| File name: | 02sall.js |
| Full analysis: | https://app.any.run/tasks/e8f4b21e-818e-4278-b892-cfe57818f910 |
| Verdict: | Malicious activity |
| Analysis date: | March 15, 2019, 02:19:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 7EB664556A2584FD478A71953AA410EF |
| SHA1: | B240BF44AAFB3283AF11F74593C18098EB64AEBD |
| SHA256: | B7F76BFEB39F3AB30210CA78465927854F712B7D332091C476CD703095D27386 |
| SSDEEP: | 6144:uQYQ4ZlCjZoN5cM6OGS3Q3y4QdQCeo6bx1P2oPRj3ICTCqtSnRSMlNqtbmQZwIZy:0tzUZW9GhQKC50FTJjHjakTwTEQ |
MALICIOUS
Changes settings of System certificates
- WScript.exe (PID: 3472)
SUSPICIOUS
Uses NETSH.EXE for network configuration
- WScript.exe (PID: 3472)
Adds / modifies Windows certificates
- WScript.exe (PID: 3472)
Creates files in the user directory
- powershell.exe (PID: 1236)
Uses REG.EXE to modify Windows registry
- WScript.exe (PID: 3472)
Executes PowerShell scripts
- WScript.exe (PID: 3472)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
45
Monitored processes
7
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1176 | "C:\Windows\System32\reg.exe" add HKLM\SYSTEM\CurrentControlSet\services\Tcpip\Parameters /v Tcp1323Opts /t REG_DWORD /d 0x02 /f | C:\Windows\System32\reg.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1236 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -enc RwBlAHQALQBXAE0ASQBPAGIAagBlAGMAdAAgAC0AQwBsAGEAcwBzACAAJwBXAGkAbgAzADIAXwBOAGUAdAB3AG8AcgBrAEEAZABhAHAAdABlAHIAQwBvAG4AZgBpAGcAdQByAGEAdABpAG8AbgAnACAAfAAgAEYAbwByAEUAYQBjAGgALQBPAGIAagBlAGMAdAAgAHsATgBlAHcALQBJAHQAZQBtAFAAcgBvAHAAZQByAHQAeQAgAC0AUABhAHQAaAAgACIASABLAEwATQA6AFwAUwBZAFMAVABFAE0AXABDAHUAcgByAGUAbgB0AEMAbwBuAHQAcgBvAGwAUwBlAHQAXABzAGUAcgB2AGkAYwBlAHMAXABUAGMAcABpAHAAXABQAGEAcgBhAG0AZQB0AGUAcgBzAFwASQBuAHQAZQByAGYAYQBjAGUAcwBcACQAKAAkAF8ALgBTAGUAdAB0AGkAbgBnAEkARAApACIAIAAtAE4AYQBtAGUAIAAnAE0AVABVACcAIAAtAFAAcgBvAHAAZQByAHQAeQBUAHkAcABlACAARABXAE8AUgBEACAALQBWAGEAbAB1AGUAIAAxADQANAAwAH0A | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2204 | "C:\Windows\System32\netsh.exe" interface tcp set heuristics ws=disabled | C:\Windows\System32\netsh.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2856 | "C:\Windows\System32\reg.exe" add HKLM\Software\ttl /v ttl /t REG_DWORD /d 0x40 /f | C:\Windows\System32\reg.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3364 | "C:\Windows\System32\reg.exe" add HKLM\SYSTEM\CurrentControlSet\services\Tcpip\Parameters /v DefaultTTL /t REG_DWORD /d 0x40 /f | C:\Windows\System32\reg.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3472 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\02sall.js" | C:\Windows\System32\WScript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
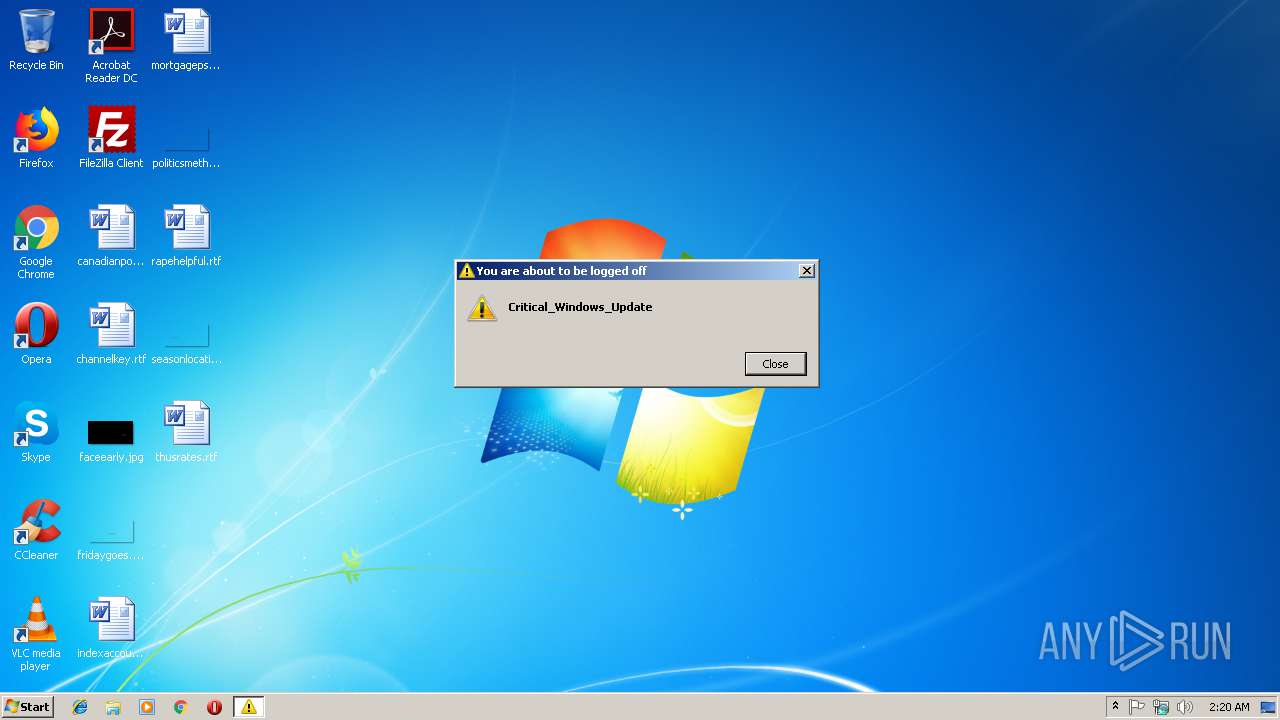
| 3776 | "C:\Windows\System32\shutdown.exe" /r /f /c "Critical_Windows_Update" /t 120 | C:\Windows\System32\shutdown.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shutdown and Annotation Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
470
Read events
326
Write events
143
Delete events
1
Modification events
| (PID) Process: | (3472) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3472) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3472) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3472) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3472) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3472) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3472) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3472) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3472) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3472) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3472 | WScript.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\Windows6.1-KB3033929-x86[1].msu | — | |
MD5:— | SHA256:— | |||
| 3472 | WScript.exe | C:\Users\admin\AppData\Local\VirtualStore\Windows\System32\IsAdm.txt | — | |
MD5:— | SHA256:— | |||
| 1236 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\1156TSFOZ1LBT209DVXX.temp | — | |
MD5:— | SHA256:— | |||
| 1236 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF1b21ad.TMP | binary | |
MD5:— | SHA256:— | |||
| 1236 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3472 | WScript.exe | 2.18.233.19:443 | download.microsoft.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3472 | WScript.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |