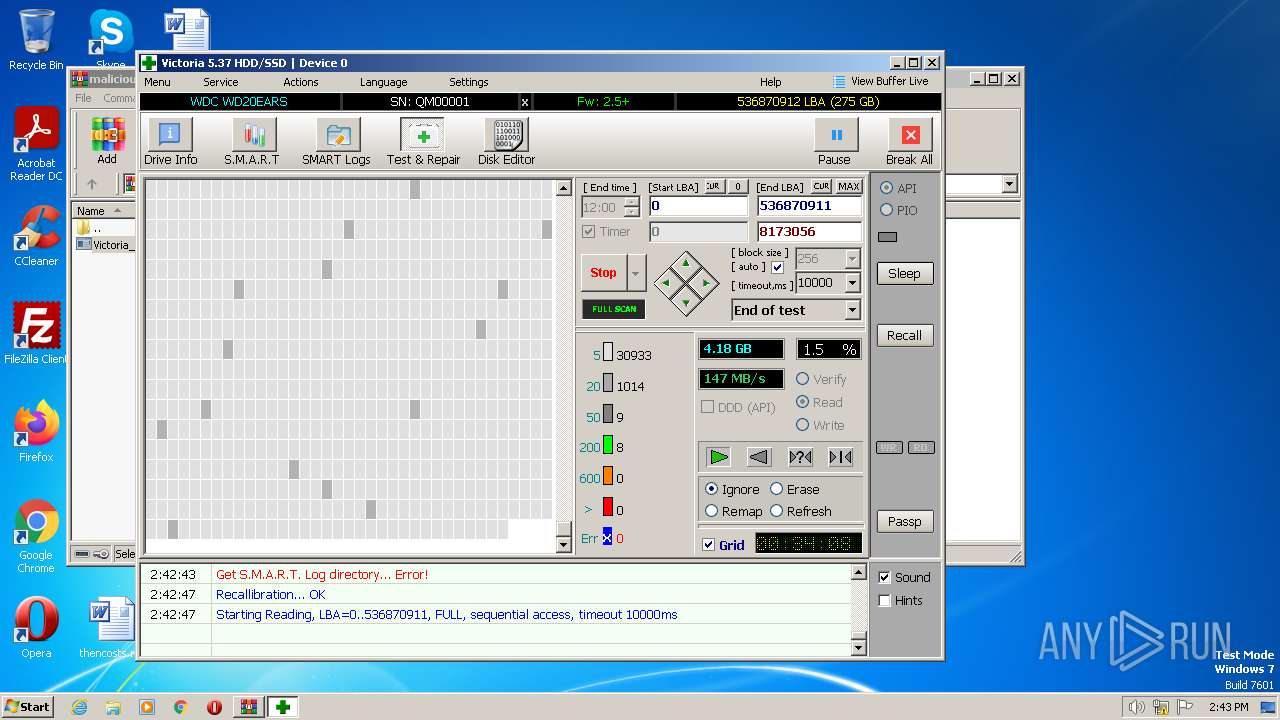
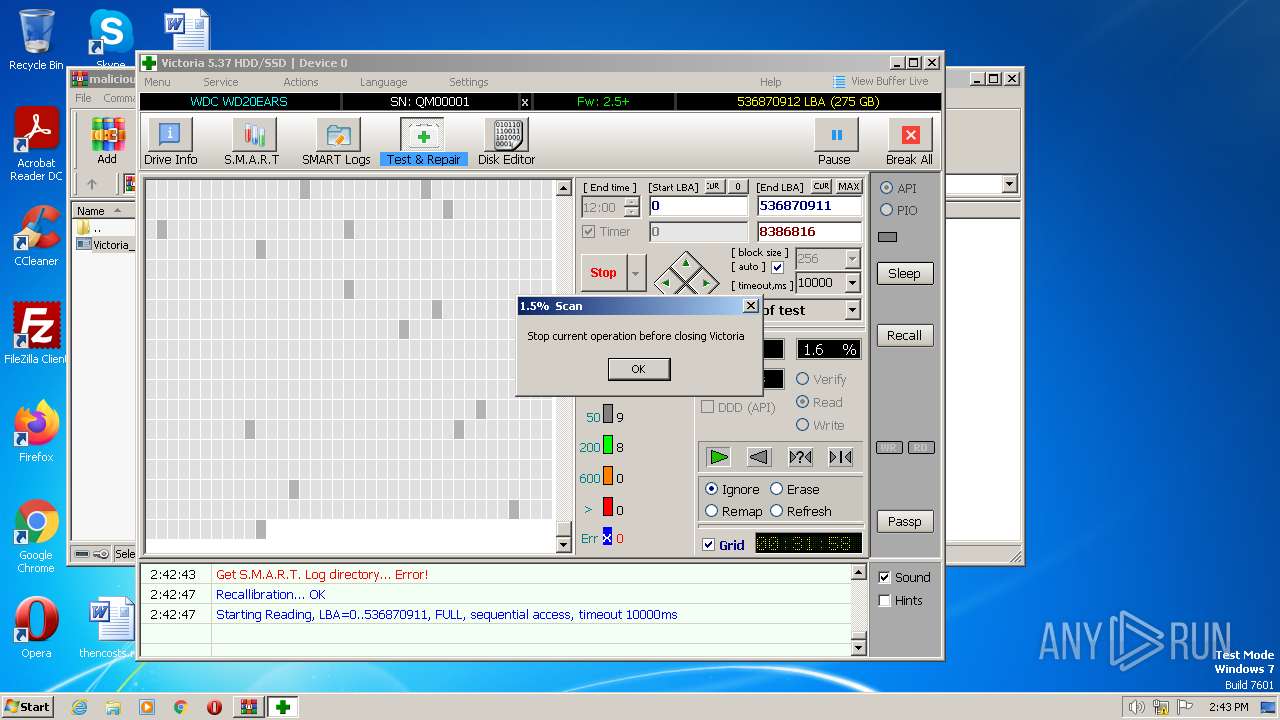
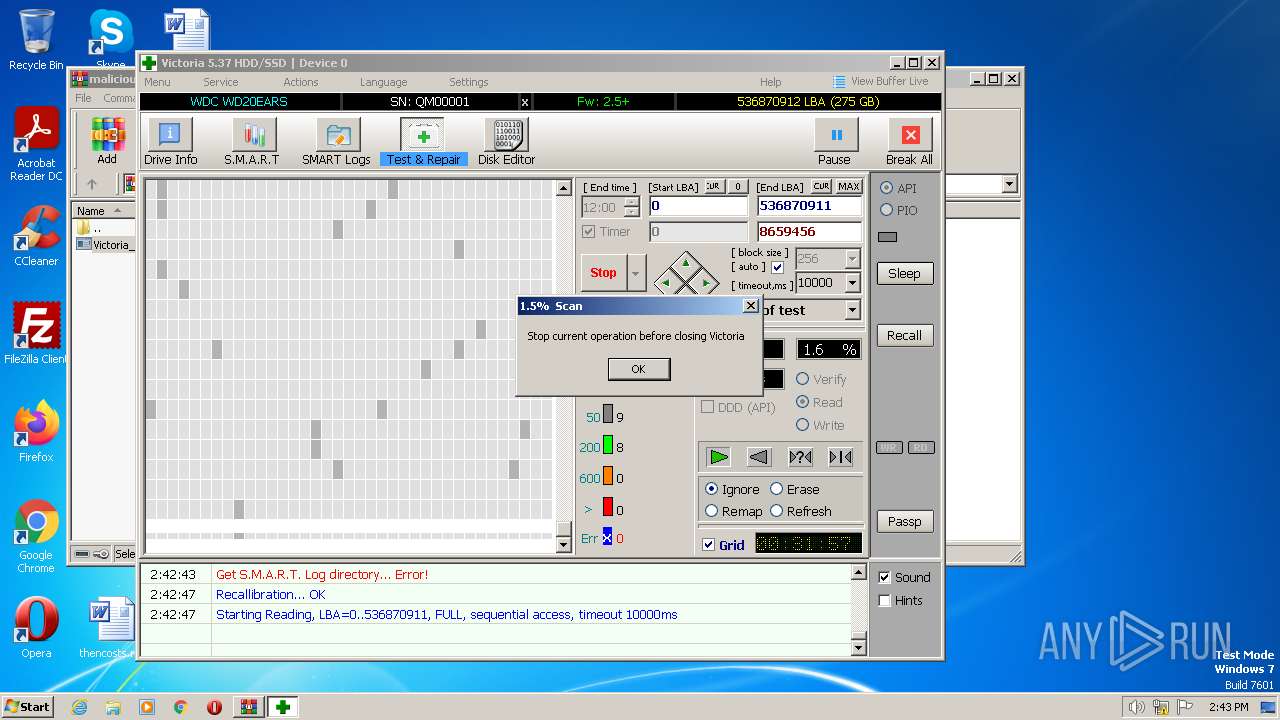
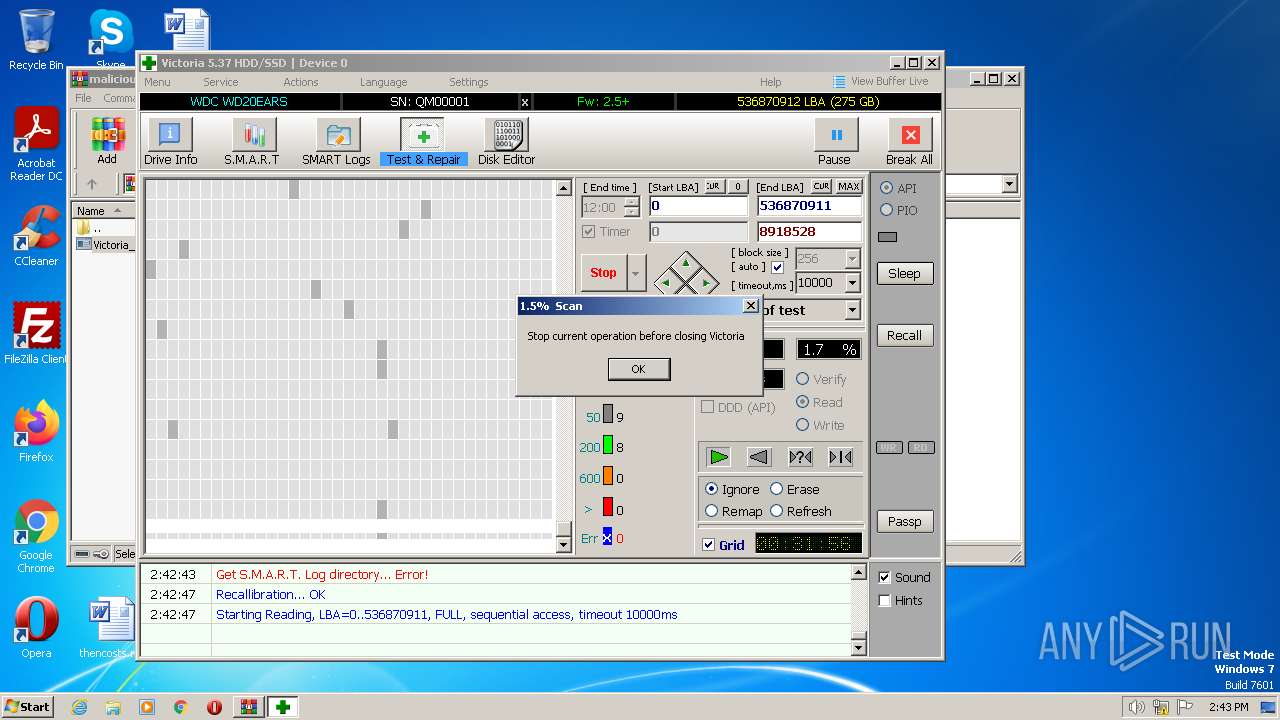
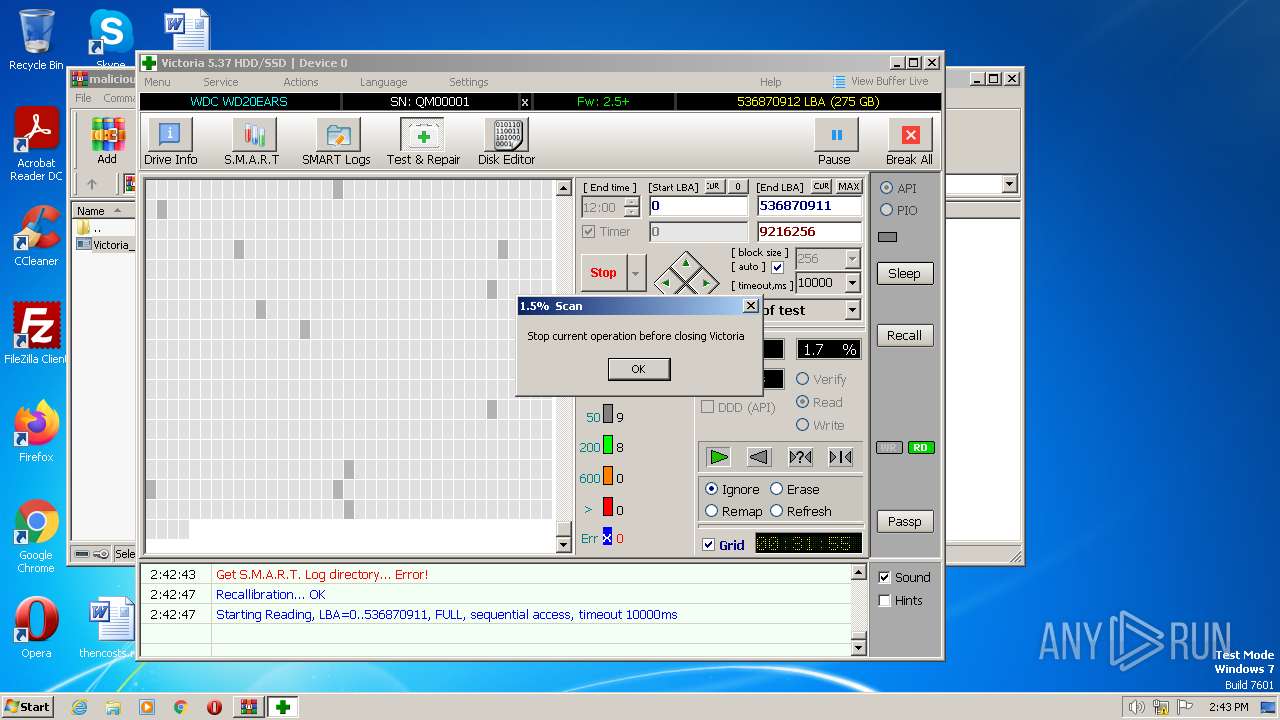
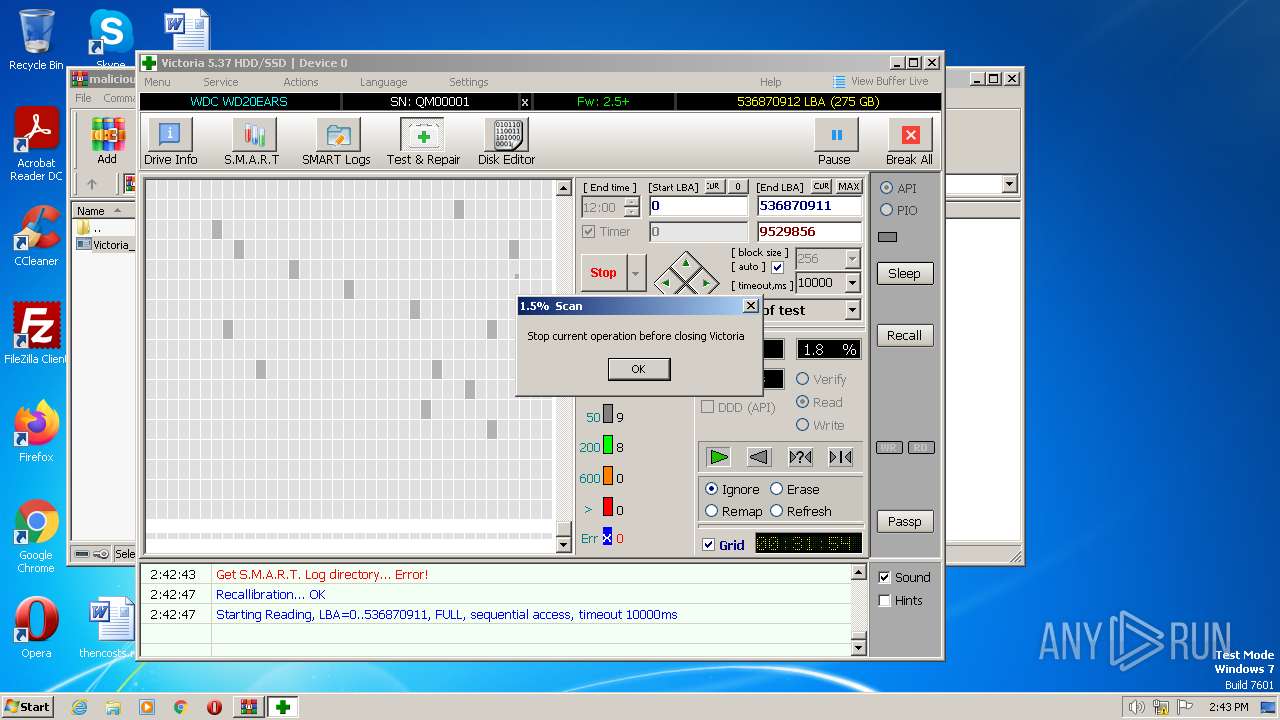
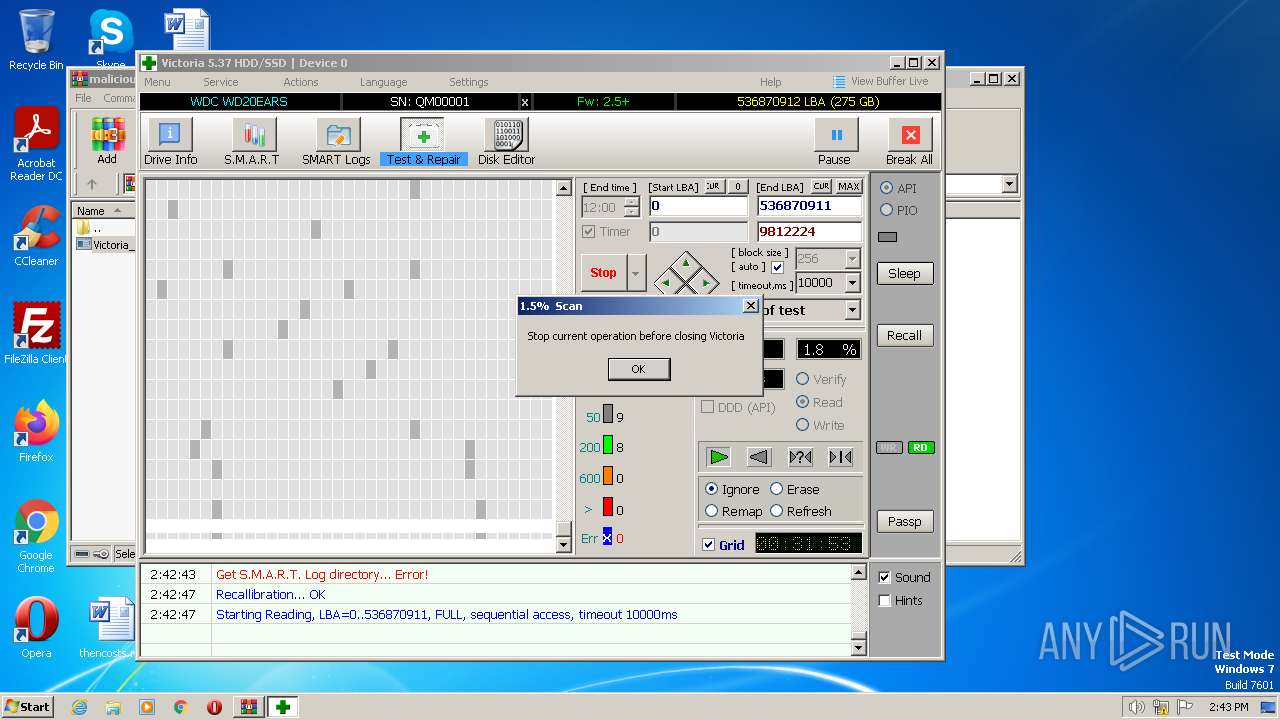
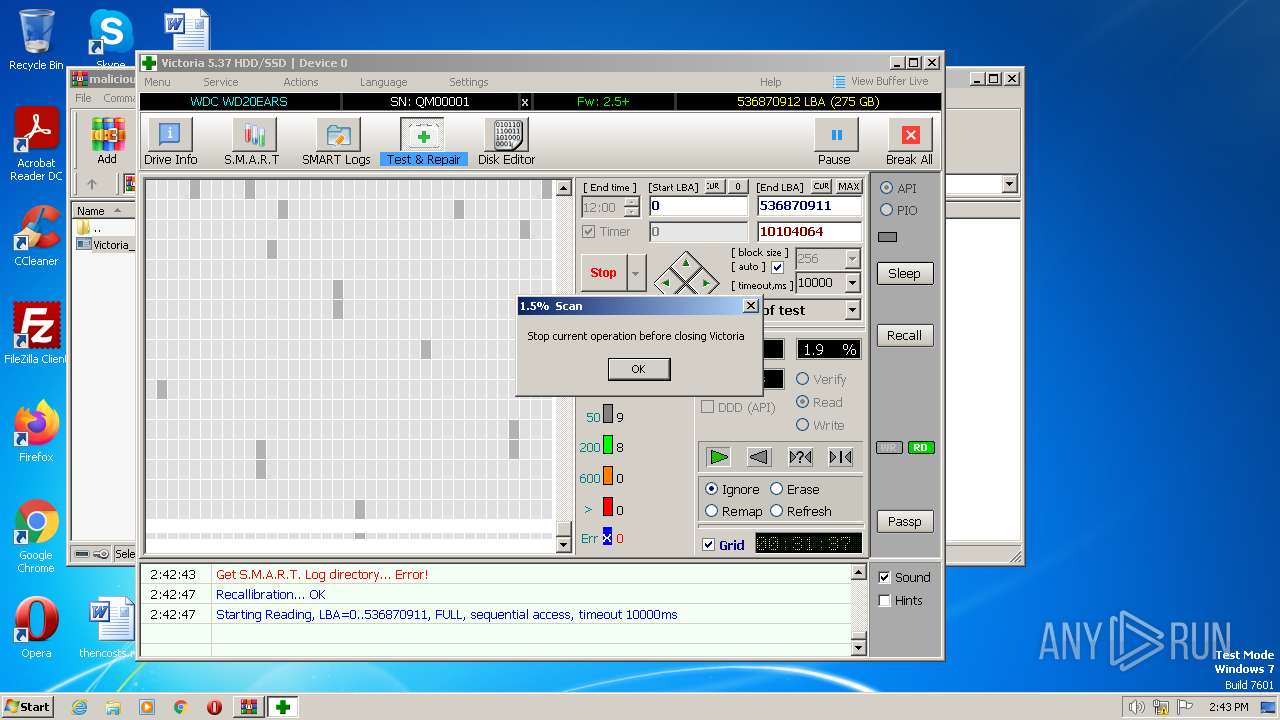
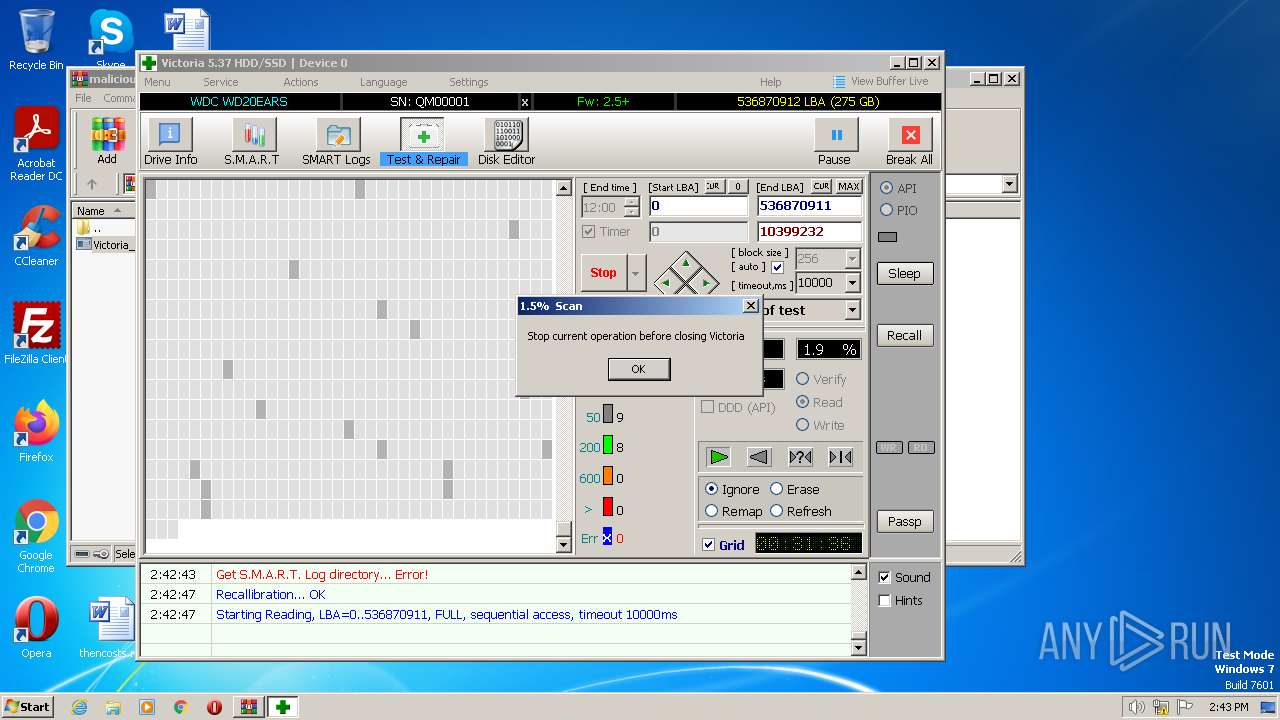
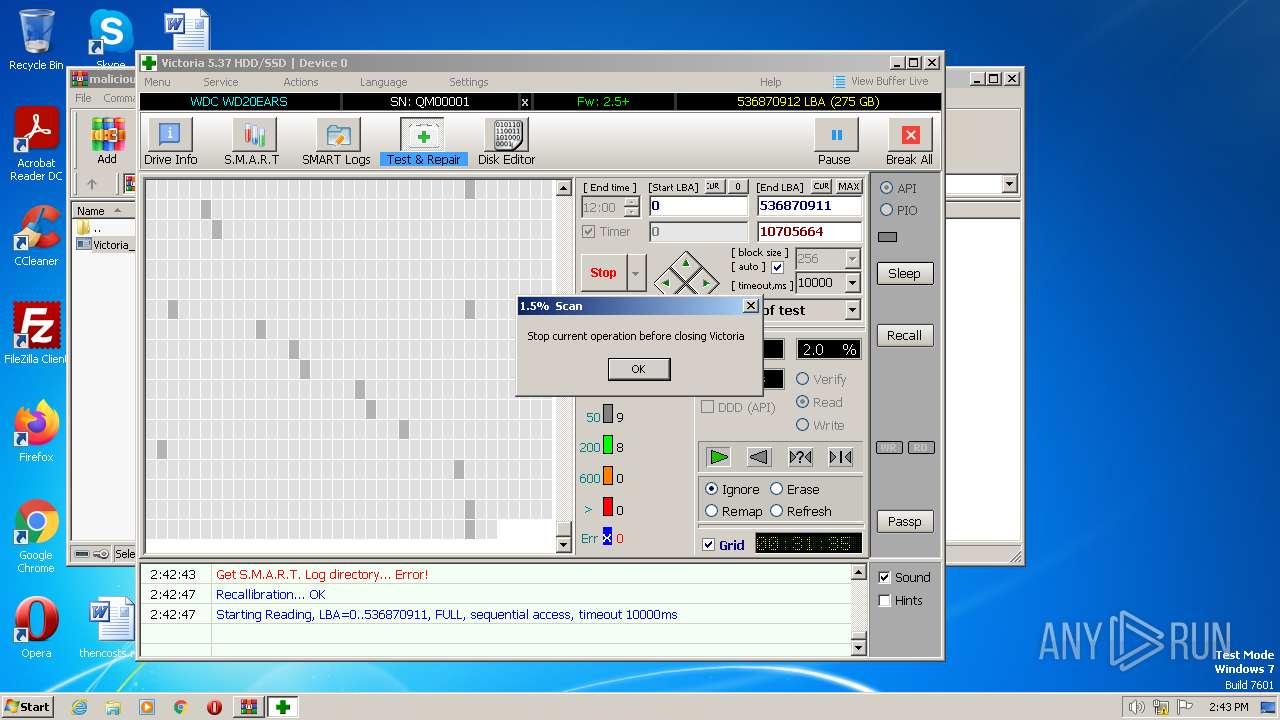
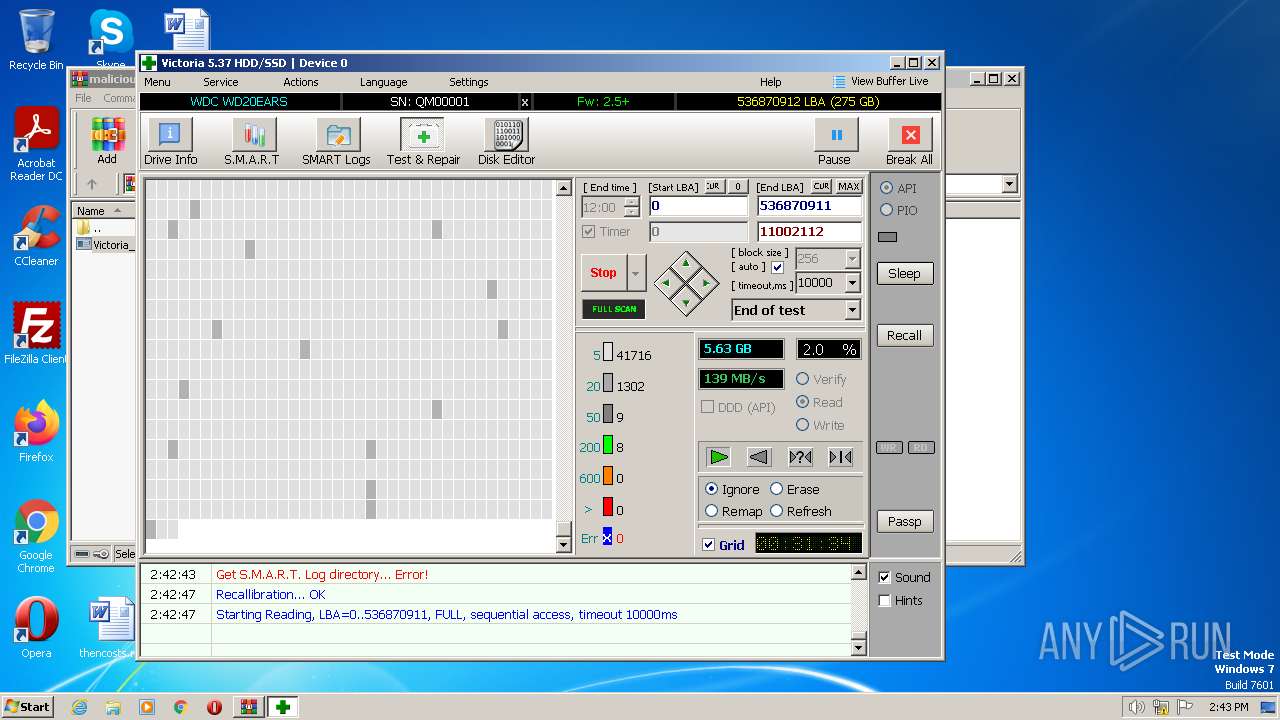
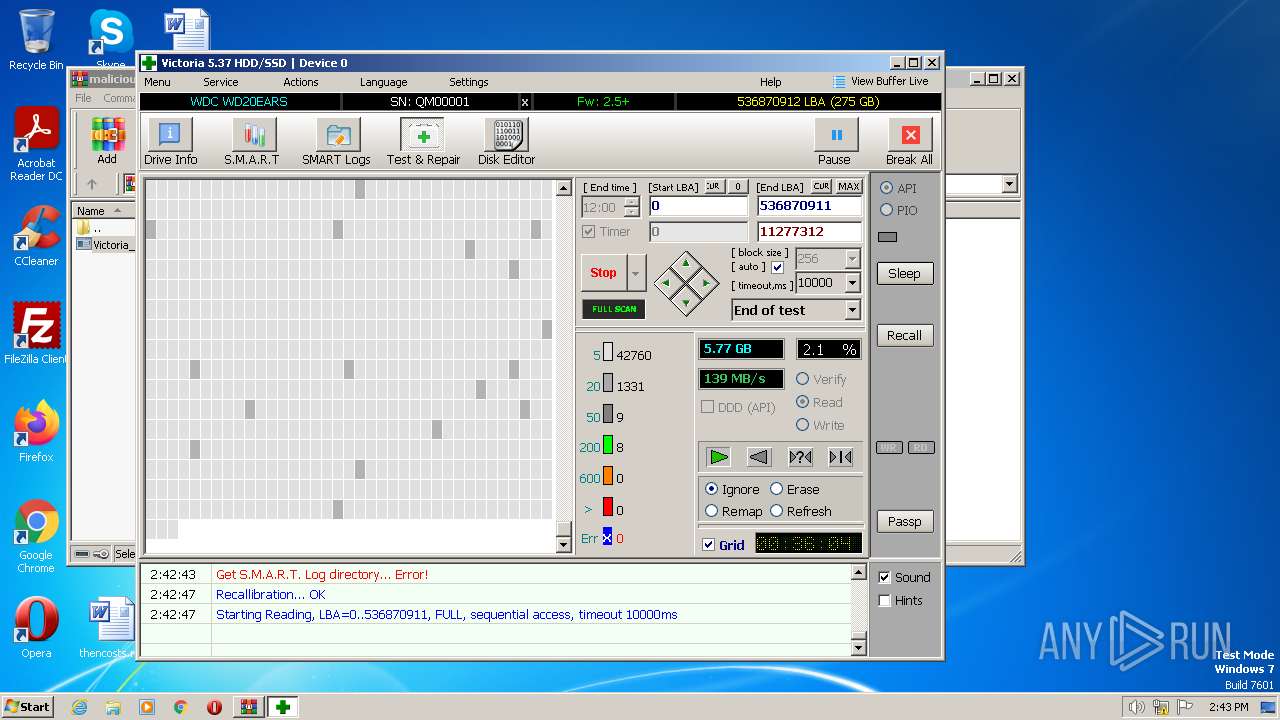
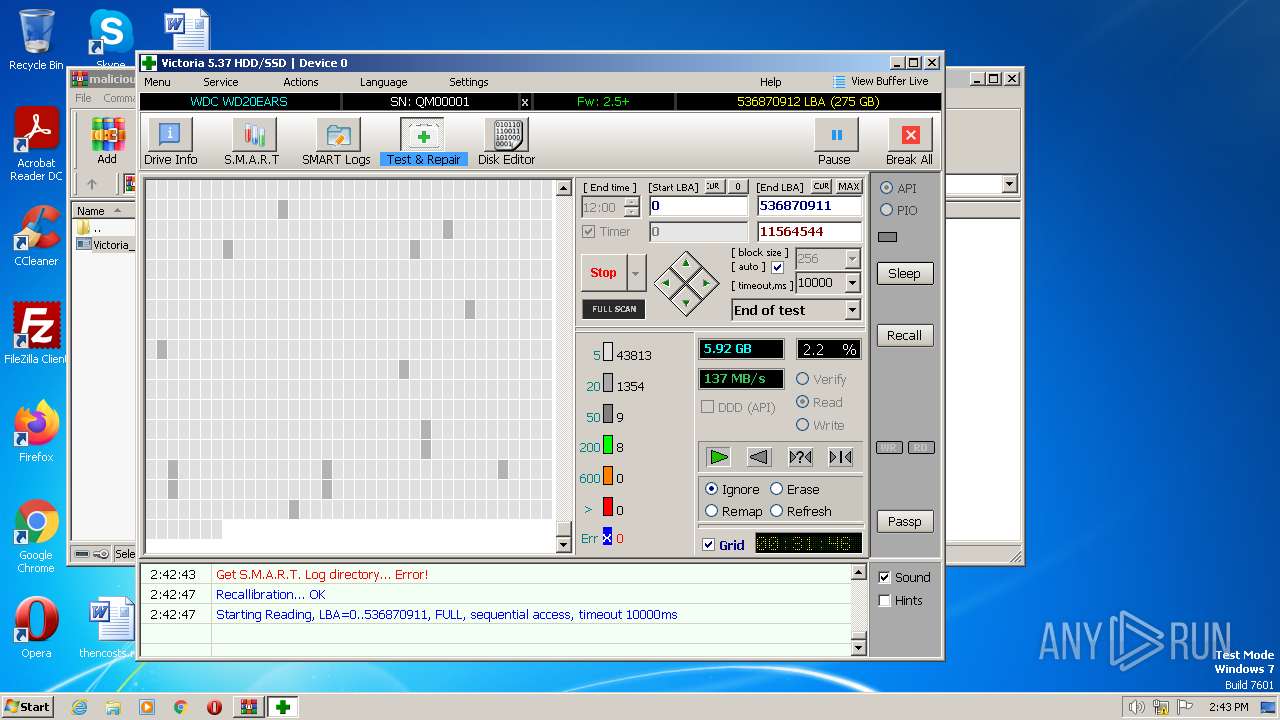
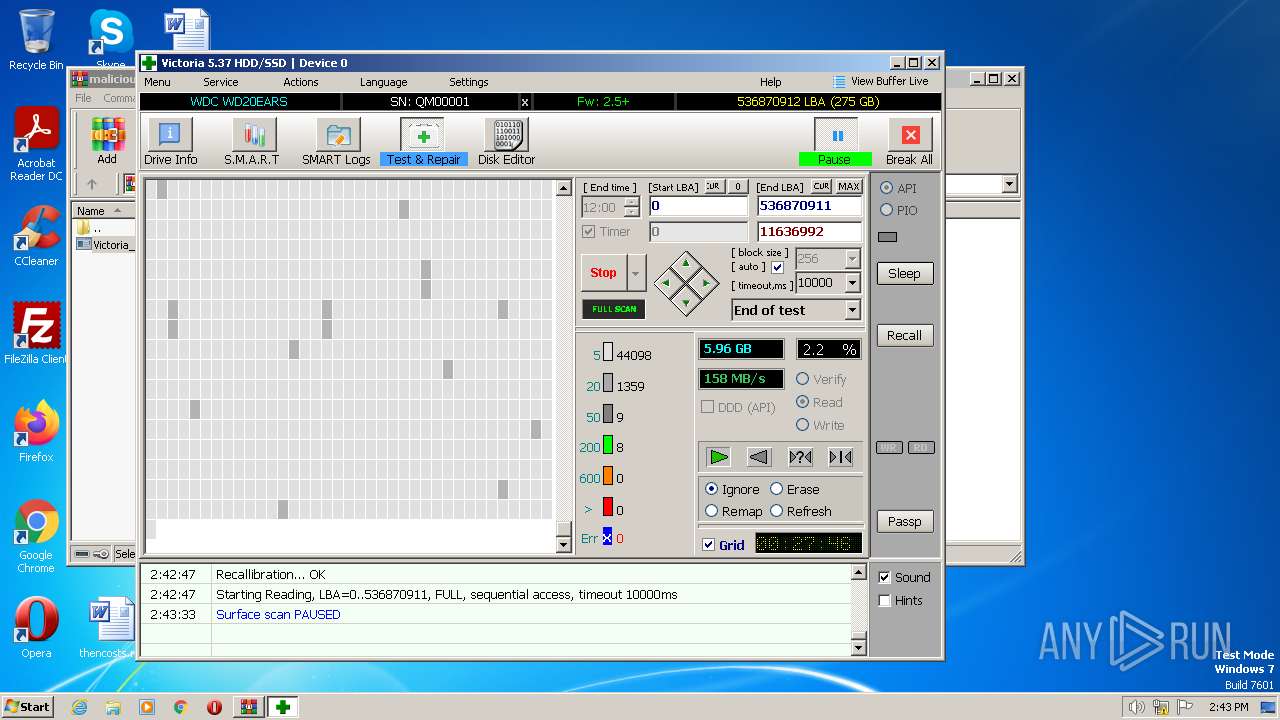
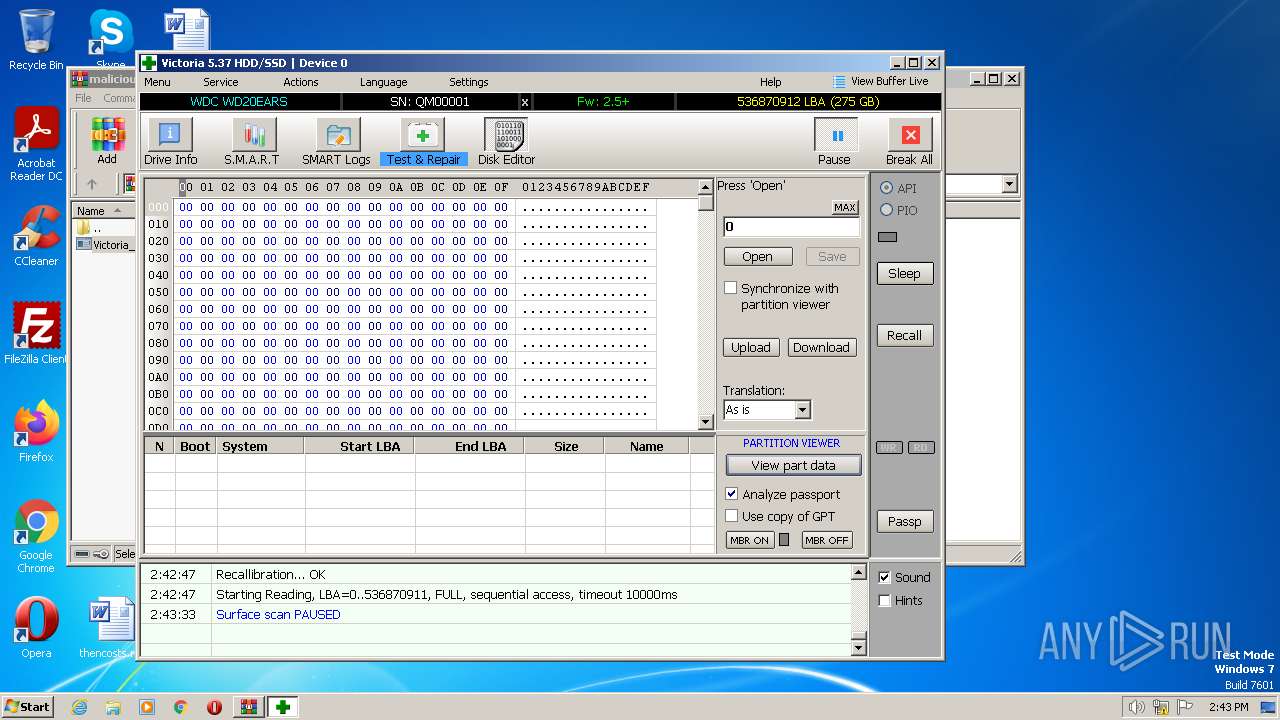
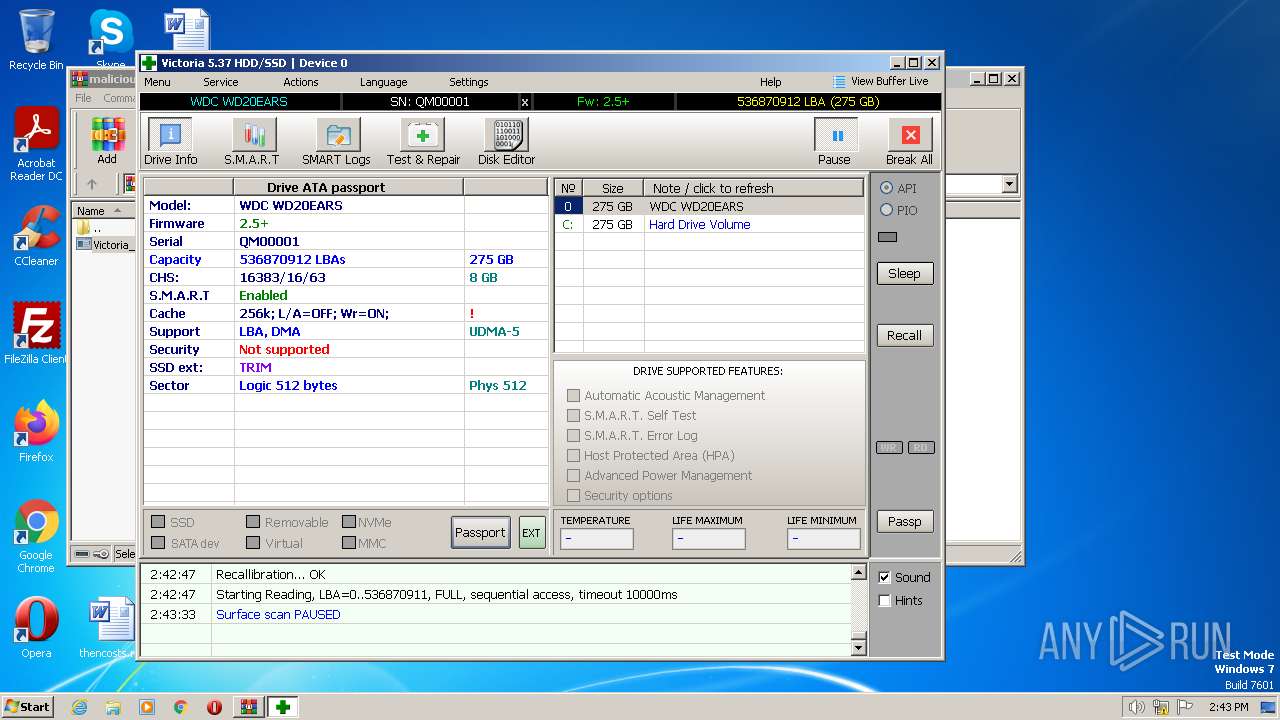
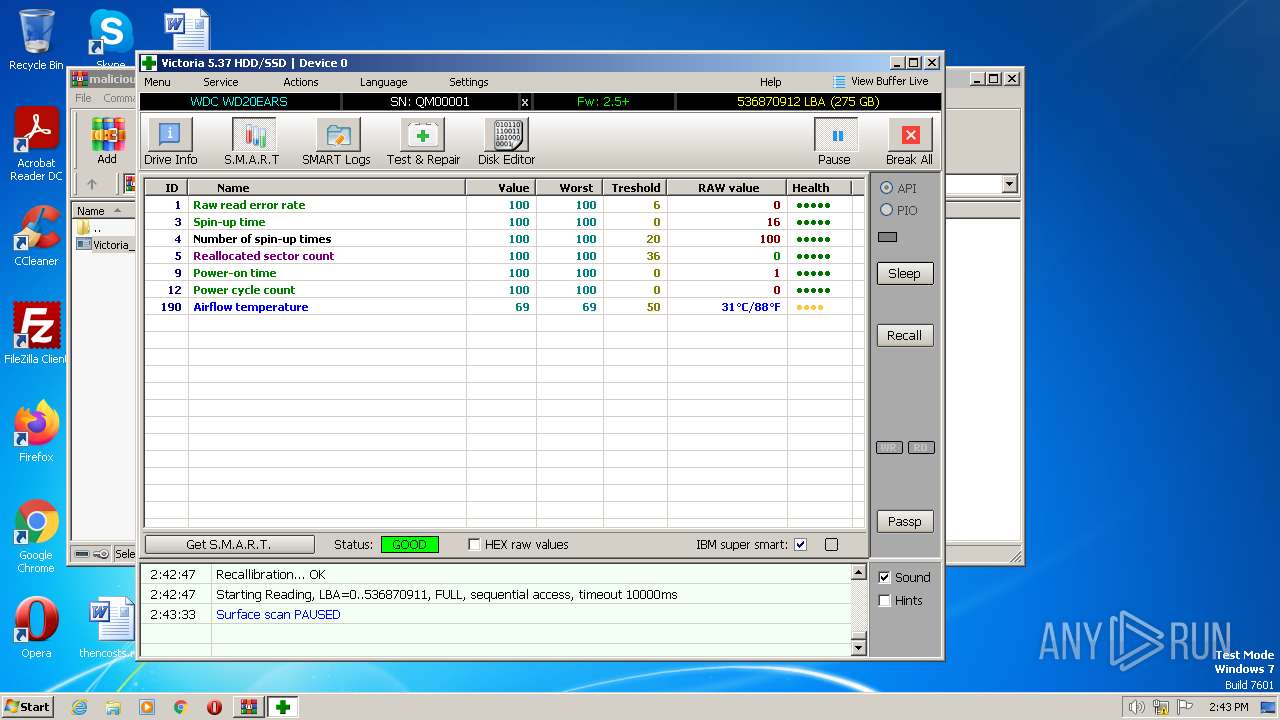
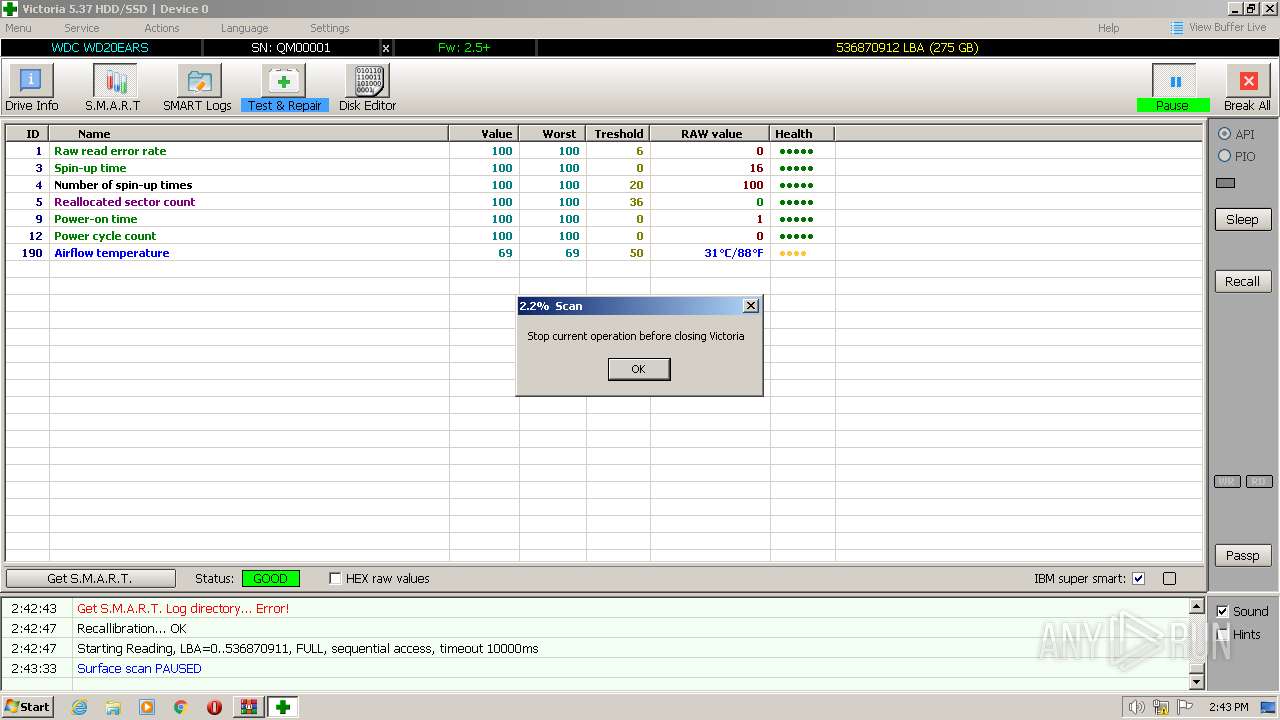
User: admin Company: HDD.BY Integrity Level: MEDIUM Description: HDD/SSD low-level test, repair & benchmark utility Exit code: 3221226540 Version: 5.3.7.0 Modules
| |||||||||||||||
| 2120 | C:\Windows\system32\cmd.exe /c start.bat | C:\Windows\System32\cmd.exe | — | hidcon.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2272 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\Victoria.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\Victoria.exe | — | cmd.exe | |||||||||||
User: admin Company: HDD.BY Integrity Level: MEDIUM Description: HDD/SSD low-level test, repair & benchmark utility Exit code: 3221226540 Version: 5.3.7.0 Modules
| |||||||||||||||
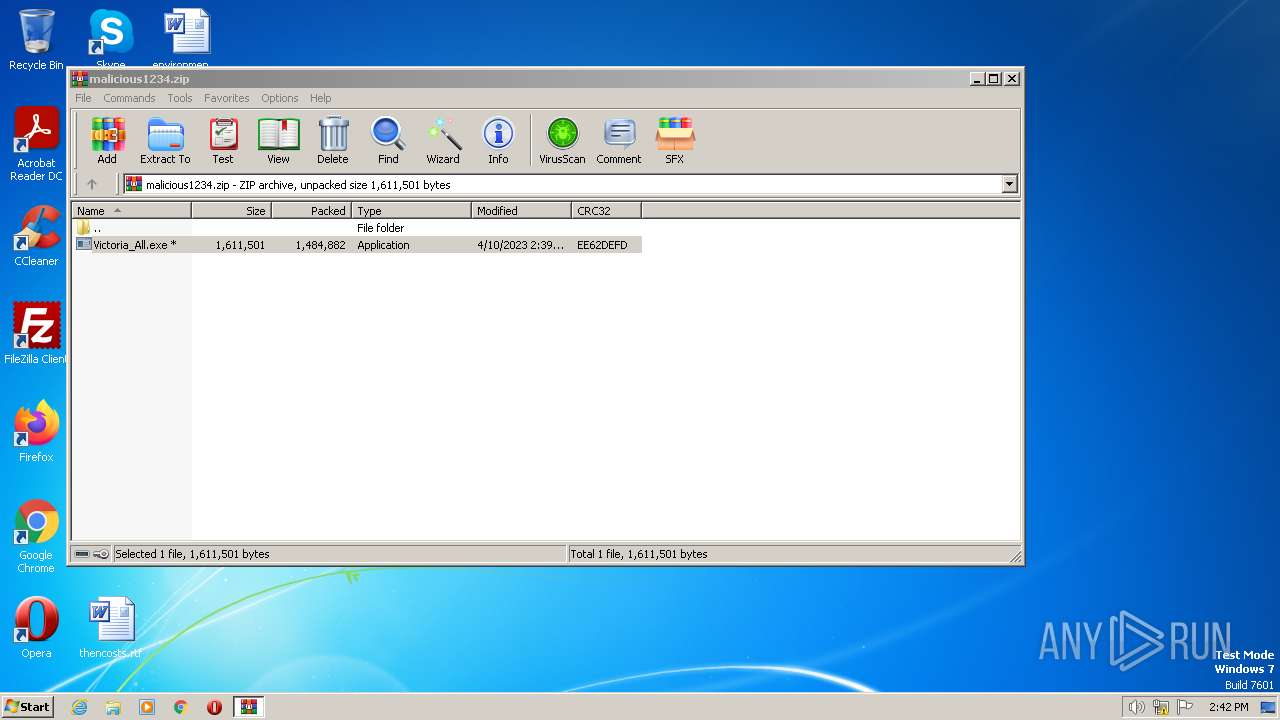
| 2808 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\malicious1234.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3156 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\Victoria.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\Victoria.exe | cmd.exe | ||||||||||||
User: admin Company: HDD.BY Integrity Level: HIGH Description: HDD/SSD low-level test, repair & benchmark utility Exit code: 0 Version: 5.3.7.0 Modules
| |||||||||||||||
| 3772 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb2808.11233\Victoria_All.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb2808.11233\Victoria_All.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3852 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\hidcon.exe" start.bat | C:\Users\admin\AppData\Local\Temp\RarSFX0\hidcon.exe | — | Victoria_All.exe | |||||||||||
User: admin Company: Andrew Grechkin Integrity Level: MEDIUM Description: Execute hidden console Exit code: 0 Version: 1, 1, 4, 0 Modules
| |||||||||||||||
Total events
4 982
Read events
4 918
Write events
64
Delete events
0
Modification events
| (PID) Process: | (2808) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2808) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2808) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2808) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (2808) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2808) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2808) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2808) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2808) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2808) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
10
Suspicious files
6
Text files
38
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2808 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2808.11233\Victoria_All.exe | executable | |
MD5:28BC06828CE1ABA3189546E8920471C1 | SHA256:AD070ACE53411CC27275FA1DDB6C80CC04B8431A8726E704D11E784B580E3E5C | |||
| 3772 | Victoria_All.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\Victoria.ini | ini | |
MD5:026A28E19E9CF5214D74163510B667E1 | SHA256:D7B3B81945CB7B8BD825596F89D9447C927A29CB84012C4BFDED4C085C428C94 | |||
| 3772 | Victoria_All.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\Help\English\whatsnew.rtf | text | |
MD5:9F5FC0015ACE5BCB72D208C8CC53663A | SHA256:119300AD57FE8B92C7E6CFBD0621B39D9C65833BEA92D075B4F22BFC295B7F06 | |||
| 3772 | Victoria_All.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\Help\Русский\vichlp.rtf | text | |
MD5:43FED3D6537208C280FAEC0FF8242692 | SHA256:FBDAE514E6F648554C58D7B6C3D1F154791DFAAC94223B88F7881471020E7933 | |||
| 3772 | Victoria_All.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\LNG\Ukraine.lng | text | |
MD5:378E4D25078B093E10914BCC2D678E0A | SHA256:AEBA810A306CB5B2D397CD1FED4E6D717CCFF3B6C30E015BCEFCD9F1430E8D57 | |||
| 3772 | Victoria_All.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\Help\Ukraine\whatsnew.rtf | text | |
MD5:9F5FC0015ACE5BCB72D208C8CC53663A | SHA256:119300AD57FE8B92C7E6CFBD0621B39D9C65833BEA92D075B4F22BFC295B7F06 | |||
| 3772 | Victoria_All.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\Help\Русский\whatsnew.rtf | text | |
MD5:9F5FC0015ACE5BCB72D208C8CC53663A | SHA256:119300AD57FE8B92C7E6CFBD0621B39D9C65833BEA92D075B4F22BFC295B7F06 | |||
| 3772 | Victoria_All.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\LNG\English.lng | text | |
MD5:1FC68FD20E3E589D8F9DEB05279620B7 | SHA256:0969ADA3E06388B76778CF92287BD3F4FEA90455C99C95682A33E96411AC9ABC | |||
| 3772 | Victoria_All.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\Help\Русский\dcomemo.rtf | text | |
MD5:190FE7511F89148F6A9A928A40E446B4 | SHA256:412C444C4964149AFC99A8DBF9AD7DA975A81BF605C264770536438349901AD6 | |||
| 3772 | Victoria_All.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\start.bat | text | |
MD5:49BCB0947787352EA242AED40C4D2A32 | SHA256:005530B0D80321160096D6A2A3E94489DC3D50D5B800FEDDE2EBA1263AEE9E25 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report