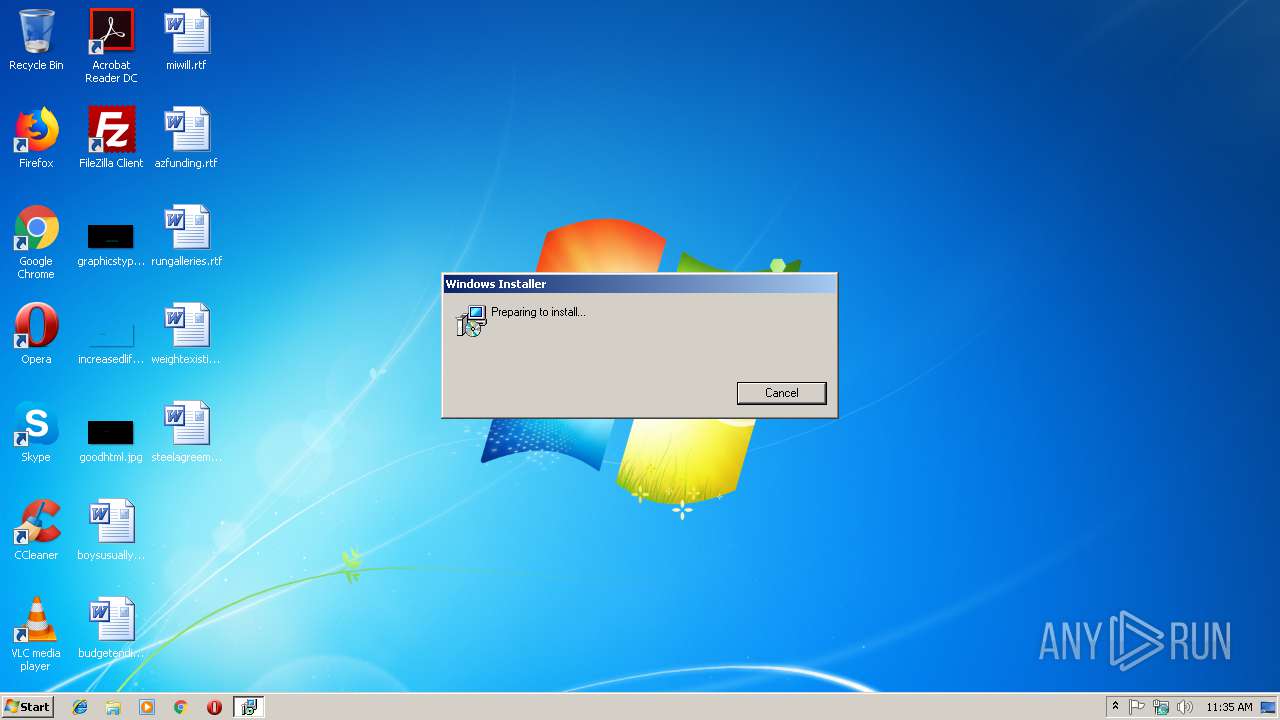
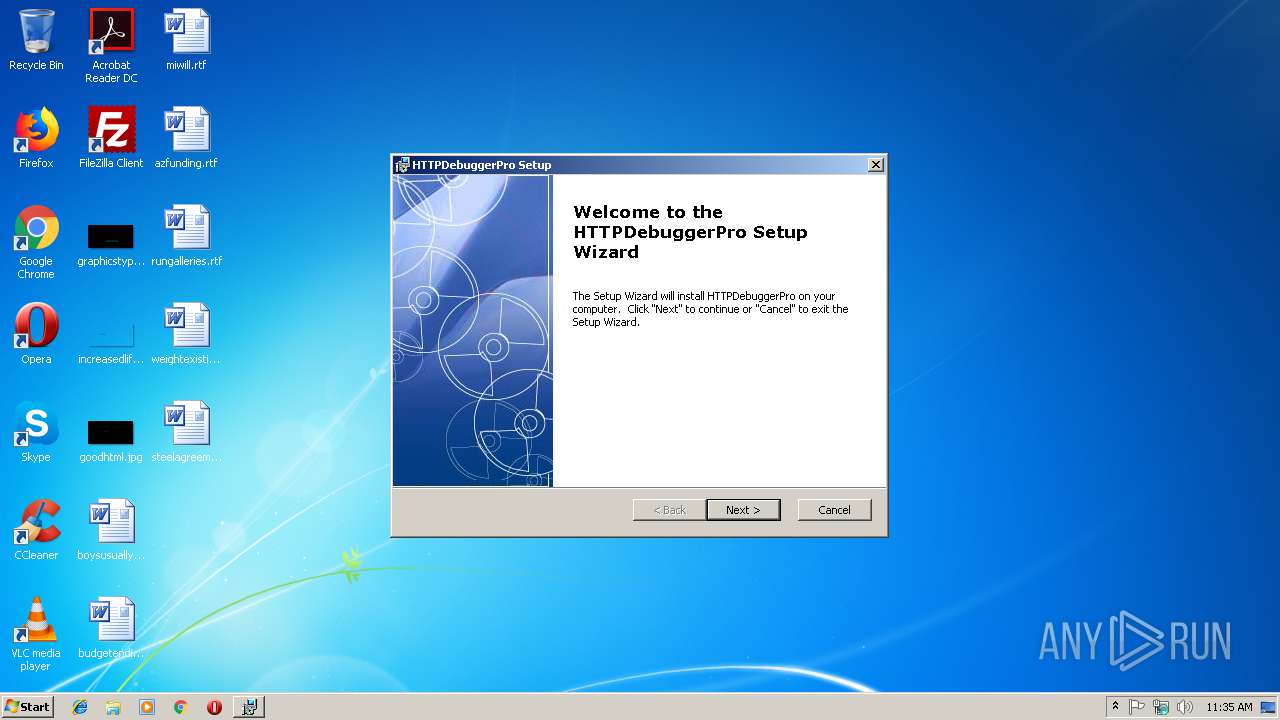
| download: | HTTPDebuggerPro.msi |
| Full analysis: | https://app.any.run/tasks/0525bb9c-32d6-4a1c-8b0f-b9978c08bb69 |
| Verdict: | Malicious activity |
| Analysis date: | December 02, 2018, 11:34:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.3, MSI Installer, Title: Installation Database, Keywords: Installer, MSI, Database, Last Printed: Fri Dec 11 11:47:44 2009, Create Time/Date: Fri Dec 11 11:47:44 2009, Last Saved Time/Date: Fri Dec 11 11:47:44 2009, Number of Pages: 200, Security: 0, Code page: 1252, Revision Number: {7F82302E-15A0-428C-9A82-45E10C745082}, Number of Words: 2, Subject: HTTPDebuggerPro, Author: HttpDebugger.com, Name of Creating Application: Advanced Installer 11.6.2 build 61089, Template: ;1033, Comments: HTTPDebuggerPro installation package. |
| MD5: | C67F274A8B24957EC2753B0294A54717 |
| SHA1: | 878D47E8E4D52B6B10A1012697D10E05BC6F5E13 |
| SHA256: | B7BFA2E2B4A35E6208DAB23E39522D627485F6096EC2DB7B2687BF8F1286DB3D |
| SSDEEP: | 196608:3XKIKdS8QmgJBStXptPpTNe2QAuB0aSY7eELr3005131sZwYRnyGu8uQ:3AnXTc2VdY7J3Z2wYRyGruQ |
MALICIOUS
Loads dropped or rewritten executable
- MsiExec.exe (PID: 3712)
- HTTPDebuggerUI.exe (PID: 1472)
- certutil.exe (PID: 3784)
Application was dropped or rewritten from another process
- HTTPDebuggerUI.exe (PID: 1472)
- HTTPDebuggerSvc.exe (PID: 3532)
- certutil.exe (PID: 3784)
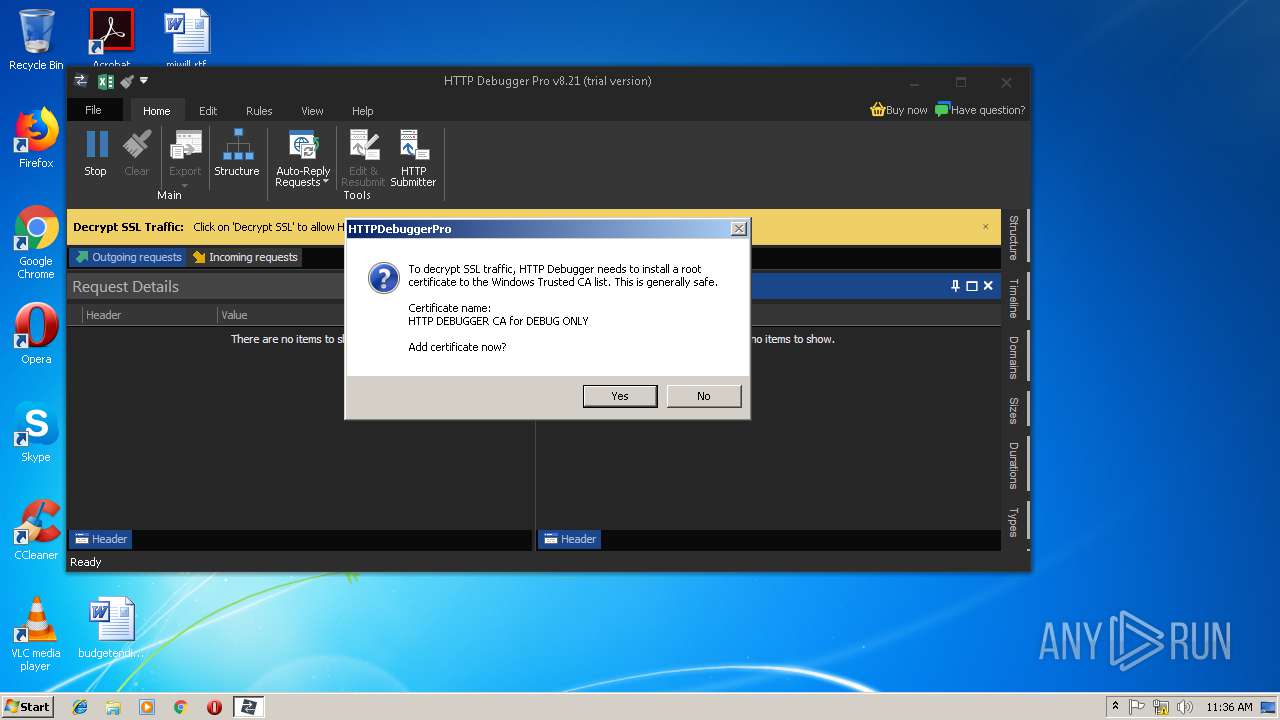
Changes settings of System certificates
- HTTPDebuggerSvc.exe (PID: 3532)
SUSPICIOUS
Executable content was dropped or overwritten
- msiexec.exe (PID: 3116)
- msiexec.exe (PID: 2728)
- HTTPDebuggerSvc.exe (PID: 3532)
Creates files in the program directory
- HTTPDebuggerSvc.exe (PID: 3532)
Creates files in the Windows directory
- HTTPDebuggerSvc.exe (PID: 3532)
Creates files in the driver directory
- HTTPDebuggerSvc.exe (PID: 3532)
Creates COM task schedule object
- MsiExec.exe (PID: 3712)
Creates or modifies windows services
- HTTPDebuggerSvc.exe (PID: 3532)
Reads Internet Cache Settings
- HTTPDebuggerUI.exe (PID: 1472)
Reads internet explorer settings
- HTTPDebuggerUI.exe (PID: 1472)
INFO
Application launched itself
- msiexec.exe (PID: 2728)
- chrome.exe (PID: 1792)
Searches for installed software
- msiexec.exe (PID: 2728)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2756)
- MsiExec.exe (PID: 2392)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2664)
Creates files in the program directory
- msiexec.exe (PID: 2728)
Creates a software uninstall entry
- msiexec.exe (PID: 2728)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (88.6) |
|---|---|---|
| .mst | | | Windows SDK Setup Transform Script (10) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| Title: | Installation Database |
|---|---|
| Keywords: | Installer, MSI, Database |
| LastPrinted: | 2009:12:11 11:47:44 |
| CreateDate: | 2009:12:11 11:47:44 |
| ModifyDate: | 2009:12:11 11:47:44 |
| Pages: | 200 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| RevisionNumber: | {7F82302E-15A0-428C-9A82-45E10C745082} |
| Words: | 2 |
| Subject: | HTTPDebuggerPro |
| Author: | HttpDebugger.com |
| LastModifiedBy: | - |
| Software: | Advanced Installer 11.6.2 build 61089 |
| Template: | ;1033 |
| Comments: | HTTPDebuggerPro installation package. |
Total processes
49
Monitored processes
18
Malicious processes
3
Suspicious processes
0
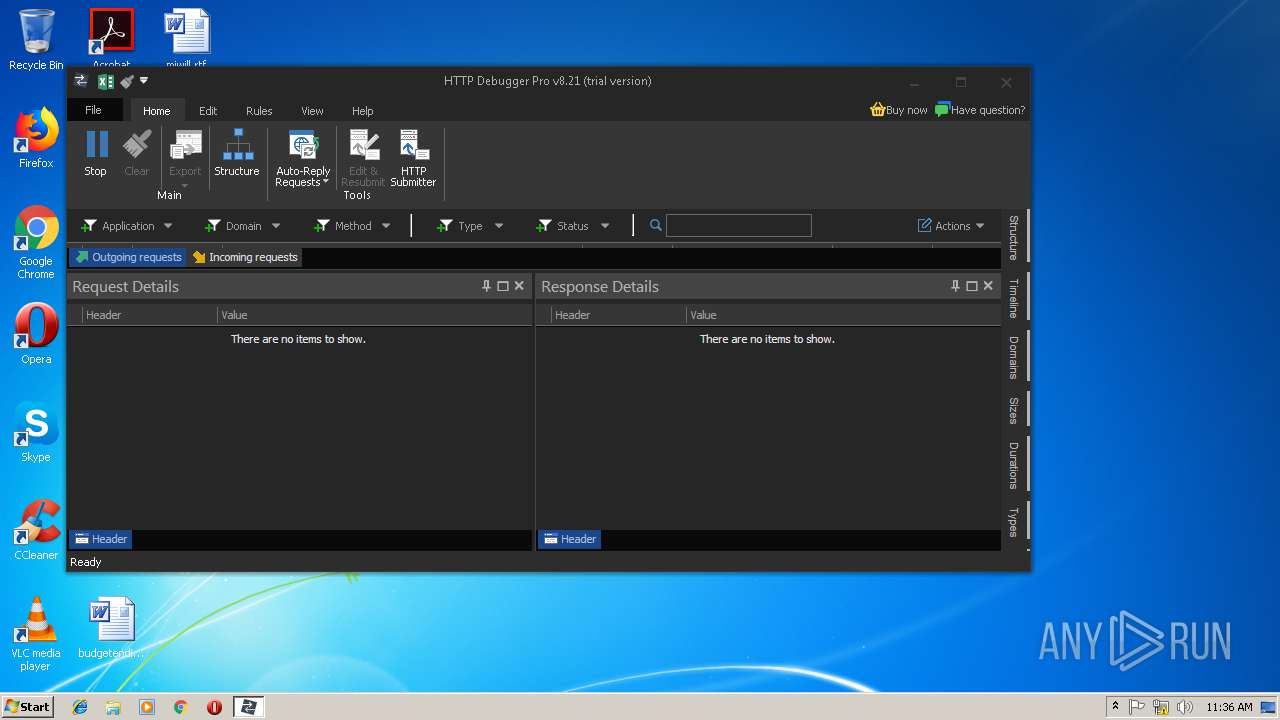
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
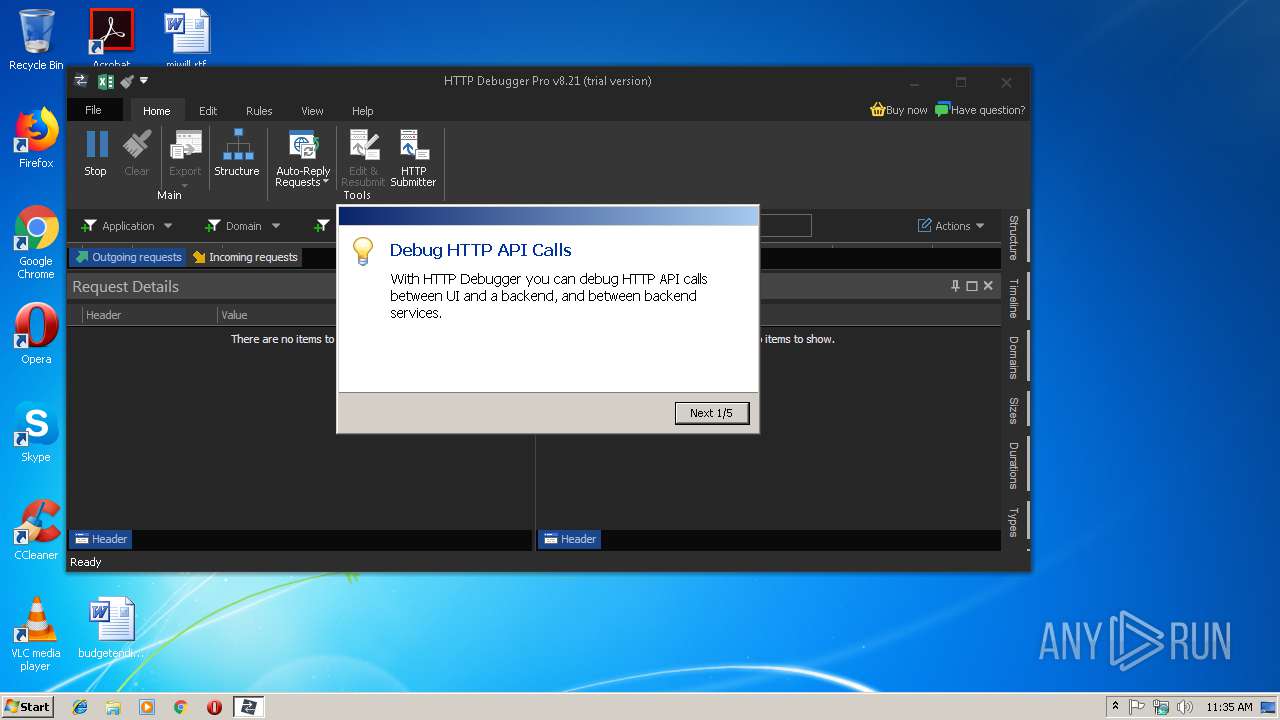
| 1472 | "C:\Program Files\HTTPDebuggerPro\HTTPDebuggerUI.exe" | C:\Program Files\HTTPDebuggerPro\HTTPDebuggerUI.exe | MsiExec.exe | ||||||||||||
User: admin Company: HttpDebugger.com Integrity Level: MEDIUM Description: HTTP Debugger Exit code: 0 Version: 8.0.0.21 Modules
| |||||||||||||||
| 1660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=972,724096389405454186,1677351058586871772,131072 --enable-features=PasswordImport --service-pipe-token=73BF8D8AB9244C7F9A9D96FB6878CE35 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=73BF8D8AB9244C7F9A9D96FB6878CE35 --renderer-client-id=3 --mojo-platform-channel-handle=1908 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1668 | DrvInst.exe "1" "200" "STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot18" "" "" "6792c44eb" "00000000" "000004D8" "000003A8" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1792 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2392 | C:\Windows\system32\MsiExec.exe -Embedding B627B2DFD00086D7812771F4AD0E1817 C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2664 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2724 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=972,724096389405454186,1677351058586871772,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=CC10329B13410ED32CB085207945D4CD --mojo-platform-channel-handle=992 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2728 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2756 | C:\Windows\system32\MsiExec.exe -Embedding F589BBAA29A39154D934DA59B6125C49 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=972,724096389405454186,1677351058586871772,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=9BF064E194D8BBA5380AE69C749EC2BE --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9BF064E194D8BBA5380AE69C749EC2BE --renderer-client-id=7 --mojo-platform-channel-handle=3824 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
1 418
Read events
700
Write events
701
Delete events
17
Modification events
| (PID) Process: | (3116) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2728) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000043AC419338AD401A80A000080090000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2728) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000043AC419338AD401A80A000080090000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2728) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 20 | |||
| (PID) Process: | (2728) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 400000000000000030E6311A338AD401A80A000080090000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2728) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000008A48341A338AD401A80A000008050000E8030000010000000000000000000000A35C6C745F7A5B4AA4A589C717A4CA700000000000000000 | |||
| (PID) Process: | (2664) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000005A5B471A338AD401680A0000840C0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2664) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000005A5B471A338AD401680A0000B40C0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2664) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000005A5B471A338AD401680A000084080000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2664) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000005A5B471A338AD401680A0000A0080000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
25
Suspicious files
65
Text files
160
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3116 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIB647.tmp | — | |
MD5:— | SHA256:— | |||
| 3116 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIB687.tmp | — | |
MD5:— | SHA256:— | |||
| 2728 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 2728 | msiexec.exe | C:\Windows\Installer\1a11e3.msi | — | |
MD5:— | SHA256:— | |||
| 2728 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DFD69FDC181223294A.TMP | — | |
MD5:— | SHA256:— | |||
| 2664 | vssvc.exe | C: | — | |
MD5:— | SHA256:— | |||
| 1668 | DrvInst.exe | C:\Windows\INF\setupapi.dev.log | ini | |
MD5:— | SHA256:— | |||
| 2728 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{746c5ca3-7a5f-4a5b-a4a5-89c717a4ca70}_OnDiskSnapshotProp | binary | |
MD5:— | SHA256:— | |||
| 1668 | DrvInst.exe | C:\Windows\INF\setupapi.ev3 | binary | |
MD5:— | SHA256:— | |||
| 2728 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
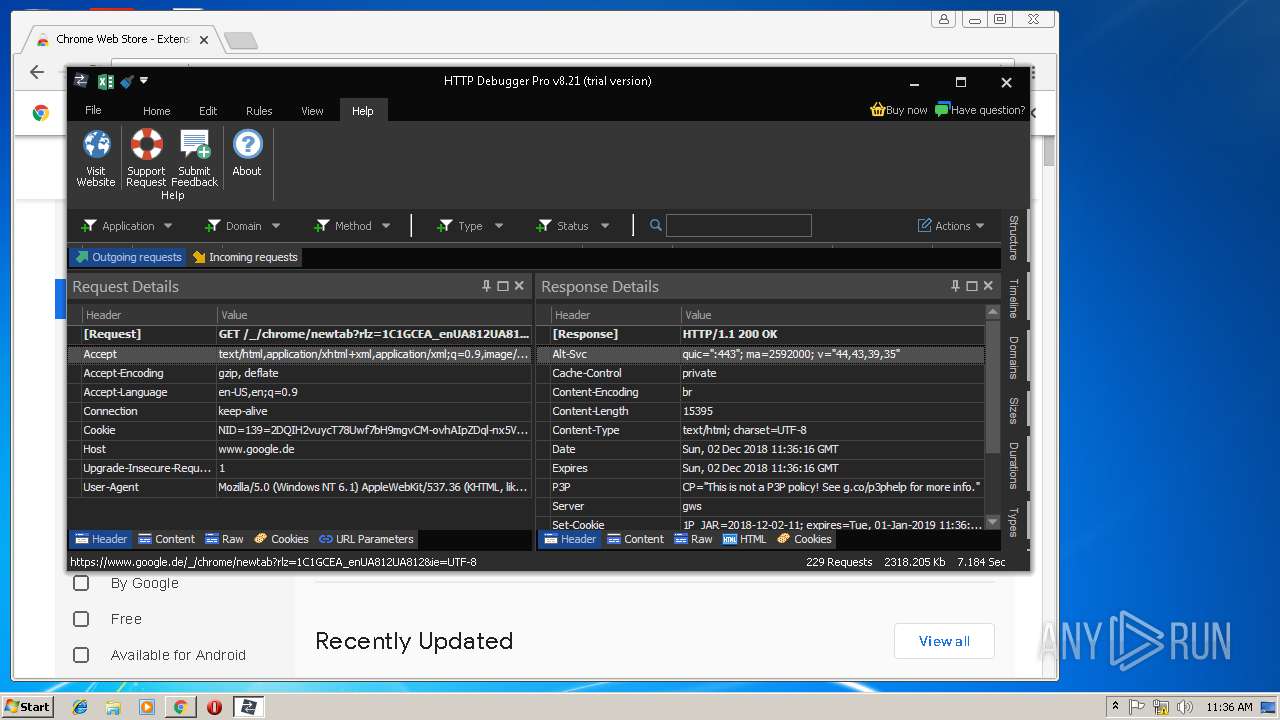
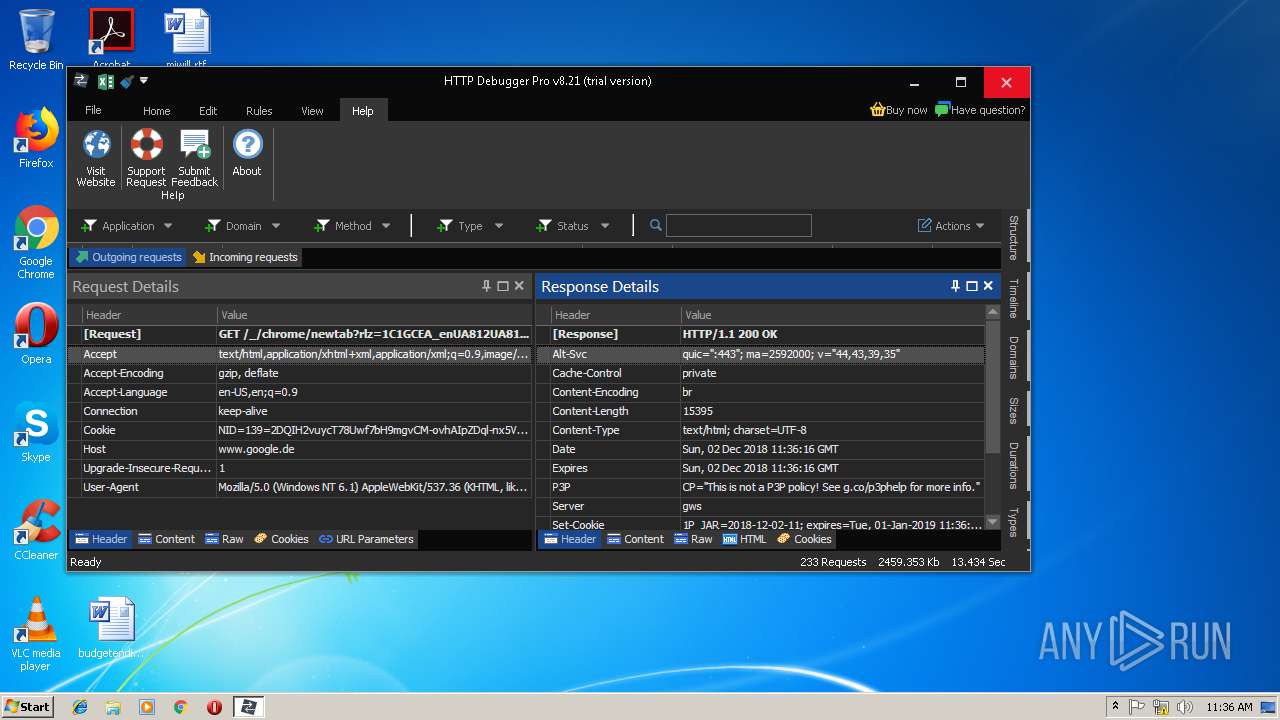
HTTP(S) requests
1
TCP/UDP connections
37
DNS requests
15
Threats
0
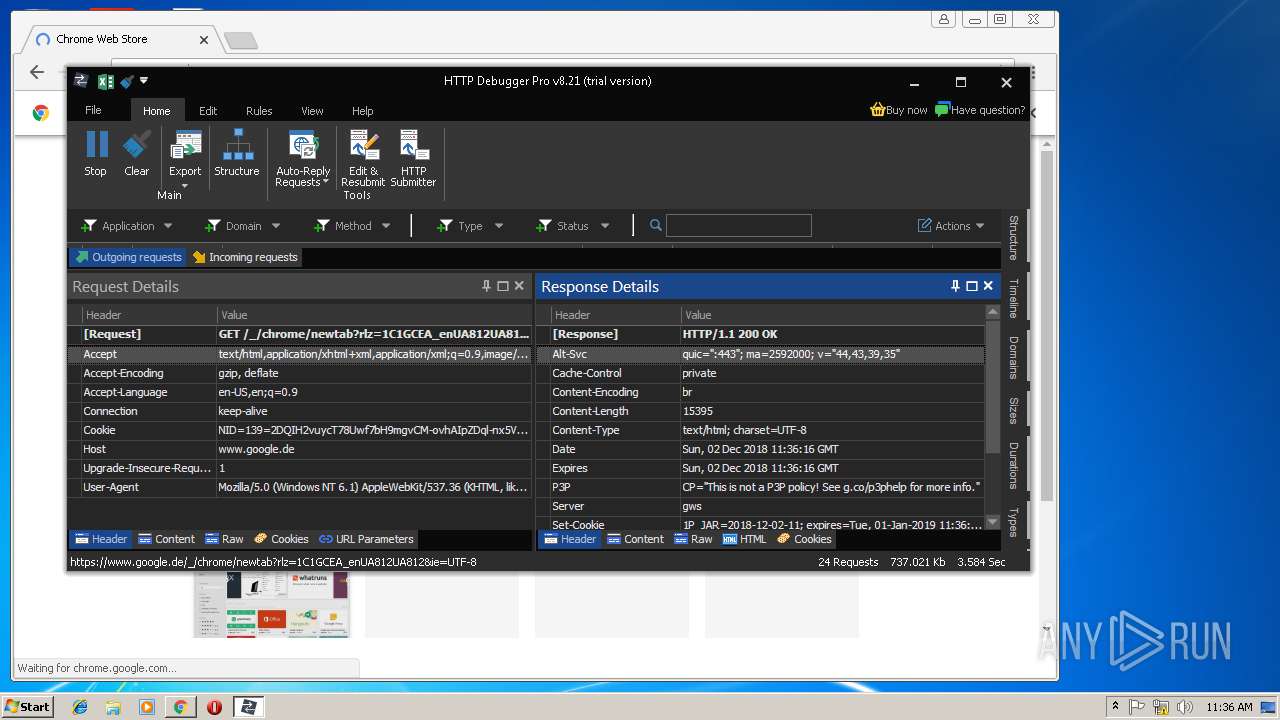
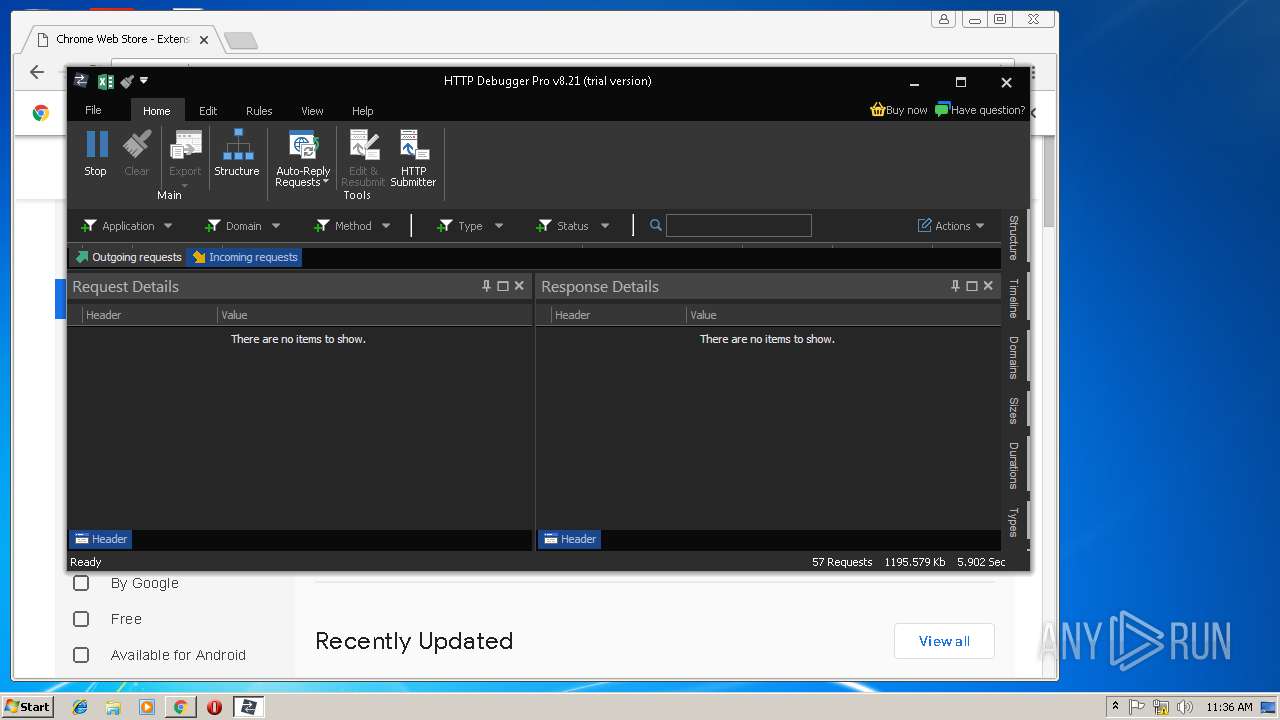
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1472 | HTTPDebuggerUI.exe | GET | 200 | 104.31.64.244:80 | http://www.httpdebugger.com/tools/checkupdate2.ashx?hash=90059c37132041a4b58d2b75a9850d2f&ver=8.0.0.21&sn= | US | text | 15 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1472 | HTTPDebuggerUI.exe | 104.31.64.244:80 | www.httpdebugger.com | Cloudflare Inc | US | shared |
1792 | chrome.exe | 172.217.168.42:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
1792 | chrome.exe | 172.217.168.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
1792 | chrome.exe | 216.58.215.238:443 | chrome.google.com | Google Inc. | US | whitelisted |
1792 | chrome.exe | 66.102.1.101:443 | apis.google.com | Google Inc. | US | whitelisted |
1792 | chrome.exe | 172.217.168.4:443 | www.google.com | Google Inc. | US | whitelisted |
1792 | chrome.exe | 216.58.215.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1792 | chrome.exe | 172.217.168.8:443 | ssl.google-analytics.com | Google Inc. | US | whitelisted |
1792 | chrome.exe | 172.217.168.3:443 | www.google.de | Google Inc. | US | whitelisted |
1792 | chrome.exe | 216.58.215.225:443 | lh3.googleusercontent.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.httpdebugger.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
www.google.de |
| whitelisted |
www.gstatic.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
chrome.google.com |
| whitelisted |
www.google.com |
| malicious |