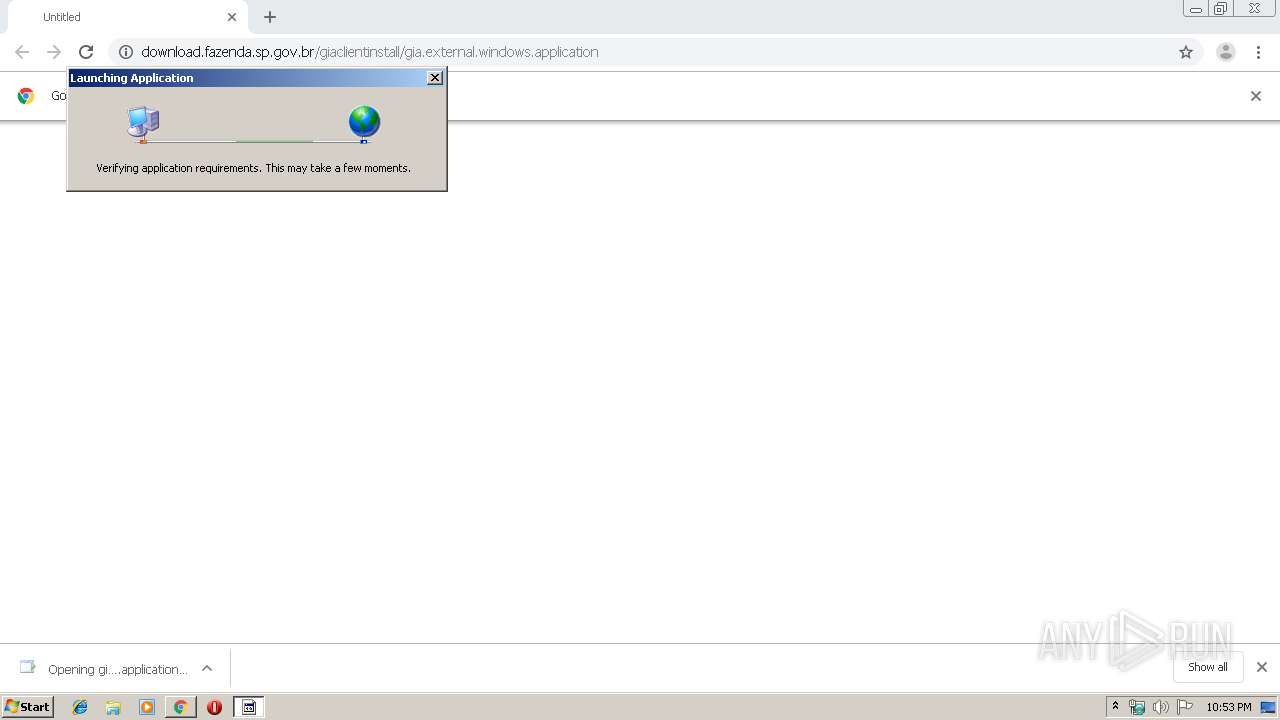
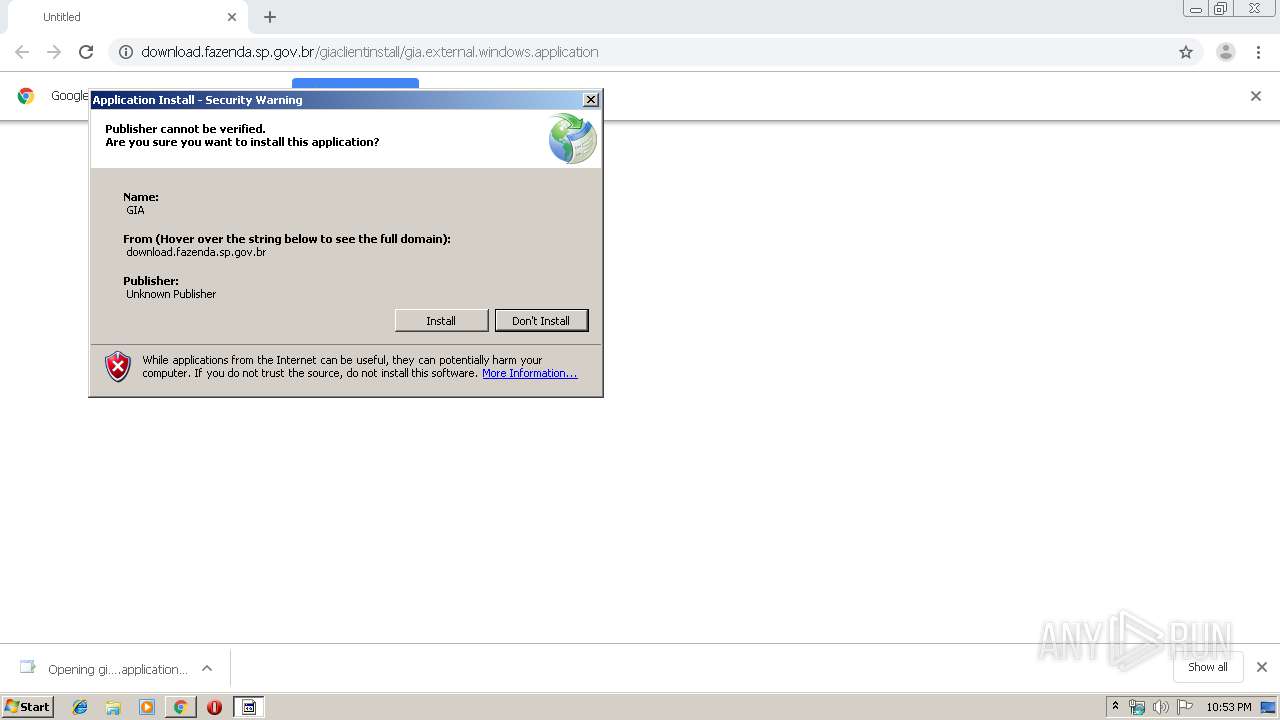
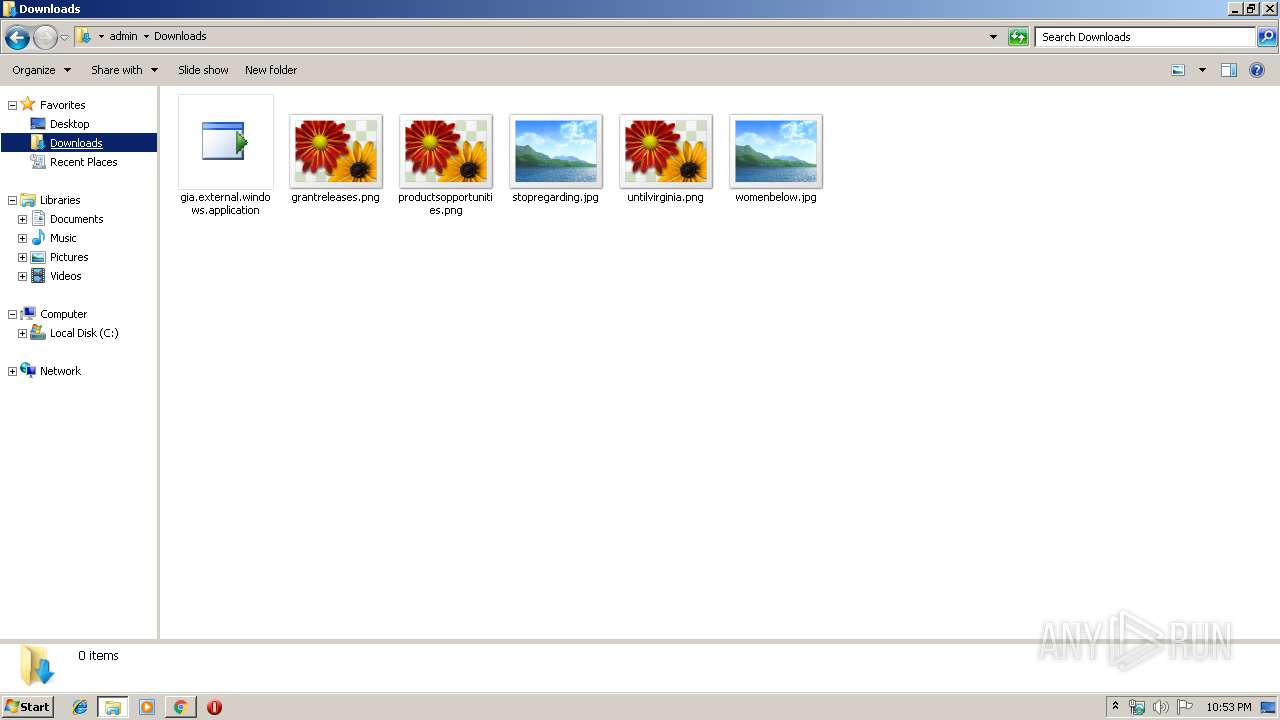
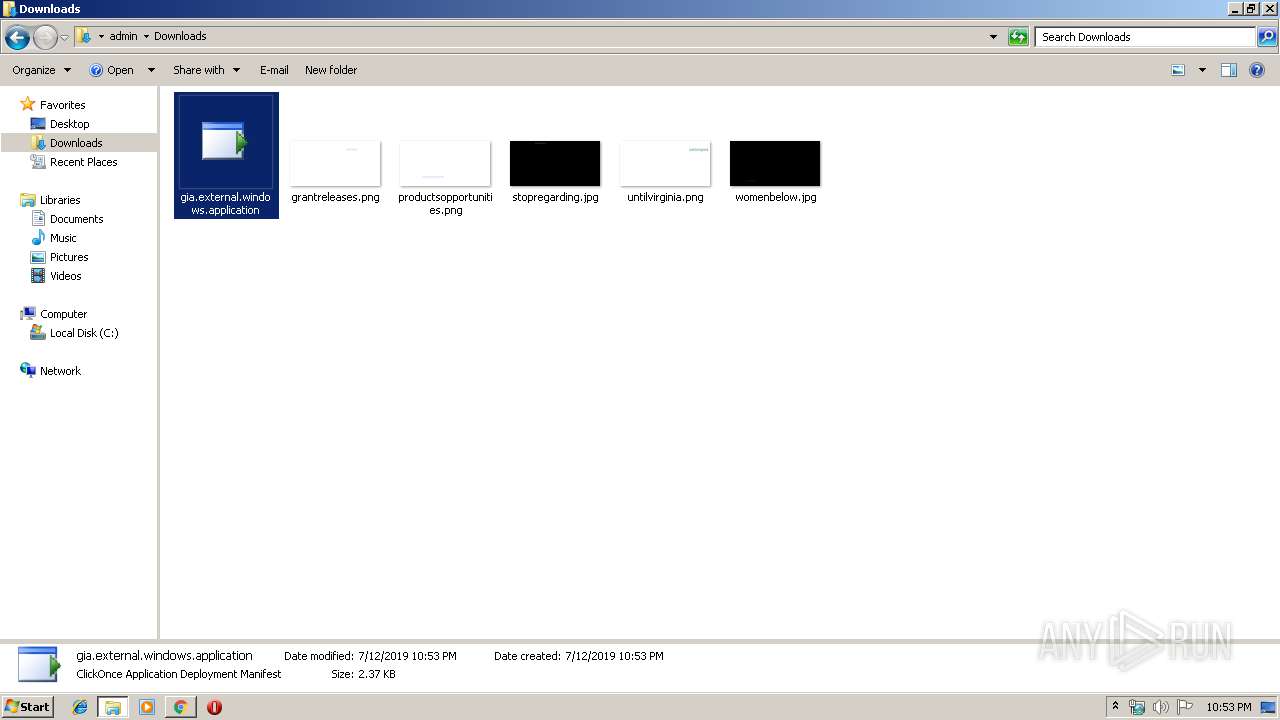
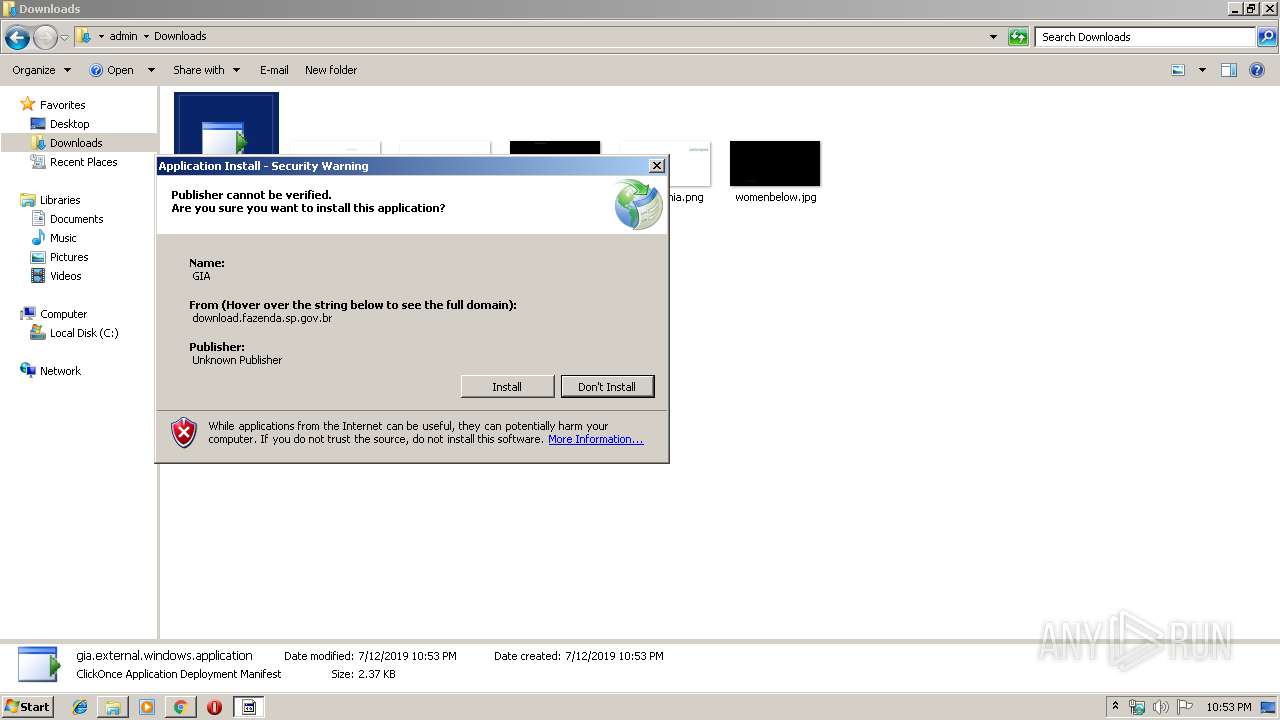
| URL: | http://download.fazenda.sp.gov.br/giaclientinstall/gia.external.windows.application |
| Full analysis: | https://app.any.run/tasks/52f1bd4d-a737-42b7-94fd-7551c77e86aa |
| Verdict: | No threats detected |
| Analysis date: | July 12, 2019, 21:52:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 2B5052F7C7D9EC27D80719434CD9FCD3 |
| SHA1: | CC46E9F473B466DD86E458F14993A6635A2DABB0 |
| SHA256: | B7E65790C3FBF162BCDFD232FAE5F478EE8676E812FCE3F8FD8A8D604ACA9DAE |
| SSDEEP: | 3:N1KaKElYo1i+DJEaAMgFSYVCdMQn:Ca5TkMJELMKHVCR |
MALICIOUS
No malicious indicators.SUSPICIOUS
Uses RUNDLL32.EXE to load library
- chrome.exe (PID: 3064)
Reads Internet Cache Settings
- dfsvc.exe (PID: 2804)
Reads Environment values
- dfsvc.exe (PID: 2804)
Reads internet explorer settings
- dfsvc.exe (PID: 2804)
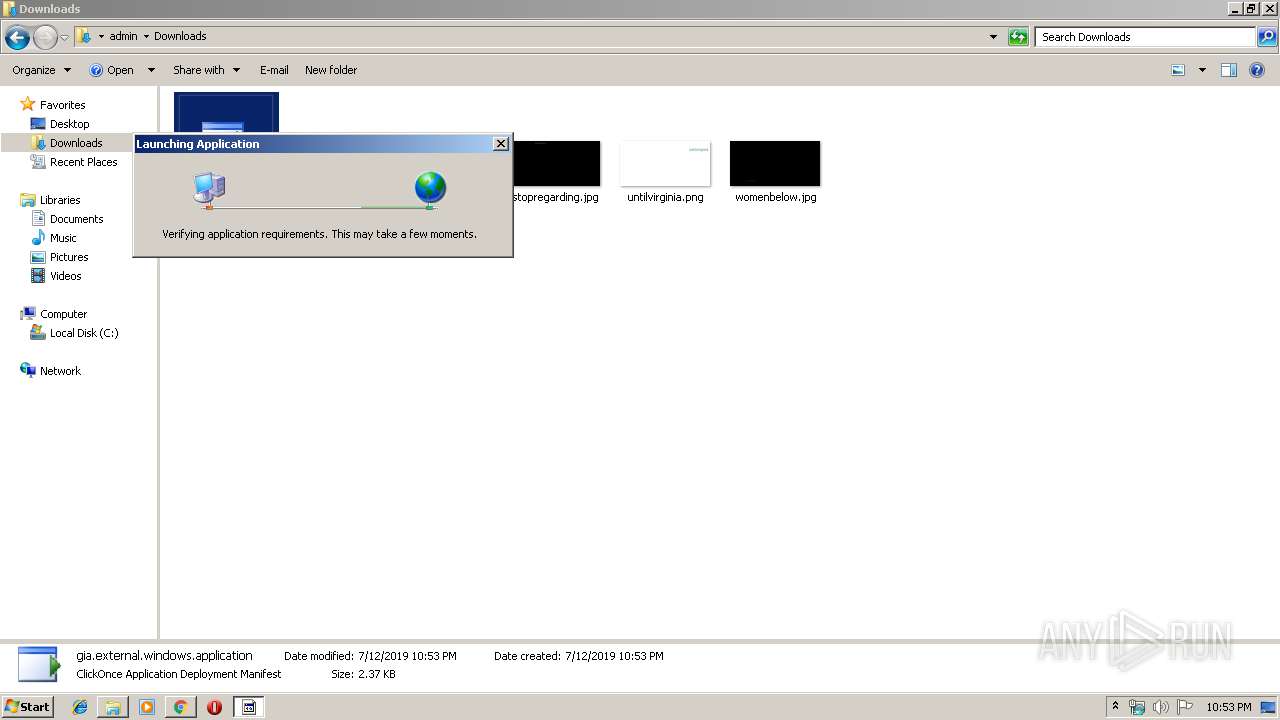
Starts Internet Explorer
- dfsvc.exe (PID: 2804)
INFO
Creates files in the user directory
- chrome.exe (PID: 3064)
- iexplore.exe (PID: 1676)
Reads Internet Cache Settings
- chrome.exe (PID: 3064)
- iexplore.exe (PID: 1676)
Application launched itself
- chrome.exe (PID: 3064)
- iexplore.exe (PID: 3468)
Manual execution by user
- explorer.exe (PID: 2588)
- rundll32.exe (PID: 3904)
Reads internet explorer settings
- iexplore.exe (PID: 1676)
Reads settings of System Certificates
- iexplore.exe (PID: 3468)
- chrome.exe (PID: 2776)
Changes internet zones settings
- iexplore.exe (PID: 3468)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
53
Monitored processes
17
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1676 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3468 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1028,1671460280302638083,9803271239349855837,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=14713255041997594370 --mojo-platform-channel-handle=1020 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2588 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,1671460280302638083,9803271239349855837,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9618853461675033472 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2216 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2732 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1028,1671460280302638083,9803271239349855837,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=13263758939825435845 --mojo-platform-channel-handle=3788 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2776 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,1671460280302638083,9803271239349855837,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=2281898104394133816 --mojo-platform-channel-handle=1600 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2804 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\dfsvc.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\dfsvc.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: ClickOnce Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 2860 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,1671460280302638083,9803271239349855837,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14220118948961374340 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2436 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3004 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,1671460280302638083,9803271239349855837,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=13212190263954115961 --mojo-platform-channel-handle=1136 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3068 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 596
Read events
1 415
Write events
174
Delete events
7
Modification events
| (PID) Process: | (3012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3064-13207441998420125 |
Value: 259 | |||
| (PID) Process: | (3064) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3064) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3064) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3064) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3064) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3064) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3064) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3064) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3064) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3064-13207441998420125 |
Value: 259 | |||
Executable files
0
Suspicious files
11
Text files
184
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3064 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\734791da-c6e4-4782-9e7a-3aad9cbd18b4.tmp | — | |
MD5:— | SHA256:— | |||
| 3064 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3064 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3064 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF1548ab.TMP | text | |
MD5:— | SHA256:— | |||
| 3064 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3064 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF1548ca.TMP | text | |
MD5:— | SHA256:— | |||
| 3064 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3064 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3064 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF1548ab.TMP | text | |
MD5:— | SHA256:— | |||
| 3064 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\MANIFEST-000001 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
29
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1676 | iexplore.exe | GET | 302 | 201.55.62.48:80 | http://www.fazenda.sp.gov.br/download/download_gia0801.shtm | BR | html | 249 b | whitelisted |
2804 | dfsvc.exe | GET | 200 | 201.55.60.34:80 | http://download.fazenda.sp.gov.br/GiaClientInstall/Application%20Files/GIA.External.Windows_8_0_1_155/GIA.External.Windows.exe.manifest | BR | xml | 23.8 Kb | unknown |
2776 | chrome.exe | GET | 200 | 201.55.60.34:80 | http://download.fazenda.sp.gov.br/giaclientinstall/gia.external.windows.application | BR | xml | 2.37 Kb | unknown |
2804 | dfsvc.exe | GET | 200 | 201.55.60.34:80 | http://download.fazenda.sp.gov.br/GiaClientInstall/GIA.External.Windows.application | BR | xml | 2.37 Kb | unknown |
2804 | dfsvc.exe | GET | 200 | 201.55.60.34:80 | http://download.fazenda.sp.gov.br/GiaClientInstall/Application%20Files/GIA.External.Windows_8_0_1_155/GIA.External.Windows.exe.manifest | BR | xml | 23.8 Kb | unknown |
2804 | dfsvc.exe | GET | 200 | 201.55.60.34:80 | http://download.fazenda.sp.gov.br/GiaClientInstall/GIA.External.Windows.application | BR | xml | 2.37 Kb | unknown |
3468 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2776 | chrome.exe | 172.217.22.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
— | — | 216.58.207.68:443 | www.google.com | Google Inc. | US | whitelisted |
2776 | chrome.exe | 172.217.16.206:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
— | — | 216.58.210.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1676 | iexplore.exe | 201.55.62.48:80 | www.fazenda.sp.gov.br | Cia Proc. de Dados do Estado de S Paulo - Prodesp | BR | unknown |
1676 | iexplore.exe | 209.197.3.15:443 | maxcdn.bootstrapcdn.com | Highwinds Network Group, Inc. | US | whitelisted |
1676 | iexplore.exe | 104.19.196.151:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | shared |
1676 | iexplore.exe | 201.55.62.43:443 | www3.fazenda.sp.gov.br | Cia Proc. de Dados do Estado de S Paulo - Prodesp | BR | unknown |
1676 | iexplore.exe | 104.45.136.42:443 | dc.services.visualstudio.com | Microsoft Corporation | US | whitelisted |
2776 | chrome.exe | 216.58.210.14:443 | clients1.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
download.fazenda.sp.gov.br |
| unknown |
accounts.google.com |
| shared |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.fazenda.sp.gov.br |
| unknown |
www.bing.com |
| whitelisted |
portal.fazenda.sp.gov.br |
| unknown |
ajax.aspnetcdn.com |
| whitelisted |
Threats
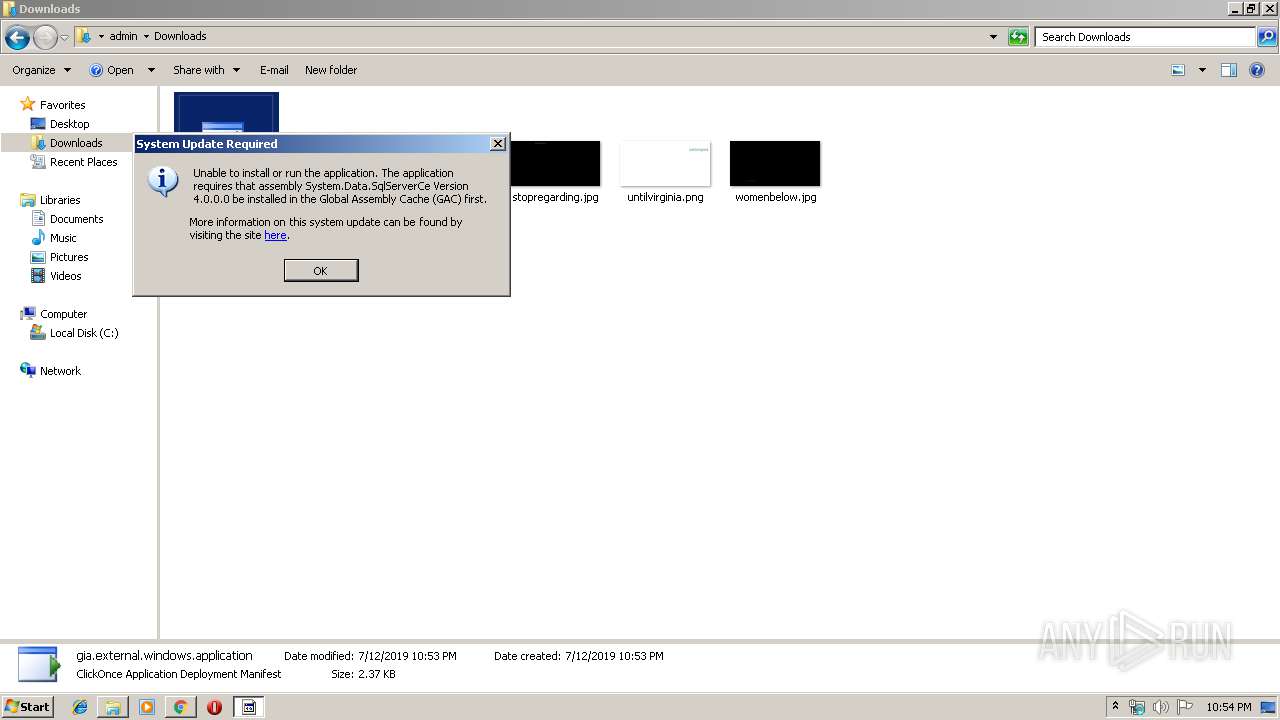
Process | Message |
|---|---|
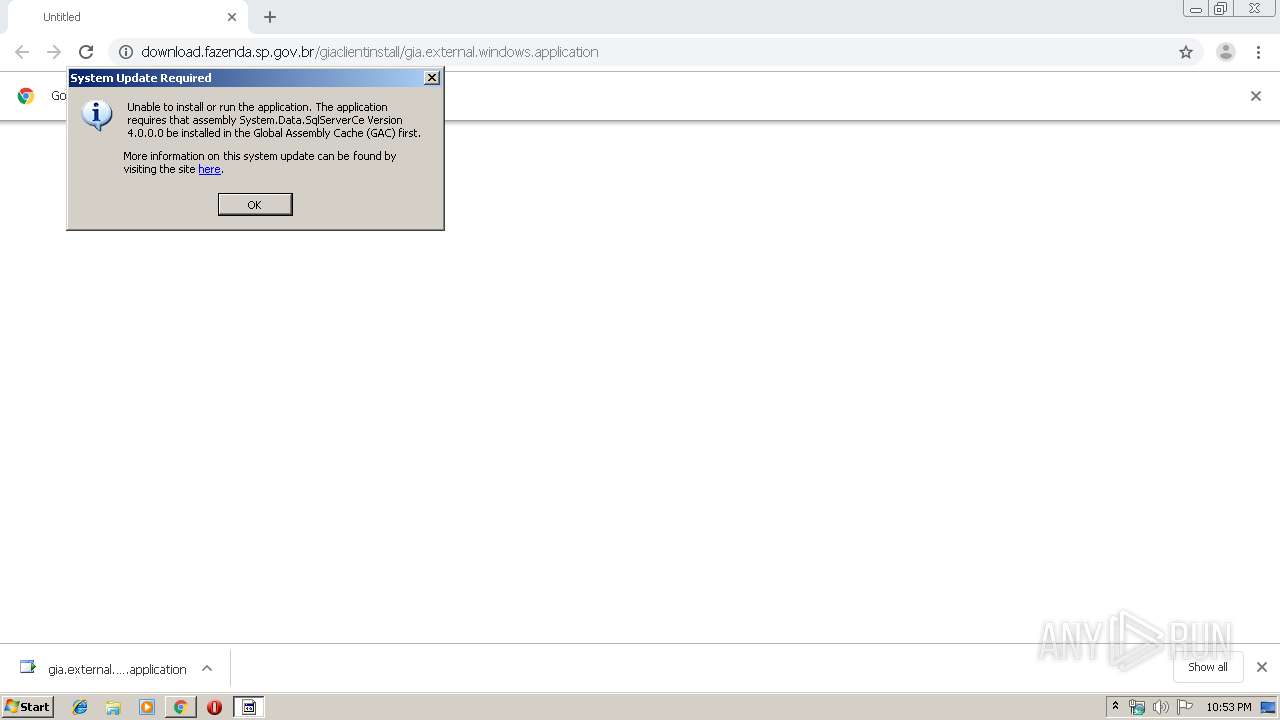
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|