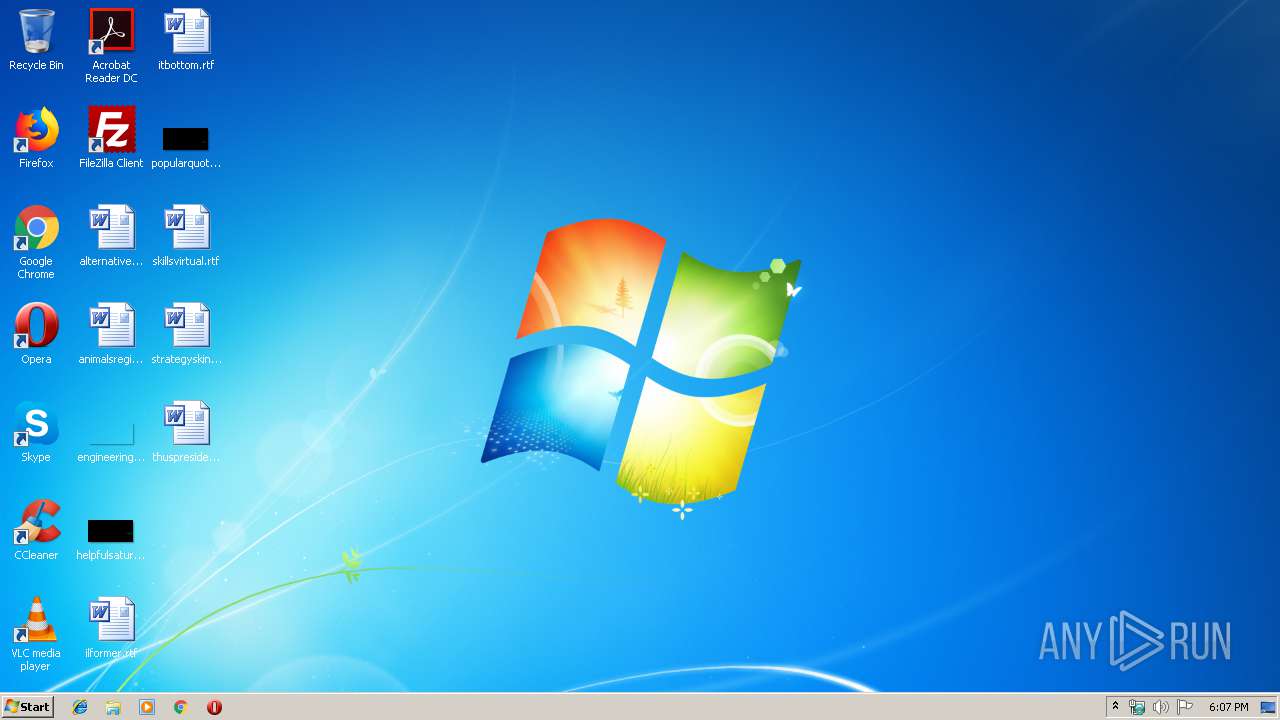
| File name: | rkill (1).exe |
| Full analysis: | https://app.any.run/tasks/c65f6971-a8e1-4601-b768-5fed8a5c7fcc |
| Verdict: | Malicious activity |
| Analysis date: | September 16, 2019, 17:06:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed, RAR self-extracting archive |
| MD5: | 28C253A0212B221E96F6A17499B91651 |
| SHA1: | 4592DE27B3D46BD32BF6779420FE441E990A45A4 |
| SHA256: | B7FC473EB8029EA559315300F953995B126B0E1942762CAFCA96B80E8D1A4207 |
| SSDEEP: | 24576:bLmfPSFQPaTQi9rl+kt7zxRHjZNjd/gUxK5Pg:QPSiAXt7zxTNjd/gUQg |
MALICIOUS
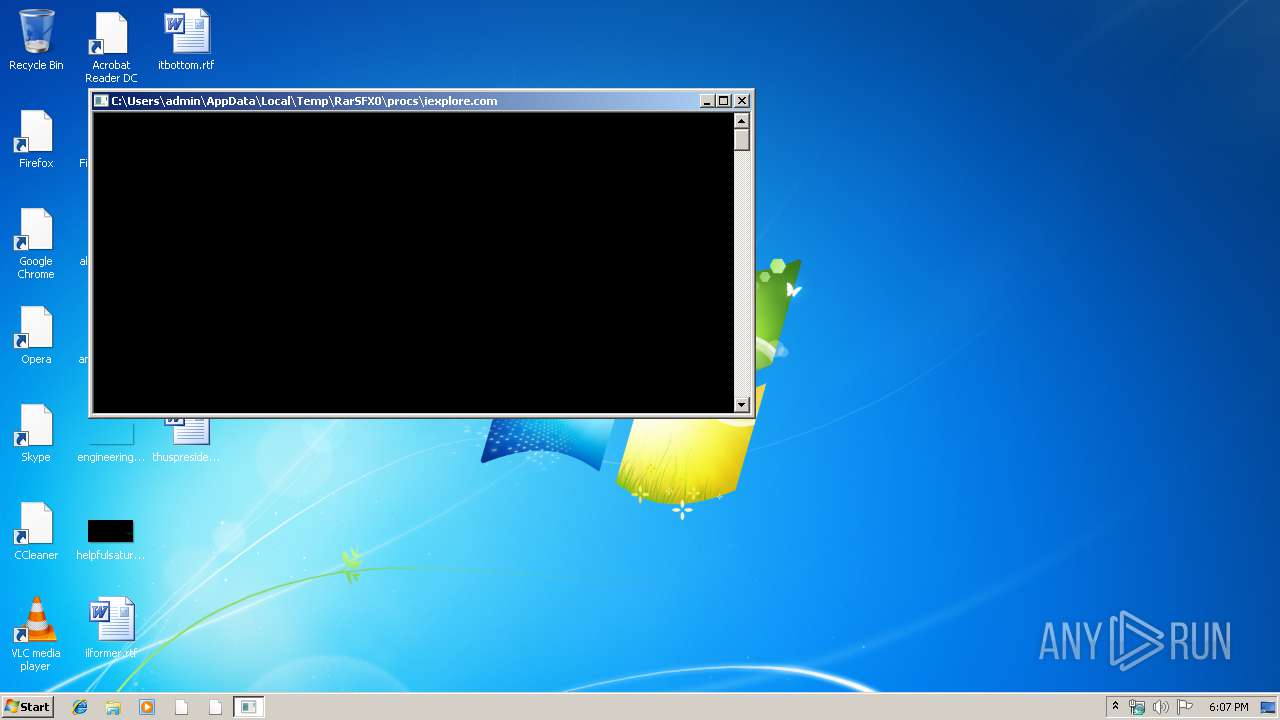
Application was dropped or rewritten from another process
- explorer.exe (PID: 3568)
- iexplore.exe (PID: 4036)
- explorer.exe (PID: 3792)
- iexplore.exe (PID: 2500)
- iexplore.com (PID: 2836)
- explorer.exe (PID: 3348)
- userinit.exe (PID: 3772)
- explorer.exe (PID: 3792)
- iexplore.exe (PID: 3348)
- iexplore.exe (PID: 3768)
- iexplore.exe (PID: 3484)
- iexplore.exe (PID: 2752)
- explorer.exe (PID: 3924)
- explorer.exe (PID: 3228)
- iexplore.exe (PID: 1876)
- iexplore.exe (PID: 2836)
- explorer.exe (PID: 3384)
- iexplore.exe (PID: 2860)
- explorer.exe (PID: 2336)
- iexplore.com (PID: 2472)
- iexplore.exe (PID: 184)
- iexplore.exe (PID: 3432)
- iexplore.exe (PID: 3804)
- iexplore.exe (PID: 2324)
- iexplore.exe (PID: 2984)
- iexplore.exe (PID: 2364)
- iexplore.exe (PID: 2784)
- iexplore.exe (PID: 2312)
- iexplore.exe (PID: 2376)
- iexplore.exe (PID: 2336)
- iexplore.exe (PID: 2964)
- iexplore.exe (PID: 3824)
- iexplore.exe (PID: 4060)
- iexplore.exe (PID: 1876)
- winlogon.exe (PID: 3380)
- iexplore.exe (PID: 2236)
- explorer.exe (PID: 4000)
- iexplore.exe (PID: 3992)
- explorer.exe (PID: 2288)
- explorer.exe (PID: 2084)
- iexplore.exe (PID: 756)
- iexplore.exe (PID: 2284)
- iexplore.exe (PID: 2168)
- iexplore.exe (PID: 3512)
- iexplore.exe (PID: 3208)
- iexplore.exe (PID: 2964)
- iexplore.exe (PID: 3008)
- iexplore.exe (PID: 4076)
- iexplore.exe (PID: 3508)
- iexplore.exe (PID: 3180)
- iexplore.exe (PID: 3560)
- iexplore.exe (PID: 3152)
- iexplore.exe (PID: 3544)
- explorer.exe (PID: 2788)
- iexplore.exe (PID: 2816)
- iexplore.exe (PID: 3108)
- iexplore.exe (PID: 3748)
- iexplore.exe (PID: 2140)
- iexplore.exe (PID: 2168)
- iexplore.exe (PID: 3976)
- iexplore.exe (PID: 3364)
- iexplore.exe (PID: 3056)
- iexplore.exe (PID: 3028)
- iexplore.exe (PID: 3412)
- iexplore.exe (PID: 3108)
- iexplore.exe (PID: 2468)
- iexplore.exe (PID: 3180)
- iexplore.exe (PID: 2732)
- iexplore.exe (PID: 4020)
- iexplore.exe (PID: 3768)
- iexplore.exe (PID: 2588)
- iexplore.exe (PID: 2652)
- iexplore.exe (PID: 2384)
- iexplore.exe (PID: 2424)
- iexplore.exe (PID: 3580)
- iexplore.exe (PID: 2952)
- nircmd.exe (PID: 2188)
- iexplore.exe (PID: 4056)
- iexplore.exe (PID: 3284)
- iexplore.exe (PID: 3536)
Changes the autorun value in the registry
- InfDefaultInstall.exe (PID: 2500)
- InfDefaultInstall.exe (PID: 3784)
- InfDefaultInstall.exe (PID: 3708)
SUSPICIOUS
Executable content was dropped or overwritten
- rkill (1).exe (PID: 1512)
Starts application with an unusual extension
- rkill (1).exe (PID: 1512)
Creates executable files which already exist in Windows
- rkill (1).exe (PID: 1512)
Modifies the open verb of a shell class
- iexplore.exe (PID: 2500)
- explorer.exe (PID: 3792)
- iexplore.com (PID: 2836)
- explorer.exe (PID: 2336)
- iexplore.exe (PID: 3348)
- iexplore.com (PID: 2472)
- iexplore.exe (PID: 2964)
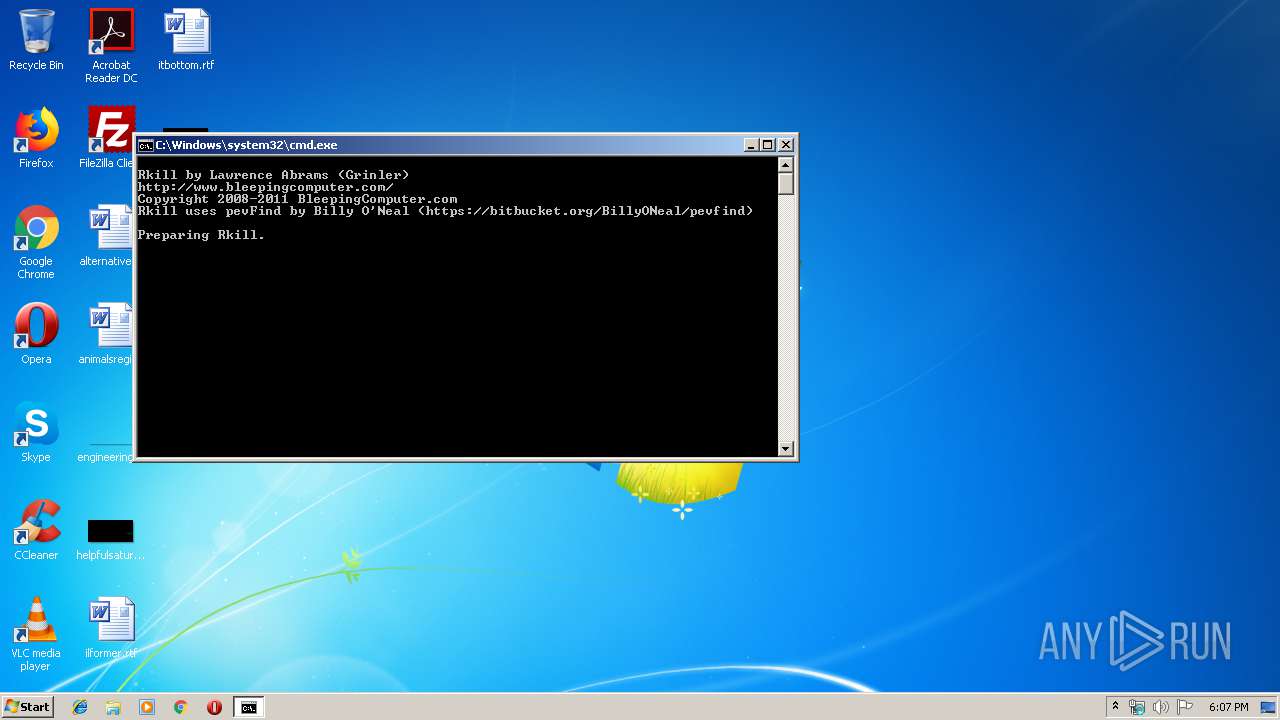
Starts CMD.EXE for commands execution
- iexplore.exe (PID: 2424)
- rkill (1).exe (PID: 1512)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (39.3) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (38.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.5) |
| .exe | | | Win32 Executable (generic) (6.5) |
| .exe | | | Generic Win/DOS Executable (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:03:15 07:27:50+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 49152 |
| InitializedDataSize: | 143360 |
| UninitializedDataSize: | 241664 |
| EntryPoint: | 0x471c0 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Mar-2010 06:27:50 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 15-Mar-2010 06:27:50 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x0003B000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x0003C000 | 0x0000C000 | 0x0000B400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.9021 |
.rsrc | 0x00048000 | 0x00023000 | 0x00022400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.72268 |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.DLL |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
162
Monitored processes
93
Malicious processes
6
Suspicious processes
14
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\nird\iexplore.exe" win close stitle "Antivirus Suite" | C:\Users\admin\AppData\Local\Temp\RarSFX0\nird\iexplore.exe | — | rkill (1).exe | |||||||||||
User: admin Company: NirSoft Integrity Level: HIGH Description: NirCmd Exit code: 0 Version: 2.37 Modules
| |||||||||||||||
| 756 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\h\iexplore.exe" procs\iexplore.exe -k "C:\Users\admin\local settings\application data\*.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\h\iexplore.exe | — | rkill (1).exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1512 | "C:\Users\admin\AppData\Local\Temp\rkill (1).exe" | C:\Users\admin\AppData\Local\Temp\rkill (1).exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1876 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\h\iexplore.exe" procs\iexplore.exe plist C:\Users\admin\AppData\Local\Temp\rks1.log | C:\Users\admin\AppData\Local\Temp\RarSFX0\h\iexplore.exe | — | rkill (1).exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1876 | procs\iexplore.exe -loadline"extra.dat" and not "C:\Users\admin\AppData\Local\Temp\rkill (1).exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\procs\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2060 | "C:\Windows\System32\grpconv.exe" -o | C:\Windows\System32\grpconv.exe | — | runonce.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Progman Group Converter Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2084 | procs\explorer.exe -k hotfix.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\procs\explorer.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 4 Modules
| |||||||||||||||
| 2140 | procs\iexplore.exe -k "ALLUSE~1\*" | C:\Users\admin\AppData\Local\Temp\RarSFX0\procs\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 4 Modules
| |||||||||||||||
| 2168 | procs\iexplore.exe -k "C:\Users\admin\*" and not "C:\Users\admin\AppData\Local\Temp\rkill (1).exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\procs\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2168 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\h\iexplore.exe" procs\iexplore.exe -k winlogon32.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\h\iexplore.exe | — | rkill (1).exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
1 640
Read events
1 563
Write events
72
Delete events
5
Modification events
| (PID) Process: | (1512) rkill (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1512) rkill (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2836) iexplore.com | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.exe |
| Operation: | write | Name: | |
Value: exefile | |||
| (PID) Process: | (2836) iexplore.com | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\exefile\shell\open\command |
| Operation: | write | Name: | |
Value: "%1" %* | |||
| (PID) Process: | (2836) iexplore.com | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.bat |
| Operation: | write | Name: | |
Value: batfile | |||
| (PID) Process: | (2836) iexplore.com | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\batfile\shell\open\command |
| Operation: | write | Name: | |
Value: "%1" %* | |||
| (PID) Process: | (2836) iexplore.com | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced |
| Operation: | write | Name: | HideIcons |
Value: 0 | |||
| (PID) Process: | (3792) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.exe |
| Operation: | write | Name: | |
Value: exefile | |||
| (PID) Process: | (3792) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\exefile\shell\open\command |
| Operation: | write | Name: | |
Value: "%1" %* | |||
| (PID) Process: | (3792) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\exefile\shell\open\command |
| Operation: | delete value | Name: | IsolatedCommand |
Value: "%1" %* | |||
Executable files
14
Suspicious files
0
Text files
18
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1512 | rkill (1).exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\rkill.bat | text | |
MD5:62590E28772FCA41D8548515D7CF2EB8 | SHA256:F41F623E6299E454594540AA5531915A8BD32CBB277EAB92A2A9CC9E25FE49BB | |||
| 1512 | rkill (1).exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\s.inf | ini | |
MD5:914650C80D2024F74AA53B7B936A548A | SHA256:5CF46D38155CDCC79898804811EB6CC4988E28912EA0BD911DF044C4758F2DE9 | |||
| 1512 | rkill (1).exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\wl.txt | text | |
MD5:175946A0BE1C6E5AD70DD11332D6CACB | SHA256:50265CB4868CFDC49A94469D1C71105B839FACD5FDDC2B9609A58CA0D40DF874 | |||
| 1512 | rkill (1).exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\procs\explorer.exe | executable | |
MD5:3C33B26F2F7FA61D882515F2D6078691 | SHA256:908FDB876715F0A77014A37396D9E964FA6359D98099929BAB4086E66D72BB9F | |||
| 1512 | rkill (1).exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\h\explorer.exe | executable | |
MD5:ABC6379205DE2618851C4FCBF72112EB | SHA256:22E7528E56DFFAA26CFE722994655686C90824B13EB51184ABFE44D4E95D473F | |||
| 1512 | rkill (1).exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\nircmdc.exe | executable | |
MD5:9CB3A38088807F54E7F89AC30E09C030 | SHA256:71579B7BB651004F9C2E3F8D62511F610443C7E8225001865415A4620BD04219 | |||
| 1512 | rkill (1).exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\h\iexplore.exe | executable | |
MD5:ABC6379205DE2618851C4FCBF72112EB | SHA256:22E7528E56DFFAA26CFE722994655686C90824B13EB51184ABFE44D4E95D473F | |||
| 1512 | rkill (1).exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\nird\iexplore.exe | executable | |
MD5:AC6094297CD882B8626466CDEB64F19F | SHA256:27C7FFD8367AAA73155FBB287A7DF1F157F2D0C3323DBB176D02B36FF616FCA5 | |||
| 1512 | rkill (1).exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\nircmd.exe | executable | |
MD5:AC6094297CD882B8626466CDEB64F19F | SHA256:27C7FFD8367AAA73155FBB287A7DF1F157F2D0C3323DBB176D02B36FF616FCA5 | |||
| 1512 | rkill (1).exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\proxycheck.exe | executable | |
MD5:43FEE8A7DA368EAAF5019443382D450D | SHA256:77E590CA7680C7C35A895FCD870EDB4CBD4C2A920D01739C21331D9FF874A9A6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report