| File name: | 3.zip |
| Full analysis: | https://app.any.run/tasks/56270ef8-8915-41d0-bab3-1a850171930d |
| Verdict: | Malicious activity |
| Analysis date: | July 11, 2019, 20:45:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | EB1C8CCB4CDA958FB8438EE755377982 |
| SHA1: | 1B2E87C560577D773F2F101BF426BC677F951AAC |
| SHA256: | B7C7E65B80959DB18E4DE9AB0172C01B3EF72ED698A7F5785CA9A2D902907ED5 |
| SSDEEP: | 6144:TuVdz/to8koiTJ8Jek8c/Ux9W4wX/RnpeU45mVIFhU:ivhoS8c/Ux9W4EgUPyU |
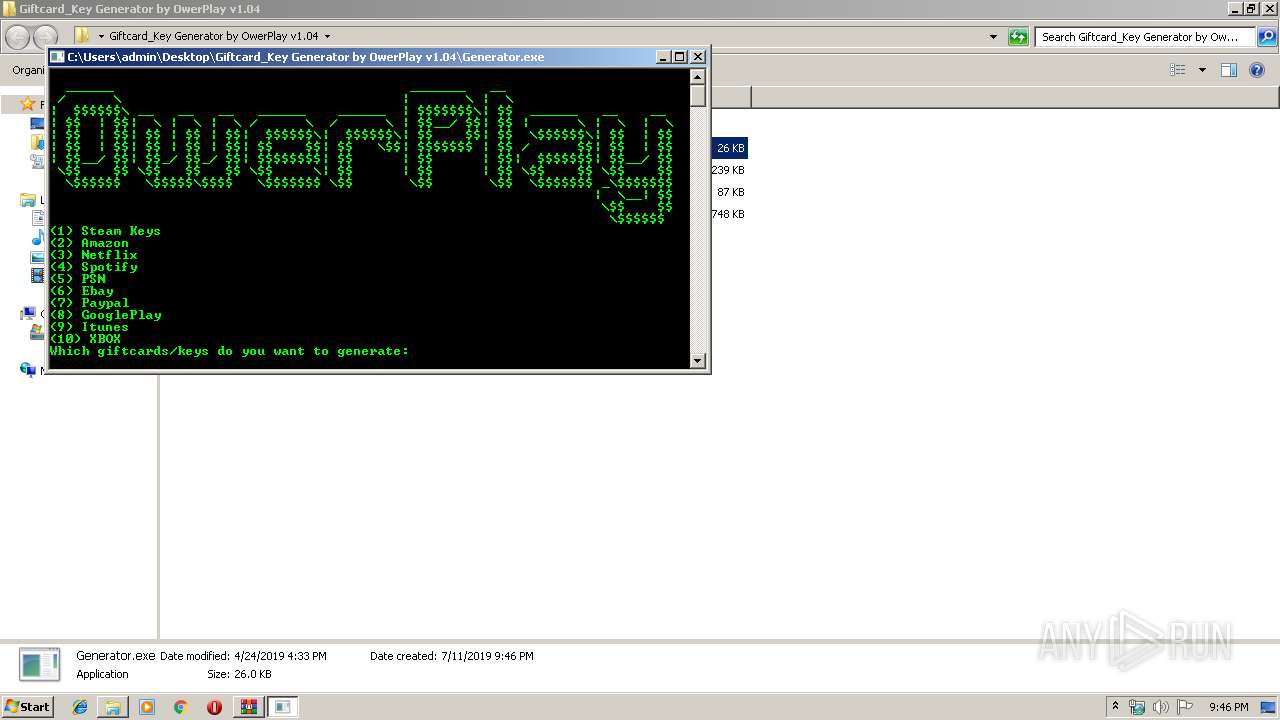
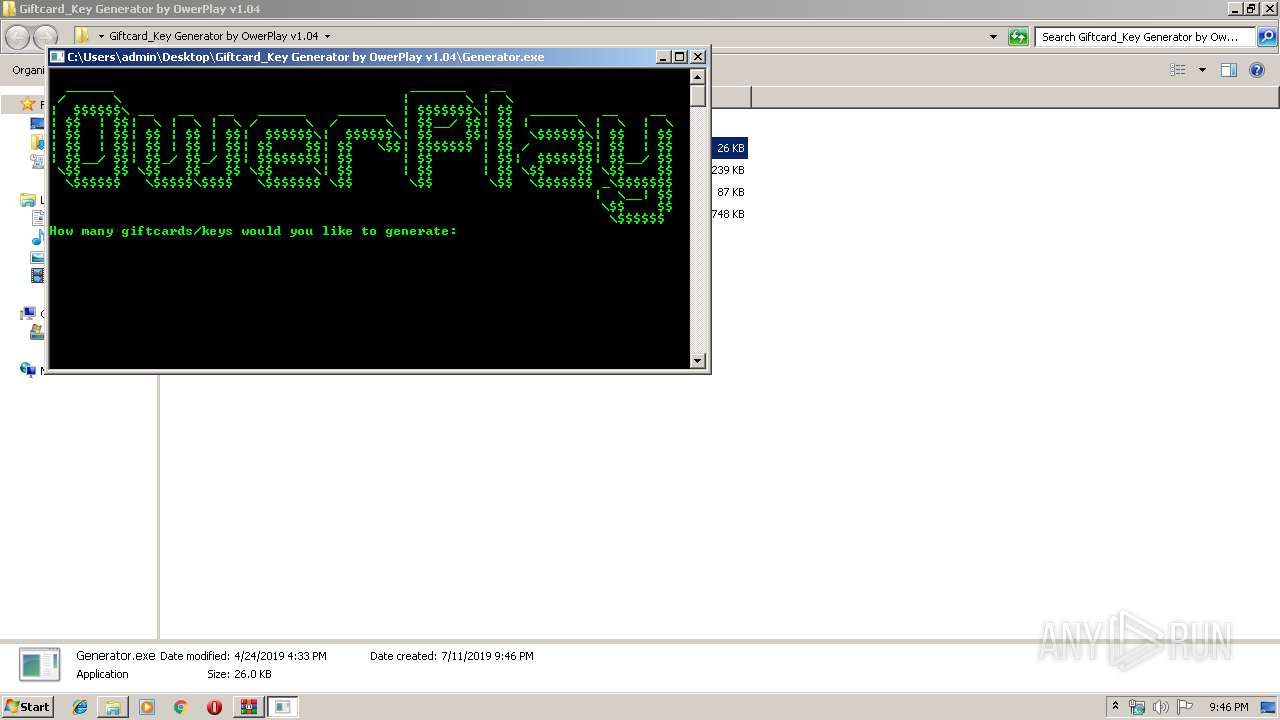
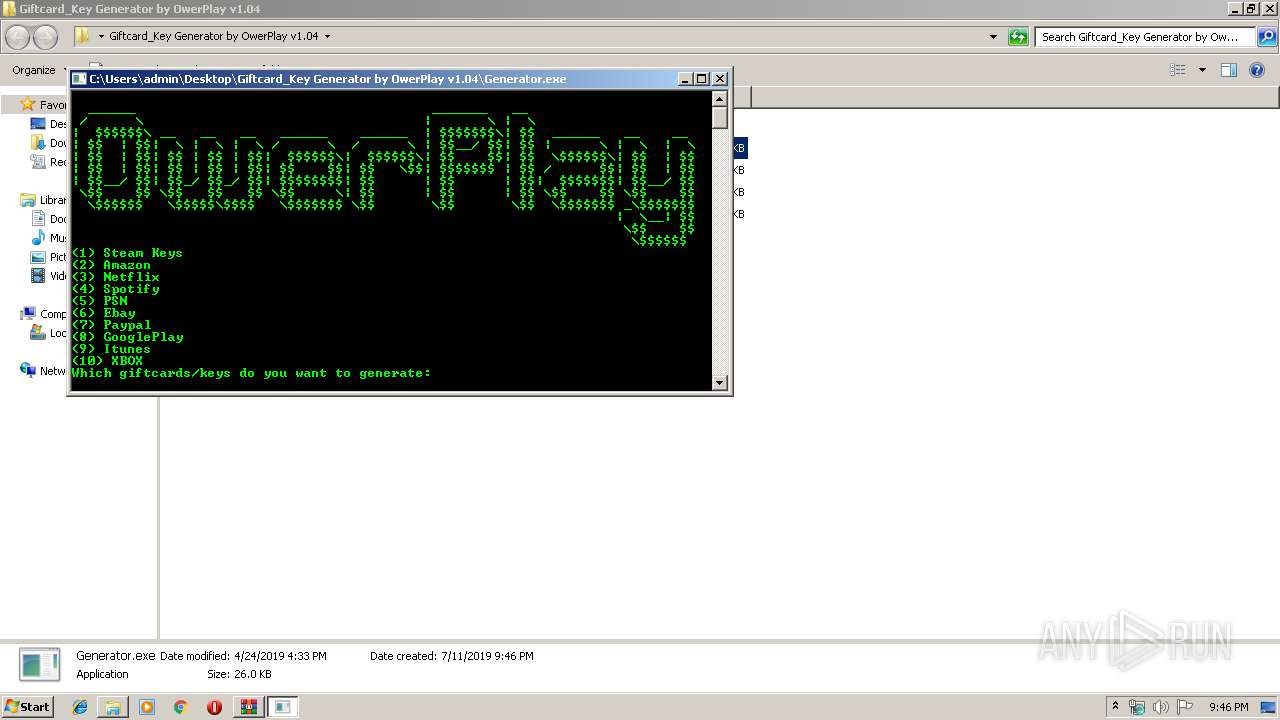
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts CMD.EXE for commands execution
- Generator.exe (PID: 3296)
- Generator.exe (PID: 3932)
INFO
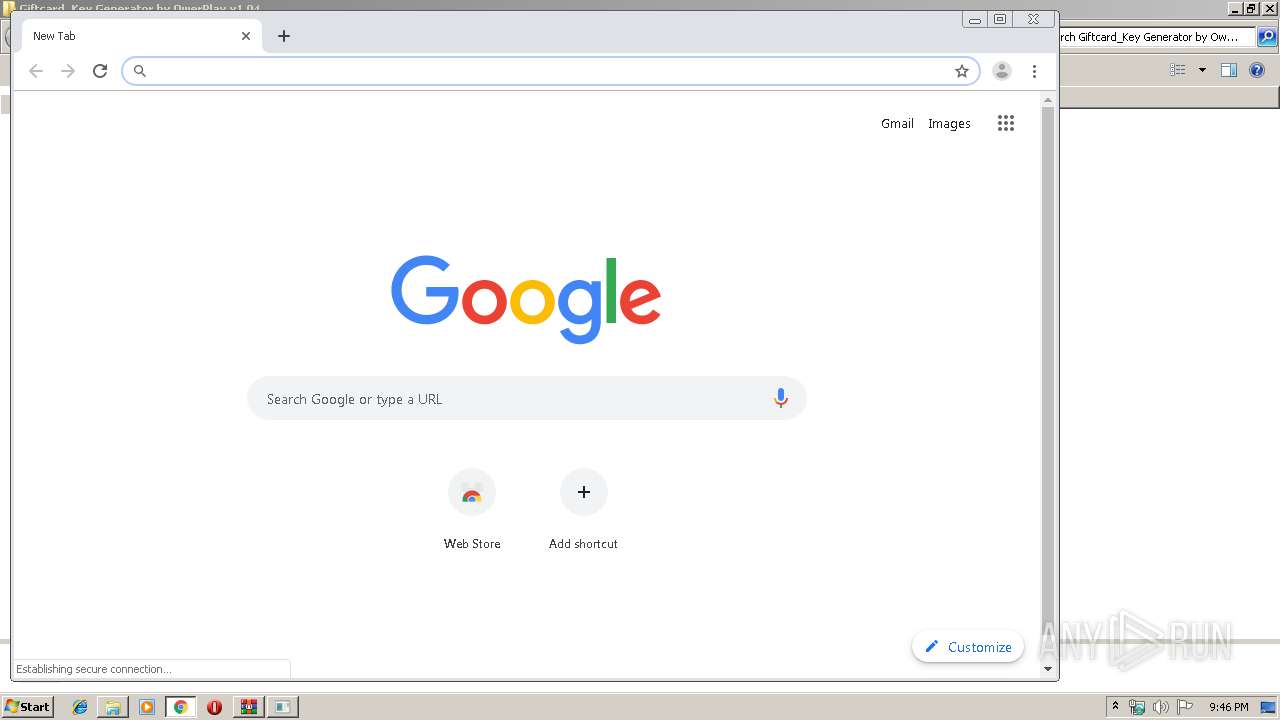
Manual execution by user
- Generator.exe (PID: 3932)
- chrome.exe (PID: 3068)
- Generator.exe (PID: 3296)
Application launched itself
- chrome.exe (PID: 3068)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
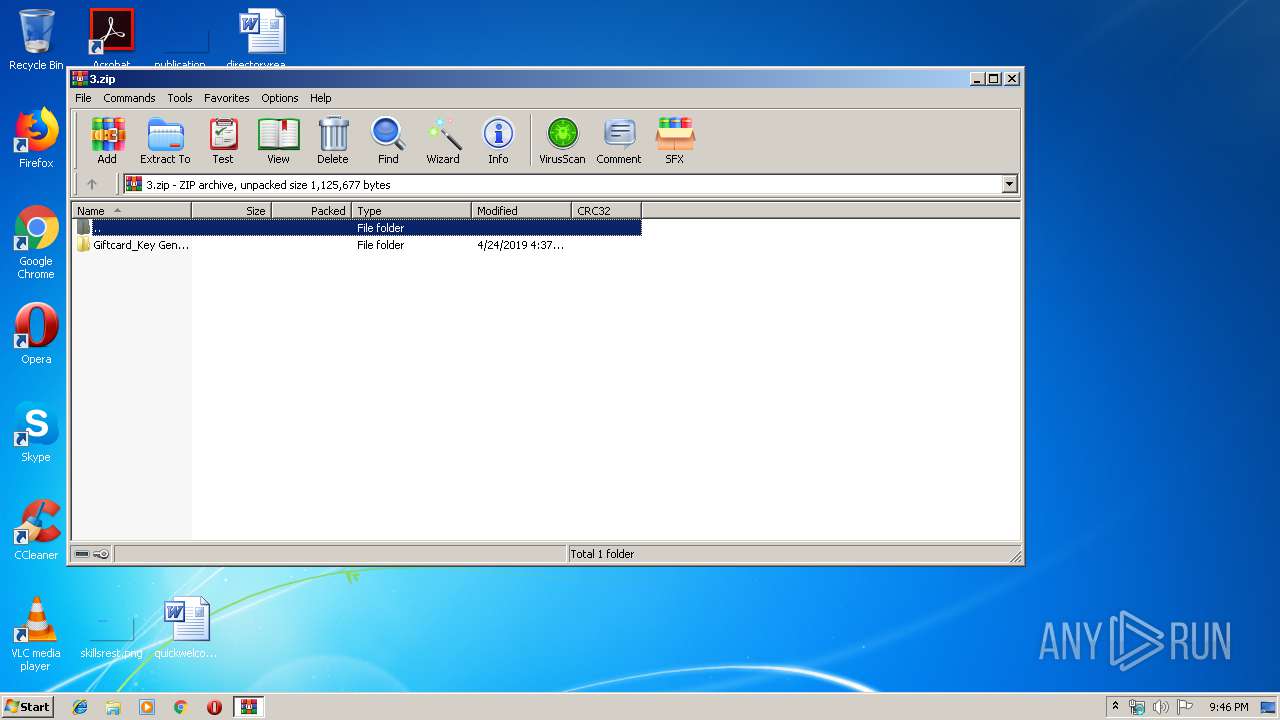
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2019:04:24 17:37:10 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
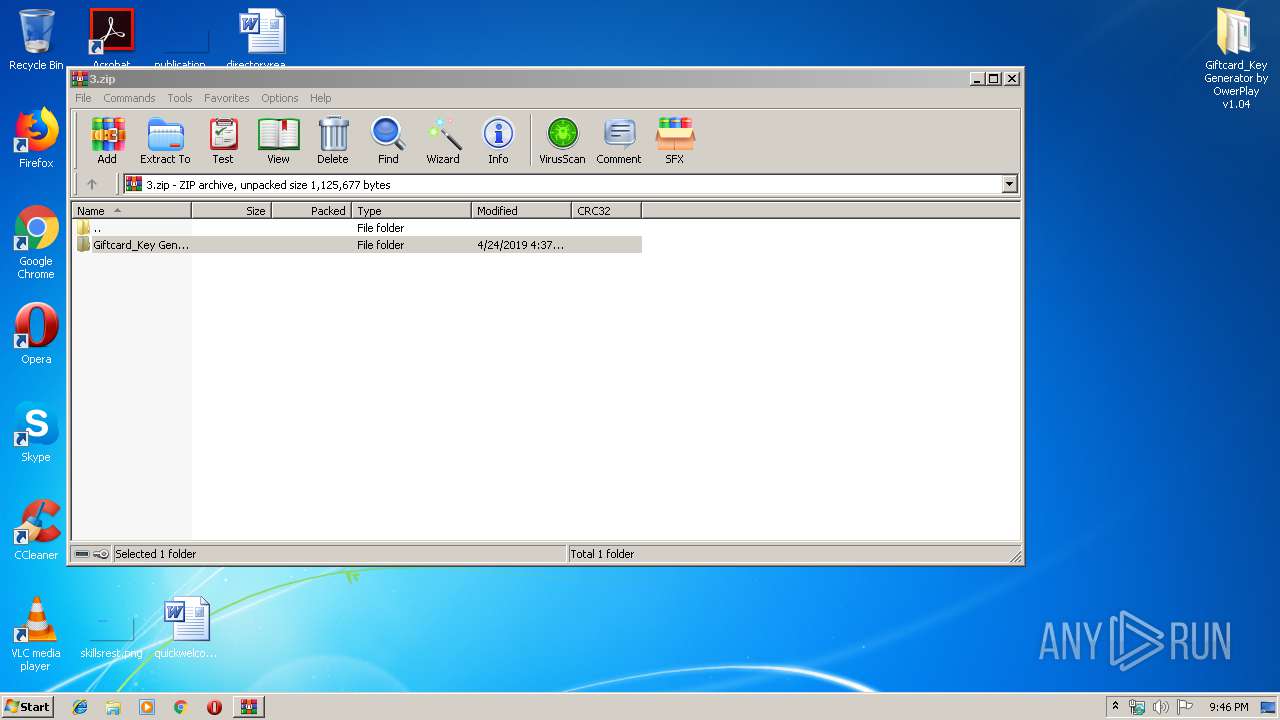
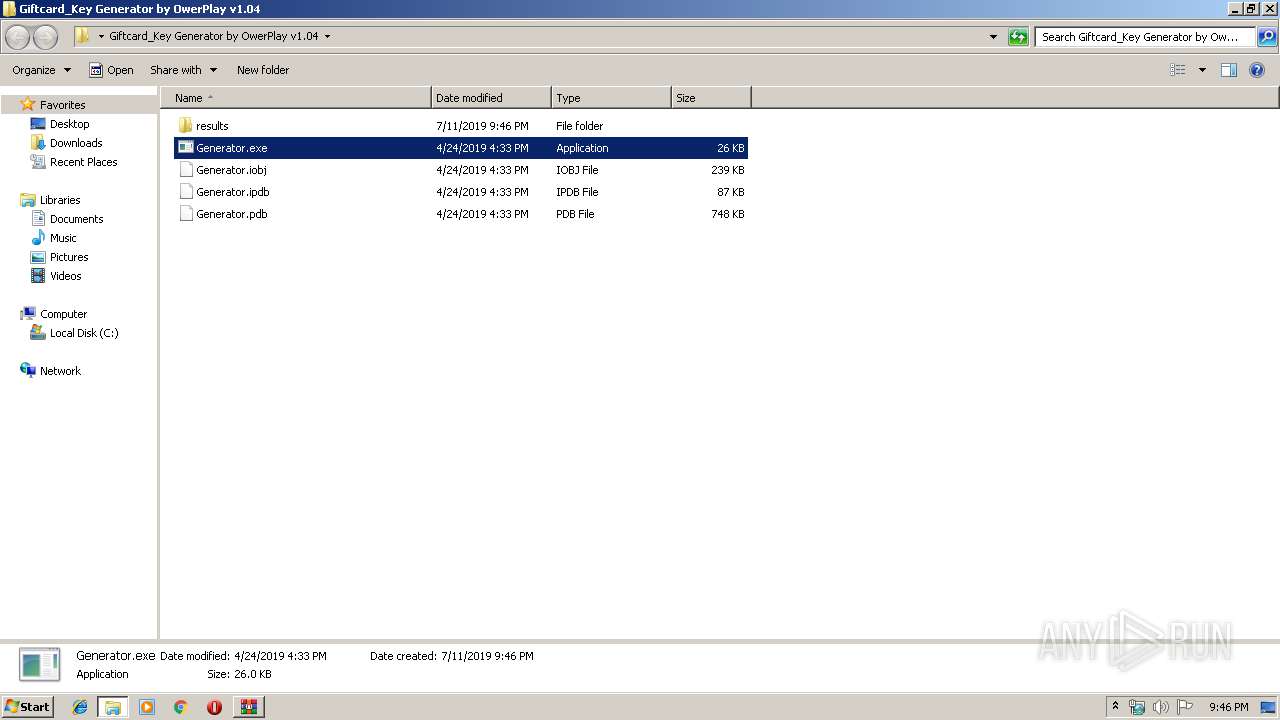
| ZipFileName: | Giftcard_Key Generator by OwerPlay v1.04/ |
Total processes
72
Monitored processes
33
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1668 | C:\Windows\system32\cmd.exe /c test&cls | C:\Windows\system32\cmd.exe | — | Generator.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,18412222342610089161,5198989174976362470,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7048686501664505446 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3452 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,18412222342610089161,5198989174976362470,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15177027433506870136 --mojo-platform-channel-handle=3244 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2364 | C:\Windows\system32\cmd.exe /c test&cls | C:\Windows\system32\cmd.exe | — | Generator.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6df8a9d0,0x6df8a9e0,0x6df8a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,18412222342610089161,5198989174976362470,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8399854725982492093 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2476 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=988,18412222342610089161,5198989174976362470,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=4211034462853430215 --mojo-platform-channel-handle=3744 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2736 | C:\Windows\system32\cmd.exe /c color a | C:\Windows\system32\cmd.exe | — | Generator.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2888 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,18412222342610089161,5198989174976362470,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16400675816145128436 --mojo-platform-channel-handle=4128 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2920 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\3.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
646
Read events
575
Write events
67
Delete events
4
Modification events
| (PID) Process: | (2920) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2920) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2920) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2920) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\3.zip | |||
| (PID) Process: | (2920) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2920) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2920) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2920) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3068) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3068) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
Executable files
0
Suspicious files
76
Text files
245
Unknown types
8
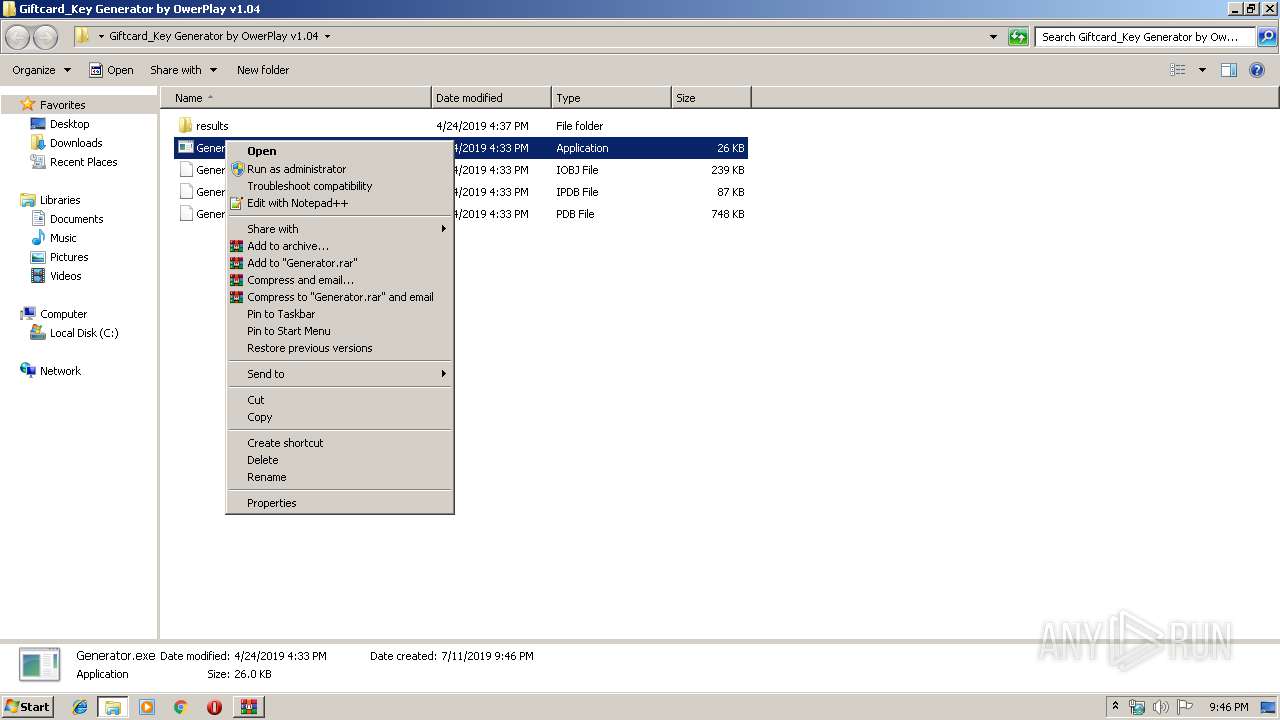
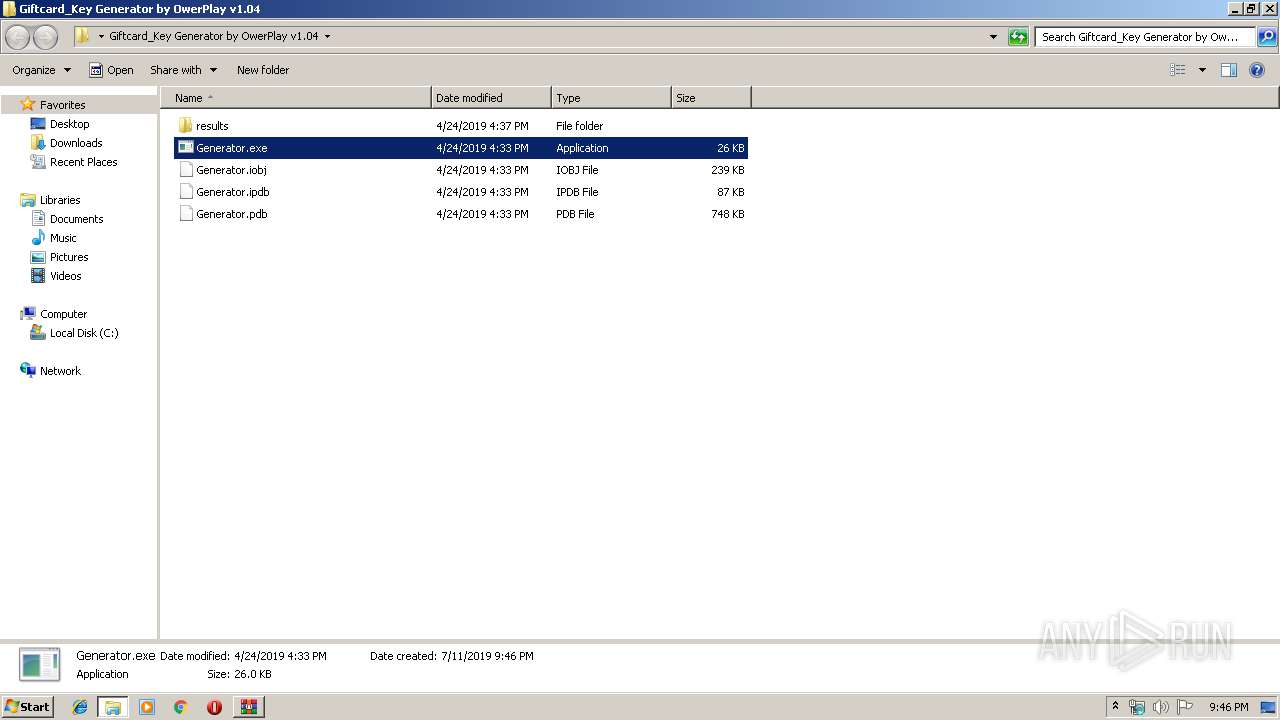
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
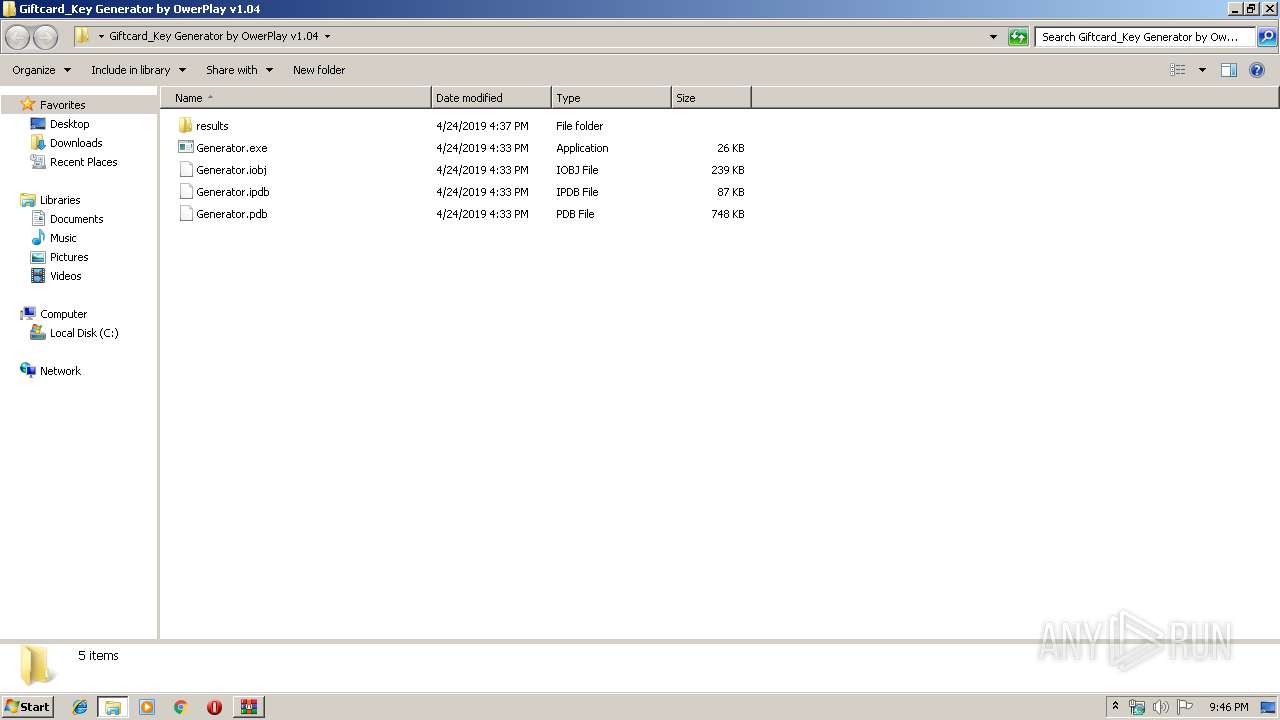
| 2920 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2920.47332\Giftcard_Key Generator by OwerPlay v1.04\Generator.exe | — | |
MD5:— | SHA256:— | |||
| 2920 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2920.47332\Giftcard_Key Generator by OwerPlay v1.04\Generator.iobj | — | |
MD5:— | SHA256:— | |||
| 2920 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2920.47332\Giftcard_Key Generator by OwerPlay v1.04\Generator.ipdb | — | |
MD5:— | SHA256:— | |||
| 2920 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2920.47332\Giftcard_Key Generator by OwerPlay v1.04\Generator.pdb | — | |
MD5:— | SHA256:— | |||
| 3068 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3068 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3068 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3068 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\54f5a0ee-6546-4fe8-bfcf-6eae853fe201.tmp | — | |
MD5:— | SHA256:— | |||
| 3068 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3068 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
82
TCP/UDP connections
53
DNS requests
60
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
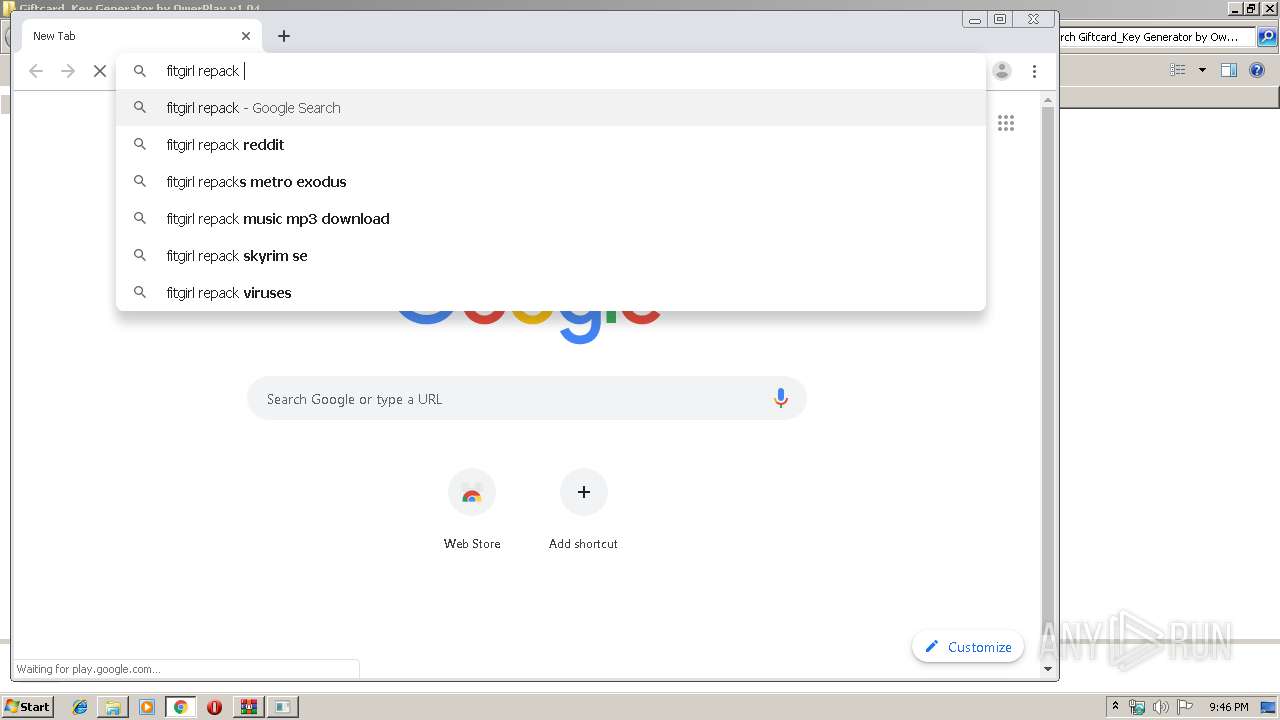
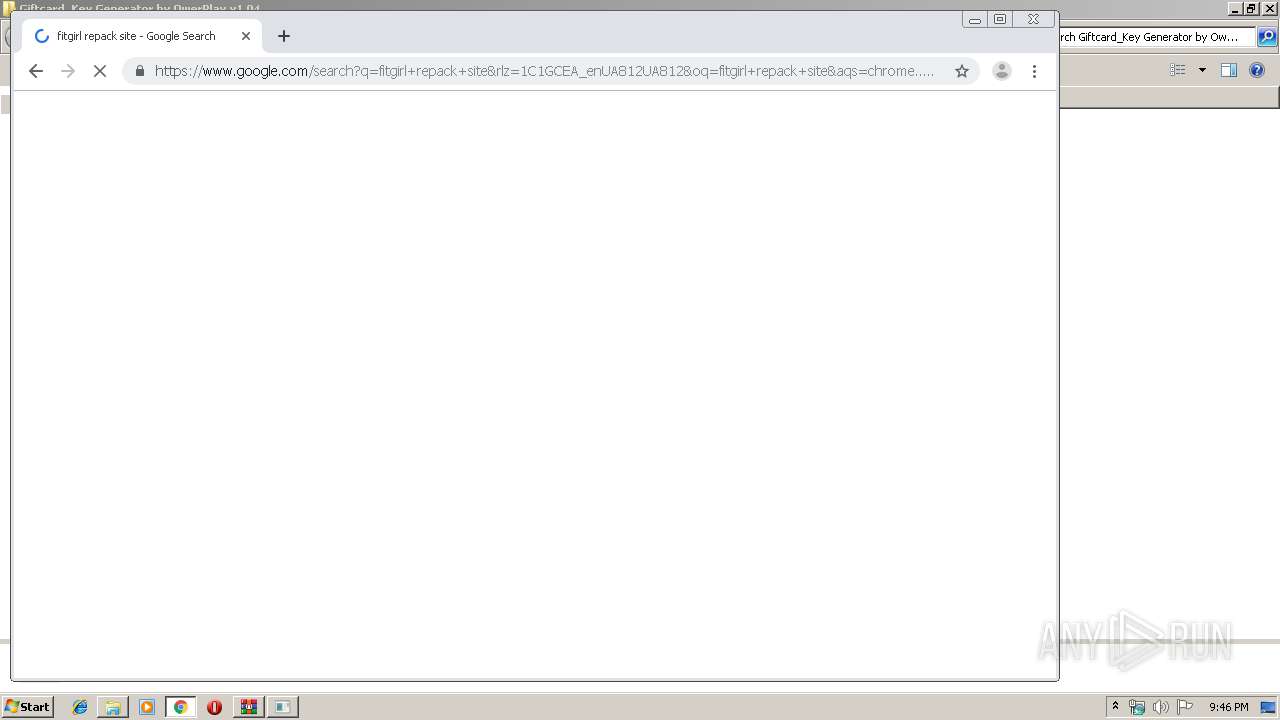
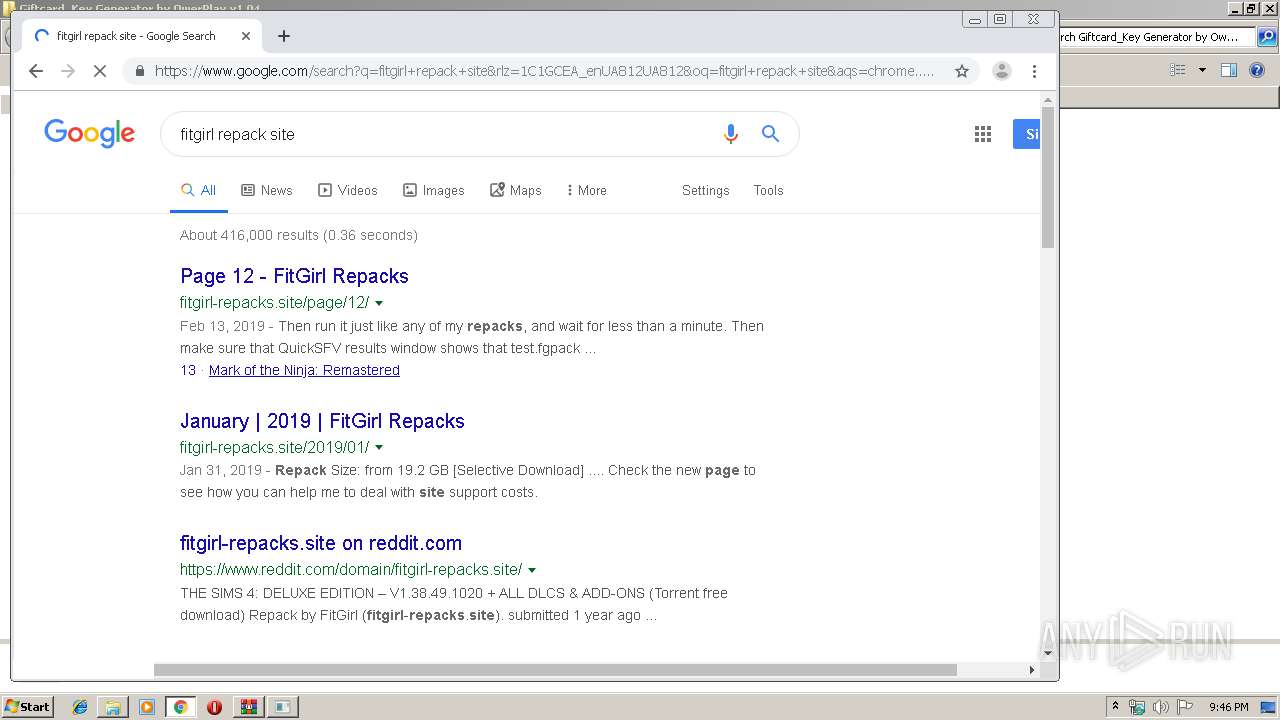
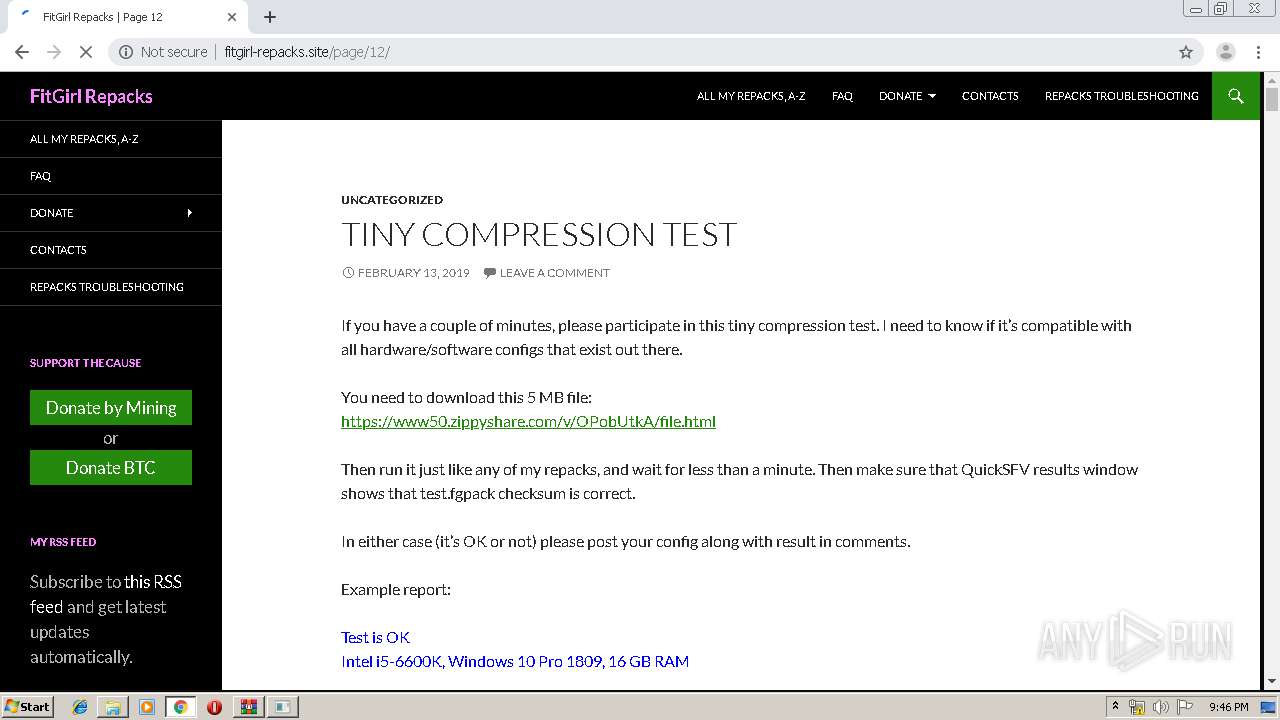
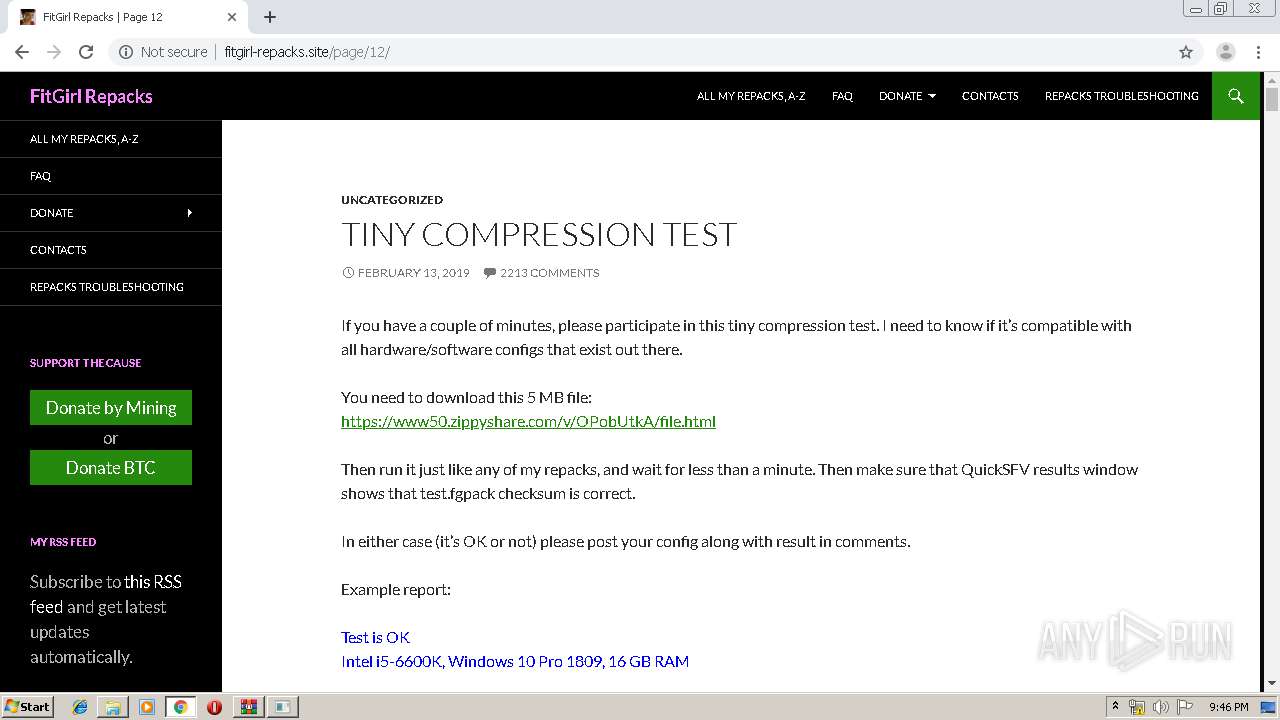
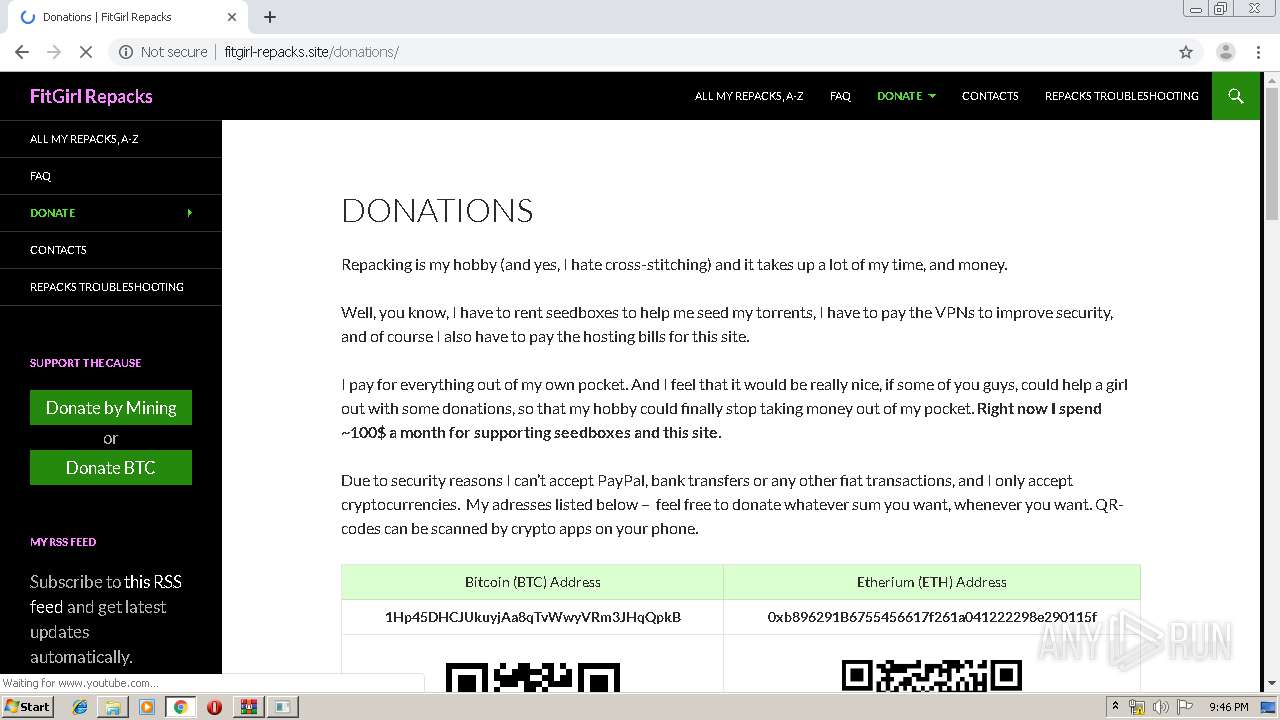
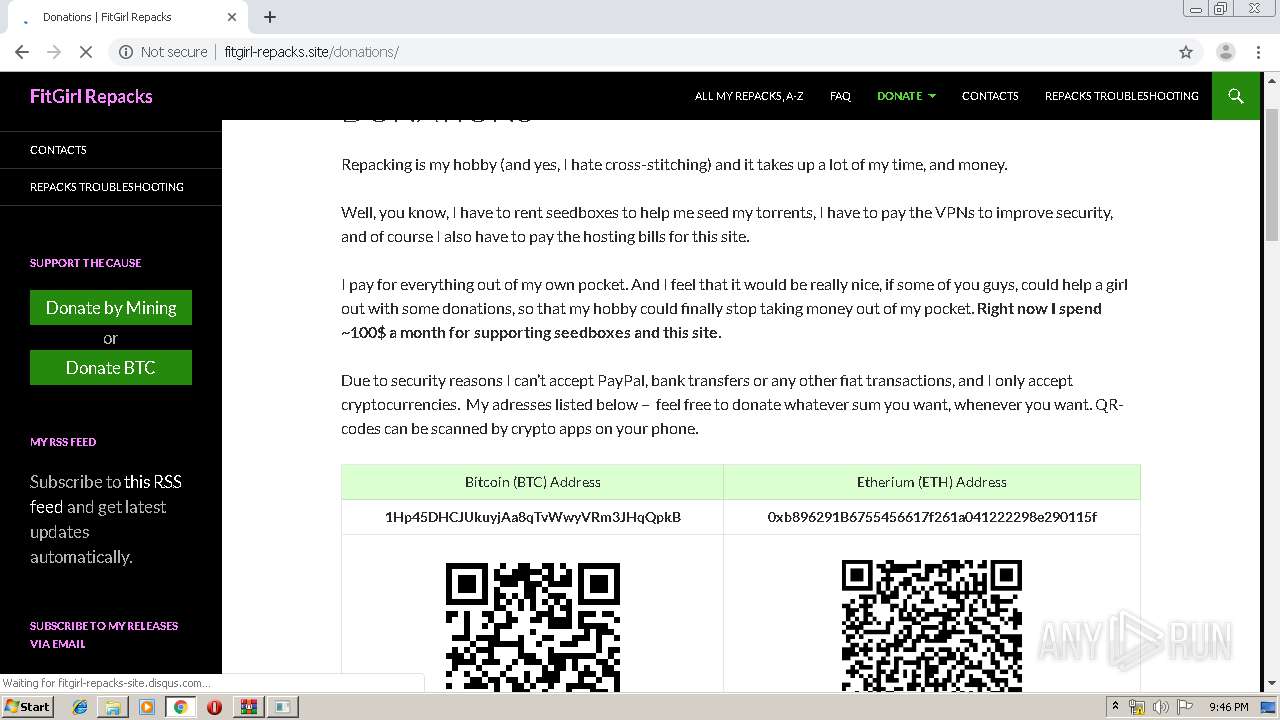
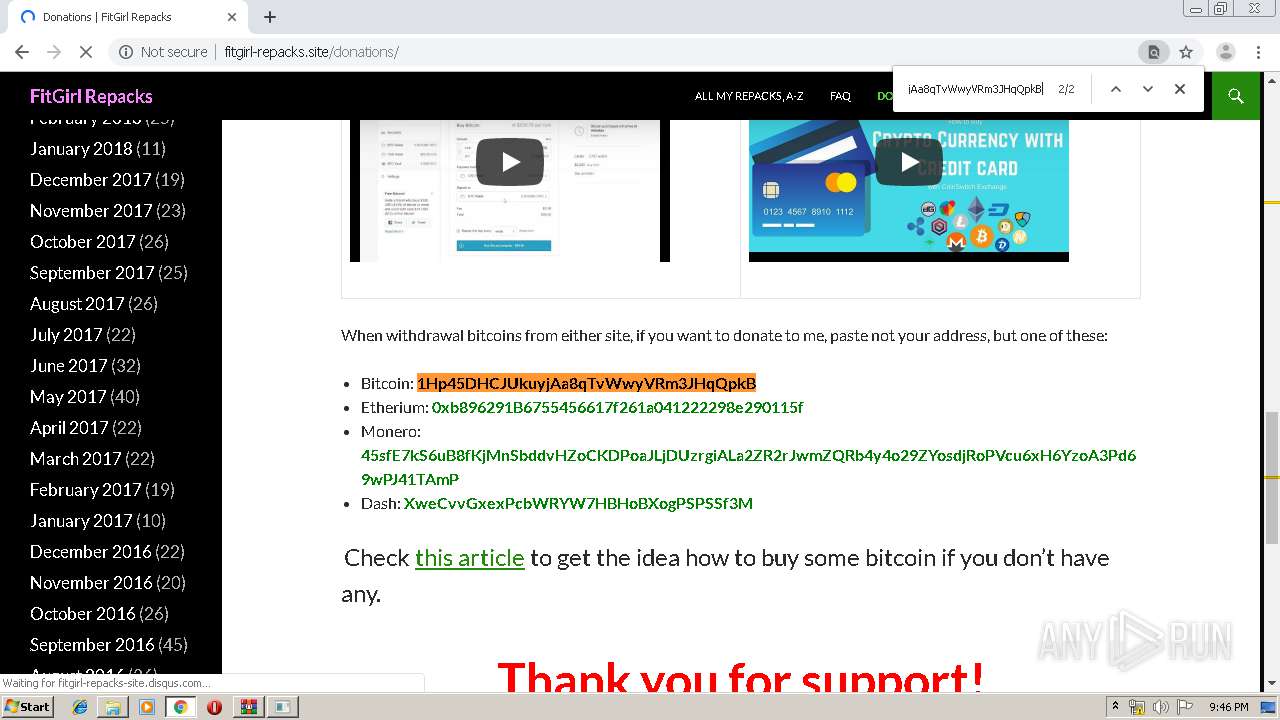
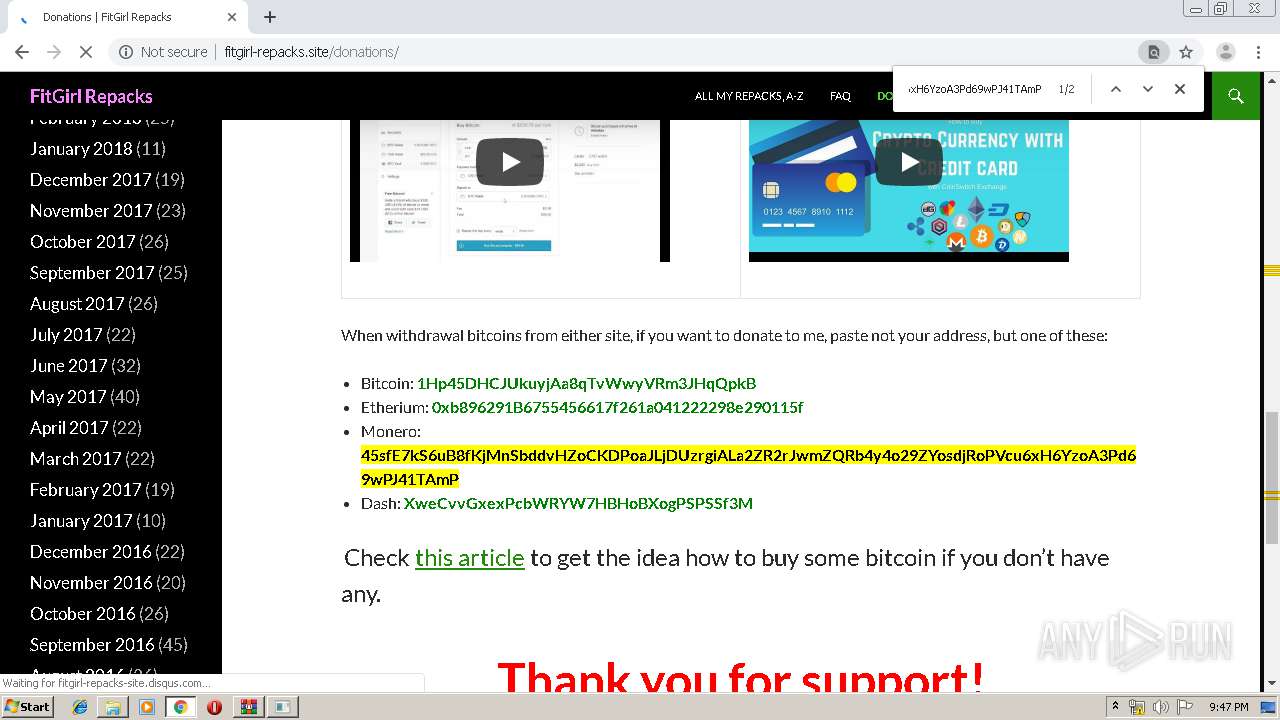
3284 | chrome.exe | GET | 200 | 104.24.127.50:80 | http://fitgirl-repacks.site/page/12/ | US | html | 23.5 Kb | suspicious |
3284 | chrome.exe | GET | 302 | 172.217.21.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 512 b | whitelisted |
3284 | chrome.exe | GET | 200 | 104.24.127.50:80 | http://fitgirl-repacks.site/wp-content/themes/twentyfourteen/style.css?ver=5.0.2 | US | text | 14.4 Kb | suspicious |
3284 | chrome.exe | GET | 200 | 104.24.127.50:80 | http://fitgirl-repacks.site/wp-content/uploads/2019/02/error.png | US | image | 20.5 Kb | suspicious |
3284 | chrome.exe | GET | 200 | 104.27.178.224:80 | http://s01.riotpixels.net/data/21/5b/215bfd5a-d7b3-4b61-86d6-5d5bcc69bc07.jpg.240p.jpg | US | image | 6.20 Kb | suspicious |
3284 | chrome.exe | GET | 200 | 104.24.127.50:80 | http://fitgirl-repacks.site/wp-content/plugins/jetpack/modules/theme-tools/compat/twentyfourteen.css?ver=5.5.1 | US | text | 1.62 Kb | suspicious |
3284 | chrome.exe | GET | 200 | 173.194.7.89:80 | http://r3---sn-p5qs7n7e.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=85.203.20.5&mm=28&mn=sn-p5qs7n7e&ms=nvh&mt=1562877826&mv=u&mvi=2&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
3284 | chrome.exe | GET | 200 | 104.24.127.50:80 | http://fitgirl-repacks.site/wp-content/plugins/social-polls-by-opinionstage/js/shortcodes.js?ver=18.1.0 | US | text | 275 b | suspicious |
3284 | chrome.exe | GET | 200 | 104.24.127.50:80 | http://fitgirl-repacks.site/wp-includes/css/dist/block-library/style.min.css?ver=5.0.2 | US | text | 4.25 Kb | suspicious |
3284 | chrome.exe | GET | 200 | 104.24.127.50:80 | http://fitgirl-repacks.site/wp-content/themes/twentyfourteen/js/functions.js?ver=20150315 | US | text | 2.09 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3284 | chrome.exe | 216.58.206.3:443 | www.google.com.ua | Google Inc. | US | whitelisted |
3284 | chrome.exe | 172.217.23.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3284 | chrome.exe | 172.217.18.174:443 | ogs.google.com | Google Inc. | US | whitelisted |
3284 | chrome.exe | 172.217.21.238:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
3284 | chrome.exe | 172.217.21.225:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3284 | chrome.exe | 172.217.22.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
— | — | 172.217.22.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
3284 | chrome.exe | 173.194.7.89:80 | r3---sn-p5qs7n7e.gvt1.com | Google Inc. | US | whitelisted |
3284 | chrome.exe | 172.217.18.98:443 | adservice.google.com | Google Inc. | US | whitelisted |
3284 | chrome.exe | 172.217.22.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
play.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1044 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |