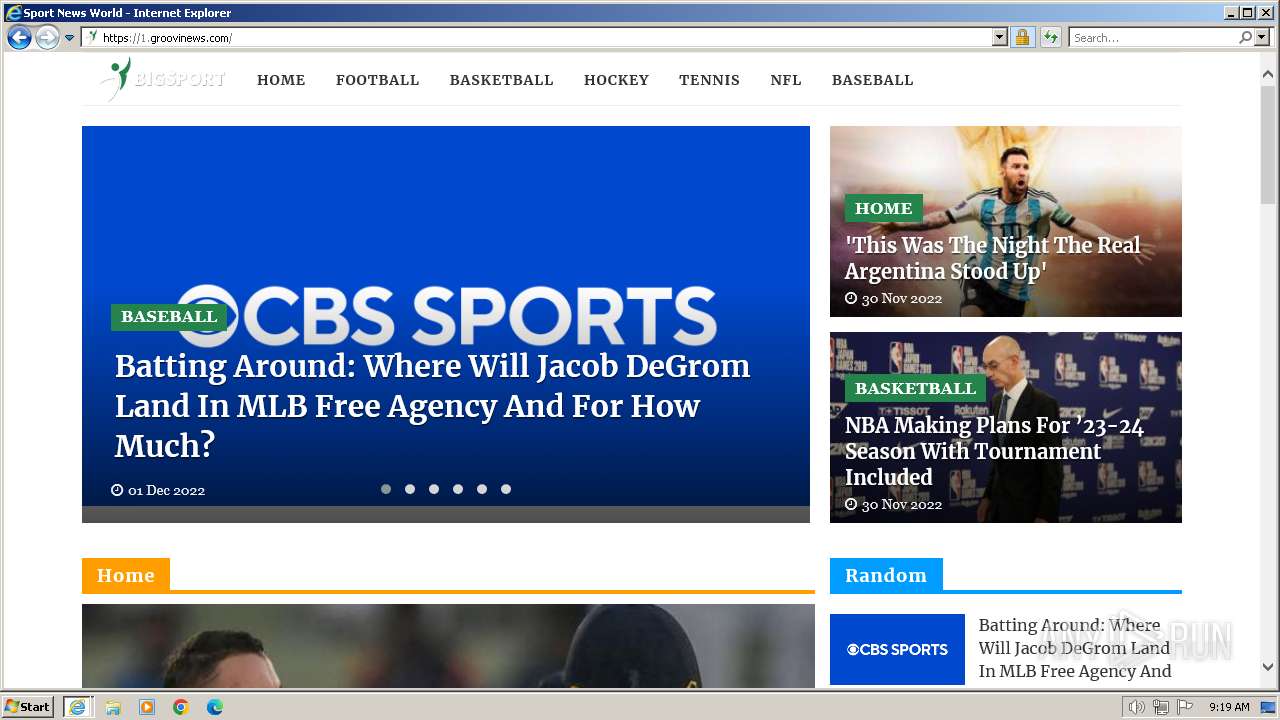
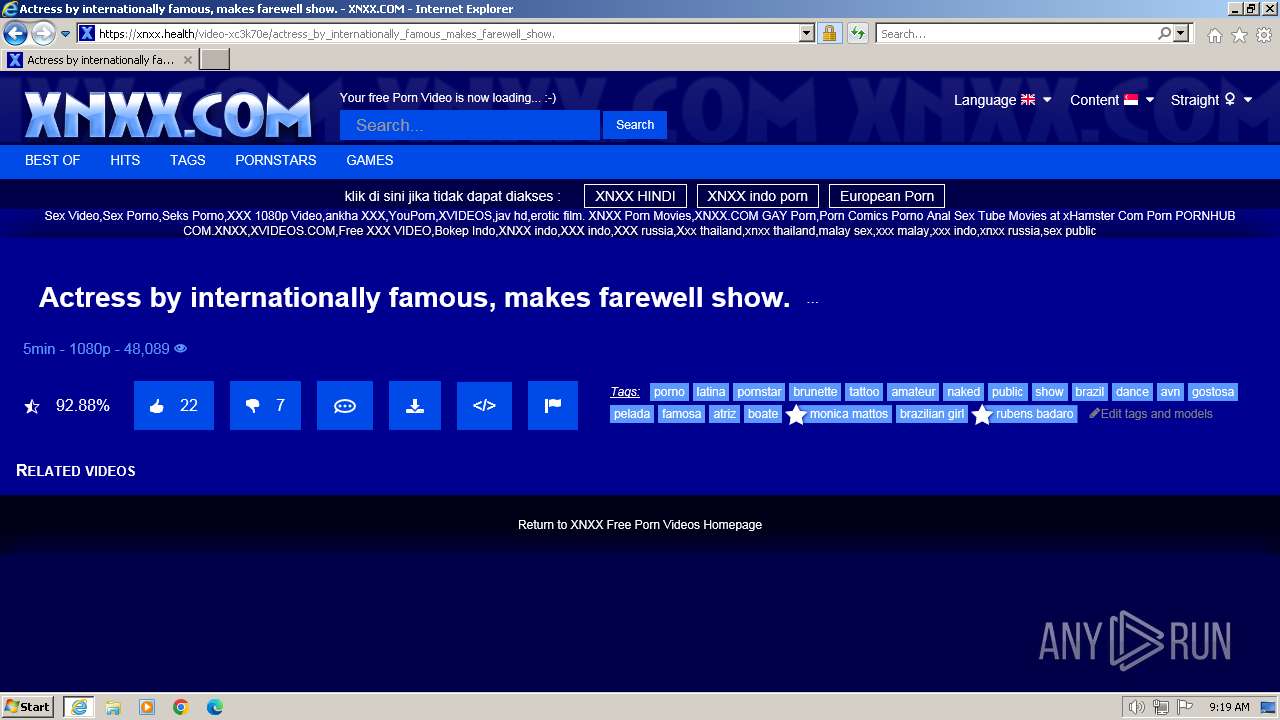
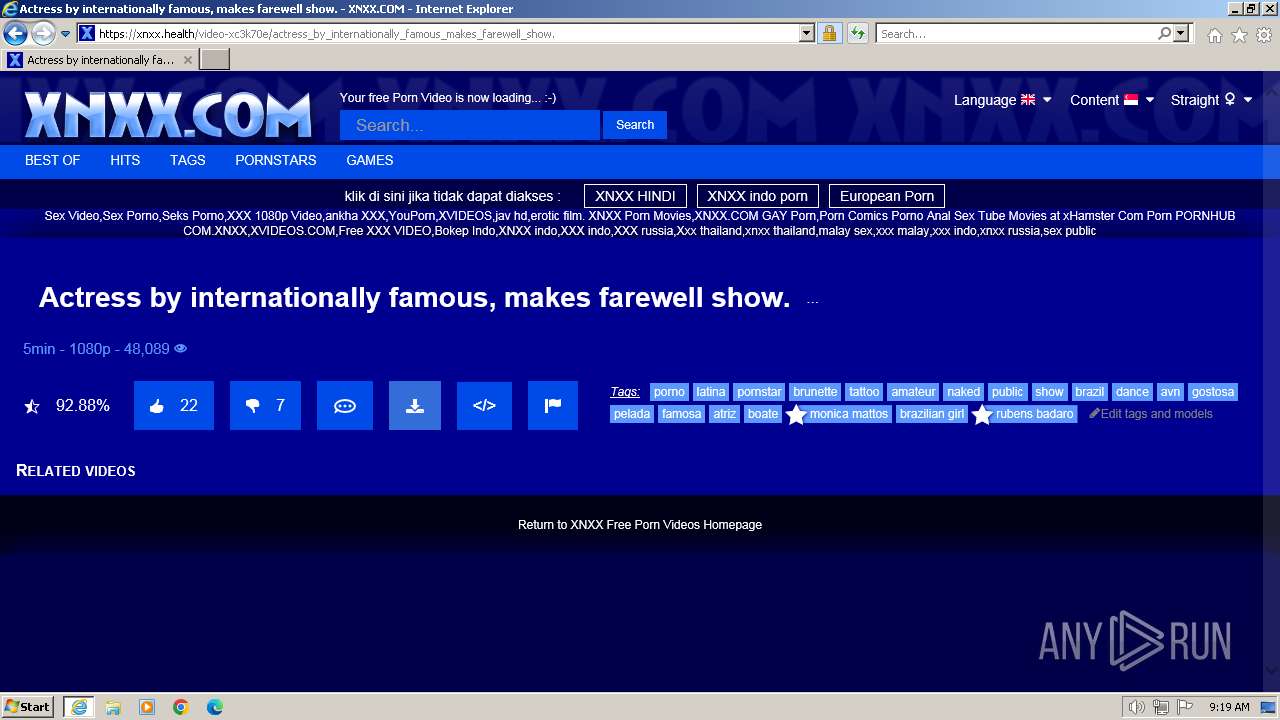
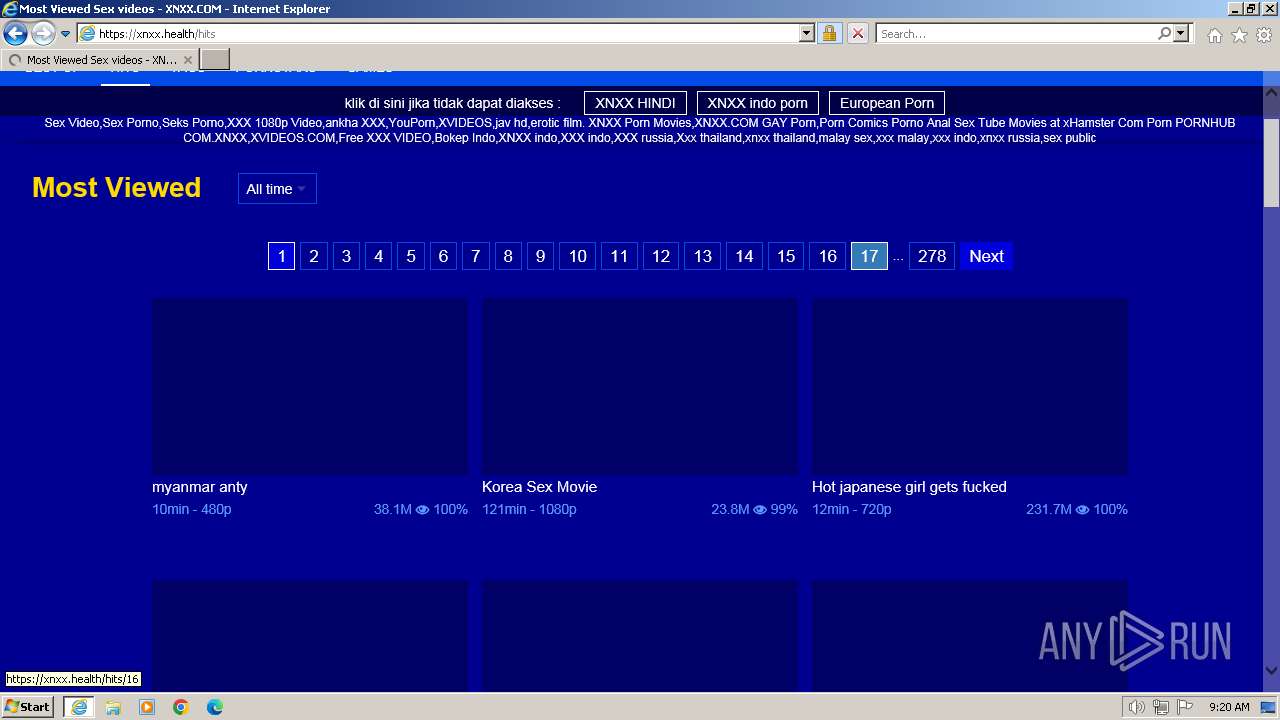
| URL: | https://xnxx.health/search/actress+bollywood+celebrities+famous/3 |
| Full analysis: | https://app.any.run/tasks/e5cc23a4-9579-4934-a405-f0802ca6d092 |
| Verdict: | Malicious activity |
| Analysis date: | January 12, 2024, 09:19:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 1E2C2A1FBA17C560195ECF1194ADC85B |
| SHA1: | 939FEF1C25D0A424D64A5B1EB6A398603C166D20 |
| SHA256: | B7B5677ECFCAD70B829449F59C9D9027CB338C7247FA6A590273EDF373F4ECFC |
| SSDEEP: | 3:N8nxAEJJwpGxAWEHcUBOZ0ZiQDKWn:2GgJwWAWEHcU4Z0jDN |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 128)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://xnxx.health/search/actress+bollywood+celebrities+famous/3" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1892 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:128 CREDAT:202020 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2032 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:128 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
29 390
Read events
29 177
Write events
207
Delete events
6
Modification events
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
80
Text files
126
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2032 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:65468040F53D22CBDFD84B5124682FA4 | SHA256:5B92674806E478A70BFDC3CFCAB59136BCD29EB5F2E22E2A1327F045A5529A4C | |||
| 2032 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_F2DAF19C1F776537105D08FC8D978464 | binary | |
MD5:8202A1CD02E7D69597995CABBE881A12 | SHA256:58F381C3A0A0ACE6321DA22E40BD44A597BD98B9C9390AB9258426B5CF75A7A5 | |||
| 2032 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:5EA79B7DE828B93E6AD0147A80918514 | SHA256:B82E4AFE5CA299DCEE74598709D18C2E93413C05C80D94720C9E0C7196F6F587 | |||
| 2032 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:4EFD39D710F594189320153618811A37 | SHA256:15E32B15A06ACC166F84D26421AB949C1032E16BD4EE9B2E4C4DB036B096D7E1 | |||
| 2032 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 128 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EAF8AA29A62AB29E614331747385D816_F9E4DC0B9D5C777357D7DB8DEF51118A | der | |
MD5:3651EFE3C0DEAC400E323005E136EEE5 | SHA256:9C928745D7E2F5561C5E5FAFE5281CA741FAEA3EB895D4A508D47ECB7AC4A148 | |||
| 2032 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab3565.tmp | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 2032 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_F2DAF19C1F776537105D08FC8D978464 | binary | |
MD5:D0EDE34F60DA7C2AC1281A01C1D33ADA | SHA256:10ED888EB67D2B9274A99E6966E2B6938AB86651F0FD8E642E33DF53D03A7C21 | |||
| 128 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EAF8AA29A62AB29E614331747385D816_F9E4DC0B9D5C777357D7DB8DEF51118A | binary | |
MD5:102C5D7B021E267CAE262A188B9ABFF7 | SHA256:06F562CCA8D4216E896D7CDB39B2193191F742773B7BB7A64D7AE6165A1C8271 | |||
| 2032 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
81
DNS requests
37
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2032 | iexplore.exe | GET | 200 | 142.250.186.99:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFCjJ1PwkYAi7fE%3D | US | binary | 724 b | unknown |
128 | iexplore.exe | GET | 304 | 95.101.54.128:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?1a6e676fbb64f2cc | DE | — | — | unknown |
2032 | iexplore.exe | GET | 200 | 95.101.54.128:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?3ce656fc36cced7b | DE | compressed | 65.2 Kb | unknown |
128 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | US | binary | 313 b | unknown |
2032 | iexplore.exe | GET | 200 | 95.101.54.128:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?7f4ae261cec090e7 | DE | compressed | 65.2 Kb | unknown |
2032 | iexplore.exe | GET | 200 | 95.101.54.128:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?57eeb1ed87d628b8 | DE | compressed | 65.2 Kb | unknown |
2032 | iexplore.exe | GET | 200 | 95.101.54.128:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?b6d654a0ac6a99ad | DE | compressed | 65.2 Kb | unknown |
2032 | iexplore.exe | GET | 200 | 95.101.54.128:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?68ff3cde403b189d | DE | compressed | 65.2 Kb | unknown |
2032 | iexplore.exe | GET | 200 | 95.101.54.128:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?5f7acf1cc1f27bc4 | DE | compressed | 65.2 Kb | unknown |
2032 | iexplore.exe | GET | 200 | 95.101.54.128:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?aeb5a2944d00d32d | DE | compressed | 65.2 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
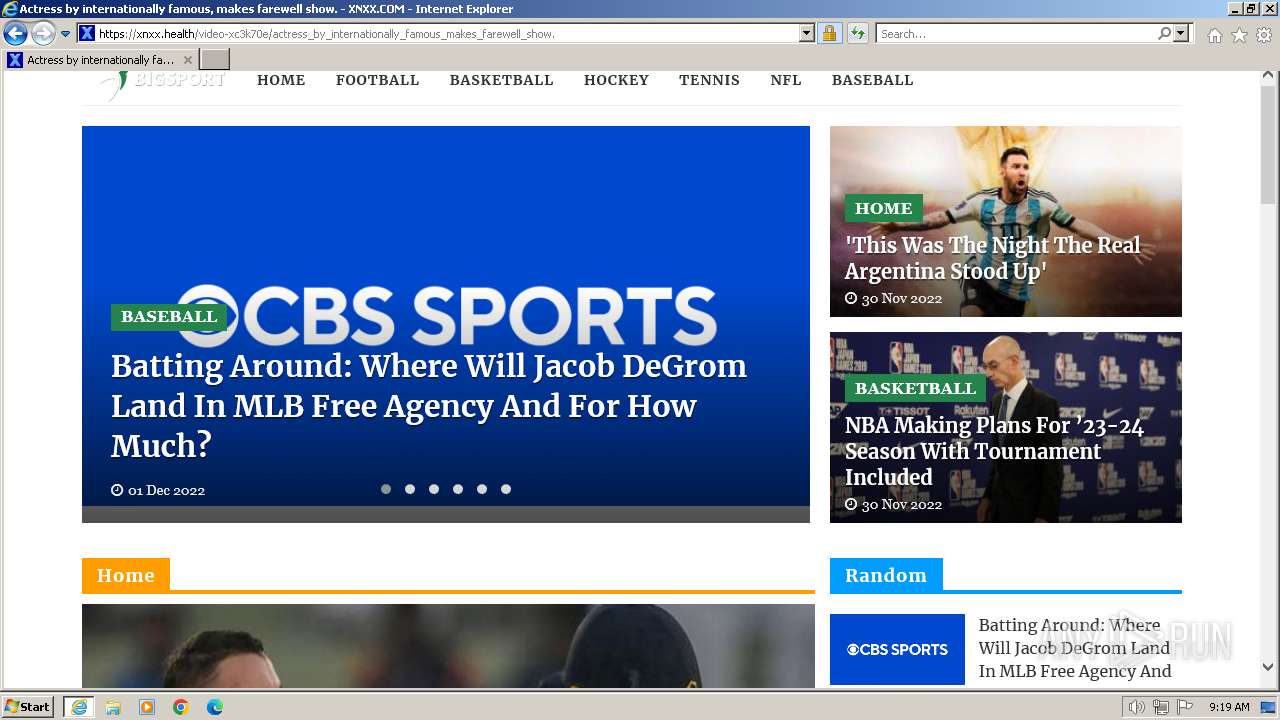
2032 | iexplore.exe | 104.26.5.154:443 | xnxx.health | CLOUDFLARENET | US | unknown |
2032 | iexplore.exe | 95.101.54.128:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
2032 | iexplore.exe | 142.250.186.99:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
128 | iexplore.exe | 2.23.209.150:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
128 | iexplore.exe | 95.101.54.128:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
128 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2032 | iexplore.exe | 156.146.33.6:443 | static-cdn77.xnxx-cdn.com | Datacamp Limited | DE | unknown |
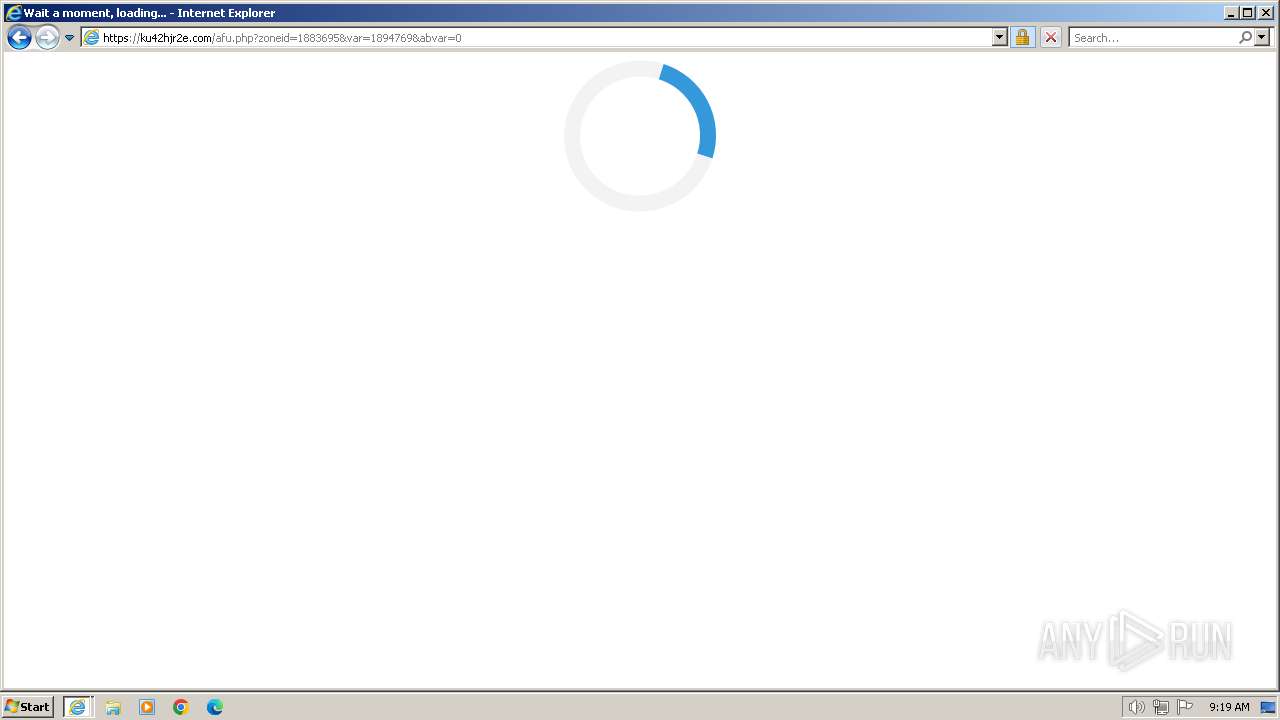
2032 | iexplore.exe | 212.117.190.201:443 | ku42hjr2e.com | — | LU | unknown |
2032 | iexplore.exe | 2.19.105.18:80 | x1.c.lencr.org | AKAMAI-AS | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
xnxx.health |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
static-cdn77.xnxx-cdn.com |
| unknown |
ku42hjr2e.com |
| unknown |
x1.c.lencr.org |
| whitelisted |
ocsp.buypass.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1892 | iexplore.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
1892 | iexplore.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
1892 | iexplore.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code.jquery .com) |
128 | iexplore.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
128 | iexplore.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |