| File name: | 0.file |
| Full analysis: | https://app.any.run/tasks/ea5886c7-9b77-4186-8b72-93180a59cd31 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 09, 2019, 19:05:56 |
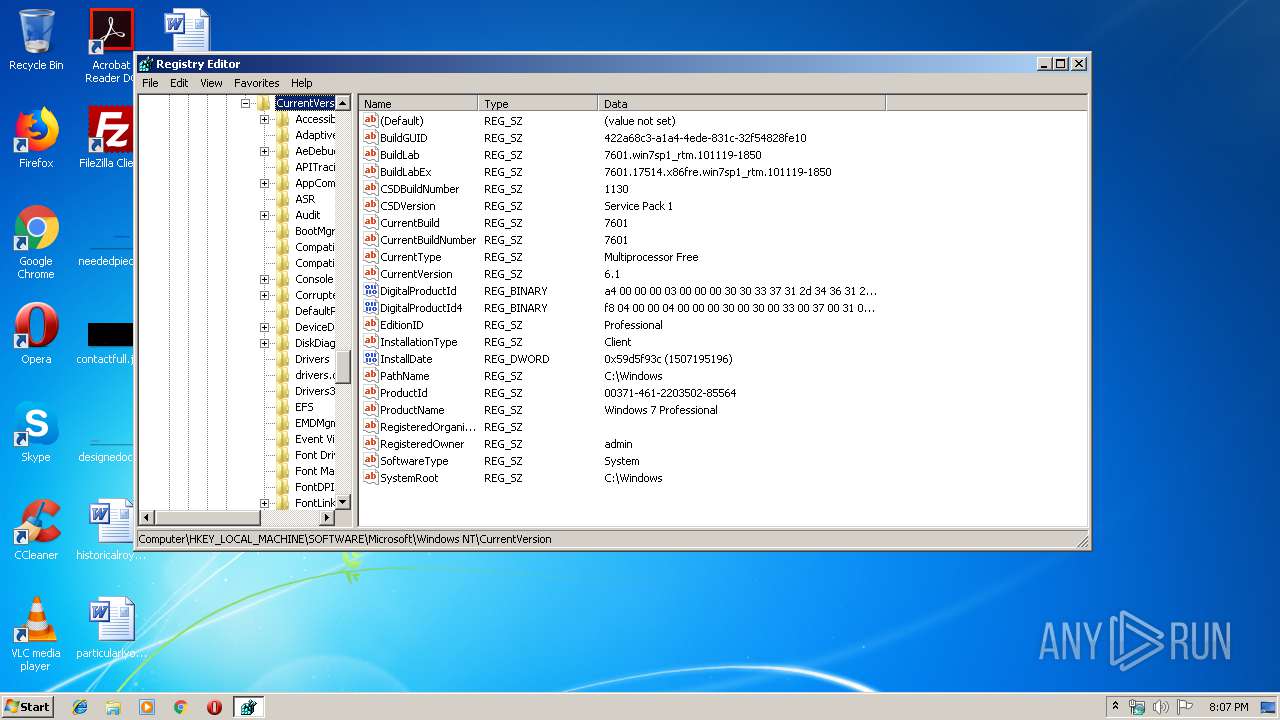
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | CB87DF0D5FCA2353D959B869151D1F86 |
| SHA1: | 42AB8941D7B6D54AE9FDB8A268716905FD9412F4 |
| SHA256: | B7CA386A1E03FADF8FF0BAB1124996333E09B1947C1076C3955785CF719DEF0B |
| SSDEEP: | 1536:PwApCnoiqMGv0uANCExj9oHhN47EF1bbk+oola0nM1QvBaijjgGd8ZSgT0rZ1trg:PwB9gUloBgubbdoolaYVjQJkaQRohMA |
MALICIOUS
Changes the autorun value in the registry
- msptermsizes.exe (PID: 3620)
- msptermsizes.exe (PID: 3008)
EMOTET was detected
- msptermsizes.exe (PID: 3620)
- msptermsizes.exe (PID: 3008)
Emotet process was detected
- dgoxs.exe (PID: 3024)
- 0.file.exe (PID: 3740)
Connects to CnC server
- msptermsizes.exe (PID: 3008)
- msptermsizes.exe (PID: 3620)
Application was dropped or rewritten from another process
- DGoxS.exe (PID: 2472)
- dgoxs.exe (PID: 3024)
- msptermsizes.exe (PID: 2316)
- msptermsizes.exe (PID: 3008)
SUSPICIOUS
Starts itself from another location
- 0.file.exe (PID: 3740)
- dgoxs.exe (PID: 3024)
Executable content was dropped or overwritten
- msptermsizes.exe (PID: 3620)
- dgoxs.exe (PID: 3024)
- 0.file.exe (PID: 3740)
Connects to SMTP port
- msptermsizes.exe (PID: 3008)
Connects to unusual port
- msptermsizes.exe (PID: 3008)
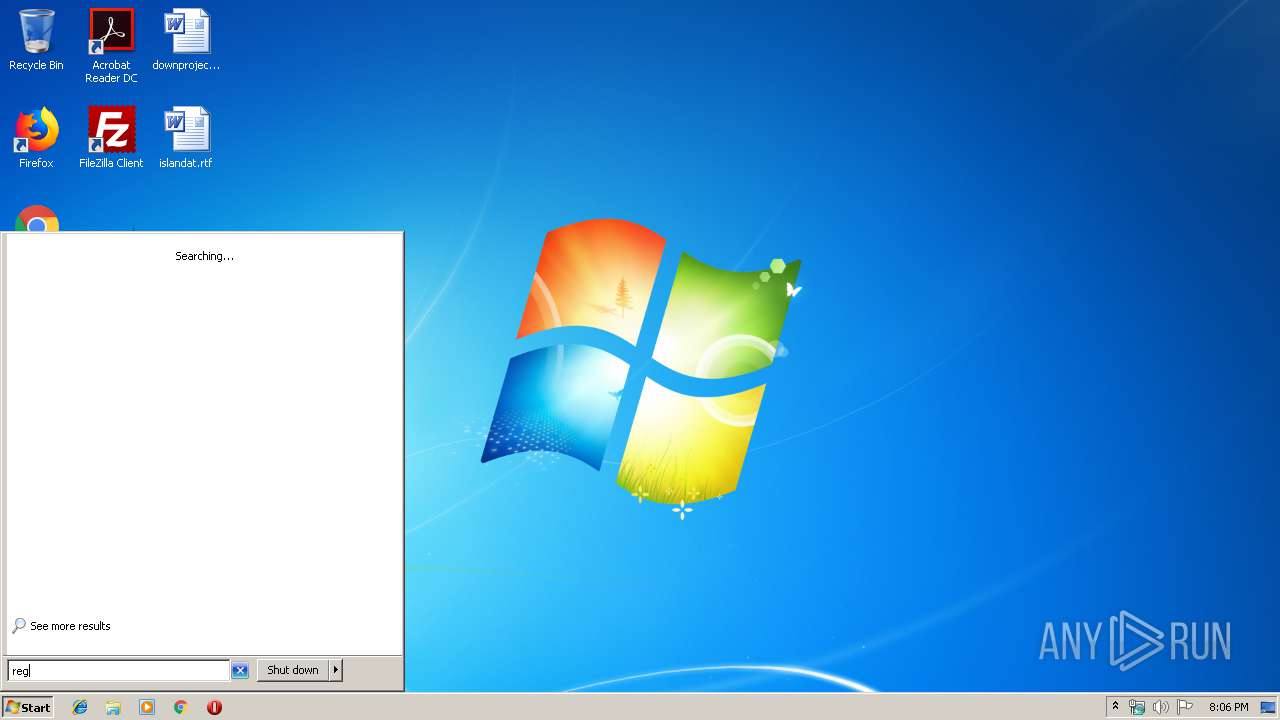
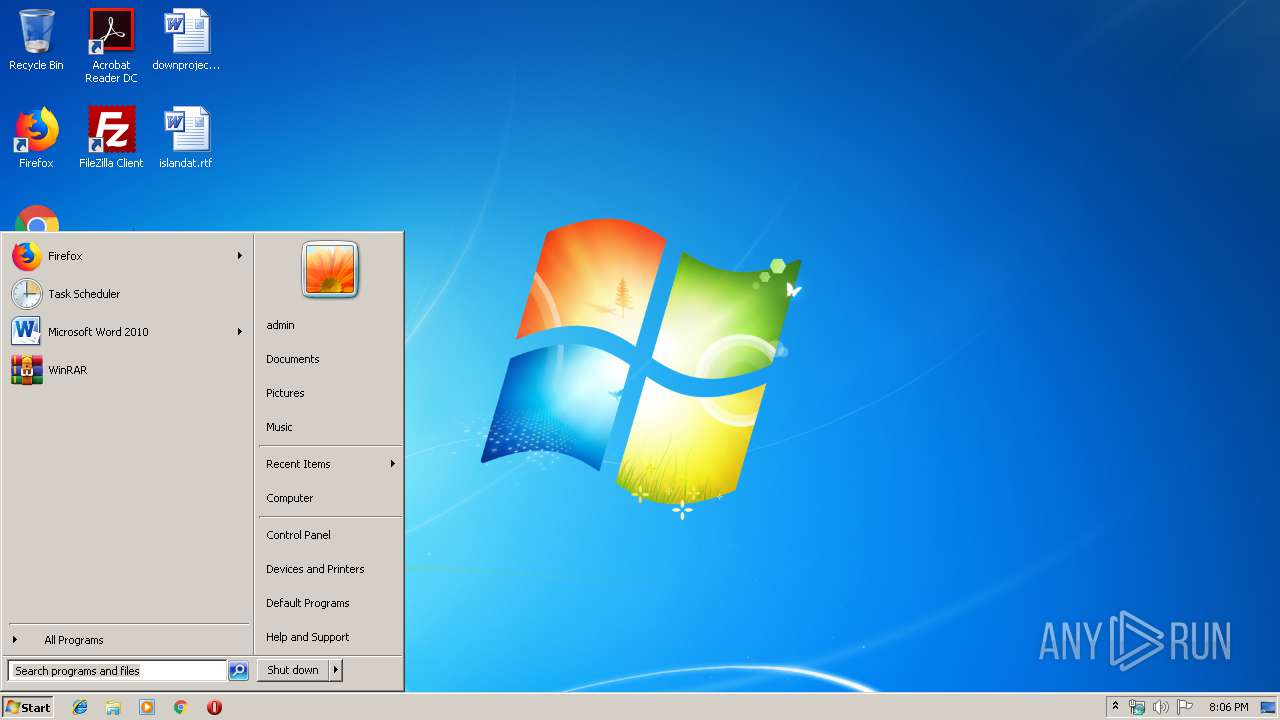
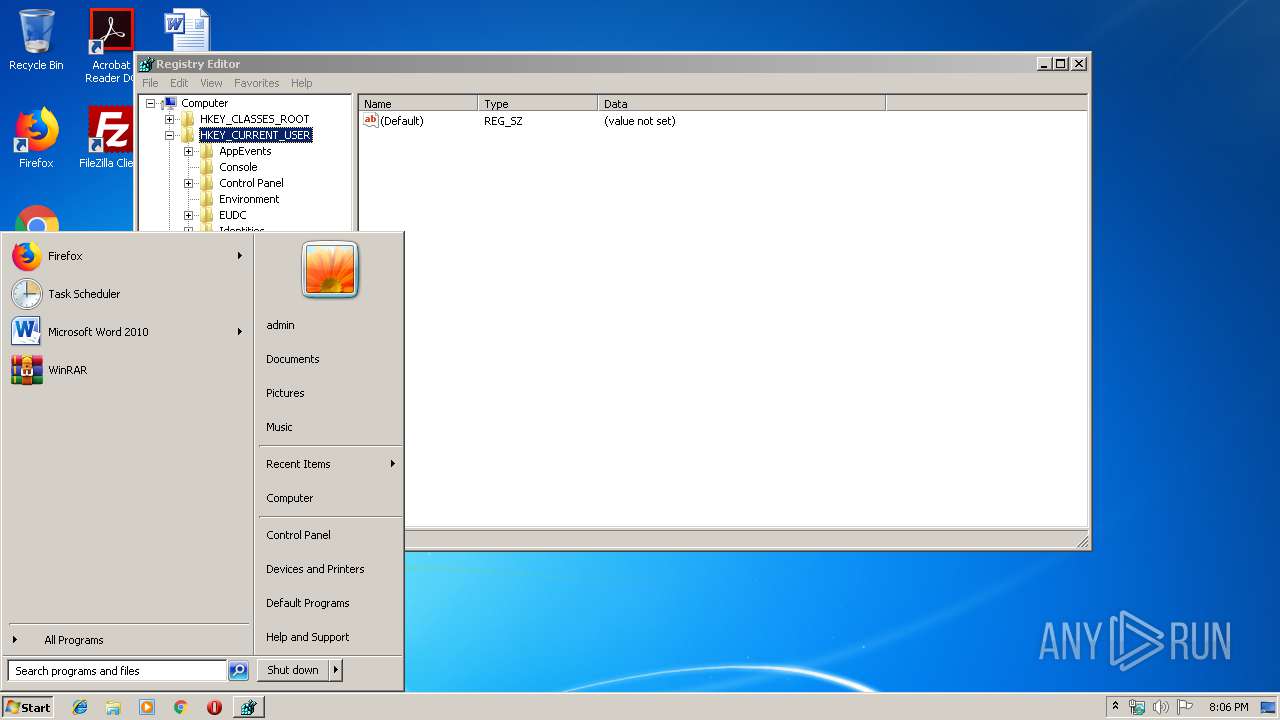
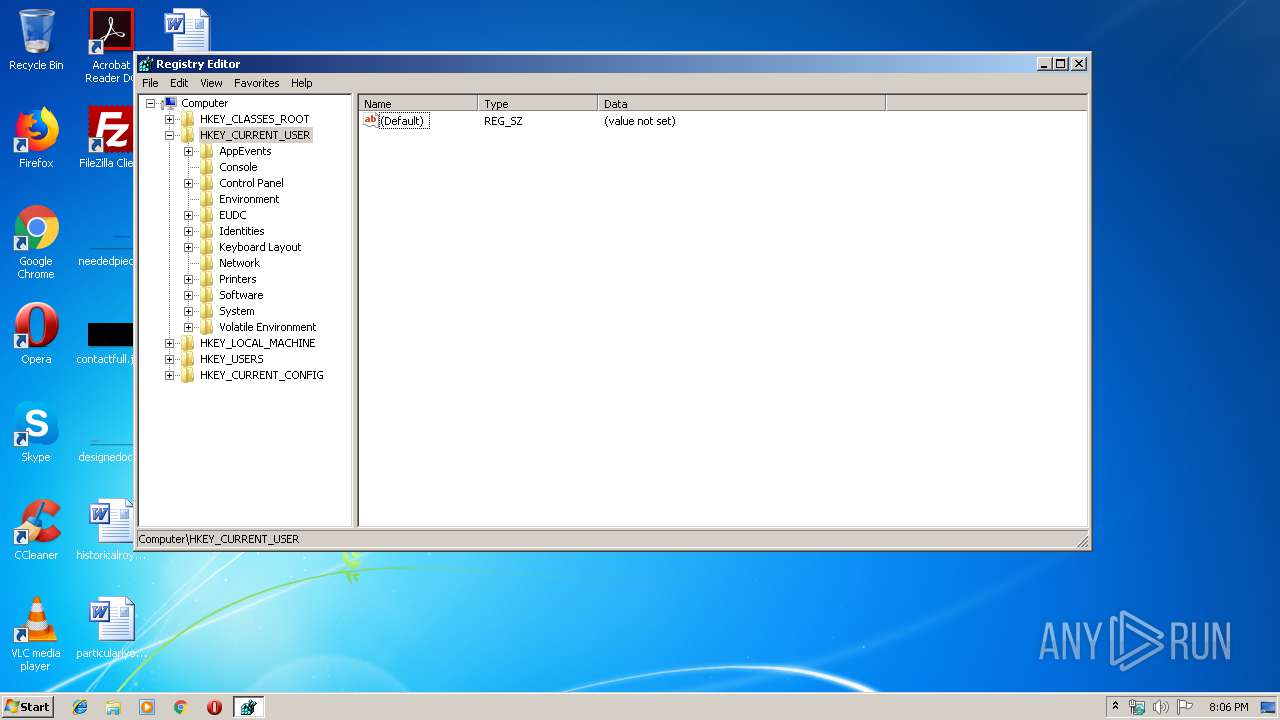
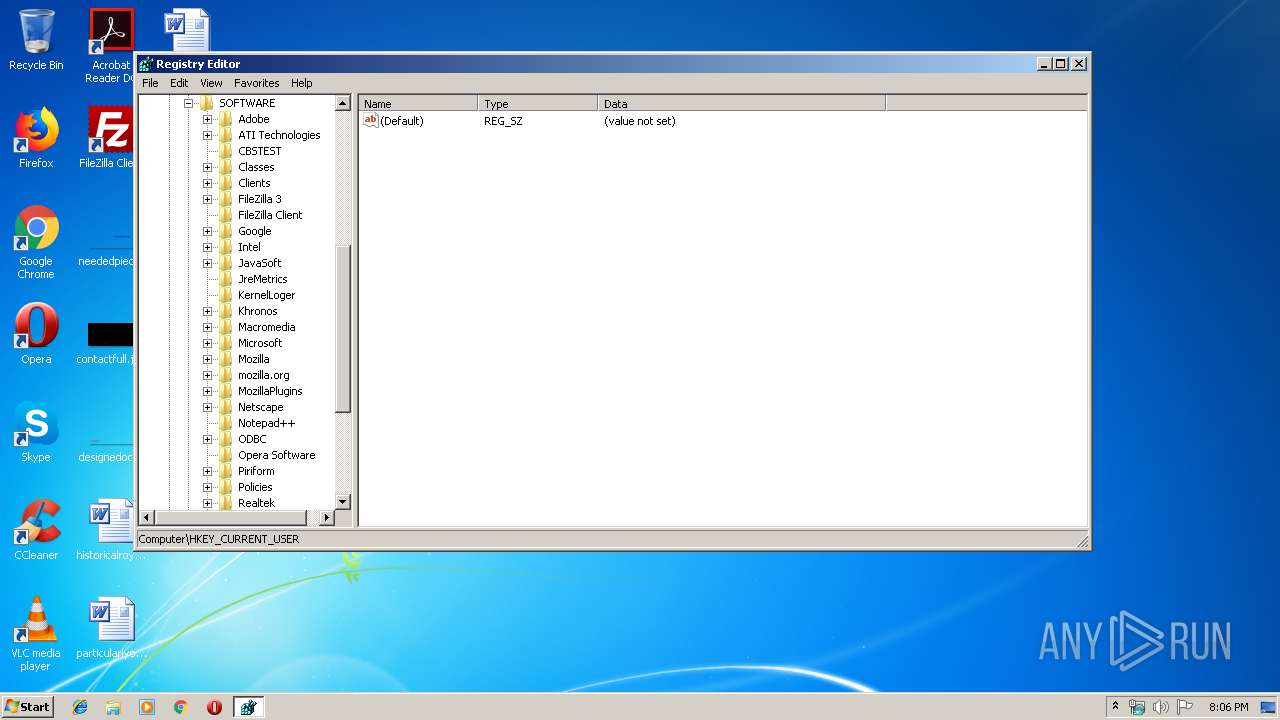
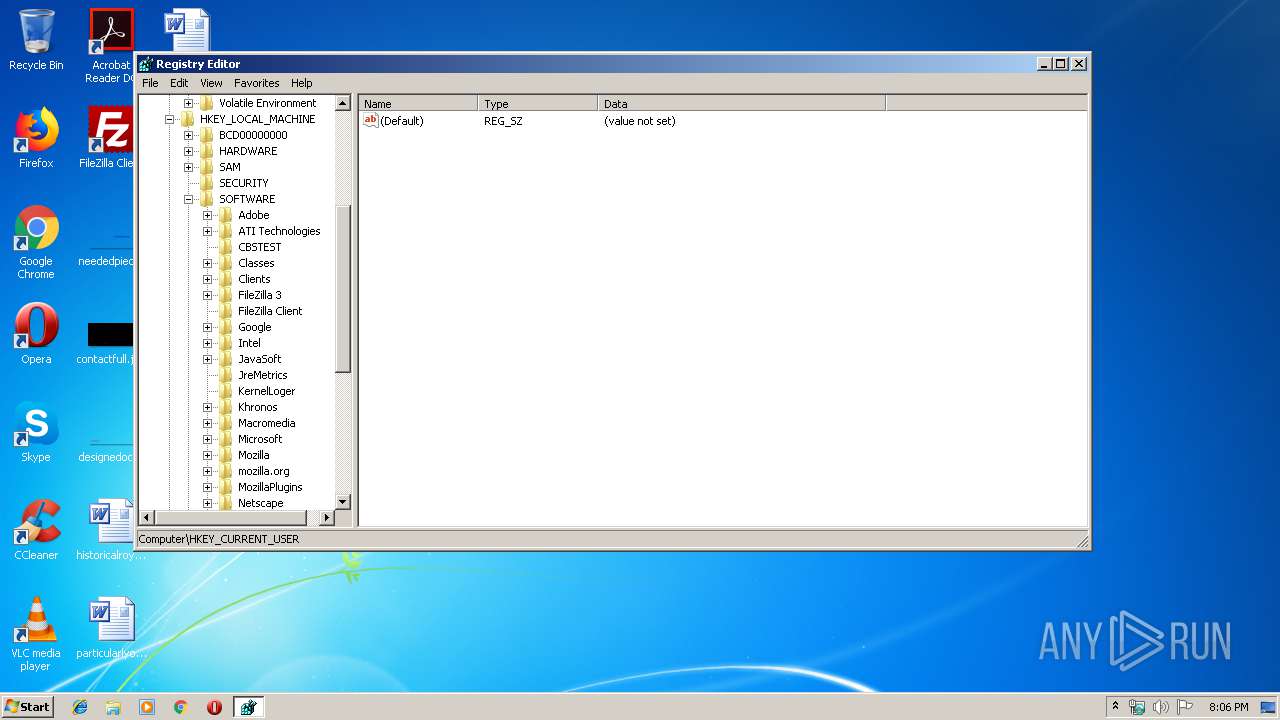
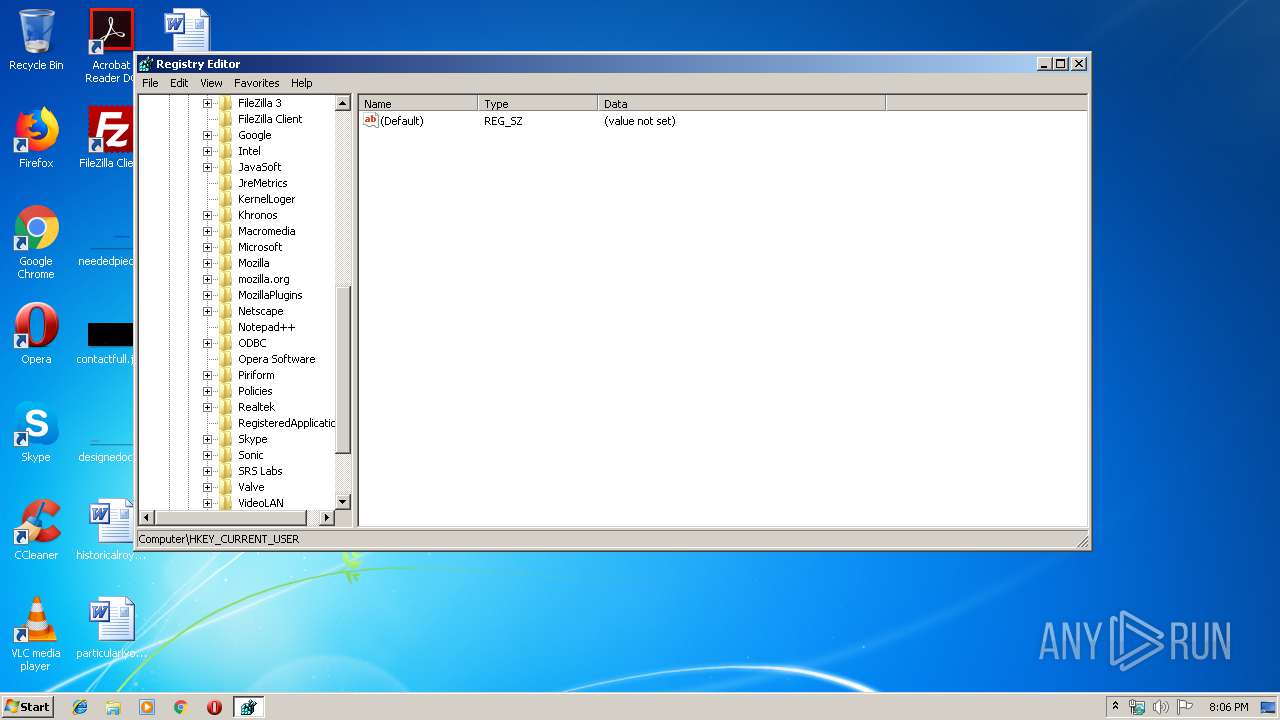
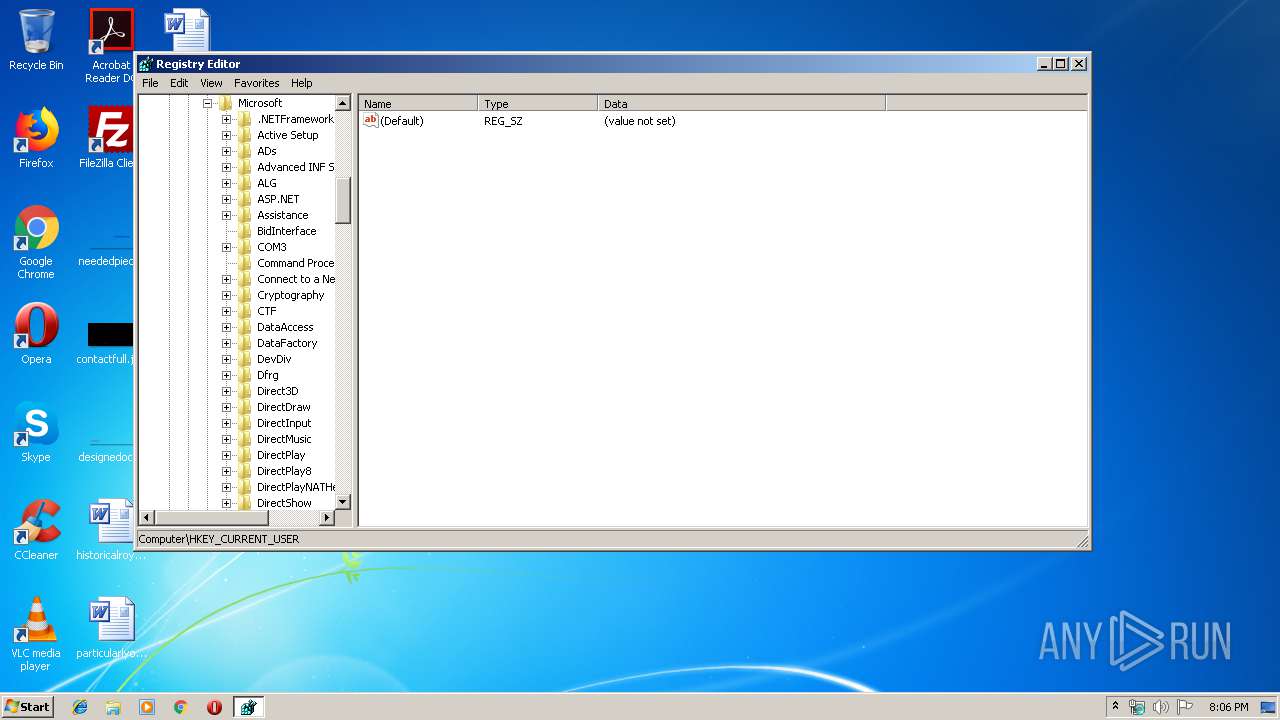
INFO
Manual execution by user
- regedit.exe (PID: 3508)
- regedit.exe (PID: 2440)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:10:03 10:26:23+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 7.1 |
| CodeSize: | 86016 |
| InitializedDataSize: | 98304 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5666 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.1 |
| ProductVersionNumber: | 1.0.0.1 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| FileDescription: | Main Application |
| FileVersion: | 1, 0, 0, 1 |
| InternalName: | Main |
| LegalCopyright: | Copyright (C) 2001 Microsoft Corporation |
| OriginalFileName: | Main.rc |
| ProductName: | Main Application |
| ProductVersion: | 1, 0, 0, 1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Oct-2019 08:26:23 |
| Detected languages: |
|
| Debug artifacts: |
|
| FileDescription: | Main Application |
| FileVersion: | 1, 0, 0, 1 |
| InternalName: | Main |
| LegalCopyright: | Copyright (C) 2001 Microsoft Corporation |
| OriginalFilename: | Main.rc |
| ProductName: | Main Application |
| ProductVersion: | 1, 0, 0, 1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 03-Oct-2019 08:26:23 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00014A4F | 0x00015000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.36664 |
.rdata | 0x00016000 | 0x00003B08 | 0x00004000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.59429 |
.data | 0x0001A000 | 0x00002400 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.15934 |
.idata | 0x0001D000 | 0x00001107 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.91217 |
.rsrc | 0x0001F000 | 0x0000FA2C | 0x00010000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.56246 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.32881 | 700 | Latin 1 / Western European | English - United States | RT_VERSION |
2 | 3.13294 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 2.68192 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 2.19943 | 72 | Latin 1 / Western European | English - United States | RT_STRING |
101 | 3.08481 | 296 | Latin 1 / Western European | English - United States | RT_DIALOG |
103 | 3.2825 | 428 | Latin 1 / Western European | English - United States | RT_DIALOG |
107 | 2.3738 | 34 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
108 | 2.02322 | 20 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
109 | 1.79879 | 16 | Latin 1 / Western European | English - United States | RT_ACCELERATOR |
445 | 7.69493 | 60228 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
USER32.dll |
Total processes
44
Monitored processes
10
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2316 | "C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe" | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | — | dgoxs.exe | |||||||||||
User: admin Company: Monkey Head Software Integrity Level: MEDIUM Description: Monkey Head Media Stream Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2440 | "C:\Windows\regedit.exe" | C:\Windows\regedit.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Editor Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2472 | "C:\Users\admin\AppData\Local\msptermsizes\DGoxS.exe" | C:\Users\admin\AppData\Local\msptermsizes\DGoxS.exe | — | msptermsizes.exe | |||||||||||
User: admin Company: Monkey Head Software Integrity Level: MEDIUM Description: Monkey Head Media Stream Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2904 | "C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe" | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | — | 0.file.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Main Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2932 | "C:\Users\admin\AppData\Local\Temp\0.file.exe" | C:\Users\admin\AppData\Local\Temp\0.file.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Main Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3008 | --f91b2738 | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | msptermsizes.exe | ||||||||||||
User: admin Company: Monkey Head Software Integrity Level: MEDIUM Description: Monkey Head Media Stream Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3024 | --b8619eb3 | C:\Users\admin\AppData\Local\msptermsizes\dgoxs.exe | DGoxS.exe | ||||||||||||
User: admin Company: Monkey Head Software Integrity Level: MEDIUM Description: Monkey Head Media Stream Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3508 | "C:\Windows\regedit.exe" | C:\Windows\regedit.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Editor Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3620 | --f91b2738 | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | msptermsizes.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Main Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3740 | --8495285e | C:\Users\admin\AppData\Local\Temp\0.file.exe | 0.file.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Main Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
124
Read events
105
Write events
19
Delete events
0
Modification events
| (PID) Process: | (3620) msptermsizes.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\msptermsizes_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3620) msptermsizes.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\msptermsizes_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3620) msptermsizes.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\msptermsizes_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3620) msptermsizes.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\msptermsizes_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3620) msptermsizes.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\msptermsizes_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3620) msptermsizes.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\msptermsizes_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3620) msptermsizes.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\msptermsizes_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3620) msptermsizes.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\msptermsizes_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3620) msptermsizes.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\msptermsizes_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3620) msptermsizes.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\msptermsizes_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
3
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3620 | msptermsizes.exe | C:\Users\admin\AppData\Local\msptermsizes\DGoxS.exe | executable | |
MD5:— | SHA256:— | |||
| 3740 | 0.file.exe | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | executable | |
MD5:— | SHA256:— | |||
| 3024 | dgoxs.exe | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
90
DNS requests
64
Threats
65
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3008 | msptermsizes.exe | POST | — | 198.199.114.69:8080 | http://198.199.114.69:8080/odbc/ | US | — | — | malicious |
3620 | msptermsizes.exe | POST | — | 91.121.116.137:443 | http://91.121.116.137:443/prov/raster/ringin/ | FR | — | — | malicious |
3008 | msptermsizes.exe | POST | — | 23.239.29.211:443 | http://23.239.29.211:443/arizona/ | US | — | — | malicious |
3008 | msptermsizes.exe | POST | 200 | 80.79.23.144:443 | http://80.79.23.144:443/mult/cab/ringin/merge/ | CZ | binary | 707 Kb | malicious |
3008 | msptermsizes.exe | POST | 200 | 80.79.23.144:443 | http://80.79.23.144:443/window/ | CZ | binary | 148 b | malicious |
3008 | msptermsizes.exe | POST | — | 185.187.198.4:8080 | http://185.187.198.4:8080/acquire/ringin/ringin/merge/ | RU | — | — | malicious |
3008 | msptermsizes.exe | POST | — | 23.253.207.142:8080 | http://23.253.207.142:8080/add/guids/ringin/merge/ | US | — | — | malicious |
3008 | msptermsizes.exe | POST | 200 | 23.253.207.142:8080 | http://23.253.207.142:8080/devices/ | US | binary | 139 Kb | malicious |
3008 | msptermsizes.exe | POST | 200 | 46.228.205.245:4143 | http://46.228.205.245:4143/glitch/devices/ringin/ | DE | binary | 1.16 Mb | malicious |
3008 | msptermsizes.exe | GET | 200 | 23.253.207.142:8080 | http://23.253.207.142:8080/news.php | US | text | 13 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3620 | msptermsizes.exe | 80.79.23.144:443 | — | Master Internet s.r.o. | CZ | malicious |
3620 | msptermsizes.exe | 91.121.116.137:443 | — | OVH SAS | FR | malicious |
3008 | msptermsizes.exe | 23.239.29.211:443 | — | Linode, LLC | US | malicious |
3008 | msptermsizes.exe | 198.199.114.69:8080 | — | Digital Ocean, Inc. | US | malicious |
3008 | msptermsizes.exe | 80.79.23.144:443 | — | Master Internet s.r.o. | CZ | malicious |
3008 | msptermsizes.exe | 23.253.207.142:8080 | — | Rackspace Ltd. | US | malicious |
3008 | msptermsizes.exe | 83.166.132.14:587 | mail.golflausanne.ch | Infomaniak Network SA | CH | unknown |
3008 | msptermsizes.exe | 212.227.15.158:587 | smtp.1and1.es | 1&1 Internet SE | DE | unknown |
3008 | msptermsizes.exe | 94.152.145.179:25 | horizont.com.pl | Krakowskie e-Centrum Informatyczne JUMP Dziedzic, Pasek, Przybyla s. j. | PL | unknown |
3008 | msptermsizes.exe | 217.69.139.74:465 | pop.mail.ru | Limited liability company Mail.Ru | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pop.mail.ru |
| shared |
mail.golflausanne.ch |
| unknown |
mail.mail.ru |
| shared |
horizont.com.pl |
| unknown |
smtp.mail.ru |
| malicious |
mx1.inco.pl |
| unknown |
smtp.1and1.es |
| malicious |
smtpauth.bluewin.ch |
| unknown |
wp11228275.mailout.server-he.de |
| unknown |
mail.leanpro.ch |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3620 | msptermsizes.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 24 |
3620 | msptermsizes.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin (Apr 2019) |
3620 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3620 | msptermsizes.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
3620 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3620 | msptermsizes.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
3008 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3008 | msptermsizes.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
3008 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3008 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
15 ETPRO signatures available at the full report