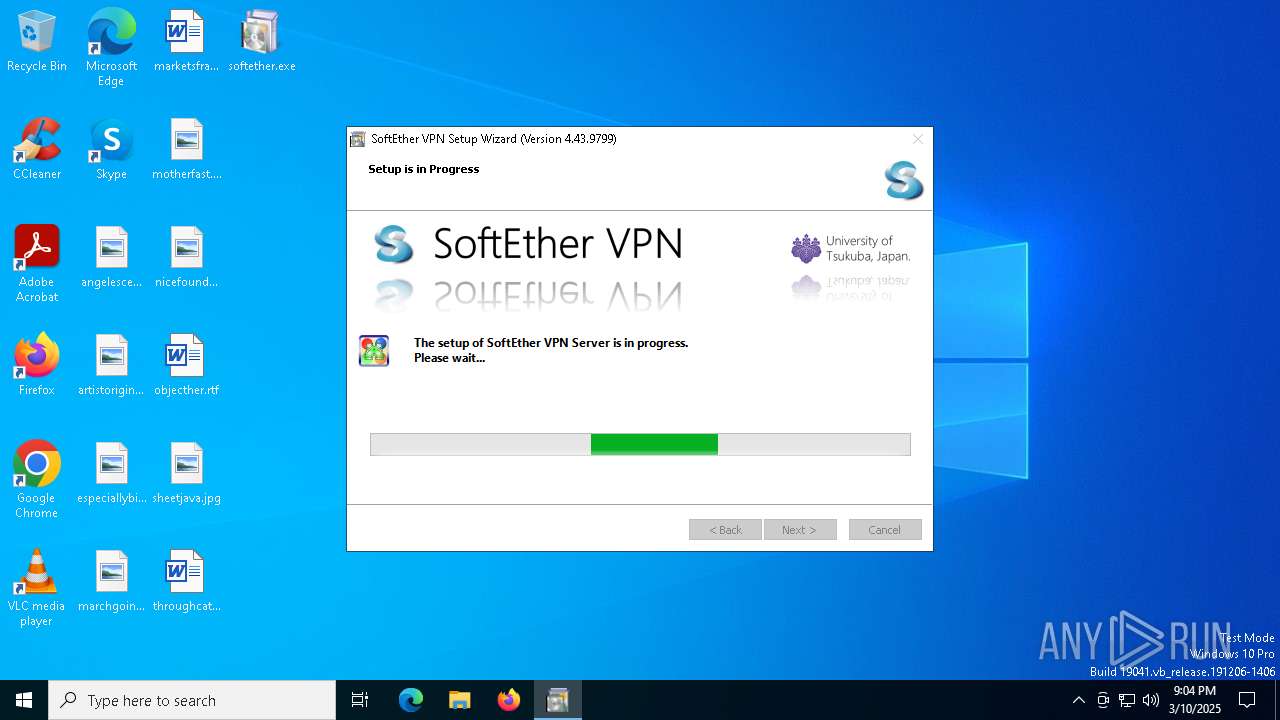
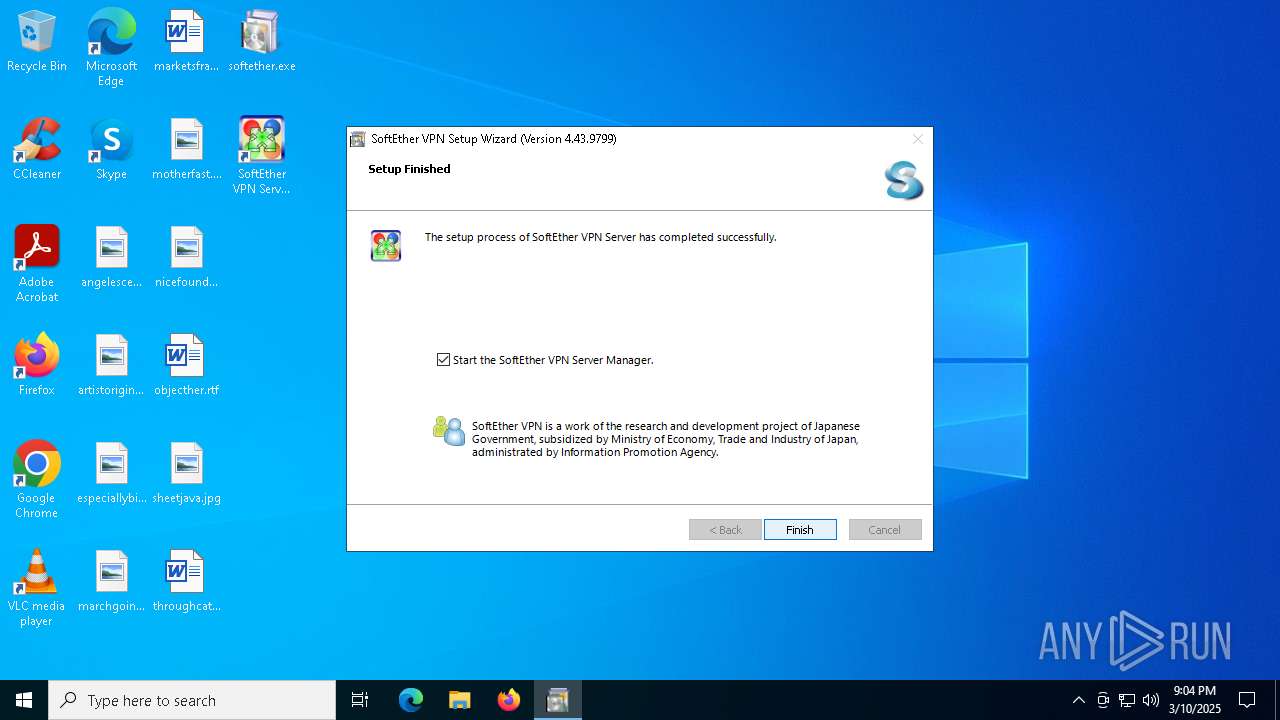
| File name: | softether.exe |
| Full analysis: | https://app.any.run/tasks/cd28b5f8-ef81-4d4d-b2ae-01e77521fd43 |
| Verdict: | Malicious activity |
| Analysis date: | March 10, 2025, 21:03:52 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | 186F4721B80F390BDF6AA14133D50F91 |
| SHA1: | 250EE62F3FAF0817DD7CAA0D9F20C1AFE6B9DC84 |
| SHA256: | B7E06A4FF2E5B5CF05F8E35F0433ECA32CAB72E1BB3D99A8E8F0F228F276E372 |
| SSDEEP: | 786432:xIAGoyXsQ8BqiszZyPxZCPe9Naw/kyKKEq9z:qAGogsVBZYZy7Cm9MyKKEqh |
MALICIOUS
Loads dropped or rewritten executable
- conhost.exe (PID: 456)
- conhost.exe (PID: 6388)
- netsh.exe (PID: 6192)
- netsh.exe (PID: 5244)
- vpnserver_x64.exe (PID: 4528)
- conhost.exe (PID: 4336)
- conhost.exe (PID: 632)
- conhost.exe (PID: 5728)
- consent.exe (PID: 2108)
- conhost.exe (PID: 1388)
- conhost.exe (PID: 6108)
- vpncmd_x64.exe (PID: 6048)
- netsh.exe (PID: 7156)
- vpnsmgr_x64.exe (PID: 5436)
- slui.exe (PID: 1348)
- conhost.exe (PID: 4152)
Accesses name of a computer manufacturer via WMI (SCRIPT)
- cscript.exe (PID: 5988)
SUSPICIOUS
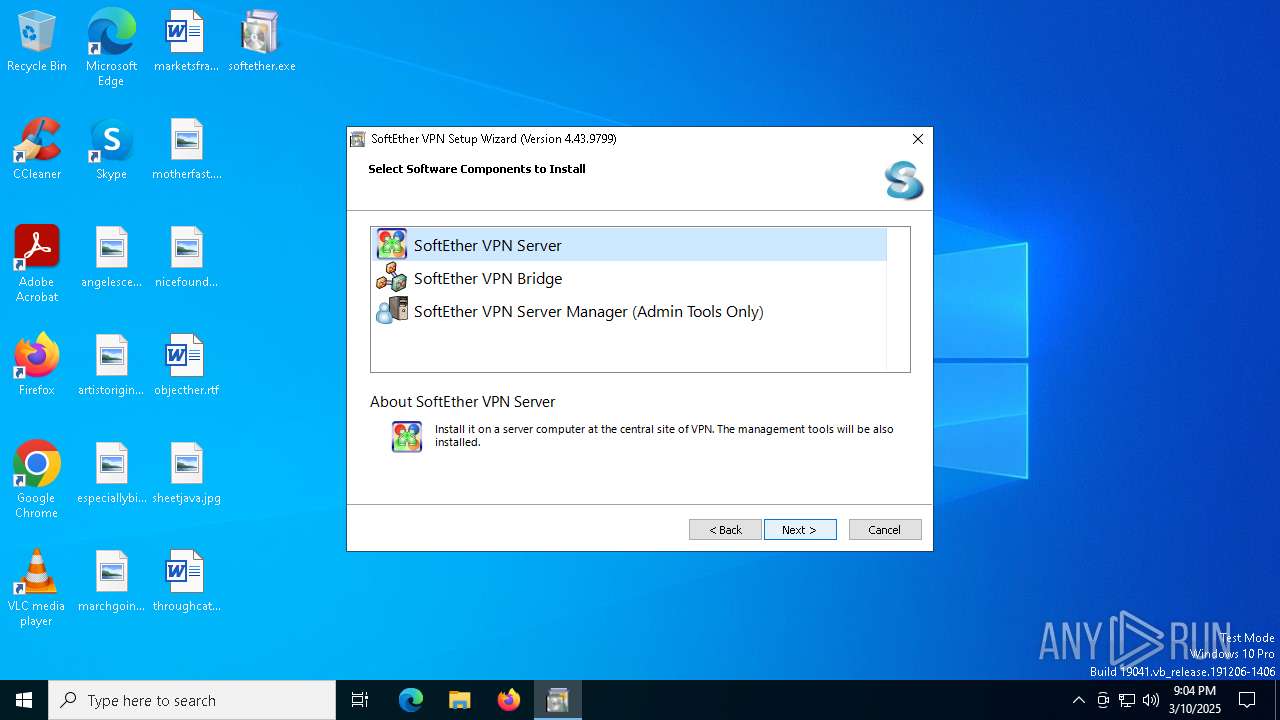
There is functionality for enable RDP (YARA)
- softether.exe (PID: 5124)
- vpnsetup.exe (PID: 2564)
- vpnsetup.exe (PID: 4652)
- vpnserver_x64.exe (PID: 4528)
- vpnsmgr_x64.exe (PID: 5436)
Reads security settings of Internet Explorer
- vpnsetup.exe (PID: 2564)
- softether.exe (PID: 5124)
Executable content was dropped or overwritten
- vpnsetup.exe (PID: 2564)
- vpnsetup.exe (PID: 4652)
- drvinst.exe (PID: 6456)
- vpnserver_x64.exe (PID: 4528)
- softether.exe (PID: 5124)
- vpncmd_x64.exe (PID: 6048)
- vpnsmgr_x64.exe (PID: 5436)
The process creates files with name similar to system file names
- softether.exe (PID: 5124)
- vpncmd_x64.exe (PID: 6048)
Application launched itself
- vpnsetup.exe (PID: 2564)
Drops a system driver (possible attempt to evade defenses)
- vpnsetup.exe (PID: 4652)
- drvinst.exe (PID: 6456)
Creates files in the driver directory
- drvinst.exe (PID: 6456)
- vpnsetup.exe (PID: 4652)
The process executes VB scripts
- vpnsetup.exe (PID: 4652)
- vpnserver_x64.exe (PID: 4528)
Suspicious use of NETSH.EXE
- vpnsetup.exe (PID: 4652)
Creates or modifies Windows services
- vpnsetup.exe (PID: 4652)
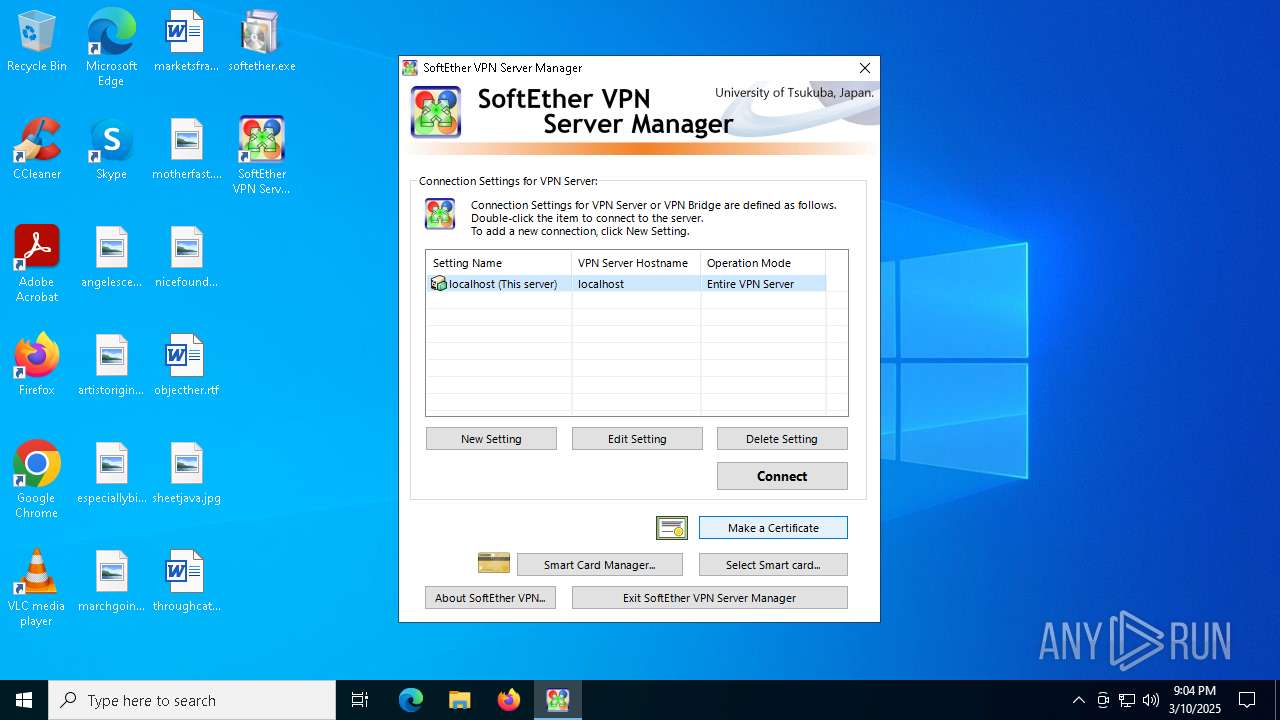
Executes as Windows Service
- vpnserver_x64.exe (PID: 4528)
Process drops legitimate windows executable
- vpnserver_x64.exe (PID: 4528)
Accesses WMI object, sets custom ImpersonationLevel (SCRIPT)
- cscript.exe (PID: 5988)
Creates a software uninstall entry
- vpnsetup.exe (PID: 4652)
INFO
Reads Environment values
- softether.exe (PID: 5124)
- vpnsetup.exe (PID: 2564)
- vpnsetup.exe (PID: 4652)
- vpnserver_x64.exe (PID: 4528)
- vpncmd_x64.exe (PID: 6048)
- vpnsmgr_x64.exe (PID: 5436)
The sample compiled with japanese language support
- softether.exe (PID: 5124)
- vpnsetup.exe (PID: 4652)
- drvinst.exe (PID: 6456)
- vpnsetup.exe (PID: 2564)
- vpncmd_x64.exe (PID: 6048)
- vpnsmgr_x64.exe (PID: 5436)
Checks supported languages
- vpnsetup.exe (PID: 2564)
- vpnsetup.exe (PID: 4652)
- drvinst.exe (PID: 6456)
- vpnserver_x64.exe (PID: 4528)
- softether.exe (PID: 5124)
- vpnsmgr_x64.exe (PID: 5436)
- vpncmd_x64.exe (PID: 6048)
Reads the machine GUID from the registry
- vpnsetup.exe (PID: 2564)
- softether.exe (PID: 5124)
- vpnsetup.exe (PID: 4652)
- drvinst.exe (PID: 6456)
- vpnserver_x64.exe (PID: 4528)
- vpncmd_x64.exe (PID: 6048)
- vpnsmgr_x64.exe (PID: 5436)
Process checks computer location settings
- vpnsetup.exe (PID: 2564)
- softether.exe (PID: 5124)
Reads the computer name
- vpnsetup.exe (PID: 2564)
- softether.exe (PID: 5124)
- vpnsetup.exe (PID: 4652)
- drvinst.exe (PID: 6456)
- vpnserver_x64.exe (PID: 4528)
- vpncmd_x64.exe (PID: 6048)
- vpnsmgr_x64.exe (PID: 5436)
Create files in a temporary directory
- softether.exe (PID: 5124)
- vpnsetup.exe (PID: 4652)
- vpncmd_x64.exe (PID: 6048)
- vpnsmgr_x64.exe (PID: 5436)
- vpnsetup.exe (PID: 2564)
Reads the software policy settings
- consent.exe (PID: 2108)
- drvinst.exe (PID: 6456)
- slui.exe (PID: 1348)
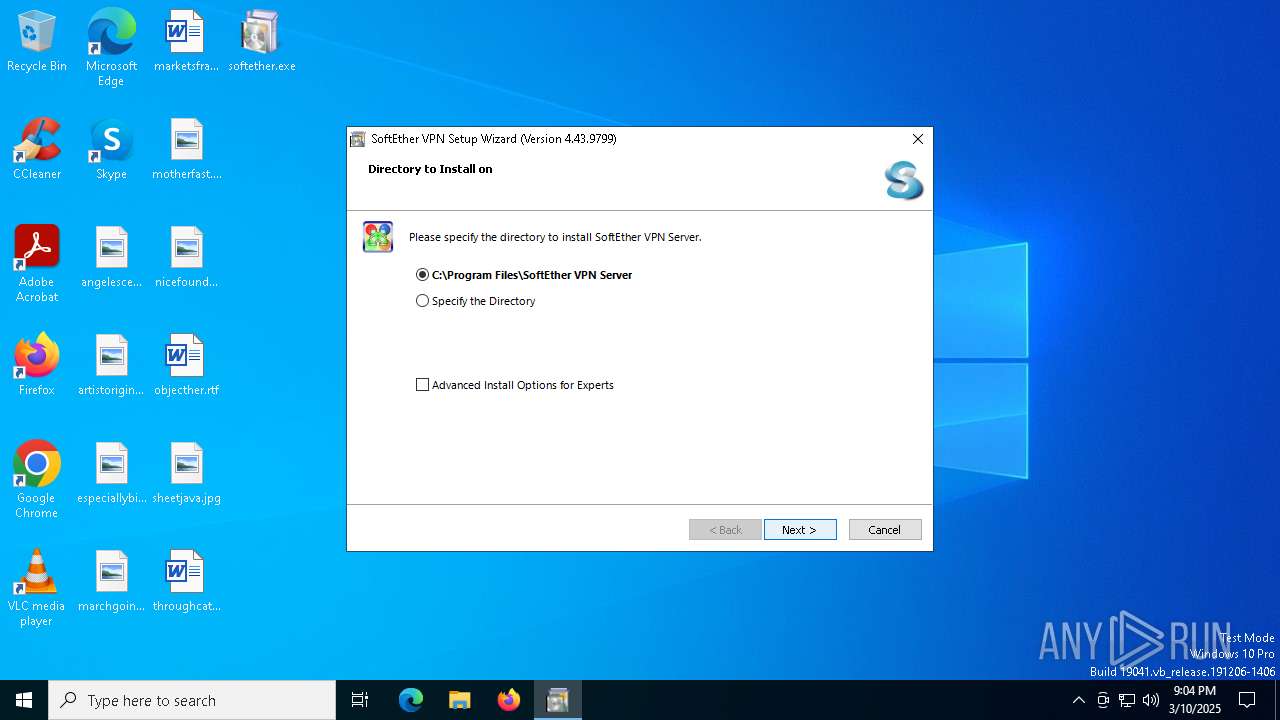
Creates files in the program directory
- vpnsetup.exe (PID: 4652)
- vpnserver_x64.exe (PID: 4528)
Reads security settings of Internet Explorer
- cscript.exe (PID: 2100)
- cscript.exe (PID: 4448)
- cscript.exe (PID: 3676)
Disables trace logs
- netsh.exe (PID: 5244)
- netsh.exe (PID: 7156)
- netsh.exe (PID: 6192)
The sample compiled with english language support
- vpnserver_x64.exe (PID: 4528)
Reads Windows Product ID
- vpnserver_x64.exe (PID: 4528)
- vpncmd_x64.exe (PID: 6048)
- vpnsmgr_x64.exe (PID: 5436)
Checks proxy server information
- slui.exe (PID: 1348)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:08:31 01:51:48+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 4411904 |
| InitializedDataSize: | 54450688 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x41854b |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.43.0.9799 |
| ProductVersionNumber: | 4.43.0.9799 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Japanese |
| CharacterSet: | Unicode |
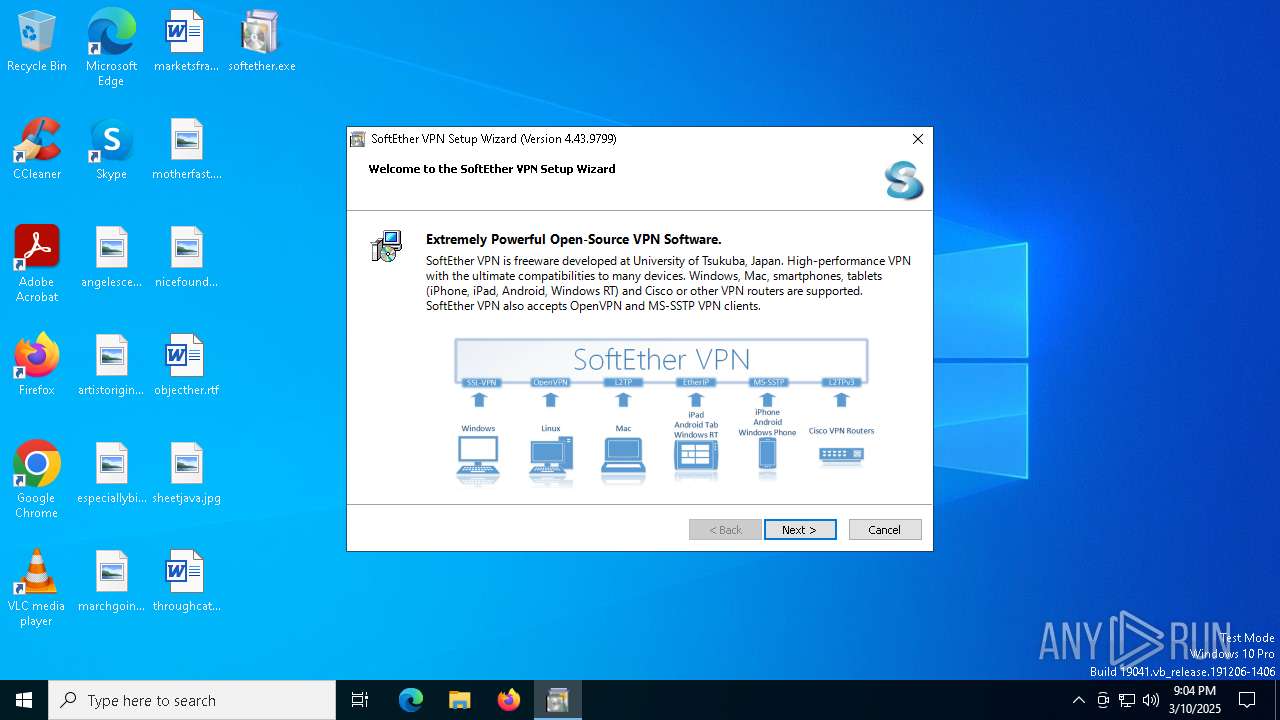
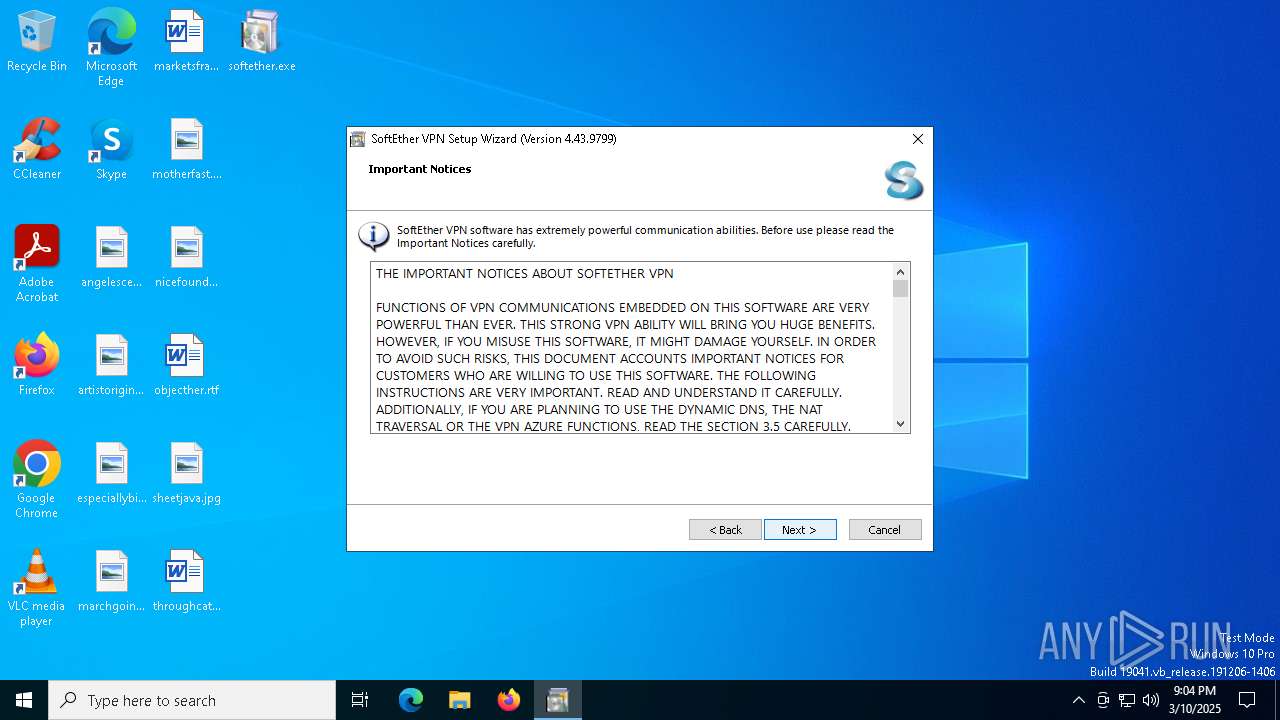
| CompanyName: | SoftEther VPN Project at University of Tsukuba, Japan. |
| FileDescription: | SoftEther VPN |
| FileVersion: | 4, 43, 0, 9799 |
| InternalName: | vpnsetup |
| LegalCopyright: | Copyright (C) 2012-2023 SoftEther VPN Project. All Rights Reserved. |
| LegalTrademarks: | SoftEther(R) is a registered trademark of SoftEther Corporation in Japan, United Status and People's Republic of China. SoftEther Corporation is a company founded at University of Tsukuba, Japan in 2004. |
| OriginalFileName: | vpnsetup.exe |
| ProductName: | SoftEther VPN |
| ProductVersion: | 4, 43, 0, 9799 |
Total processes
145
Monitored processes
25
Malicious processes
7
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1280 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cscript.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1348 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1388 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | netsh.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2100 | C:\WINDOWS\system32\cscript.exe "C:\Users\admin\AppData\Local\Temp\VPN_AD42\winfire_B93DC3223B44.vbs" | C:\Windows\SysWOW64\cscript.exe | — | vpnsetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 2108 | consent.exe 4916 664 0000021B57606940 | C:\Windows\System32\consent.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Consent UI for administrative applications Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2564 | "C:\Users\admin\AppData\Local\Temp\VPN_7032\vpnsetup.exe" /CALLERSFXPATH:"C:\Users\admin\AppData\Local\Temp\VPN_7032\installer.cache" /ISEASYINSTALLER:0 | C:\Users\admin\AppData\Local\Temp\VPN_7032\vpnsetup.exe | softether.exe | ||||||||||||
User: admin Company: SoftEther VPN Project at University of Tsukuba, Japan. Integrity Level: MEDIUM Description: SoftEther VPN Exit code: 0 Version: 4, 43, 0, 9799 Modules
| |||||||||||||||
| 3676 | C:\WINDOWS\system32\cscript.exe "C:\Users\admin\AppData\Local\Temp\VPN_AD42\winfire_F2FD62F5B0D5.vbs" | C:\Windows\SysWOW64\cscript.exe | — | vpnsetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 4152 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | CompatTelRunner.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
17 449
Read events
17 406
Write events
39
Delete events
4
Modification events
| (PID) Process: | (4652) vpnsetup.exe | Key: | HKEY_LOCAL_MACHINE |
| Operation: | write | Name: | Vpn_Check_Admin_Key_4003674586 |
Value: 7DD3EDA3F408497C1CF8926A16F77B079C9F0A06B8C42A6C49A72153B7BF6837 | |||
| (PID) Process: | (4652) vpnsetup.exe | Key: | HKEY_LOCAL_MACHINE |
| Operation: | delete value | Name: | Vpn_Check_Admin_Key_4003674586 |
Value: 퍽ꏭࣴ籉檒ݻ龜؊쒸氪ꝉ匡뾷㝨 | |||
| (PID) Process: | (4652) vpnsetup.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\SetupapiLogStatus |
| Operation: | write | Name: | setupapi.dev.log |
Value: 4096 | |||
| (PID) Process: | (4652) vpnsetup.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Network\TemporaryInstallStage|6808|SeLow|{FEE27966-D653-4D74-847F-5544508A807A}\Ndi |
| Operation: | write | Name: | Service |
Value: SeLow | |||
| (PID) Process: | (4652) vpnsetup.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Network\TemporaryInstallStage|6808|SeLow|{FEE27966-D653-4D74-847F-5544508A807A}\Ndi |
| Operation: | write | Name: | HelpText |
Value: A lightweight helper kernel-mode module for PacketiX VPN / SoftEther VPN. | |||
| (PID) Process: | (4652) vpnsetup.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Network\TemporaryInstallStage|6808|SeLow|{FEE27966-D653-4D74-847F-5544508A807A}\Ndi\Interfaces |
| Operation: | write | Name: | UpperRange |
Value: noupper | |||
| (PID) Process: | (4652) vpnsetup.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Network\TemporaryInstallStage|6808|SeLow|{FEE27966-D653-4D74-847F-5544508A807A}\Ndi\Interfaces |
| Operation: | write | Name: | LowerRange |
Value: ndis5,ndis4 | |||
| (PID) Process: | (4652) vpnsetup.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\GroupOrderList |
| Operation: | write | Name: | PNP_TDI |
Value: 080000000500000001000000020000000300000004000000060000000700000008000000 | |||
| (PID) Process: | (4652) vpnsetup.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\SeLow |
| Operation: | write | Name: | SlVersion_Win10 |
Value: 48 | |||
| (PID) Process: | (4652) vpnsetup.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\SeLow |
| Operation: | write | Name: | Start |
Value: 1 | |||
Executable files
28
Suspicious files
27
Text files
11
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5124 | softether.exe | C:\Users\admin\AppData\Local\Temp\VPN_7032\hamcore.se2 | — | |
MD5:— | SHA256:— | |||
| 5124 | softether.exe | C:\Users\admin\AppData\Local\Temp\VPN_7032\installer.cache | — | |
MD5:— | SHA256:— | |||
| 5124 | softether.exe | C:\Users\admin\AppData\Local\Temp\VPN_7032\vpnsetup_x64.exe | executable | |
MD5:43017413E07BC2E6BBD2E55189666A4A | SHA256:2C0E307879F381C10D48921DB2AB38A69FAC06535711774035DE7AC58F276FA9 | |||
| 5124 | softether.exe | C:\Users\admin\AppData\Local\Temp\VPN_7032\vpncmd.exe | executable | |
MD5:C0847C1AA7C92A24CF477FEE38CF3990 | SHA256:FB919F469214A11D98F5168CC7F50A062B9F6F483753B3E2C909829B090DA194 | |||
| 5124 | softether.exe | C:\Users\admin\AppData\Local\Temp\VPN_7032\vpnsetup.exe | executable | |
MD5:4E0AE023B67CEE4B5A1EC15151757573 | SHA256:0A45AD33F8BBA71F69213DFEE21CF4472D4888642F4CB108A505FB686A575586 | |||
| 5124 | softether.exe | C:\Users\admin\AppData\Local\Temp\VPN_7032\vpnserver_x64.exe | executable | |
MD5:45E50E7975374C3E8DAA0C46B9289D7E | SHA256:FA10F23220AB85FECC7F351F97FB6F56F3BE3DB587F5E0BA9A4069697279C774 | |||
| 5124 | softether.exe | C:\Users\admin\AppData\Local\Temp\VPN_7032\vpncmd_x64.exe | executable | |
MD5:3744B85D67545C8DD8067395B314037C | SHA256:8315D1CDB7BFE13E3FD03517307A389D89DF52AAA5C9ED606ABD0EA40BF8D2A1 | |||
| 5124 | softether.exe | C:\Users\admin\AppData\Local\Temp\VPN_7032\vpnbridge_x64.exe | executable | |
MD5:F333BCC066C69BD98F754E4870A85B95 | SHA256:4F9D9A6CBA88832FCB7CFB845472B63FF15CB9B417F4F02CB8086552C19CEFFC | |||
| 2564 | vpnsetup.exe | C:\Users\admin\AppData\Local\Temp\VPN_7032\lang.config | text | |
MD5:233A7DF4DE14FE71D5A8391429C64F3B | SHA256:198A807286EFE5D84BCCCD01CA6D2E4B71DD0B4024919406395483117B745B81 | |||
| 5124 | softether.exe | C:\Users\admin\AppData\Local\Temp\VPN_7032\vpnbridge.exe | executable | |
MD5:96E5AC9FAD4B7A0824BAF38D7010619E | SHA256:F7C892710FE003F5386AACD7F17DDD169ECD28E4C239331D72509E5928D39CD2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
24
DNS requests
44
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4528 | vpnserver_x64.exe | GET | 200 | 103.41.63.79:80 | http://get-my-ip.ddns.softether-network.net/ddns/getmyip.ashx?v=17393608821649943909 | unknown | — | — | unknown |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | — | — | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4528 | vpnserver_x64.exe | 130.158.6.60:5004 | x2.x9.servers.nat-traversal.softether-network.net | — | — | unknown |
4528 | vpnserver_x64.exe | 184.24.77.24:80 | www.msftncsi.com | Akamai International B.V. | DE | whitelisted |
4528 | vpnserver_x64.exe | 103.41.63.66:443 | xf.x3.servers.ddns.softether-network.net | SoftEther Corporation | JP | unknown |
4528 | vpnserver_x64.exe | 103.41.63.79:80 | get-my-ip.ddns.softether-network.net | SoftEther Corporation | JP | unknown |
5436 | vpnsmgr_x64.exe | 130.158.6.62:443 | update-check.softether-network.net | University of Tsukuba | JP | unknown |
2284 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
keepalive.softether.org |
| whitelisted |
xf.x3.servers.ddns.softether-network.net |
| unknown |
x2.x9.servers.nat-traversal.softether-network.net |
| unknown |
www.msftncsi.com |
| whitelisted |
xf.x3.servers-v6.ddns.softether-network.net |
| unknown |
get-my-ip.ddns.softether-network.net |
| unknown |
get-my-ip-v6.ddns.softether-network.net |
| unknown |
update-check.softether-network.net |
| unknown |